Abstract
International border security operations are diverse and include tasks to facilitate the legitimate movement of goods, thwart crime, maintain safety around borders and safeguard natural resources. All these operations are vital and enduring; however, three operations are currently of exceptional concern to countries around the world: counterterrorism, illegal drug control and illegal migration. The usage of flying ad hoc networks promises new ways for both military and civilian applications, such as border surveillance and remote sensing. Many systems were developed to assist border authorities with more effective surveillance and reliable decision-making support. Such systems vary in terms of the used technology, accuracy, types of events that can be detected and monitoring continuity. This article investigates the technical capabilities of existing and emerging surveillance technologies used for international border monitoring applications. It describes the effectiveness of these systems along with the technological infrastructure required for their implementation. Particular attention has been given to identifying the strengths and weaknesses of these systems and their ability to meet current and future challenges. Our analysis shows that flying ad hoc networks can be used to deliver a rapidly deployable, self-configurable, flexible and relatively small operating cost network for border surveillance.
Keywords
Introduction
Continuous monitoring of international borders has become a necessity in recent years due to immigration crises such as the southern US border, political developments such as the UK Brexit as well as the steady increase in organised crime, terrorist threats and smuggling activities. 1 Any gaps or interruption in monitoring may cause severe damage to the security of a country. However, continuous border surveillance is a challenging and expensive task, and its processes and systems require a high degree of accuracy. This study is of interest to policy makers, monitoring technology experts, security analysts and border guard authorities responsible for establishing and implementing border security systems and trying to understand how to develop measures for the effectiveness of homeland security programmes.
Like border monitoring, other applications such as gas/water pipeline and railway monitoring require high levels of security. These applications share the same underlying linear infrastructure that can run over thousands of kilometres. Any security incident to these applications may result in serious damage to public and national security. A surveillance interruption may also lead to severe financial crises or major security threats. For instance, in late April 2014, a gang of thieves managed to steal thousands of gallons of diesel from Britain’s most important pipeline that runs the 130 miles from Fawley refinery to the West Midlands. 2 A similar incident happened in Nigeria when some community members stole oil from the national oil pipeline and the spiralling cost of oil theft in 2013 was 1 billion pound a month. 3 This not only disturbed the security forces and energy prices, but also had an impact on the environment as it caused significant pollution. Another example is railway disruption, which can lead working nations into massive interruptions when a break in the main railway links is caused. 4
Such incidents highlight the importance of secure surveillance infrastructures that can stop, or even prevent, any disruption that might occur – something that an ideal border solution should also do. These infrastructures are national property and they are costly to deploy. However, such expensive property is the vital backbone of public need in any modern society. Such important systems require high-capability security monitoring systems that allow real-time surveillance at minimum cost. This increases the necessity of developing a complete generic system that can provide an appropriate level of security for many applications including border monitoring.
In developing an integrated system for border monitoring, such a system will adaptively utilise various approaches to surveillance in order to maximise the amount and quality of monitoring information while minimising human resource utilisation. By providing this standardised system, we anticipate promoting interoperability and information integration.
The best border monitoring system should integrate various technologies to achieve high performance and accuracy. Implementing static, mobile and/or ad hoc sensor networks has proven to offer systematic coverage that fills in the gaps in other surveillance systems – their numerous advantages listed in section ‘Requirements of an effective border surveillance system’ warrant this conclusion. It is worth mentioning that wireless sensor network (WSN) systems can utilise various types of sensors to detect different variables such as acoustic, vibration, chemical, environmental changes, weather factors, humidity, flow, position, angle, displacement, distance, speed, light, video. In addition, when deployed beyond enemy lines, WSN technology can raise early alarms to prevent potential threats to a border rather than flagging an incident when it has already happened.
This article assesses the limitations of existing border surveillance systems in relation to the current challenges facing border surveillance systems and emerging security threats. The severe limitations of current surveillance systems motivate the development of a new monitoring system that is inexpensive, suitable for covering large geographical areas and combines the advantages of existing systems by efficiently integrating them to provide continuous surveillance. We present the argument that WSN – whether fixed, mobile, flying, underground, over-ground or even underwater – are particularly well-suited to dealing with modern day border breaches. In particular, flying sensor network (FSN) is a candidate solution to modern and evolving challenges in the field of border surveillance. They are low-cost, often autonomous, devices that can be spatially deployed over harsh environments to monitor physical conditions and even respond to pertinent changes accordingly.
The rest of the paper is organised as follows: Section ‘Understanding the geo-spatial challenges of border surveillance’ reviews the strengths and weaknesses of exiting border monitoring systems. Section ‘Existing border surveillance systems’ discusses the limitation of the current systems. Section ‘The role of FANETs in the future of border surveillance’ presents the design challenges and requirements of a new monitoring system. Section ‘Requirements for a new border surveillance system’ presents the need for a new border monitoring system. Section ‘Conclusion’ concludes the paper and highlights future research avenues.
