Abstract
Although higher learning institutions (HEIs) are quickly evolving and opening to cyber-attacks, we question this very process cautiously with the intention of capturing the vulnerabilities of the HEIs systematically over the time frame of the 2018 to 2025, which PRISMA framework allows transparency and rigour in the methodology. The thematic and content analysis of 33 peer-reviewed articles revealed nine main cybersecurity challenges that include phishing, malware attacks, intellectual property theft, external threat actors, software vulnerabilities, password insecurity, insufficient physical protection, and weak incident disclosure practices. Their results suggest that phishing and malware have remained the most reported most reported threats, and human factors such as the absence of cybersecurity awareness and inadequate training provided keep on increasing the institutional risk. In addition, the research points out to unbalanced coverage of research methods where quantitative research studies prevail, and the qualitative or mixed methods research studies are underrepresented. This research is significant because it discusses general threats in the various categories of threats and distinguishes between outside and inside vulnerability of an organisation, and matches the threats with the current frameworks, such as the CIA (Confidentiality, Integrity, Availability) triad and NIST cybersecurity standards. The review summarises the implications with practical suggestions for implementing integrated cybersecurity frameworks, integrating technical protection, user education and policy planning. Other directions for future research include expanding geographically and investigating the new threats presented by artificial intelligence, cloud computing and Internet of Things (IoT) infrastructure in HEIs.
Plain Language Summary
Higher education institutions (HEIs) are becoming increasingly digital, which exposes them to more cybersecurity risks. This study reviews research published between 2018 and 2025 to better understand the main threats faced by universities and colleges. Using a transparent and structured approach (the PRISMA framework), we analysed 33 peer-reviewed studies. The review identifies nine major cybersecurity challenges affecting HEIs, including phishing, malware, software weaknesses, password problems, theft of intellectual property, and limited physical security. Phishing and malware continue to be the most common threats. Many risks also stem from human behaviour, such as low awareness of cybersecurity issues and limited training for staff and students. We also found that most existing research focuses on quantitative methods, with fewer studies using qualitative or mixed approaches. This limits deeper insights into how cybersecurity issues actually affect people and processes within HEIs. This review adds value by distinguishing between threats coming from outside the institution and vulnerabilities that exist inside it. We also compare these risks with widely used cybersecurity frameworks, such as the CIA triad and the NIST standards. Based on the evidence, we offer practical suggestions for improving cybersecurity in HEIs, including better technical safeguards, stronger user education, and clearer institutional policies. Finally, the study highlights the need for future research on new and emerging risks related to artificial intelligence, cloud services, and the Internet of Things (IoT), as well as more studies from different regions of the world.
Introduction
Many sectors, including telecoms, government, businesses and healthcare, face pressing challenges with online safety. Especially in the education sector, HEIs are among those where hackers can access networks and steal sensitive data anytime and anywhere. HEIs present an increased risk as they operate in an open system that guarantees free data access (Davidson & Hasledalen, 2014). Davidson and Hasledalen (2014) are right that cybersecurity threats are more prevalent for higher education institutions since they have an open and accessible architecture, but such an understanding fails to account for how institutional policies layered defences, and evolving awareness programmes impact risk.
This is because HEIs have a long history and have considerable historical resources, including intellectual property and research results. Also, such elements are used as an inducement for criminals to attack universities to carry out acts of this nature (Di Berardino & Corsi, 2018). It is about safeguarding faculty/students’ insights, knowledge base, and personal information. The proliferation of social media platforms has further complicated cybersecurity risk management; users can post anything and be targeted for criminal purposes, such as for identity theft, and then on. This transparency might generate attacks such as phishing, where attackers exploit gaps to acquire personal or academic information on a student. (Elmi, 2019; Madyira, 2015).
Many people in the education sector do not know much about simple things concerning the cyber world, despite efforts being put in place to teach them (Kennison & Chan-Tin, 2020). This is a situation they can always face, especially when involved in online research, studies, and academic communications, since cybercriminals are fond of attacking such people through phishing, among other crimes (Elmi, 2019). This leads to catastrophic academic results, like loss of data, which may range from research findings to personal details.
These risks are largely attributable to internal institutional weaknesses within universities, including inadequate implementation of fundamental security controls and insufficient user awareness of phishing attacks. The literature indicates that many cybersecurity breaches in higher education institutions stem from human error, such as poor password practices, weak identity and access management, and users inadvertently compromising credentials through phishing and social engineering (Yaro & Mohd, 2025). Many educational institutions, primarily smaller ones, face the problem due to the absence of specialised cybersecurity squads; it becomes difficult for them to enforce effective network monitoring or act swiftly in the face of security incidents (Oslan et al., 2023). The IT departments of these institutions are often involved in many roles, including administration and security, thus increasing the pressure on them and reducing their ability to handle cyber threats effectively (Yusif & Hafeez-Baig, 2023). Conversely, the security measures implemented on other university networks remain exposed through security holes, such as weak password schemes or unprotected data transmissions (Nurse et al., 2021; Yusif & Hafeez-Baig, 2023;).
