Abstract
This study aims to offer a bibliographic review of publications on cybersecurity behaviour from the Scopus database, emphasizing the trends and impact of these publications. As of September 11, 2023, this study compiled 2,540 articles published from 2012 to 2022, based on a search using keywords related to cybersecurity behaviour. Following this work, three tools was used namely Microsoft Excel, VOS viewer software and Herzing’s Publish and Perish software to analyse the gathered articles from Scopus database. This study presents the findings regarding the current trends and impact of publications on cybersecurity behaviour. The bibliometric analysis indicates a gradual increase in the number of publications over time. A total of 1,569 articles have been published, receiving over 1,090.45 citations annually, with an average of 7.64 citations per article and 3.66 authors per paper. It was found that more than half of documents were published as journal articles, and United States and China emerge as the top two contributors to the field of cybersecurity behaviour research. This study focuses only on the Scopus database. For future research, the other database such as Google Scholar, Web of Science, Pub Med and Dimension could be considered for a more meaningful and impactful findings. This is the first study, to the author's knowledge, to offer a review on cybersecurity behaviour.
Keywords
Introduction
In the pace of globalization, digitalization and smart technologies, cybersecurity issues are becoming a day-to-day struggle for businesses and government agenciesCyber vulnerabilities create major risks for companies, including operational disruptions, privacy violations, and financial losses (Cramer et al., 2022; Sheehan et al., 2019). The annual global spend on cybersecurity is approaching $100 billion while global losses to businesses due to cyber incidents are nearing $1 trillion (Wirth, 2017). Inadequate cybersecurity measures are estimated to have cost the global economy USD 945 billion in 2020 (Cramer et al., 2022; Smith et al., 2020). Recent industry reports have emphasized the growing exposure and potential impact of cyber risks (Allianz, 2021; Cramer et al., 2022). In Malaysia, a study by Frost and Sullivan commissioned by Microsoft in its report mentioned that economic loss due to cyber-attacks is estimated to be US$12.2 billion (RM50.9 billion), which is 4% of its Gross Domestic Product (GDP) of US$296 billion (Paramasivam, 2018). According to Home Ministry, around 13,000 cybercrime cases were reported in 2019 involving total losses of RM539 million, and the number increased to approximately 17,000 cases in 2020. While in 2021, the number of cases increased to more than 20,000, with total losses worth RM560 million (Bernama, 2022).
Businesses adopting digital technology into their operations are flourishing and working more effectively than ever (Shalhoub & Al Qasimi, 2010). The activities carried out in digital space are exposed to greater risk because an unwanted target or fraudster can access such data and use it negatively against the ethics of the government, private organizations, or a breach of personal privacy (Bakri et al., 2019). This is where cybersecurity is most needed. Cybersecurity is more than just preventing criminals from gaining access to government and business information; it is also about protecting and securing the digital environment from risks and threats of vulnerabilities that may affect government functions, private businesses, and in particular, the digital economy (Meeuwisse, 2015).
Several academics have commented that, for the most part, human is the weakest link in the cybersecurity chain (Anwar et al., 2016; De Bruijn & Janssen, 2017; Hadlington, 2020). Human mistake is responsible for 99% of successful assaults (Othman, 2018). Security technology that has been installed has failed to solve the issue when workers fail to follow cybersecurity standards or participate in actions that endanger themselves and the firm. The increasing complexity of cyberinfrastructure, the interdependence of its components, and human behaviour has escalated the cybersecurity threats (Hadlington, 2018; Lange et al., 2017).
Understanding user behaviour has the benefit of allowing academics and security practitioners to put this knowledge to use and begin to affect behaviour to improve cybersecurity. Furthermore, since most cyber incidents are human-enabled, there is a dire need to expand existing research to underexplored areas such as behavioural aspects of cybersecurity (Lahcen et al., 2020). Human behaviour associated with cybersecurity threats and incidents is termed risky cybersecurity behaviour in the literature. Risky cybersecurity behaviour can be described as actions that increase the vulnerability of personal or organizational information assets (Aivazpour & Rao, 2018). Such behaviour includes clicking on a phishing link or sharing passwords with unauthorized individuals (Aivazpour & Rao, 2018). These actions can put people at risk online and increase the likelihood of a cybersecurity breach or malicious attack (Milne et al., 2009; Hadlington, 2018).
In the Malaysian context, little is known about the possible determinants of risky cybersecurity behaviours that will expose employees and companies to cyber threats in industries vulnerable to cyber-attacks and critical to national safety and security. Risky cybersecurity behaviour can describe online activities that pose a risk to individuals constitute negative cybersecurity behaviour, which can increase the susceptibility to malicious attacks and the likelihood of a cybersecurity breach (Hadlington, 2018; Milne et al., 2009). Attitudes towards cybersecurity can significantly impact individuals’ behaviour and decision-making regarding protecting themselves and their personal information online (Hadlington, 2018). A negative attitude towards cybersecurity can lead to risky behaviours that can compromise their security. A negative attitude towards cybersecurity can significantly impact behaviour in several ways (Venture, 2018). For instance, individuals who view cybersecurity as unimportant may fail to regularly update their software, including operating systems, browsers, and antivirus programs, leaving their devices and personal information vulnerable to cyber threats (Hadlington, 2017). Additionally, those who are careless about online security might reuse the same password across multiple accounts, making it easier for attackers to access their personal information (Ernst & Young, 2019). In conclusion, a negative attitude towards cybersecurity can lead to risky behaviours that compromise an individual’s security and personal information. Individuals must understand the importance of protecting themselves online and take the necessary steps to secure their digital lives.
