Abstract
Since the dynamics and forms of cyber violence evolve at the same rapid pace as technology platforms, we used social big data to develop an ontology for cyber violence victimization in South Korea. Following the seven-stage ontology development process, we extracted keywords from 3,075 social media data sources including online articles, comments, and blogs. Focus group interview data was also obtained from 40 adolescents and 5 cyber violence experts. The analysis identified domains for (1) participants subdivided by age, school level, sex, form, and relationship; (2) protective and risk factors by individuals, family, friends, school, community, and online systems; (3) types by form and method of violence; (4) characteristics by media and distinct features; (5) outcomes by individual and relational/social; and (6) interventions and policies by personal coping strategies, services/interventions, and laws/policies. These findings provide a multi-faceted perspective on cyber violence victimization experiences in South Korea. In addition, the results elucidate the newest types of cyber violence in real-life terms.
Plain Language Summary
Introduction
According to the Korean National Cyber Violence Survey 2021, 23.6% of Korean adolescents were the victims of cyber violence, which is substantially higher than that of adults—13.0% (Korea Communications Commission & National Information Society Agency [KCC & NIA], 2022). Of this total, 22.9% of victims were in middle school, and 20.1% were in high school (KCC & NIA, 2022). By subtypes, adolescents reported that verbal/written cyber violence was the most prevalent (16.4%), followed by defamation (10.8%), stalking (8.3%), sexual/visual (5.1%), invasion of privacy (4.4%), exclusion (4.0%), extortion (3.5%), and coercion (3.4%) (KCC & NIA, 2022). Cyberbullying and cyber violence have been observed in other countries as well. For instance, Brochado et al. (2017) reported that the overall global percentage of cyberbullying victimization among adolescents varied from 1.0% to 61.1%, while perpetration varied from 3.0% to 39.0%, and both victimization and perpetration ranged from 1.5% to 72.0%. Additionally, Camerini et al. (2020) found that cyberbullying perpetration among children and adolescents ranged between 5.3% and 66.2%, while victimization ranged between 1.9% and 84.0%.
However, cyber violence is not isolated to the adolescent population. In fact, 14.9% of young adults in New Zealand and 39.7% of adults in Malaysia reported experiencing cyberbullying, while 41.6% of Egyptian women claimed to have experienced cyber violence (Balakrishnan, 2015; Hassan et al., 2020; M. Wang et al., 2019). This demonstrates that the prevalence of cyber violence varies greatly across different studies and nations. Although the distinction between cyberbullying and cyber violence remains ambiguous in much of the existing literature, this study holds the view that cyber violence differs from cyberbullying, and will use the term cyber violence throughout the manuscript.
Following the rapid advancement of technology, cyber violence went through drastic changes over a short period of time (Tomczyk, 2017). In particular, South Korean society has experienced a rapid expansion in the spectrum of cyber violence over the past few years. One of the salient areas for change includes cyber (or digital) sexual crime and cyber fraud or cybercrime (H. Kim, 2021a; W. S. Lee, 2023). These areas now cover leakage of personal information, illicit recording/photo-taking (especially of the body), photo or video editing/photoshopping, cyber stalking, voice and messenger phishing, smishing, pharming, voice mail manipulation, hacking, and other forms of crime related to bitcoin and telegram (H. Kim, 2021a; W. S. Lee, 2023; Wan, 2021). There were also several incidents of zoom-bombing after the outbreak of COVID-19, whereby an unknown or uninvited individual joins and disturbs the meeting/class by bombarding pornographic contents and making indiscriminate slanders (H. Kim, 2021b). Moreover, the recent emergence of cyber violence in the metaverse, particularly in the form of avatar attacks, is raising new concerns and has become a pressing social issue in South Korea (Ban & Nam, 2023).
Given the fast-evolving nature of cyber violence, relying on traditional methods of measuring and conceptualizing cyber violence is no longer an efficient way to capture this phenomenon. Rather, researchers should focus on more extensive data (i.e., social big data) retrieved from various types of online sources in order to completely comprehend the vast dynamics and forms of cyber violence (Han et al., 2019). One of the benefits that come from utilizing social big data is being able to conceptualize cyber violence victimization as encompassing participants, types, risk and protective factors, outcomes, and interventions and policies (Han et al., 2019). Despite this, few studies have attempted to use social big data to address the issue of cyberbullying or cyber violence (S. Lee & Chun, 2020; Muneer & Fati, 2020; Song & Song, 2021). Although cyberbullying is related to cyber violence to some extent, the latter is conceptually more exhaustive (Backe et al., 2018; Broadband Commission for Digital Development, 2015; KCC & NIA, 2022; Peterson & Densley, 2017).
In this study, we focused primarily on cyber violence victimization rather than perpetration. This was done with the intention of clearly distinguishing the factors associated with the victimization experience from those associated with the perpetration experience. In addition, we explored cyber violence victimization beyond the school setting and focused on cyber violence from a universal perspective rather than framing it as part of some other phenomenon. We also collected data from various platforms (e.g., social networking sites, news, blogs, etc.) instead of focusing on a single online platform and covered both risk and protective factors as well as interventions/policies associated with cyber violence victimization.
