Abstract
As previous literature on the effect of controls usage on the outcome of controls (controls effectiveness) are rare, this study intends to use controls framework to explain controls effectiveness as HIS (hotel information system) quality and user satisfaction. The purpose of our study is understanding of the critical role of security controls on qualities perceived by hotel employees and the satisfaction of hotel employees using HIS based on controls framework perspective. The research model was tested using a sample of 583 respondents who have worked with HIS. General controls directly and indirectly contribute to the improvement of the satisfaction of hotel employees through their effects on qualities, while application controls indirectly affect satisfaction. Although general controls affect information and system quality, application controls influence information and service quality. The findings provide insights to the hotel industry by building a basis for designing different level for general and application controls.
Keywords
Introduction
Information security has been one of the growing concerns for most organizations; large organizations detected 28% more security incidents in 2014 compared with the year before (PWC, 2015). Security controls are rather deficient in comparison with resources deployed to prepare for other types of crime due to the lack of available information to evaluate the efficacy of existing preventive measures (Kennedy, 2015; Mugellini, Isenring, & Killias, 2015).
In the hospitality and tourist industry, the extensive commercial usage of World Wide Web and communication technologies has created limitless chances for the use of hotel information system (HIS) for performing business transactions, distributing and sharing business knowledge, and maintaining business relationships. Previous studies suggest that IT internal controls affect firm performance (Benaroch, Chernobai, & Goldstein, 2012; Chapman & Kihn, 2009; Stoel & Muhanna, 2011), and in a similar vein, as HISs are accessed by a larger number of hotel customers and employees than before via the Internet and outside intranets, it makes greater the criticality of security for consumer information, mostly obtained through Internet based sources by the hotel (Kim, Ma, & Kim, 2006). As Internet enables tourism enterprises to extend both their market reach and operational efficiency, security studies driven by the needs of practitioners have focused on the impact of controls and security in the effective diffusion of HIS (Kim et al., 2006).
There are several motivations for this study. First, this study intends to extend the studies on the relationship of controls usage (or factors related to controls) and the outcome of controls (controls effectiveness) in organizations. Our study intends to extend previous studies on the outcome of IS controls. For instance, Lee (2010), Lee and Ahn (2010) suggested the effects of controls on system implementation success such as volume and sophistication. Lee and Lee (2010) showed the influence of informal as well as formal IS controls on system performance. Although these studies relate controls with implementation success or systems performance, they do not explain the effect of controls on IS qualities and user satisfaction. Our study intends to fill this void.
Previous related studies investigate the outcome of security controls such as the effect of proactive investments on security performance (Kwon & Johnson, 2014), the impact of fear has an impact on the behavioral intentions to comply with security procedures to be abided by individuals (Johnston & Warkentin, 2010), training to promote adherence to IS policy (Puhakainen & Siponen, 2010), the establishment of security protection standards or auditing for social welfare (Hui, Hui, & Yue, 2012-2013), information quality trust, which has an effect on compliance with controls (Han, Ada, Sharman, & Rao, 2015), the quality of information security management (Soomro, Shah, & Ahmed, 2016) the performance analysis of cloud data security models (Ramachandran & Chang, 2016), financial records (Roumani, Nwankpa, & Roumani, 2016), or information security system effectiveness (Moon, Choi, & Armstrong, 2018). However, studies on the relationship among controls usage, IS qualities, and user satisfaction are necessary. Our study intends to fill this gap by investigating control effectiveness in terms of the role of controls for HIS qualities and user satisfaction.
Second, previous studies have emphasized both management- and technology-based controls (Moon et al., 2018; Soomro et al., 2016), and to suggest the holistic and balanced controls, this study intends to use a controls framework perspective from control objectives for information related technology (COBIT; ITGI, 2015; ISACA, 2017) 5 and 4.1 by Information Systems Audit and Control Association (ISACA) to suggest general and application controls for HIS. Although previous studies on controls have been centered on the relationship between controls usage (or factors related to controls) with the outcome of controls, and security have begun to pay attention to different effects of different controls (Shah, Peikari, & Yasin, 2014; Silva, Gusmão, Poleto, Silva, & Costa, 2014) the attention toward suggesting differentiated controls according to effectiveness of controls have been less focused on. The study intends to fill this void by suggesting that controls can be classified into general and application controls based on a widely used classification of controls suggested also by COBIT 4.1 (ITGI, 2015). Furthermore, IS success model (DeLone & McLean, 1992, 2003) is used as a theoretical lens to suggest information, system, and service qualities as mediating factors for the effects of control on user satisfaction.
Third, as empirical literature regarding the security controls and quality of hotel systems operation and management perceived by hotel employees are rare and should be further developed (Kim, Lee, & Ham, 2013), our study intends to focus on the security controls as crucial factors for satisfaction of employees who may represent the perceptions of customers. For instance, Berezina, Cobanoglu, Miller, and Kwansa (2012) suggested that hotel operators should continuously pay attention to protect the sensitive data, which is entered from their guests, and that incompetence to do so may result in negative guest perception regarding service quality, consumer satisfaction, and future reservation intentions. Berezina et al. (2012), however, has focused on the effect of security breach not security controls. Furthermore, they did not deal with specific information system’s quality and user satisfaction with the system. Furthermore, while there is a number of studies on measurement of service quality on hotels (Bai, Law, & Wen, 2008) the impact of security controls on quality of HIS perceived by hotel employees and the satisfaction of hotel employees as well as the mediating role of quality have not been studied. Our study is to overcome this void.
In this study, employees are posited to show the satisfaction of users of HIS because including customer relationship management or reservation systems, employees are actively using HIS and can indicate their impression and satisfaction with HIS. Although a hotel intends to be integrated with outside reservation systems of other company, employees usually process work in the front-end reservation systems, and can be knowledgeable with customers’ impressions on HIS as well.