According to Herath and Rao (2009), corporate (organization), contextual, and individual factors influence employees’ adherence to cyber security practices. Several studies have been conducted, mainly in the Western context, to examine the effects of individual factors such as gender (Anwar et al., 2016; Ameen et al., 2020; Gratian et al., 2018), age (Ameen et al., 2020; Cain et al., 2018; Hadlington, 2018), and personality traits (Denis et al., 2024; McBride et al., 2012; McCormac et al., 2016, 2017; Shropshire et al., 2006, 2015; Uebelacker & Quiel, 2014) on cybersecurity behaviour. Organizational factors such as the size of the company, policies (Kostyuk, 2020), culture, management support and employee participation and training (Briney & Prince, 2002; Chang & Lin, 2007; Hadlington, 2018; Kraemer & Carayon, 2005; Kraemer et al., 2009; Osborn, 2015) also have been associated with cybersecurity behaviour. The contextual factors influencing cybersecurity behaviours include both physical and social environmental elements, such as system accessibility, task convenience, availability of technical expertise, presence of security measures, peer influence, frequent interaction with colleagues, family, or friends, organizational hierarchy, collaborative work requirements, a shared sense of purpose, and exposure to others’ actions and behaviours (Johnston et al., 2019; Kirova & Thanh, 2019; Kroenung & Eckhardt, 2015; Snyman & Kruger, 2019; Wu et al., 2019).
In short, the study of cybersecurity is rapidly evolving alongside technological advancements. In managing cybersecurity, both hard and soft approaches are crucial. Focusing solely on hard factors, such as investments in information systems or platforms, can only partially address cybersecurity issues. Moreover, the comprehensive array of soft factors that can influence attitudes and mitigate risky cybersecurity behaviour are likely to reduce cyber-attack incidents, complementing the existing hard approaches already in place. Despite various hard and soft strategies, ranging from enhancing information security to enacting various laws and policies to curb cyber-attacks, the incidence of such attacks remains high, raising concerns about the effectiveness of current interventions in addressing this issue. According to Cybersecurity Malaysia, 99% of successful attacks result from human error and negligence (Othman, 2018). This indicates that people still do not fully adhere to the established cybersecurity policies and protocols. Given the increasing complexity of cyber infrastructure, the interrelationships between its various components, and the impact of user actions on security, particularly in critical sectors like water, it has become necessary to examine human behaviour in relation to cybersecurity risks (Lange et al., 2017; Hadlington, 2018). Consequently, developing nations are recognizing the importance of deepening their understanding of cybersecurity behaviour, as seen in countries like China and the United States. Additionally, the field of cybersecurity behaviour remains ripe for exploration and development to ensure cyber safety.
This research involved a bibliographic analysis of published articles on the topic of cybersecurity behaviour, guided by two research questions (RQs): RQ1: What are the current trends in publications on cybersecurity behaviour studies? (Tengku et al., 2024) RQ2: What is the impact of publications in cybersecurity behaviour research? (Tengku et al., 2024). The aim of this paper is to conduct a bibliometric review of publications on cybersecurity behaviour sourced from the Scopus database, with a focus on analysing publication trends and assessing the impact of existing research in the field.
The rest of this paper is organized as follows: the next section covers the methodology, followed by the findings, discussion, and future research directions (Abdul Shukor & Karttiyapornpong, 2024; Hussain, 2018).
Methodology
In every discipline, bibliometric analysis stands out as a powerful tool for assessing publication productivity, trends, and future research directions. It effectively identifies, categorizes, and analyzes publications, leading to meaningful conclusions (Merigó & Yang, 2017; Erfanmanesh & Abrizah, 2018). A bibliometric literature review aims to fairly, rigorously, and transparently summarize research findings on a specific issue. Unlike traditional systematic or narrative reviews, bibliometric analysis uses statistical methods to identify both descriptive and analytical variations within research topics. This method not only supports the growth and development of the topic’s profile but also reveals potential research opportunities in the field (Bhandal et al., 2022; Ganji & Afshan, 2024; Mishra et al., 2016).
Search Strategy
The data for this study is sourced from the Scopus database. In this research, the following query is used: (TITLE, ABSTRACT, KEYWORD (“Cybersecurity” AND “Behaviour”) was as applied in the search procedure. Based on the Scopus database, this study examines all publications issued between 2012 and 2022 (Tengku et al., 2024). The study examined publications from 2012 to 2022 to cover ten years of research and observe how cybersecurity behaviour has developed over time. The year 2012 was chosen as the starting point because research on this topic began to grow significantly around that time, driven by rising global attention to cybersecurity issues in organizations, including major data breaches and the introduction of regulations like the GDPR.
Our search strategy is depicted in Figure 1. The search can be grouped into three phases as follow: (i) determines the topic, scope and eligibility, (ii) screening, and (iii) inclusion. The following steps are followed based on above phases: (i) determine the topic, (ii). determine the scope and coverage, (iii) determine the keywords and search string, (iv) date extract the data, v. record identification and screening, (vi) record removed, and (vii) record included for bibliographic analysis. The procedure has found 1569 documents deemed appropriate for additional analyses based on the keyword search were conducted as of 11th September, 2023 (Tengku et al., 2024).