Because ontology development allows for the collection of unrefined user-generated data, classifying main keywords by types and identifying the relationships among these concepts enables researchers to clearly depict the phenomenon they are studying (Han et al., 2019; Noy & McGuinness, 2001). Thus, this study aimed to develop an ontology for cyber violence victimization that includes the definition, participants, types, risk and protective factors, outcomes, and interventions and policies.
Literature Review
Definition of Cyber Violence
While some researchers view cyber violence and cyberbullying as synonymous (Menesini et al., 2012), others have distinguished between them, defining cyber violence as a broader concept than cyberbullying. For instance, the Korea Communications Commission and National Information Society Agency (KCC & NIA, 2022) defined cyber violence as “an action that harms others or gives discomfort and the feelings of anxiety to others by verbal, text message, videos, etc. in the cyberspace (i.e., internet, smartphone, etc.).” This definition encompasses the following eight forms of cyber violence: verbal/written, defamation, stalking, sexual/visual, invasion of privacy, exclusion, extortion, and coercion.
Similarly, the Broadband Commission for Digital Development (2015) identified the following six categories of cyber violence against women and girls: hacking, impersonation, surveillance/tracking, harassment/spamming, recruitment, and malicious distribution. The “Committing and Experiencing Cyber-Violence Scale” defines cyber violence as the “online risk behavior inclined to harm others” and identifies five components in the victimization scale, including shaming, information manipulation, hate speech, technology abuse, and information sharing (Šincek, 2021). Furthermore, cyber violence is also described as “online actions that assault or endanger a person’s physical, psychological, or emotional well-being, whether criminally or non-criminally” (Alotaibi & Mukred, 2022).
Cyber violence research is becoming increasingly extensive, but studies have continued to utilize inconsistent definitions of cyberbullying and cyber violence—evidently struggling to clearly delineate the components of this global phenomenon (Chun et al., 2020; Langos, 2012). As a result of the limitations caused by the aforementioned inconsistencies, this study attempts to provide a clearer definition and typology of cyber violence, separate from cyberbullying, by developing ontology. However, at the same time, we expect to see the following six characteristics in cyber violence: “1) use of electronic means or devices, 2) vulnerability, 3) repeated harm or behavior, 4) deliberate or intentional act, 5) unwanted information of others, and 6) purpose of threatening/harassing/embarrassing others” (Chun et al., 2020, p. 3).
Cyber Violence and Social Big Data
Regarding relevant ontology development, S. Lee and Chun (2020) developed an ontology for cyberbullying that identified information regarding participants, causes, types, environments, harms, and cyberbullying interventions. Although they attempted to account for the perspectives of victims and perpetrators, they were ultimately unable to clearly distinguish between victimization- and perpetration-related factors. Similarly, Han et al. (2019) developed an ontology for school violence by analyzing the social big data from Korean websites. They divided the participants by age group (e.g., adolescent and adult); the causes by strain, social control, socio-ecological, and delinquent factors; the types by direct and indirect means; the places by offline and online; and the solutions by laws/policies, centers, and programs (Han et al., 2019). However, the results were limited to bullying incidents in a school setting and only partially described cyber violence victimization and/or perpetration. Additionally, Song and Song (2021) developed a decision tree that facilitated the identification of cyberbullying risk factors. They contended that cyberbullying involves three groups—victims, perpetrators, and bystanders, respectively—and the associated factors include impulses, obesity, appearance, sociability, and culture (Song & Song, 2021). However, they did not provide information regarding protective factors, outcomes, and interventions/policies.
Meanwhile, some researchers have used machine learning and deep network learning to detect cyberbullying without having to seek out victims and understand languages used for cyber aggression and hate speech in general (Dewani et al., 2021; Muneer & Fati, 2020). While these detection models displayed good accuracy, the study drew social big data mainly from Twitter and did not incorporate a sufficient amount of online platforms (Muneer & Fati, 2020). The detection models also could not process all the up-to-date slang phrases (Dewani et al., 2021). There was also an attempt to analyze public attitudes and sentiments toward cyberbullying and cyber violence through text mining. Lu et al. (2022) collected 53,526 text data from online websites and identified the following three topics related to cyberbullying: critiques on cyberbullying and support for its victims, rational expressions of anger and celebrity worship, and calls for further control. Notably, most of these topics were connected to negative emotions such as anxiety, anger, and sadness. Similarly, S. Lee et al. (2021) also analyzed 3,075 documents collected from online news and blog posts in the South Korean search engine Naver. The results revealed that the public generally had negative sentiments toward cyber violence (72.3%) and yielded four topics related to cyber violence, including sexual violence, school violence, real person slash, and target and response (S. Lee et al., 2021).
The use of social big data to develop a cyber violence victimization ontology has countless potential benefits. Classifications of related keywords depend on the previous studies and judgments of other researchers. In previous cyber violence studies, participants have largely been classified into the following categories: adolescent and adult populations (Hinduja & Patchin, 2013; Jenaro et al., 2018), males and females (Chun et al., 2020), and victims, perpetrators, and bystanders (Bastiaensens et al., 2014). The big data regarding cyber violence victimization collected from online platforms tend to:
(1) reveal risk and protective factors at different socio-ecological levels (e.g., individual, family and peer, school, and system level), and
(2) highlight various outcomes and impacts (e.g., physical, behavioral, externalized, internalized, school, and peer-related outcomes) (Calvete et al., 2016; Chun et al., 2021; Hong et al., 2018; J. Lee, Chun, et al., 2020; S. Lee & Chun, 2020).