Controls Framework for HIS Security
While security is an important issue in hotel industry, less research has been suggested to show the outcome of HIS controls and which type of controls are necessary. The hotel industry provides an attractive target for hackers due to a generally weak IT security practices adopted by hotels (Haley & Connolly, 2008). Security has been considered a less important issue in hotels business, and some hotels did not elevate security levels (Pizam, 2010). The potential results of an IT security incidents for hoteliers include brand reputation damage, consumer behavior alterations, and financial cost. In general, service quality can be compromised if information security protection was not provided appropriately. The security issues in hotels include managed factors of corporations using security systems (Dhillon & Torkzadeh, 2006), biometric technology for security and its utilization in the lodging business (Jackson, 2009), the role of transaction security for trust and repurchasing intentions (Kim, Lee, & Chung, 2012) and effect of security on system reliability (Kim et al., 2012), the impact of security perceptions on trust and the intention to purchase travel online (Ponte, Carvajal-Trujillo, & Escobar-Rodríguez, 2015) the effect of security on the perception of service quality for backpackers (Brochado, Rita, & Gameiro, 2015). These studies have not provided an integrated model of IS controls and the outcome of controls (IS qualities and user satisfaction).
Especially, Park and Gretzel (2007) suggested an integrated framework of generally adopted success factors for website emerged from the investigation of previous studies and included nine facilitators, that is, fulfillment, personalization, information quality, visual appearance, interactivity, responsiveness, ease of use, security/privacy, and trust. However, Park and Gretzel did not suggest the causal interrelationships among these factors, especially between security and other factors. The establishment of high-tech security is an important factor to consider to keep customers satisfied (Chan & Lam, 2013), and customers’ perceptions that a hotel system perform transactions in a secure way affect consumers’ behavioral intentions to adopt mobile payments (Morosan & DeFranco, 2016). Ponte et al. (2015) examined that the consumers’ perceived security depends on third-party independent seals for assurance, and security and privacy policies. Perceived information quality and perceived security have an impact on trust and the intention to buy travel online. However, they did not investigate the role of perceived security for information quality. Thus, given the review of previous studies on security in hotel literature, the studies on security and on the influence of security on IS qualities are lacking and become necessary in hotel and security literature.
While previous studies on IS controls have been focused on the relationship between controls usage and the outcome of controls, the types of controls have not sufficiently suggested in previous studies because the attention is less directed toward the differentiated controls according to outcome of controls. HIS controls in our study is based on the concepts of organizational controls and controls framework of ISACA (2017), especially COBIT framework, which shows a rigorous model of controls to be followed in business organizations.
Information systems controls, a subtype of organizational controls, may be described as those activities that protect assets, promote data integrity, effectively pursue organizational goals, and efficiently use customer resources (ISACA, 2017). HIS security controls are the policies and procedures devised to offer comprehensive assurance that security goals can be accomplished and that unintended events should be prevented or identified and corrected. For reducing the scope of controls, our study examines security-related controls, an area few previous studies have examined.
Based on general control classification framework, HIS security controls can be classified as general and application controls. This framework is one of the mostly used classification of controls in practice (ESS, 2019; ITGI, 2015; Mendez, 2015; Turban & Volonino, 2012). General controls are described as fundamental controls because they deal with general HIS management, HIS implementation and maintenance, operations management, and security management. General controls become more important as a more holistic approach to emphasize management’s role in management of information security becomes increasingly important (Soomro et al., 2016). General controls comprise procedures and policies that are relevant to many user applications and assist the successful operation of application controls by providing assurance of the continuous appropriate systems operation. Application controls intend to assure that each application system accomplishes security and integrity requirements. Application controls are relevant to certain business applications and transactions. Application controls concern three controls; input controls (transactions captured, properly authorized, accurately recorded), processing controls to check transaction processing to be performed as intended, and output controls for the accuracy of processing outcome.
The COBIT 5 or 4.1 framework (ISACA, 2017; ITGI, 2015) asserts that to accomplish business demands, information must satisfy seven criteria, that is, compliance, efficiency, availability, confidentiality, reliability, effectiveness, and integrity. These qualities are related to information, system, or service qualities of HIS and COBIT 4.1 suggest that control processes ensure to accomplish these criteria indicating HIS controls are having an influence on HIS qualities. Based on these notions suggested by COBIT 4.1, our study suggests that general and applications controls are related to HIS qualities.
Research Model
The current control frameworks of HIS indicate the effect of general and application controls on information, system, and service quality of HIS. The COBIT 4.1 (ITGI, 2015) matches each COBIT process to the information criteria that the process influences, and thus, can offer an auditor with a method of examining specific controls for the impact on information quality. To pursue certain control objectives, the specific systems processes or service quality should be established by an organization (Tuttle & Vandervelde, 2007). Thus, in our article, general and applications controls, which represent one of the control frameworks similarly have a positive impact on information, systems, and service quality which are the critical facilitators of IS use and satisfaction based on IS success model (DeLone & McLean, 1992, 2003).
The concepts and importance of three HIS qualities can be explained as follows. As one of critical HIS qualities to be evaluated, information quality represents the qualities of information which IS create, and is crucial for the success of IS (DeLone & McLean, 2003). De Wulf, Schillewaert, Muylle, and Rangarajan (2006) posited that easiness to understand, recency, and reliability provide an important effect on the attitude toward information. The quality of information is a key characteristic affecting consumer satisfaction and loyalty in social networks (Jaiswal, Niraj, & Venugopal, 2010; Lee & Kim, 2017).
System quality represents measures of system characteristics regarding IS use encompassing security, availability, efficiency, and reliability. The customers’ needs for qualities should be supported by system functions provided for completing user tasks (Stefani & Xenos, 2011). System quality is regarded as capability of IS to create data, and to affect consumer satisfaction (DeLone & McLean, 2003; Lee & Kim, 2017).
Service quality indicates the extent that a user assesses services created by the service provider through the website, and is included as a facilitator of website success (DeLone & McLean, 2003). Service quality realizes that consumers are delivered with efficient, satisfactory, and reliable service and if HIS service cannot realize expectation, it results in negative experience and discontinuing of service usage. The e-service qualities encompass e-commerce design that allows customers to assess their satisfaction regarding business process, reliability that allows customers to assess fulfillment processes, privacy and security that help customers assess their privacy perception, which supports customers check service support (Heim & Field, 2007). Thus, each of these three HIS qualities provides the role of criteria, which HIS controls should accomplish.
