Abstract
With rapid development in the Internet infrastructure, new and innovative services using the Internet of Things (IoT) have emerged. Despite the wide range of topics regarding IoT services that have been discussed, regulatory concerns solely concentrate on personal information and privacy protection in academic research and legislation. In other words, a comprehensive regulatory framework for IoT services should be developed with potential consumers in mind; however, relevant studies are lacking. To bridge this research gap, this study estimates consumer preferences to build an appropriate regulation for IoT service deployment. The study uses conjoint analysis and a layered model to investigate the importance of attributes for IoT services as part of the consideration supporting IoT regulations. Based on the estimation results, all attributes of the IoT services are relevant to potential consumers, and as an example of IoT applications, the Big Data analysis application is more critical to consumers in terms of marginal willingness-to-pay and relative importance. Furthermore, a new type of vertical integration is appealing to potential customers. Policymakers can benefit from the development of various IoT policies, simultaneous pursuits of IoT application innovation and privacy concerns, and nondiscriminatory regulation principles.
Introduction
The Internet has evolved owing to technological advancements in many areas, thereby contributing to the development of innovative contents, services, and applications. The explicit and straightforward resolution of the Internet is a “global information system” designated by the Federal Networking Council in 1995. However, information services over the Internet are categorized differently from traditional communication services, such as voice telephony, radio communication, broadcasting services, and cable TV, which were categorized before the Internet emerged. Thus, different regulatory frameworks have been implemented for the Internet (e.g., Schlesinger, 2022).
The traditional regulatory framework before the emergence of the Internet was the vertical or silo regulatory framework, which classifies communication services into voice, broadcasting, and cable TV services, and imposes separate regulations on each type (Frieden, 2003). However, since the Internet’s inception, newly converged telecommunications and broadcasting services over the Internet have not been classified into separate groups; hence, no regulation has been imposed on new Internet-based information services. For example, the voice over Internet protocol (VoIP) service is remarkably similar to the traditional voice telecommunication service. However, the VoIP service was not classified as a telecommunication service as voice signals are transported through the Internet network. Thus, during the hand-off approach period, VoIP service providers had sufficient time available in the business operations for open-access Internet networks (D. H. Shin, 2006). In other words, the lack of regulations made it easy for new and diverse content, service, or application firms to enter and exit the market.
Consequently, studies and discussions on a layered or horizontal regulatory framework were conducted to provide a suitable regulatory framework for information services based on the Internet (Frieden, 2003; D. Kim, 2018; Werbach, 2002; Wu, 2006). As a simplification of D. Kim (2018), the horizontal regulatory framework classifies the entire Internet-related services into two layers: the first is a network layer that transports digital data, and the second is a content layer that produces contents, services, or applications. Furthermore, each layer is subject to a varied set of regulations. Generally, economic regulations concerning competition and discrimination issues are imposed on the network layer (D. Lee & Kim, 2014), whereas content regulations concerning sociocultural issues are imposed on the content layer (C. Lee et al., 2017).
With the rapid development of Internet infrastructure, new and innovative services have emerged, such as the Internet of Things (IoT), which is predicted to be prevalent worldwide (Boos et al., 2013; Lu et al., 2018; Onungwa et al., 2021; Popescul & Georgescu, 2013; Winter, 2014). Moreover, various IoT services have been launched and are presently available to consumers (Gaurav et al., 2023; Tewari & Gupta, 2020). In conjunction with the emergence of IoT services, a new regulatory framework that differs from the horizontal or layered regulatory frameworks in the Internet era will be required.
Although numerous topics pertaining to IoT services, such as security, healthcare, manufacturing, and business processes, as well as the methods of service development in an IoT environment, have been discussed (Korzun et al., 2013; Sestino et al., 2020), regulatory concerns regarding IoT services are limited to personal information and privacy protection, both in the academic research (Brass & Sowell, 2021; W. Kim et al., 2022; Peppet, 2014; Weber, 2009, 2010) and legislation areas (European Union, 2016; Weber, 2015). Following a systematic review of IoT-related studies, Nord et al. (2019) stated that the literature on regulatory issues is mainly linked to securities. A comprehensive regulatory framework for IoT services should be developed in terms of potential consumers; however, relevant studies are lacking. This is regarded as a regulatory gap as well as a research gap where the growth of new innovative services can be restrained (Rommetveit & van Dijk, 2022). To bridge these gaps, we should consider the opinions of consumers using new services while developing appropriate regulations that do not restrict the benefits of IoT services for them. As the purpose of regulations is to protect consumer welfare and promote industries (Horwitz, 1989), estimating consumer preferences and incorporating them into regulations become a necessary procedure.
