Abstract
The debate over teenagers’ exposure to cyberbullying has aroused broad public concern, but there are few nationwide empirical studies on teen cyberbullying in China. Based on social cognitive theory, this study analyzes the current state of cyberbullying among Chinese teenagers using a questionnaire survey (N = 1,538) distributed to teenagers in eastern, central, and western regions of China. The results suggest that 18.1% (N = 279) of respondents reported having bullied someone and 54.6% (N = 839) reported having been bullied online, and that age, gender, individual school performance, and risky online behaviors may predict different cyberbullying behaviors. Enhancing teenagers’ awareness of the importance of protecting their personal information is critical, along with implementing social protective measures to contain cyberbullying.
Introduction
The growth of the internet worldwide has led to online platforms being misused as a new opportunity for teen bullying (Herrera-López et al., 2017). According to a 2019 United Nations survey covering 31 countries, one-third of young people reported exposure to cyberbully, and one-fifth of them skipped school because of it (Naftalin, 2019). Cyberbullying is also prevalent among Chinese teenagers and getting worse (Chen & Chen, 2020; Li & Hesketh, 2021). According to the 2019 National Research Report on Minors’ Internet Access, there were 175 million internet users under the age of 18 at the end of 2019, equaling 93.1% of minors, of whom 42.3% had experienced cyberbullying (CNNIC, 2020; Liang & Wu, 2021).
Teenagers targeted by cyberbullying report increased depression, anxiety, loneliness, suicidal behavior, and somatic symptoms (Nixon, 2014). In recent years, China has debated how to protect teenagers from cyberbullying. On October 17, 2020, the government of China revised the Law on the Protection of Minors and introduced restrictions on cyberbullying for the first time. Under the law, no organization or individual may insult, slander, or threaten minors in the form of words, pictures, audio, or video (Beijing News, 2021).
A large number of studies of cyberbullying have been conducted in different countries such as Spain and United States (Marin-Lopez et al., 2020; Paez, 2018). Research on cyberbullying of Chinese teenagers has also been developing in recent years. Previous studies have explored the individual and family factors to cyberbullying perpetration and victimization among Chinese teenagers (Chen & Chen, 2020; Rao et al., 2019; Zhou et al., 2013) and risk factors for school bullying and cyberbullying (Li et al., 2019; Li & Hesketh, 2021). Most of these studies lack a theoretical basis and analyze the risk factors of cyberbullying primarily from a psychological perspective, without addressing impact factors at individual, society, and media levels at the same time, and ignoring the current status of Chinese teens’ cyberbullying (Li et al., 2019; Li & Hesketh, 2021). Besides, the existing data is from specific areas of China and does not consider the influence of varying levels of economic development and internet literacy in different regions of China (Rao et al., 2019; Zhou et al., 2013). To examine the current status of cyberbullying perpetration (CP) and cyberbullying victimization (CV) among Chinese teenagers over a wider area, our research team administered a printed survey to 1,538 teenagers in seven provinces and regions in eastern, central, and western China in 2019. Using social cognitive theory, this study analyzed the individual, social, and media factors that influences cyberbullying via social cognitive theory.
Literature Review and Research Questions
Cyberbullying and Social Cognitive Theory
While the word cyberbullying has entered people’s daily vocabulary, researchers did not universally agreed on the definition of it. Roberto et al. (2014) define cyberbullying as “the deliberate and repeated misuse of communication technology by an individual or group to threaten or harm others” (p. 98). Grigg (2010) describes it as “behaviors using mobile phones or the internet to carry out bullying, harassment, stalking, abuse, assault or hostility” (p. 152). Thus cyberbullying uses electronic means to perpetrate malicious, humiliating, offensive, and provocative acts against a person or group.
This study applies Bandura’s (1999) Social Cognitive Theory (SCT) to understand the role of social factors as well as an individual’s characteristics and online behaviors in cyberbullying. Under this theory, individuals, their behaviors, and the social environment mutually influence each other (Bandura, 1999). Here, the research situates SCT within a wider socio-ecological perspective of cyberbullying (Espelage, 2014; Hong & Espelage, 2012) emphasizes various contexts in the social environment on human behavior.
