Abstract
Source Location Privacy (SLP) in Wireless Sensor Networks (WSNs) refers to a set of techniques and strategies used to safeguard the anonymity and confidentiality of the locations of sensor nodes (SNs) that are the source of transmitted data within the network. This protection is important in different WSN application areas like environmental monitoring, surveillance, and healthcare systems, where the revelation of the accurate location of SNs can pose security and privacy risks. Therefore, this study presents metaheuristics with sequential assignment routing based false packet forwarding scheme (MSAR-FPFS) for source location privacy protection (SLPP) on WSN. The contributions of the MSAR-FPFS method revolve around enhancing SLP protection in WSNs through the introduction of dual-routing, SAR technique with phantom nodes (PNs), and an optimization algorithm. In the presented MSAR-FPFS method, PNs are used for the rotation of dummy packets using the SAR technique, which helps to prevent the adversary from original data transmission. Next, the MSAR-FPFS technique uses an improved reptile search algorithm (IRSA) for the optimal selection of routes for real packet transmission. Moreover, the IRSA technique computes a fitness function (FF) comprising three parameters namely residual energy (RE), distance to BS (DBS), and node degree (ND). The experimental evaluation of the MSAR-FPFS system was investigated under different factors and the outputs show the promising achievement of the MSAR-FPFS system compared to other existing models.
Keywords
Introduction
The Internet of Things (IoT) is an integral technology of Industry 4.0, in which many smart gadgets or devices are connected to communication networks [1]. The gadgets process the outgoing and incoming data ubiquitously, and they independently interact with each other. Hence, IoT remains at the core of evolving new experiences and applications which include smart homes, smart industries, smart wearable devices, smart agriculture, etc. [2]. The smart gadgets of IoT are playing a significant part in forwarding, gathering, and processing data from source to sink nodes via multi-hop networks [3]. These autonomous and ubiquitous communication outcomes in WSN include innovative challenges in terms of their sustainability. From one perspective, as these devices have limited capabilities such as range, energy supply, computing power, transmission, etc., more and more research works have mainly focused on developing routing techniques that deal with these devices [4]. Instead, such networks are mostly operated and deployed in unattended environments. So, such networks are perhaps prone to several kinds of attacks that may affect the functioning of the network completely or partially, like finding the position of critical network nodes (sink nodes and SNs) [5]. Securing the position of the critical node in WSN becomes a crucial task that should be handled on various fronts.
Protecting source location privacy (SLP) has been gaining more significance in various application fields, specifically in security-critical circumstances [6]. The core ideology is to delay the hacker in finding source locations with the use of SLP routing protocols. In a non-SLP-protected network, a feeble aggressor, for example, a dispersed eavesdropping invader may backtrack along the message path via the network to capture the asset and identify the source location [7]. Thus, to overcome this SLP issue, different classes of SLP-aware routing techniques were devised. The phantom routing was devised for safeguarding the SLP by making some changes in the flooding routing protocol that contains a flooding and initial directed random walk. Even though the random walk-related techniques defend the SLP in theory [8], it is met with the problem of link failure and the message could not be sent to the sink (low data delivery) successfully. The method of fake sources is put on a sensor node (SN) in the network since fake sources transfer fake messages, so an opponent could not able to find which is the real one [9]. These class methods can protect the SLP effectively costing higher energy utilization of SN. Another method in delay-tolerant networks adopted the messages delay method to reach near-optimum SLP [10], costing delivery latency. Hence, many existing routing protocols have incurred high overheads (spatial or temporal) to offer SLP.
This study focuses on the design of metaheuristics with a sequential assignment routing-based false packet forwarding scheme (MSAR-FPFS) for source location privacy protection (SLPP) on WSN. The presented MSAR-FPFS model performs false packet and true packet forwarding via two separate routes to accomplish SLPP. In addition, the presented MSAR-FPFS model uses the SAR technique for false packet forwarding by phantom nodes (PNs). Furthermore, the MSAR-FPFS technique uses an improved reptile search algorithm (IRSA) for the optimal selection of routes for real packet transmission. The performance validation of the MSAR-FPFS technique is investigated under different factors. In short, the key contributions of the study are summarized as follows. Develop an MSAR-FPFS model which comprises a dual-route forwarding mechanism, where false packets and true packets are forwarded separately. This innovative approach enhances source location privacy protection by introducing confusion for potential adversaries. Employ the SAR approach, utilizing phantom nodes (PNs) to facilitate the forwarding of false packets. This technique plays a crucial role in obfuscating the origin of genuine data transmission. Design an optimal Route Selection with IRSA for the optimal selection of routes for real packet transmission. By considering factors such as residual energy (RE), distance to the base station (DBS), and node degree (ND), the algorithm ensures efficient and effective data routing.
The rest of the paper is organized as follows. Section 2 provides the related works and section 3 offers the system model. Next, section 4 discusses the proposed model. Then, section 5 gives the result analysis and section 6 concludes the paper.
Related Works
Shukla et al. [11] present an innovative technique called SLP-RRRCT to guarantee SN location privacy through the SLPP method by randomized ring routing and confounding broadcast. The SLP-RRRCT can be benefitted from random routing including confusing transmission by making a distraction of the adversary backtracking procedure. As soon as packets were sent to the base station (BS) by neighbour grid-based ring routing once the random routing phase expired. In [12], a Jellyfish Dynamic Routing Protocol (JDRP) for conserving congestion avoidance and position confidentiality by having minimum delay guaranteed was devised. The whole sensor field can be classified as various subdivisions with this routing approach and all subdivisions opt for a targeted zone by calculating its communication distance. The dynamic routing protocol contains a virtual ring named a radial line and bell nodes termed tentacle nodes use a lot of nodes to build the network.
In [13], three source privacy protection techniques depend on clustering techniques for protecting contextual privacy. Such techniques are a hybrid method, dynamic tree and shortest path methods. Remarkably, to split the network into various square clusters, a grid-based clustering method was implemented. Zhou and Shan [14] modelled a new method based on a random walk called the multi-branch SLPP approach. This technique masks the position of real SNs by setting many proxy sources. Furthermore, the proxy source was selective arbitrarily, thwarting attackers from gaining a position-associated dataset of real SN.
In [15], a protection structure related to sector phantom routing (PSSPR) routing to solve SLP problems. The authors used the coordinates of centre node
In [17], the authors proposed a probabilistic SLP (PSLP) protection method for WSN and focused on the SLP issue in WSN. To predict the state of the source, a robust adversary has used a hidden Markov model (HMM). To deal with this type of adversary, fake sources and PNs were accountable for mimicking the source behaviour employed for diversifying the routing path. In [18], a technique that depends on the cloud utilizing multi-sinks (CPSLP) was modelled for solving the problem of SLP. The authors modelled a technique that changes packet destination arbitrarily in all transmissions. As well, many sinks were implemented to create several routing paths. The outline of the intermediate node presents the routing path more flexible and random.
System Model
Network model
A standard Panda-Hunter method is used to study the security of SLP in this paper. Usually, pandas are supposed to inhabit a surveillance zone with a considerable amount of uniformly and randomly distributed SNs [15]. The SN becomes the SN once the panda is detected and frequently stated monitored messages to sink nodes in a multi-hop manner. The hunter is capable of acquiring the immediate place of SNs in the way of a backtrack packet by considering the communication signal. Once the hunter entered the visible region of the source position, the exposed source position. The following assumptions we make for the network: 1) All SNs in the network are deployed uniformly and randomly in the sensory region. 2) The sink node was considered the last target of the data packet and remained in the whole network centre. After deployment, the position of every SN remains the same. 3) Any two SNs in the network communicate via more than one hop. Furthermore, every SN has similar features that imply they have cache memory, similar computation capability, and initial energy.