The roles of general and application controls for HIS qualities can be explained as follows. For HIS qualities, hotel and tourist organizations can employ general controls to achieve a variety of performance. General (or management) controls through integration of IS is positively associated with flexibility, global transparency, local transparency, and repair of systems process and information characteristics (Chapman & Kihn, 2009). Through general controls, HISs intend to establish a common data set, along with clearly designed business processes. General controls support technical analysis enabling the modular architecture of HIS and the development of a technical control system that may provide the state regarding the inner workings of the business processes it monitors, improving flexibility and repair of process and information transparency.
In a similar vein for HIS qualities, application controls are implemented in a HIS to evaluate the internal application systems, such as a sales system and a production system, which are connected through the Internet to a B2B network. Because integration in HIS is high, minor errors or failures of one subsystem can negatively influence other subsystems. HIS application controls include detective controls and associated contingency planning that prevents errors in one application from affecting the whole system.
COBIT 5 or 4.1 (ISACA, 2017; ITGI, 2015) show that the realization of the following goals is possible using strong internal controls: compliance with regulations and laws, reliability of financial reporting, and efficiency and effectiveness of operations, which are related to information, systems, and service quality in this study. For instance, some of the processes suggested in COBIT 5 are “Manage Quality,” “Manage Service Requests and Incidents,” “Monitor, Evaluate, and Assess Performance and Conformance.” These are all related to information, systems, and service quality of HIS.
Before a company determines to develop business-to-consumer information systems, the systems controls should be prepared to ensure the belief that IS is accurate and safe to consumers and to promote the ability for adjustment and implementation (Lee & Ahn, 2010). The potential impact of security breaches and errors, which contributes to increasing security concerns, should be assessed because it has a negative influence on business performance (Lee & Ahn, 2010). The provision of quality information regarding use of products/service and maintenance, which relates to information quality is enabled by the appropriate use of controls for communication controls, access controls, and system continuity. IS controls and knowledge of IS controls have an effect on performance such as process improvement and work efficiency (Lee & Lee, 2010), which relates to system and service qualities in this study. Berezina et al. (2012) showed that if hotel operators do not protect the confidential data that are gathered from their customers, this exerts a negative influence on guest’s quality perception of service.
Thus, IS controls are intended to be designed for IS qualities, that is, information, system, and service quality, which are the antecedents of other IS success measures (DeLone & McLean, 1992, 2003). Based on the previous notion of controls framework, purpose of controls, and HIS qualities, the general and application controls in HIS can exert an impact on information, systems, and service quality.
The satisfaction of the employees who are users of HIS encompassing intranet and functional systems can be explained using the perspectives of “customers” for HIS. The employees’ satisfaction with HIS can be based on how much they meet customer’s needs for their business processes through HIS. The previous empirical results should be replicated in different groups and the employees’ perspective is often used to assess the IS performance. For instance, Stefanovic, Marjanovic, Delić, Culibrk, and Lalic (2016) have used government employees to assess e-government systems. Hsu, Yen, and Chung (2015) have used employees who use enterprise resource planning (ERP) to investigate the relative criticality of system, information, and service quality for implementation success. Thus, previous studies on hotel customer needs can be used to explain how they can be applied to show the effects on employees satisfaction with HIS.
Prior to the introduction of HIS, the security controls for HIS should be designed to assure the belief that system is accurate and safe and to improve the ability for adjustment and implementation. HIS security-oriented controls have begun to receive attention by those responsible information management and processing in hotels.
Previous studies suggest the customer needs of security, which may affect their satisfaction. Kim et al. (2006) has shown that as Chinese hotel customers become more experienced Internet users, they tend to less depend on hotel brands and price discounts and more depend on information provisions and information security. As HIS becomes more depended upon, integrity and reliability of information are more demanded to increase organizational productivity, indicating the necessity of HIS security controls.
Payment card industry data security standards (PCI DSS) in hotel industry show such issues as communication with external systems, culture of shared log-ins and easy vendor access, numerous systems employed in hotels, poor implementation of high speed Internet access (HSIA), as these issues can result in legal costs, financial cost, bad reputation (Haley & Connolly, 2008). Berezina et al. (2012) posited that there exists a negative influence of information security incidents on consumer satisfaction. Hotel customers’ perceived security positively affects their intentions to adopt mobile payments in hotels (Morosan & DeFranco, 2016).
HIS security controls must perform a wide range of security functions. A consumer’s transaction must be protected from hackers, and the resulting database protected from corruption and physical damage. Security-oriented controls make consumers feel assured that their information is secure and should be used appropriately and ethically. Partner companies are not comfortable if they transmit confidential information over the Internet without ensuring the integrity and confidentiality of the communication networks. The consumers’ perceptions of fairness and control in the exchange affect consumers’ trust and satisfaction (Namasivayam & Guchait, 2013). The consumers’ response to a service interaction emphasizes the role of controls during the service providing (Noone, 2008). Although the installation of safety and security systems cannot be based solely on customer viewpoint, it is necessary to understand how guests perceive security, and security systems allow hoteliers to achieve customer loyalty or satisfaction, enhancing their corporate image and improve business performance (Chan & Lam, 2013). Thus, we suggest the following hypothesis.
In this study, based on recent studies on the qualities of website (Liang, Ho, Li, & Turban, 2011; Lin, Fan, & Chau, 2014), each of HIS qualities has an effect on employees’ satisfaction as follows. Information quality is considered as the output and values of HIS. Information quality includes timeliness, accuracy, relevance, understandability, and efficiency. Measures of information quality are based on user’s opinions of the outputs generated by the IS (DeLone & McLean, 1992). Information quality is a key characteristic affecting consumer satisfaction and loyalty to websites (Jaiswal et al., 2010). Information quality is considered as the quality of contents, and can critically influence consumers’ attitudes and service experience in websites (Hasan & Abuelrub, 2011).