While the socio-ecological approach emphasizes the general influence of contextual factors on an individual’s development, it does not specify the mechanisms of developmental or behavioral outcomes (Wachs et al., 2020). In line with SCT and the environment of cyberbullying, this study concerns the socialization agents suggested by SCT across various environmental contexts (such as family and school), and adds individual online behaviors as the main influence mechanism for human agency.
Before investigating the causes of cyberbullying perpetration and victimization, we need to discover the types of bullying that occur and their frequency. Thus the first two research questions are:
Risk Factors for Cyberbullying Perpetration and Victimization
Individual characteristic factors
Traditional bullying usually relates to a dynamic of unbalanced or unequal power between the perpetrator and the victim; thus teenagers are more likely to be bullied by those power (Olweus, 2003). Demographic characteristics such as gender, age, urban versus rural location, and academic performance are considered critical variables related to traditional bullying (Sobba et al., 2019). In the case of cyberbullying, victims cannot know the true identity of perpetrators due to the anonymity and concealment of the internet; thus power imbalance may be not the essential factor at work in cyberbullying. Whether demographic variables that have been identified in general bullying also apply to cyberbullying remains to be investigated.
How gender influences cyberbullying is a topic of debate, with inconsistent results in the literature. Many researchers have found that boys are more likely to be perpetrators, while girls are more likely to be victims of cyberbullying (Li, 2006; Rao et al., 2019). However, some researchers have found that girls switch their roles from victims of traditional bullying to perpetrators of cyberbullying, while boys switch their roles from perpetrators to victims (Kowalski & Limber, 2007). Chang et al. (2015) arrived at a third conclusion: compared with girls, boys are more likely to be both perpetrators and victims of cyberbullying. Boys are likely to spend more time playing cyber games, thus exposing themselves to the risk of being bullied and also having more opportunities to become perpetrators, but whether this amounts to a significant difference between boys and girls has not yet been confirmed (Monks et al., 2012).
Age also has a complicated association with cyberbullying and again, study results are inconsistent. In traditional bullying, being a victim generally decreases as teenagers get older, but being a perpetrator may increase (Whitney & Smith,1993). With cyberbullying, some studies have revealed that teenagers tend to be increasingly exposed to social media as they get older, and thus are more likely to become both perpetrators and victims (Robson & Witenberg, 2013). In contrast, Slonje and Smith (2008) found that older students (15–18 years old) were less involved in cyberbullying than younger students (12–15 years old). Smith et al. (2006) demonstrated that age has no significant influence on CP and CV.
Academic performance is associated with cyberbullying. In a survey of 610 students at the senior secondary level, poorer academic performance was correlated with higher perpetration (Muzamil & Shah, 2016). Similarly, in a survey of 1,438 high school students in China, Zhou et al. (2013) found that compared with higher performing students, poorer students are more likely to be perpetrators of cyberbullying. In traditional bullying, poorer students are more likely to be victims, but a similar correlation has not yet been established for cyberbullying. Thus this study examines the influence of academic performance on the likelihood of becoming a victim of cyberbullying.
A limited number of studies have investigated the influence of people’s location in urban versus rural environments on cyberbullying. In rural areas, internet access may be less reliable than in more urban areas (Bauman, 2010). However, in a survey conducted at an online social networking site in Turkey, Akbulut et al. (2010) found that rural and urban participants are similar in their victimization scores. Participants in that study were not necessarily adolescents, and the relationships between cyberbullying and location are unclear.