Attack model
Let us patient attacker mode with smaller network visibility in the standard SLP protection scenario. The adversary only can eavesdrop on any data for the packet in the sensor network and cannot interfere with the normal operation of sensory networks. According to a certain routing protocol, the information monitored by the sources is often transferred to the sink destination node. Thus, under a normal scenario, once the attacker is primarily located at the sink node, then it guarantees to effectively capture every individual packet. The adversary is an illegitimate attacker based on huge profits, viz., equipped with effective tools to eavesdrop on some data in the source. Once the aggressor overhears the novel message, it measures the arriving angle and the signal strength which is received to recognize the immediate transmitter node; it won’t have some powerful effect on the network. Afterwards, the attacker implements passive attacks by initiating back tracing packet path by moving to the prior nodes near the source till the SN is reached.
The Proposed Method
In this article, we have developed a novel MSAR-FPFS approach to achieve SLPP on the WSN. The presented MSAR-FPFS technique follows a two-stage process: false packet forwarding and real packet forwarding. Initially, the MSAR-FPFS technique enables the PNs to forward false packets in the WSN using the routes discovered by the SAR technique. At the next stage, the real packets are forwarded by the IRSA technique to accomplish privacy-preserving data transmission in the network. At the same time, the IRSA technique computes an FF comprising three parameters they are ND, RE, and DBS. Figure 1 illustrates the overall procedure of the MSAR-FPFS system.
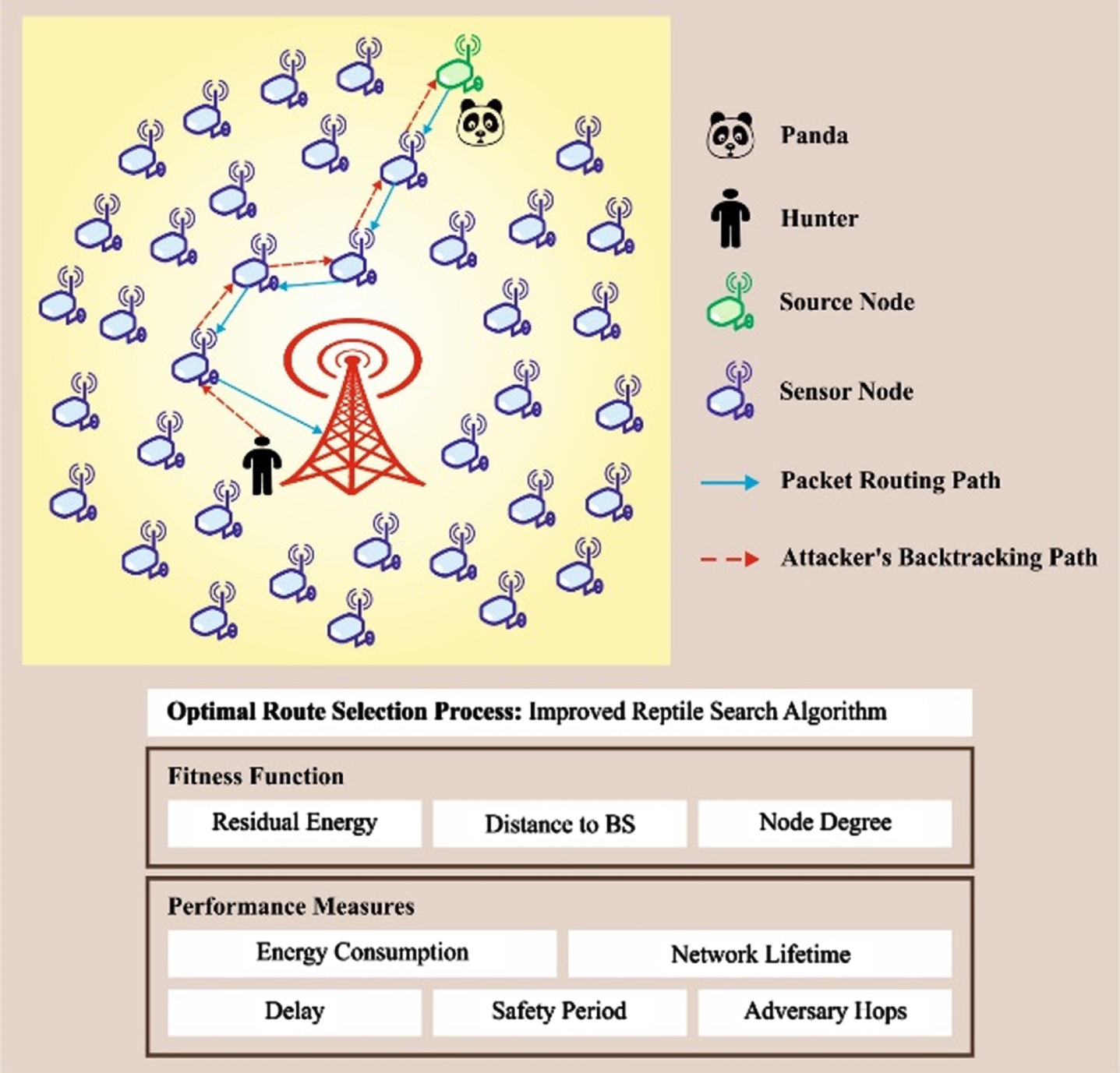
Overall procedure of MSAR-FPFS approach.
In this work, the false packets can be forwarded by the PNs using the SAR technique to BS. PN has been placed on every corner grid of the network [19]. Also, the source of fake data packets from PN can be rotated in a round-robin manner for transmitting the original data packets in the SNs to BS. The aggressor believes that the SN continuously changes its position. At last, the original data packets were transferred at the BS through neighbour gird-based ring routing. It is shown that the distance and count of hops from SNs to BS are different for all the routing data packets, and also all data packets from SNs to the BS follow a random path.
In the MSAR-FPFS approach, the adversary might be misled by the stimulated packet communication technique through the PNs. Once the adversary has received the PN’s dummy packet and backtracked the routing path, the SN’s safety hours can be improved. The fake packet communication from the PN in a round-robin manner might increase the privacy of SNs and generate a dilemma in the aggressor’s mind regarding the movement of SNs. In the MSAR-FPFS method, the stimulated packet communication technique is used, however, the count of hops in stimulated packet routing was constrained. Therefore, the presented technique raised the privacy of SNs and depleted non-hot spot area energy.
