Abstract
Cognitive processes, including understanding, thinking, and interpretation, are necessary to influence safe behaviour in cyberspace. However, among Technical and Vocational Education and Training (TVET) youth, educational focus prioritises technical skills development over cognitive and digital skills. Furthermore, systematic and coherent approaches are lacking to provide students with consistent, quality learning experiences that enhance their understanding of cyber ethics. The research model integrates the cognitive appraisal components based on the Protection Motivation Theory (PMT) with three social learning strategies: cyber ethical digital games, lecturer reminders, and motivational impact of achievement certificates, to understand TVET youth ethical decision-making in cyberspace refers to PAPA model (privacy, accuracy, property, and accessibility). The research employed a quantitative approach using a survey method with questionnaire instruments for data collection, with a random sample of 340 respondents selected from six community colleges around Selangor. Partial least squares structural equation modelling (PLS-SEM) analysis through SmartPLS version 4 software was used to analyse hypotheses and validate the developed model. Hypothesis testing revealed that 12 out of 14 hypotheses were significant, with Perceived Severity (PS), Self-Efficacy (SE), and Response Efficacy (RE) suggesting relationships in TVET youth’s cyber ethical behaviour. The three social learning strategies also demonstrated significant relationships with cyber threats’ appraisal and response processes. The developed Cyber Ethical Behavioural (CEB) model enhances the understanding of TVET youth’s cyber ethical behaviour and promotes the coordination of cyber ethics knowledge enhancement in TVET institutional environments, aligning with new technological developments such as Artificial Intelligence (AI).
Plain Language Summary
This research explores how TVET (Technical and Vocational Education and Training) students make ethical decisions in digital spaces. While TVET programs focus heavily on technical skills, they often overlook the cognitive skills needed for safe digital behavior. The study aimed to understand how different learning approaches could help students make better ethical choices in cyberspace. The research model integrates the cognitive appraisal components based on the Protection Motivation Theory (PMT) with three social learning strategies: cyber ethical digital games, lecturer reminders, and motivational impact of achievement certificates, to understand TVET youth ethical decision-making in cyberspace refers to PAPA model (privacy, accuracy, property, and accessibility). They examined how these affected students’ ethical decisions about privacy, accuracy, property, and accessibility in the digital environment. The study surveyed 340 students from six community colleges in Selangor, Malaysia using questionnaires. Through questionnaires, the study collected data from 340 students across six community colleges in Selangor. Statistical analysis revealed strong support for 12 out of 14 research hypotheses. Notably, the three learning strategies demonstrated significant effectiveness in improving students’ understanding and response to cyber threats. The resulting Cyber Ethical Behavior model provides TVET institutions with a structured approach to teaching cyber ethics that remains adaptable to emerging technologies like AI.
Introduction
New technological evolutions such as Artificial Intelligence (AI) and Internet of Things (IoT) applications are introduced to protect cyberspace from cyber threats that cause different harm to individuals, organisations, the economy, social harmony, and national security. However, using technology alone is insufficient to protect against cyber threats. Experts estimate that approximately 80% of cyber attacks result primarily from human behavioural errors (Amoresano & Yankson, 2023). Notably, seemingly innocuous human behaviours, such as posting social media status updates and leaving comments, can inadvertently expose users to cyber stalkers and compromise security. Moreover, sharing unverified current information can lead to misunderstandings and create societal confusion. Therefore, creating a safer cyber ecosystem requires a fundamental understanding of how humans respond to initiatives to improve compliance and behaviour in the face of escalating cybersecurity risks.
In the context of cyber technology development and internet usage, cyber ethical behaviour represents moral principles that limit human conduct from actions that could harm others. According to Xiang and Hasbullah (2023) and Harris (2022), cyber ethics encompasses moral aspects that touch on cyber-human values. Cyber human values serve as the foundation for evaluating actions taken toward oneself and others to rationalise attitudes and behaviours. The characteristics of cyber human values include respect, honesty, responsibility, peace, tolerance, and taking actions that align with basic human values (Xiang & Hasbullah, 2023). Therefore, this study defines cyber ethical behaviour as behavioural decisions based on cyber human values to establish healthy relationships, protect and prevent the misuse of others’ rights, and create well-being and security in cyberspace.
Statistics released by the Malaysian Communications and Multimedia Commission (MCMC) in 2022 revealed that young people, particularly post-secondary students in colleges and universities, represent the largest percentage of cyberspace users at 70.7%, as summarised in Table 1. The report also revealed that youth aged 18 to 24 spend the longest time in cyberspace, averaging 5 to 8 hr, with some users spending up to 18 hr online. Cyberspace has become an essential resource for TVET youth for academic purposes and social communication. However, they can easily become involved in unethical and irresponsible actions, especially with the creators of easily accessible and shareable online content, such as audio, video, and graphics, which can challenge their ability to make rational decisions. Even though these factors alone do not necessarily cause such behaviour, if cyber ethical behaviour is not given the attention it deserves, it may become normalised, reducing graduates’ sensitivity to cyber human values. This could lead to security vulnerabilities for others and organisations in their future employment sectors.
Statistics on the Use of Cyberspace by Students in Educational Institutions (MCMC, 2022).

Estimate has a relative standard error (RSE) between 25% and 50% and should be used with caution. **Estimate has a relative standard error (RSE) greater than 50% and is considered unreliable.
Ethical and responsible behaviour in cyberspace is directly linked to an individual’s cognitive ability to interpret, evaluate, and understand cyber threats. This necessitates continuous education to guide ethical and responsible online behaviour among TVET youth. However, preliminary studies at several TVET institutions reveal that cyber ethical behaviour is not consistently emphasised in their formal curriculum structure. Despite various awareness initiatives, including radio interviews, the National Principles Appreciation programme, campaigns for responsible social media use, and the NETHICS campaign promoting good social media ethics through webinars, there remains a lack of systematic and coherent approaches to provide students with consistent, quality learning experiences in cyber ethics. Consequently, many students remain unaware that their online behaviour, particularly on social media, significantly influences employers’ hiring decisions (BERNAMA, 2024).
This study uses the PAPA model, which includes privacy, accuracy, intellectual property, and accessibility, to understand the cognitive process in cyber ethical behaviour among TVET youth. The survey results discovered that the cyber ethical behaviour of youth, based on the PAPA model, is not comprehensive. Most studies focus on only one or two PAPA issues at a time, and most studies among youth focus on cyberbullying issues (Durak, 2019; J. Ma et al., 2024; Park & Bae, 2025), privacy (Zani et al., 2025) and interactions on social media (Baig & Nasreen, 2024; Dunmade, 2023; Kilicer et al., 2017; K. Mahmud et al., 2024; Saeed, 2019). In addition, studies on cognitive processes in cyber ethical behaviour models are still limited. Most behavioural models of information security protection associate cognitive processes with security policy compliance behaviour (Boyett, 2020; Hina et al., 2019; Quoc & Huu, 2023), the use of security software and hardware (L. Li et al., 2022), and password setting (Farooq et al., 2021; Mwagwabi & Jiow, 2021). Since cognitive processes involve thinking and judgment, information sources through non-formal learning are connected in the study model to determine appropriate learning strategies for cyber ethics education across the current curriculum. In particular, non-formal learning aims to develop students’ potential as a complement or substitute for formal education through the mastery of knowledge and skills (Syaadah et al., 2023). Some previous studies have referred to non-formal learning through Social Learning Theory (SLT) by Bandura (1986), who argued that learning occurs mainly through observing and imitating models in social settings. However, there is still a gap in the study of social learning strategies on students’ cognitive skills in cyber threat appraisal since most of the identified social learning strategies are more applied in the context of employees (Hina et al., 2019; Liang et al., 2023; Sepp, 2023) and public users (Justitia et al., 2022; Yuen et al., 2020).