Gaps in the literature on the influence of individual characteristics on cyberbullying lead to the third research question:
Social environmental factors: Families and schools
Social Cognitive Theory indicates that social environmental factors influence individual behaviors. The family has been demonstrated to be one of the most critical environmental factors influencing perpetrators and victims in traditional bullying (Ahmed & Braithwaite, 2004). The increasing popularity of the internet has created new challenges for parents and teenagers regarding the boundaries between parental control and adolescent autonomy in virtual spaces (Erickson et al., 2016). Still, parents have a key role to play in reducing cyberbullying. Some researchers have found that cyberbullying can be reduced if parents discipline their children by restricting their internet access (Legate et al., 2019; Monks et al., 2016). Sasson and Mesch (2017) found that the restrictive measures taken by parents would significantly reduce their children’s risk of being bullied online. However, Elsaesser et al. (2017) reported that parental restrictions on internet access are only weakly associated with perpetration and victimization. Mesch (2009) found that prohibiting the use of cellphones or restricting internet access does not influence cyberbullying among teens ages 12 to 17 (Mesch, 2009). Given these conflicting conclusions, the fourth research question is:
Educators and schools are vital participants in promoting the positive development of teenagers and guarding them against cyberbullying and mitigating its negative outcomes among teens (Hinduja & Patchin, 2013). Measures taken by schools do reduce in-school traditional bullying (Wang et al., 2013). Merrell et al. (2008) found that cyberbullying intervention measures taken by schools cannot lead to a significant influence. Stauffer et al.(2012) conducted a survey of 66 U.S. high school teachers and concluded that school cyberbullying prevention programs produce minimal change. But Bevilacqua et al. (2017) held that schools’ management might have an impact on reducing cyberbullying. Such as monitoring students’ online behavior more diligently (Brown et al., 2006). Thus, the fifth research question is:
Media factors
Many researchers have found that people who spend more time using information communication technology are more likely to be involved in cyberbullying perpetration and victimization (Akbulut et al., 2010; Bauman, 2010; Lee & Shin, 2017; Zhou et al., 2013). Kowalski et al. (2014) found that media exposure was a critical risk factor for cyberbullying. In particular, internet surfing time, personal privacy disclosure, and exposure to internet pornography and violence significantly increase the likelihood of teenagers being exposed to cyberbullying perpetration and victimization (Chen et al., 2017; Kokkinos & Antoniadou, 2019). First, more daily time on the internet is associated with a higher likelihood of perpetration and being victimized. Ybarra and Mitchell (2004) found that the odds of experiencing aggressor/target behaviors are 2.5 times higher for teenagers who use the Internet three hours a day or longer compared to less than three hours. However, Vandebosch and Van Cleemput (2009) found that weekly internet surfing time was irrelevant to whether teenagers would become perpetrators or not. Second, dangerous internet behaviors such as leaking personal information are correlated with online harassment and sexual solicitation. Those who leak personal information to online strangers or provide passwords to friends are more likely to become perpetrators and victims of cyberbullying (Kwan & Skoric, 2013; Walrave & Heirman, 2011).
Give those conflicting studies, and this study considers whether internet exposure and personal information leakage are related to cyberbullying. The sixth and seventh research questions are:
Methods
Sampling
Considering the wide variations in the development of the internet economy across different regions of Mainland China, we conducted a questionnaire survey using a multistage, stratified-cluster random sampling method. Two or three provinces (municipalities or autonomous regions) were selected from the eastern, central, and western regions. A capital city was selected from each, and then a prefecture-level city or municipal district with a wide economic gap with the capital city was selected according to its 2018 provincial GDP. At each site, the survey was administered to one or two randomly selected classes at a local public senior high school at the medium and high rankings of comprehensive strength. To ensure reliability and validity, 400 pretest questionnaires were distributed at community libraries, parks, and museums frequented by teenagers in Guangzhou, Guangdong. Fourteen adolescent respondents attended an intensive interview, and the questionnaire items were revised according to the interview responses. The survey period was from August 20, 2019, to October 15, 2019. A total of 2,000 questionnaires were distributed and 1,538 (76.9%) were recovered. This survey covered the following regions and cities: Eastern region: Guangzhou (129 respondents) and Qingyuan (94) in Guangdong Province, Jinan (88) and Linyi (141) in Shandong Province. Central region: Changsha (161) and Huaihua (157) in Hunan Province; Zhengzhou (104) and Pingdingshan (135) in Henan Province. Western region: Yongchuan (109) and Beibei (77) in Chongqing; Nanning (57) and Baise (119) in Guangxi Zhuang Autonomous Region; Kunming (83) and Qujing (84) in Yunnan Province.
This distribution assured a representative sample across China. Students chose freely whether to participate and all respondents provided informed consent from their parents and schools. The statistical description indexes of the samples are given in Table 1.