System quality encompasses factors critical to the operational efficiency of the HIS. System quality indicates the operational efficiency of function (Seddon, 1997). System quality is an engineering-oriented construct with measures of performance that include system flexibility, accuracy, turnaround time, currency, response time, reliability, and completeness. In addition, system quality includes technical characteristics such as system availability, reliability, and responsiveness (DeLone & McLean, 1992), and service functions need to meet customers’ requirements in competing tasks (Stefani & Xenos, 2011). From the viewpoint of the users of a system, these factors tend to have a rather immediate impact on their attitudes toward the system. If users find it difficult to interact with a system, for example, they are unlikely to have favorable perceptions about the usefulness of the system as a tool for accomplishing their goals.
Service quality is a broader concept than system quality. It encompasses education and support from the information systems department, provision of information technology, problem-solving ability, and attitudes of personnel. Service quality represents the support and education of user department, provision of IT, and capability in problem resolution (Van Dyke, Pryvutok, & Kappelman, 1999). Kettinger, Park, and Smith (2009) empirically investigated a nomological network that included service value, service quality, consumer satisfaction, and the intention to continuously use service. The ratings provided by users on the attributes of system quality may vary depending on the perceptions about the quality of service. The importance of service quality in hotels is suggested in previous hotel literature. For instance, service guarantees have an effect on perceived quality and perceived risk of consumers (Wu, Liao, Hung, & Ho, 2012). It is necessary to devise further some insights on the determinants on service quality in hotel business.
A good information, system, and service quality allow consumers to adopt a website to overcome their problems. A good website quality may support consumers obtain the greatest potential of website. System quality is related to member satisfaction in online community (Lin, Fan, & Wallace, 2013; Lin et al., 2014). Further information and service quality allow users an easy navigation and efficient interaction using, for example, online chatting and messaging. Thus, information, system, and service quality can assure appropriate technical functions in HIS and can improve user satisfaction. This study posits that information and service quality, which have a strong effect on appropriate technical functions can increase the satisfaction of hotel employees using HIS. HIS can more improve employees’ users commitment, interactions, and satisfaction when employees more greatly experience reliable, easy-to-use, and fast functions and contents.
The effect of HIS controls on user satisfaction can be direct or indirect. The rationale for the indirect effect can be suggested through controls framework of COBIT and IS success model. The processes suggested in COBIT 5 such as “Manage Quality,” “Monitor, Evaluate, and Assess the System of Internal Control,” “Ensure Benefits Delivery” (ISACA, 2017) are all increasing information, systems, and service quality of HIS.
Furthermore, to accomplish business goals, information should abide by specific control criteria, which COBIT 4.1 (ITGI, 2015) relates to as business conditions for information: (a) integrity which represents the information completeness, validity, and accuracy in compliance with business expectations and values; (b) effectiveness which involves information being pertinent and relevant to the business practices and being provided in a usable, consistent, correct, and timely manner; (c) availability which deals with that information is available to be used by business practices. These information requirements pursued by controls represent information, systems, and service qualities. Thus, if HIS controls can have a direct on information, systems, and service qualities and qualities directly influence user satisfaction, HIS controls can have an indirect impact on user satisfaction through their effect on HIS qualities. The research model is shown in Figure 1.

Research model based on controls framework and IS success model for explaining controls effectiveness.
Research Method
Data Collection
The data used in testing the research model was gathered as part of a research activity which was performed regarding HIS implementation in Korea. A field survey was performed to test the significance of hypotheses.
The employees’ satisfaction with HIS can be based on how much HIS meet customer’s needs for their business processes through HIS. The employees’ perspective is often used to assess customer needs and satisfaction. Previous studies on hotel customer needs (Hsu et al., 2015; Stefanovic et al., 2016) can be used to explain how they can be applied to show the effects on employees’ satisfaction with HIS. Thus, this study intended to measure the employees’ perceptions of HIS qualities and satisfaction because employees are users of HIS and mostly understand the performance of HIS in terms of the accomplishment of customer needs.
Given the sensitive nature of data collection of our study regarding security and controls, we selected the target group of respondents systematically following several steps. First, this study selected the target sample as the employees of top first-class hotels (5 star) and top second-class hotels (3 or 4-star) in Korea which have their sophistication in developing strategies for IT security. That is, the sample included the employees processing consumer information in their departments, managers, and supervisors. To compose sample, firstly, 15 top first-class hotels and 12 top second-class hotels are randomly selected. The chosen hotels were kindly requested to show the employees and their departments that were involved with handling customer information via HIS. The hotel group of first and second class is set to be the target hotel group in this study as HIS of the hotels in the group is more sophisticated than those of the other groups.
Second, the questionnaire was mailed to 810 employees of these hotels who were chosen by the contact managers of these hotels, and 618 employees replied. To have the list of appropriate respondents for our study, the manager who is the departmental head was first contacted and his or her suggestion determined the including of employees in our survey.
Third, once the list of respondents was obtained, by interviewing with managers supervising the respondents regarding content validity of questionnaire items, the researchers of the study check whether the employees in the list are appropriate for making response in the questionnaire item and are not subject to potential intentional responses resulted from supervisor’s influence. The employees were further checked whether their HIS can permit them to perceive any security controls and system quality issues incurring while working through HIS.
Table 1 shows descriptive statistics of 618 respondents. 41.2% of respondents are in their 30s. 25.2% of respondents work for 2 to 3 years.
Demographic Statistics of Respondents.

The unit of analysis for our study was each employee in hotels. Of the 810 questionnaires distributed, 618 questionnaires were returned and 583 questionnaires proved usable and were included in a final sample. The response to the survey was encouraged via email and the goals of the study were explicated in the email. 317 employees belong to the hotels of Top First class and 266 employees belong to the hotels of top second class: Some hotels reject to participate because they fear to expose IT weaknesses and sensitive controls.
Measures
This section identifies how the concepts in the research model were operationalized (see appendix). Items for HIS security controls were revised using various sources regarding controls, such as ITGI (2015), ISACA (2017), Davis and Schiller (2011), Moeller (2010) which explicate the traits and techniques of controls and auditing. The measures were chosen according to their importance for accomplishing the goals of our study and special contexts of hotels. The measures were changed, accommodating the implementation phase of HIS. Some measures of controls were not included because hotels are not normally prepared for such measures and that employees are having insufficient knowledge to make their responses. The measures were devised to assess the hotel’s usage extent of controls. This study describes general controls as “the extent to which general hotel business and IT processes are controlled.” General controls are measured using five items. Application controls are defined as “the extent to which each hotel process related to IT is controlled.” The research variables are assessed by 7-point Likert-type scales using the statements to which the respondent greatly agree or disagree.
