Abstract
Micro, small, and medium-sized enterprises (MSMEs) shoulder a disproportionate share of cyber risk yet remains underrepresented in empirical cybersecurity research. This study develops and validates an integrated Technology–Organization–Environment (TOE) and Resource-Based View (RBV) framework to explain cybersecurity management effectiveness and its performance payoffs in MSMEs. Using a sequential explanatory mixed-methods design, we analyze survey data from 847 MSMEs across sectors and regions, complemented by 32 expert interviews. Psychometrically validated measures feed a structural equation model (SEM) and a fuzzy-set qualitative comparative analysis (fsQCA). SEM results show cybersecurity awareness is the strongest predictor of management effectiveness (β = .486,
Plain Language Summary
Small and medium-sized businesses (SMEs) are the backbone of the global economy but are increasingly targeted by cyberattacks, and our research discovered how these smaller companies can best protect themselves despite limited resources by finding that while advanced technology is helpful, the most important factor is cybersecurity awareness—making sure every employee understands online risks and follows good practices—and that while tight budgets are the biggest hurdle, there is no one-size-fits-all solution, as some businesses succeed by pairing technology with training, others excel through exceptional awareness alone, some use regulations as a blueprint, and many find success through a balanced approach, proving that strong protection is achievable by strategically focusing on training and choosing a practical combination of measures that fit a specific budget and needs.
Keywords
Introduction
Small and medium-sized enterprises (MSMEs) increasingly rely on digital technologies to support their operations, enhance productivity, and access broader markets. Yet, this rapid digitalization, accelerated further in the post-COVID environment, has also expanded their exposure to cybersecurity threats. Compared with larger organizations, MSMEs typically operate with limited financial, technical, and human resources, making them disproportionately vulnerable to cyberattacks and operational disruptions. The contemporary cybersecurity landscape has also been reshaped by the rapid emergence and adoption of AI technologies, which has introduced new risks that many earlier SME-focused cybersecurity studies did not anticipate (Junior et al., 2023). Recent advances in generative AI, automated vulnerability discovery, and AI-orchestrated social engineering have lowered the technical barriers for attackers, enabling more scalable, adaptive, and targeted cyberattacks (Khan et al., 2025). AI-driven phishing tools, synthetic identity generation, automated reconnaissance, and polymorphic malware increasingly bypass traditional controls, posing amplified challenges for resource-constrained MSMEs with limited monitoring capabilities (Chandran et al., 2025). At the same time, the defensive potential of AI remains unevenly distributed, with smaller firms lacking access to advanced AI-based detection and response systems commonly used in larger enterprises. These developments suggest that longstanding cybersecurity vulnerabilities in MSMEs, such as weak cyber hygiene, limited awareness, and underinvestment in security infrastructure, are now compounded by emergent AI-enabled threats (Karahan et al., 2025). Thus, examining cybersecurity management effectiveness in MSMEs requires acknowledging both the historical drivers of vulnerability and the rapidly evolving risk landscape shaped by AI technologies.
A further layer of complexity arises from the growing dependence of MSMEs on external cloud platforms, outsourced IT services, and digital supply-chain partners. Many MSMEs rely on third-party providers for data storage, software delivery, payment processing, authentication, and remote collaboration tools, services that often sit outside the direct control of the firm. These dependencies introduce upstream and downstream vulnerabilities, as cybersecurity failures in any linked entity can propagate across shared infrastructures. Moreover, heterogeneous security practices among cloud vendors, managed service providers, and subcontracted partners create fragmented risk environments in which MSMEs may lack the capacity to evaluate, monitor, or enforce compliance. Such inter-organizational dependencies amplify exposure to misconfigurations, supply-chain attacks, credential compromise, and service disruptions, making cybersecurity management inherently more complex for resource-limited MSMEs. Recognizing these interconnected risks is essential for understanding the structural pressures shaping cybersecurity effectiveness in contemporary MSME ecosystems.
Digital technologies have transformed the operations of MSMEs and opened new opportunities, while also amplifying their exposure to cyber threats (Abdallah-Ou-Moussa et al., 2024; Wynn & Felser, 2023). Rapid digitization, accelerated by COVID-19, often proceeded without enterprise-grade defenses, leaving firms to navigate economic constraints, compliance burdens, and organizational awareness gaps amid evolving regulation (Akinsola, 2025; Aragòn-Correa et al., 2020; Darvishi et al., 2022; Hasani et al., 2023; Nakpodia et al., 2025). Because cyber-attacks are asymmetric, the cybersecurity paradox disproportionately endangers resource-constrained organizations (Bada et al., 2019; Benz & Chatterjee, 2020). The existing evidence base remains fragmented. Although many studies report positive associations between cybersecurity adoption and organizational performance, these relationships are complex and often context-dependent (Hasani et al., 2023). Research on decision processes surrounding cyber insurance and risk management also remains under-specified (Darvishi et al., 2022). In addition, organizational readiness varies significantly across socio-technical and regional contexts, and MSMEs face diverse and multifaceted risks (Armenia et al., 2021; Bada et al., 2019; Michelotto & Joia, 2024; Reniati et al., 2025; Trenerry et al., 2021; Zhang et al., 2025). The Technology-Organization–Environment (TOE) perspective is promising but remains incompletely validated or is applied only in narrow contexts. Similarly, the Resource-Based View (RBV) requires further integration into cybersecurity research to fully explain performance differences among MSMEs (Albar & Hoque, 2019; Badi et al., 2021; Bening et al., 2023; Herath et al., 2020; Nair et al., 2019; Ramdani et al., 2009; Tsou & Hsu, 2015; Wallace et al., 2021). Business value from security investments remains uncertain; optimization/insurance models can be too technical for MSMEs, and Theoretical Foundations of Cybersecurity Insurance and Risk Sharing Mechanism (Bodin et al., 2018) require MSME-specific tests; culture, awareness, and institutional influences are salient yet theoretically underdeveloped (Angst et al., 2017; Georgiadou et al., 2022; Tang et al., 2016; Uuganbayar et al., 2021). Adjacent digitalization research is informative, but not explicitly focused on cybersecurity (Gkrimpizi et al., 2023; Wynn et al., 2024). The business value of cybersecurity investments remains uncertain, as empirical findings in this area are still mixed and context-dependent. Existing optimization and insurance models also tend to be highly technical and may exceed the analytical capacity of many MSMEs. Furthermore, the theoretical foundations underlying cybersecurity insurance and risk-sharing mechanisms require additional testing in MSME contexts. Culture, awareness, and institutional influences are likewise salient factors, yet they remain theoretically underdeveloped in current research.
The study integrates the Technology–Organization–Environment (TOE) theory with the Resource-Based View (RBV) to explain the effectiveness of SMEs’ cybersecurity management and its mediated link to organizational performance. As depicted in Figure 1, the TOE dimensions, technology, organization, and environment, jointly shape the effectiveness of cybersecurity management (the mediating construct), which in turn influences performance outcomes. TOE is appropriate because it captures technological capability, organizational characteristics, and environmental pressure that drive adoption decisions (Herath et al., 2020; Wallace et al., 2021). RBV complements this by explaining why firms facing similar environments and access to technology nonetheless achieve different levels of security effectiveness through idiosyncratic resources and capabilities. Technologically, technology readiness encompasses both infrastructure capacity and the willingness to deploy sophisticated solutions (Tsou & Hsu, 2015), acknowledging that tools require organizational capacity to implement and operate effectively. Organizationally, cybersecurity awareness, employees’ security knowledge, managerial commitment, and cultural conditions condition the adoption and execution of cybersecurity measures (Tang et al., 2016). Environmentally, regulatory compliance imposes external standards while economic constraints limit feasible investment, together bounding managerial choice (Benz & Chatterjee, 2020). Collectively, the integrated TOE–RBV framework (Figure 1) identifies the determinants of cybersecurity adoption and the mechanisms through which these decisions affect organizational performance via cybersecurity management effectiveness.