Requirements of an effective border surveillance system
Analysing current solutions shows that there is no single technology that performs best in all situations and a need for integrating multiple technologies to achieve high level of security. According to Giompapa et al., 5 there are five factors that must be considered when developing a border monitoring system:
There exists a high number and variety of potential threats.
Surveillance operations occur during peace conditions.
Many environmental elements can lead to confusion and cause distraction.
Threat detection and identification can be made more complicated using covert technologies.
The monitored area is typically vast and requires significant physical resources to provide complete coverage.
These five aspects, if considered when creating border solutions, can ensure a better monitoring system and, hence, more secure borders. They also address possible vulnerabilities as well as the identification of the capabilities of the system. The use of stealthy methods for detection and surveillance, for instance WSN technology, makes this task further challenging. The installation of surveillance devices under the ground or in a hidden location can make them more effective, because they are concealed and therefore their operation is more difficult be disrupted. Usually, borders constitute a large geographical area that is a combination of both rough and plain terrain and the used surveillance apparatus should have physical security (e.g. solid), be long-lasting, effective and compatible with other devices already in place. WSNs if added to a border monitoring setup can take the surveillance process to a new level, since they can directly reduce human dependency and work autonomously potentially using artificial intelligence. A fully embedded WSN possesses all the essential components which are needed for successful border monitoring and combats or does not exhibit many of the disadvantages of the systems outlined in Table 1. Al-Fayez and colleagues6–8 study extensively the simulation and deployment methods of such technology.
Summary of the advantages and disadvantages of systems reviewed in this section.
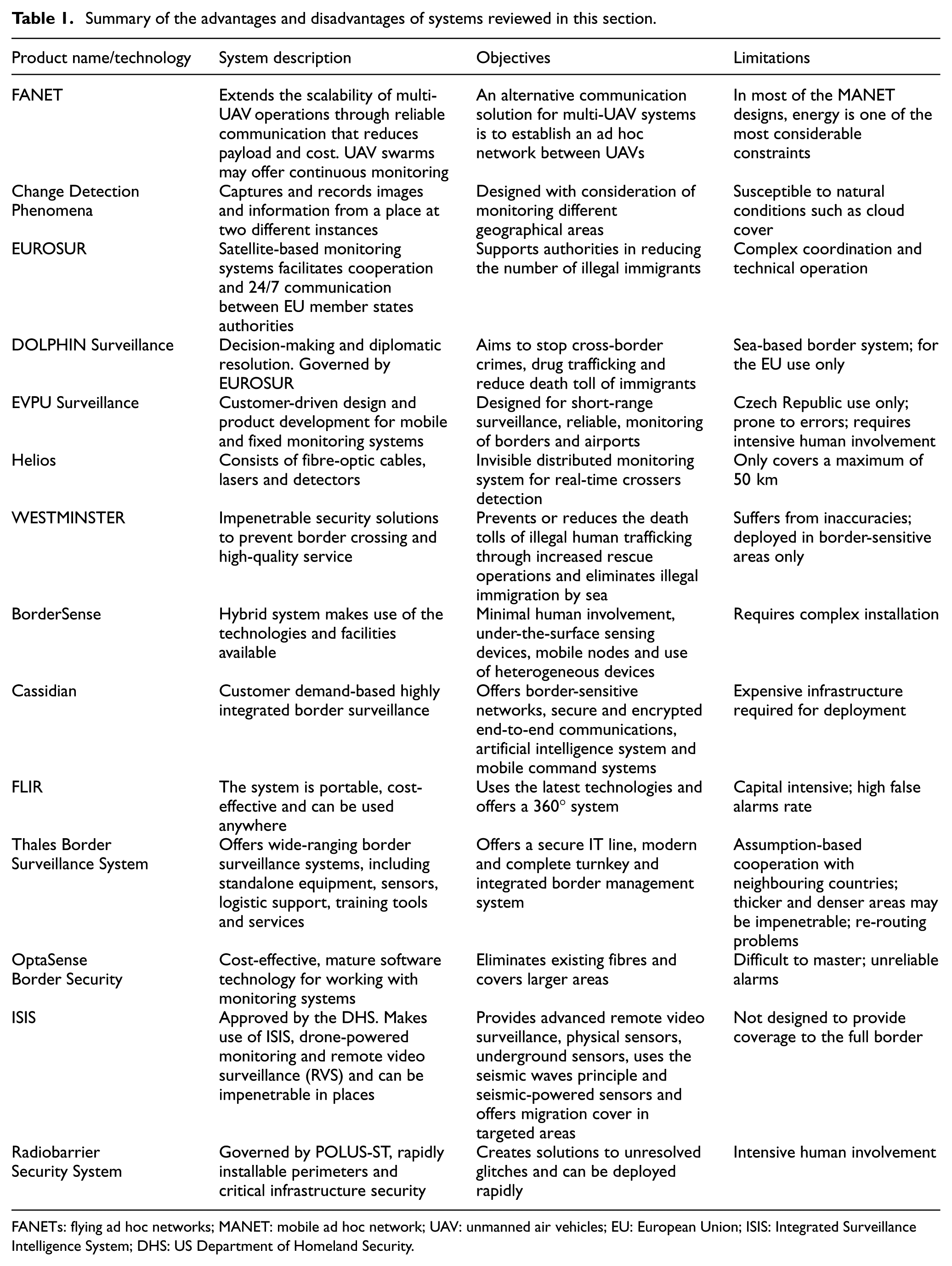
FANETs: flying ad hoc networks; MANET: mobile ad hoc network; UAV: unmanned air vehicles; EU: European Union; ISIS: Integrated Surveillance Intelligence System; DHS: US Department of Homeland Security.