Following recent breach examples, the security of information systems inside the education segment has gained growing concern. Cybersecurity is the protection of assets, which involves treating the threat of how data is processed through the Internet, where it is stored, transmitted and retrieved, and stored on an electronic network (Ariffin & Ahmad, 2021). A university in the United States, for instance, suffered with ransomware in 2024 that encrypted documents critical to student life, including their personal details, leaving the campus without access to the necessary files for weeks (Singh Lallie et al., 2025). As a ransom, the criminals demanded millions, which interrupts both the learning process and damages its image before the public domain (Chabrow, 2015). Likewise, an unpatched post detected in an educational platform available on its login page contributed to an invasion of personal and scholastic data among more than 200,000 users in a similar incident in the U.K. (Brown & Taylor, 2024). This is why all schools should be incorporating strong measures of identification like multi-factor authentication in addition to regular application updates, to ensure their students’ records are secure as well.
Cybercriminals target universities because they carry and process vast amounts of user financial and research data. Inside a university, there is not just the usual external threat with external factors involved; universities also face a new insider threat from the student population (Savas & Karatas, 2022). Even with access to many sensitive systems, students and staff may not have adequate cybersecurity training. This paper is a comprehensive assessment of the current state of cybersecurity threats facing UK universities stemming from the analysis of existing data. Cases are classified according to incident type and the CIA triad to create a timeline of major cyber-attacks against universities (Singh Lallie et al., 2025). There are a few issues identified. A major concern in higher education cybersecurity is the limited disclosure of attack details, as incident information is often withheld for security and reputational reasons, thereby constraining institutions, ability to fully assess vulnerabilities and implement effective countermeasures. This challenge is further exacerbated by the increasing reliance of universities on third-party service providers, particularly cloud platforms, where a successful attack on external providers can directly compromise institutional data security and disrupt university operations (Afolalu & Tsoeu, 2025). Other threats remain, even though SQL injection attacks that used to be a major problem appear to have declined in prevalence, perhaps due to better defences. Ransomware and phishing attacks remain popular, but higher education institutions are now less concerned with DDoS, and this prompts us to believe that the defences have worked. Internal threats are added to these threats particularly by IT literate students which consists of an IT amalgamation of knowledge (Singh Lallie et al., 2025). Insiders may unintentionally or intentionally aid a cyber-attack, and this translates to a perpetual problem for IT service providers in universities. New research potentially resulted in a thorough reconsideration of such things by the universities in the context of cybersecurity. It appears evident to us that due to the evidence that we must concentrate on developing the policy, provision of the necessary training to employees and following international norms that this is not about a tick box but that current threats have indeed become more complex. Facing the fact that such protection may be insufficient, such software protection must be regularly updated with several factors of authentication and frequent basic software updates in case an institution wants to be adequate in the protection of student records.
The implications are barely theoretical. A 2024 breach of an Australian university in which the attackers took advantage of an unencrypted backup demonstrates this fact. Their perimeter defences turned out to be resilient, but lacked internal protocols, so that no one knew what was going on (Jones et al., 2024). Higher education organisations in Malaysia have similarly experienced data theft by phishing attacks. Consequently, Malaysia took the initiative to develop the Cybersecurity Act 2024 to create awareness and improve cyber resilience mechanisms in educational organisations (Lee & Tan, 2024). The Malaysian government has also been proactive in upgrading its ICT infrastructure to better protect digital assets improve the credibility and trust that people have for using cyberspace (Zammani et al., 2019). In 2020–2024, their Malaysian Cybersecurity Strategies were a systematic approach which aims to address security in the governmental, business, and social sectors (Zammani & Razali, 2021). Data breaches are on the rise and, in sectors that handle heavy volumes of sensitive information (such as education), the need for more holistic and adaptive cybersecurity frameworks has never been greater (Salam et al., 2025). Universities, an organisation that has extensive data repositories, are particularly susceptible to these risks and need to put an emphasis on these problems to protect their communities.
These breaches contribute to the greater issue of cybersecurity readiness in schools throughout the country. As there are schools which deploy current technology to safeguard student information systems from being hacked by the outside or from within, many are left armed with outdated equipment, poorly trained staff, and inadequate financial support (Wilson, 2024). And as the digitalisation of administrative tasks, e-learning, expands, so too do the challenges faced by campuses when wanting to update themselves with the most up-to-date information of the day, be it attacks like malware attacks coming from which they might need to address the situation, and this could call for a move away from pure technology solutions and instead make a systemic change, where establishment-wide staff are trained on cyber security via regular updates.
In reality, cybersecurity is essential to the success of institutions of higher learning, from examples of such events as the cyber-attacks endured by the UK’s leading universities such as the University of Oxford and University College London, that had given rise to fears that hackers would be able to gain access and keep a profile on institutions (Mai Online, 2017). Elsewhere, in locations for which criminals have demanded tremendous sums in exchange for repairs to lost files that have been breached (Butt et al., 2020), for instance, the Harare Institute of Technology. This implies that the financial threats of hacking on university systems are growing. Conversely, some university libraries have some reliance on open-source software, so softcopy printouts in these institutions are questionable. Although cheap, open-source solutions may leave HEIs more vulnerable to cyber-attacks due to insufficient protection (Okokpujie et al., 2021; Rafiq & Ameen, 2021). As such, institutions of higher learning are responsible for large numbers of research papers, so they need to build a secure system responsible for information protection.