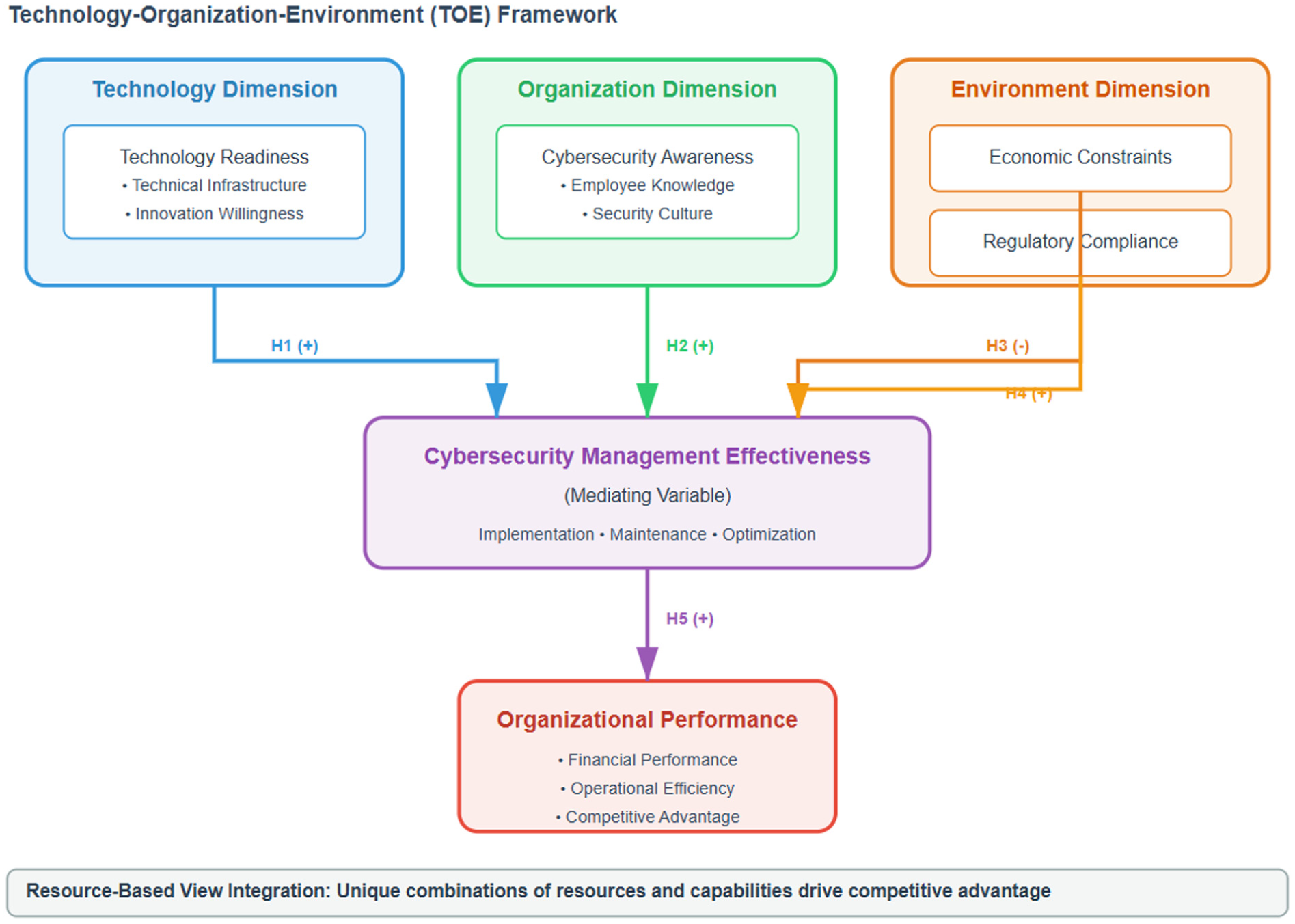
Integrated TOE-RBV framework for cybersecurity management in MSMEs.
Addressing these gaps, the study proposes and empirically validates an integrated TOE–RBV framework that models technology readiness, budget priorities, regulatory compliance, and cybersecurity awareness, as well as their interactions, against management processes and organizational performance. Using SEM and fsQCA, it identifies both linear relationships and equifinal configurational pathways, yielding actionable guidance for resource-constrained MSMEs, policy implications, theoretical advances in cybernetic management, and methodological tools for future work.
Recent empirical and review-based studies consistently show that the cybersecurity posture of small and medium-sized enterprises (SMEs/SMBs) is shaped by persistent structural vulnerabilities, behavioral limitations, and technological constraints. Ncubukezi et al. (2020) provide qualitative evidence demonstrating that cyber hygiene varies substantially across business sectors, with many SMEs lacking formalized rules, operational procedures, and security guidelines. Their findings reveal that the absence of documented policies, combined with limited employee preparedness, leads to weak cyber hygiene and inconsistent implementation of essential security practices.
Complementing these insights, Kandpal et al. (2023) highlight more systemic cybersecurity readiness challenges in SMEs. Their comprehensive review shows that many SMEs underestimate their risk exposure due to the widespread belief that “small firms are too insignificant for attackers.” This misconception, compounded by chronic shortages of financial resources, limited security expertise, and the inability to deploy or manage advanced controls, results in low detection capabilities, delayed response to threats, and a generally poor cybersecurity posture across global SME populations. Beyond structural and resource-based constraints, recent research emphasizes the pivotal role of employee awareness and behavior in shaping cybersecurity resilience. Onkiso (2024) argues that cybersecurity awareness in small businesses is influenced by psychological factors, such as perceived threat severity, self-efficacy, and social norms, as well as the clarity of internal policies and leadership engagement. Drawing on frameworks such as Protection Motivation Theory, Theory of Planned Behavior, and Social Cognitive Theory, his work demonstrates that awareness is not merely an informational construct but a behavioral capability requiring continuous reinforcement, tailored training, and organizational incentives.
In parallel, Maity and Lee (2025) show that remote and hybrid work environments have intensified cybersecurity risks for SMEs. Their systematic literature review indicates that while flexible work models enhance productivity, they also expand the attack surface due to the use of personal devices, home networks, and decentralized communication systems. Many SMEs lack the robust digital infrastructure and security protocols needed to support distributed work environments securely, making them more susceptible to cyber breaches. Technical analyses of SME infrastructure further illustrate growing operational challenges. Rajagopalan’s (2020) survey of server load balancing and application delivery technologies shows that as SMEs transition toward more digitalized, interconnected systems, their reliance on scalable and secure IT infrastructures increases. This shift amplifies the need for strong cybersecurity governance, as performance and security become intertwined in modern SME environments.
The integrated model posits that cybersecurity management effectiveness serves as a mediating construct, translating technological, organizational, and environmental inputs into organizational performance outcomes. As shown in Figure 1, effectiveness is defined by both the technical adequacy of security measures and their alignment with organizational needs and capabilities, thereby explaining how inputs are transformed into results.
The decision-making processes of MSMEs differ substantially from those of larger organizations due to persistent resource constraints, competing operational priorities, and limited managerial bandwidth. These constraints force MSMEs to engage in explicit trade-offs between short-term operational needs and longer-term cybersecurity investments. As a result, MSMEs often adopt incremental or reactive security measures rather than systematic, capability-based strategies. Within the TOE–RBV framework, economic constraints interact with technological readiness, awareness, and compliance pressures to shape how MSMEs prioritize and sequence cybersecurity actions. Therefore, the hypothesized relationships in this model should be interpreted within the context of MSMEs’ constrained resource environments, which fundamentally influence adoption logic, capability development, and the ability to realize cybersecurity effectiveness.
Hypotheses (as in Figure 1):
Accordingly, the aim of this study is not to prescribe idealized or resource-intensive cybersecurity models but to identify empirically viable combinations of technological, organizational, and environmental conditions that MSMEs can realistically assemble under genuine economic constraints. The integrated TOE–RBV approach is therefore used to capture how SMEs combine limited capabilities to achieve cybersecurity management effectiveness, rather than to imply convergence toward a single optimal configuration.
Method
Research Design and Philosophical Approach
The study adopts a sequential explanatory mixed-methods design to examine how technological, organizational, and environmental factors influence cybersecurity management in MSMEs. Grounded in an instrumentalist epistemology, the design integrates quantitative and qualitative phases to address organizational complexity. In the quantitative phase, structural equation modeling (SEM) is used to test the theoretical framework, allowing simultaneous estimation of multiple relationships while accounting for measurement error. The qualitative phase applies fuzzy-set qualitative comparative analysis (fsQCA) to identify configurational pathways and alternative routes to cybersecurity effectiveness that linear models may overlook. This sequencing provides both statistical validation of hypothesized relationships and deeper insight into how different factor combinations produce effective cybersecurity management, particularly in resource-constrained contexts.
Sampling Strategy and Sample Characteristics
The target population comprises MSMEs across multiple industries with varying levels of technological and cybersecurity maturity. Consistent with international standards, MSMEs are defined as organizations with fewer than 250 employees and turnover below specified thresholds, in line with the WTO definition and applicable across national contexts. To enhance generalizability under diverse regulatory and economic conditions, the sampling frame includes organizations from multiple geographical regions.
As shown in Figure 2, a stratified purposive sampling strategy was used to ensure representation across industry, firm size, technology level, and location. Key sectors such as manufacturing, services, retail, healthcare, and financial services were explicitly stratified to capture sector-specific cybersecurity challenges. The final sample of 847 organizations exceeds the minimum requirements for complex SEM analysis and provides sufficient statistical power to detect moderate effect sizes, based on prior studies and pilot testing. The inclusion of firms from both developed and developing economies further strengthens external validity and supports comparative analysis of how economic context shapes cybersecurity management.

Sequential explanatory mixed-methods research design.
To ensure methodological clarity, we specify the inclusion and exclusion criteria applied in the sampling process. Eligible participants were organizations classified as micro, small, or medium-sized enterprises according to the employment and turnover criteria established by their respective national jurisdictions. Firms were included if they operated in one of the following sectors: manufacturing, professional and business services, retail and consumer trade, information technology, logistics and transportation, healthcare, education, hospitality, and financial and insurance services. These categories represent the full set of high-level industry groups incorporated in the study. Organizations were excluded if they did not meet MSME size definitions, operated solely as informal or unregistered entities, or lacked a designated individual with managerial or cybersecurity-related responsibilities capable of completing the survey.
MSMEs were identified through a multi-stage recruitment strategy using commercial business directories, national chamber-of-commerce databases, and publicly accessible SME registries. Initial contact was made via email and LinkedIn outreach to owners, managers, IT personnel, and cybersecurity focal points. To avoid single-country bias and enhance representativeness, the sampling frame targeted MSMEs across multiple geographical regions, including Western Europe, Eastern and Central Europe, South and Southeast Asia, the Middle East and North Africa, Sub-Saharan Africa, North America, and Latin America. A total of 847 firms from these regions provided complete responses.
