Abstract
In today’s technologically advanced world, the escalating prevalence of phishing attacks necessitates an urgent exploration of effective countermeasures. This study delves into the crucial investigation of how self-regulation influences phishing susceptibility, while also examining the mediating role of information processing and the moderating influence of financial knowledge. A comprehensive survey was meticulously crafted, targeting 370 recent university graduates. The collected data underwent rigorous analysis using Hayes’ PROCESS macro, unveiling a mediated moderation model. The findings reveal that self-regulation does not directly predict phishing susceptibility. However, information processing, whether systematic or heuristic, significantly impacts phishing susceptibility. Additionally, information processing serves as a mediator, connecting self-regulation to phishing susceptibility. Notably, the interaction between systematic information processing and financial knowledge emerged as a significant determinant of phishing susceptibility. By establishing a comprehensive mediated moderation model, this study provides invaluable insights for individuals and organizations seeking to bolster their defenses against phishing attacks. Furthermore, it emphasizes the vital role of financial knowledge and employees’ heuristic information processing in mitigating cyber threats. This research serves as a crucial scientific contribution, offering compelling evidence that proactive management of contributing factors can effectively mitigate the escalating threats posed by phishing attacks.
Plain language summary
The crucial role of self-regulation, information processing, and financial knowledge in combating phishing attacks.
Introduction
Over the past few years, phishing has become a severe threat to individuals and organizations that involve deceptive attempts to steal sensitive or personal information using social engineering methods (Alabdan, 2020). A wide range of phishing types, including email, smishing, whaling, spear, and angler phishing, are designed by hackers who pretend to be trusted and reputed bodies and steal confidential information for illegal activities (Tandale & Pawar, 2020). The attackers usually practice persuasion and social influence principles to provoke internet users to behave a certain way (Lawson et al., 2017). For instance, sophisticated phishing attacks have targeted mobile banking users and persuaded them to open a link through SMS or email to perform a “SIM-swap” or retrieve bank-related information (Samunderu, 2014). Although server-side filter technologies attempt to prevent these scams (Gangavarapu et al., 2020), relying merely on technology does not eradicate this threat. For that, organizations that rely more on their information security system are profoundly concerned about recruiting employees who are less likely to be predisposed to phishing (Williams et al., 2018). At the corporate and government level, security education training campaigns are inaugurated to make information technology (IT) users aware of phishing attacks, but they still cannot produce the desired outcomes (Caldwell, 2016; Volkamer et al., 2018), possibly due to varying individualized ways of cognitive and information processing or other mental preoccupations (Moreno-Fernández et al., 2017). Since human vulnerabilities are equally complex to tackle as technical vulnerabilities (Yan et al., 2018), it is essential to identify why some people are more prone to phishing susceptibility than others so that the impact of such fraudulent attempts can be reduced.
While evaluating the determinants of phishing susceptibility, researchers found that information processing plays a prominent role in determining one’s vulnerability to phishing scams. While processing any kind of information, some individuals resort to a heuristic approach rather than a systematic approach leading to ignorance toward suspicious messages (Frauenstein & Flowerday, 2020). Studies also documented the significant influence of demographics (Sheng et al., 2010), detection and behavior decisions (Canfield et al., 2016), cognitive, preconscious, automatic processes, detection process difficulty, and outcome failures (R. Chen et al., 2020; Vishwanath et al., 2011). Moreover, research has shown that individual differences in self-regulation can contribute to the susceptibility to phishing attacks. Self-regulation, a psychological construct rooted in self-control and self-monitoring, involves the ability to regulate one’s thoughts, emotions, and behaviors following desired goals (Hoyle, 2010). Theoretical support for the relationship between self-regulation and phishing susceptibility can be found in the context of the Dual Process Theory (G. W. Evans & Kantrowitz, 2002; Roghanizad et al., 2021). The Dual Process Theory posits that human decision-making processes involve two distinct systems: the reflective system and the impulsive system (Chaiken & Trope, 1999). The reflective system operates consciously, involving careful deliberation, logical reasoning, and analysis. On the other hand, the impulsive system operates unconsciously, relying on heuristics, quick judgments, and automatic responses. In the context of phishing susceptibility, individuals with higher levels of self-regulation are more likely to engage the reflective system, allowing them to critically evaluate suspicious messages and resist impulsive reactions (Montañez et al., 2020; Sarno & Black, 2023). Existing literature supports the notion that self-regulation plays a crucial role in determining individuals’ vulnerability to phishing attacks. For example, studies have shown that individuals with low self-regulation tend to exhibit impulsive behaviors, such as clicking on suspicious links or sharing sensitive information without proper verification (Pradipto et al., 2016). These findings suggest that enhancing self-regulation skills could potentially reduce individuals’ susceptibility to phishing attacks.