Application controls are measured using four items. The measurement is based on the respondents’ perception of the state of controls. Each item of a construct indicates the usage level of a control. For instance, items of general controls include: “Audits are performed at regular and irregular intervals”; “Access controls and back-ups protect against hacking, virus attack, and fire.” If respondents greatly agree with the statement (score 6 or 7), the usage level of the controls check is high.
Information quality of HIS is defined as “the quality of the output that the HIS produces.” The measures of systems, information, and service quality are adapted and newly composed based on items from Kettinger et al. (2009). System quality is described as “the operational efficiency of HIS function.” Service quality is described as “the quality of the service which the HIS function provides to users.” Information, systems, and service quality are measured using five, five, and four items, respectively.
User satisfaction represents “the extent of satisfaction of users with the use of the HIS” and is measured using four items. In this study, employees are used to suggest the satisfaction of users of HIS because including reservation systems, employees are on-going active users of HIS and can provide their impression and satisfaction with HIS. While a hotel chooses to cooperate with outside reservation systems with other company, employees exist to work in the front-end reservation systems, and can understand customers’ impressions with HIS as well. The items of user satisfaction are adapted from Kohli, Devaraj, and Mahmood (2004) and Seddon (1997).
Results
The second-order measurement model is chosen as the study intends to measure security controls which have two inherent variables. Then the first-order measurement model is used to investigate the causal structural model. Confirmatory factor analytical procedure implemented in AMOS was utilized to test the measurement model. In Table 2, the composite reliability is having values from 0.806 to 0.928 and shows the reliability of variables.
Results of Confirmatory Factor Analysis.

As convergent validity is indicated by the significance of the estimated parameters of measurements (Anderson & Gerbing, 1988), the significant parameter estimates (factor loadings) of each measurement variable shows that convergent validity of variables is established.
Discriminant validity is established when the square root of average variance extracted of the variables is greater than the correlations among latent variables. All correlations do not exceed the square root of average variance extracted for each inherent variable (Table 3). This presents that discriminant validity of variables is established.
Correlation Analysis of Variables.

To investigate for common method variance (CMV), this study tested the measurement model where all items as the indicators of a factor showing the method effect and re-estimated the model (Malhotra, Kim, & Patil, 2006). The results presented a poor fitness. Thus, it shows that CMV was unlikely a serious problem.
Figure 2 and Table 4 show the test results of the structural equation model where each of HIS security controls (general controls, application controls) directly affect quality (information quality, system quality, service quality) and user satisfaction.
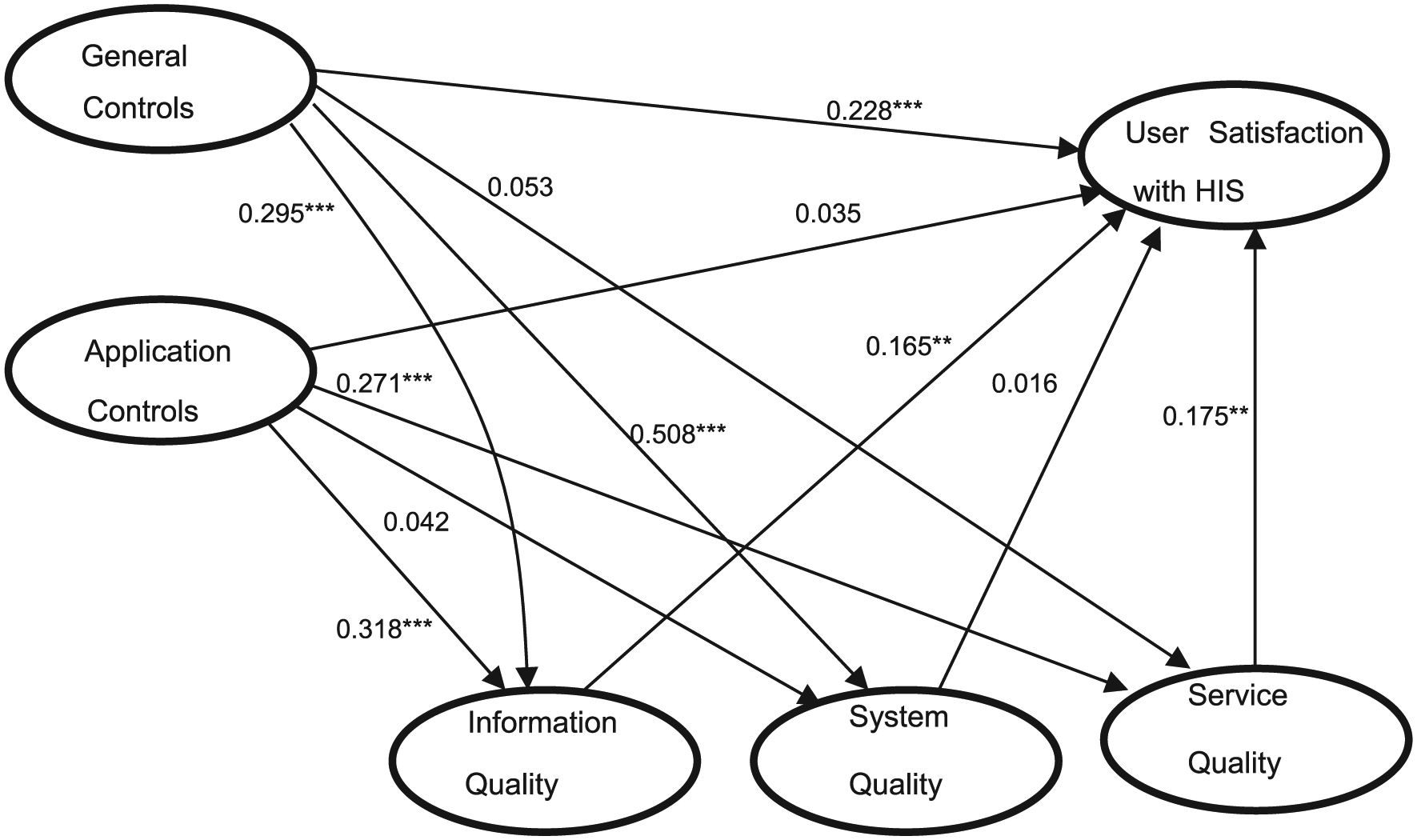
Structural analysis of research model without second-order constructs.