Participation in the study was entirely voluntary, and no monetary remuneration or material incentives were offered. This decision was made to reduce the risk of response bias and ensure that participation reflected genuine organizational engagement rather than incentive-driven motivation. Respondents were assured of confidentiality, and no identifiable organizational data were collected beyond sectoral classification and regional location.
To enhance transparency and strengthen external validity, the geographical distribution of the sample is reported explicitly. The final dataset of 847 MSMEs comprises organizations from seven major geographical regions, ensuring representation across both developed and developing economies. Specifically, 29.4% of the firms (
Given the resource-constrained conditions under which MSMEs operate, the hypothesized relationships emphasize how technological, organizational, and environmental factors shape cybersecurity management effectiveness within this context. Rather than assuming that all firms optimize security investments, we position MSMEs as entities that must prioritize selectively, making trade-offs between cost, capability, and compliance. The following hypotheses therefore articulate how limited resources condition the influence of technology readiness, awareness, economic constraints, and regulatory pressures on cybersecurity management effectiveness.
Data Collection Procedures and Instruments
Data were collected from both primary and secondary sources, including an organizational survey, internal records, and public datasets. The structured questionnaire was developed through an extensive literature review, expert consultation, and pilot testing, as outlined in Figure 2. Validated scales were adopted where available, while newly developed measures underwent psychometric validation. The data collection achieved a response rate of 62.3%, with 94.7% complete cases, resulting in 847 usable responses that exceeded the minimum requirements for SEM and fsQCA analyses.
Technology readiness was measured by adapting established technology readiness scales to the cybersecurity context, capturing both infrastructure capability and willingness to adopt advanced solutions. Cybersecurity awareness assessed employee knowledge, managerial commitment, and supportive security culture, while economic constraints captured resource scarcity and allocation priorities. Instrument quality was strengthened through cognitive interviews and pilot testing. Bias mitigation strategies included repeated contacts, incentives, and respondent anonymity. The final dataset contained less than 5% missing data, exhibited low common method variance, and showed no significant non-response bias.
Analytical Approaches and Statistical Methods
The analytical strategy integrates quantitative and qualitative methods to address the research questions while maintaining methodological rigor. The combined use of structural equation modeling and fuzzy set qualitative comparative analysis is illustrated in Figure 3, which presents the overall analytical process.

Analytical process—SEM and fsQCA integration.
Structural equation modeling serves as the primary quantitative approach and simultaneously assesses the measurement model and structural relationships, as shown in the left panel of Figure 3. This approach explicitly accounts for measurement error and allows testing of complex mediating relationships that are not feasible with other multivariate techniques. The full analytical sequence, including data preparation, measurement validation, structural model evaluation, hypothesis testing, and mediation analysis, is detailed in Figure 3.
Structural equation modeling follows established best practices using a two-step approach, in which confirmatory factor analysis is conducted prior to structural model estimation, as shown in Figure 3. The measurement model is evaluated for construct reliability, convergent validity, and discriminant validity using standard criteria, including composite reliability above 0.7, average variance extracted above 0.5, and the Fornell Larcker criterion. Structural model assessment examines path significance, effect sizes, and overall model fit using indices such as the comparative fit index above 0.95, root mean square error of approximation below 0.08, and standardized root mean square residual below 0.08.
Data calibration in fsQCA uses the direct method to transform interval scale variables into fuzzy set membership scores ranging from 0 to 1, based on theoretical and empirical anchors, as shown in Figure 3. Thresholds define full membership at 0.95, the crossover point at 0.5, and full non membership at 0.05. Necessity analysis examines the presence or absence of conditions in cases with high cybersecurity management effectiveness, while sufficiency analysis identifies combinations of conditions that produce high effectiveness using truth tables and logical minimization.
Solution quality is evaluated through consistency and coverage metrics, as illustrated in Figure 3. Consistency assesses how reliably configurations lead to the outcome, while coverage indicates the proportion of cases explained. Both parsimonious and intermediate solutions are considered to balance theoretical simplicity and empirical relevance. Robustness is assessed through sensitivity analysis and threshold variation to ensure solution stability.
Measurement Development and Validation
The study develops and validates a measurement instrument to ensure construct reliability and validity across diverse organizations. Four antecedents and two outcomes are operationalized. Technology readiness assesses infrastructure adequacy, adoption propensity, and technical capability. Cybersecurity awareness captures employee knowledge, managerial commitment, and security-oriented culture across organizational levels. Economic constraints measure budget limitations and allocation tradeoffs affecting cybersecurity investment. Regulatory compliance reflects adherence to mandatory and voluntary standards, including regulatory knowledge and implementation adequacy.
Cybersecurity management effectiveness is measured through technical adequacy, strategic alignment, and operational integration across prevention, response, and continuity activities. Organizational performance is assessed using financial, operational, and strategic outcomes, including growth, efficiency, reliability, customer satisfaction, and competitive positioning, with attention to indirect effects. In addition to expert review, the pilot survey instrument was distributed to 200 MSME participants to assess item clarity, response consistency, and preliminary reliability. The pilot questionnaire consisted of 22 items covering all constructs in the conceptual model. The pilot results demonstrated acceptable internal consistency, with a Cronbach’s alpha of α = .80 for the overall instrument, confirming that the measures were sufficiently reliable for full-scale deployment.
The development of the measurement instrument was informed by prior validated scales used in cybersecurity, technology adoption, and organizational behavior research. Items relating to technology readiness were adapted from Tsou and Hsu (2015) and Ramdani et al. (2009), while measures for cybersecurity awareness drew on established scales from Tang et al. (2016), Angst et al. (2017), and Uuganbayar et al. (2021). Regulatory compliance items were adapted from Benz and Chatterjee (2020), and economic constraint measures were based on prior work examining resource scarcity and managerial prioritization (Hasani et al., 2023). Cybersecurity management effectiveness and organizational performance items were informed by constructs validated in Wallace et al. (2021), Herath et al. (2020), and Bening et al. (2023). All adapted items were modified minimally to reflect the MSME context.
The final instrument was administered as a self-completed, online questionnaire distributed via SurveyMonkey. The questionnaire consisted of closed-ended items measured using a 5-point Likert scale ranging from 1 (strongly disagree) to 5 (strongly agree). Additional categorical items captured organizational demographics including size, sector, and geographical region. No items required researcher facilitation, and all respondents completed the instrument independently.
To ensure content validity, an expert panel reviewed the measurement instrument prior to data collection. The panel comprised eight specialists: three cybersecurity researchers, two information systems scholars, two senior cybersecurity practitioners, and one MSME digital transformation consultant. Panel members evaluated item clarity, construct relevance, and domain coverage. Recommended revisions included minor wording adjustments and reordering of items for cognitive coherence.
A pilot test was subsequently conducted with 42 MSME representatives across manufacturing, services, and retail sectors to assess face validity, item comprehension, response-time burden, and initial reliability. Pilot feedback confirmed that items were understandable and appropriately targeted for MSME managers. Cronbach’s alpha values for all constructs exceeded the recommended threshold of .70, supporting internal consistency. Insights from the pilot informed minor refinements to instructions and layout prior to full-scale deployment.
Validity and Reliability Considerations
Construct validity is assessed using multiple strategies, including expert review for content validity, factor analysis for convergent validity, and correlation and variance comparison for discriminant validity. Convergent validity is established through factor loadings above 0.70 and average variance extracted above 0.50, while discriminant validity requires shared variance between constructs to be lower than extracted variance.
Reliability is evaluated using Cronbach’s alpha and composite reliability, with values above .70 indicating adequate internal consistency, as specified in Figure 3. Scale stability is examined through temporal comparison, and common method bias is addressed through procedural remedies such as anonymity and measurement separation, as well as statistical tests including Harman’s single factor test and latent factor analysis.
Ethical Considerations and Data Management
Ethical approval was obtained through the author’s institutional review board procedures. Informed consent was secured, participation was voluntary, and confidentiality was ensured throughout the study. Participants were informed of the research purpose, data collection procedures, confidentiality safeguards, and their right to withdraw.
Data were collected and stored using encrypted systems, with access restricted to authorized researchers. No personally identifiable information was included in the analysis, and anonymity was maintained in reporting. Data retention and secure disposal followed institutional policies. Findings are reported in aggregated form to protect organizational identities, while summary reports with practical insights were shared with participating organizations. This ethical framework supports rigorous analysis and ensures that the study’s findings contribute reliably to cybersecurity management theory and practice in MSMEs.
Result
Descriptive Statistics and Data Quality Assessment
The analysis began with a detailed study of the data’s characteristics and distribution properties, as well as its quality. Table 1 presents descriptive statistics for the study constructs that exhibit sufficient variation and normality, allowing for analysis. The survey and interviews conducted from September to early October 2022 on a sample of 847 MSMEs resulted in a high level of diversity across all constructs. Specifically, the technology readiness score ranged from 1.2 to 6.8, with a mean of 4.23 and a standard deviation of 1.15. Cybersecurity awareness score ranged from 1.5 to 6.9 with a mean of 4.47 and
Descriptive Statistics and Correlation Matrix.