Statistical Description of Demographic Characteristics (N = 1,538).

Measurement
The research variables in this study include demographic variables, cyberbullying perpetration (CP), cyberbullying victimization (CV), internet access restricted by parents and school, teenagers’ online time, and their personal information leakage.
Demographic variables
The demographic variables in this study are gender, age, location in urban or rural areas, and academic performance (Table 1). Gender and age were indicated out by respondents on the survey. Academic performance was assessed by asking respondents the grade they received on the average grade for all of their courses of the previous semester: failed, poor, fair, good, or excellent, with assigned values of 1 to 5 (M = 3.55, SD = 0.90).
Cyberbullying
To measure the extent of participants’ exposure to cyberbullying (as both perpetrators and victims), this study uses the Cyberbullying Questionnaire (CBQ) designed by Calvete et al. (2010), and the internationally accepted European Cyberbullying Intervention Project Questionnaire (ECIPQ; Del Rey et al., 2015), which have been shown to have good construct validity and adequate reliability.
Cyberbullying perpetration
To measure perpetration, the respondents were asked to indicate how often they engaged in the following behaviors during the previous 2 years: (1) sent information and photos threatening or harming classmates; (2) posted embarrassing jokes, spoke ill of others, or spread rumors on the internet; (3) accessed others’ accounts to pirate personal information; (4) posted a video, photo, or other malicious content on social media that was harmful to another person; (5) shared others’ secrets or photos on the internet without their permission; (6) deliberately removed or blocked someone from a WeChat, QQ, or game group or BBS; (7) deliberately targeted or ignoring someone in a WeChat or QQ group. The range of answers on a 5-point Likert scale was 1 = never, 2 = once or twice total, 3 = about once or twice over six months, 4 = about once a month, and 5 = about once a week. The summation of seven behavioral items is the assigned value for perpetration (M = 7.62, SD = 2.25, α = .90).
Cyberbullying victimization
To measure CV, the respondents were asked to indicate how often they were the target of the following behaviors over the previous 2 years: (1) someone sent information and photos threatening or harming me; (2) someone posted embarrassing jokes, spoke ill of me, or spread rumors about me on the internet; (3) someone intruded in my personal accounts to pirate my personal information; (4) posted a video, photo, or other malicious content on social media that was harmful to me; (5) someone shared my secrets or photos on the internet without my permission; (6) someone deliberately removed or blocked me from a WeChat, QQ, or game group or BBS; (7) someone deliberately targeted or ignored me in a WeChat or QQ group. The range of answers on a 5-point Likert scale was 1 = never, 2 = once or twice total, 3 = about once or twice over six months, 4 = about once a month, and 5 = about once a week. The summation of seven items is the assigned value for victimization (M = 8.60, SD = 2.83, α = .84).
Internet access restriction
The extent of internet access restrictions imposed by teachers and parents was measured according to the criteria used in the China Education Panel Survey (CEPS), a national survey administered by the National Survey Research Center (NSRC) at Renmin University of China to document the association between students’ educational outcomes and family, school, community, and social contexts. Restrictions were measured on a 5-point Likert scale, ranging from 1 = never to 5 = very strict (M = 3.52/4.36, SD = 0.87/0.88).
Time on the internet
Time spent on the internet was measured by asking participants the average time they spent on the internet each day, ranging from 1 = never to 5 = over 3 hours (M = 3.59, SD = 0.90) respectively.
Leaking personal information
Leaking personal information was measured using Debatin et al.’s (2009) design scheme. Respondents were asked to indicate which of 13 types of personal information they had posted on social media (QQ, WeChat, etc.) in the past 2 years, such as their real name, a real photo, date of birth, or interests and hobbies. The sum of the scores indicates the extent of participants’ personal information disclosure. A higher score means a higher level personal disclosure (M = 2.92, SD = 1.86).
Data Analysis
We used descriptive statistics to discover how teenagers are currently exposed to cyberbullying perpetration and victimization through descriptive statistics. In the next step, demographic variables related to CP and CV were compared by ANOVA and t-test. Then, a regression model was constructed using least-squares linear regression analysis (OLS regression), with CP and CV treated as dependent variables, and individual, social, and media factors treated as independent variables. All data were analyzed and processed on StataSE16.0 statistical software.