Furthermore, researchers have typically considered cyberbullying in its verbal/written, visual/sexual, and social exclusionary forms (Chun et al., 2020). Given the sufficient amount of data regarding cyberbullying types and devices used, we can categorize the key concepts based on previous studies. Additionally, intervention- and policy-related data sources generally encompass prevention and intervention programs in school (Tanrikulu, 2018), specific coping strategies of the individual (Raskauskas & Huynh, 2015), school policies (Chalmers et al., 2016), and legislation (Asam & Samara, 2016).
Despite the efforts made to use social big data in cyber violence research, the main focus of these studies centered on the detection of language, sentiments, and risk factors associated with cyberbullying—not cyber violence. All of these previous findings add significance to the current body of research. However, ontology would allow researchers to navigate through research topics related to cyber violence in a more comprehensive manner, as it functions like a dictionary encompassing all the terms related to the problem being studied (Gruber, 1993; Noy, 2005; D. Wang et al., 2016).
Methods
Ontology Development
Ontologies are “formal specifications of the terms in the domain and relations among them” (Gruber, 1993). Overall, ontologies define sets of data and their structures with terms, and their development establishes foundations for shared understanding and knowledge bases that can be used in other programs (Noy, 2005; D. Wang et al., 2016). In this study, we employed the seven-stage development process recommended by Noy and McGuinness (2001) to develop an ontology for the collection and analysis of cyber violence social big data. In addition, we referred to prior studies (Han et al., 2019; J. Lee, et al., 2020; S. Lee et al., 2021) that adapted, modified, and supplemented Noy and McGuinness’s (2001) study and process. Figure 1 shows the specific stages used in the development of our ontology.

Ontology Development Process.
Step 1: “Determine the Domain and Scope of the Ontology”
As the first step of ontology development, Noy and McGuinness (2001) suggested using “competency questions” to determine and limit the domain and scope of the ontology (Gruninger & Fox, 1995). Competency questions provide guidance for the particular domain and subject matter of an ontology while limiting the content and level of detail to a certain extent by identifying who, where, and how the findings will be used (Noy & McGuinness, 2001).
The competency questions we used include the following domains of cyber violence: definition (e.g., “What is the definition of cyber violence?”); characteristics (e.g., “Through what platforms does cyber violence occur?”); participants (e.g., “Are there any significant others except for the victims and perpetrators of cyber violence?”); types (e.g., “What types of cyber violence have recently appeared?”); factors (e.g., “What is the family factor of cyber violence?”); results (“What is the social impact of cyber violence?”); and coping strategies (e.g., “What are the legal coping strategies for cyber violence?”). Table 1 shows the study’s specific domain and competency questions.
Domains and Competency Questions of Cyber Violence Victimization.

Step 2: “Consider Reusing Existing Ontologies”
The second step is to review existing related ontologies and determine how they can be modified, supplemented, or extended (Noy & McGuinness, 2001). J. Lee and Chun (2021) developed an adolescent cyberbullying ontology with six domains: “cyberbullying target, factor, type, environment, negative impact, and response” (J. Lee & Chun, 2021). Because our analysis targeted cyber violence, which is a broader concept than cyberbullying, we ultimately created an extended version of this cyberbullying ontology. Furthermore, we focused on cyber violence victimization, while J. Lee and Chun (2021) did not distinguish between victimization and perpetration. In particular, this study used data from both social media (online articles, comments, and blogs) and focus group interviews (FGIs) to extract key ontology terms. This enabled us to develop an ontology that more effectively reflects people’s voices.
Although there are several definitions of social media, a formal definition has yet to be established (Weller, 2015). For example, Russo et al. (2008) defined social media “as those that enable online communication, networking, and/or collaboration” (p. 22). Similarly, Kent (2010) characterizes social media as “any interactive communication medium that enables two-way interaction and feedback” (Kent, 2010, p. 645). Likewise, a review conducted by Duong (2020) outlines the following characteristics of social media: (1) participation of many users, (2) sharing, (3) community-driven, (4) multi-way interaction, and (5) multimedia content. In the past, news and newspapers were representative types of traditional mass media (Duong, 2020). However, contemporary online news sites now facilitate multi-way interaction by including social media features, such as commenting, sharing, and following (Chung, 2008). Blogs that include key features such as user accounts, comment sections, and blog networks are considered another common type of social media (Duong, 2020; Nations, 2021). Hence, this study extracts keywords from online articles with comments and blogs.
In addition to J. Lee and Chun’s (2021) cyberbullying ontology, we also reviewed Han et al.’s (2019) school bullying ontology which was developed to collect and analyze social big data. Although not exactly a cyber violence ontology, we were ultimately convinced of its utility as cyber violence derives from traditional school bullying in many ways. Consequently, we utilized and extended both J. Lee and Chun’s (2021) adolescent cyberbullying ontology and Han et al.’s (2019) school bullying ontology.
Step 3: “Enumerate Important Ontology Terms.”