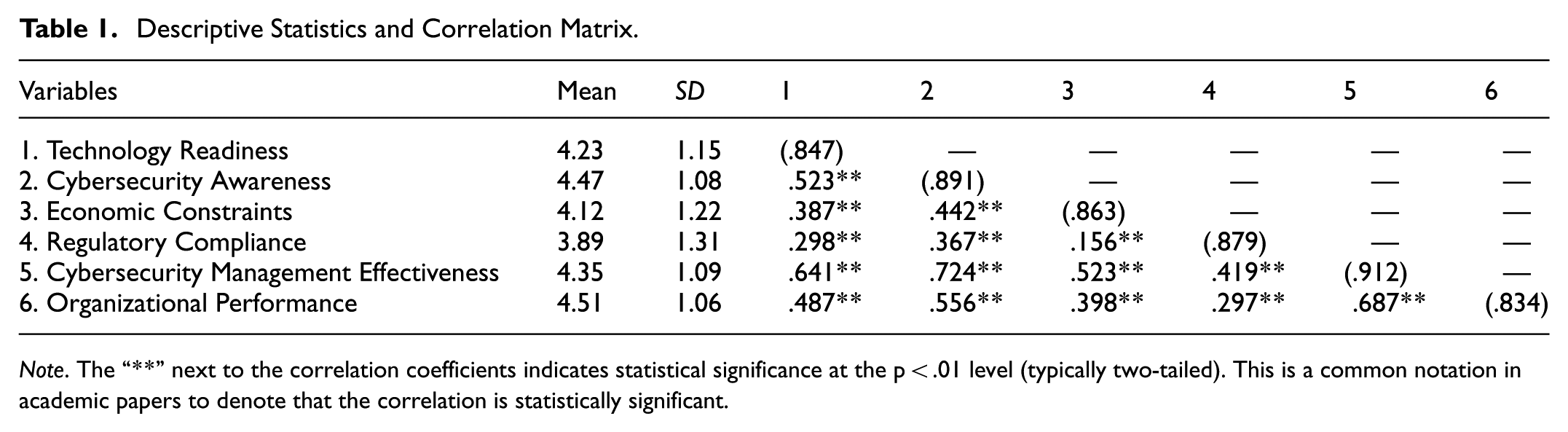
Descriptive characteristics of the final sample indicate that micro enterprises accounted for 35% of respondents (
The analysis indicated that the dataset met all required assumptions for further statistical examination. Missing data accounted for 2.8% of the dataset and were missing at random, remaining below the threshold associated with bias risk. Outlier detection using Mahalanobis distance identified 23 cases, representing 2.7% of the sample, which were retained as they did not materially affect the results. Normality was confirmed through Shapiro Wilk tests and distributional inspection, with skewness ranging from −0.34 to 0.28 and kurtosis from −0.19 to 0.04, all within acceptable limits for SEM.
Common method bias was assessed using multiple approaches. Harman’s single factor test showed that the largest factor accounted for 34.2% of variance, well below the critical threshold. Confirmatory factor analysis further indicated that a multi factor model fit the data significantly better than a single factor model. Procedural remedies, including temporal separation, anonymized responses, and randomized question order, were also applied to mitigate potential bias.
Measurement Model Assessment
The measurement model assessment was conducted through confirmatory factor analysis to evaluate construct reliability, convergent validity, and discriminant validity prior to structural model testing. According to the results provided in (Figure 4), the measurement model results, comprising factor loadings, construct reliabilities, and fit indices, indicate excellent psychometric properties for all constructs. The factor loadings range from 0.724 to 0.891, thus exceeding the threshold of 0.700. The assessment of construct reliability produced excellent outcomes across all the measures. The coefficients of Cronbach’s alpha ranged from .847 to .923, which is far above the minimum of 0.7. The composite reliability coefficients ranged from 0.851 to 0.927, thus also higher than the requirements. The values of average variance extracted (AVE) range from 0.532 to 0.684 and are beyond the minimum threshold of 0.5. Thus, convergent validity is ensured. The results indicated that all scales had high internal consistency and good convergent validity. Specifically, Cronbach’s alpha coefficients for the final measurement model ranged from .847 to .923, all exceeding the recommended threshold of 0.70 and demonstrating strong internal consistency across constructs.

Measurement model results and factor loading matrix.
Discriminant validity was assessed using multiple criteria. All construct pairs satisfied the Fornell Larcker criterion, with square roots of AVE exceeding inter construct correlations. Cross loading analysis showed that all items loaded more strongly on their intended constructs, with differences greater than 0.1. HTMT ratios for all construct pairs were below 0.85, further confirming discriminant validity.
Measurement model fit was excellent, with comparative fit index values above 0.95, RMSEA at 0.047, SRMR at 0.041, and TLI at 0.969. Reliability and validity results reported in Table 2 indicate strong psychometric properties, with Cronbach’s alpha values above .83, composite reliability above 0.85, factor loadings between 0.724 and 0.891, and AVE values exceeding 0.5. These results confirm that the measurement model provides a robust foundation for subsequent structural analysis.
Measurement Model Reliability and Validity Assessment.

Structural Model Results and Hypothesis Testing
The analysis of the structural model investigated the postulated associations between constructs, while accounting for measurement error and providing a comprehensive evaluation of the theoretical assumptions. The results of the structural model, including standardized path coefficients, significance levels, effect sizes, and variance explained for the different endogenous constructs, are presented in Figure 5. The model’s fitting features were simultaneously characterized by CFI = 0.964, RMSEA = 0.049, SRMR = 0.043, and TLI = 0.959, thus confirming a good correspondence between theory and practice.
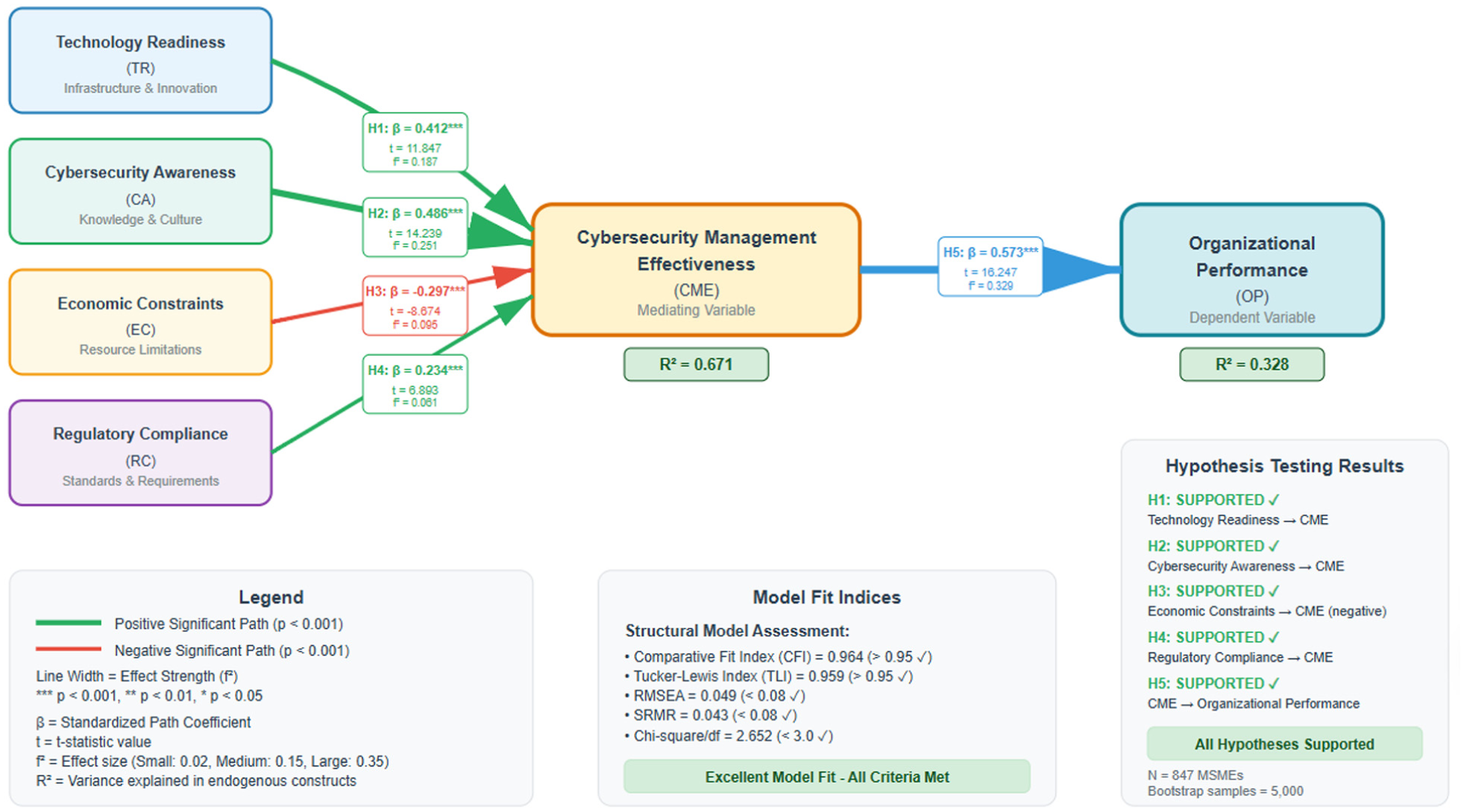
Structural model results with path coefficients and significance levels.
Hypothesis testing provided strong support for the theoretical framework. Technology readiness had a significant positive effect on cybersecurity management effectiveness (β = .412,
Regulatory compliance was positively related to cybersecurity management effectiveness (β = .234,
Structural Model Path Coefficients and Hypothesis Testing Results.