Owing to the different cognitive abilities, attention spans, and information processing, not all individuals are equally susceptible to phishing. Systematic processing may require more cognitive resources, and efforts and the decision may be influenced by information credibility, self-efficacy, and relevant knowledge (Griffin et al., 2002; Xiao et al., 2018). The careful attention, deep thinking, and intensive reasoning involved in systematic processing may prevent individuals from falling into scams. Likewise, financial knowledge also facilitates individuals to make informed financial decisions and provides them with the degree of sophistication necessary to detect fraud (Engels et al., 2020). Prior studies assert that financially literate individuals estimate the fair value of an asset, use their numeracy skills while processing information, and are less likely to portray cognitive biases (Peters & Levin, 2008). Similarly, Engels et al. (2020) found that financial knowledge provides the degree of sophistication necessary to detect deception with the increasing complexity of fraud tactics. It is also believed that a higher degree of financial knowledge may facilitate systematic processing and mitigate heuristic processing consequently leading to reduced phishing susceptibility.
Individuals may become victims of phishing attacks despite their adequate computer literacy (Vishwanath et al., 2011), awareness, and knowledge of security threats (Diaz et al., 2020; Halevi et al., 2013). This study attempts to answer the call of prior literature, which suggested that more quantitative assessments in terms of individual behaviors and traits are needed to restrict phishing susceptibility (Ge et al., 2021; Williams et al., 2017; Yan et al., 2018). We believe that this study is the first attempt that contribute to the discipline of information security by investigating the effect of self-regulation on phishing susceptibility through heuristic-systematic information processing. The contribution to the existing literature is further expanded by introducing the moderating role of financial knowledge in the underlying relationships.
Literature Review
The advances in phishing have influenced cognitive abilities and triggered human emotions using persuasion principles (Ferreira & Teles, 2019). When users do not give adequate attention to the genuineness of the message, phishers may abuse behavioral and cognitive vulnerabilities using persuasion principles. Six persuasion principles are identified by previous studies, that is, scarcity, liking, authority, conformity or social proof, consistency or commitment, and reciprocity (Cialdini, 2007). To obtain a user response, phishers usually adopt political, religious, and financial beliefs or trending events through persuasion (Bullée et al., 2015; Vishwanath et al., 2011). Prior researchers have suggested that self-regulation, encompassing emotional regulation and cognitive control, can also play a crucial role in influencing the impact of commercial messages and advertisements (Hyland-Monks et al., 2018; Kopp, 1982). The ability to regulate emotions and exercise cognitive control aligns with the concept of self-regulation and can enhance individuals’ resistance to persuasive tactics employed in phishing attacks. Furthermore, self-regulation encompasses inhibitory control, which enables individuals to effectively manage their thoughts and actions in uncertain or complex situations (Hania et al., 2019; Seufert, 2018). This cognitive control can reduce susceptibility to deceptive tactics used in phishing attempts, as individuals with higher levels of self-regulation are better equipped to resist impulsive responses and critically evaluate suspicious messages.
Attentional flexibility, another aspect of self-regulation, plays a vital role in shifting attention away from interferences (Hofmann et al., 2012; Rothermund et al., 2008). It is argued that individuals with higher attentional flexibility are more likely to pay greater attention to email content, allowing them to detect and avoid phishing attempts. Working memory, a cognitive function linked to self-regulation, enables individuals to plan and execute complex tasks while maintaining a focus on relevant information (Cokely & Kelley, 2009; Schmeichel et al., 2008). Having a higher working memory capacity may enhance individuals’ ability to resist deceptive tactics employed in phishing attacks by enabling them to consider potential risks, evaluate information more comprehensively, and make rational decisions. The theoretical foundations of self-regulation concerning persuasion and decision-making align with the importance of self-regulation in the context of phishing susceptibility. By incorporating self-regulation as a theoretical framework, this research expands our understanding of the psychological mechanisms underlying individuals’ vulnerability to phishing attacks. It emphasizes the need to develop interventions and educational programs that enhance self-regulation skills to mitigate the risks posed by phishing attempts.
The Self-Regulation Theory (Carver & Scheier, 2000) provides a comprehensive theoretical framework to support the relationship between self-regulation. According to this theory, self-regulation involves the continuous monitoring and adjustment of one’s thoughts and behaviors in pursuit of goals. It encompasses processes such as setting goals, monitoring progress, exerting self-control, and engaging in strategic planning. Individuals with higher levels of self-regulation are more likely to exhibit better cognitive control, emotional regulation, and attentional flexibility, which aligns with the cognitive processes associated with resisting phishing attacks. Within the Self-Regulation Theory, inhibitory control, attentional flexibility, and working memory can be understood as key components of the self-regulatory process. Inhibitory control allows individuals to inhibit impulsive responses and override automatic or habitual behaviors, which can be critical in avoiding phishing scams. Attentional flexibility facilitates the shifting of attention from distractions to relevant information, enabling individuals to detect and evaluate potential threats in phishing messages. Working memory, on the other hand, supports the organization and manipulation of information, facilitating rational decision-making and reducing vulnerability to deceptive tactics.