In this study, we explored the relationship between social learning strategies and students’ threat and coping appraisal processes, as outlined in PMT. Therefore, this study aims to answer two research questions: “What is the relationship between the cognitive processes of TVET youth in cyber ethical behaviour?” and “How are social learning strategies related to students’ cognitive processes in promoting ethical behaviour in cyberspace?” We then developed a model of cyber ethical behaviour and gathered the perceptions of TVET youth at Malaysian Community Colleges regarding the relationship between cognitive processes and social learning strategies in cyber ethical behaviour. Accordingly, we constructed a theoretical model using Protection Motivation Theory (PMT) to examine and explain the cognitive processes of TVET youth when they engage in cyber ethical behaviour. In this context, cognitive processes refer to how TVET youth evaluate potential cyber ethical violations, take steps to avoid involvement, and employ coping strategies to deal with these threats.
The paper is organised as follows: We first present the study highlights, research model, and hypotheses, followed by the methodology and empirical results. We then discuss the findings, contributions, and implications, concluding with recommendations for future research.
Study Highlights
The PAPA model was developed by Manson in 1989, and although it has been three decades, the PAPA model is still used in recent studies (Aderibigbe et al., 2021; Başaran & Rukundo, 2018; Ndumbaro, 2018). Table 2 summarises the definition of cyber ethical issues based on the PAPA model by Mason (1986), cyber human values and the significance of behaviour in cyberspace for the protection of self and other people.
Summary of Cyber Ethical Issues Based on the PAPA Model, Cyber Human Values and the Importance of Behaviour in Cyberspace.

Table 2 identifies four core ethical issues: privacy, accuracy, property, and accessibility. They are viewed through the lens of cyber human values, guided by value-based ethical reasoning. Recent literature argues that alignment between values such as respect, honesty, responsibility, and patience shapes safe and ethical behaviour in cyberspace. For instance, the issues of privacy and intellectual property are both anchored in the value of respect, which is conceptualised as adherence to legal compliance (Althibyani & Al-Zahrani, 2023) and highlights the ethical obligation to prevent harm to others (Prathomwong & Singsuriya, 2022). Similarly, the concept of honesty emerges across multiple ethical domains (privacy, accuracy, and intellectual property), with a typical application: to prevent the misuse of others’ data and ownership through acts such as information falsification (Yaokumah, 2020), plagiarism, digital content manipulation, and violations of copyright (Dumas-Mallet & Gonon, 2022) and online identity (Kołodziej et al., 2022).
The overlap of values across ethical domains suggests that honesty and the other three human values identified in this study, responsibility, respect, and honesty, are foundational in guiding ethical cyber behaviour. However, based on the Protection Motivation Theory (PMT) framework, a key question arises: to what extent do cognitive processes such as threat appraisal and coping appraisal among youth support the consistent internalisation and application of these values when engaging in digital interactions?
Protection Motivation Theory (PMT)
PMT offers a valuable lens for understanding how individuals assess cyber risks and determine appropriate behavioural responses. This theory refers to the cognitive abilities of individuals and the processes that mediate certain behaviours in response to danger (Shevchenko et al., 2023). The cognitive abilities involve the belief that the recommended delaying response can effectively prevent the occurrence of an aversive event (Rogers, 1975). For instance, when individuals perceive a cyber threat, they engage in two key cognitive processes such as threat appraisal and coping appraisal, which guide their motivation to adopt protective behaviour (Sulaiman et al., 2022).
Some recent studies have demonstrated the potential of PMT in predicting human behaviour for security protection, such as information security behaviour (Sharma & Aparicio, 2022; Torten et al., 2018) and cybersecurity (Sulaiman et al., 2022). Based on PMT, threat appraisal refers to the consideration of how negative the consequences of the threat (Perceived Severity, PS) and the possibility that the threat will occur in a way that will affect them directly, which is through the perception of weakness (Perceived Vulnerability, PV) (Rogers, 1975). Meanwhile, in coping appraisal, a person assesses whether engaging in the recommended action will eliminate the threat (Response Efficacy, RE), their level of confidence in acting (Self-Efficacy, SE), and the cost involved (response costs) (Rogers, 1975). Thus, threat and coping appraisal can lead to ethical behaviour through mechanisms such as denial or avoidance.
In this study’s context, not all components of the cognitive process were included. Based on the frequency of use and the significant relationship between the components in previous studies, four PMT components were selected: PS, PV, SE, and RE. The reward and response cost components have been underutilised in past studies. Notably, several cybersecurity and information security studies have been identified for not integrating these components into their security compliance behaviour model (Song et al., 2024; Sulaiman et al., 2022). Moreover, the reward component has a misleading interpretation since the consideration to perform inappropriate behaviour relies on the reward received from the action taken. Regarding response cost components, financial, time, and effort cost requirements in cyber ethical behaviour involving moral judgments are complex to interpret. Compared to cybersecurity and information security, consideration of response costs in terms of the need for financial costs, time, and effort in using anti-virus software or firewall hardware can be observed.
Social Learning Theory (SLT)
Bandura’s (1977) Social Learning Theory (SLT) provides a foundational framework for understanding how external cues influence individual attitudes and behaviours through observational learning. Rather than relying solely on direct experience, SLT posits that individuals acquire new behaviours by observing others in informal social contexts, cognitively processing those stimuli through mechanisms such as attention, retention, reproduction, and motivation. This reciprocal interaction between cognitive, behavioural, and environmental factors makes SLT particularly relevant for exploring how ethical behaviour is shaped in non-formal learning settings.
While SLT has been widely applied in fields such as entrepreneurship (Wasim et al., 2024), STEM education (Chiu et al., 2023), and health communication (Liu et al., 2022), its use in understanding digital moral behaviour—particularly in the context of cyber ethics among TVET youth—remains limited. This study addresses that gap by applying SLT to investigate how informal learning strategies can enhance cognitive processing toward ethical decision-making in cyberspace. The integration of three social learning strategies, such as cyber ethical digital games, lecturer reminders, and the motivational impact of achievement certificates, is grounded in the four sources of self-efficacy expectations proposed by Bandura: performance accomplishments, vicarious experiences, verbal persuasion, and emotional arousal.