The SAR technique constructs various trees, where the root of every tree is a single-hop neighbour of the sink. Every tree grows outwards from the sink and ignores nodes having higher delay or lower throughput. Most of the node belongs to multiple trees at the end of the procedure. The tree rooted at A & B, the single-hop neighbour of the sink, is demonstrated. Node C belongs to these two trees, and correspondingly has path lengths of 3 & 5, to the sink, using the two trees. Every SN records the two parameters regarded every path through it: the additive quality of services (QoS) metrics like delay and the accessible energy resource on the path. This enables the node to select a single path from among multiple relays for its data to sink. The SAR technique selects a path with higher assessed energy sources, and provision is made for accommodating the packet of various priorities. A weighted QoS metric handles prioritized packet that is calculated by the product of delay and priority level. The routing makes sure that the similar weight QoS metric can be preserved. Therefore, low priority packet uses the path of high delay, and high priority packet takes low delay path. For instance, if node
Design of IRSA-based Real Packet Forwarding
The IRSA technique computes a FF comprising three parameters namely RE, DBS, and ND. The hunting and the encircling stages are the two different phases of RSA [20]. The RSA shifts among the hunting search phase and the encircling phase and the switching among various phases can be done by separating the iteration count into four diverse segments. RSA commences with an initially generated set of candidate solutions stochastically utilizing Equation (1):
χ
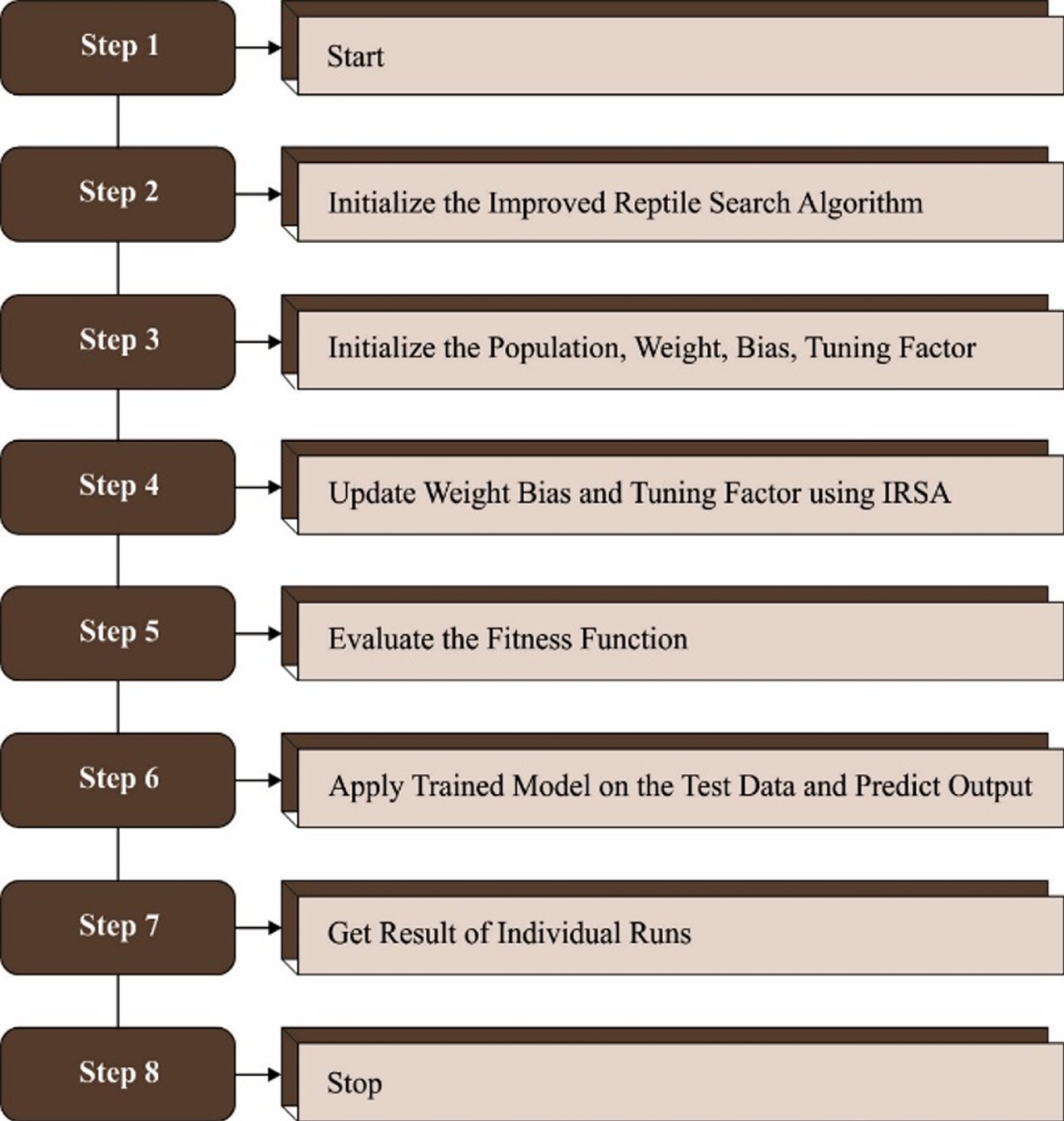
Steps involved in IRSA.
The encircling phase was an exploration of the high-density area. High walking and belly walking were the two phases of the encircling stage based on the movements of the crocodile which plays a major role. This movement helps to discover a wide search space however it doesn’t help to catch the prey.
Let
In Equation (4), β indicates the sensitivity parameter, and it defines exploration accuracy. Another intention of the
In Equation (5),
In Equation (6),
In Equation (7),
In resemblance to the encircling stage, the hunting stage consists of different policies like hunting cooperation and coordination. For the exploitation phase, Equations (9) and (10) are used:
Where
The RSA is a recently established optimizer method that could effectively resolve different optimization problems. However, the RSA possess certain shortcomings while resolving high dimensional nonconvex optimization problems like local minima trapping, slower convergence speed and high computational complexity. Thus, certain modifications are proposed to the original RSA technique to overcome these issues. To avoid trapping local minima it needs the solution candidate for widely exploring the search space. Thus, to improve exploration, a sine operator was added in the RSA technique’s higher walking phase. These adjustments have been stimulated by the dynamic exploration method in the sine cosine model. The sine operator offers a global exploration ability. In IRSA, with the sine operator, Equation (2) was replaced with the subsequent formula.
In Equation (11),
In Equation (12),
From the expression,
Equation (16), ⊕ denotes the entry-wise multiplication, and
Based on the following parameters, the FF can be derived.
RE: The objective in mapping every cluster head (CH) to the Next-Hop node (NHN) based on the remaining energy of NHN [21]. A CH node chooses a node amongst potential NHN so that it has additional RE when compared to others.
Objective 1:
DBS: The objective in mapping all CH to NHN is based on the distance between NHN and BS. A CH node chooses CH amongst potential NHN so that it has reduced distance between the BS and other potential nodes.
ND: Each CH mapping to the NHNs is based on the ND of the NHNs. A CH is assigned to the NHN evaluated by the minimum ND.
In Equation (19), a weighted combination method is implemented for lessening the objective as this doesn’t contradict one another. Hence, the following FF is implemented:
Where,
In this segment, the investigational validation of the MSAR-FPFS technique is investigated in detail. The proposed MSAR-FPFS technique is simulated by utilizing the MATLAB tool. Table 1 defines the details of parameter settings. A detailed comparison study is made with existing models [19, 23] such as baseline, source location protection protocol based on dynamic routing (SLPDR) [22], source location privacy protection scheme based on ring-loop routing (SLPRR) [23], and source location privacy protection scheme based on random rings and limited hop fake packet routing scheme (SLP-RRFPR) [19] techniques. In this work, the first-order radio energy model is used to analyze the energy consumption [24].
Parameter settings
Parameter settings
Table 2 and Figs. 3-4 illustrates the comparative analysis of the consumed energy in the data receiving and forwarding method from the SN to BS. The distance between an SN, BS, and communication radius was different for analyzing the effect of energy consumption (ECON). Figures 3 and 4 demonstrate that flooding-based systems: probabilistic, phantom, and baseline utilize major energy because of packet communication in all the SNs from the network. The SLPDR and SLPRR have depleted the minimal energy in every comparative protocol. The presented SLP-RRFPR has depleted somewhat a little energy compared to the SLPDR and SLPRR approaches. During the presented method, it exploits the dummy packet communication with the confounding communication and with the PNs to make a distraction for the attacker’s backtracking procedures. Besides, the dummy packet communication’s count is superior to the recent algorithms. However the dummy packets were forwarded in the SNs of the hot spot field, and the SN privacy was enhanced. Thus, a further ECON is suitable. It is noted from the outcomes that once the distance between SN and BS was augmented, the energy exhaustion was enhanced. However, the ECON was decreased to enhance the communication radius because of some hops needed in the SN to BS.