In line with Frauenstein and Flowerday (2020) study, we have utilized persuasion principles to elucidate how self-regulation and individual behaviors are exploited, particularly in the context of Social Networking Services (SNSs). Certain personalities, cognitions, or behaviors on social media platforms are more susceptible to specific persuasion techniques when individuals feel relaxed and perceive a lower risk of deception (López-Aguilar & Solanas, 2021). Drawing from psychological literature, we propose that individuals with higher levels of self-regulation are less vulnerable to phishing scams. Self-regulation encompasses cognitive abilities that enhance persuasion processing by reducing interference, promoting planned behavior, and improving performance in social settings (Hughes et al., 2019; Wheeler et al., 2007). Hence, based on the aforementioned literature review, we posit that stronger self-regulation mitigates phishing susceptibility through enhanced information processing. Specifically, we hypothesize that
H1: A higher level of self-regulation decreases phishing susceptibility by reducing heuristic information processing.
H2: A higher level of self-regulation decreases phishing susceptibility by improving systematic information processing.
Generally, systematic responses yield a normatively correct response when responders possess relevant knowledge and expertise (Stanovich et al., 2016). Moreover, financial literacy aids individuals in applying their cognitive resources (e.g., mathematical aptitude, processing speed, attention, and memory) to comprehend monetary information (Huhmann, 2017). Thus, the relationship between the literature on numerical competence or financial knowledge and the basic features of dual-process (heuristic-systematic) theories in decision-making is largely straightforward. In the absence of any cognitive restrictions (working memory load or time constraints), more financially literate individuals generate normatively superior processes and strategies (Skagerlund et al., 2018). They are also less likely to be influenced by irrelevant information or cognitive biases when choosing between a risky and a sure option (Peters & Levin, 2008) and generally calculate a more accurate expected value (Garcia-Retamero et al., 2019). Similarly, Engels et al. (2020) found that financial knowledge provides the degree of sophistication necessary to detect fraud with the continuously increasing complexity of fraud tactics.
Further evidence also suggests that when financially literate individuals face a financial crisis or macroeconomic shocks more effectively, they are more likely to be engaged in financial management activities, and are well aware of financial instruments (Balloch et al., 2015; Klapper et al., 2013; Lusardi & Mitchell, 2011). Researchers also support the notion that financial knowledge improves investment decisions by decreasing cognitive biases (Ahmad & Shah, 2022; Sabir et al., 2019). Accordingly, we theorize that financial knowledge mitigates the positive effect of heuristic information processing on phishing susceptibility and supports systematic processing to decrease phishing schemes. Based on these arguments, we specifically hypothesize that
H3: Financial knowledge will moderate the direct positive relation between heuristic processing and phishing susceptibility, such that the relationship will be weaker when individuals have more financial knowledge
H4: Financial knowledge will moderate the direct negative relation between systematic processing and phishing susceptibility, such that the relationship will be stronger when individuals have more financial knowledge
Methodology
Sample and Data Collection
Our sample is drawn from young adults in their early career stage as they are more vulnerable to phishing than other age groups (Sheng et al., 2010). We contacted different Pakistani universities, mainly from three metropolitan cities (i.e., Lahore, Multan, and Islamabad), to provide the list of students who nearly graduated from their universities. Employees in the exploration stage of their careers are generally more indecisive (Storme & Celik, 2018) and more likely to become phishing victims. For a population above 1 million, a sample of 384 can be employed as per Krejcie and Morgan (1970) guidelines. Nonetheless, we employed a larger sample size to generalize the results of our study. A total of 780 questionnaires were distributed online using Google Forms, of which 370 were received with complete information. Our final sample size is similar to previous studies (Frauenstein & Flowerday, 2020; Sheng et al., 2010). There were 250 females (68%), and 120 males (32%). The mean age is 23.28 (S.D. = 2.80), which is considered a more vulnerable age group to phishing (Sheng et al., 2010).