Flow diagram of the search strategy.
Data Sources
The Scopus database was chosen for the bibliometric analysis due to its reputation as the leading citation database globally. Scopus offers the largest collection of abstracts and citations for peer-reviewed publications, including journals, books, and conference proceedings, providing a comprehensive overview of research across various fields such as science, technology, health, social sciences, and the arts and humanities. It also features advanced methods for recording, assessing, and interpreting research (About Ganji & Afshan, 2024; Morandi et al., 2015). Compared to other databases, Scopus offers a large and diverse dataset of journals and conference proceedings, advanced search functions and consistent metadata structure, and Compatibility with bibliometric tools like VOSviewer and Publish or Perish. However, we also acknowledged in the Limitations section that using only Scopus may introduce coverage bias, and future research should consider incorporating additional databases such as Web of Science, IEEE Xplore, and Google Scholar.
On September 11, 2023, a search was conducted using the parameters TITLE-ABS-KEY ((“Cybersecurity” AND “Behaviour”), and limit to (PUBYEAR, 2012–2022). This search was limited to English language articles to ensure consistency in language based analysis. This search initially yielded 2,540 documents. To refine the data, a time span constraint was applied, focusing on publications from 2014 to 2022, which reduced the number of documents to 2,046. Of these, 2,022 were in English. Publications that were not research articles or conference papers, such as books and book chapters, were excluded, resulting in 269 documents. Further refinement at the publication stage removed 19 documents, and additional filtering by subject areas—limited to Computer Science, Decision Sciences, Social Sciences, Energy, Business, Psychology, and Arts—eliminated another 165 documents (Kahraman, 2018). Ultimately, 1,569 documents were included for analysis. Citation data, bibliographic information, abstracts, keywords, and funding details were downloaded in CSV format. Figure 1 illustrates the search methodology used.
Data Analysis
Bibliometric analysis is one the appropriate method of data analysis that focuses on quantifying and evaluating scholarly literature within a specific field or domain (Broadus, 1987; Pritchard, 1969). This format of data analysis involves systematically gathering, processing, and interpreting data from academic publications, citations, and other relevant sources. By employing various bibliometric indicators such as citation counts, co-authorship patterns, and publication trends, researchers gain valuable insights into the impact, collaboration networks, and knowledge dissemination within their chosen area of study s (Palmatier et al., 2018; Pramono et al., 2024; Tranfield, Denyer, & Smart, 2003). The findings obtained through bibliometric analysis enable researchers, institutions, and policymakers to make informed decisions, identify emerging research trends, and assess the influence and significance of individual scholarly contributions, thereby fostering the advancement of knowledge and scientific progress (Aguinis et al., 2011; Donthu et al., 2021; Junni et al., 2013).
Criteria for Data Exclusion
To ensure the relevance and quality of the dataset, specific inclusion and exclusion criteria were applied. Included were publications from 2012 to 2022, written in English, and categorized as journal articles, conference papers, or reviews that focused on cybersecurity behaviour within organizational contexts. Excluded were non-English publications, document types such as editorials, letters, notes, and book chapters, as well as duplicate or incomplete records. Additionally, articles that focused purely on technical aspects such as encryption or malware detection without a behavioural or organizational component were also excluded.
Data Cleaning Process
After exporting the records from Scopus, the dataset was cleaned through both manual and automated processes. Duplicate entries were identified and removed by checking metadata such as titles, DOIs, and authorship. Titles and abstracts were then reviewed to ensure each article was relevant to the research focus on cybersecurity behaviour in organizations. Finally, the cleaned dataset was saved in CSV format to ensure compatibility with the analysis tools used in the study.
Method of Analysis
This study utilized bibliometric analysis (Castriotta et al., 2019). When paired with social network analysis, it highlights the structure and central themes of a research field (Tunger & Eulerich, 2018). Consequently, bibliometric analysis helps identify current trends and potential future research directions (Li et al., 2017). Regarding the tools used for analysis, Microsoft Excel 2007 was employed to perform basic bibliometric calculations and data organization (Tengku et al., 2024). Harzing’s Publish or Perish (PoP) tool was utilized to calculate citation metrics, including total citations, h-index, g-index, and average citations per article. PoP supports data from Scopus and complements VOSviewer by providing detailed quantitative performance indicators. In addition, VOSviewer was selected for its strong capabilities in creating visual representations of bibliometric networks, such as co-authorship, keyword co-occurrence, and citation linkages. It offers clear and interactive visualizations that help reveal patterns and relationships among authors, institutions, and key research topics in the field of cybersecurity behaviour.
Drawing upon recommendations, we conducted a bibliometric analysis of the literature on cybersecurity behaviour using such tools as a citation analysis, co-citation analysis, keyword co-occurrence analysis, PageRank analysis, and co-authorship analysis. These widely used tools are suitable for answering our RQs. Following these works, software packages including Bib Excel (Persson et al., 2009) was used for analysis purpose. Bib Excel provides flexibility and compatibility with other software packages such as Gephi, Pajek, and VOSviewer (Persson et al., 2009). Besides, the bibliometric network was created and visualized using VOSviewer.