Unlike traditional compliance settings where behaviour change is often driven by technical policies or rule enforcement, this study emphasises internalising ethical values through peer modelling, reflective engagement, and positive reinforcement. For instance, cyber ethical digital games provide vicarious and experiential learning through role simulations; lecturer reminders represent structured verbal persuasion that supports moral reasoning; and achievement certificates tap into performance accomplishments to reinforce positive behaviour. Moreover, this study highlights the emotional and cognitive interplay in social learning, particularly how vicarious experiences influence emotional control and ethical self-regulation (Müllner-Huber et al., 2022). Thus, the model developed in this study applies SLT in a new context and extends its application by integrating cognitive processes into the cyber environment to guide the development of safe and ethical online behaviour.
Research Model and Hypotheses Development
The research model is presented in Figure 1. Cyber ethical behaviour is directly influenced by threat appraisal, which consists of PS and PV, while coping appraisal consists of SE and RE. Three social learning strategies are used in this study: cyber ethical digital games, which are connected to the cognitive processes of PS, PV, SE, and RE. Meanwhile, the lecturer’s reminder affects the same four constituents, while the motivational impact of the achievement certificate affects two components of the cognitive process: SE and RE.

Research model.
The research model developed in Figure 1 comprises 14 hypotheses, which will be elaborated in the following section.
Hypotheses Development
PS can be defined as an individual’s assessment of the consequences or threats associated with an event (Rogers, 1975). The higher the perceived threat, the more likely online users will take precautions. In the context of this study, assessing severity in terms of threats and harm to themselves or others influences students to practice ethical behaviour in cyberspace. This is attributed to the severity of the detected threat, which will increase the user’s desire to take action to reduce the threat through behaviour control. Based on these assumptions, the following hypothesis is developed:
PV reflects an individual’s apprehension about cyberattacks and their perceived inability to implement adequate preventive measures (Rogers, 1975). It represents the degree to which a person believes they are susceptible to a specific threat (Muhammad et al., 2022). PV has been shown to influence employee information security behaviour significantly (Humaidi & Alghazo, 2022; X. Ma, 2022). However, research findings concerning PV among students in the context of information security behaviour are less consistent. For example, Zulkiplee et al. (2025) reported a positive relationship between PV and secure behaviour, whereas Mwagwabi and Jiow (2021) and Bottyán (2024) found a negative association. Despite these mixed results, the direction of the relationship remains theoretically consistent with the Protection Motivation Theory (PMT) assumptions. Based on this theoretical foundation, the hypothesis of this study is:
Self-efficacy (SE), defined as an individual’s belief in their ability to effectively manage cyber threats through appropriate preventive measures (Rogers, 1975), has been widely recognised as a critical determinant of secure behaviour. Research has demonstrated a consistent positive relationship between SE and information security behaviour across professional and educational contexts. Among employees, studies by L. Li et al. (2022), X. Ma (2022), and Sulaiman et al. (2022) highlight how high SE contributes to greater adherence to cybersecurity protocols. Similarly, investigations involving students (Alam et al., 2025; Mwagwabi & Jiow, 2021; Thompson & Oldfield, 2024) reinforce the role of SE in fostering secure and responsible online conduct. These consistent findings suggest that individuals with higher SE are more resilient and proactive in mitigating cyber risks. Indicated a positive relationship of SE in safety behaviour. As previous researchers emphasised, strong self-efficacy enhances individuals’ coping mechanisms when facing challenges and facilitates positive behavioural changes related to personal protection (Y. Chen et al., 2023; Norman & Kpeglo, 2023). These insights underscore the potential of SE to influence ethical behaviour in cyberspace, particularly among TVET youth. Based on this synthesis, the following hypothesis is proposed:
RE is the degree to which individuals believe that the recommended response will effectively reduce the threat to them (Rogers, 1975). However, previous studies examining the influence of RE on users’ password compliance behaviour have yielded diverse results. For instance, Simon et al. (2025) reported a significant positive effect, whereas Dodge et al. (2023) found no such relationship. In contrast, studies conducted in workplace settings consistently demonstrate that RE significantly influences information security compliance behaviour among employees (L. Li et al., 2022; Menard et al., 2017; Mwagwabi & Jiow, 2021). Drawing upon the assumptions of Protection Motivation Theory (PMT) and these varied outcomes, it is posited that students’ beliefs about the effectiveness of recommended responses—particularly in avoiding the negative consequences of unethical cyber behaviour—may shape their ethical actions in cyberspace. Accordingly, the following hypotheses are proposed to examine the relationship between response effectiveness and cyber ethical behaviour:
Digital games (DGs) are gaining increasing traction among educators in both skills training and Higher Education Institutions (HEIs) due to their ability to simulate real-world scenarios in engaging, interactive visual formats. This approach captures students’ attention and facilitates deeper understanding through experiential learning. In cybersecurity, Alqahtani et al. (2020) demonstrated that DGs can effectively raise awareness and influence user behaviour to mitigate cyber threats. Beyond cybersecurity, studies in various domains have highlighted the pedagogical potential of DGs. For instance, Fatma Sukmawati et al. (2025) and Gruber and Faßbender (2025) found that DGs stimulate curiosity and engagement in STEM education. Similarly, research in entrepreneurship (Casau et al., 2023) and fire safety training (Kwok et al., 2022; Metallinou, 2022) shows that DGs provide immersive experiences that enhance learning outcomes. These findings suggest that DGs focused on cyber ethics can serve as powerful tools for social learning, offering realistic simulations of ethical dilemmas and behavioural threats in cyberspace. Such experiences can evoke emotional responses, shaping students’ ethical decision-making in real-life digital contexts. Supporting this view, psychological research by Hauke and Pokoyski (as cited in Scholl, 2018) indicates that emotional involvement enhances conceptual understanding. In light of these insights, this study proposes a hypothesis linking cyber ethics DGs’ use to activate cognitive processes underlying ethical behaviour in cyberspace.
Persuasive messages, such as warnings about the dangers of weak cybersecurity protection, often make headlines in the cybersecurity field. This message serves as a reminder that something should be done; however, very few of these messages tell what to do. In the context of behaviour in cyberspace, a more specific and clearer reminder from the closest people is crucial. Accordingly, LR is a source of verbal persuasion through persuasive messages that can guide students’ cognitive processes in cyberspace, which requires high-level thinking. Persuasive messages, also known as persuasive communication, significantly impact an individual’s confidence and ability to perform protective behaviours to defend themselves from threats Mourali et al., 2023). When faced with the temptation to engage in unethical cyber behaviour, lecturer reminders can indirectly shape students’ responses by promoting caution and ethical decision-making. Based on the above, four hypotheses are developed to link LR with threat and coping appraisal in cyber ethical behaviour:
Effectively providing tangible rewards increases motivation and performance, especially for tasks that may not be immediately attractive. According to X. Li et al. (2022), student motivation is vital at the higher education level since it is the basis for their achievement in the professional life they pursue. Ronald (1985) asserted that a person’s motivation to perform an act in the future is if he gets a reward for that act (positive reinforcement). In this study, certificates of achievement for students who demonstrate ethical behaviour in the cyber world while at educational institutions, and awareness of cyber security is a significant reward. This certificate confirms the student’s commitment to ethical online behaviour and helps develop performance and responsibility that impact their professional career. Studies related to student behaviour suggest that giving certificates motivates student’s performance (Ostermaier, 2018), engagement (Dogan, 2015; Nayir, 2017), and learning behaviour (Phungphai & Boonmoh, 2021). Therefore, two hypotheses are developed to observe the student perception of the motivation impact of the achievement certificate on their SE and RE towards cyber ethical behaviour:
Research Methodology
This study employed a cross-sectional design, in which data were collected at a single point in time using a structured questionnaire administered to TVET students. This approach was chosen because the aim was to examine the relationships between cognitive processes, social learning strategies, and cyber ethical behaviour, rather than to observe changes over time. The cross-sectional design also allowed for efficient data collection from a large sample within the limited timeframe and resources of the study (Thomas, 2020). Questionnaires require students to think independently to answer a question and are easy to process and synthesise. The detailed questionnaire items for each construct are provided in Appendix A.