The key endogenous constructs created a significant variance, which the structural model explained. The
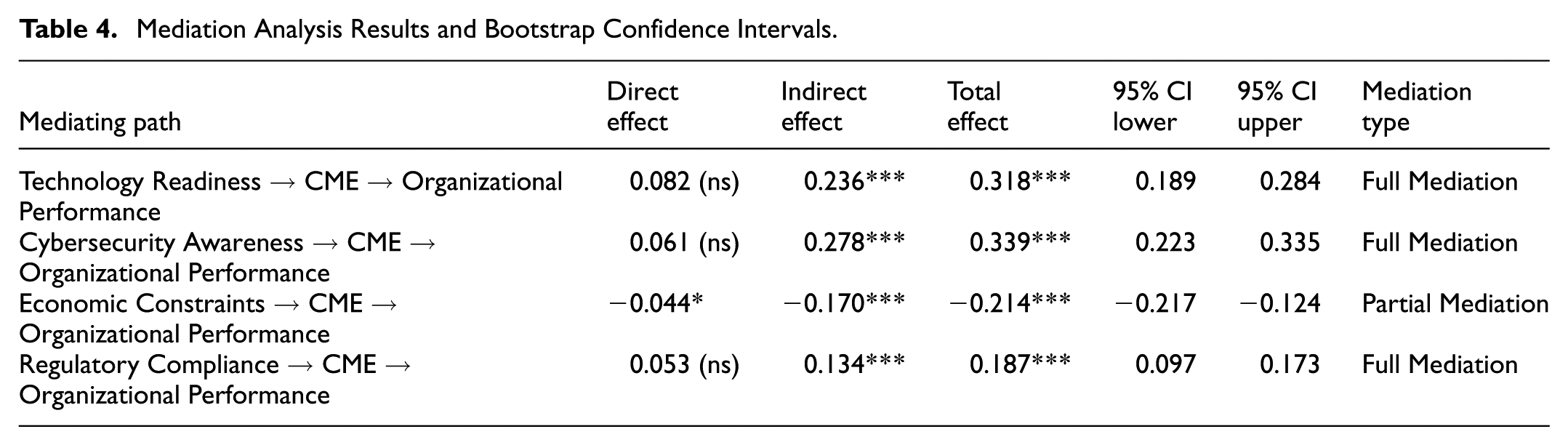
Mediation Analysis Results
The study examined whether the management effectiveness of cybersecurity mediates the relationship between techno-organizational and environmental factors and organizational performance. As represented in Figure 6, the mediation model structure and results indicate a significant indirect effect through cybersecurity management effectiveness for all four antecedents.
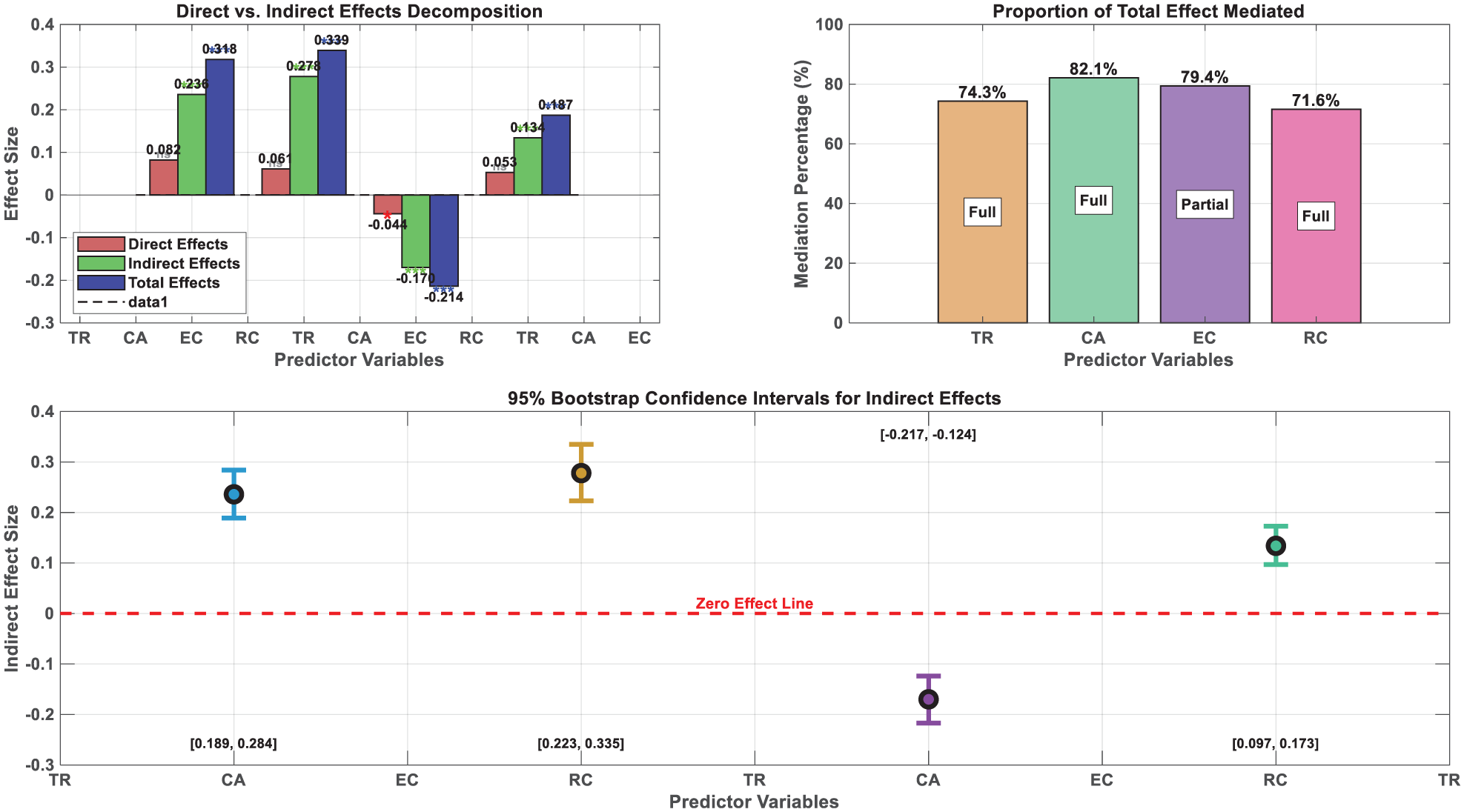
Mediation analysis results and indirect effect decomposition.
Mediation analysis shows that cybersecurity management effectiveness significantly transmits the effects of key antecedents to organizational performance. Technology readiness exhibited a significant indirect effect through cybersecurity management effectiveness (β = .236,
Economic constraints had a significant negative indirect effect on performance through cybersecurity management effectiveness (β = −.170,
Mediation Analysis Results and Bootstrap Confidence Intervals.
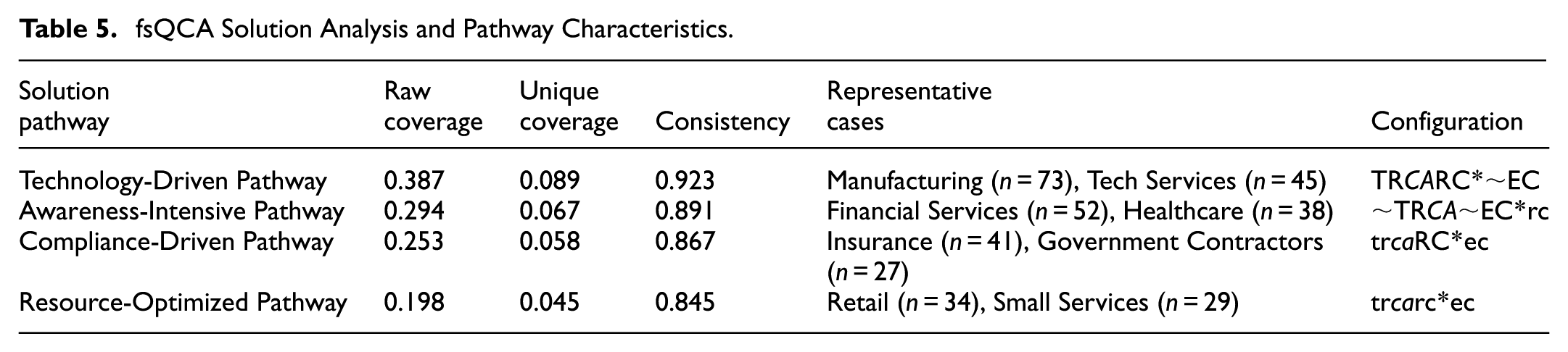
Fuzzy-Set Qualitative Comparative Analysis Results
Analysis of fsQCA confirmed the results of SEM and identified the configurational pathways that lead to the high effectiveness of cybersecurity management. Furthermore, it showed that firms may achieve the same result through different combinations of conditions. The calibration points and membership distributions for all of the conditions are presented in Figure 7. In all conditions, judgments vary appropriately and do not cluster toward the extremes. This is important as clustering near the extremes can create analytical invalidity.

Fuzzy-set calibration and membership score distributions.