As a modified version of the research conducted by Na (2017), this study estimates consumer preferences to build an appropriate regulation for IoT service deployment. Using conjoint analysis, the study investigates the importance of attributes for IoT services as part of the consideration supporting IoT regulations. Generally, conjoint analysis measures consumer preferences toward attributes embedded in products and services (Green & Srinivasan, 1990). Recently, numerous studies have suggested policy alternatives using conjoint analysis in various fields (J. Lee et al., 2006; M. Lee et al., 2017; J. Shin et al., 2014). The projected findings of this study can be used to bridge the gap in IoT regulation by considering the preferences, willingness-to-pay (WTP), and relative relevance of each attribute of IoT services among potential consumers.
The following is a summary of the estimation results. First, all attributes of IoT services are significant to potential customers. Second, as a representative of IoT applications, the Big Data analysis application is more critical to consumers in terms of marginal WTP and relative importance. Third, a new type of vertical integration is appealing to prospective consumers. Based on the estimation results, the following contributions can be made to IoT services:
Suggestions regarding diverse IoT policies, including vertical regulation
Concurrent pursuits of IoT application innovation and privacy concerns
Nondiscrimination regulation principles
The remainder of this study is structured as follows. Section 2 explains the basic concept of IoT from previous studies to construct a research framework. Section 3 presents the empirical analysis to examine users’ preferences, resulting in a few regulatory concerns regarding IoT services. Section 4 explains the result of the empirical analysis and Section 5 discusses on new IoT regulation direction. Finally, Section 6 concludes this study.
Basic Concept of IoT and Layered Approach
For the comprehension of social science readers, Section 2 introduces the fundamental concept of IoT from early studies. Additionally, this section classifies IoT component classifications suggested by the existing literature to explain the construction process of the layer-based approach framework.
Ashton (2009) noted that the term IoT was first used by Procter & Gamble during a presentation in 1999, which demonstrated the results of studies on how radio frequency identification (RFID) would be better in the Internet environment from the perspective of the supply chain. Hence, numerous studies have claimed that RFID technology was the origin of IoT (Atzori et al., 2010; Gubbi et al., 2013). As a new concept, Atzori et al. (2010) defined IoT as the convergence of three visions: things-oriented, Internet-oriented, and semantic-oriented visions. Miorandi et al. (2012) stated that IoT is universally used from three standpoints: (1) as a global network interconnecting smart objects, (2) as a set of supporting technologies, and (3) as an ensemble of applications and services.
International Telecommunication Union (ITU, 2012) defined IoT as “a global infrastructure for the information society enabling advanced services by interconnecting (physical and virtual) things based on existing and evolving, interoperable information and communication technologies.” Moreover, Minerva et al. (2015) stated the following: “An IoT is a network that connects uniquely identifiable ‘Things’ to the Internet. …… information about the ‘Thing’ can be collected and the state of the ‘Thing’ can be changed from anywhere, anytime, by anything.” As explained by the ITU (2005), the IoT application area can be expanded to anything that can be connected to the Internet, which is the new dimension of the IoT: Any THING can have a connection.
Following the aforementioned definitions of the IoT, this study proposes a new definition with a three-layered model of the IoT service. The IoT is an Internet-related service comprising a sensing device, the Internet network, and an application. Sensing devices encompass the capability of computation; thus, they can automatically sensor information and transport it to the Internet network. The Internet network of the IoT service has two interfaces: one for sensing devices and the other for applications for information analysis. An interface for sensing devices is usually a wireless network; however, it varies with the type of service. If a sensing device is not in motion, Wi-Fi and Bluetooth are more appropriate. Conversely, mobile network technologies are more appropriate if in motion. Another interface for IoT applications is usually a fixed-line network, which varies with the type of service. A dedicated line or private network would be more appropriate if the IoT service deals with critical information, such as a human being’s life, public security, or disaster monitoring. Although sensing devices with the capability of computation and networking are important, analyzing the collected information is the most crucial component of the IoT service, as the analyzed information helps track end users’ post actions. The end user can either be a human being, other devices, or machinery. If the solution is feedbacked to the human user, they will decide the post-action following the feedbacked solution. Moreover, if the end user is another device or machinery, it operates in the direction of the feedbacked solution.