Findings
This section presents the results derived from the bibliometric analysis to address the research questions (Tengku et al., 2024). The first research question (RQ1) aims to identify the current trends in publications on cybersecurity behaviour studies. The second research question (RQ2) seeks to assess the impact of publications in this area. The analysis of the extracted Scopus database was organized according to the following categories:
A. Publication Trends—This section will analyse publication trends based on the following items; publication by year, document and sources type, subject areas and the geographical distribution of publications (Alareeni & Hamdan, 2023).
B. Impact of Publication—This section will examine impact of publication based on the following items: authorship analysis, most active institutions, keywords analysis, citation analysis, publication by sources title and abstract analysis.
Publication Trends
This section analyses publication trends on an annual basis. Table 1 presents the number of documents related to ‘cybersecurity behaviour’ collected each year, summarizing annual publications from 2012 to 2022. The data reveals a general increase in the number of publications over this period. Notably, 2018 has the highest number of citations, with a total of 3,133 citations (Khoury, 2024). The field of ‘cybersecurity behaviour’ began with 11 publications in 2012 and has demonstrated a trend of consistent growth and development since then. In 2022 alone, 487 articles were published. Furthermore, the majority of publications were published in 2022, 2021, and 2020. Figure 2 illustrates this growth in publications. In general, total publication have increased year by year. Similarly, for total citation, the analysis trend shows a positive trajectory, increasing consistently from 2012 to 2022. The most significant spike in citations occurred in 2018.
Publication Trends From 2012 to 2022.
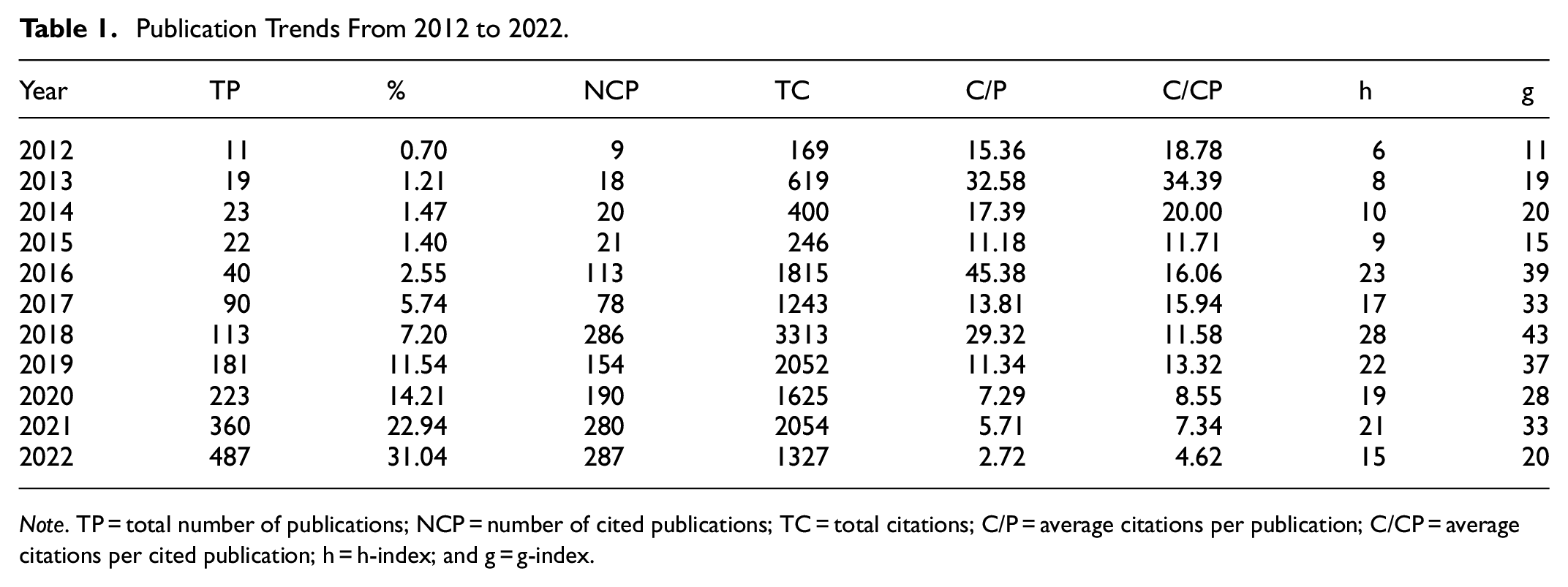
Note. TP = total number of publications; NCP = number of cited publications; TC = total citations; C/P = average citations per publication; C/CP = average citations per cited publication; h = h-index; and g = g-index.