The calibration of data utilizes direct method calibration for theoretical and empirical anchors. The threshold of full membership (0.95) corresponded to the 90th percentile for the distribution. The threshold for crossover points membership (0.5) corresponded to the median for the distribution, and the threshold of full non-membership (0.05) corresponded to the 10th percentile for the distribution. The calibration anchors of technology readiness were set at full membership (5.8), crossover (4.2), and full non-membership (2.6). The anchors for cybersecurity awareness were established at 5.9, 4.5, and 2.8, respectively. Due to economic constraints, reverse calibration with anchors at low constraints (full membership) 2.3; crossover 4.1; low constraints (full non-membership) 5.7 was required. The anchors for regulatory compliance were placed at 5.6 (full membership), 3.9 (crossover), and 2.4 (full non-membership). A necessity analysis was conducted to identify the presence of a single condition across cases with high cybersecurity management effectiveness. “Figure 8 presents the results of the necessity analysis, including consistency and coverage scores for the condition and negation.” None of the conditions reached the 0.9 consistency level necessary for necessity, with the highest at 0.847, for cybersecurity awareness. This confirms that no single condition is necessary for effective cybersecurity management. The configurational approach looks at combinations of conditions.

Necessity analysis results for high cybersecurity management effectiveness.
The analysis of truth tables identified important combinations for effective cybersecurity management. The analysis, conducted with a frequency threshold of 2 cases and a consistency threshold of 0.8, yielded a total of 12 configurations that are logically sufficient and have empirical coverage. The truth table, which includes consistency and coverage scores for each configuration in Figure 9, shows the configurations considered in the sufficiency analysis.

Truth table analysis and configuration assessment.
Through logical minimization procedures, a sufficiency analysis indicated the existence of four pathways to the high effectiveness of cybersecurity management. According to the diagram in Figure 10, which illustrates the solution pathways along with their consistency and coverage scores, there are several pathways to success. Furthermore, these solutions are flexible and can be easily modified to suit the organization’s needs while remaining economical.
Solution 1—Awareness-Driven Pathway: Firms lacking advanced technology readiness but possessing strong cybersecurity awareness and managerial commitment can achieve high effectiveness by leveraging human-centric safeguards, low-cost process controls, and informal monitoring practices.
Solution 2—Technology-Light, Governance-Strong Pathway: Firms with moderate technology readiness and high internal governance discipline (policy adherence, procedural coherence) can compensate for limited investment capacity by emphasizing consistency, documentation, and structured routines.
Solution 3—Compliance-Aligned, Resource-Constrained Pathway: MSMEs facing moderate regulatory requirements—not equivalent to critical infrastructure—achieve effectiveness by aligning low-cost procedural controls with sectoral compliance expectations. These firms lack extensive budgets but meet baseline regulatory obligations through documentation, periodic audits, and employee compliance training.
Solution 4—Balanced but Modest Capability Bundle: Firms with moderate technology readiness and moderate cybersecurity awareness, together with manageable economic constraints, achieve effectiveness through balanced but limited-strength capabilities, showing that small improvements in several areas can collectively generate meaningful cybersecurity performance.
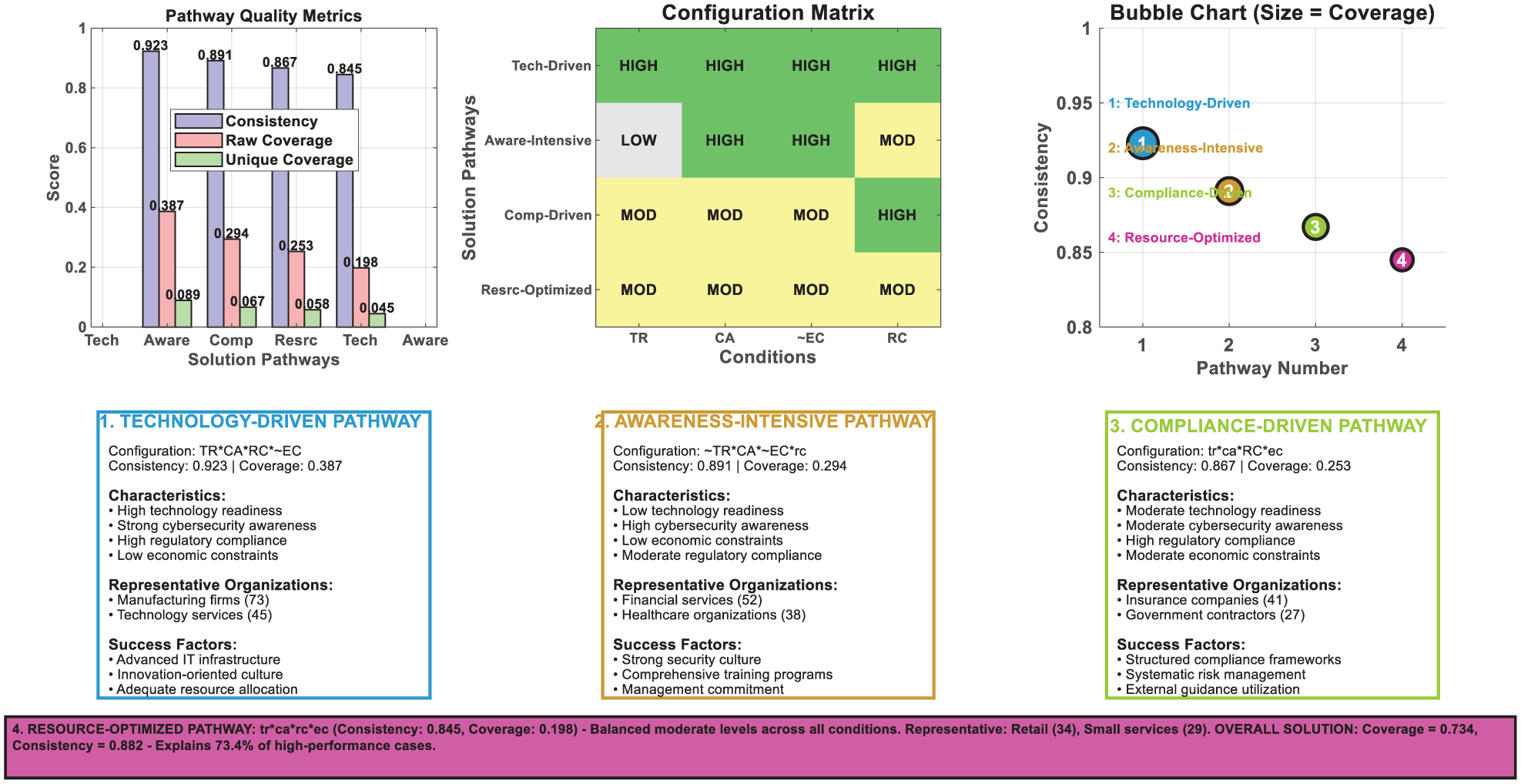
Solution pathways to high cybersecurity management effectiveness.
The overall solution achieved excellent characteristics, with a consistency of 0.882 and coverage of 0.734, indicating that the four pathways together explain 73.4% of the cases with high cybersecurity management effectiveness and demonstrate a high standard of consistency. A novel coverage test revealed limited overlap among pathways, with each solution corresponding to a distinct organizational context and strategic approach. Table 5 presents the findings of the fuzzy-set qualitative comparative analysis regarding the configurational pathways that contribute to effective cybersecurity management. Results from the qualitative comparative analysis complement results from the structural equation modeling. The fsQCA approach emphasizes the principle of equifinality, which means that organizations may achieve similar levels of cybersecurity effectiveness through different strategic configurations rather than a single optimal path. Each solution pathway has its own technological, organizational, and environmental combinations that lead to consistently high effectiveness in cybersecurity management. Coverage scores indicate the percentage of successful cases that can be attributed to the respective pathway. Consistency scores measure the reliability of each configuration in producing high effectiveness. The table has an organizational type representative for each pathway. The table clearly indicates that specific configurations are aligned with various industries and organizational characteristics. The insights from the thresholds necessary analysis offer methodological transparency and, importantly, they indicate that there is no single condition necessary for cybersecurity effectiveness. These findings underscore the configurational approach, which examines the complexity of the system.
fsQCA Solution Analysis and Pathway Characteristics.
Robustness Testing and Sensitivity Analysis
An extensive evaluation of robustness examined the stability of the solution across different specifications and threshold values. The solution is robust when consistency thresholds range from 0.75 to 0.85 and frequency thresholds range from 1 to 4 cases, as shown in Figure 11. The four main pathways remained stable across modifications, while coverage levels varied according to the threshold used.

Robustness testing and sensitivity analysis results.
Alternative calibration specifications, using different anchor points, yielded substantially similar results, with a correlation coefficient between the original and alternative membership scores of over .94 for all conditions. The use of counterfactual analysis examined whether different logical remainders yield different characteristics of the solution. Notably, the intermediate solution provided the most theoretically meaningful and empirically robust solution. A comparison between SEM and fsQCA results revealed complementary findings that enhanced the understanding of the effectiveness of cybersecurity management. The SEM results revealed that cybersecurity awareness was the strongest individual predictor of the outcome. The fsQCA analysis revealed that high cybersecurity awareness can operate in conjunction with various technological and environmental conditions to achieve effectiveness. SEM confirmed that economic constraints have effects. However, fsQCA reveals that various combinations of other factors can mitigate these constraints.