A horizontal or layered regulatory framework roughly divides traditional Internet service into network and content layers. Atzori et al. (2010) divided IoT services into two groups based on the enabling technologies: (1) middleware, which performs analysis of collected raw data and tasks related to securities and management, and (2) sensing and communication technologies, which sense raw data and transport them to the middleware. Similarly, Minerva et al. (2015) suggested three-tier architecture similar to the three-layer model in this study. It divides IoT services into application, networking and data communications, and sensing; however, the three-layered model in this study divides IoT services into three layers from the service perspective. The three layers comprising one IoT service are IoT devices, network, and IoT application layer.
This study proposes dividing IoT service into three layers, similar to the traditional Internet regulatory framework (Kong & Ma, 2020). The IoT device layer is a set of devices capable of sensing raw data, computing, and sending raw data to a network. The IoT device layer bears a conceptual similarity with the definition of sensing by Minerva et al. (2015) and device by ITU (2012). The network layer is the Internet network, which connects IoT devices to IoT applications and IoT applications to users. The IoT application layer is a computing system that analyzes raw data from IoT devices, develops a better solution, and provides feedback to the user. On behalf of IoT service users, IoT applications analyze raw data gathered from IoT users and provide possible solutions to them. IoT applications are similar to middleware as claimed by Atzori et al. (2010) and application as claimed by Minerva et al. (2015). Figure 1 describes the three-layer model.

Three-layer model in IoT.
This section constructs a three-layer model that can describe IoT services and their components after reviewing several definitions and core components of IoT addressed in previous literature. As this study analyzes the preferences of IoT services that are perceived as important attributes for potential consumers, and as the structure of preferences is based on a three-layer model, an applicable and socially relevant regulatory system can be developed for each layer.
Empirical Analysis
This study investigates consumer preferences for imaginary IoT services reflecting the regulation and innovation conditions. A mixed logit methodology and a conjoint survey were used for the analysis.
Description of Empirical Analysis
The application area of IoT services is extremely diverse across sensing, network, and analysis technologies. Miorandi et al. (2012) categorized IoT application areas into smart homes and smart building, smart cities, environmental monitoring, smart businesses by inventory and product management, and security and surveillance. Gubbi et al. (2013) categorized IoT services into personal, home, enterprise, utility, and mobile. However, two types of separation guidance, namely, consumer status and IoT device status, are required to investigate consumers’ preferences for IoT services. Consumer status is divided into three groups: individual, enterprise or business, and government or public area. Whereas, IoT device status is divided into two groups: mobile device and fixed device.
This study assumed a household environmental (temperature, moisture, and indoor air quality) monitoring service as an imaginary IoT service. A consumer of the imaginary IoT service is an individual and a sensing device attached to the house, which implies “fixed.” To use or subscribe to this IoT service, consumers should purchase IoT devices capable of sensing environmental conditions and transmitting information to the IoT application. Accordingly, a survey questionnaire focuses on the relationship between (1) IoT devices and the network and (2) IoT devices and the IoT application. According to Korzun et al. (2019), smartness properties such as location awareness, design principles, and user experience are key enablers that may be preferred by IoT service consumers. However, unlike Korzun et al. (2019)’s examples of e-tourism and e-healthcare, this study assumed an imaginary IoT service regarding a household environmental monitoring, which is a more stationary situation—individual and fixed; thus, such smartness properties are not incorporated into the survey.
Regarding innovation, a private network for the network layer and Big Data analysis for the IoT application layer were cited as examples. Prior to IoT services, private networks were developed and frequently used in business area; however, these networks were not widely preferred by households or for personal Internet access. Therefore, private networks were selected as an attribute of an IoT service, which could be interpreted as a consumer preference for a private or prioritized network with a more innovative IoT service in the future. In addition to being created independently of IoT services, Big Data analysis will be widely adopted owing to innovations in the IoT application. However, Big Data require a mixture of data from other sources; hence, protecting personal information will become a matter of concern. The questionnaire sufficiently explains this situation. Finally, to reflect economic concerns in the IoT era, this study considered consumer preferences for vertical integration between IoT devices and the network and IoT devices and the IoT application. Without integration, consumers can arbitrarily select a network or an IoT application following the purchase of IoT devices.