ECON analysis of MSAR-FPFS approach with other systems
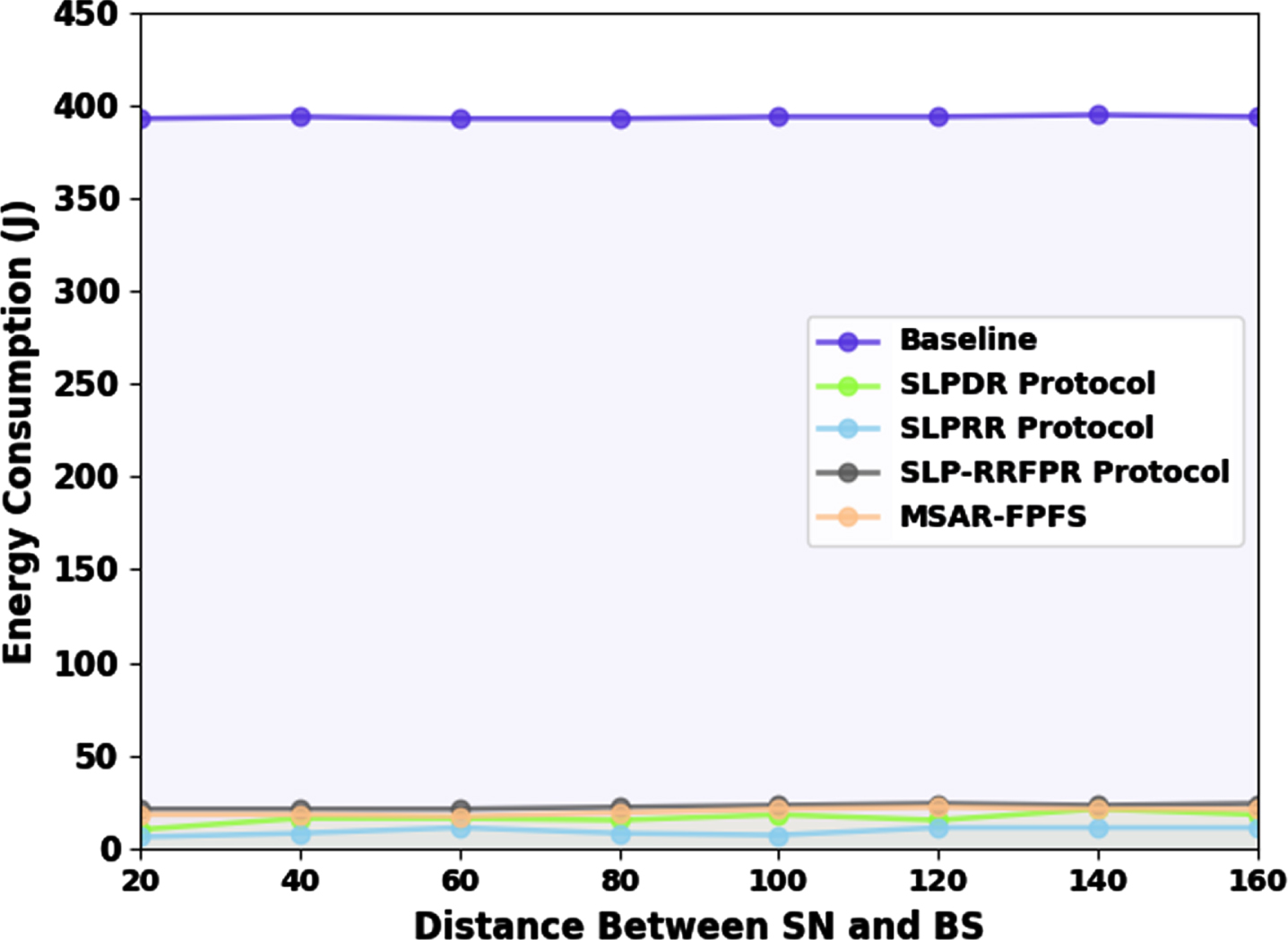
ECON analysis of MSAR-FPFS approach under varying distances between SN and BS.
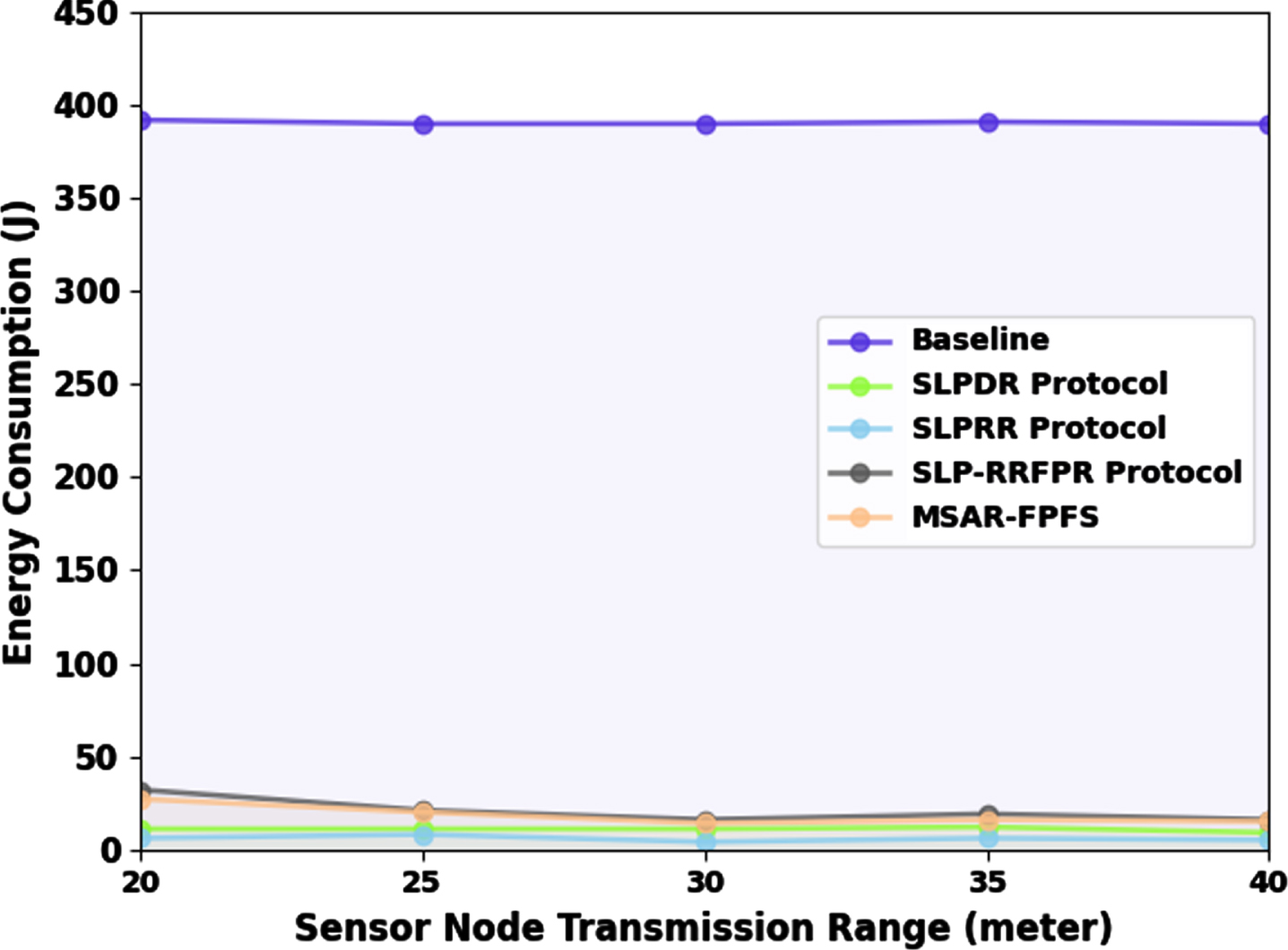
ECON analysis of MSAR-FPFS approach under varying SNTR.