Results
Question 1 examined the types of cyberbullying that Chinese teenagers engage in as perpetrators, and how often they occur. As shown in Table 2, the frequency of all perpetration behaviors does not exceed 10% in any instance. “Deliberately targeted or ignored someone in WeChat or QQ Group” (8.3%) is the most frequent perpetration behavior, followed by “deliberately removed or blocked someone from WeChat Group, QQ Group, game group, or BBS” (7.5%), “shared others’ secrets or photos on the internet without their permission” (6.6%), and “spoke ill of others or spread rumors on the internet” (6.6%). “Accessed others’ accounts to pirate personal information” (3.5%) is the least frequent perpetration behavior. The results show that 18.1% of participants (279) reported that they had engaged in at least one or two perpetration behaviors in the previous 2 years. Boys accounted for 59.7% (166) of perpetrators and girls accounted for 40.2% (112; Table 2).
Teenagers’ Exposures to Cyberbullying Perpetration and Cyberbullying Victimization.
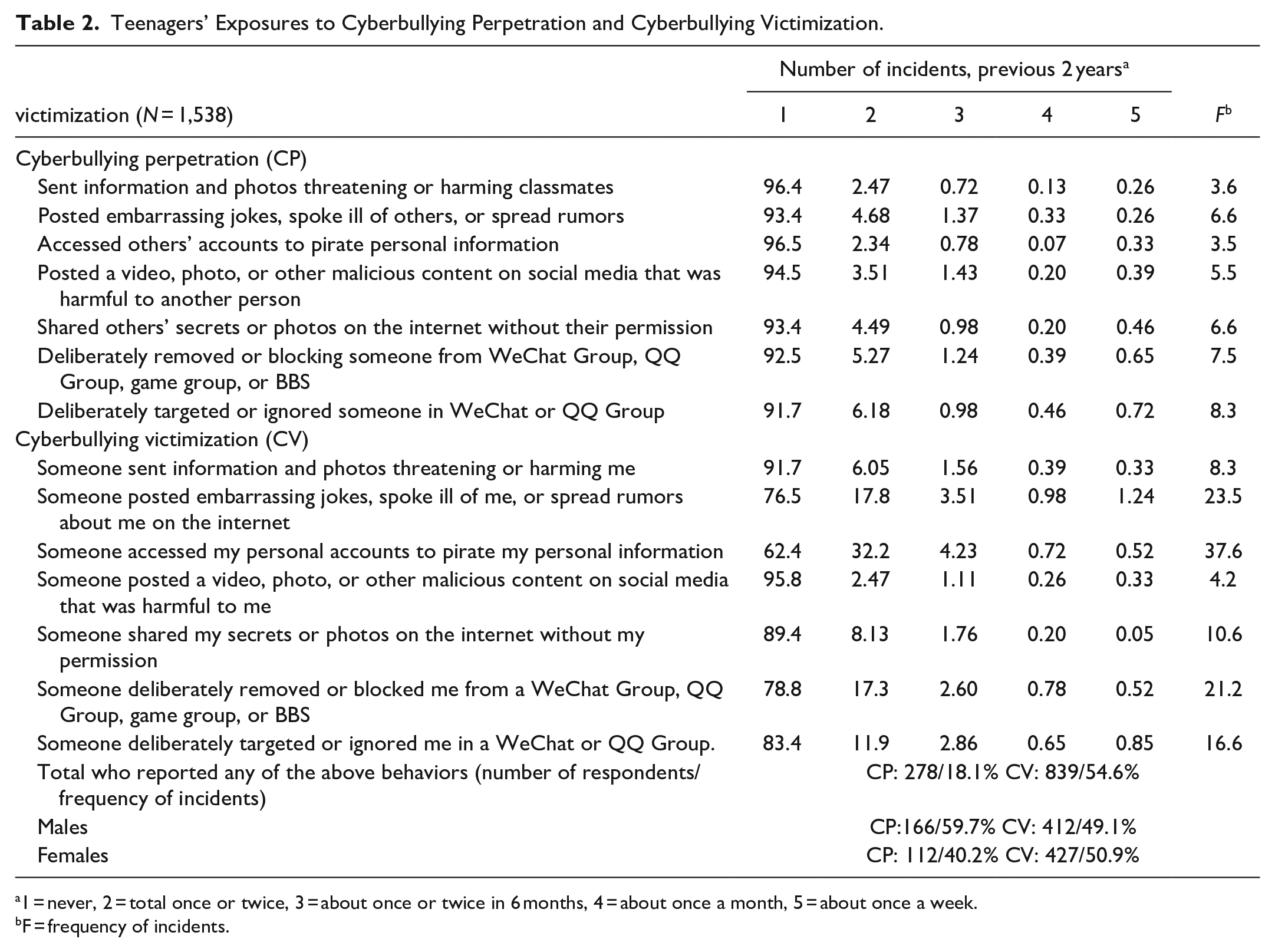
1 = never, 2 = total once or twice, 3 = about once or twice in 6 months, 4 = about once a month, 5 = about once a week.