The cybersecurity issues faced by HEIs go beyond the technology aspect and go beyond it, it is to the part of preventing human error, like mere password maintenance practices, which is a highly serious risk. Users are advised to use many combinations of different types of passwords (e.g. complex vs random), but even this makes users always resort to short passwords or still resort to the old ones, rendering the systems more at risk for attack (Pavlova, 2020; Szumski, 2018). Secondly, the safety of physical security for university infrastructures that include servers and data storage systems is generally assumed, so that it may fall victim to external and internal threats (Ngulube, 2019). Education institutions continue to be vulnerable to phishing, malware and ransomware attacks. Global report finds >200,000 cases of malware infection daily (Alzubaidi, 2021). HEIs, like any other organisation, needs a holistic response to the threat of cyber-attacks with technological solutions and user awareness to combat such incidents (Cranor, 2017; Datta, 2022).
The limitations of this review are addressed in three aspects. First, it uses a transparent and systematic approach following the PRISMA framework to locate and summarise empirical studies published between 2018 and 2025. Second, it distils redundant categories into higher-level themes that are more direct and non-redundant by way of categorising threat and vulnerability but stay true to the evidence. Third, it integrates methodological trends and practical suggestions to show where the field is converging on–and where it may need more effort–by integrating empirical evidence on governance, technical controls and security culture in the governance area. To inform the study, it is based on three questions: RQ1) What are the major cybersecurity threats and vulnerabilities in higher education institutions? (RQ2) What research methods and trends characterise the evidence base? (RQ3) What recommendations emerge for improving cybersecurity practice and policy in higher education? The answers to such questions give a systematic representation of existing risks, outline the boundaries of these perceptions and guide actionable steps to make cyber resilient universities.
Contribution to HEIs Digitalisation
The rapid pace of digitalisation in higher education has increasingly exposed universities and colleges to cybersecurity threats. These kinds of institutions with their open networks and large quantities of data stores prove easy prey for cybercriminals looking to take advantage of vulnerabilities. Sensitive information such as scientific reports, student records, and proprietary data has become more vulnerable than ever, facing dangers like hacking, phishing, and ransomware attacks (Newhouse et al., 2017). Even as technology has advanced, most institutions are not ready, with outdated hardware and software, a lack of qualified specialists to work in a cybersecurity role, and poor internal policies. The growing intricacy and occurrence of computer attacks which include malware and data invasion, among others points to the great need to ensure that higher educational bodies possess a detailed and in-depth cybersecurity strategy.
That should not just be through investing in hi-tech solutions but rather should be placed within the general policy framework to handle these issues. Human behaviour is a matter of central concern to security, and huge hack attacks are committed through mere human errors, password misuse, experience of phishing frauds and ignorance regarding security. Therefore, a culture of cybersecurity should be encouraged at the entire campus. Students, staff, and faculty must be made sure by institutions to get access to data regarding the risks and the most optimal practices in cyberspace.
Moreover, robust cybersecurity systems would also imply continuous updates to the systems, as well as their additions and utilisation of multifactor authentication under the assistance of specialised security forces (Yaro & Mohd, 2025). By rather than focusing on the technical deficiencies, the human factors of the situation will afford the high education institutions more ground in combating the compounded dangers and improving the persistence and authenticity of their educational endeavours.
This study contributes to a clearer understanding of how higher education institutions can strengthen their cybersecurity posture amid rapid digitalisation. By systematically reviewing empirical evidence from 2018 to 2025, the paper consolidates scattered insights into a coherent view of current risks, patterns, and mitigation strategies in the academic context. This study integrates the technical, institutional, and human aspects of cybersecurity, in contrast to many previous studies that only looked at technology or policy. The results are intended to help researchers, policymakers, and university administrators create a more knowledgeable, secure, and resilient academic community.
Methodology
Considering the rising popularity of studies on cybersecurity published during the 2018–2025 period, the definition of this time was informed by the growing concern that higher education institutions face cyber threats. In their study process, the authors did not deviate off PRISMA (Preferred Reporting Items of Systematic Reviews and Meta-Analyses) guidelines. PRISMA aids organisations to perform identification, screening, and synthesising of available literature in a systematic way that reduces bias and enhances a stronger methodological consistency (Page et al., 2021). Although its fundamental principles were originally introduced in health and medical research, it is also being used in other fields of practice, such as social sciences, education, and cybersecurity, whereby synthesising systematic evidence is vital to come up with practice recommendations and actionable policies.
PRISMA is among the fundamental strengths in this respect; the fact that the framework is clear and replicable is a great strength as well. It consists of a detailed checklist and flow chart where the authors begin with the construction of the research question and proceed to identification and selection of studies, data synthesis and emphasis (Moher et al., 2009). Not only did this rigorous process make sure that bias and error are kept at a minimum, but it also allowed the reader to follow a series of step-by-step progress towards conclusions from the study. Explicitly defined inclusion and exclusion criteria during the screening process were also followed, and a systematic approach was maintained to extract and analyse data in this study (Moher et al., 2009). Therefore, through the PRISMA framework, they took care to conduct an unbiased and comprehensive analysis of the existing literature. This ensures the quality, reliability, and reproducibility of systematic reviews and meta-analyses, regardless of the research domain.
Formulation of Research Questions (RQ)
The PICo framework: population, interest, and context were used in the current study to clearly develop the topic of their research. Using these parameters, they set exact boundaries according to these constraints. enables them to hone their inquiries and refine the main research question. PICo contains three conceptual dimensions: population or problem, interest, and context. The research questions were developed by way of a PICo framework emphasising Population, Interest, and Context.