Test Results of Research Model Without Second-Order Constructs.

The fitness indices of the model indicate that the model has high fitness. For example, GFI (goodness of fit index) is 0.95 and is greater than 0.9, which indicates high fitness.
Discussion
The results in Figure 2 present that the effects of security controls on qualities are significant except the impact of general controls on service quality, and the effect of application controls on system quality. This shows that general and application controls have a different impact on information, system and service quality, which is in line with the notion for different role of various controls in organizational contexts (ISACA, 2017; Lee, 2010; Lee & Ahn, 2010; Silva et al., 2014); general controls improve information and system quality while application controls increase information and service quality. Different dimensions of controls may involve different criticality for HIS qualities.
Service quality, which assessed the extent to which HIS provides adequate technological functions to users or HIS is a very user-friendly system may not be directly related to security procedures and policy suggested by general controls. While direct benefits may not derive from security procedures in terms of service improvement through HIS, security management may result in information and system quality because general controls provide high-level procedures and policies to ensure technical HIS qualities such as information and system quality, which supports the notion that management activities and management role of security as well as technology-based controls factors are important for the quality of security management (Moon et al., 2018; Soomro et al., 2016). That is, managerial aspects of information security and various managerial activities are necessary for technical (information and system) quality of HIS.
Given that the respondents of this study are generally less knowledgeable in technical aspects of HIS such as application controls or system quality, application controls, which ensure effective error correction during data input and output, and processing of data according to standard procedures may not appear directly related to system quality which assess the extent to which HIS software is easily updated or HIS data are integrated with other systems. This further leads to insignificant effect of application controls and system quality on user satisfaction. While general controls directly and indirectly affect user satisfaction, applications controls do not directly affect user satisfaction; application controls only indirectly influence user satisfaction. While HIS qualities except system quality affect the satisfaction of hotel employees with HIS, indicating that information and service quality are directly relevant for employees to feel satisfaction, users who are not interacting with inner technical processes of HIS, may consider application controls and system quality less important for their satisfaction. This indicates that employees’ insignificant knowledge on IT results in insignificant effect of application on systems quality and satisfaction and this is in line with the notion that integrated knowledge represented by cross-domain interconnectedness between business and IT is important for information security systems effectiveness (Moon et al., 2018). The less are this coordination and communication between business and IT, the less effective are the application controls of HIS.
This study also tested the alternative model with second-order constructs, which defines HIS security controls and quality as having two (general controls, application controls) and three dimensions (information quality, system quality, service quality), respectively (Figure 3 and Table 5). While the model with second-order constructs is conceptually coherent encompassing the correlated constructs together as belonging to single second-order construct, the structural model without second-order constructs is better in explaining the separate effect of one construct on another. The test results of the alternative model confirm that HIS controls directly and indirectly affect user satisfaction, which supports H2 and H4, and that controls are positively influencing HIS qualities, which supports H1.
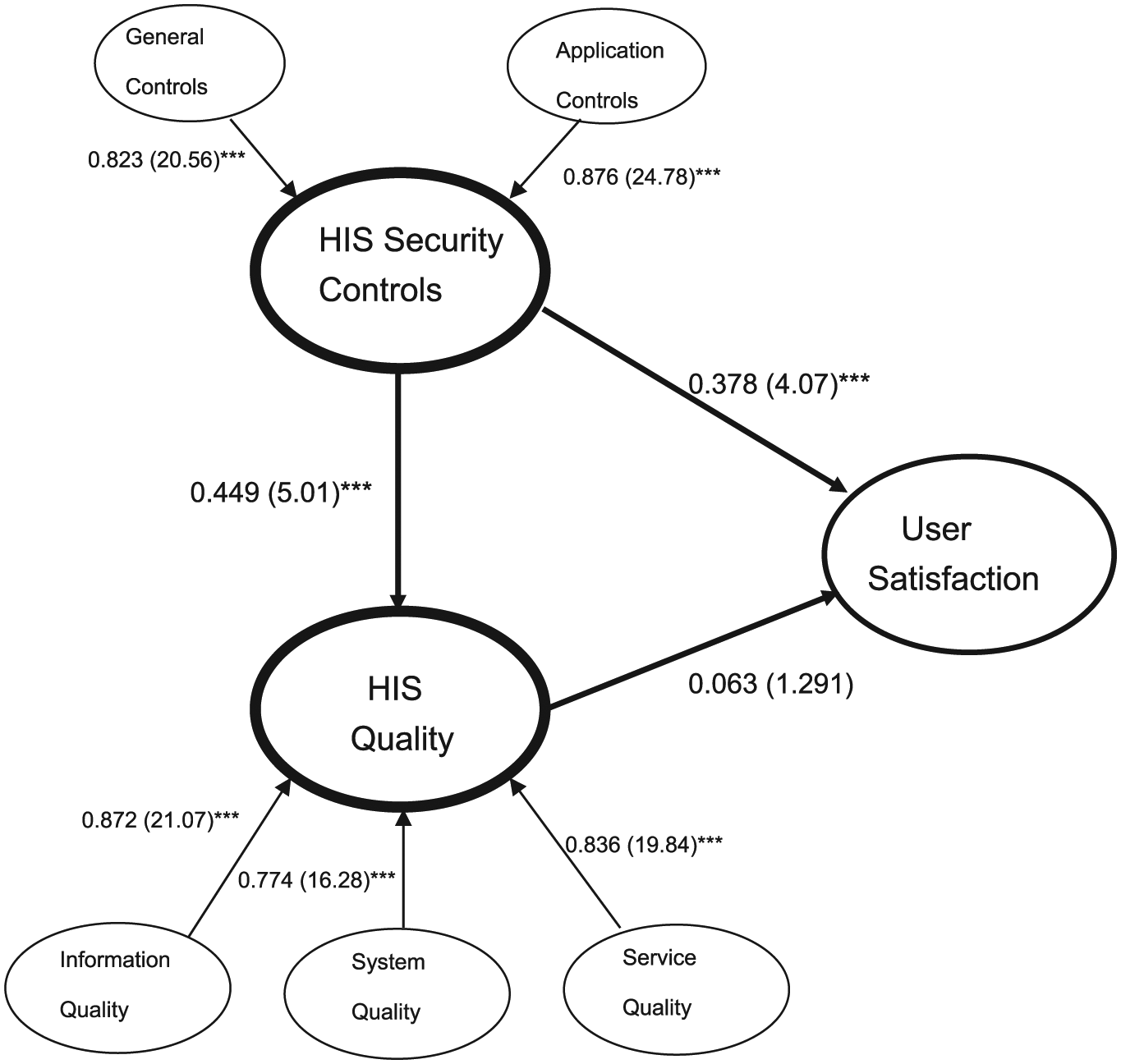
Structural analysis of research model with second-order constructs.