In Table 3, a detailed network lifetime (NLT) investigation of the MSAR-FPFS technique with recent models is demonstrated [19]. Figure 5 represents the NLT assessment of the MSAR-FPFS technique under varying distances between SN and BS. The results deliberated that the MSAR-FPFS technique reaches higher values of NLT under all aspects. With a distance of 20 m, the MSAR-FPFS technique gains an increasing NLT of 1623 rounds while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques obtain decreasing NLT of 1136, 371, 364, and 1590 rounds respectively. Eventually, with a distance of 160 m, the MSAR-FPFS algorithm reaches a higher NLT of 1541 rounds while the baseline, SLPDR, SLPRR, and SLP-RRFPR systems gain lesser NLT of 1136, 492, 436, and 1214 rounds correspondingly.
NLT analysis of MSAR-FPFS approach with other systems
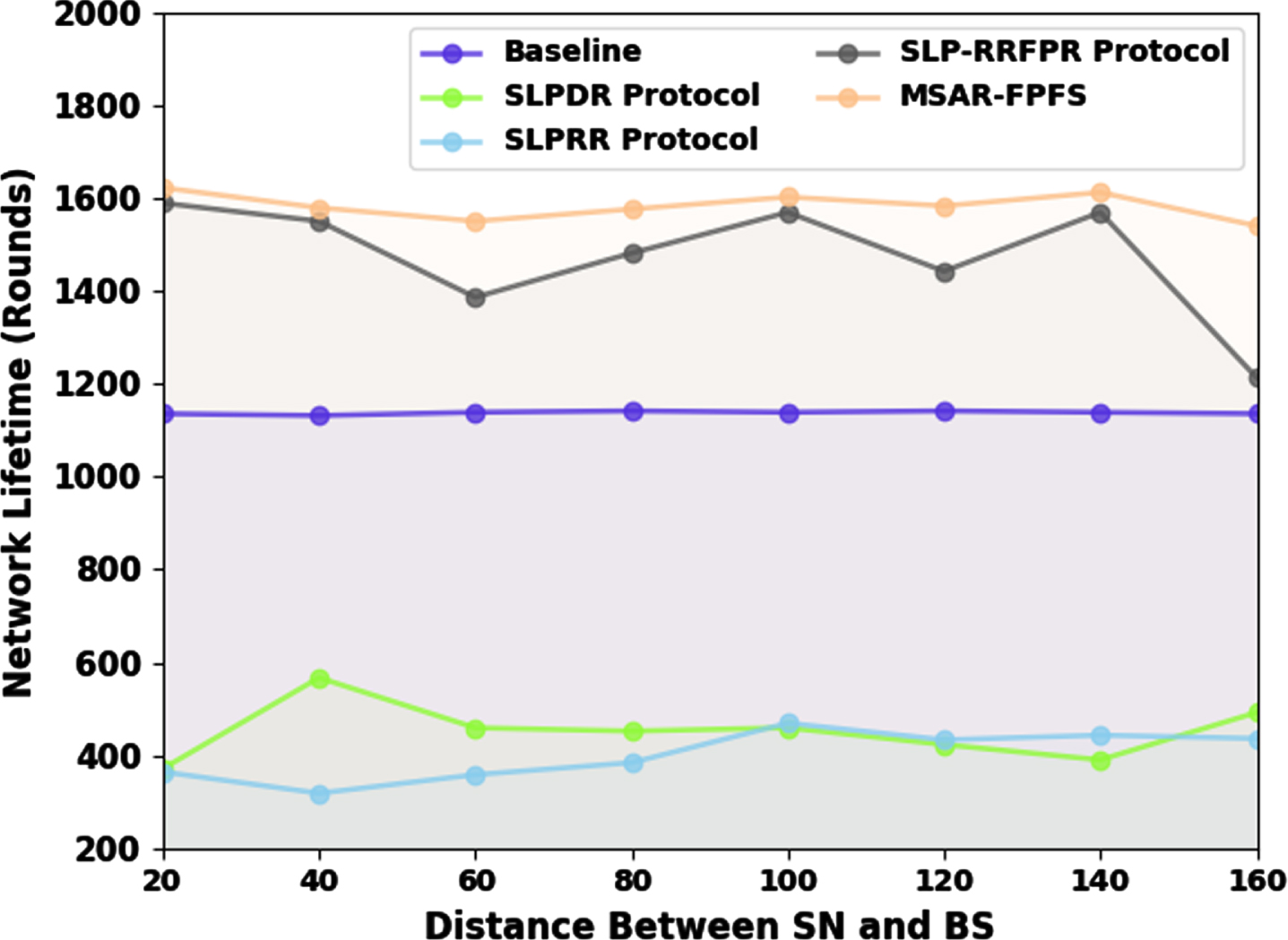
NLT analysis of MSAR-FPFS approach under varying distances between SN and BS.
Figure 6 signifies the NLT analysis of the MSAR-FPFS system under varying SN transmission ranges (SNTR). The outcomes deliberated that the MSAR-FPFS method reaches greater values of NLT under all aspects. With SNTR of 20 m, the MSAR-FPFS technique achieves a maximum NLT of 1772 rounds while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques obtain reduced NLT of 1207, 430, 403, and 1647 rounds correspondingly. Finally, with SNTR of 40 m, the MSAR-FPFS methodology reaches maximal NLT of 1620 rounds while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques attain minimal NLT of 1077, 267, 218, and 1419 rounds respectively.