Participants
This study involved students from Community Colleges in the Selangor zone who were enrolled in certificate-level programs. Selangor was selected as the accessible population due to its high student density, strategic location near the national administrative centre, and established role as a pilot zone for policy implementation by the Department of Community College Education (JPPKK). Seven of the 11 Community Colleges in Selangor were categorised as urban institutions and four as rural. Based on Krejcie and Morgan’s (1970) sample size table, the minimum required sample was 335 students from the total accessible population of 2,574.
To ensure a balanced and representative sample, stratified random sampling was applied. Samples were drawn from six colleges—three urban and three rural—selected based on stratified criteria, including geographic classification and enrolment size (with only colleges having more than 100 registered students deemed eligible). Within each selected college, participants were recruited proportionally according to student enrolment, ensuring equal selection probability. A target of 168 students was set per zone category. In total, 377 responses were collected, but after data cleaning to exclude incomplete or invalid entries, 340 valid responses were retained for final analysis. This rigorous sampling strategy enabled the collection of a diverse and representative dataset reflecting urban and rural student populations.
Questionnaire Development
The questionnaire is divided into two main parts. Part I of the question is a closed Likert scale type. The Likert scale is used since it has an even format, which makes it easier for the researcher to analyse the data obtained. Meanwhile, Part II uses nominal and ordinal data, which include demographic factors such as gender, ethnicity, religion, age, specialisation, semester, college community, internet usage time, and user feedback regarding awareness of the importance of cyber ethics for cybersecurity protection. The survey instrument was developed by adopting questions from previous research and adapting them to the context of the study, while also including new questions for constructs that previously lacked question items. The questionnaire was developed in Bahasa Malaysia. The questionnaire requested respondents to answer each item using a 5-point Likert scale ranging from (1) strongly disagree to (5) strongly agree. A 5-point Likert scale makes it easier for respondents to understand and make more accurate answer choices.
To ensure clarity and gather valuable feedback, this study employs three types of validity: face validity, content validity, and construct validity, to eliminate any ambiguous questions from the survey. Face validity ensures the items’ clarity, question appropriateness, adequate response time, and, most importantly, that they measure what they are intended to measure. To assess face validity, three experts evaluate the questionnaire using a dichotomous scale: “Suitable” and “Not Suitable” refer to Patel and Desai (2020). As a result of the face validity assessment, lengthy questions were shortened, ambiguous terms were clarified, and synonymous English words were used for better understanding. Meanwhile, content validity was further assessed to ensure that the measured domain fully represents the intended content. The Content Validity Index (CVI) was used to determine whether each question item met a predetermined validity threshold (Bohari et al., 2022). Three experts evaluated the questions, rating each item using the scale proposed by Davis (1992): 1 = Not suitable, 2 = Needs modification, 3 = Suitable but needs refinement, and 4 = Suitable. Following Koohi Rostami and Jahnifar (2022), ratings were recorded as 1 (for relevance scales 2 or 4) or 0 (for relevance scales 1 or 2) before calculating the CVI. The calculation results indicated that all question items achieved a value of 1, as recommended by Polit and Beck (2006) for studies involving three experts. However, several question items were revised based on expert feedback and suggestions.
Construct validity aims to observe how well an instrument accurately measures what it is supposed to measure before the test is deemed valid. A pilot study was conducted at Selayang Community College with the Selangor State Peer Counselling Psychology Programme. A total of 42 forms were completed for analysis. To determine the level of reliability of the developed questionnaire, the data obtained from the pilot study was analysed using Statistical Package for Social Sciences (SPSS) software version 27. The internal consistency reliability, as measured by Cronbach’s Alpha coefficient, is summarised in Table 3.
Reliability Analysis of Research Instruments.
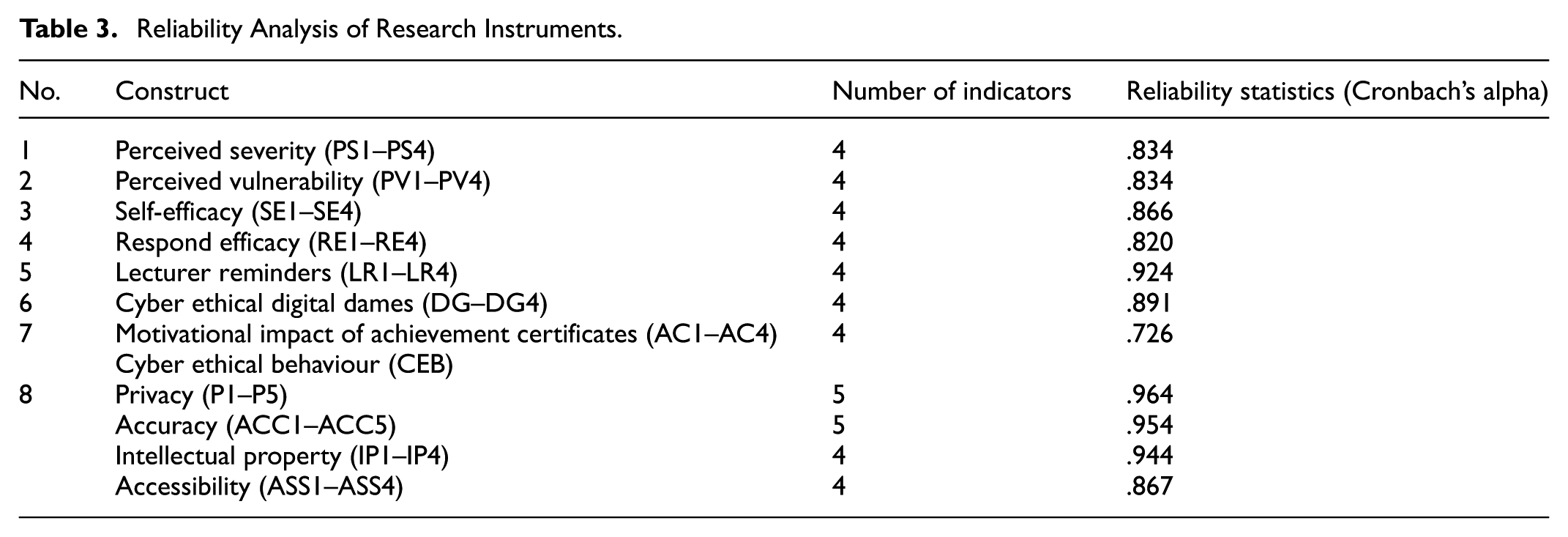
The reliability analysis results, summarised in Table 3, show that the Cronbach’s alpha values for all constructs exceeded 0.7, indicating acceptable internal consistency. In addition to statistical analysis, three students were asked to provide feedback on item clarity. Based on their input and the reliability results, several items were refined. The final version of the instrument consisted of 46 items. Construct validity, including convergent and discriminant validity, was further evaluated during the main study using Confirmatory Factor Analysis (CFA) with a larger sample (
Data Collection
The administration for the collection began with the researcher submitting a letter of application for permission to the Department of Polytechnic Education and the community college to conduct the research at the University. After receiving permission, the application letter to conduct the study was sent to the selected community colleges in Selangor. An appointment was made with the Head of the Research, Innovation, and Commercial Unit at the community college to set a suitable date for the study. The researcher proceeded to the field to survey receiving approval. Before distributing the questionnaire, the researcher facilitated an online cybersecurity digital game activity titled
Data Preparation
The results of the descriptive analysis using Microsoft Excel software reveal that all variables and questionnaire items have less than 10% missing data. The mean imputation technique was applied to address missing data. The analysis also revealed that 46 survey responses were identified and eliminated due to the presence of straight-line responses. A set of questionnaires with a straight-line response pattern that is not removed will trigger an inflated correlation (Hair et al., 2018). In addition, the z-score approach was used to detect extreme values. Of the 377 survey responses analysed, 37 were reported to have extreme values, scored above 3.29, and were excluded from the dataset. As a result, 340 survey responses remained, meeting the required total data target of 101%.