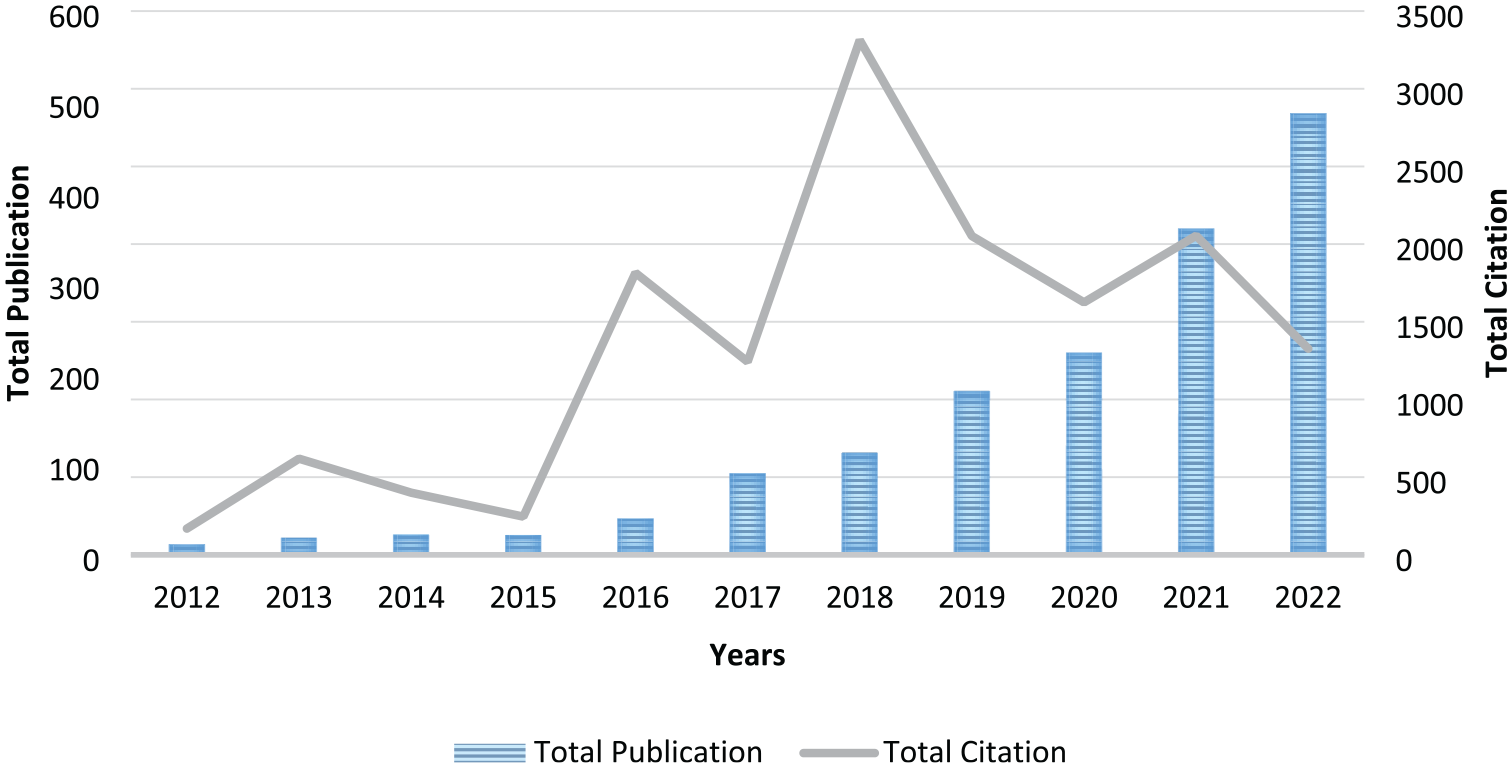
Total publications and citation by year.
Documents and Sources Type
This section reports on published documents based on two criteria: document type and source. Document type categorizes publications by their format, such as articles, conference papers, and books. Source type refers to the medium of publication, including journals, conference proceedings, and book series. For instance, a conference paper may later be published as a journal article, conference proceedings, or book chapter, depending on its final status (Mansour et al., 2021; Smith, 2020).
The distribution of document types in ‘cybersecurity behaviour’ studies is presented in Table 2. Conference papers and articles are the predominant forms of publication, highlighting the significance of both conference research and regular articles. Conference papers represent 61.19% of all publications, while articles account for 38.81%. Specifically, Table 3 categorizes, the analysis is the source of documents is presented in Table 3. The documents into four source types. Conference proceedings are the most common source type (49.33%), followed by journals (38.62%) and book series (11.66%)
Breakdown of Publication Based on Document Type.

Source. Khoury (2024).
Note. TP = total number of publications.
Breakdown of Publication Based on Source Type.

Source. Mansour et al. (2022).
Note. TP = total number of publications (Khoury, 2024).
Subject Area
A subject area refers to a particular area of research or discipline to which a publication or set of publications belong. It categorizes scholarly works based on their content, research focus, or academic domain (Ellegaard & Wallin, 2015; Mori et al., 2023). Subject areas play a crucial role in bibliometric analysis as they allow researchers to examine research trends, identify key contributors, track developments within specific disciplines, and gain insights into the scholarly landscape. The publication information based on the subject area is presented in table 4 (Tengku et al., 2024). The provided data shows the distribution of publications across various subject areas in the analysed “cybersecurity behaviour” dataset (Pramono et al., 2024). The dominance of Computer Science and significant representation of Engineering, Mathematics, Social Sciences, and other fields reflect the research focus within the dataset. Other subject areas such as Biochemistry, Genetics and Molecular Biology, Chemistry, Economics, Environmental Science, Materials Science, Medicine, Multidisciplinary, Psychology, and Arts and Humanities have varying percentages ranging from 0.13% to 3.38% (Umunnawuike et al., 2024). These subject areas represent smaller proportions of the dataset.
Breakdown of Publication Based on Subject Area.