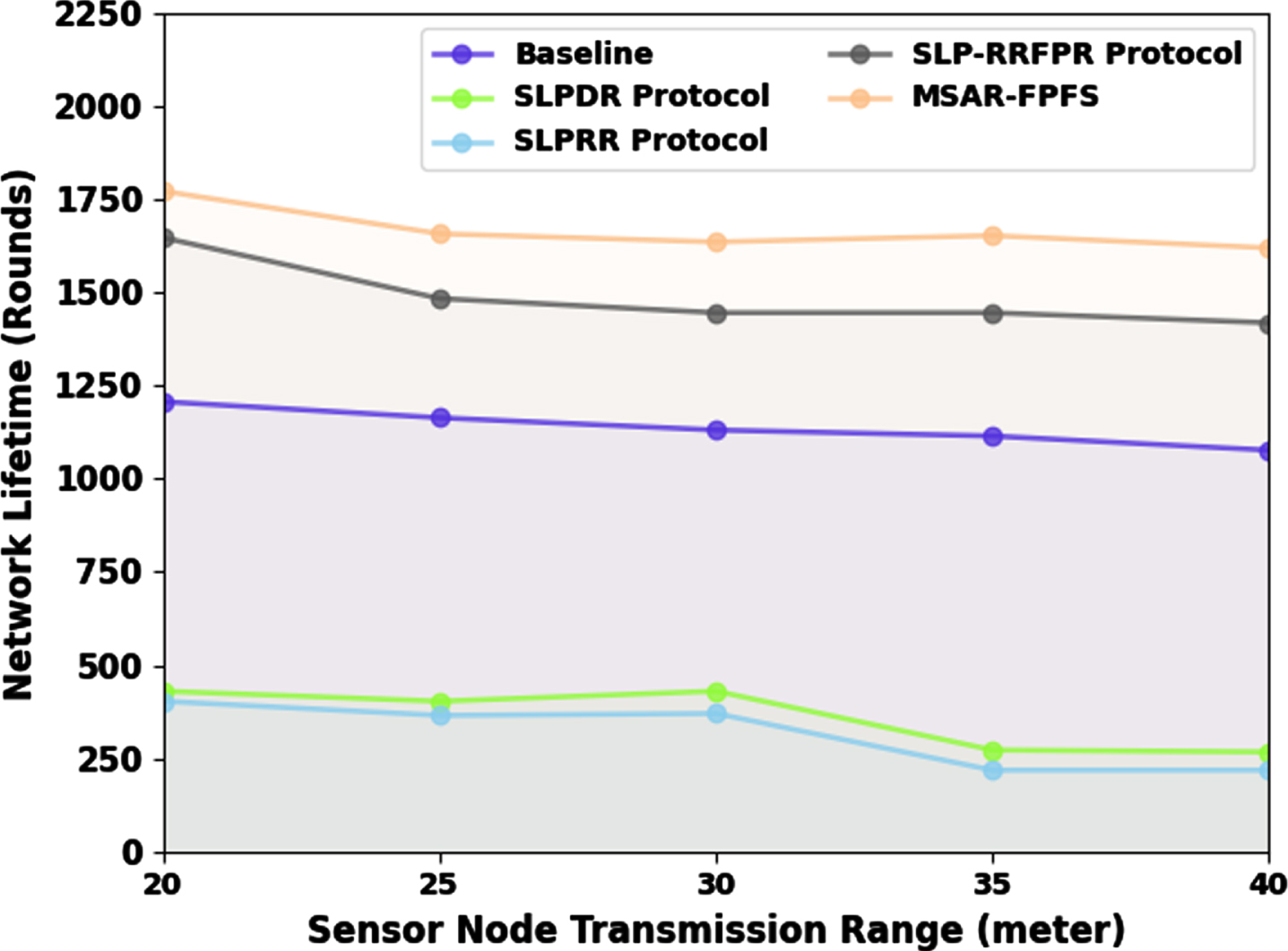
NLT analysis of MSAR-FPFS approach under varying SNTR.
A comparison study of the MSAR-FPFS technique with recent approaches in terms of delay (DEL) is reported in Table 4. In Fig. 7, the DEL assessment of the MSAR-FPFS technique with recent models is revealed under several distances between SN and BS. The results indicate the promising DEL values of the MSAR-FPFS technique. With a distance of 20 m, the MSAR-FPFS technique provides the least DEL of 1 hop while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques accomplish increased DEL of 19, 2, 3, and 21 hops respectively. Simultaneously, with a distance of 100 m, the MSAR-FPFS algorithm provides minimal DEL of 12 hops while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques accomplish increased DEL of 39, 17, 16, and 31 hops respectively. Concurrently, with a distance of 160 m, the MSAR-FPFS system provides least DEL of 15 hops while the baseline, SLPDR, SLPRR, and SLP-RRFPR systems accomplish increased DEL of 58, 22, 32, and 40 hops correspondingly.
Delay analysis of MSAR-FPFS approach with other systems
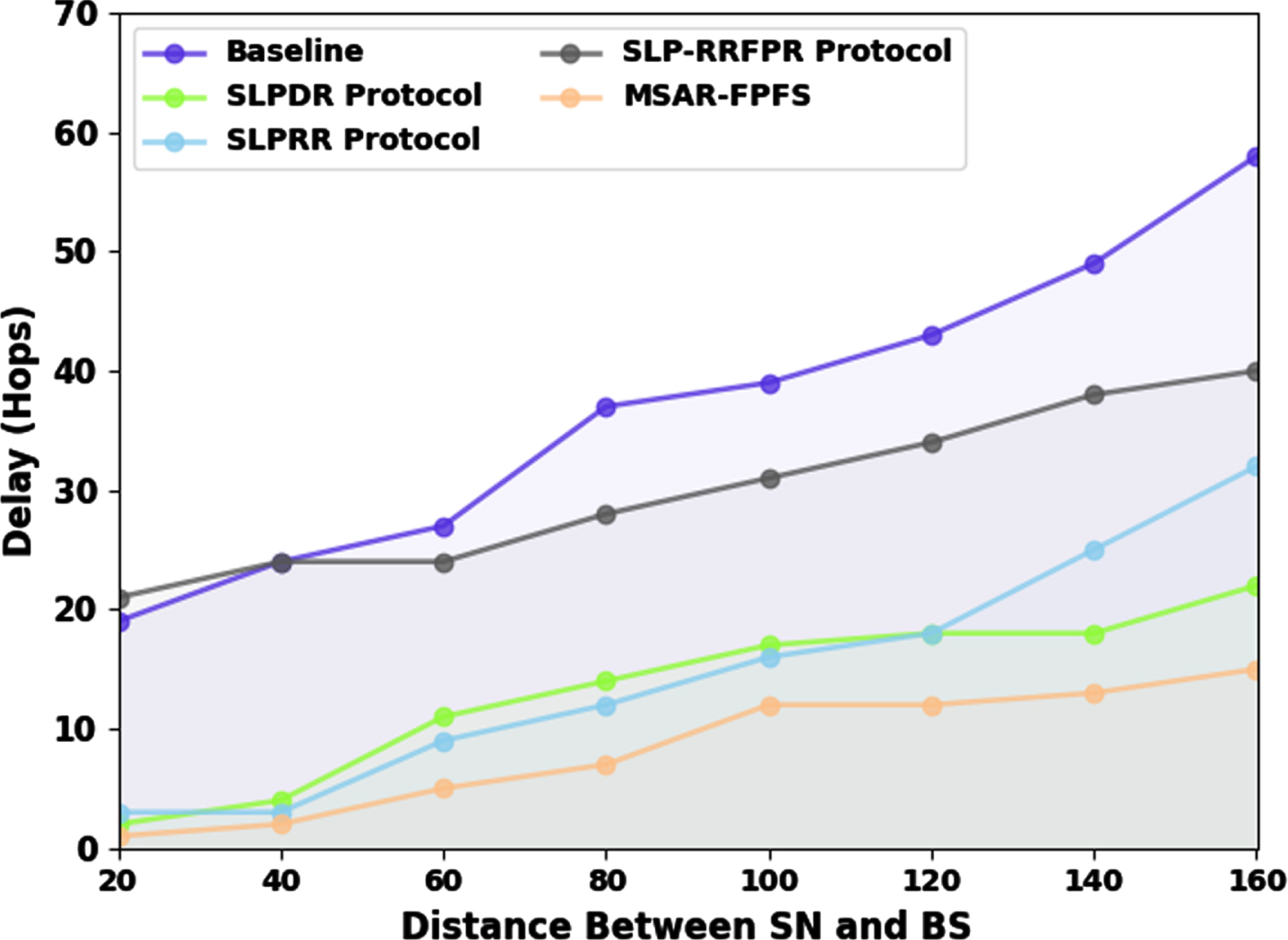
Delay analysis of MSAR-FPFS approach under varying distances between SN and BS.