Common Method Variance
The single-setting and self-reported survey methods are generally criticized for increasing the probability of common method variance (CMV) bias which may cause less accurate conclusions relating to the validity and reliability of instruments (Podsakoff & Organ, 1986). We utilized both preventative and statistical approaches to mitigate this bias. Initially, we sought feedback from the respondents about the survey’s dubiety and ambiguity through a pilot study. After guaranteeing the clarity of survey items, we distributed the questionnaire to the respondents. We provided complete information and the purpose of the study to the respondents to ensure an authentic and open response. We also encouraged respondents to avoid any identifiable personal information. Furthermore, we used Harman’s single-factor test to detect the CMV bias by incorporating all the variables in a principal component factor analysis suggested by Podsakoff et al. (2003). The test evaluated satisfactory results as the largest variance explained by a single factor was (31.18, 48.39, 49.45, 44.32 for self-regulation, information, financial knowledge, and phishing susceptibility, respectively) suggesting no concern of CMV bias. Based on the suggestion of Bagozzi et al. (1991) that CMV may influence the discriminant validity of the constructs, we confirmed that none of our constructs exceeds the single factor variance of 50%, suggesting that CMV is not a potential issue in the study.
Measurements of the Variables
The main variables of the study include phishing susceptibility (dependent), self-regulation (independent), information processing (mediating), and subject financial knowledge (moderating). The individual items and measures for these variables were adopted from previous studies after ensuring their statistical reliability (See Table 1).
Reliability Analysis and Descriptive Statistics of Self-regulation, Systematic Information Processing, Heuristics Information Processing, Financial Knowledge, and Phishing Susceptibility (N = 370).

Note. M = mean; SD = standard deviation; α = Cronbach’s alpha.
Phishing Susceptibility
Since our focus is to identify SNSs linked to phishing rather than email phishing, we have used a stimuli/image retrieved from Facebook. A multi-choice seven-item scale was used (1 = check the page for more products, 2 = try to swipe left or right to see more pictures, 3 = unsure, 4 = ask for the price, 5 = scroll away from the page, 6 = order the product, 7 = ignore the advertisement). Likewise, Frauenstein and Flowerday (2020) employed the Generalized Structural Equation Model (GSEM), taking into account the binary dependent variable that we created on testing phishing susceptibility (coded as 0 = not susceptible; 1 = susceptible). Phishing susceptibility was identified using “check the page for more products,”“try to swipe left or right to see more pictures,”“ask for the price,” and “order the product.” At the same time, no susceptible items include “scroll away from the page” and “ignore the advertisement.” The item “Unsure” represents if the respondent either does not want to respond or is not exactly sure about his/her choice.
Self-regulation
An 89-item self-report Barkley Deficits in Executive Functioning Scale (BDEFS) was developed by Barkley (2011). Recently, Kamradt et al. (2021) validated the same scale on a sample of college students with an age range between 18 and 28 years. This scale effectively measures the deficits in self-regulation in adults. It has five subscales, including self-regulation of emotion (13 items), self-motivation (12 items), self-restraint (19 items), self-organization/problem-solving (24 items), and self-management to time (21 items). The scale items are scored on a 4-point Likert scale (1 = never to 4 = very often).
Information Processing
The relevancy of the message can directly influence the persuasion of individuals. Frauenstein and Flowerday (2020) employed a survey instrument based on six stimuli/images of a social network phishing-related persuasive message. Nonetheless, we made some changes to stimuli as Frauenstein and Flowerday (2020) conducted the study in South Asia, and there are major differences in cultural norms between Pakistan and South Asia. For example, most of the population in Pakistan follows a conservative philosophy related to religious, social, and traditional perspectives (Shaikh & Ochani, 2018). Thus, we cannot receive honest responses about human sexuality, such as “video of a drunk woman appearing to be raped” or “Shocking video of a 16-year-old girl allegedly being raped.” However, we made sure that every stimulus must include at least one persuasive principle. There were no grammatical mistakes in the screenshots derived from the Facebook smartphone apps. Individuals may show certain cognitive biases based on prior encounters or personal interests while processing a specific message. The three-item scale of systematic processing is adopted from the studies of Griffin et al. (2002) and Vishwanath et al. (2011). Heuristic processing was assessed using a four-item scale initially developed and modified by Griffin et al. (2002) and Vishwanath (2015). These two scales were used by Frauenstein and Flowerday (2020) who found their reliability satisfactory. The items are to be answered on a five-point Likert scale (1 = disagree strongly to 5 = agree strongly). Systematic information processing was assessed by questions such as, “I will spend some time thinking about the picture before I made my decision, and I would briefly look at the picture and the source of picture” and “I would think about my previous experiences and predict about the originality of this advertisement.” Heuristic information processing was assessed by questions such as, “I don’t want going into the detail of the given picture” and “I would briefly look at the picture and the source of picture.”