Population: university personnel, including students, faculty members, and administrators
Interest: cybersecurity issues, threats, and vulnerabilities
Context: higher education institutions
Based on this structure, three guiding research questions were developed:
RQ1: What are cybersecurity threats and vulnerabilities in higher education?
RQ2: What are the trends in research methods observed in the articles?
RQ3: What are the recommendations in the articles?
Systematic Searching Strategies
The systematic searching strategies have four main processes: identification, screening, eligibility, and inclusion (refer to Figure 1).
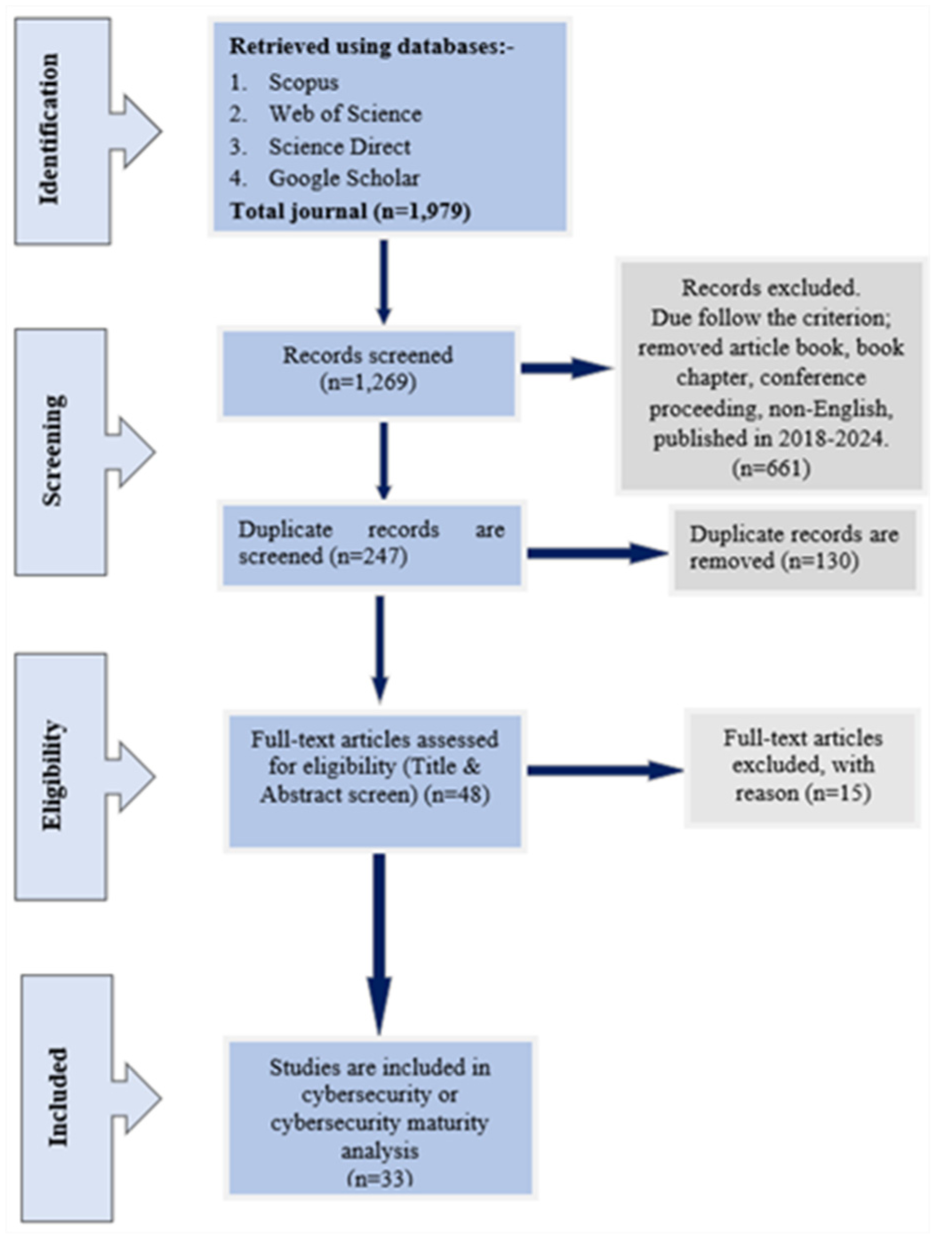
The PRISMA flow diagram
Identification
A comprehensive search strategy was employed to identify studies that addressed cybersecurity issues in HEIs. Four major academic databases were selected for their disciplinary breadth and research quality: Scopus, Web of Science, ScienceDirect, and Google Scholar. The search strings were constructed using combinations of keywords and Boolean operators (AND, OR) to maximise coverage and retrieve all relevant studies.
Example of a search string:
(“cybersecurity” OR “cyber-security”) AND (“issues” OR “threats” OR “vulnerabilities”) AND (“higher education” OR “university” OR “public university”)
These search strings were adapted slightly to fit the syntax and indexing systems of each database. To enhance reliability, the researchers also reviewed reference lists of key papers to identify additional relevant studies not captured through database searches. Boolean operators were applied to refine searches, words near each other, and truncation to retrieve different word endings without typing every possible form of a word, among many other things. Two significant advantages of these databases are intricate search engines, multiple disciplinary coverage, and quality assurance protocols (Table 1). Because of this, they qualify as top databases for systematic reviews concerning articles’ readability on different subjects. Moreover, Science Direct and Google Scholar were chosen for supplemental research to increase the thoroughness of the search.