Current systems successful operation is subject to the physical presence of humans, or at least the actual intervention and supervision of humans. They also require huge capital investment in software and hardware resources. Moreover, full coverage of the monitored area is an important aspect of any surveillance system. The coverage must be combined with real-time delivery of information; late data delivery will result in the failure of the surveillance mission as most situations require spontaneous intervention and response. 5
Another major challenge is the line-of-sight factor that curtails functioning and prevents monitoring behind walls or, in fact, or any type of physical obstacle. Many existing systems suffer from this defect, which degrades their performance not just in terms of long-range detection, but also in terms of the expenditure incurred due to repetitive installation of surveillance units. All these factors call for an effective and dynamic surveillance system, which will enable more accurate monitoring that is less dependent on human intervention and is much more effective in terms of range and accuracy.
Understanding the geo-spatial challenges of border surveillance
Recently, the US–Mexico border has been the news headlines over the immigration crises. Similarly, the central Mediterranean route has become a serious concern to the European Union (EU) state members. 9 This route refers to the North Africa flow towards the EU through the Mediterranean Sea. Human traffickers use old fishing boats with no sufficient sailing equipment, fuel and navigation to cross immigrants to Italy or Malta. 10 In 2008 alone, 40,000 emigrant attempted illegal crossing to the EU through this route. This has almost stopped in 2009 after Italian–Libyan agreement. After eruption of civil unrest in 2011 in Libya and Tunisia, the number has increased rapidly reaching more than 64,000 immigrants. The immigrants’ number is increasing every year since and in 2014, 170,000 migrants arrived to Italy. 9
The Eastern EU border is another area of concern to the EU. 11 The most recent statistics show an increase in the number of threats caused by illegal activities in this location.11,12 These activities include illegal crossing, smuggling of tobacco, vehicles, petroleum products and drugs. In one incident alone, 4 million cigarettes were smuggled over the Russian–Finnish border. 12 According to a recent FRONTEX report, 11 in 2014, there is a 24% increase in the number of reported illegal border crossings, compared with 2013. These crossings were conducted between checkpoints. Latest figures show that 45% of detected land crossings of the Eastern Mediterranean side of the EU are at the Bulgarian–Turkish border. 11
The EU’s Ukrainian border is one of several key ‘trouble spots’ allowing illegal crossing to the EU, and, according to the FRONTEX report, 12 it is ‘the central transit and origin of irregular migration at the common borders’. In addition, Ukraine is the main transit area for Afghanistan, Eritrean and Somalian illegal migrants. The EU’s Ukrainian border is made up of about 24,000 km2 of land. This border is geographically unique and extremely complex. A section located between Poland and Ukraine is 535 km long. Figure 1 shows the EU’s Ukrainian border on the map. The Bug River is located at the northern part of the border and is surrounded by plains, but there are mountains and forests found in the South. In this location, traditionally, border monitoring is conducted through manual means, using physical checkpoints or tasking entire military units with monitoring certain sections of the border.

The EU’s border with Ukraine and associated surveillance challenges.
These two examples illustrate the scale and complexity of securing international borders. The geographic span of borders combined with the challenging topographic nature, for example, coastal plains, high mountains, dunes and large deserts, make it infeasible to deploy border guards personal without monitoring coverage gaps. Moreover, the cost of such mission would be excessively high. This led to increasing interest in developing intelligent border monitoring systems to help countries protect their citizens. The best form of border surveillance involves minimal human intervention. 13
Existing border monitoring systems Systems that currently exist range from simple fence and wall systems to very advanced surveillance devices. Intelligent border monitoring systems are desirable because they increase operational efficiency, but, simultaneously, reduce costs. 14 Modern monitoring systems face considerable variable challenges and demands. Such demands include large, busy and complex landscapes. There are also demands for real-time acquisition and interpretation of evolving events, and instantaneous identification of potentially critical situations in all weathers and lighting conditions.