Subjective Financial Knowledge
Financial literacy in Pakistan is very low because only 13% of adults in Pakistan are financially inclusive (i.e., accessibility to financial services and products) (Fatima, 2019). Additionally, our sample does not specifically consist of accounting and finance students, data collection related to objective financial knowledge may provide downwardly biased outcomes. Thus, we have employed subjective financial knowledge to increase the generalizability. The six-item scale developed by Deenanath et al. (2019) was used to assess to subjective financial knowledge of the respondents. The scale measures the responses on a five-point Likert scale ranging from (1) disagree strongly to (2) agree strongly. The questions were asked related to their knowledge of auto insurance, credit rating, debt, interest, credit cards, etc., and an index was computed based on the responses. Some of the scale items were, “I am anxious about financial and money affairs” and “I tend to postpone financial decisions as long as possible.” A higher value of the index denotes more financial knowledge. Deenanath et al. (2019) testified to the reliability of their scale (Cronbach’s alpha = .83).
Results
Moreover, the evidence of skewness and kurtosis of the distribution showed that the values fell under the acceptable ranges of normal distribution. Byrne (2016) argued that data is normal if skewness is between −2 to +2 and kurtosis is between −7 to +7. The Shapiro-Wilk test was found to be non-significant, which also validated that self-regulation distributions, systematic information processing, heuristics information processing, financial knowledge, and phishing susceptibility were normality distributed.
It was hypothesized that information (systematic and heuristics) would mediate the relationship between self-regulation and phishing susceptibility. Moreover, financial knowledge is likely to moderate the relationship between information (systematic and heuristics) and phishing susceptibility. Additionally, the indirect effect of information systems on self-regulation and phishing susceptibility will be moderated by financial knowledge. The analyses were carried out using SPSS (PROCESS) macro v3.5.3 (Hayes, 2017) (See Table 2).
Direct and Interaction Effects of Self-regulation, Systematic Information Processing, Heuristics Information Processing, Financial Knowledge, and Phishing Susceptibility (N = 370).

Note. Coeff = unstandardized regression coefficient; FK = financial knowledge.
The results showed that self-regulation significantly positively predicted systematic information processing while it was a significant negative predictor of heuristic information processing. In contrast, self-regulation was found to be a non-significant predictor of phishing susceptibility. In addition, whereas systematic information processing was a significant negative predictor of phishing susceptibility, heuristic information processing was a significant positive predictor of phishing susceptibility. Simultaneously, financial knowledge was a non-significant predictor of phishing susceptibility, while the interaction effect of systematic information processing and financial knowledge was significant on phishing susceptibility approving the first hypothesis.
The conditional effect of financial knowledge showed that the nature of the relationship between systematic information processing and phishing susceptibility becomes negative at low and high financial knowledge levels. However, the high level of financial knowledge strengthens the negative relationship between systematic information processing and phishing susceptibility. This finding attested to the initially proposed third and fourth hypotheses (See Figure 1). At the same time, the low level of financial knowledge buffers the negative relationship between systematic information processing and phishing susceptibility (See Figure 2). Moreover, the interaction effect of heuristic information processing and financial knowledge was found to be non-significant in determining phishing susceptibility.

Interaction effect by systematic information processing.

Interaction effect by heuristic information processing.
The indirect effects of systematic and heuristic information processing on the relationship between self-regulation and phishing susceptibility were significant (H3). Results dictated that the increase in self-regulation tends to increase systematic information processing (H2). While the increase in systematic information processing, in turn, decreases phishing susceptibility. In contrast, the increase in self-regulation tends to decrease heuristic information processing (H1). The decrease in heuristics information processing, in turn, decreases phishing susceptibility (see Table 3).
Indirect Effects of Information (Systematic and Heuristics) Between Self-regulation and Phishing Susceptibility (N = 375).
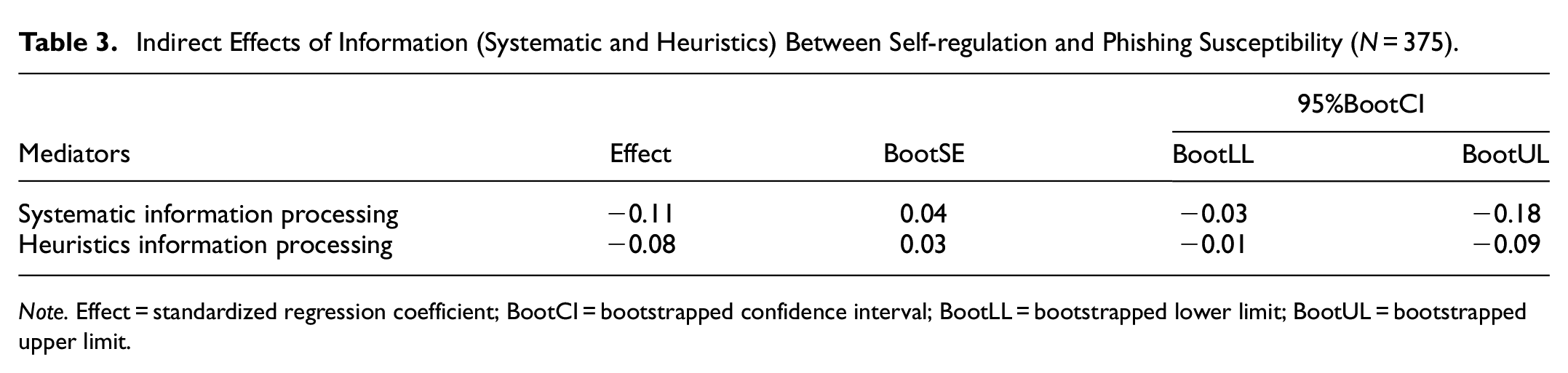
Note. Effect = standardized regression coefficient; BootCI = bootstrapped confidence interval; BootLL = bootstrapped lower limit; BootUL = bootstrapped upper limit.