The Search String.

Based on Gusenbauer’s (2019) findings, it is recommended that a combination of keywords be utilised through phrase searching and Boolean operators (OR, AND), as indicated in Table 1. The academic search engine performed satisfactorily, as shown in the research findings, with Google Scholar, Science Direct, Scopus, and Web of Science seen as essential additions. It also shows the number of articles based on the search string in the table. Results of the search conducted on those databases produced 1,979 articles—an illustration is given in Figure 1.
Screening
Under the criteria established by Kitchenha and Charters (2007), which were applied automatically through the database’s sorting function, all 1269 selected articles were screened. This process was carried out to answer the research question (Kitchenham & Charters, 2007). Because there are so many published works, academics cannot possibly review them all. Consequently, scholars should direct their research towards epochs.
According to the findings by Higgins and Green (2011) in their study, it should be implemented on limited dates, during which the relevant research work could be carried out. The search results from the chosen database revealed that the number of studies on cybersecurity issues in higher education has risen from 2018 to 2025. To ensure the review’s validity, only studies with actual data published in academic journals and written in English were considered (Table 2). Fifteen articles were excluded because they did not meet the inclusion criteria, while 48 were used in the eligibility assessment process.
The inclusion and exclusion criteria.

Eligibility
The authors carefully studied the retrieved articles for the qualification to ensure that all other articles, after the screening process, met said criteria. This was achieved by going through and analysing the titles and abstracts of the articles (Bolbot et al., 2020). This selection excluded nine articles because their focuses were cybersecurity and higher education, not K-12 education. Therefore, only 48 articles were picked.
Studied Included
Following screening of eligibility, the data of the included studies were systematically extracted and organised in a spreadsheet with the title of the study, authors, year of publication, country, and research design. Thematic analysis was subsequently conducted to examine those cybersecurity threats and vulnerabilities that repeatedly occurred in HEIs. The analysis was launched by reading all the included studies to define the repetitive patterns and new cybersecurity issues. Major keywords and concepts including ransomware, data breaches and password vulnerabilities were further identified and coded as initial indications of bigger problems. The initial codes were aggregated to similar tabulations and formed the basis used to make a choice of nine big themes.
To make sure that this was conceptually clear and representative of the data, the themes were further developed under the process of iterative comparison (Belle & Zhao, 2023). The coding was mainly inductive, and patterns and themes just emerged out of the studies contained without trying to pre-decide them. However, there was a deductive lens applied simultaneously that put the results into the context of current cybersecurity models such as the NIST modelling, especially the tenets of confidentiality, integrity and availability. This was a hybrid that saw to it that the thematic data-driven and theoretically consistent architecture that informed the design of the thematic framework was data-driven and synthesis between empirical evidence and conceptual rigour.
Results and Discussion
RQ1: What are Cybersecurity Threats and Vulnerabilities in HEI?
The review identified nine major cybersecurity themes across the analysed studies: intellectual property attacks, external threat actors, vulnerability disclosure, malware-related incidents, phishing, physical security weaknesses, password security, software vulnerabilities, and malware proliferation. Table 3 shows that phishing was the most studied issue among these themes. Similarly, hacking was another frequently studied.