Existing border surveillance systems
This section presents a review of the most recent and prominent commercial as well as experimental international borders monitoring systems. This review limited to land border monitoring systems, where most threats originate. It is important to note that there is a general lack of resources with detailed information about these systems due to their sensitive commercial or military nature. Thus, we present the relevant systems using the best available resources. Nevertheless, despite the lack of literature, we acknowledge and discuss the general problems pertaining to these systems when possible (summarised in Figure 2).

Border security and surveillance challenges, threats and technology roadmap.
Image processing-based surveillance
The first class of border surveillance systems is the image processing-based surveillance. In image processing-based systems, borders are monitored from sky using various technologies including satellites, unmanned air vehicles (UAVs), flying ad hoc networks (FANETs) or monitoring balloons. In general, these systems operate by comparing the current view with a pre-recorded one; any changes are reported to the end users. FANET is essentially an ad hoc network between UAV, is considered as a relatively new network family. Multi-UAV systems pose unique challenges, particularly communication protocols.15,16
One of the popular satellite-based system is called Change Detection Phenomena-based Monitoring (CDPM). 17 CDPM involves capturing and recording images of and information about a place from two different locations. This is commonly done using a satellite that monitors activity in a place constantly and records any difference that has occurred in the monitored environment during a fixed time-slot. This model was used by the EU along the Ukrainian border for preventing any illegal movement across the border. The working principle of this system is that images of an area must be captured at different intervals. For accuracy, the calibrations of instruments and the resolution of imaging devices must be kept constant when taking images across two different periods. Image processing, voice signal threshold and modulation activities must be performed to refine the images and voices that are recorded. 18 This system was designed with the demands of monitoring different geographical areas in mind. One challenge for this system concerns differentiating between changes that may occur due to natural reasons and changes that might occur due to humans crossing the border. This system is also susceptible to natural conditions, such as cloud cover and other weather changes, which can also affect the monitoring effectiveness in terms of miss-rate or false alarms.
EUROSUR is another satellite-based system which is used to monitor the external European borders. 19 This system is designed for surveillance across the Schengen borders using satellite data to track vessels and smugglers movement. The purpose of EUROSUR is to reduce the movement of illegal immigrants across borders by providing the common technical framework required to facilitate cooperation and round-the-clock communication between different member state authorities. The key motivation underpinning the EUROSUR project was to support member states in their efforts to reduce the number of illegal immigrants in Europe. EUROSUR has the same limitations as CDPM plus limitations related to the complexity of technical operations and maintaining coordination.
With the aim of improving decision-making and diplomatic approaches to solving immigration matters emerging from the European maritime border, DOLPHIN was designed. 20 DOLPHIN prevents or reduces the death toll of illegal human trafficking through rescue operations. DOLPHIN is governed by EUROSUR to specifically control any type of immigration activity along the EU maritime borers. 21 Dolphin inherits all the limitations of EUROSUR. As a sea-based border system limits its use to maritime borders only. In addition, the system was designed only for EU maritime use, 20 which hinders international collaboration.
To overcome the problems with satellite surveillance, a CCTV-based border monitoring system was developed in by EVPU Defence. 22 EVPU Defence is known for several projects, such as deploying pans or tilts, which are intended to provide customers with optimal short-range surveillance. EVPU designed both fixed and mobile products. This allows rapid deployment of resources to respond to emerging threats. As a surveillance system, EVPU is intended to achieve the objectives of effective stationary and mobile multi-sensory systems by acting on targets quickly and flexibly. Using new SAMBA technology, SAMBA is a polarisation-difference digital camera based on a fast (up to 10 kHz) polarisation analysis, increases video quality and protects large areas from unwanted intrusion by trespassers and illegal crossers. This system is, unfortunately, tied to the Czech Republic, and, as such, is not open to other nations. In addition, the newly introduced SAMBA technology may be erroneous to some extent. 22 The main drawback of CCTV-based systems, as for other systems presented here, is the intensive human involvement required in operating such system.
Predefined hybrid systems
The second class of the border monitoring systems is the hybrid systems, which integrate multiple technology. The goal of such systems is to achieve effective monitoring under various conditions, for example, dark, cloudy and no line of sight. Technologies used include mobile/fixed CCTV, radar, fibre-optic cables, sensors, satellites and so on. Combining multiple technologies increases the deployment and operational cost of the monitoring systems. Moreover, we observe that most of these systems suffer from the limitations of rigid design, that is, they require major modifications to include new technology. Moreover, technology vendors put little effort in providing interfaces to allow integration with other systems. This is mainly due to the sensitive military nature of the products as well as commercial reasons.