The index for moderated mediation was calculated to investigate the conditional effect of financial knowledge upon the indirect effect of self-regulation on phishing susceptibility through information processing. Findings (See Figure 3) indicate the negative indirect effect of systematic information processing between self-regulation and phishing susceptibility. A portentous increase in self-regulation tends to increase systematic information processing, while an increase in systematic information processing, in turn, decreases phishing susceptibility. The connection becomes strengthened at a high level of financial knowledge confirming H4 (index = −0.002, bootSE = 0.001, bootLLCI = −0.003, bootULCI = −0.001) (Hayes, 2017) (See Table 4). In contrast, the conditional effect of financial knowledge was found to be non-significant upon the indirect effect of the heuristic information processing between the relationship of self-regulation and phishing susceptibility (H3 approved) (index = 0.001, bootSE = 0.001, bootLLCI = −0.001, bootULCI = 0.002).

Emerged statistical model for self-regulation, systematic information processing, heuristics information processing, financial knowledge, and phishing susceptibility.
Conditional Effects of Financial Knowledge on the Relationship Between Self-Regulation, Systematic Information Processing, and Phishing Susceptibility (n = 370).

Note. Effect = standardized regression coefficient; BootCI = bootstrapped confidence interval; BootLL = bootstrapped lower limit; BootUL = bootstrapped upper limit.
Discussion
The internet allows consumers worldwide to use its services with no marketplace restrictions, which fascinates individuals for its frequent use. Consequently, the presence of individuals on one platform attracts the phishers as well. Phishing; a scam that makes a person lose his money, personal information, credit card details, or social media account, is among the top cyberattack vectors threatening individuals and corporations (Dhamija et al., 2006). These attacks are aimed to trick users into thinking an e-mail or website is legitimate and to convince them to divulge their secrets or to inadvertently install malware by clicking on malicious links or attachments (Canfield et al., 2016); such scams scare millions of victims each year. Moreover, social media is a trending source for attackers to persuade victims because of the convenience of reaching out to a larger number of potential victims (Alam & El-Khatib, 2016). For that, individuals are continuously in danger of phishing attacks. Numerous studies have been conducted on phishing, but there is still a need for further exploration through empirical evidence. One promising avenue for extending this domain is to examine the relationship between self-regulation and phishing susceptibility, considering the mediating effect of information processing. This study aims to address two fundamental questions: “What is the impact of self-regulation on phishing susceptibility?” and “Does individuals’ financial knowledge influence the association between self-regulation and phishing susceptibility?” Drawing upon existing literature on phishing and information processing systems, we have found that while these variables have been discussed, the specific mechanisms through which self-regulation mitigates the risk of falling victim to phishers remain relatively unexplored. To bridge this gap, this study presents a phenomenon that sheds light on our first question regarding the effect of self-regulation on phishing susceptibility.
This study advocates that phishing susceptibility mainly occurs for two main reasons, cognitive and information processing. The human thinking process and their behavioral vulnerabilities play a vital role in responding to a threat (Musuva et al., 2019). Any limitation in cognitive processing can become the most important reason for a person’s susceptibility (Vishwanath et al., 2018). Phishers take advantage of recent events to manipulate the human thinking process (Oest et al., 2018), thus making it challenging to foresee the upcoming threat. Most of the time, people know about phishing and how to detect a threat, but they don’t know how to avoid it by utilizing prior information. It happens due to susceptibilities in human personalities, which make security awareness ineffective (Yan et al., 2018). Thus, to effectively protect from phishing, individuals need to strengthen their information processing system. Research (Kleitman et al., 2018; Vishwanath et al., 2011) documented that individuals have their patterns of perceiving events, and how they process that event solely depends on their cognitive patterns. Generally, individuals tend to process information heuristically rather than systematically, which leads them to ignorance of phishing threats (Frauenstein et al., 2020). Heuristic information processing tends to require less cognitive thinking, which leads the individual to fall for a phishing scam. Systematic information processing requires more cognitive thinking, which can detect any threat (Griffin et al., 2002; Xiao et al., 2018). Our findings align with prior literature, which concluded that an efficient information processing system reduces the vulnerability caused by phishers (Frauenstein & Flowerday, 2020; Harrison et al., 2016; Vishwanath et al., 2011).