The Cybersecurity Issues.
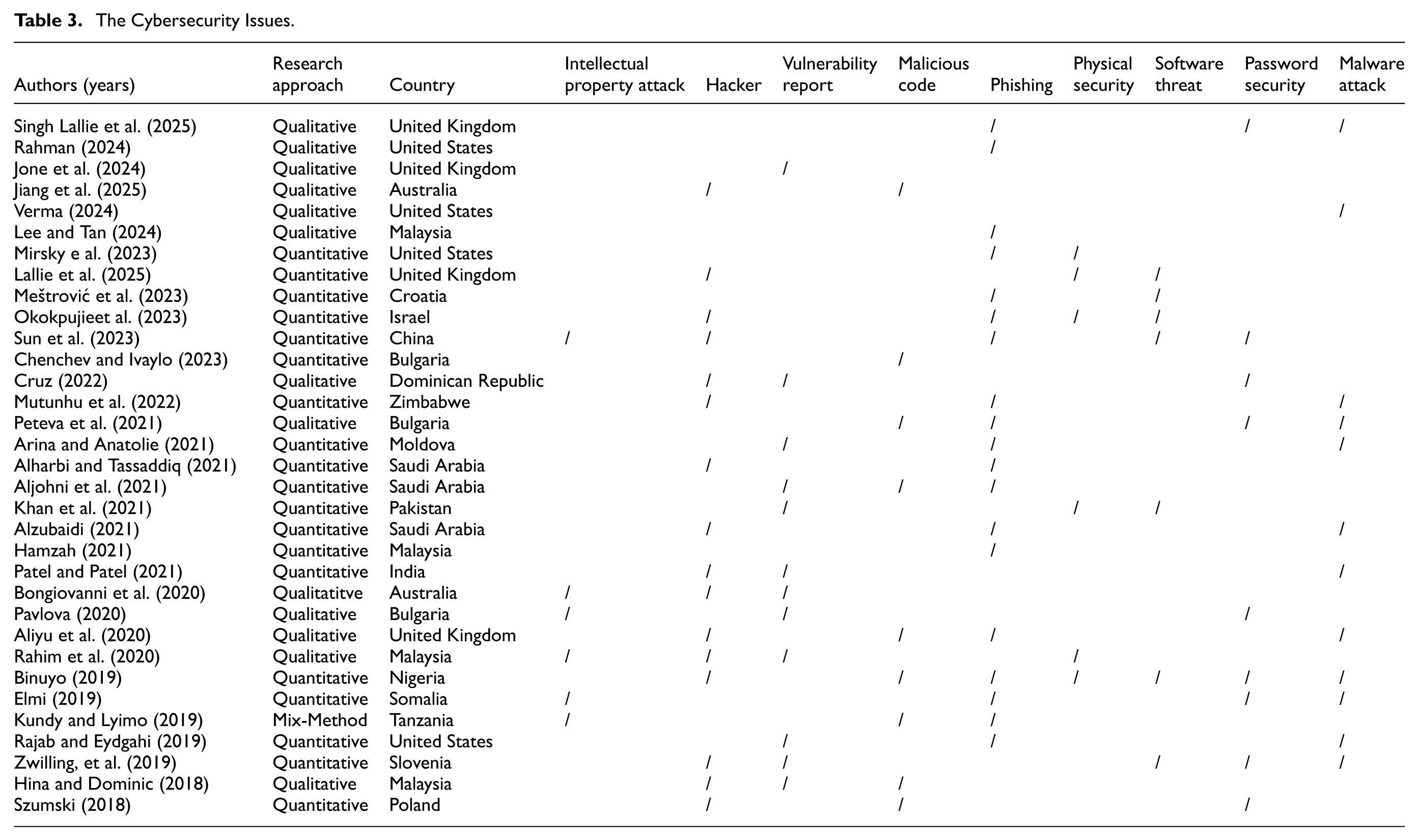
The third issue is the vulnerability report, which has been the subject of numerous studies. Similarly, the fourth issue is extensive malware attacks. The fifth issue is malicious hackers, which have also been studied. The sixth issue is password security, which has been addressed in various studies. Lastly, software threats, intellectual property attacks and software threat issues have also been the subject of research. Figure 2 illustrates the cybersecurity threats in higher education, highlighting the issues identified in each area.

Cybersecurity threats.
From the results, there may be some conceptual overlap between these themes and refinement is necessary. For example, “malicious code” and “malware attacks” cover the same phenomenon, and “hackers themselves” is too vague to be an analytic category. These terms should be replaced by clearer conceptual names that are more closely linked with academic field names: “external threat actors” or “malicious agents,” for example. The aim, by refining these categories, is to ensure that every theme is a unique and relevant dimension of cybersecurity risk at HEIs.
The thematic synthesis further shows that phishing is still the most studied and common threat followed by malware attacks and unauthorised access to intellectual property. There were other weaknesses that were not thoroughly investigated such as poor passwords, loopholes in the software, and physical access to the system, which are, however, crucial areas of vulnerability. Threats and vulnerabilities should be distinguished to explain these results in a more suitable way. Threats can be defined as an external or internal activity that can compromise the institutional security, including ransomware or phishing. Weaknesses are internal factors that can facilitate the attacks on institutional systems (e.g., bad password practices, backward software).
The analysis is more aligned to the principles of well-known frameworks like the CIA triad and the NIST categories of cybersecurity since the themes were organised through these notions. This method increases the level of analytical richness of the given study and relocates it into the framework of existing cybersecurity theory. These fine-tuned themes would be used collectively to offer better insight, and an understandable view of the inter-relational and intricate cybersecurity dangers facing HEIs. And the findings point out that the loopholes in the defence cannot be only technological but also human behaviour and organisational practices.
RQ2: What are the Trends in Research Methods Observed in the Articles?
This research made evident the existence of definite patterns in the research methodology that is applied to explore cybersecurity in institutions of higher learning. Quantitative research was the most frequently used tool; around 59% of the studies. The main idea of such approaches was based on the statistical analysis with an aim to understand the scope of the prevalence of cybersecurity threats, the level of risks and the efficiency of the mitigating strategies. 38% of studies employed qualitative methods and were guided by an intention to develop an understanding of the experiences, perceptions, and behaviours of students, staff, and administrators in cybersecurity.
These methods provided valuable indicators of human factors including susceptibility to phishing or password mismanagement, which would not hold true obtained through exclusively quantitative methods. Mixed methods were less frequent, only 3% of the studies, yet provided a more balanced perspective by combining numerical data with in-depth qualitative analysis as in Figure 3. Ultimately, trends indicate that, though quantitative data is the overall dominant trend in the field, qualitative and mixed methods are needed when studying the complex human and organisational dimensions of cybersecurity in HEIs.

Research Methods.