Helios is a distributed acoustic sensor (DAS) system created by a British company called Fotech Solutions. 23 Helios utilises CCTV, fibre-optic cables, lasers and sensors for border monitoring. Originally, it was designed and proposed for surveillance across Southern Arizona’s borders specifically, and in other parts of America as well. Helios is still in development; yet, it has several features that distinguishe it from other existing border surveillance systems including: it minimises the hassle of wires; it is significantly scalable compared to other systems and it offers greater accuracy (up to 1 m) of intruder detection using GPS. However, interfacing with mobile communication and the Internet for remote monitoring is major drawback as most of the borders are out of Internet coverage.
The WESTMINSTER surveillance system 24 was designed to assist in the provision of high-quality services pertaining to fencing and other physical mechanisms for preventing border encroachment. The system features bespoke surveillance and border-cross detection (for land, sea and air). WESTMINSTER offers control along borders made up of diverse terrains, which is ideal for curbing illegal immigration and human trafficking. 24 The system uses solar power to illuminate remote borders and makes use of RADAR, UAVs, SONAR and small craft detection systems to detect illegal crossings. 25 WESTMINSTER is by far the most mature and comprehensive solution in the market. However, it is designed to function only with a set of predefined vendors and technologies, which can lead to a lack of cooperation with other systems. This also could mean that clients may be paying for a technology that is not relevant to their environment. This leads to unjustifiable additional installation costs above those of lesser systems, and human involvement is essential to operate the system, which has implications in terms of training and salaries.
Flexible hybrid systems
Many defence organisations have realised the drawbacks of the predefined hybrid systems and introduced a new class of systems, which we refer to here as the flexible hybrid systems. These systems offer a generic platform that allows the integration of compatible technologies and hardware to provide a continuous monitoring that suits the application requirements.
BorderSense 26 makes use of various existing technologies such as sensors, UAV and monitoring towers. One key advantage of BorderSense is that it requires minimal human involvement – ideal for cutting monitoring cost, and for surveillance of inhospitable terrain. The technologies embedded in the entire system constitute multimedia and sensing devices, under-the-surface sensing devices, and mobile surveillance nodes. The system provides beyond-the-line-of-sight detection, that is, even if a target is covered by material, it can still be properly detected, allowing for tracing and eventual interception of the target. Visibility is considered a point of weakness in many border systems. For this reason, the underground sensing capability of BorderSense is one of its key selling points. Although it incorporates existing technologies, the architecture of BorderSense is slightly different to existing monitoring techniques that are available. A variety of heterogeneous nodes are operationalised in this form of surveillance system, which increases range as well as accuracy, and reduces the degree of false alarms at the same time. Another major advantage of this system is the compatibility with aerial surveillance systems. Since BorderSense is a hybrid system, it has the capacity to easily accept new systems/technologies, which makes it one of the most capable of modern systems. 26 However, BorderSense installation is complex and it was not been thoroughly test in real-world environment.
Cassidian 27 Border Solution was developed by Airbus Defence and Space as a highly integrated border surveillance system. It deploys an artificial intelligence feature that is capable of gathering, aggregating and evaluating data from numerous sources. 28 The system uses encrypted communication subsystems to provide a high level of security. Its design assumes a set of predefined fixed and mobile command centres, which provide users with decision-making tools, helping them to conduct the required operations effectively. 27 However, such capabilities require an expensive infrastructure.
An significant example of hybrid border monitoring systems is the one proposed by FLIR. 29 FLIR, a company specialised in thermal imagining, offers solutions for land border protection, maritime monitoring and airport security. Their systems combine a variety of sensors, such as thermal cameras, radars, and a host of other sensors, in order to achieve the best available degree of detection and surveillance. FLIR operationalises reliable and cost-effective equipment, claiming low false-alarm rates and a low life-cycle, which allows it to survive in all weather conditions. The main advantage of this system is that it limits the number of false alarms experienced in most border security systems. 30 FLIR equipment is very expensive and require a huge capital investment, which makes it unpopular solution. Moreover, the system requires continuous human operation. 29
Thales, another world leader in the defence industry, proposed a hybrid border surveillance system 31 to improve basic border management and control. The system offers an impressive and high-quality service using standalone equipment, such as sensors. Thales offers services to customise its product for logistic support purposes. The product comes with a set of training tools and services to support its adoption. 31 Thales design philosophy was to ensure that present security levels are evaluated and appropriate preparations for the future are made. They tailored current operations to securely adapt to present IT hardware and software. Thales’s solution is designed to address the specific needs and constraints of each border guards entity. 32 Nevertheless, Thales’ border monitoring system has some weaknesses; these include assuming partnership and collaboration between neighbouring countries; and thicker and denser areas of terrain may be impenetrable to the system, hindering operations, as some radars may not re-route information back to the head office.