The third step is to extract and enumerate all of the terms associated with the research topic (Noy & McGuinness, 2001). In this study, we first used internet news and blog data to identify keywords related to cyber violence that correspond to the previously defined ontology areas. However, various media such as glossaries, dictionaries, textbooks, related literature, websites, social media, and interviews with experts and related people can also be used to extract key terms (Park & Jung, 2018). While extracting core terms from texts such as reports or academic studies on related topics is common, extracting terms from social media platforms requires research regarding ontology development for social media analysis (J. Kim et al., 2020). Therefore, in this study, we extracted terms from social media (online articles, comments, and blogs) related to cyber violence, focusing on the top most frequent keywords present in entire documents after removing redundancies from the collected documents. The search keywords were “cyberbullying,”“cyber violence,”“online violence,”“cyber school bullying,”“cyber ostracism,”“online bullying,”“cyber harassment,” and “online harassment.” We collected data from a one-year period (March 9, 2020 to March 8, 2021), amassing a total of 3,075 social media data sources, including online news (n = 2,194) and blogs (n = 881).
In addition, we analyzed data from FGIs with adolescents to extract key terms related to cyber violence using their direct voices. Prospective participants had to meet the following criteria: (1) be an adolescent aged 13 to 17, and (2) have experience as a victim or witness of cyber violence. A purposive non-probability sampling technique was used to collect the data. Ultimately, a total of 40 adolescents participated in 45-minute brainstorming FGIs. During these group interviews, the participants were encouraged to freely express their thoughts regarding the definition, consequences, and protective factors of cyber violence victimization. The brainstorming interview questions were as follows: (1) What do you think cyber violence is? (2) How do you think cyber violence victimization affects you? (3) What do you think will help prevent or reduce cyber violence damage?
Finally, we also utilized data from FGIs with cyberbullying-related experts to extract key terms. A total of five experts participated, including community education experts, school social workers’ association members, and employees at youth-related centers. Thus, in total, we used FGI data from 40 adolescents and, with the assistance of 5 cyberbullying experts, extracted key terms in top-, middle-, and lower-level categories.
Step 4: “Define the Classes and the Class Hierarchy.”
The fourth step is to divide the key terms extracted into the defined class hierarchy (Han et al., 2019; Noy & McGuinness, 2001). In this study, a class hierarchy was developed using a “combination development process” (Uschold & Gruninger, 1996) that combines “the top-down and bottom-up approaches: we define the more salient concepts first and then generalize and specialize them appropriately” (Noy & McGuinness, 2001). We classified and stratified the previously extracted keywords to build higher concepts from lower concepts, this was done while stratifying the class from specific concepts to take into account the attributes of each keyword. The Classification was then used—a task that binds similar information into a single unity of composition—to arrange the keywords of different attributes and classes based on the following attributes: “participants, characteristics, protection and risk factors, types, impacts, and coping strategies.” We also layered the classified keywords within the classification criteria by dividing them into higher and lower concepts.
Steps 5, 6, and 7: “Define the Properties of Classes,”“Define the Facets of the Slots,” and “Create Instances.”
After the classes are defined from the list of terms, the fifth step is to describe the properties of the classes (Noy & McGuinness, 2001). We utilized various types of properties including (1) “intrinsic” properties (e.g., keywords related to the “types” of cyber violence victimization); (2) “extrinsic” properties (e.g., keywords related to the “platforms” of cyber violence victimization); and (3) “relationships to other individuals” (e.g., keywords related to the “participants” in cyber violence victimization) (Han et al., 2019; J. Lee & Chun, 2021; Noy & McGuinness, 2001).
In the sixth step, the “properties” become “slots” attached to classes (Noy & McGuinness, 2001). All subclasses of a class inherit slots, which have different facets describing “the value type.” These “value types” include the following: (1) “String” such as name, (2) “Number” with numeric values, (3) “Boolean slots” (yes–no flags), (4) “Enumerated slots,” and (5) “Instance -type slots.” In this study, “string” was used as a major type to define the facets of the slots (Han et al., 2019; J. Lee & Chun, 2021; Noy & McGuinness, 2001).
The seventh and final step is to create individual instances of classes in the hierarchy by choosing a class, creating an individual instance of that class, and filling in the slot values (Noy & McGuinness, 2001).
Results
Keyword Extraction
In this study, we collected social data related to cyber violence written in Korean from online news, comments, and blogs. After completing the five steps of ontology development, the results were then translated into English. The most frequently used words were “adolescents,”“school violence,”“crime,”“punishment,” and “digital.”Table 2 shows a sample of the collected top keywords. The analysis of the top keywords offers a preliminary comprehension of the extent to which specific keywords are significantly associated with cyberbullying. For instance, the keywords that pertain to the participants—such as adolescent, victim, student, female, children, perpetrator, and preschooler—were highly employed in data from online news, comments, and blogs. Notably, children (n = 5,391), student (n = 7,658), and adolescent (n = 10,827) were referenced more frequently than teacher (n = 1,559), man (n = 1,008), adult (n = 941), and professor (n = 864).
Top Keywords from Social Media, with Frequencies.