Respondents cannot write their names in the questionnaire in the recovery procedural method to protect their identity. Respondents were also asked to answer honestly, apart from being informed that there are no right or wrong answers. The statistical recovery method involves Harman’s single factor test to determine if there is bias in the questionnaire data by all indicator variables that measure dependent and independent variables, which were analysed based on factor analysis without rotation using IBM SPSS statistical software version 27. The analysis results indicate that the first factor explains 47.068% of the variance, below the 50% threshold for total variance. Therefore, these results suggest that the sampling method used in this study is not affected by standard method variance bias and aligns with Hair et al. (2017) recommendations. To assess the data’s multivariate normality, skewness and kurtosis values were examined using SPSS software. The results confirm that the data distribution is normal, with the standard error of each variable considered. Most of the data fall within the recommended skewness and kurtosis range of ±2.00, as Hair et al. (2014) suggested.
Empirical Analysis and Results
Descriptive Analysis
All participating community colleges are located in Selangor, with 28% from Selayang CC, 24% from Kuala Langat Community College, 19% from Hulu Langat Community College, 19% from Sabak Bernam Community College, 7% from Hulu Selangor Community College and 5% from Kelana Jaya Community College. Twelve certificate programmes are involved, including the following: Information Technology (27%), Computer and Network (7%), Basic Culinary (9%), Hotel Operations (3.2%), Pastry (10%), Food Processing and Quality Control (6%), Business Operations (6%), Refrigeration and Air Conditioning (10%), Interior Design (5%), Light Vehicle Service (5%), and Electrical Technology (12%). Students are primarily from the first semester (62%), followed by the third semester (20%) and the second semester (18%). Approximately 58% of the respondents are female, and 42% are male. Most respondents are 18 years old (51%), followed by 19 years old (37%). The remaining respondents are 20 years (8%), 21 years (2%), 22 years (1%), and 23 years (1%). Respondents’ feedback on internet usage indicates that 20% use the internet for 1 to 3 hr, 40% for 4 to 5 hr, and 40% for more than 6 hr a day. Additionally, 23% of respondents report using a computer for more than 6 hr daily. Regarding awareness of the significance of cyber ethics for cybersecurity protection, 35% are unaware, 40% are somewhat aware, and 25% are very aware.
Assessment of the Theoretical Model
This study employed Partial Least Squares Structural Equation Modelling (PLS-SEM) using SmartPLS 4.0 due to its suitability for exploratory research and prediction-oriented analysis. The conceptual model, developed from prior literature, examined the predictive relationships between cognitive and behavioural constructs such as perceived severity, perceived vulnerability, self-efficacy, response efficacy, and informal learning strategies. PLS-SEM was selected for its ability to handle complex models, including a second-order construct (cyber ethical behaviour) with four first-order dimensions, and its robustness to non-normal data distributions.
The analysis involved two main stages: evaluating the measurement model to assess the constructs’ reliability and validity, then testing the structural model to examine the hypothesised relationships. This approach allowed for validation of the research instrument and in-depth assessment of the proposed theoretical model.
Measurement Model
A Confirmatory Factor Analysis (CFA) was conducted to assess construct validity using data from 340 respondents, which meets the recommended sample size for structural equation modelling, particularly for complex models (Hair et al., 2019). This analysis was carried out to verify the unidimensionality and adequacy of each construct in the measurement model. During CFA, indicators with factor loadings below 0.4 or above 0.95 were removed, as recommended by Hair et al. (2019). For example, item AC4, which had a factor loading of 0.588, was excluded from further analysis due to insufficient contribution to its construct. Indicators with loadings below 0.6 were also excluded due to weak inter-item correlation.
The final CFA results demonstrated acceptable measurement properties. All retained items had factor loadings ranging from 0.685 to 0.948, indicating strong indicator reliability. The internal consistency reliability was confirmed with Cronbach’s alpha values ranging from 0.920 to 0.965, and Composite Reliability (CR) values above 0.7 (ranging from 0.914 to 0.947). Furthermore, Average Variance Extracted (AVE) for all constructs exceeded the minimum threshold of 0.5, confirming convergent validity. These results confirm that the constructs used in this study demonstrate both validity and reliability, as summarised in Table 4.
Latent Variable, Loadings (Confirmatory Factor Analysis, CFA), Cronbach’s Alpha, Composite Reliability, and AVE.

The Fornell-Larcker criterion was applied to assess discriminant validity. This method compares the square root of the Average Variance Extracted (AVE) for each construct with the correlations among constructs. As shown in Table 5, the square roots of AVE (diagonal elements) are all higher than the corresponding inter-construct correlations, confirming that each construct is distinct from the others in the model. These results prove adequate discriminant validity (Fornell & Larcker, 1981).
Fornell-Larcker Criterion.

Based on the Heterotrait-Monotrait (HTMT) ratio correlation approach from the multitrait-multimethod matrix, the discriminant validity of a construct is considered valid if the HTMT value is less than 0.85 (Henseler et al., 2015) or less than 0.90 (Teo et al., 2008). A discriminant validity value that exceeds 0.85 indicates that there is a serious problem with discriminant validity. Table 6 indicates that the HTMT value is below the stricter criterion of ≤0.85, indicating that the respondents distinguish the eight constructs as separate, demonstrating strong discriminant validity.
Heterotrait-Monotrait (HTMT) Ratio.