In Fig. 8, the DEL investigation of the MSAR-FPFS technique with recent approaches is exposed under several SNTRs. The outcomes indicate the promising DEL values of the MSAR-FPFS system. With SNTR of 20 m, the MSAR-FPFS method gives reduced DEL of 1 hop while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques accomplish higher DEL of 32, 14, 6, and 2 hops correspondingly. At the same time, with SNTR of 30 m, the MSAR-FPFS approach provides minimal DEL of 1 hop while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques achieve enhanced DEL of 27, 8, 5, and 3 hops respectively. Simultaneously, with SNTR of 40 m, the MSAR-FPFS system provides least DEL of 1 hop while the baseline, SLPDR, SLPRR, and SLP-RRFPR algorithms realize increased DEL of 21, 5, 4, and 2 hops correspondingly.
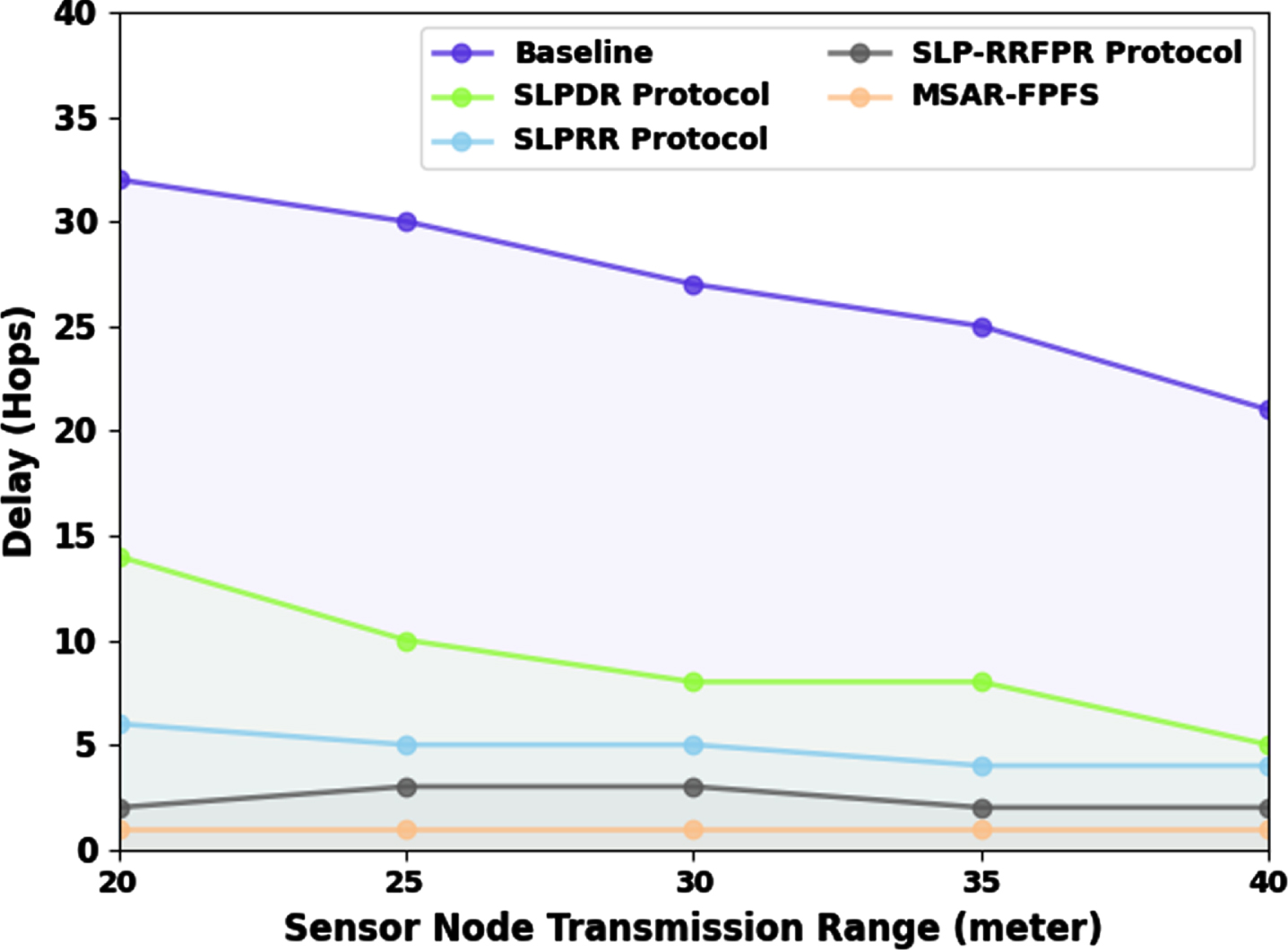
Delay analysis of MSAR-FPFS approach under varying SNTR.
In Table 5, a detailed safety period (SPD) study of the MSAR-FPFS method with recent approaches is revealed. Figure 9 exemplifies the SPD study of the MSAR-FPFS algorithm under varying distances between SN and BS. The results inferred that the MSAR-FPFS methodology obtains enhanced values of SPD under all aspects. With a distance of 20 m, the MSAR-FPFS approach attains enhanced SPD of 76 while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques obtain minimal SPD of 2, 20, 20, and 53 correspondingly. Lastly, with distance of 160 m, the MSAR-FPFS system gains increasing SPD of 154 while the baseline, SLPDR, SLPRR, and SLP-RRFPR methods achieve decreasing SPD of 6, 55, 49, and 148 correspondingly.
Safety period analysis of MSAR-FPFS approach with other systems
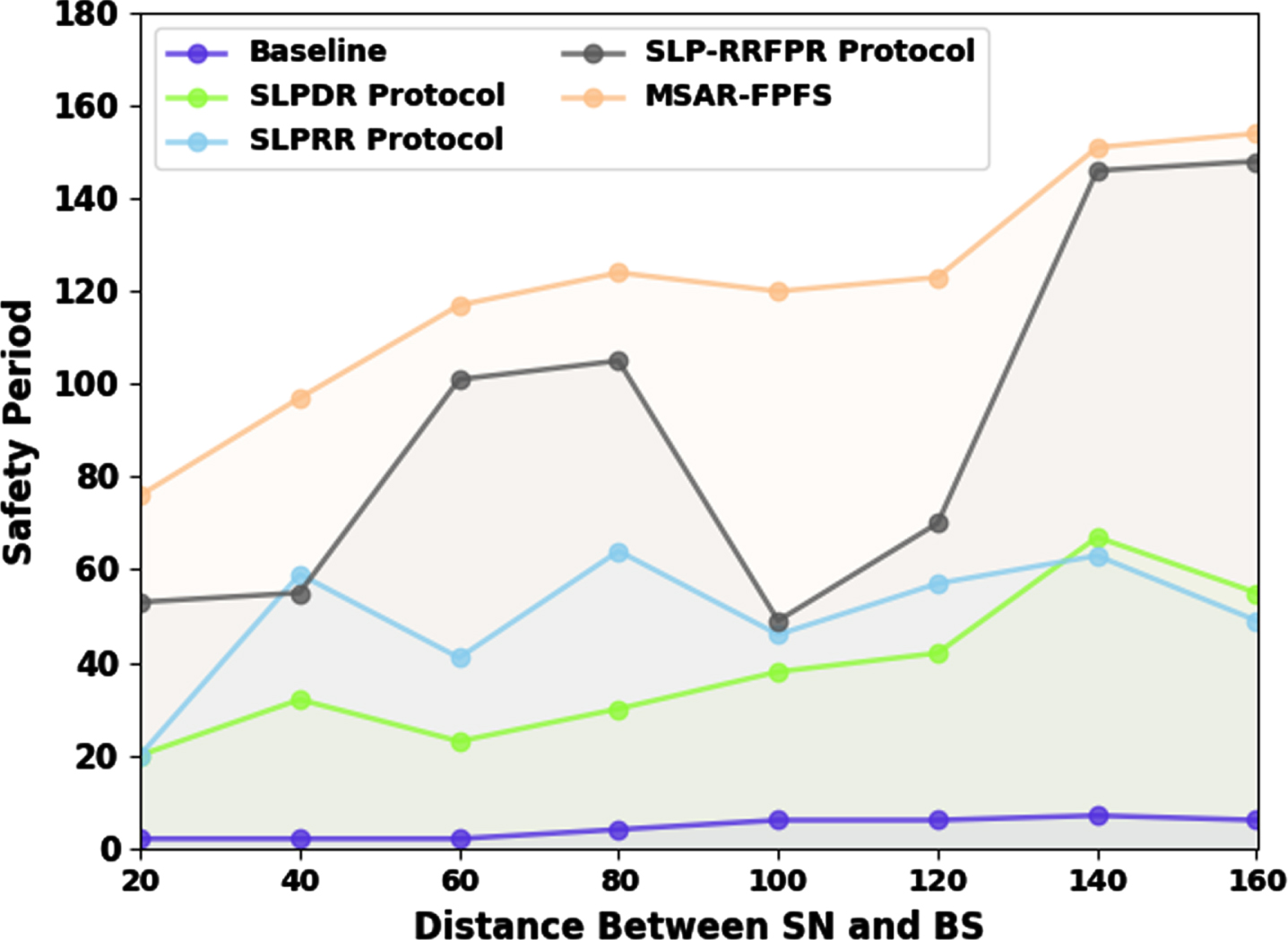
SPD analysis of MSAR-FPFS approach under varying distances between SN and BS.