Meanwhile, we extended existing ontologies by utilizing the data collected in FGIs with adolescents and related professionals to identify practical terms used by the real people involved. The study organized keywords extracted from FGIs by referring to the competency question domains: participants, protective and risk factors, types, platforms, characteristics, impacts, and coping strategies. Table 3 shows the top cyber violence-related keywords extracted from the FGIs with adolescents and professionals. The domains were divided as follows: (1) participants (e.g., friend, family, person, a senior, and a junior); (2) protective and risk factors (e.g., parent, school teacher, acquaintance, neighbor, and attention); (3) types (e.g., bullying, harassing, attack, exclusion, backbiting, and KakaoTalk prison); (4), platform (e.g., KakaoTalk, phone call, internet, chatting, group chatroom, and personal chatroom); (5) characteristics (e.g., anonymity, bad intentions, intentional, continuous, and deliberate); (6) impacts (e.g., self-esteem, trauma, alienation, irritation, and eeriness); and (7) coping strategies (e.g., report, police officer, teacher, parent, and boy/girlfriend).
Keywords from FGIs with Adolescents and Professionals.

Class Hierarchy of Ontology
After subdividing the classes into types and layers, we specified their respective attributes and attribute values. The objects were then assigned to the class-specific attributes in order to complete the ontology and ensure that it contained both the collected terms and the terms extracted from the FGIs. The cyber violence ontology for adolescents we developed had six top areas: participants, factors, types, characteristics, impacts, and coping strategies. Figure 2 shows the specific hierarchy of the completed ontology, represented using Protégé—an ontology editor jointly produced by Stanford University and the University of Manchester, which is suitable for designing ontology hierarchies and representing relationships between concepts (Jung, 2016). Table 4 provides the definition of the top level in the class hierarchy and examples of the key terms.

Ontology Class Hierarchy Utilizing Protégé.
Top Level in the Class Hierarchy.

While many previous cyberbullying studies have focused on adolescents attending middle and/or high schools (Chun et al., 2020; Hinduja & Patchin, 2013), cyberbullying is a severe problem for the adult population as well (Jenaro et al., 2018). Furthermore, the prevalence of cyberbullying among adolescents differs by gender (Chun et al., 2020). This implies that those affected by and involved in cyberbullying can largely be classified into the following categories: adolescents and adults, males and females, and middle and high school students. Target populations can also be further subdivided into victims and perpetrators, as well as bystanders, a role that is beginning to attract more attention in cyberbullying studies (Bastiaensens et al., 2014). As such, we expected the social big data used in this study to yield results regarding victims, perpetrators, and bystanders. We divided the participant class hierarchy into the following middle levels:
(1) Age, with a bottom level including children and adolescents, and adults (e.g., students and acquaintances).
(2) School level, with a bottom level including middle school students and high school students (e.g., middle school students and high school students).
(3) Sex, with a bottom level including female and male (e.g., women and men).
(4) Form, with a bottom level including victims or perpetrators, significant others, individuals/groups, and others (e.g., gangs, parents, groups, and celebrities).
(5) Relationships, with a bottom level including friends and strangers (e.g., teammates and someone).
Table 5 shows the participant class hierarchy and a sample of its keywords.
Class Hierarchy of Participants.

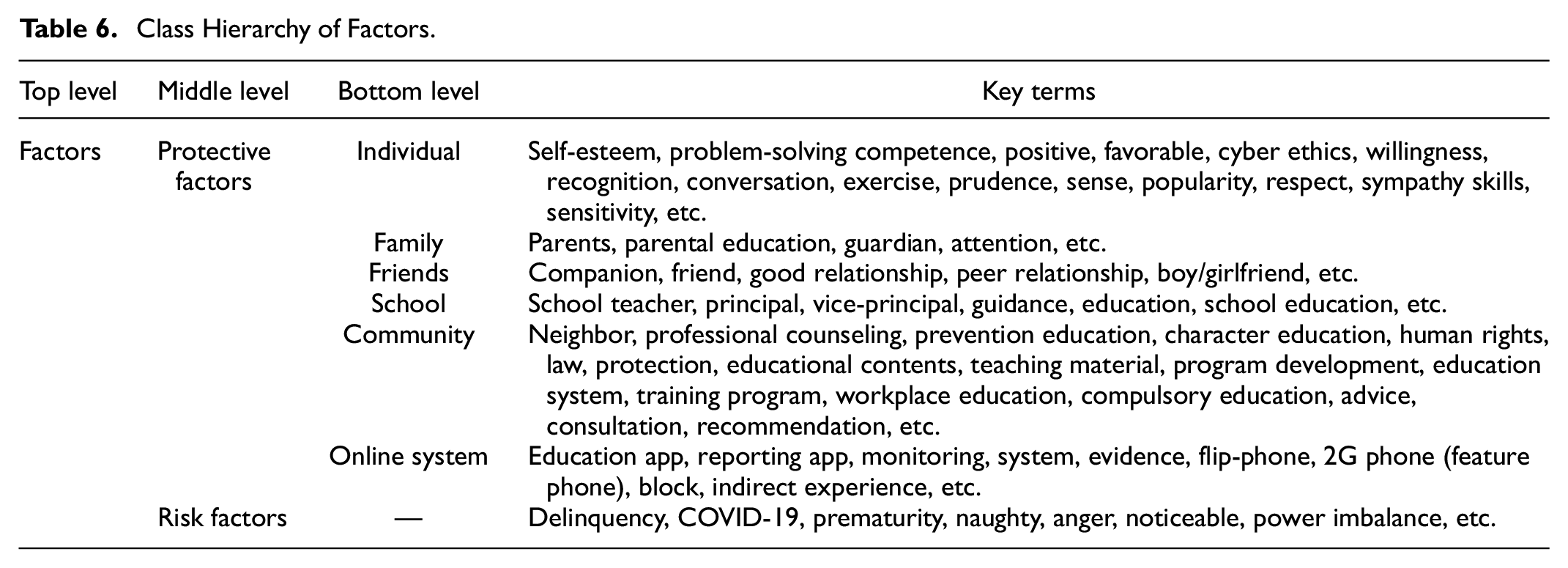
Several studies have adopted the socio-ecological model to categorize cyberbullying protective and risk factors into groups (Chun et al., 2021; Görzig & Machackova, 2015; Hong et al., 2018; Chun, et al., 2020). For instance, Chun et al. (2021) reorganized the cyberbullying victimization protective factors into individual, family, peer, school, and system levels. The domain of cyber violence factors encompassed keywords related to the predictors. It consisted of a middle level represented by protective factors (with a bottom levels, including individual, family, friends, school, community, and online system [e.g., self-esteem, good relationship, schoolteacher, neighbor, and reporting app]) and risk factors including delinquency, COVID-19, and prematurity. Table 6 shows the factor class hierarchy and a sample of its keywords.