Along the lines of the forgoing system, OptaSense 33 is a hybrid and cost-effective border monitoring system whose makers claim robust protection. The system features a maturely-set software technology, which can work with monitoring systems such as UAVs. OptaSense is chiefly intended to monitor access routes for a more secure border environment, both along roads and in forests. The system tries to alter the asset deployment schema and offer not just portable, but also effective systems – aiming to improve on the inadequacies of existing systems. 34 Fibre installation and configuration along the border allow the system to work with other assets, such as cameras, and offer a secure means of providing data. The use of various static and mobile surveillance technologies allows OptaSense to monitor large geographic areas and provide utmost security. The major drawback of this system, however, is that it requires deployment along an entire border, which entails a substantial pre-engineering cost. In addition to this, the software platform used requires user training. OptaSense equipment has the reputation of raising a number of false alarms, making it unreliable in the event of a genuine threat to a border. 33
Another hybrid system in the literature is the Integrated Surveillance Intelligence System (ISIS), which is managed by the US Department of Homeland Security (DHS). ISIS delivers the latest technologies, for example, drone-powered monitoring, sensors and Remote Video Surveillance (RVS). Its key goal is to detect and prevent illegal crossing to the United States. 35 Essentially, the objectives of this project are to offer more advanced RVS and physical sensors for detecting movement in the target areas. The system can only monitor a targeted area of interest, however, and cannot provide coverage of the full border. 36
Radiobarrier 37 is one of the surveillance systems introduced by POLUS-ST Ltd for line monitoring of the international border. Radiobarrier makes use of all the latest technological advances. POLUS-ST Ltd works towards developing rapidly installable perimeters and critical infrastructure security. As a result, Radiobarrier is the perfect system in urgent situations, where rapid intervention is needed. Generally, the objective of the company is to find solutions for any unresolved gap on a monitored border. There is, however, a lack of detailed technical information about the Radiobarrier system so it is difficult to judge its actual performance in the field. The obvious limitation of Radiobarrier is the intensive human involvement, which is required from installation right through to decision-making. 37
Current systems solve these problems from different angles depending on their individual applications. The focus is on applications’ perspectives rather than on developing general solutions that suit applications sharing the same deployment requirements. There is a need for new surveillance systems to close the gap between the existing systems and their limitations. New innovative solutions must be developed that can combat the shortcomings summarised in Table 1.
The role of FANETs in the future of border surveillance
This article presents border surveillance technologies, their limitations and benefits. There are many approaches for addressing these applications; however, they are rather expensive, unreliable and difficult to implement. Recent advances in FANETs combined with their increasingly low prices make them an attractive solution to border surveillance. FANETs can be deployed promptly and easily to offer border monitoring. 38 The low cost of UAV allows their deployment in large numbers to provide complete border monitoring coverage. These devices can be equipped by a variety of sensors, including camera, and can support live streaming. UAV can be configured to patrol the borders autonomously using on-board GPS or by communicating with ground devices. They can also be controlled by human operators to respond to incidents. Besides offering sensing capabilities, UAVs can serve as a deterrence tool to prevent criminal activities.
However, FANETs have severe limitations which limits their use as sole permanent solution for border surveillance. Since they are battery powered, UAVs have limited flying time before they require charging. Landing and launching these devices requires skilled personal. In addition, UAVs have limited flying range and require connectivity to relay their data in real-time; this is not always feasible and could be expensive. The on-board UAV sensors have a small effective distance, which requires the UAVs to fly at a low height. The visibility and reachability of these devices put them at the risk of being vandalised or destroyed. Moreover, the small size of these devices and the nature of their fitted sensors may limit their use in bad weather conditions where visibility is poor and environmental conditions are harsh.
FANETs are still in their early development stages and there are currently many technical challenges that must be resolved before they can be widely adopted. For instance, communication remains as one of the most challenging design issues for FANET systems. Moreover, there is multiple FANET design considerations that are still being investigated by the research community, including scalability, latency, adaptability, UAV platform constraints and bandwidth. Finally, there are many security concerns around the use of FANETs such as wide availability of ‘drone guns’ that are capable of shooting down UAVs from 2 km away and block UAVs using the 2.4 and 5.8 GHz frequencies as well as jam GPS signals.
A review of the current state of UAV regulations on the global scale is presented in Berrahal et al. 39 The applied methodological approach includes research assessment of UAV regulations through extensive literature review and a comparative analysis of national regulatory frameworks. It studies the statuses of different regulations since early 2000s, as countries started to establish legal framework to protect its airspace. It was found that regulations often focus on risk management and minimisation of perceived harms such as technical failures, mid-air collisions and resulting damages to people and property on the ground.