Discussion and Implications
Theoretical Contributions and Framework Validation
The empirical evidence strongly confirms the integrated theoretical framework of TOE-RBV, while also providing nuanced insights into the existing cybersecurity management theory. The strong explanatory power of the structural model (
These findings directly address the research gaps outlined in the Introduction by demonstrating how the integrated TOE–RBV framework explains both average and configurational patterns of cybersecurity management effectiveness in MSMEs. The SEM results confirm the linear contributions of technology readiness, cybersecurity awareness, regulatory compliance, and economic constraints, thereby substantiating the multi-dimensional drivers suggested by prior TOE–RBV literature. The fsQCA analysis complements these results by revealing equifinal pathways, showing that MSMEs can achieve high cybersecurity effectiveness through different combinations of capabilities rather than a single optimal configuration. This integrative perspective nuances the average effects identified in SEM: for example, while awareness emerged as the strongest linear predictor, fsQCA demonstrates that awareness-driven, technology-driven, and compliance-supported pathways can all lead to high effectiveness depending on contextual conditions. Together, these results extend theoretical understanding by showing how synergistic resource bundles, not just individual factors, shape cybersecurity outcomes in resource-constrained settings.
These reinterpreted configurational pathways align more realistically with MSME conditions than traditional, resource-intensive security models. Rather than assuming high investment capacity or sophisticated technological infrastructures, the pathways reveal how MSMEs combine procedural controls, basic technical measures, staff awareness, and compliance routines to offset financial constraints. This clearer alignment with MSME realities ensures both theoretical coherence and practical applicability, directly addressing the research gap concerning how smaller firms achieve security effectiveness without enterprise-level resources.
Configurational Insights and Equifinality Principles
The results obtained through fsQCA analysis reveal sophisticated configurations that advance the theoretical understanding of equifinality—the concept that linear antecedents have multiple pathways leading to the same outcome in cybersecurity.
There are four ways you can choose to achieve a high level of cybersecurity management effectiveness in your MSMEs. In other words, they have done so through different paths. Following the theoretical arguments supporting technological sophistication, the Technology-Driven Pathway emphasizes that technology leadership should be combined with a strong awareness and moderate compliance for effectiveness. This setup contradicts the notion that technology alone determines success in cybersecurity, demonstrating that investing in technology must be complemented by organizational capabilities for effective results. The Awareness-Intensive Pathway strongly suggests that limited-technology organizations can achieve effective cybersecurity through well-designed awareness programs and prudent allocation of resources. The results show that human capital development can compensate for technological inadequacies among MSMEs that have access to sufficient funds and adequate management commitment. The Compliance-Driven Pathway demonstrates that regulations can serve as organizing principles that facilitate the systematic evolution of cybersecurity when other factors are moderate. This configuration is particularly pertinent to organizations working in regulated industries. It demonstrates how compliance requirements can provide a helpful structure to facilitate cybersecurity development that exceeds minimum regulatory requirements. The Resource-Optimized Pathway suggests that attention across multiple fronts can achieve effectiveness even when balanced rather than superior in any one area. This arrangement is crucial for small organizations that cannot dominate any single technology, awareness, or compliance area but can optimize across multiple ones concurrently.
Interpreting these configurational findings through the Resource-Based View further highlights that the four pathways do not simply represent additive combinations of antecedents, but instead reflect distinct forms of resource synergy and strategic balance. From an RBV standpoint, high cybersecurity effectiveness emerges when firms construct internally coherent bundles of technological, organizational, and environmental resources that mutually reinforce one another. The Technology-Driven Pathway demonstrates a form of vertical synergy, where technological sophistication amplifies the value of awareness and compliance capabilities, aligning with RBV arguments that advanced resources yield superior performance only when complemented by absorptive and operational capacities. The Awareness-Intensive Pathway illustrates human-capital centric synergy, in which cultural and knowledge-based resources compensate for technological scarcity; this configuration exemplifies RBV’s emphasis on leveraging idiosyncratic, socially complex capabilities to offset tangible resource limitations. The Compliance-Driven Pathway reflects externally anchored synergy, where regulatory structures serve as scaffolding that coordinates and disciplines internal resources, balancing capabilities in a way that would not emerge from internal investments alone. Finally, the Resource-Optimized Pathway highlights strategic balance, showing that MSMEs can achieve effectiveness through the alignment of moderately developed resources when these are configured to reduce internal contradictions and maximize cross-resource complementarities. Collectively, these insights reinforce that configurational effectiveness in MSMEs is grounded not in isolated resource strength but in the strategic integration and balance of heterogeneous, mutually enabling resource bundles.
This pathway reflects organizations that place significant emphasis on regulatory compliance due to external requirements but face moderate constraints in terms of technology and financial resources. These organizations typically operate in sectors with strict regulatory requirements (e.g., healthcare or finance), where compliance drives the prioritization of security measures. Despite having moderate technology readiness and cybersecurity awareness, these organizations are constrained by their limited resources and thus may prioritize cost-effective, regulatory-driven security measures, such as compliance audits, data protection protocols, and staff training on regulatory standards, over advanced technological investments. This solution suggests that organizations with these characteristics focus on achieving basic compliance while managing cybersecurity with available resources, without investing heavily in sophisticated technology infrastructure. The empirical results show that this pathway is typical of SMEs in highly regulated sectors, where compliance is non-negotiable but where resources for broad security enhancements are limited.
This configuration characterizes MSMEs that face sector-specific regulatory obligations, but not at the intensity found in critical-infrastructure sectors. In such firms, regulatory compliance is a central driver of cybersecurity action, yet economic resources remain limited. As a result, these organizations prioritize low-cost, regulation-aligned security practices, such as formal policies, procedural controls, mandatory documentation, and staff adherence to compliance protocols, rather than large-scale technology investments.
Technology readiness and cybersecurity awareness tend to be present at moderate levels, sufficient to meet compliance requirements but not indicative of substantial technological advancement or deep security expertise. Rather than deploying advanced cybersecurity infrastructures, these firms rely on compliance-driven minimum standards, audit alignment, and process-based controls that satisfy legal requirements within their available budgets.
The empirical fsQCA results show that this compliance-oriented configuration can still yield high cybersecurity management effectiveness when procedural controls, regulatory discipline, and governance structures compensate for limited technological sophistication. This pathway is therefore typical of MSMEs in regulated service sectors (e.g., finance-adjacent services, education, or regulated retail), where compliance is necessary but where the economic capacity for extensive security investment remains constrained.
Mediation Mechanisms and Performance Linkages
The mediation analysis provides insight into the theoretical understanding of the effects of technological, organizational, and environmental factors on organizational performance outcomes. The discovery that cybersecurity management effectiveness acts as a complete barrier between most predictor variables and organizational performance supports theories that describe cybersecurity as an active capability that transforms organizational inputs into performance. The effects of technology readiness are fully mediated by cybersecurity management effectiveness, meaning that performance benefits resulting from technological investments stem from enhanced cybersecurity capabilities rather than direct mechanisms. According to this finding, it has noteworthy implications for technology investment decisions in MSMEs. In other words, technology investments should be evaluated by their contribution to cybersecurity effectiveness. The comprehensive mediation of cybersecurity awareness effects shows that awareness programs create performance benefits by generating capabilities in managing cybersecurity, rather than through any other effect. Taxpayers are often wary of spending money on cybersecurity because it appears to be preemptive spending. This research suggests that taxpayers may be willing to accept such investments. Partial mediation of economic constraints effects shows that resource constraints can hinder operating performance directly. The impact is also not negligible when it comes to indirectly affecting operational performance through cybersecurity efficiency. The results of this study suggest that organizations under economic pressure should maintain a focused investment strategy in cybersecurity. Thus, minimize the impact on direct and indirect performance.
Practical Implications for MSME Management
Based on the study, MSME managers could use evidence to optimize cybersecurity investment within available resources. The fact that cybersecurity awareness is identified as the most significant predictor suggests that organizations must invest in awareness development programs that include employee training, management commitment, and the development of a security culture. Investments in awareness lead to a greater return than similar investments in technology alone.
The configurational pathways allow strategies that fit multiple organizational contexts, as well as resource availabilities. The Technology-Driven Pathway should be pursued by organizations eager to make technological investments and implement comprehensive awareness programs, accompanied by a moderate level of compliance. Organizations with limited technological resources should consider the Awareness-Intensive Pathway, which emphasizes the development of human capital through adequate resource allocation.
A compliance-driven pathway offers organizations operating in regulated industries the opportunity to utilize regulatory requirements as a framework for systematically enhancing their cybersecurity capabilities. Tiny organizations should optimize resources to achieve a balanced focus on multiple dimensions of cybersecurity. Furthermore, the intention should not be one-dimensional excellence in a single area.
The findings of the mediation suggest that investment in cybersecurity can be evaluated in terms of growing overall cybersecurity management efficacy, rather than focusing on technology or awareness. Businesses need to adopt integrated cybersecurity management strategies that coordinate technological, awareness, compliance, and resource adequacy to benefit from operational performance.
To translate these findings into more actionable guidance for practitioners, especially those operating under economic constraints, several concrete and resource-efficient awareness interventions can be recommended. First, MSMEs can implement micro-learning based awareness modules-short, scenario-driven lessons delivered weekly through email or mobile platforms, which have been shown to substantially improve employee recognition of phishing and social engineering attempts at minimal cost. Second, organizations can institutionalize “security touchpoints,” such as brief five-minute reminders integrated into regular staff meetings, enabling continual reinforcement of secure behavior without requiring additional budget allocations. Third, role-specific awareness training can be prioritized by identifying high-impact positions (e.g., finance staff, managers handling sensitive data) and tailoring content to their threat exposure, thereby maximizing return on training investments. Fourth, MSMEs can deploy internal simulation exercises, such as periodic phishing tests or password hygiene audits, to translate awareness into behavioral change; low-cost open-source tools make these exercises feasible even for firms with limited resources. Finally, organizations can strengthen security culture by designating non-technical “security champions” within each department who disseminate best practices and serve as local points of contact, creating a peer-driven, socially reinforced awareness structure. Together, these targeted, incremental, and low-cost practices operationalize the study’s findings on awareness as a central capability and offer MSMEs practical pathways for enhancing cybersecurity resilience despite financial limitations.