Class Hierarchy of Factors.
In addition, cyberbullying typically manifests in verbal/written, visual/sexual, or social exclusionary forms (Chun et al., 2020). We divided the class of each type into middle-level factors, including violence (with a bottom level including verbal violence, visual violence, and sexual violence [e.g., backbiting, manipulation, and sexual harassment]), and method of violence (with a bottom level including ostracism, extortion and exploitation, invasion of privacy, and crime [e.g., exclusion, blackmail, dissemination, and spam messages]). Table 7 shows the types of class hierarchy and a sample of its keywords.
Class Hierarchy of Types.

A systematic review of cyberbullying measurements found that cyberbullying frequently occurs via mobile phone, e-mail, text messages, and other electronic media (Chun et al., 2020). The characteristics class hierarchy comprised the middle level of media forms (bottom level of social media, messenger, distinct features, etc.). Table 8 shows the characteristics class hierarchy and a sample of its keywords.
Class Hierarchy of Characteristics.

Studies have found that cyberbullying victimization has physical-, behavioral-, externalized- and internalized-, school-, and peer-related outcomes (Bonanno & Hymel, 2013; Brighi et al., 2012; Calvete et al., 2016; Landoll et al., 2015; S. Lee & Chun, 2020). The third classification focuses on the impacts of cyber violence and includes two divisions: individual (with a bottom level including physical, mental [internalized], mental [externalized], and financial [e.g., hair loss, trauma, revenge, and property loss]), and relational/social (with a bottom level including family, friend, and school [e.g., estrangement, conflict, and school transfer]). Table 9 shows the impacts class hierarchy of impacts and a sample of its keywords.
Class Hierarchy of Impacts.

Additionally, studies have repeatedly emphasized the importance of cyberbullying prevention and intervention programs in schools (Tanrikulu, 2018), specific individual coping strategies (Raskauskas & Huynh, 2015), school policies (Chalmers et al., 2016), and legislation (Asam & Samara, 2016) as means of counteracting cyberbullying. Thus, we expected the intervention and policy data sources to include these components. The coping strategies class hierarchy comprised the middle level of personal coping strategies (including reports, will to overcome, and pass), services/interventions (including professional counseling, services, and interventions), and law/policies (including police officers, punishments, and legal remedies). Table 10 shows the class hierarchy of coping strategies and its’ sample of keywords.
Class Hierarchy of Coping Strategies.

Discussion
Overall, our analysis generated domains for the following categories:
(1) Participants. Subdivided by age (e.g., adolescents and adults), school level (e.g., middle school students and high school students), sex (e.g., girl or boy), form (e.g., victim or perpetrator), and relationship (e.g., friends or strangers).
(2) Protective and risk factors. Subdivided by individual (e.g., problem-solving competence and self-esteem), family (e.g., parents and parental education), friends (e.g., companions and associates), school (e.g., teacher and principal), community (e.g., expert consultation and prevention education), and online systems (e.g., reporting apps and monitoring systems).
(3) Types. Subdivided by the form of violence (e.g., deep fakes and sexual assault) and method (e.g., WIFI-shuttle (forced to provide mobile data whenever and wherever the perpetrator demands it) and extortion).
(4) Characteristics. Subdivided by media (e.g., Instagram and Telegram) and distinct features (e.g., repetitive and intentional).
(5) Outcomes. Subdivided into individual (e.g., suicide and trauma) and relational/social (e.g., transfer to other schools and conflict).
(6) Intervention and Policies. Subdivided by personal coping strategies (e.g., avoidance and blocking), services/intervention (e.g., artificial intelligence and interests), and law/policies (e.g., lawyers and police) regarding cyber violence.
An ontology “reflects the structure of the world” and often concerns the “structure of concepts” (Noy, 2005, p. 6). As a result, the development of this cyber violence ontology will enable researchers to conceptualize the structure of cyber violence in a manner that accounts for the participants, types, risk and protective factors, characteristics, impacts, and coping strategies. In other words, this study provides a multi-faceted perspective on cyber violence experiences in South Korea and addresses the complexity and variety of unstructured text that makes the systematic collection and analysis of data challenging. This study identified key terms and their relationships by developing an ontology to extract key concepts and effectively collect data. In so doing, it becomes possible to answer the competency questions, which comprise of the following domains: definition (e.g., “What is the definition of cyber violence?”); characteristics (e.g., “Through what platforms does cyber violence occur?”); participants (e.g., “Are there any significant others except for the victims and perpetrators of cyber violence?”); types (e.g., “What types of cyber violence have recently appeared?”); factors (e.g., “What is the family factor of cyber violence?”); results (“What is the social impact of cyber violence?”); and coping strategies (e.g., “What are the legal coping strategies for cyber violence?”).