The studies conducted showed four studies were conducted in the United Kingdom, United States and Malaysia, three studies were done in Saudi Arabia, and Bulgaria, and two in Australia. In addition, one study was conducted in Israel, Moldova, Nigeria, Pakistan, Poland, Slovenia, Somalia, Tanzania, and Zimbabwe. Only one review article for cyber-attacks in 2025, five of the 33 selected articles were published in 2024, six in 2023, two in 2022, eight in 2021, four in 2020, five in 2019, and two in 2018 (Figure 4). The research landscape is geographically not uniform. Most studies were conducted in the US and Malaysia, then Saudi Arabia, the UK and Bulgaria. A smaller number were from countries like Australia, China, Nigeria and Zimbabwe (Figure 5). This dispersion means that research on cybersecurity in higher education is yet to be extended to broad areas, leading to the generalisation of results. This includes (but is not limited to) extending the geographical area to underrepresented regions, including Africa, Latin America, and Eastern Europe—would strengthen the world knowledge and add more inclusive cybersecurity policies.
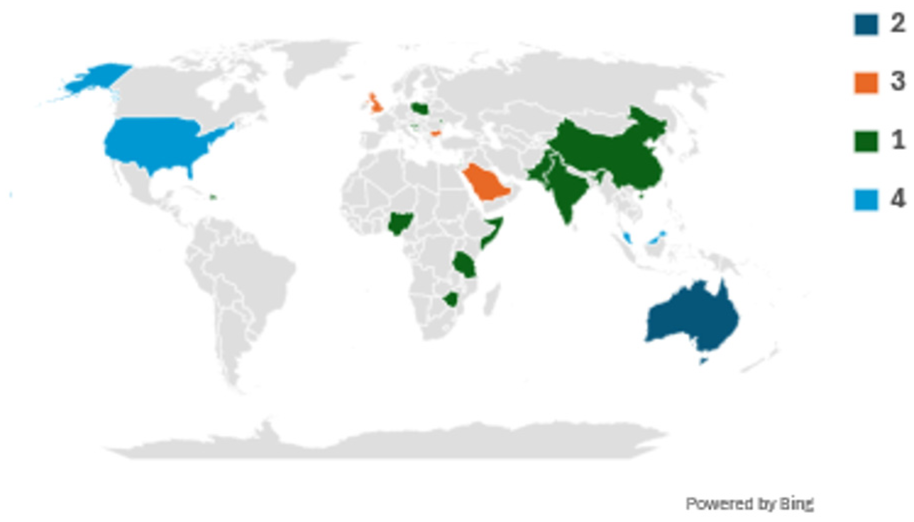
Proportion of published articles distributed by country.

Total number by year.
Finally, most of the studies carried out are quantitative in data characterising high levels of empirical support; though relative lack of qualitative or mixed methodology suggests that further finer studies are needed on how behavioural and institutional factors contribute to cybersecurity outcomes.
RQ3: What are the recommendations in the articles?
In the reviewed studies, the researchers kept emphasising the fact that the improvement of cybersecurity stands in need of a more thorough and active reaction by combining human awareness, technical control, and institutional governance in higher education in general. One of the recommendations is to enhance the level of cybersecurity awareness and training provided to students, faculty and the administrative staff. The addresses of such initiatives should be concerned with phishing awareness itself, good passwords, and risky online behaviour. Integrating cybersecurity training into orientation, staff education and problem-solving issue learning activities focus on embracing which ensures a culture of collective digital safety.
Technically speaking, organisation is recommended to engage multi-factor authentication, frequent point releases and system patches, network security monitoring, access control banking. Having good backup schemes and disaster recovery mechanisms would ensure that service operates in the event of cyber incidents as well is essential in response to them should they arise. The article also highlights the significance of collaboration and policymaking. Universities should create a rapport with the government officials, cybersecurity experts, and industry stakeholders, with whom they can share their threat intelligence, to make their campuses more resilient. Implementing internationally recognised standards and framework relevant to cybersecurity including ISO/IEC 27001 or the NIST guidelines can be used to assist HEIs to achieve consistency and responsibility in their security governance practices. All these recommendations indicate that cybersecurity in higher education is not a technical failure but a complicated problem with human behaviour and institutional culture and strategy. This implies that a formidable cybersecurity atmosphere requires combined effort of all parties in the academic ecosystem.
Summary of Key Gaps in Threats and Vulnerabilities Identified
Despite new studies that highlight the necessity of enhancing and broadening cybersecurity in relation to higher education, black spots can be viewed as issue in the research field now. First, most works tend to be very cursory with the details-there is much talking about the problem of cybersecurity at universities, but few writers narrow the focus on much more specific threats, such as the theft of intellectual property, ransomware, or an epidemic of phishing. Regarding solution that can be taken in the context of HEIs? Almost zero presence (Aliyu et al., 2020; Rahim et al., 2020).
The other issue that is always constant is the lack of comprehensive and specific cybersecurity training and awareness. Literature always refers to students, faculty, and staff as being unprepared and, in most cases, this is due to bad password practices and low knowledge of social engineering (Alzahrani et al., 2022). The possible solutions such as regular training and awareness are also reported and rarely investigated in relation to efficacy or effectiveness (Aliyu et al., 2020; Arina & Anatolie, 2021). Institutions of higher education on the software side usually are on open-source or free tools, typically due to budget concerns (Kissoon, 2020). However, no research has been conducted to investigate the security risks associated with such platforms, especially compliance and privacy (Okokpujie et al., 2021; Rafiq & Ameen, 2021). Furthermore, the field is also short of empirical studies. Most of them are theoretical; hardly any of them present grounded case studies or empirical evidence (Pavlova, 2020; Cruz, 2022). Equally, some of the reviewed literature reaches cybersecurity governance and policy but does not delve into policy creation, implementation, and/or evaluation in practice (Aliyu et al., 2020; Bongiovanni et al., 2020).