F = frequency of incidents.
Question 2 examined the types of cyberbullying that Chinese teenagers experience as victims and how often they occur. The results show that, of total, 54.6% (N = 839) reported being bullied online, which is much more than bullies (18.1%). Boys accounted for 49.1% (N = 412) and girls accounted for 50.9% of those victims (N = 427). As shown in Table 2, “someone accessed my personal accounts to pirate my personal information” (37.6%) is the most frequent CV behavior, but this item was reported with the least frequency in perpetration behaviors. The next most frequent CV behaviors are “someone posted embarrassing jokes, spoke ill of me, or spread rumors about me on the internet” (23.5%) and “someone deliberately removed or blocked me from a WeChat Group, QQ Group, game group, or BBS” (21.2%). “Someone posted a video, photo, or other malicious content on social media that was harmful to me” (4.2%) was reported as the least frequent CV behavior.
Question 3 examined how individual factors such as gender, age, academic performance, and urban versus rural location are associated with CP and CV. Comparative and regression analyses (Tables 3 and 4) show, first, that girls engage in perpetration behaviors at a significantly lower rate than boys (t = 3.29, p < .005), and they experience significantly less cyberbullying victimization than boys (t = 6.48, p < .001). Second, different age groups engage in perpetration behaviors with significant differences (F = 5.13, p < .001), and older teenagers have more perpetration behaviors; different age groups are also exposed to CV with differences (F = 0.28). Nonetheless, age has no influence on CV (Table 4), which means that other factors have intervening effects. Third, whether in t-tests or regression analysis, urban versus rural location has no significant influence on CP and CV (p > .05): teenagers in rural areas (M = 7.60, SD = 2.15) and those in urban areas (M = 7.64, SD = 2.39) have similar perpetration behaviors, and their exposure to CV behaviors (rural areas: M = 8.54, SD = 2.76; urban areas: M = 8.69, SD = 2.92) is also very similar. Finally, academic performance only negatively influences CV (b = −0.23), meaning, the better a teenager’s academic performance, the lower the experiences of CV.
Comparative Analysis of Teenagers’ Engagement in Cyberbullying Perpetration and Experiences of Cyberbullying Victimization (N = 1,538).

Notes. The t values were calculated using t-test, the F values were calculated using ANOVA.
OLS regression analysis of cyberbullying perpetration and cyberbullying victimization (N = 1,538).