Assessment of the Structural Model
The variance inflation factor (VIF) values were assessed to ensure the absence of multicollinearity. As shown in Table 7, all VIF values ranged from 1.244 to 3.238, well below the commonly accepted threshold of 7. This indicates that multicollinearity is not a concern in this study (Hair et al., 2019).
VIF Values of Predictor Constructs.

This study employed a one-tailed t-test because all hypothesised relationships between constructs were expected to be positive, based on supporting theoretical foundations. This test was chosen because the study’s objective was not to compare two groups in general but rather to determine whether a construct has a significant effect in a specific direction on another construct being tested.
The study employed 5,000 samples for the bootstrap procedure, as Hair et al. (2017) recommended, to ensure consistent values. Notably, a structural relationship between exogenous and endogenous constructs is accepted if the
Next, the relationship between the exogenous DG and the four endogenous constructs: PS, PV, SE, and RE was examined. The obtained values are as follows: DG → PS (β = 0.534,
Then, the relationship between the exogenous construct LR and the four endogenous constructs: PS, PV, SE, and RE was examined. The obtained values are as follows: LR → PS (β = 0.320,
Finally, the relationship between the exogenous construct AC and the two endogenous constructs, SE and RE, was examined. The obtained values are as follows: LR → SE (β = 0.328,
Hypothesis Test Results.

β is significant if
The squared multiple correlation (
Discussion
This section discusses the findings related to the relationship between threat and coping appraisal components and cyber ethical behaviour (CEB), as well as the influence of social learning strategies on these cognitive processes. It also includes a critical reflection on non-significant findings, outlines the study’s theoretical and practical contributions, and offers implications and recommendations for future research.
The Relationship Between Threat Appraisal Components (Perceived severity and Perceived vulnerability) and CEB
In this study, threat appraisal includes perceived severity and perceived vulnerability. Perceived severity captures how seriously individuals view the consequences of violating cyber ethics, while perceived vulnerability reflects their belief in how likely they are to experience cyber threats personally. The test of the relationship between the perceived severity construct and TVET youth CEB (Hypothesis H1) exhibited a significant correlation. However, the relationship between the perceived vulnerability construct and TVET youth CEB (Hypothesis H2) revealed no significant effect. In contrast, the relationship between perceived vulnerability (PV) and cyber ethical behaviour (CEB) was found to be statistically non-significant (H2). This finding aligns with previous studies involving youth, public users, and employees, which suggest that perceived exposure to cyber threats alone does not strongly predict ethical conduct (Boerman et al., 2021; Ekanem, 2023; Jamil, 2022; Mtambeka et al., 2023; Naufal & Hadee, 2022; Sulaiman et al., 2022). While TVET youth may recognise cyber risks, such awareness is not necessarily translated into ethical behaviour.
The Relationship Between Coping Appraisal Components (Self-efficacy and Response efficacy) and CEB
This study explores the relationship between the components of coping appraisal and self-efficacy, which refers to the ability to effectively respond to cyber threats, and response efficiency, which involves the belief that taking action against a threat can prevent cyber ethical violations. The test of the self-efficacy construct and TVET youth CEB (Hypothesis H3) tested a significant relationship. Similarly, the test of the relationship between the response efficiency construct and TVET youth CEB (Hypothesis H4) also revealed an important relationship. This finding is consistent with previous research, which identifies self-efficacy and response efficacy as the most consistent predictors of youth security protection behaviour, particularly in areas such as privacy management (Meng & Feng, 2022; Thongmak, 2022), password hygiene (Jiow & Tay, 2025), protection against phishing attacks (Lee et al., 2023), and the adoption of IoT-based home security devices (A. Mahmud et al., 2023). This suggests that TVET youth possess a high level of self-efficacy in making appropriate behavioural decisions and tend to act ethically in the cyber environment. Accordingly, TVET youth are also able to ensure that the actions taken are based on strong ethical principles to prevent exposing themselves and others to cybersecurity threats. Therefore, it is crucial to provide training that can strengthen these two competencies among TVET students, enabling them to oversee increasingly complex cyber issues more ethically and effectively in their future workplace.
The Relationship of Social Learning Strategies and Cognitive Process in CEB
This study links three learning strategies: cyber ethical digital games, lecturer reminders, and motivational impact of achievement certificates with cognitive process components, threat appraisal (perceived severity and perceived vulnerability) and coping appraisal (self-efficacy and response efficacy). The following section will discuss the findings of this relationship.
The Relationship Between Cyber Ethical Digital Games and the Cognitive Process
Cyber ethical digital games are defined as a source of experience involving visual observation and interactive elements within social learning. Testing was conducted to observe the students’ perception of the relationship between cyber ethical digital games with perceived severity, perceived vulnerability, self-efficacy, and response efficacy, a hypothesis as H5, H6, H7, and H8. The results revealed a significant relationship between cyber ethical digital games and all the cognitive process components. This finding explains that cyber ethical digital games can stimulate students’ cognitive abilities towards threat and coping appraisal in influencing the TVET youth CEB. This result is in line with previous studies, which discovered that digital games has an impact on students’ cognitive processes on water saving (Chang & Yang, 2023), cyber well-being literacy (Wang et al., 2023), STEM learning (Ishak et al., 2022), mathematical learning (Annamalai et al., 2022), and entrepreneurial thinking (Gatti, 2022; Junior & Kim, 2025). These findings support previous studies that indicate digital games are a source of experiential learning (Metallinou, 2022) and promote student engagement in addressing cybersecurity threats (Tay et al., 2024; Winger et al., 2024).
The Relationship Between the Lecturer’s Reminder and the Cognitive Process
The lecturer’s reminder is a form of social learning through persuasive messages or persuasion, which plays an essential role in influencing cognitive processes, confidence, and the ability of individuals to perform ethical behaviour in cyberspace. This study has linked the lecturer’s reminder with two components of the cognitive process: threat assessment and coping assessment. Testing was conducted to observe the student’s perception of the relationship between the student’s perception construct and perceived severity, perceived vulnerability, self-efficacy, and response efficacy, which are hypotheses H9, H10, H11, and H12. The results of the analysis revealed a significant relationship between the lecturer’s reminder and all the components of the connected cognitive process. These results explain that lecturers play an essential role in influencing students’ behavioural decisions in cyberspace by influencing students’ assessment and response to cyber threats. This finding is consistent with studies that highlight the influence of verbal persuasion on self-efficacy among young people, particularly in promoting protective behaviours related to environmental (Han et al., 2025; Syabania et al., 2023) and health (Hwang et al., 2023; Kollerup et al., 2025; Riniasih et al., 2022; Taheri et al., 2025) issues. Overall, this elucidates that social learning through communication or continuous memory from lecturers with emphasis on lectures, guidance, or discussion of responsibility aspects in cyberspace is a fundamental, easy, and available social learning strategy. Therefore, every lecturer needs to improve their knowledge about cyber ethics so that the emphasis on responsible behaviour in cyberspace can be implemented continuously. Not only lecturers in the field of specialisation in information technology and computer networks, but also all lecturers need to take this role.