This ontology could also serve as a good reference and guide for designing research models. For instance, researchers examining cyber violence protective factors could apply it to consider these factors at different levels, including individual, family, friends, school, community, and online systems. In addition, researchers could learn from our ontology that the embedded variables in each category (i.e., participants, types, factors, characteristics, impacts, and coping strategies) should be considered a priority. For example, researchers could investigate the relationship between COVID-19 and cyber violence, which no study has yet examined or established.
In addition, the results include participants subdivided by age, school level, sex, form, and relationship, while the prior study (J. Lee & Chun, 2021) only has three classes (i.e., sex, school level, and characteristics). Previous studies have generally divided cyberbullying into three types: verbal/written, visual/sexual, and social exclusion (Chun et al., 2020). Meanwhile, adolescent cyberbullying ontology developed by J. Lee and Chun (2021) divided types roughly using direct (subdivided using verbal, relational, and other approaches) and indirect methods. The current study’s findings are more comprehensive and thorough because the domain of our ontology includes more specific classes (e.g., verbal violence, visual violence, sexual violence, ostracism, extortion and exploitation, invasion of privacy, and crime). Furthermore, our ontology appears to effectively reflect recent cyber violence trends and encompass new types of cyber violence, including deep-fakes and Real Person Slash (RPS). In addition, it can detect unfamiliar types of cyber violence, such as trolling, which has not typically been addressed in academic research. Future studies should endeavor to extend and update the ontology with whatever new keywords there may be at the time of the research being conducted.
Many of the protective and risk factors of cyber violence are similar to those of cyberbullying victimization. For instance, Kowalski et al. (2014) identified social intelligence, school safety, parental monitoring, perceived support, empathy, school climate, and parental control of technology as factors that protect against cyberbullying. This demonstrated that traditional victimization/bullying, age, frequency of internet use, social anxiety, moral disengagement, risky online behavior, anger, and hyperactivity are correlated with cyberbullying victimization. Our findings confirm that sympathy skills, parents, and school education act as important buffers against cyber violence and point to anger as a risk factor. By expanding upon these factors, we identified additional factors at the individual, family, friend, school, community, and online system levels. In particular, we compared protective factors in online systems (e.g., reporting apps) with those identified in previous studies. Practitioners and researchers could use this list of factors when designing and organizing new cyber violence-related studies and/or intervention programs.
While researchers have previously classified cyber violence outcomes into physical, internalized, and externalized impacts that occur at mental, financial, family, friend, and school levels, most studies have focused on the psychological impacts of cyberbullying victimization, including depression, anxiety, loneliness, stress, and suicide (Kowalski et al., 2014). While this study similarly identifies these outcomes, we also found that cyber violence may result in self-harm, feelings of betrayal, social phobia, property loss, estrangement, and school transfers. The keywords in our ontology are not just words extracted from online databases; they depict in detail what might actually happen to cyber violence victims. As a result, it also provides guidance for planning strategies in order to intervene and prevent such violence from occurring.
The findings of our study also suggest that coping strategies could extend beyond the personal level to include services, interventions, laws, and policies. A systematic review of cyberbullying coping strategies listed social support seeking, avoidance coping, online or technical strategies, and self-efficacy as being the most useful (Raskauskas & Huynh, 2015). This list partially aligns with the results of our ontology, which identifies the will to overcome, pass, disregard, and avoid as personal coping strategies. However, our ontology also indicates that professional counseling, services, petitions, policies, and school violence committees can serve as equally effective strategies for coping with and counteracting cyber violence. Although coping styles may vary by generation and country, this list of non-personal coping strategies highlights the need for experts to take more initiative and for societal-level changes to occur. In addition, imprisonment was also extracted as a strategy used to cope with cyberbullying. Nowadays, a range of cyber violence phenomena manifest, all varying in severity, from those classified as cybercrimes subject to legal jurisdiction, to light-level cyber violence (S. Lee et al., 2021). Further, cyber violence has exhibited an increase in its degree of brutality (S. Lee et al., 2021). Given this current reality, imposing criminal sanctions on cyber violence may also represent a crucial and effective response to prevent and manage this social issue (Rao, 2022). Specifically, the punitive measure of imprisonment serves both a “general deterrence effect” (aims to prevent potential offenders from engaging in criminal activity by demonstrating that committing a crime will result in severe legal consequences) and a “special deterrence effect” (aims to deter a specific offender from reoffending) (Rao, 2022; Yeon, 2003). Pertinently, in 2021 a man who was found guilty of coercing and exploiting several female children and adolescents to produce and distribute sexually exploitative content through Telegram received a verdict of 42 years imprisonment by the Supreme Court of Korea (S. Kim, 2022).