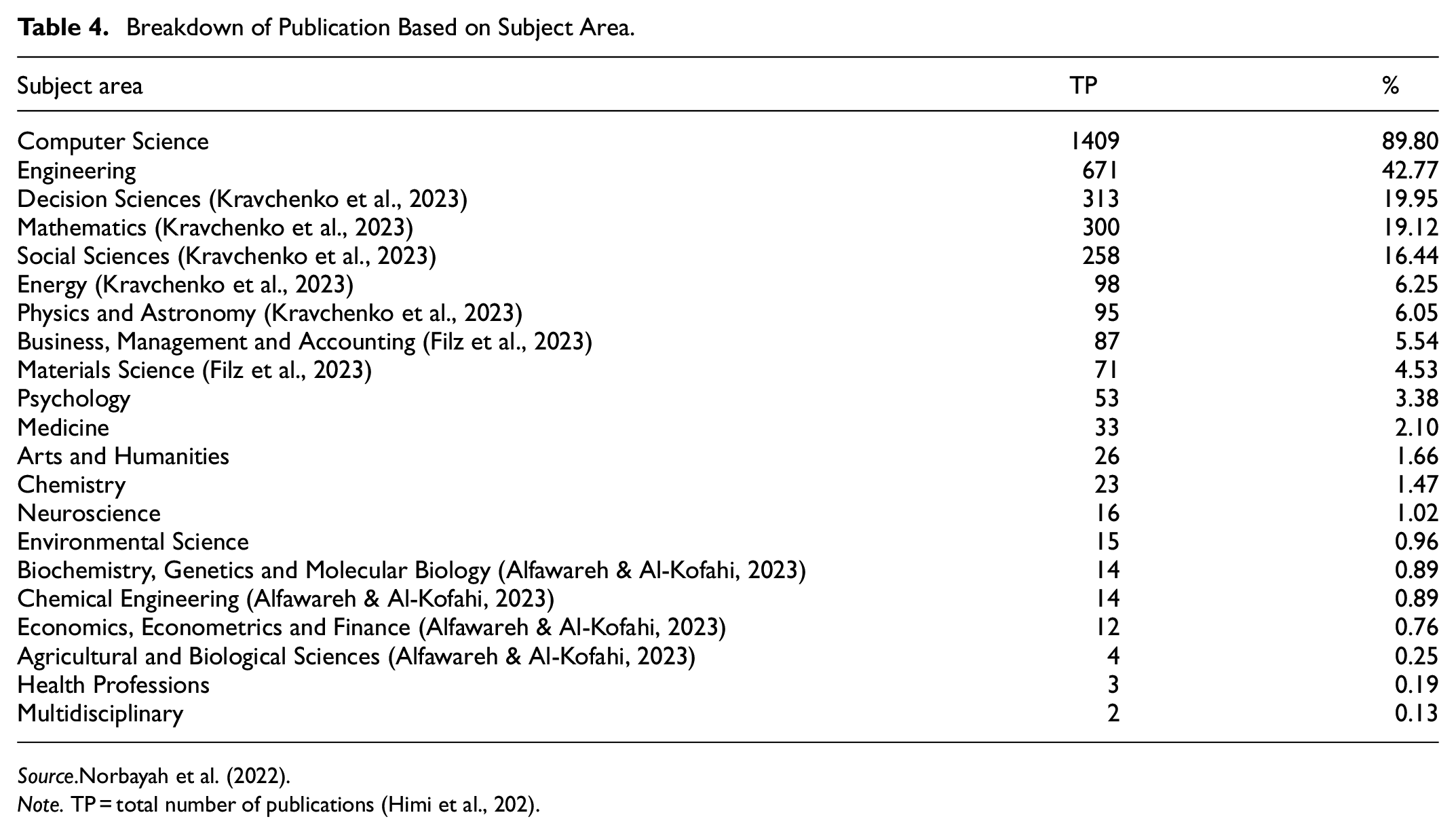
Source. Norbayah et al. (2022).
Note. TP = total number of publications (Himi et al., 202).
Countries
This section presents an analysis of the publication counts by countries. A total of 21 institutions have contributed their scholarly documents to Scopus. The showcases the top ten institutions that have been most active in contributing to publications in the field of cybersecurity behaviour is show in Table 5. Ranked first with 536 published documents, followed by China in second place with 143 published documents, and the United Kingdom in third with 134 published documents (Tengku et al., 2024).In terms of total citation, the United States still has the greatest total citation with 4,837. United Kingdom is placed in the second with 1514 total citation, and followed by China in the third place among top 10 countries contributed to the publications, with total citation of 1,128 (Khoury, 2024).
Top 10 Countries Contributed to the Publications.

Source. Hassan et al. (2022).
Note. TP = total number of publications; NCP = number of cited publications; TC = total citations; C/P = average citations per publication; C/CP = average citations per cited publication; h = h-index; and g = g-index.
Using VOSviewer, we conducted a co-authorship analysis to explore collaborative patterns among researchers and across countries. This revealed key research hubs, particularly in the United States, China and United Kingdom, which emerged as the most active and interconnected contributors in the field on cybersecurity behaviour due to various factors (Zhang et al., 2024). We interpret this trend as a reflection of these countries’ significant investments in cybersecurity infrastructure and research funding, as well as their high publication output across related disciplines.