Finally, physical integration and cybersecurity are large oversight. They are frequently considered as distinct in research and not considered as interplays, such as the role of physical access control in the protection of digital assets or the degree to which physical access control plays a crucial role (Ngulube, 2019; Zwilling et al., 2019). To sum up, higher education institutions still have critical gaps in cybersecurity research: they are not paying sufficient attention to the particular and emerging challenges, the successful or untested programmes, are not doing the research to prove the programmes, relying on open source software, not doing sufficient evidence-based research, have not critically reviewed policy implementation, and barely consider physical security role in cyber defence. To be sure, if these issues are left unaddressed, HEIs will continue to face significant vulnerabilities in a complex threat landscape.
Implication and Conclusion
Practical and Policy Implications
The results of this review show that cybersecurity in HEIs is not only an issue of technology but also a challenge of both organisational and behavioural nature. Today’s universities operate in a highly digitised environment were data flows continuously across multiple platforms, creating vast opportunities for cyber threats. The signs are obvious: A lot of institutions are unprepared, having outdated systems, having small budgets, and staff training (Kissoon, 2020). HEIs ought to create a to achieve institutional resilience integrated cybersecurity model that integrates technological security measures, human training and control policies. Security technologies (that include multi-factor authentication, encryption, and intrusion detection systems) should be invested in yet well supported with the regular education campaigns that will enable both users and administrators to recognise and counter possible threats.
HEIs need to develop and implement open cybersecurity practices on a policy level based on international recommendations, including the NIST Cybersecurity Framework or ISO/IEC 27001. These frameworks assist institutions to establish standard operations of security, periodically carry out risk evaluations, and properly put down procedures concerning incidence reaction. Having close cooperation with governmental bodies, and technology partners, as well as other universities, is also important in terms of sharing threat related information and techniques. However, ultimately cybersecurity needs to be treated not as a technical matter that has a technical solution, but as collective institutional issue. The academic society, both the administrators and the students, has a role to play in ensuring that the digital environment is safe.
Theoretical Implications and Research Contribution
The research contributes to the body of higher education cybersecurity literature because it generates a methodical synthesis of collected empirical evidence from 2018 to 2025. Synthesising nine overlapping themes into clearly defined categories provides a more consistent framework by which to interpret the cyber threats in the academic environment. This improved structure separates cyber threats (external or internal actions that take advantage of weaknesses) and vulnerabilities (the inherent weaknesses that make an easy time of threat). Aligning these themes with models such as the CIA triad enhances the theoretical rigour of this approach and allows for comparative analysis in later research. The consequences emphasise the importance of cross-disciplinary work on cybersecurity that spans technical, educational, and behavioural domains. Although current research is heavily quantitative, qualitative and mixed methods should be incorporated into future work to include the human and cultural aspects shaping cybersecurity behaviours in HEIs.
Limitations and Future Research Directions
Although this review is informative, it is not without limitations. This analysis is based on studies published between 2018 and 2025, and most come from a small collection of countries (i.e., the United States, Malaysia, Saudi Arabia, and the United Kingdom). Consequently, the global relevance of these findings might be diminished. More studies are needed to include more locations, and more studies should include a wider geographical representation, with special attention to underrepresented areas of the world, like Africa, Latin America, and Eastern Europe. Also, most studied analyses were descriptive rather than theoretically or policy oriented.
Future research should extend beyond the survey about enumerating threats and concentrate on creating predictive frameworks, risk assessment models, or behavioural interventions that can guide cross-institutional applications. The introduction of new types of vulnerabilities because of emerging technology, including artificial intelligence, cloud computing, and the IoT infrastructure, offer credible subjects of academic research. Future research therefore needs to work on the effects of digital transformation, remote learning and hybrid education setting on cybersecurity risks and governance.
Conclusion
In the era of a digital revolution, where digitisation is being the carrel of higher education, securing institutional information systems is not only an advantage worth having but a necessity. This article highlights that human error, technical flaws, and institutional weaknesses in governance are some of the factors that cause cybersecurity threats in HEIs. To enhance cyber resilient universities, the management should adopt a multi-layered actively defensive approach, with references to investment and advantage of the technology and the arrangement of the development, human-focused and adequate policies. This research project can be used as a source of cybersecurity knowledge development, resilience, and flexibility by synthesising and refining applicable theories and literature in the institutions of higher learning. The overall idea is obvious: cybersecurity in institutions of higher education is not a one-time product, but a commitment to constant vigilance, flexibility, and collective responsibility.
Footnotes
Acknowledgements
The authors would like to express their gratitude to the anonymous reviewers and the Editor for their insightful comments on the article, which significantly improved its quality and presentation.
Ethical Considerations
As this study is a systematic literature review, no human participants were involved; all included studies were previously published and are assumed to have adhered to ethical research standards.
An ethics statement (including the committee approval number) for animal and human studies. If this is not applicable,please state this instead
Not applicable.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: Funding by Universiti Kebangsaan Malaysia, Bangi, Malaysia.
Declaration of Conflicting Interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