Test Results of Research Model With Second-Order Constructs.

While information and service quality affect satisfaction, HIS qualities turn out to insignificantly affect satisfaction when they are treated as a second-order construct, which rejects H3. This shows that the insignificant effect of system quality on satisfaction leads to the insignificant effect of HIS qualities on satisfaction. Furthermore, insignificant impact of application controls on system quality and satisfaction may lead to the insignificant effect of system quality on satisfaction. This shows that employees’ satisfaction are more affected by general controls and information and service quality than by application controls and system quality. Thus, our study supports the notion of previous studies regarding the different effectiveness of different controls for each parts of information systems such as communication security, security management information and systems, and infrastructure (Silva et al., 2014), security policy or communications and operations management (Yildirim, Akalp, & Aytac, 2011) internally or externally provided assurance for website security (Shah et al., 2014). That is, the outcome of controls effectiveness can be different for each type of controls.
Based on the model with second-order constructs, the study results indicate that security controls directly and indirectly affect the satisfaction of hotel employees through their effect on quality. As the path from controls to satisfaction and from controls to qualities are significant, the indirect effect from controls to satisfaction appears to be existing although the impact of qualities on satisfaction is not significant. General security controls contribute to the information and system quality, and application controls improve information and service quality. This is in line with the previous researches on the hotel’s IT security involved with administrative security and security policy for safeguarding customers’ personal information (O’Connor, 2007). The costs from damage to the environment, deprivation of liberty, the loss of life can be high (Hashim, Murphy, & Law, 2007). The HIS security controls help lower system risks and errors and improve information, systems, and service quality. This will greatly increase the satisfaction of hotel employees.
In the second-order construct model, controls directly and indirectly influence the satisfaction of hotel employees through their effect on quality. In the alternative model without second-order constructs, general controls turn out to significantly affect user satisfaction. This shows that individuals exercise security controls to foster relationships to engender cooperation and elicit individual contributions. Application controls fail to directly affect user satisfaction, showing that while general controls are expected to coordinate specific activities, and to manage individual cooperation and contributions, HIS security application controls may generate more complex work process or loading, and this is one of the most common challenges of security controls (Stallings & Brown, 2015). Many users and even security administrators consider strong security as an impediment to efficient and user-friendly process of an information system or “more is better” mentality for defending computer systems can even create perverse effects in defense of computer systems and have opposite effects on security (Wolff, 2016). This can explain the insignificant effect of application controls on satisfaction.
These results of the study contributed to security literature in hotels by examining security control effectiveness in the context of HIS. This study extends the previous literature on service quality on hotels (e.g., Bai et al. (2008)) by suggesting the impact of security controls on quality of HIS perceived by hotel employees and the satisfaction of hotel employees as well as the mediating role of quality. By focusing on the outcome of security controls for the quality of HIS in hotels, the study extends the result of previous studies on security issues in tourism (Kim et al., 2012). Many customers are dissuaded from doing transactions through website because of fear about theft of confidential personal information and credit card numbers. Furthermore, companies face serious risks if they make decisions, such as the issuance of orders or bills that are based on incorrect data. Deliberate computer abuse such as hacking and disruptions of processing due to natural disasters increase the risks of HIS. Our results shed insight on the contribution of security controls on the quality of HIS and the satisfaction of hotel employees in tourism industry. This may extend the previous studies in hotel management on service quality (e.g., Briggs, Sutherland, and Drummond [2007] as this study addressed the antecedents of the service quality, along with information and systems) of HIS for the hotel industry.
Contribution to Theory
This study provides insights to security researchers by suggesting the results that different controls can have different controls effectiveness, extending the studies on the controls design and security management (Chen, Kataria, & Krishnan, 2011; Fielder, Panaousisb, Malacariac, Hankina, & Smeraldic, 2016; Lee & Ahn, 2011). General and application controls result in different effects on qualities and satisfaction, which extends previous studies on the different effects of different controls (Shah et al., 2014; Silva et al., 2014; Yildirim et al., 2011). Employees may consider less significance in the effect of application controls and system quality on satisfaction than general controls. Users who are not participating in inner technical processes of IS, may place less importance on application controls and system quality for their satisfaction.
This study further provides an extension to the studies on the holistic approach to security, which emphasizes both management and technology for security (Moon et al., 2018; Soomro et al., 2016). Our study suggests general and application controls which represent managerial and technical aspects of controls and have different effects on HIS qualities, respectively, and general controls and not applications have a positive influence on employees’ satisfaction. This further extends previous studies by supporting the notion that management is believed to be responsible for developing a successful information security procedure.
This study intends to examine the security controls as crucial determinants for satisfaction of employees by extending security literature in hospitality such as Berezina et al. (2012), Chan and Lam (2013), Morosan and DeFranco (2016) which investigated the relationship between security and hotel business service equality or satisfaction. While there exist several studies on the impact of security usage (Hui et al., 2012-2013; Lee & Ahn, 2010; Lee & Lee, 2010), the studies on the relationship between controls usage and IS qualities are almost nonexistent. This study extends the previous studies on the outcome of controls, which suggested the effects of security controls on system implementation success (Kwon & Johnson, 2014; Lee, 2010; Lee & Ahn, 2010; Hui et al., 2012-2013). From a security management and planning perspective, this study investigates the usage extent of security procedures for enhancing user satisfaction.