The survey in Mohamed et al. 40 discusses the practical implications of UAV applications and opportunities in future smart cities. It investigates application and integration requirements referring to the technical and non-technical issues as well as the legal and regulatory aspects of UAV uses in smart cities. This research highlights that some upgradation is needed in integrating UAVs in smart cities including the design of efficient development models, improved middleware platforms, and better deployment and integration techniques.
In Oubbati et al. 41 the authors conduct a survey on location-based routing protocols designed specifically for FANETs. The study present an in depth taxonomy and classifications of the investigated routing protocols. The authors present an overview of open research and technical challenges to design a new type of interaction between UAVs and existing vehicular ad hoc networks (VANETs) on the ground. This study confirms our research on the need for protocols to handle the high UAV mobility and the low ground sensors density. Other issues that need to be resolved are the communication delay, intermittent connectivity of FANETs and frequent packet losses.
The state of the art of both aerial ad hoc networks (AANETs) and aquatic ad hoc networks (AQNETs) showing the resemblance between these two networks as applicable to the domain of interest. 42 Previous surveys had not covered the various aspects of AANETs and AQNETs with regard to their design and evaluation tools. This research has paved way for transferring knowledge between these two related network technologies.
The exponential advancement in FANET and mobile ad hoc network (MANET) technologies leads to the emergence of new FANET network system that inherits their design and deployment constraints. A detailed comparison between FANET and other ad hoc network types in terms of various network elements has been discussed in Bekmezci et al. 38 The study also discussed the scope of FANET test beds and simulators.
Berrahal et al. 39 propose a hybrid system that uses WSN to detect track trespassers while signing lightweight UAVs (quadcopter) to improve surveillance, detect nodes failures, maintain sensors, track trespassers and video record the scene. Experimental result shows the proposed work was able to identify coverage holes, detect nodes failures, video record scene in real-time and deploy new nodes in appropriate position. It is not clear how the quadcopters can carry and deploy nodes to close coverage gaps due to their small size and limited capabilities. In addition, the limited energy of the quadcopter and the detection of tracking tasks with close exit times could allow some intruders to cross the borderline without being detected by the quadcopter.
In Sarıçiçek and Akkuş, 43 another UAV-based solution for border monitoring is presented. The authors focused on selecting hubs, switching points in communication systems, among the airports and finding the best optimal solution for each hub around Turkey’s borders. The study addresses the single allocation of p-hub median problem to determine the hubs location for UAV, which allows building large-scale FANETs. The authors also present a mathematical model to determine the optimal route for UAVs using a set of criteria including illegal border crossing and the number of illegal border incidents. The contribution in this study unfolds that cost data can be added to hub determination model in future. However, the cost data is not used by the hub determination model. Also, the model utilises a limited set of parameters. Finally, the proposed mathematical models present a trade-off between the cost minimisation and surveillance optimisation.
Another FANET-based system, that is, networks of UAVs, for border protection and intrusion detection was proposed in Kim et al. 44 This research addresses the challenge of UAV collision avoidance and movement strategy. The authors construct a collision-free UAV-reinforced system that minimises the total travel distance of multiple UAVs in a FANET from initial locations. An adjustable potential location to support UAV travel is used to build a heuristic zone-based strategy. The authors analyse the performance of their system using simulation. The simulation was not based on real-life UAV platform and sensor devices. Additionally, the performance evaluation did not consider the energy efficiency of the FANET in harsh environmental conditions with various obstacles and many regions of interest.
The proliferation of unmanned aircraft systems (UASs) paved the way for creating a control strategy towards better coordination of multiple UASs. Rangel and Carrillo 45 examined the implementation of a control strategy for a better correlative UAS system in a real-time scenario. This study investigates the advancement of safety distance, thereby developing a safe unmanned traffic network (UTN) management network to avoid collision. NetLogo, an agent-based programming language, has been efficiently used to evaluate the performance of the proposed system. The researchers introduced the concept of a safety bubble to avoid collision in coordination with the neighbouring agents to secure the system to minimise collision hazard. This research was not evaluated in real-time experiment. The system performance would significantly improve by adding the safety bubble into ground mobile vehicles and enable motion capture system or a GPS. The system performance can be further enhanced by denying access once critical conditions are encountered.