To date, researchers have struggled to conceptually distinguish cyber violence from cyberbullying and have often used the two words interchangeably without providing clear definitions (Blaya et al., 2018). For example, Backe et al. (2018) defined cyber violence as types of abuse that occur online, including cyberbullying, online harassment, cyber dating abuse, revenge porn, and cyberstalking. Meanwhile, cyber violence has also been defined as any violence that occurs via social media and social networking sites (Peterson & Densley, 2017). While this study did not succeed in drawing a clear distinction between cyberbullying and cyber violence, our ontology provides an overview of the factors that comprise cyber violence. We encourage researchers to use it as a foundational resource to conceptualize cyber violence and determine how it differs from cyberbullying.
Most existing cyber violence studies have been limited to conceptualization, prevalence estimation, and examination of various associated factors (Backe et al., 2018; Peterson & Densley, 2017). These studies merely define what cyber violence is, how serious it is, and what affects it. Unlike other research, which has primarily used variables from previous studies, our ontology allows for the identification of new events, topics, and trends that are potentially related to cyber violence. This could include things such as game item shuttle, which indicates behavior forcing victims to hand in-game items. Furthermore, this ontology encompasses data from online resources and keywords highlighted by cyber violence victims/witnesses and experts on the topic. Taking this additional information into account enabled us to identify hidden keywords that could have otherwise remained unidentified. Thus, in order to develop a comprehensive picture of the phenomenon in question, we recommend that cyber violence researchers collect data from various resources beyond websites, including FGIs, academic resources, and policy papers.
The findings of our study also have practical implications, providing a basis for social big data research on cyber violence. The ubiquity of smart devices and social media means that cyber violence can occur anytime and anywhere, making it a social issue with global relevance (Kowalski & Limber, 2007). Cyber violence generally occurs on the same social media platforms that serve as the primary sources of social big data, which plays direct or indirect roles in the cyber violence discourse. Big data analysis gives shape to the unpredictable and unstructured data generated by social media, providing a basis for social perspectives on cyber violence issues (Han et al., 2019) and a useful ground for discussions of cyber violence prevention and intervention. Therefore, this study’s creation of a cyber violence ontology marks a significant step forward in the collection and analysis of social big data regarding cyber violence issues. This is also why this study is so meaningful. It presents and extends a cyber violence-related ontology as the initial step in the collection and analysis of related social big data. Social big data analysis is the process of extracting meaningful value from the vast amounts of data generated daily on various social media platforms. The insight it provides regarding the future developments of related trends makes it possible to effectively analyze and predict cyber violence. In the future, the effective prediction of cyber violence signs should help screen potential perpetrators and victims, thereby accelerating intervention and prevention.
One limitation of this study is that it did not cover all social media, documents, and keywords related to cyber violence. In reality, extracting all keywords related to cyber violence and including them in an ontology structure is simply not feasible. Thus, future studies should endeavor to extend and update our ontology with more keywords from various social media platforms. Second, the study was based on big data from South Korea and, therefore, does not represent other countries. Although cyber violence has common characteristics globally, supplementing the current ontology with keywords that reflect the distinct characteristics of each country remains necessary. Third, ontology class hierarchies vary based on the criteria used to classify keywords. Although we followed the Ontology Development 101 steps and tried to minimize subjective judgments by referring to various prior studies, no uniform criterion for establishing a classification system currently exists. Moreover, since this study collected and analyzed social network data through inductive research methods, there may be fundamental limitations as the context and meaning of each extracted term may not be clearly classified (J. Lee & Chun, 2021; S. Lee et al., 2021). That is, a specific term may not necessarily be included in only one specific classification, or it may overlap with multiple perspectives (J. Lee & Chun, 2021; S. Lee et al., 2021). In addition, it was not possible to analyze the overall frequency or significance of the keywords as this study utilized both social media data—which provided information on the frequency of the keywords—and FGI data, which lacked such information. However, in future studies, the ontology presented in this study could be leveraged to assess the importance of the keywords as a whole.
Nevertheless, the classification system established in this study will make it a leading ontology in future development efforts, enabling it to contribute to the construction of more advanced cyber violence ontologies. Moreover, it will serve as a framework for future cyber violence research and social analysis. For future reference, we highly encourage the researchers to:
(1) pay more attention to new types of violence identified in this ontology, such as deep-fakes, RPS, and trolling;
(2) update the ontology, with recent keywords and other means of sources, including academic papers, policy papers, etc.;
(3) figure out ways to draw a borderline between cyberbullying and cyber violence; and
(4) enlarge the spectrum of ontology to reflect features of cyber violence in other countries.
Conclusion
Despite this study’s limitations, our cyber violence ontology provides an important framework for social big data analysis. In this study, we believe we have developed the most up-to-date and comprehensive cyber violence ontology that reveals the essence of cyber violence. This was achieved by using real-life terms based not only on social media but also on the real voices of adolescents and professionals and reflects recent forms and characteristics of cyber violence. By elucidating the definition, participants, characteristics, types, factors, impacts, and coping strategies of cyber violence, our ontology enhances the knowledge of researchers and professionals in cyber violence-related fields and has practical implications for efforts to combat this phenomenon.
Footnotes
Acknowledgements
None.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Ministry of Education of the Republic of Korea and the National Research Foundation of Korea (NRF-2018S1A5A2A01034744).
Ethical Approval and Patient Consent
Not applicable.
Data Availability Statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