This study contributes to IS control literature by investigating controls effectiveness according to the impact of controls on qualities and user satisfaction by using IS success model (DeLone & McLean, 2003). IS success model provides a theoretical framework for IS success as causally relations among information, system and service quality, and user satisfaction. Information and service qualities (except system quality) turned out to be antecedents of one of the IS success measures, that is, employees’ satisfaction. Thus, information and service qualities (except system quality) are mediating factors for the effects of controls on user satisfaction.
Implications to Practice
Although IT security is not the greatest concern in hotel operations, it may still be considered as one of the crucial parts for the overall hotel experience. Hotels have a large record of sensitive information (service preferences, payment information, personal information, etc.) about customers. This study provides the implications to security practitioners that general and application controls should be designed by employees and that general controls should be provided more to provide intended benefits. General controls for security which appear to directly improve information and system quality and this will more contribute to the improvement of employees’ satisfaction than application controls. While service improvement through HIS may not appear to be derived from security procedures and management, general controls are upper level security management procedures which are more visible to employees than application controls to ensure technical information and system quality. As HIS maintains hotels’ information and utilizes it into customer relationship management (CRM), the assessment of security of HIS is critical for reliability of the hotel. The results of the study emphasize the necessity of checking whether general (application) controls adversely affect information and system quality (information and service quality). General and application controls as well as information, systems, and service quality are completely evaluated as security problems are exacerbated by vulnerabilities that cross from one component (or application, policy, procedure) to another.
Our study intends to enhance the industry’s perception of the criticality of IT security, and thus, strengthening IT security in the hotel industry. IT security for secure online transactions should crucial in a hotel’s website (Law & Hsu, 2006). Korean hoteliers who pay additional attention to security and controls can obtain superior performance in the areas of information, systems, and service quality that ultimately lead to the satisfaction of hotel employees. For example, if a hotel may offer a secure e-commerce transaction channel that brings benefits to its visitors, the visitors will finally bring reward to the company through purchases. The HIS is a competitive weapon in the hotel business and hotels build HIS for the explicit purpose of increasing efficiency and value. We argued that security-related controls greatly affected employees’ satisfaction. Technically, any internal database created from transactions should be utilized in an authorized manner and be protected from outside attackers. When controls are adequately established and information, systems, and service quality is improved, the satisfaction of hotel employees increases and management performance is enhanced.
The findings can show that the more usage of HIS controls will ultimately increase the satisfaction of hotel employees as they can then feel confident that customer information is secure and are used appropriately and ethically. HIS managers should, thus, focus on operating the systems enabling users perceive secure to finish their reservations and to enhance their trust. From a practical perspective, our findings bring benefits to hotel business by offering a basis to maintain measures to enhance security controls as they are directly related to information, systems, and service quality as well as employees’ satisfaction with HIS. Thus, our study offers implications to hotel business to enhance general and application control strategies to assure IT security.
Our results provide the assessment tool which would be greatly useful in helping management assess controls and decide on the outcome of security controls they need. This study uses a controls framework perspective from COBIT 5 and 4.1 (ISACA, 2017) to produce the control framework of general and application controls, and tested the impact of security-oriented controls. In the case of HIS, based on this control framework, partner companies can necessitate an “adequate” level of controls, delineated in service level agreements with the hotel company, before they will send sensitive information related to business transactions. The results of the study provide insight to practitioners as they provide the instrument to measure general and application controls based on adaptation from the measures from ISACA (2017), and suggest the instrument’s use in future assessment for establishing security of HIS.
Conclusion
Recently, it becomes increasingly clear to HIS users that they must balance risk and control in rapidly changing IT environment. Because complete security cannot be attained, experts and management must continually evaluate the different risk factors and their impact on the organization’s information resources. This study investigates the critical effect of security controls on quality perceived by hotel employees and the satisfaction of hotel employees using HIS based on the perspective of controls framework and IS success model. General controls have an influence on information and system quality while application controls exert an effect on information and service quality. General controls directly and indirectly influence the satisfaction of hotel employees through their effects on qualities, while application controls indirectly affect satisfaction. Thus shows that employees’ satisfaction are more influenced by general controls and information and service quality than by application controls and system quality. Our findings provide insights to researchers and practitioners in hotel business by contributing an empirical result on the outcome of security controls and a basis for designing a different level for general and application controls.
Limitations and Future Research Directions
There are several limitations along with future research issues. First, our study used the classification of general and application controls, and while they are one of the most frequently used framework of controls, there can be another control framework to be examined such as prevention, correction, and recovery controls or confidentiality, integrity and availability controls. Future research may also investigate how combinations of specific mechanisms of control can be utilized to achieve the objectives of hotel companies. Second, we did not use full components of IS success model, and it will be better to encompass the individual and organizational impact. However, we did not have data for these data, so it is not possible at this point to include these variables. This study focuses on precursors in IS success, that is, quality and user satisfaction, which affect individual and organizational level. In the future study, the effects of controls on individual and organizational impact can be considered to provide deeper insights on the effect of HIS controls. Other performance variables, such as customer satisfaction, increase in measures of financial performance, can be investigated as possible measures of HIS performance. Third, the future study in the outcome of controls will be necessary in another industry context such as financial or manufacturing, to examine the difference across different industries. Fourth, other factors affecting controls effectiveness can be considered. For instance, trust can become important greater enhancing the security benefits by coping with people issues, process issues, and establishing technology (Gill & Crane, 2015). The role of trust can be examined in sensitive information sharing which likely exists among employees. Fifth, because the sample is collected only from top class hotels, our findings cannot be applied to other class of hotels. Sixth, future study is necessary to examine the difference between satisfaction of customers and satisfaction of users who work inside hotels. Finally, the measures of controls can be further developed using different sources and more in-depth items exploration process.
Footnotes
Appendix
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