Requirements for a new border surveillance system
Given the sheer length of international borders, there is an increasing demand to make border surveillance systems less reliant on human intervention or supervision. Human intervention takes many forms, from guard’s patrols to command centres personnel. Besides the cost incurred by employing more people and training them to operate border monitoring systems such as FANETs, there are concerns over the efficiency of humans managing such a large-scale mission, for example, corruption, and sometimes their safety. Moreover, humans cannot be deployed in some hostile terrains, for example, deserts. As such, there is a need to establish new surveillance systems that are compatible with and versatile in variable circumstances. Such a system should be modelled in such a way that adjustments can be made without disrupting the operation of the entire system or completely reconfiguring every surveillance device.
Monitoring devices must be multi-hop communication enabled, which supports network scalability. For instance, UAVs have severe resource constraints, which necessitates careful planning of their resources without risking the overall system throughput. Energy consumption is another challenge in the monitoring of remote areas, where nodes cannot be maintained or replaced at regular intervals. FANETs possess many of these key features, which makes them a key element to an effective border surveillance system. They are low-cost, self-powered, self-configuring, autonomous devices equipped with a variety of sensors. FANETs come with methods, tools and techniques to maximise their lifetime and adapt to failures without service interruptions. Moreover, FANETs can be deployed beyond the enemy lines. They can complement data collected by other technologies, for example, satellites or ground sensors.
Deploying FANETs at international borders for surveillance and security has significant advantages over current systems, but it introduces new challenges. An effective remote surveillance system must consider the following major issues towards achieving a successful FANET deployment for border surveillance:
Quality of service, for example, real-time data delivery, error rates.
Power efficiency to extend the lifetime of the system.
Reducing downtime by offering coverage redundancy and self-healing features.
Covert methods to be deployed in harsh environmental conditions and beyond enemy lines.
Their simple architecture limits the need for over-constructor resources.
Efficient communication techniques for relaying data over long distances.
Efficient coverage overlap and coordination protocol to achieve continuous and full monitoring.
Efficient coordination protocol is one of the methods being developed and employed to support border surveillance purposes. Two main challenges must be addressed in the coordination protocols: energy saving and on-time data delivery, maximising node lifespan through applying protocols that allows nodes to switch off their sensors and stop transmitting data in coverage overlap areas. Most existing border monitoring techniques or systems reviewed in section ‘Existing border surveillance systems’ can only claim robustness and reliability in limited scenarios, with limited networks of sensors, video footage, fault tolerance and for a small variety of landscapes.
New deployment strategies specific to FANETs are needed to fill the gaps in existing knowledge and technology. The aim of this deployment method would be to support heterogeneity, scalability and energy efficiency. A network must adopt heterogeneous node deployment that allows for different nodes’ capabilities and functionalities. For instance, some devices sense motion, while others might sense temperatures. This introduces the need for effective data filtering, fusion and analysis methods. Given the disadvantages of current protocols and techniques, a new border security platform is required.
Conclusion
There is no perfect technology; each technology has specific features that work well in certain situations. The authors believe that a carefully designed sensor network system that combines ground and flying devices can reduce risks of illegal activities and enhance border surveillance systems. Combining the features of various surveillance technologies can mitigate their respective drawbacks enabling a hybrid border surveillance system that is not just efficient, but functions according to the needs of the hour. Such a hybrid system can address the wide array of threats as well as adapt to border challenges and conditions, for example, weather and topography.
The success of a large-scale border surveillance system depends on its reliability in terms of monitoring coverage, activity detection accuracy and real-time operation. Such requirements should be met at low hardware and operation costs, under challenging weather and terrain conditions, minimal human intervention and in the presence of frequent hardware failures. The cost of operating and monitoring of mobile technologies such as FANETs can be reduced using artificial intelligence techniques for autonomous navigation and target detection.
While the cost of FANETs and other sensor technologies is in decline, there are several challenges that hinder their wide adoption. Physical security measures are needed to protect nodes from theft, vandalism and natural conditions (e.g. flood). Similarly, such systems must be secured against communication security attacks such as signal jamming. Other open challenges relate to the integration of heterogeneous devices and the fusion of their data to maximise information return and enable collaborative monitoring. There is also an exigent demand for methods to calculate devices placement, density and mobility paths that considers the nature of threat, terrain, weather, border length, geo-political conditions and so on. Therefore, future work is needed on new deployment strategies specific to FANETs to fill the gaps in existing knowledge. These deployment strategies should support heterogeneity, scalability and energy efficiency. They should also support the adoption of heterogeneous nodes and accommodate their different capabilities. For instance, some devices sense motion, while others might sense temperatures. This introduces the need for effective data filtering, fusion and analysis methods. The design and selection of surveillance technologies should be driven by the need for more autonomous operation through advanced data analytics and machine learning.
Footnotes
Acknowledgements
The authors would like to thank Deanship of Scientific Research at Majmaah University for supporting this work under project number nos 1440-66, 1440-72.
Handling Editor: Andrey Koucheryavy
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