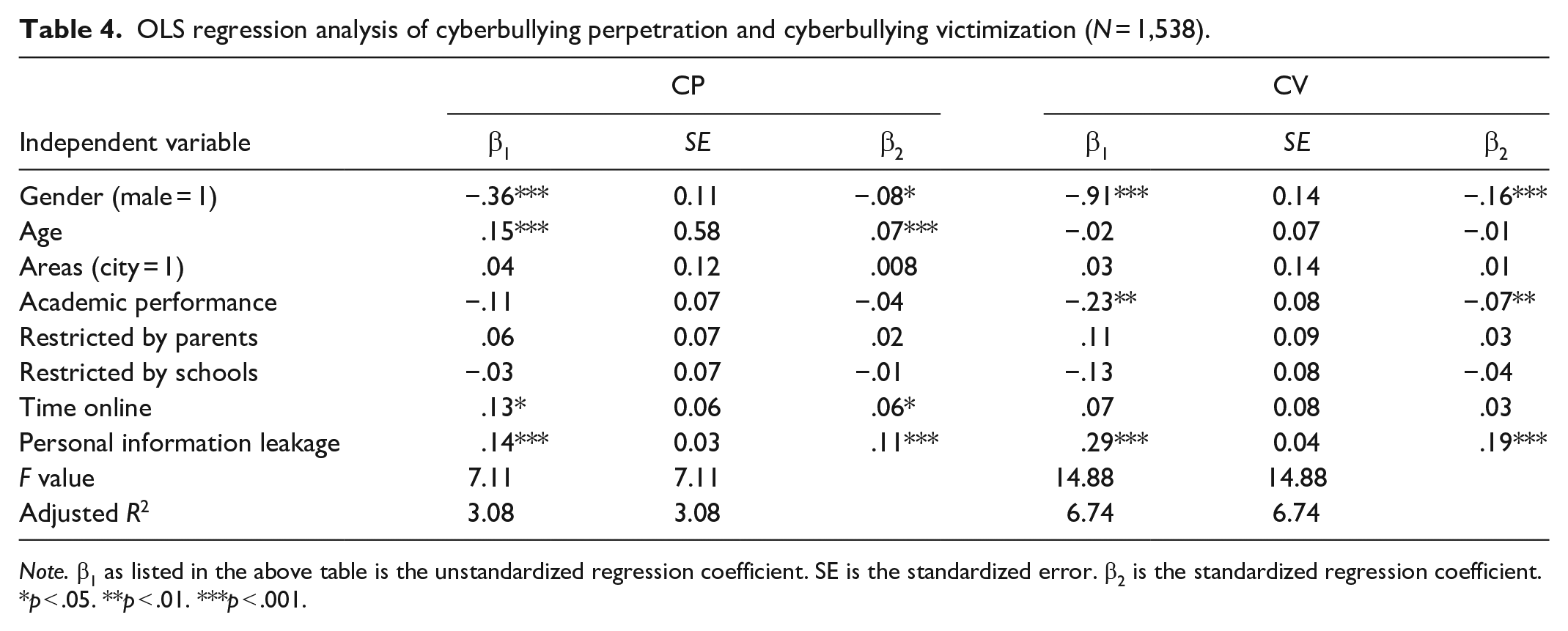
Note. β1 as listed in the above table is the unstandardized regression coefficient. SE is the standardized error. β2 is the standardized regression coefficient.
p < .05. **p < .01. ***p < .001.
Questions 4 and 5 investigated how restrictions on internet access imposed by schools and parents are associated with CP and CV. The regression analysis found that this factor was not significant, meaning that that restricted internet access has no influence on CP and CV (Table 4).
Question 6 examined how the time that teenagers spend on the internet is associate with cyberbullying perpetration and victimization. According to the regression analysis (Table 4), the regression for time online is significantly positive for CP (β1 = .13, p < .05), meaning that more time online is associated with higher perpetration.
Question 7 considered how personal information leakage on the internet is associated with teen cyberbullying perpetration and victimization. The results show that personal information leakage has a significantly positive influence on CP and CV (β1 = .14, p < .001; β1 = .29, p < .001), meaning that more personal information disclosure is associated with higher CP and CV.
Conclusions
Teenage cyberbullying has attracted extensive attention among Chinese policymakers and legislators, but there have been few national empirical studies on cyberbullying. This study consisted of a survey administered to high school students in more than 10 cities and 7 provinces, spanning eastern, central, and western China, to investigate the types and frequencies of cyberbullying that teenagers engage in as perpetrators and are subjected to as victims.