The Relationship Between the Motivational Impact of Achievement Certificates and the Cognitive Process
Motivational impact of achievement certificates is a source of information to increase the individual’s confidence and ability to maintain correct behaviour. This study has linked the motivational impact of achievement certificates with the cognitive process component of coping appraisal. The test was conducted to observe students’ perception of the relationship between the motivational impact of achievement certificates, self-efficacy, and response efficiency. The result revealed a significant relationship between the motivational impact of achievement certificates and self-efficacy (H3). This is in line with previous studies that reported intrinsic and extrinsic motivation has a substantial effect on the self-efficacy of medical students in their academic achievement (Wu et al., 2020), students actively participating in physical exercise (N. Li et al., 2023), and student’s achievement in English language proficiency (El Haj & Benhima, 2024). The result shows the role of achievement certificates in reinforcing students’ self-efficacy, a key cognitive factor, thereby encouraging sustained ethical conduct in digital environments beyond their academic setting. However, the results revealed no significant relationship between the motivational impact of achievement certificates and students’ response efficacy (H4) in cyber behaviour. This indicates that the motivational impact of achievement certificates does not guarantee the effectiveness of responses to prevent threats, as negligence and disregard for cyber human values can still occur.
In conclusion, the findings indicate that PMT and the social learning process can be combined to predict the cyber ethical behaviour of TVET youth. The findings of the study demonstrate that students who receive social learning can influence threat appraisal (support for H1, H2, H5, and H6) and coping appraisal by affecting students’ self-efficacy and response efficiency (support for H7, H8, H11, H12, and H13). The research outcome is summarised in the path modelling results shown in Figure 2.

Path modelling results.
Critical Reflection on Non-significant Findings
While most of the hypothesised relationships in this study were supported with significant results, a few were found to be statistically insignificant. These non-significant findings warrant further attention, as they may reveal important theoretical insights and practical limitations that were not immediately apparent. In particular, the absence of significant relationships between perceived vulnerability (PV) and cyber ethical behaviour (CEB), as well as between the motivational impact of achievement certificates (AC) and response efficacy (RE), prompts a deeper analysis. The following sub-sections critically examine these outcomes and explore possible explanations grounded in existing literature, contextual factors, and theoretical frameworks such as Protection Motivation Theory (PMT) and Social Learning Theory (SLT).
Perceived Vulnerability and CEB
The finding that perceived vulnerability (PV) does not influence cyber ethical behaviour (CEB) suggests that perceived susceptibility to threats alone is insufficient to drive ethical cyber behaviour among TVET students, unless it is supported by other elements such as emotional engagement, a sense of responsibility, and belief in one’s ability and the effectiveness of their actions. Although students know cyber risks, they often underestimate these threats, relying solely on technical safeguards like antivirus software and firewalls, while overlooking the broader ethical consequences of their actions on others.
Furthermore, students often perceive cyber threats as stemming solely from technological weaknesses, without recognising that individual responsibility is critical in mitigating risks and fostering a safer, more ethical digital environment. This attitude indicates that awareness of one’s vulnerability is unlikely to translate into behavioural change unless accompanied by a deeper understanding of ethical values and the broader impact of one’s actions on the digital community.
The finding that PV does not significantly influence CEB challenges the original Protection Motivation Theory (PMT) assumptions, which posits a direct link between perceived threat and protective behaviour. However, this study suggests that such a relationship may be conditional and mediated by other psychological constructs. In particular, the efficacy components namely, self-efficacy and response efficacy, which showed significant influence in this study, may act as mediators that strengthen the impact of PV on ethical behaviour. This mediation is likely more effective when cyber human values are consistently emphasised within educational interventions. As Bandura (1977) suggests, efficacy beliefs are essential in converting perceived threats into meaningful behavioural change.
Motivational Impact of Achievement Certificate and Response Efficacy
The study found that while the motivational impact of achievement certificates can enhance self-efficacy, they are insufficient to strengthen individuals’ belief in the effectiveness of their actions (response efficacy) when addressing cyber ethical issues. Confidence in one’s ability to respond appropriately in cyberspace may be undermined or uncertain, particularly as new technologies and emerging threats evolve rapidly. Each advancement in technology is often accompanied by the emergence of new and increasingly complex cyber threats, which can challenge individuals’ preparedness and perceived ability to respond effectively (SentinelOne, 2025). Technological developments bring convenience and efficiency in daily life and open up space for abuse, ethical violations, and more serious data security and privacy risks. Therefore, fostering adaptive ethical competence through sustained, value-based digital education is essential to ensure individuals are not only aware of threats but also confident in addressing them responsibly.
Therefore, although achievement certificates can serve as a motivational boost, they do not fully guarantee that students will avoid behaviour contrary to cyber ethics. Theoretically, these findings suggest that AC is not a direct driver of response efficacy, but it is still relevant as a supporting element to strengthen students’ self-efficacy. Its effectiveness can be enhanced through active learning approaches such as ethical digital games and lecturer reminders relevant to technological advances and the latest cyber challenges.
Contribution
This study has made a significant contribution to the field of cyber security, especially concerning cyber ethical behaviour. Compared to previous studies on developing cybersecurity behaviour models, the observed cognitive mediating process focuses on behaviours related to software, hardware, and compliance with security regulations. In contrast to this study, the cognitive mediating process is linked to behaviours that emphasise moral principles grounded in cyber human values aimed at protecting themself and others from cyber threats. Thus, this study strengthens the cybersecurity behaviour model by developing a CEB model based on cognitive mediating process components by integrating PMT theory and SLT theory.
The study also contributes to empirically validating the PMT and SLT components from the developed CEB model. The study results suggest that the cognitive components of PMT, namely perceived severity, self efficacy, and response efficacy, are related to the cyber ethical behaviour of TVET youth. However, the cognitive mediating component of PMT related to perceived vulnerability, which refers to a person’s belief that they are at risk from cyber threats, does not relate to TVET youth’s cyber ethical behaviour. This indicates that TVET youth are aware of the seriousness of cyber threats but underestimate their potential exposure to these threats due to carelessness and poor judgment resulting from irresponsible behaviour in cyberspace. Furthermore, empirical results also confirm that social learning strategies through cyber ethical digital games, lecturer reminders, and the motivational impact of achievement certificates are related to the development of the cognitive mediating process of youth.
Previous studies on safety protection behaviour among students have primarily focused on cyberbullying and privacy issues. However, other critical issues outlined in the PAPA model, such as content accuracy, intellectual property, and accessibility, also require attention and further study in the context of students today. Therefore, this study highlights cybersecurity behaviour issues encompassing security threats and the impacts of victimisation, exposure to illegal activities, and violations of moral values and responsibilities.
Implication
The findings of this study carry important implications for both educational practice and policymaking, particularly in the context of preparing TVET graduates to navigate ethical challenges in cyberspace:
(a)
Educators should integrate structured modules on cyber threats and ethical behaviour into TVET curricula. The model developed in this study can guide educators in assessing students’ cognitive readiness and tailoring learning materials to enhance resilience against cyber threats. This supports the Malaysia Cyber Security Strategy (2020–2024) by fostering collaborative content development across institutions.