In addition to these general practices, MSMEs can adopt several highly cost-effective awareness initiatives that require minimal financial outlay while yielding substantial improvements in cybersecurity posture. For instance, organizations can utilize freely available cybersecurity awareness toolkits provided by international agencies such as ENISA, NIST, and regional CERTs, which include ready-to-use posters, checklists, and training modules. MSMEs can also implement a “security minute” rotation, where employees take turns presenting one practical security tip per week using publicly available materials, thereby creating shared responsibility without formal training expenses. Another low-cost measure is the deployment of password-policy automation using built-in functions in commonly used office software suites, removing the need for proprietary security tools while promoting better credential hygiene. MSMEs can further encourage employees to adopt multi-factor authentication by integrating free or low-cost authentication apps into internal systems. Finally, establishing a simple incident-reporting channel, such as a dedicated email address or messaging thread, can dramatically accelerate response times and reinforce a culture of collective vigilance. These concrete and scalable actions help bridge the gap between the foundational importance of awareness and the practical budgetary constraints faced by MSMEs, enabling them to operationalize cybersecurity capability development in an economically sustainable manner.
For policymakers, the findings underscore the importance of designing targeted support mechanisms that help MSMEs overcome economic and knowledge-based constraints. This includes subsidized training programs, simplified regulatory guidance, and incentives for adopting baseline security controls. For MSME managers, the results indicate that strengthening cybersecurity awareness should be a top priority, as it consistently predicts management effectiveness across methods. However, awareness must be complemented by basic technology readiness, such as maintaining updated systems, secure configurations, and reliable backup procedures, and by meeting regulatory standards where applicable. A balanced emphasis on human, technical, and compliance capabilities offers MSMEs the most viable path toward cybersecurity resilience under resource constraints.
For economically constrained MSMEs, a more nuanced approach to cybersecurity investment is required. Rather than investing broadly in technology solutions, firms should prioritize those technologies that directly address their most pressing risks, which can be identified through a simple risk-assessment framework. This approach allows firms to allocate resources to cybersecurity tools that provide measurable returns in risk mitigation rather than committing to a broad, all-encompassing technology investment. For example, firms could prioritize investing in automated security monitoring tools that provide real-time detection of vulnerabilities, which would be more cost-effective than high-end security infrastructure that might exceed the firm’s operational needs.
Another cost-effective strategy is to focus on baseline security controls such as MFA and secure password policies. These foundational controls can provide significant cybersecurity benefits at relatively low cost and can be implemented quickly without requiring a large financial commitment. Additionally, MSMEs should consider investing in cybersecurity training that is specifically tailored to their employees’ roles, instead of generalized, one-size-fits-all training programs. This approach helps to focus limited training resources on areas where the risk is greatest, thereby enhancing overall effectiveness and reducing the likelihood of human error, which remains a major vulnerability for many organizations.
Additionally, MSMEs should look to external partnerships and MSSPs as a means to access high-level expertise and tools without the upfront costs of building an internal cybersecurity department. Leveraging MSSPs can help MSMEs gain access to expert advice and services that would otherwise be unaffordable, such as 24/7 security monitoring, incident response support, and vulnerability assessments. These partnerships can provide high levels of protection while allowing MSMEs to scale their security investments as their businesses grow.
Finally, policy-makers and industry groups could support MSMEs by providing cybersecurity grants, subsidized training programs, and simplified compliance frameworks that take into account the resource constraints faced by smaller firms. By reducing the financial burden of cybersecurity improvements, these initiatives can empower MSMEs to take proactive measures that would otherwise be unattainable.
Policy Implications and Regulatory Considerations
The research paper findings will enable policymakers to enhance cybersecurity capabilities among MSMEs. A well-designed regulation has a dual benefit. On one hand, it fosters compliance, and on the other, it helps enhance the enterprise’s cybersecurity levels. Regulatory frameworks can be developed by regulators, taking into account the resource constraints under which MSMEs typically operate. The substantial adverse effects of resource allocation suggest that policies related to resource allocation could yield significant gains in cybersecurity. Investment incentives for critical infrastructure cybersecurity, public–private partnerships that reduce costs for individual organizations while enhancing national cybersecurity capabilities, and shared cybersecurity service programs. Cybersecurity enhancements can take place in resource-constrained settings, if people programs are undertaken through the Awareness-Intensive Pathway. There is a need for policymakers to allocate funds that support cybersecurity education and training programs tailored to MSME contexts, including sector-level guidance and practical implementation frameworks. The configurational results suggest that policy interventions should cater to diverse organizational pathways rather than a common one. A flexible set of policies that allow for different strategic approaches and only require minimum standards could better address the diverse MSME population.
Limitations and Boundary Conditions
The interpretation of these findings should consider several boundary conditions. First, the study employs a cross-sectional design, which restricts causal inference and captures cybersecurity practices at a single point in time. Longitudinal designs would better capture how MSMEs evolve their security posture in response to changing technological and regulatory environments. Second, the measures rely on self-reported data from managers and IT personnel, which may be subject to perceptual biases despite the anonymity of responses. Third, although the sampling frame intentionally spanned multiple regions and sectors, variations in sectoral representation, particularly the under-representation of healthcare firms, may limit the generalizability of sector-specific insights. These boundary conditions highlight where future research may extend or refine the present study’s conclusions.
Limitations restrict the generalization and interpretation of research results. Due to the cross-sectional research design, we cannot infer causality, although it may have occurred. Long-term studies provide more substantial evidence regarding the cause-and-effect relationship of development in cybersecurity management. The sample composition, although varied across sectors and organizational sizes, is nevertheless concentrated in particular geographical areas that are not representative of the global MSME population as a whole. The relationships identified in this study may be affected by cultural, regulatory, and economic differences across national contexts. Despite the psychometric validation of the self-report measurement approach, it may be subject to perceptual biases that can alter the estimates of relationships. It will not hurt to dust off that book and see what is inside. Consequently, organizational-level factors, when considered in isolation, would mean missing out on individual-level variables. Future research should examine how the attributes of key decision-makers and organizational factors combine to influence cybersecurity outcomes. The existing technological focus on cybersecurity technologies may not encompass the emerging threats and technological developments that can alter the relationships identified in this study. Implementing research strategies that adapt to technological change will enhance our understanding of cybersecurity management in rapidly evolving technological environments. It is also important to note that healthcare organizations were comparatively under-represented in the dataset. Given the distinctive regulatory environment, data-sensitivity requirements, and operational risk profile of healthcare firms, this under-representation may limit the generalizability of certain findings to that sector. Future research should consider targeted sampling of healthcare MSMEs to better capture security practices in high-regulation, high-risk environments.
A further limitation concerns the purposive sampling strategy and the response rate achieved in the study. Although purposive sampling enabled the deliberate inclusion of MSMEs from multiple sectors and geographical regions, it also restricts the statistical generalizability of the findings because participation was not random. Firms that elected to participate may possess higher levels of digital engagement or cybersecurity interest than the broader MSME population, potentially introducing self-selection bias. Additionally, the observed response rate may reflect underlying non-response patterns, such as limited managerial availability, low cybersecurity awareness, or survey fatigue, that could influence the representativeness of the sample. Consequently, while the configurational patterns and structural relationships identified in this study offer valuable theoretical and practical insights, they should be interpreted as indicative rather than universally generalizable. Future research employing probabilistic sampling or stratified random sampling designs would help validate and refine the boundary conditions of the present findings.
Conclusion
This study set out to examine how technological, organizational, and environmental factors jointly influence cybersecurity management effectiveness and, in turn, organizational performance in MSMEs. By integrating the TOE framework with the Resource-Based View and applying both SEM and fsQCA, the study identified the linear effects of technology readiness, cybersecurity awareness, economic constraints, and regulatory pressures, while also revealing multiple configurational pathways through which MSMEs can achieve high cybersecurity effectiveness despite resource limitations. The results underscore the central role of cybersecurity awareness as the strongest predictor of management effectiveness and demonstrate how diverse combinations of capabilities can produce equifinal outcomes.
These findings contribute to the cybersecurity management literature by offering a multi-theoretical and multi-method understanding of how MSMEs can develop resilience in increasingly complex digital environments. For practitioners, the study highlights the importance of prioritizing awareness, aligning investments with resource constraints, and leveraging complementary technical and organizational capabilities.
By refining the configurational pathways to reflect realistic capability bundles available to MSMEs, this study strengthens the alignment between its theoretical framing, empirical analysis, and practical context. The findings demonstrate that cybersecurity effectiveness in MSMEs emerges not from high-end investments but from feasible, context-sensitive combinations of awareness, governance, baseline technology readiness, and compliance. These insights support future work aimed at building resource-aware cybersecurity models that more accurately reflect the constraints and opportunities faced by MSMEs globally.
Footnotes
Funding
The author received no financial support for the research, authorship, and/or publication of this article.
Declaration of Conflicting Interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
All data is presented in the article. Further details are available on request from the corresponding author.*