The results support the Social Cognitive Theory framework (Bandura, 1999). It reveals cross-level effects of individual characteristics and media use behaviors on cyberbullying perpetration and victimization. Far more Chinese teenagers (54.6%) report that they have been victimized by cyberbullying than those who say they have engaged in it as a perpetrator (18.1%). Thus, according to self-reporting, teenagers are more likely to be victims than perpetrators in cyberspace. This result broadly agrees with recent findings in China: Li et al. (2019) found that 16.6% of middle school students admitted to being perpetrators, while 31.4% reported that they had been victims of cyberbullying. Interestingly, in our study, the most frequent form of cyberbullying reported by victims (37.6%) was “someone accessed my personal accounts to pirate my personal information,” while this was the least frequent CP behavior reported (3.5%). A possible reason is that teenagers lack the technical skill to pirate others’ personal information. This further implies that internet strangers are more inclined to pirate teenagers’ personal information than peers.
This study also shows that gender, age, and academic performance as individual characteristic factors influence CP and CV. The influence of gender is significant: boys are more likely to be both perpetrators and victims than girls, which occurs less frequently (Calmaestra et al., 2020). This may be attributed to cultural differences. In traditional Chinese culture, girls are raised to be gentle and polite, while boys are encouraged to be active and brave (Zhou et al., 2013). Boys are told to be brave and may lead their aggressive behaviors, while girls are more empathetic than boys generally, and cultural context may protect girls from being victims because boys may consider girls as weaker and more in need of protection (Popovic-Citic et al., 2011). Age has a positive influence on CP: older age is associated with higher perpetration, which may reflect a power asymmetry in cyberspace. Unlike the power asymmetry in traditional bullying, older teenagers who spend more time online may have more proficient internet skills, allowing them to bully others. We also found that better academic performance is associated with a lower risk of being victimized, which may correspond to their specific internet activities. In this survey, participants with higher grades reported spending less time on risky online activities and more time on online course activities. Finally, urban versus rural locations had no significant influence on CP and CV in this study: teenagers from villages and cities experienced a similar rate of perpetrating and being victimized by cyberbullying. Thus the severity and prevalence of cyberbullying are immune to differences in internet access conditions between rural and urban areas.
Consistent with Social Cognitive Theory, this study found that restricting teenagers’ internet time use could reduce CP, and enhancing their privacy on the internet could also prevent CP and CV, which proves that individual media exposures are crucial for protecting teenagers from CP and CV. However, restricted internet access imposed by schools and parents has a limited effect on CP and CV (Elsaesser et al., 2017; Mesch, 2009). Since the internet is the main platform to connect their social world, teenagers fear being deprived of the privilege of using it. Thus they seldom divulge any experiences of cyberbullying to their parents and other adults who may remove their internet privilege (Mishna et al., 2009). In this sense, parents and schools should not merely impose restrictions on internet access, and they need to taking more collaborative strategies such as evaluative mediation and co-use (Elsaesser et al., 2017).
The results of this study have several policy implications. First, teenagers need to be educated about the legal and safety ramifications of their internet activities and cyberbullying. They need to be able to recognize specific types of cyberbullying, such as pirating personal information. Second, schools and parents need to be made aware of how teenagers’ personal characteristics, such as age, gender, and school performance, contribute to the likely that they will become either perpetrators or victims of cyberbullying in order to deliver targeted education to vulnerable teens and take precautionary measures to reduce it, especially among older teenagers and boys. It is especially critical to educate teenagers about the importance of protecting their privacy online. Policymakers need to implement measures to regulate online platforms to protect teens’ personal information.
This study has some limitations. First, it did not take into consideration any specific national conditions or cultural characteristics of China. Future studies can gain further insight into cyberbullying by considering detailed strategies by schools, parents, and internet platforms and measure them more accurately. This survey was only conducted among high school students, mainly ages 15 to 19; thus the results may not be generalizable to other age groups. Finally, this study relied on self-reporting by teenagers; thus the data reflect what participants were willing to reveal about their cyberbullying as perpetrators or their experiences as victims. Participants may have had psychological reasons such as loss of self-esteem or felt social pressures to not be truthful, or they may have feared the loss of anonymity in the school setting where they filled out the survey. Future studies shall combine one-to-one interviews with teens’ expressions on social media.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: Guangzhou Cultivation and Research Base for Youth Talents in Maxism Theory (2019GZJD02).