In the United States, the presence of leading technology companies and research institutions has positioned the country at the forefront of cybersecurity innovation. This environment promotes extensive research into cybersecurity behaviour to address the evolving complexity of cyber threats. The U.S. government has supported this research through substantial investments from agencies such as the National Security Agency (NSA) and the Department of Homeland Security (DHS), further driving academic and industry research in the field (Chowdhury et al., 2021). Similarly, to the United States, China has made cybersecurity a national priority as part of its ambition to lead in technology and digital innovation. The Chinese government has invested heavily in cybersecurity research, technology development, and education, supported by policies such as the Cybersecurity Law and national strategies aimed at improving cybersecurity across all sectors. This focus on securing its extensive digital landscape has driven significant research into cybersecurity behaviour to manage the human factors associated with cyber risks. Likewise, the United States and China, The United Kingdom also views cybersecurity as a crucial national security issue, especially given its role as a major global financial centre and its dependence on digital infrastructure (Lubis & Yus, 2024). The UK government has invested significantly in cybersecurity research through funding for specialized research centres, public-private partnerships, and national strategies. These investments have spurred both academic and industry research into cybersecurity behaviour, particularly in protecting critical infrastructure and sensitive data.
To conclude, the leading contribution of the United States, and China in cybersecurity behaviour research can be attributed to significant government funding, robust national cybersecurity initiatives, and a high output of academic and institutional research. A high average citation per article indicates that the field is generating impactful and widely referenced studies, which likely influence organizational policies and best practices. Additionally, the identification of keyword clusters is important as it reveals the intellectual structure of the field, helping researchers to understand current research priorities, detect knowledge gaps, and identify emerging topics for future investigation.
Impact of Publication
Publication by Authors
This section focuses on identifying the most prolific authors who published in Scopus database (Mansour et al., 2022). The top 10 most active authors with a minimum of six publications in the field of cybersecurity behaviour is summarized in Table 6 (Lubis &Yus, 2024; Mansour et al., 2022). Based on the table, Conventry, L and Rege, A are the top two authors who published more than nine articles. While for total citation, the top two authors are Anwar, M (322) and Li, L (321). Furthermore, Conventry, L (13) and Briggs, P (9) are the top authors of the number of cited publications.
Top 10 Authors Name to the Publications.

Note. TP = total number of publications; NCP = number of cited publications; TC = total citations; C/P = average citations per publication; C/CP = average citations per cited publication; h = h-index; and g = g-index.
Keywords Analysis
Table 7 shows the top 20 of keywords being used in the articles. Keywords “cybersecurity” is the highest use among authors in 1,777 publication and yielded 113.26%. Keyword that used the exact word of “Behavioural Research” has 257 publications. It is the fourth top author’s keyword used.
Keywords the Publications.

Note. TP = total number of publications.
Figure 3 shows there are six themes (clusters) that have recognized in this research, which are represented by colours. Among the themes that are used in this research are cybersecurity, information, learning, software and computers. Specifically, red colour shows the keyword related to cybersecurity, cyber threats, security incidents, human behaviour, and decision making. While the yellow colour shows some keyword, namely, machine learning, deep learning, learning algorithms, network and cyber attack detection. Furthermore, the list of keyword in green colour are embedded systems, cyber-physical systems, smart power grid, and game theory.

Co-occurrence of the keywords.
Discussion and Conclusion
The aim of this paper is to conduct a bibliometric review of publications on cybersecurity behaviour sourced from the Scopus database, with a focus on analysing publication trends and assessing the impact of existing research in the field. This study reviews all types of scholarly works based on the search terms “Cybersecurity” AND “Behaviour” (Tengku et al., 2024). In total, bibliometric data for 1,569 documents published over a 10-year period (2012–2022) were extracted from the Scopus database. This study focusses to address two significant inquiries related to cybersecurity behaviour studies. The initial query focuses on the current publication trends in this field. To address this, a bibliometric analysis was conducted to uncover descriptive patterns in publications, including authors, keywords, sources, types, subjects, and areas (Tengku et al., 2024). The results from the bibliometric analysis show a steady rise in the number of publications on cybersecurity behaviour over time. Among the various document types, journal articles comprise more than half of the published works. Notably, the United States and China emerge as the top two contributors to the field of cybersecurity behaviour research. Furthermore, this research is predominantly published in the two major subject areas, namely computer sciences and engineering (Tengku et al., 2024).
The second research inquiry delves into the influence of publications in the realm of cybersecurity behaviour. To conduct this analysis, citation metrics have been employed, shedding light on the significance of cybersecurity behaviour articles as discussed in this study (Tengku et al., 2024). Over the past 10 years (2012–2022), a total of 1,569 articles have been published, resulting in more than 109.64 citations. On average, cybersecurity behaviour papers from the Scopus database receive approximately 1,090.45 citations each year, with an average of 7.64 citations per paper and 3.66 authors per paper (Punj et al., 2023).
Based on the findings of this paper, several key points can be discussed:
Increasing Trend in Publications: The study indicates a significant upward trend in the number of publications on cybersecurity behaviour from 2012 to 2022. This suggests growing academic and industry interest in understanding and managing human factors in cybersecurity. The growing number of publications reflects the increasing significance of cybersecurity behaviour research as organizations and researchers seek to address the evolving nature of cyber threats (Pramono et al., 2024).
Impact and Citation Metrics: With an average of over 1,090 citations annually and 7.64 citations per paper, the research in this field is having a meaningful impact on the academic community. The citation metrics highlight the importance and influence of these publications within the field. The average of 3.66 authors per paper suggests collaborative research efforts, which are common in complex, interdisciplinary fields like cybersecurity.