(b)
Policymakers can leverage the model to update institutional policies and national guidelines on 21st-century skills, ensuring TVET graduates are equipped for global digital challenges. This aligns with Phase 3 of the Malaysia Education Blueprint (2015–2025), emphasising adaptability and innovation in institutional governance.
(c)
Educators should embed cyber human values—such as responsibility, respect, and accountability—into soft skills training, enabling TVET graduates to meet ethical standards demanded by IR 4.0 industries. Policymakers can support this through national-level training frameworks.
(d)
Policymakers should develop anticipatory guidelines to manage ethical risks posed by technologies such as AI. This study highlights the urgency for ethical foresight in TVET, ensuring sustainable and responsible digital citizenship in a rapidly evolving landscape.
Limitations and Directions for Future Research
While this study provides valuable insights into the cognitive and ethical behaviour of TVET youth in cyberspace, several limitations should be acknowledged. First, the study relied on self-reported questionnaire data, which may be influenced by social desirability bias or limited self-awareness among respondents. Future studies could incorporate observational or behavioural measures to triangulate findings. Second, the sample was drawn from community colleges within a specific region, which may limit the generalizability of results to all TVET institutions nationwide. Expanding the sampling frame to include a more diverse demographic and institutional background would enhance representativeness. Lastly, the study employed a cross-sectional design, which restricts causal interpretation. Future research may consider longitudinal or experimental designs to explore changes in ethical behaviour over time or in response to targeted interventions.
Conclusion
This study offers a meaningful contribution by proposing a cyber ethics model that integrates cognitive processes and human values to explain ethical digital behaviour among youth. While grounded in the Malaysian TVET context, the model’s foundational elements such as ethical awareness, reasoning, peer influence, and responsible digital behaviour are applicable across cultural and educational settings. The incorporation of social learning strategies and value-driven constructs enables adaptability to various institutional environments, including vocational, secondary, or tertiary education systems globally. This model can be tailored to reflect local values and norms in multicultural or digitally diverse societies while preserving its core emphasis on ethical conduct in cyberspace. As such, the model has the potential to inform digital ethics education internationally, especially in efforts to develop responsible digital citizens in an increasingly interconnected world.
Footnotes
Appendix
Questionnaire Items.

| No. | Construct | Indicator | Question item ( |
|---|---|---|---|
| Cyber ethics behaviour (CEB) |
|
||
| 1 | Privacy (P) | P1 | do not share images that could embarrass my friends. |
| 2 | P2 | do not share videos that could embarrass my friends. | |
| 3 | P3 | avoid discussing other people’s problems on social media. | |
| 4 | P4 | believe that tagging a friend on Facebook or Instagram without their consent is a violation of privacy. | |
| P5 | use other people’s details for personal gain (e.g., misusing their health issues or tragedies to collect donations) |
||
| 6 | Accuracy (ACC) | ACC1 | am careful when giving opinions. |
| 7 | ACC2 | avoid rushing to share information. | |
| 8 | ACC3 | check the authenticity of information before sharing it. | |
| 9 | ACC4 | refrain from making statements without consideration. | |
| 10 | ACC5 | provide honest comments when leaving feedback in the comment section. | |
| 11 | Intellectual property (IP) | IP1 | copy entire articles to use as my assignment |
| 12 | IP2 | always indicate the reference source when using content or material taken from others. | |
| 13 | IP3 | encourage friends to download software illegally (other than from iTunes, shareware, demo, etc.) |
|
| 14 | IP4 | am aware that copying other people’s ideas to sell for profit is wrong. | |
| 15 | Accessibility (ASS) | ASS1 | believe that attempting to access a webpage using someone else’s password is wrong. |
| 16 | ASS2 | will not check a friend’s exam results without their knowledge. | |
| 17 | ASS3 | am aware that revealing other people’s secrets on the internet is wrong (e.g., uploading a friend’s exam results to a social media site). | |
| 18 | ASS4 | keep my passwords secure and prevent misuse by others, including immediate family members. | |
|
|
|||
| 19 | Perceived severity (PS) | PS1 | sharing private information can lead to misuse by others. |
| 20 | PS2 | disseminating information is monitored by the relevant authorities. | |
| 21 | PS3 | distributing other people’s intellectual property is illegal (e.g., eBooks, paid software, graphic design, images, audio, or movies). | |
| 22 | PS4 | hacking can lead to the leakage of information. | |
|
|
|||
| 23 | Perceived vulnerability (PV) | PV1 | take easy in protecting private information |
| 24 | PV2 | I re-share content without examining the source and its accuracy. | |
| 25 | PV3 | I ignore the negative effects of spreading other people’s intellectual property. | |
| 26 | PV4 | I read other people’s emails or WhatsApp messages without permission. | |
|
|
|||
| 27 | Self-efficacy (SE) | SE1 | protect other people’s private or confidential information (e.g., passwords, ID card numbers). |
| 28 | SE2 | only share information that I believe to be valid. | |
| 29 | SE3 | download intellectual property only for personal use, as permitted. | |
| 30 | SE4 | change my password at least three times a year. | |
|
|
|||
| 31 | Response efficacy (RE) | RE1 | my comments on social media do not violate cyber laws. |
| 32 | RE2 | the information I share does not cause confusion. | |
| 33 | RE3 | I do not distribute copyrighted material to others. | |
| 34 | RE4 | I use passwords that are difficult to guess. | |
|
|
|||
| 35 | Cyber ethical digital games (DG) | DG1 | capture my attention. |
| 36 | DG2 | improve my memory. | |
| 37 | DG3 | facilitate my understanding of the importance of cyber ethics. | |
| 38 | DG4 | provide a representation of real life in the form of a game. | |
|
|
|||
| 39 | Lecturer reminders (LR) | LR1 | made me aware of the importance of privacy. |
| 40 | LR2 | prevent me from hacking. | |
| 41 | LR3 | reminded me not to misuse other people’s intellectual property. | |
| 42 | LR4 | prevent me from spreading false information. | |
|
|
|||
| 43 | Motivational impact of achievement certificates (AC) | AC1 | increased my confidence in maintaining good behaviour in cyberspace. |
| 44 | AC2 | motivates me to be more responsible while in cyberspace. | |
| 45 | AC3 | affects my behaviour, even in the future workplace. | |
| 46 | AC4 | give added value to my personal development. |
Ethical Considerations
This study of survey participants received formal approval from the Department of Polytechnic and Community College Education (JPPKK), Ministry of Higher Education Malaysia. Permission was subsequently obtained from the participating institutions prior to data collection. All respondents were informed of the purpose of the study and gave their consent before completing the questionnaire. Participation was voluntary, and all data were treated with strict confidentiality and used solely for academic purposes.
Author Contributions
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research is funded by the GUP-2024-045.
Declaration of Conflicting Interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
The data that support the findings of this study are available from the corresponding author upon reasonable request.
The Disclosure of AI Usage
The authors declare they have used AI services, specifically ChatGPT, to generate or edit parts of our analytical script. They carefully reviewed the script to ensure its correctness.