Furthermore, this study also demonstrates that individuals with strong self-regulation do not behave similarly, which directly answers our second question, that is, does individuals’ financial knowledge affect the association between self-regulation and phishing susceptibility. Our findings suggest that the negative relationship between self-regulation and phishing susceptibility is strengthened for high financial knowledge. Literature on financial knowledge and phishing susceptibility has indicated that individuals with higher financial knowledge tend to have a better understanding of the risks associated with phishing attacks (Kumaraguru et al., 2007). They may possess a greater awareness of common phishing techniques, such as fraudulent emails or deceptive websites designed to steal sensitive information (Liu & Campbell, 2017). Consequently, individuals with high financial knowledge are more likely to engage in self-regulatory behaviors to protect themselves from falling victim to phishing scams. Self-regulation refers to the ability to control and direct one’s thoughts, emotions, and actions toward achieving specific goals (Baumeister et al., 2007). In the context of phishing, individuals with stronger self-regulation skills are more likely to engage in careful information processing, critically evaluate the legitimacy of online messages, and resist impulsive responses (Gavett et al., 2017). They may also be more vigilant and proactive in implementing security measures, such as using strong passwords, regularly updating security software, and being cautious about sharing personal information online (Egelman et al., 2013).
The Protection Motivation Theory (PMT) provides a theoretical framework to understand individuals’ responses to threats and their motivation to adopt protective behaviors (Rogers, 1983). PMT suggests that two main factors influence individuals’ protective behaviors: threat appraisal and coping appraisal. In the context of phishing, threat appraisal involves perceiving the risk and severity of being victimized by phishing attacks, while coping appraisal refers to evaluating one’s ability to effectively respond to these threats. Drawing upon PMT, it can be argued that individuals with high financial knowledge possess a more accurate threat appraisal of phishing attacks. Their knowledge of common phishing techniques, combined with their understanding of the potential consequences, strengthens their motivation to engage in self-regulatory behaviors (Lokanan & Liu, 2021). By actively applying their financial knowledge and utilizing their self-regulation skills, these individuals are better equipped to resist phishing attempts and protect their personal information. Supporting this notion, previous research has found that individuals with high levels of financial literacy demonstrate a greater ability to recognize and avoid financial scams, including phishing attacks (H. Chen & Volpe, 1998; Lusardi & Mitchell, 2011). These individuals are more likely to employ critical thinking, use external information sources to verify the legitimacy of online requests and exercise caution when sharing financial or personal information online (Cheshire et al., 2010).
The findings of the study indicate several important relationships and provide valuable insights into understanding the factors that influence individuals’ vulnerability to phishing attacks. One key finding is the significant interaction effect between systematic information processing and financial knowledge, which predicts phishing susceptibility. This finding highlights the nuanced nature of the relationship, suggesting that the protective effect of systematic information processing against phishing susceptibility is contingent upon individuals’ level of financial knowledge. This finding aligns with the Cognitive Reflection model (Shtulman & Young, 2023), which posits that individuals’ ability to override intuitive and erroneous responses is influenced by their domain-specific knowledge. In the context of phishing, individuals with higher financial knowledge demonstrate a heightened understanding of the potential risks involved and are more proficient at leveraging systematic processing strategies to critically evaluate online messages. As a result, their susceptibility to phishing attacks is mitigated. These findings contribute to the growing body of literature on phishing by shedding light on the underlying mechanisms and providing empirical evidence for the interplay between cognitive processes, domain-specific knowledge, and susceptibility to phishing attempts. By incorporating the cognitive reflection model, this study underscores the importance of considering individuals’ level of financial knowledge as a moderating factor that influences the effectiveness of systematic information processing in reducing phishing susceptibility. The observed interaction effect highlights the need for targeted educational interventions that enhance individuals’ financial knowledge, particularly in the context of online security. By equipping individuals with a deeper understanding of the risks associated with phishing attacks, interventions can empower users to make informed decisions and employ systematic processing strategies when encountering suspicious online messages. Such interventions can play a pivotal role in strengthening users’ defenses against phishing attempts and reducing the overall success rate of these fraudulent activities. In conclusion, this study’s findings contribute to a more comprehensive understanding of the multifaceted nature of phishing susceptibility. The identification of the interaction effect between systematic information processing and financial knowledge highlights the importance of considering individuals’ domain-specific knowledge when designing strategies to mitigate phishing risks. Results further explained that self-regulation cannot directly predict phishing susceptibility but through cognitive information processing and financial knowledge. The Dual Process Theory (J. S. B. Evans, 2017) suggests that self-regulation indirectly affects phishing susceptibility by influencing cognitive information processing. Meanwhile, the Protection Motivation Theory (Norman et al., 2015; Rogers, 1983) explains how self-regulation impacts individuals’ motivation to protect themselves through accurate threat perception and confidence in protective measures. By employing systematic processing and utilizing financial knowledge, individuals with higher self-regulation are better equipped to detect and resist phishing attempts, reducing their vulnerability.