Figure 10 indicates the SPD examination of the MSAR-FPFS system under varying SNTR. The outcomes considered that the MSAR-FPFS method reaches higher values of SPD under all aspects. With SNTR of 20 m, the MSAR-FPFS approach gains increasing SPD of 61 while the baseline, SLPDR, SLPRR, and SLP-RRFPR techniques obtain diminishing SPD of 6, 51, 53, and 60 correspondingly. At last, with SNTR of 40 m, the MSAR-FPFS technique gains maximal SPD of 37 while the baseline, SLPDR, SLPRR, and SLP-RRFPR approaches obtain minimal SPD of 2, 23, 27, and 26 correspondingly.
From these results and discussion, it is guaranteed that the MSAR-FPFS technique reaches better performance than other models.
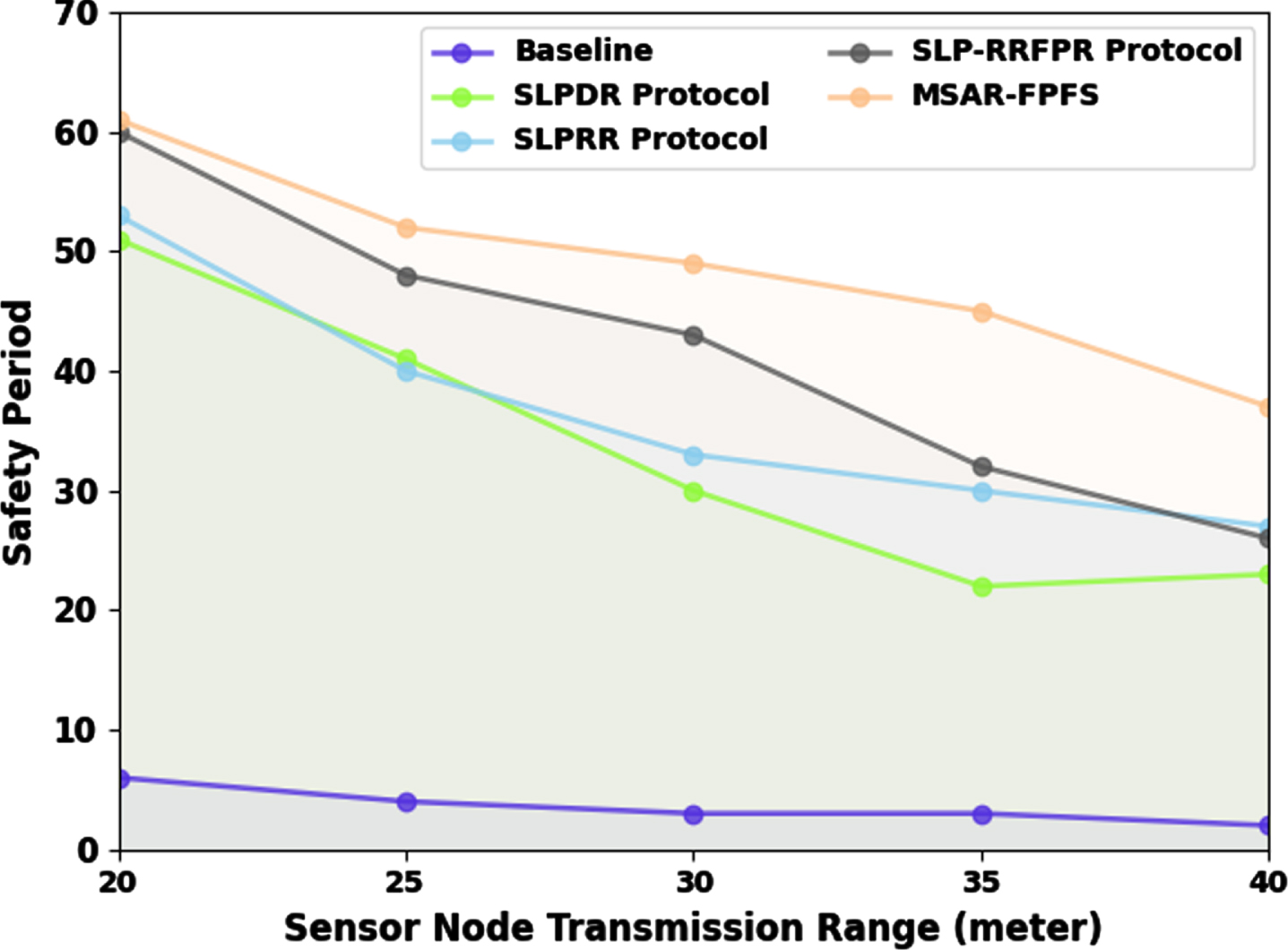
SPD analysis of MSAR-FPFS approach under varying SNTR.
In this study, we have developed a novel MSAR-FPFS approach to achieve SLPP on the WSN. The presented MSAR-FPFS technique follows a two-stage process: false packet forwarding and real packet forwarding. Initially, the MSAR-FPFS technique enables the PNs to forward false packets in the WSN using the routes discovered by the SAR technique. At the next stage, the real packets are forwarded by the IRSA technique to accomplish privacy-preserving data transmission in the network. The performance validation of the MSAR-FPFS approach is tested under different aspects and the outcomes are investigated under varying transmission ranges of SNs and distances from SNs to BS. A widespread comparison results show the promising performance of the MSAR-FPFS technique compared to other existing models. Therefore, the presented MSAR-FPFS technique can be employed for accomplishing SLPP in WSN. In future, data encryption schemes can be integrated into the MSAR-FPFS technique to improve security in WSN.
Declarations
Ethical Approval
Not Applicable
Competing interests
Authors don’t have any competing interest
Authors’ contributions
Pitchandi@Sankaralingam - Data Collection, Conceptualization
Arunachalaperumal - Data Curation, Investigation,
Arunachalaperumal –Validation, Editing
Pitchandi@Sankaralingam - Review and Editing
Funding
Not Applicable
Availability of data and materials
Data can be provided on request.