Dominance of Journal Articles: More than half of the documents are published as journal articles, underscoring the importance of peer-reviewed journals in disseminating research findings. This highlights the role of journals in advancing knowledge and fostering academic dialogue in cybersecurity behaviour.
Leading Contributors: The United States and China are identified as the leading contributors to cybersecurity behaviour research (Hassan & Ahmi, 2022). This may be attributed to their substantial investments in cybersecurity research, development, and education. The U.S. benefits from a strong presence of technology companies and research institutions, while China’s national priorities and strategic investments in cybersecurity drive significant research output.
Research Limitations: The research’s reliance on the Scopus database limits its scope (Khurshid & ul Islam, 2024). Including other databases such as Google Scholar, Web of Science, PubMed, and Dimensions could offer a more comprehensive understanding of the field and potentially reveal additional trends and influential works that are not captured in Scopus (Tengku et al., 2024).
The implications of the study can be discussed as follow:
For Researchers: The findings suggest a dynamic and growing field, with significant contributions from major global players. Researchers can leverage these insights to identify key trends, leading contributors, and influential works, which can guide future research directions and collaborations.
For Practitioners: The increasing volume and impact of cybersecurity behaviour research highlight its importance in addressing cyber risks. Practitioners should stay informed about the latest research to apply findings effectively in practice.
For Policy Makers: The prominent role of the U.S. and China in this field suggests that national policies and investments play a crucial role in advancing cybersecurity behaviour research. Policymakers in other countries might consider similar strategies to enhance their own cybersecurity research and capabilities.
Overall, the research offers important insights into the trends and impact of cybersecurity behaviour research, revealing the growing interest and influence of this field while also highlighting areas for further exploration (Khoury, 2024).
Limitations and Suggestions for Future Research
This study primarily focusses on the Scopus database, renowned for its extensive collection of academic research (Khoury, 2024). While Scopus is a reputable and widely used bibliographic database known for its extensive coverage of peer-reviewed literature across disciplines, it is important to note that Scopus does not cover all published source (Tengku et al., 2024). As such, certain relevant studies, especially those published in regional journals, emerging conferences, or niche publications not indexed in Scopus, may have been inadvertently excluded. Consequently, the findings presented in this study may not fully reflect the entire scope of global research on cybersecurity behaviour. To enhance the comprehensiveness and generalizability of future bibliometric analyses, it is strongly recommended that additional databases such as Web of Science (WoS), Google Scholar, IEEE Xplore, Dimensions, and PubMed be incorporated (Tengku et al., 2024). These databases cover different sets of journals and conference proceedings and may include unique publications not captured by Scopus for. Including multiple databases would help overcome the coverage bias of a single-source analysis and ensure a more holistic representation of scholarly activity in cybersecurity behaviour research. Future studies adopting this approach would be better positioned to identify regional research trends, underrepresented authors or institutions, and interdisciplinary linkages that may not be visible through Scopus alone.
An alternative approach for potential research involves combining resources from various databases, thereby enhancing the significance and impact of the findings. Additionally, it is essential to include the most recent years in data management, such as incorporating data from 2024. Furthermore, future research should incorporate multiple bibliographic databases to enhance the breadth and depth of bibliometric coverage. While tools like VOSviewer and Harzing’s Publish or Perish are highly effective for visualizing co-authorship networks, citation patterns, and keyword co-occurrence, however advanced bibliometric software such as SciMAT offers additional analytical capabilities that can significantly enhance the depth of analysis and insight generation.
Thematic Evolution over Time:
SciMAT allows researchers to analyse the conceptual and thematic evolution of a research domain across different time periods. This means it can show how core topics in cybersecurity behaviour have emerged, evolved, or declined, which helps identify research trends and shifts in scholarly focus.
Strategic Diagrams and Density Maps:
SciMAT can produce strategic diagrams that classify themes into categories such as motor themes (well-developed and important), niche themes, emerging/declining themes, and basic themes. This enables researchers to evaluate the development level and relevance of specific topics within cybersecurity behaviour.
Longitudinal Performance Metrics:
Unlike static analyses, SciMAT offers longitudinal indicators like the evolution of citations, centrality, and density across different time intervals, helping identify which topics are gaining scholarly traction and which are stagnating.
Integration with Multiple Data Sources:
SciMAT supports data from Scopus, Web of Science, and other bibliographic databases, allowing comparative studies across databases and improving the generalizability of findings.
Knowledge Structure Mapping:
By combining clustering algorithms with performance analysis, SciMAT helps map the knowledge structure of a field. This can uncover hidden relationships and interdisciplinary links between cybersecurity and related organizational behaviour themes.
The use of other software is also highly encouraged in bibliometric analysis, such as Gephi, R and Python, HistCite, EndNote, and Cite Space. From the perspective of cybersecurity studies, it is also important to address the readiness of employees to adopt and utilize technology effectively.
Footnotes
Acknowledgements
We would like to thank Ministry of Higher Education (MOHE) of Malaysia for supporting this research through Fundamental Research Grant Scheme (FRGS/1/2021/SS02/UUM/02/2).
Ethical Considerations
There are no human participants in this article and informed consent is not required.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported by Ministry of Higher Education (MOHE) of Malaysia through Fundamental Research Grant Scheme (FRGS/1/2021/SS02/UUM/02/2).
Declaration of Conflicting Interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