Overall, the implications of this study highlight the need to move beyond solely focusing on self-regulation as a predictor of phishing susceptibility. Instead, a comprehensive approach that considers the role of cognitive information processing and financial knowledge can provide valuable insights for developing effective interventions and strategies to mitigate the risks associated with phishing attacks. Recognizing that self-regulation plays a significant role in reducing susceptibility to phishing attacks through cognitive processing and financial knowledge, interventions can focus on enhancing these factors. Strategies may include providing training programs that promote systematic information processing skills and financial literacy in individuals, particularly those with lower levels of self-regulation. By improving cognitive processing abilities and knowledge related to online financial transactions, individuals may be better equipped to detect and avoid phishing attempts. Educating individuals about the risks and consequences of phishing attacks, as well as providing them with practical knowledge and skills to identify and respond to phishing attempts, can enhance their ability to protect themselves online. Organizations and institutions can implement cybersecurity training programs that address both cognitive information processing strategies and financial knowledge, thereby empowering individuals to make informed decisions and reduce their susceptibility to phishing threats.
Limitations and Recommendations
Despite the interesting findings, there are some concerns regarding this study. First, the measurement of self-regulation was based on self-rated instruments, which may introduce limitations such as the possibility of positive response bias. Respondents might tend to present themselves in a favorable light, which increases the potential for common method variance (CMV). To address this issue, we encourage future researchers to collect data from multiple sources and consider using multi-wave designs to assess the robustness of the findings. Additionally, demographic factors inherent in different cultures, such as wealth, age, and job status, could potentially influence phishing susceptibility. Previous research has shown that individuals from disadvantaged backgrounds may be more vulnerable to phishing attempts. Similarly, younger individuals who tend to be more risk-takers may also be easier targets for scammers. Therefore, future studies need to control for such factors to prevent potential inflation of the relationships between the study variables. To address these concerns, we recommend employing more objective measures of self-regulation and collecting data from diverse sources to ensure a comprehensive understanding of the construct. Furthermore, researchers should consider including demographic variables as covariates or conducting subgroup analyses to examine their potential impact on phishing susceptibility. By addressing these limitations and considering the broader context of demographic factors, future research can build upon this study and provide more nuanced insights into the relationship between self-regulation, financial knowledge, and phishing susceptibility.
Conclusion
This study explored the relationship between self-regulation, cognitive information processing, financial knowledge, and phishing susceptibility. The findings indicate that self-regulation indirectly affects phishing susceptibility through its influence on cognitive processing and financial knowledge. The Dual Process Theory helped explain how individuals with higher self-regulation engage in systematic processing, enhancing their ability to detect phishing attempts. Conversely, those with lower self-regulation may rely more on heuristic-based shortcuts, making them more vulnerable to phishing attacks. The Protection Motivation Theory highlighted that individuals with higher self-regulation accurately perceive the severity of the threat and have greater confidence in their ability to protect themselves. This confidence, coupled with systematic processing and financial knowledge, reduces their vulnerability to phishing attacks. These findings underscore the importance of promoting self-regulatory skills, cognitive processing strategies, and financial knowledge to mitigate the risks of phishing. Educational initiatives should focus on these areas to empower individuals in recognizing and effectively responding to online threats. Overall, this study contributes to the literature by shedding light on the indirect effects of self-regulation on phishing susceptibility and the underlying mechanisms involved. By addressing these factors, individuals can enhance their resilience against phishing attacks and safeguard their personal and financial information in the digital age.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Ethical Approval
Research Ethics Committee at Institute of Southern Punjab approved the research procedure and reviewed it according to research ethics criteria provided by the institute. All the participants of research were assured of their anonymity and that data will be used for research purposes.
Consent to Participate
Participants filled a consent form prior to participating in the research. In which it was clearly mentioned that they had the right to withdraw from research anytime they want to and they had no objection on letting their provided information used for research.
Consent for Publication
All the authors of this research have no conflict of interest and give consent to journal to publish the information for knowledge of future researchers and clinical practitioners.