Hence, four attributes, namely, (1) private networks, (2) selecting a network, (3) selecting an IoT application, and (4) Big Data analysis for imaginary IoT services, were chosen to estimate consumer preferences. Moreover, a monthly usage fee was included as another attribute to calculate consumers’ WTP for each attribute. After conducting a mixed logit analysis, this study estimated the consumer preference or utility for each attribute of the IoT service. With these estimated preferences, the median marginal WTP and the relative importance of each attribute were calculated.
Methodology: Mixed Logit
This study uses a mixed logit model of conjoint analysis with a survey to investigate consumer preferences for IoT services. Although conjoint analysis has primarily been used to measure consumer preferences for attributes embedded in products and services, its applications to public policy continue to provide valuable insights for policy decisions (Green & Srinivasan, 1978), such as renewable portfolio standard of energy policy (J. Kim et al., 2012) and the number portability of telecommunication policy (J. Lee et al., 2006). Green and Srinivasan (1978) stated that conjoint analysis is useful for estimating the monetary value of each policy attribute. In particular, the assumption that the heterogeneity of individuals has been revealed in newly emerged products or services justifies the use of stated preference, which is suitable for employing conjoint analysis. Compared with other discrete choice models based on a random utility model, such as a logit or probit model, the mixed logit model has several advantages. The model can reflect consumers’ heterogeneity concerning their preferences for goods or services, select different distributions for each attribute, and relax the robust assumption of independence from irrelevant alternatives imposed on the logit model (Train, 2009). In the random utility model, consumer n can have utility
Consumer utility is composed of a deterministic term
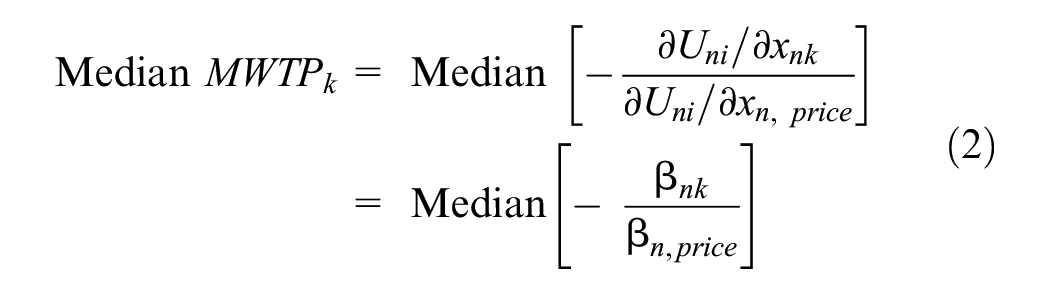
Marginal Willingness-to-Pay
Marginal WTP (MWTP) refers to the monetary unit that the consumer will pay additionally to maintain a comparable level of utility with one unit change of another attribute of a good or service. The MWTP for attribute k is calculated using Equation 2 with estimated coefficients of
Relative Importance of Attributes
Depending on the relative value that consumers attach to each feature, as determined by Equation 3 and as utilized by Na et al. (2020), each attribute has a varied impact on the decision-making or selection process.
Attributes and Levels
The attributes and their levels for the conjoint survey are represented in Table 1. An orthogonal test is used to select eight alternatives choice. The price attribute is assumed to have a log-normal distribution, whereas the four other attributes have a normal distribution. Table 2 shows the eight alternatives.
Attributes and Levels.

Eight Alternatives.

Analysis Result
Conjoint Survey
An online conjoint survey was conducted with 923 respondents from October 27 to 31, 2016. Each respondent was asked to select their preferred IoT service between two alternatives in one choice set. The four-section processes led to a total of eight orthogonal alternatives, and this choice process with a different choice set was repeated twice for a more detailed analysis and the elimination of an inaccurate choice response. Table 3 shows the basic statistics of survey respondents.
Basic Statistics of Survey Respondents.

Estimated Coefficients: IoT Service Users’ Preferences
Table 4 shows the estimated coefficient
Estimated Coefficients.

Statistically significant at 1% confidence level.
The nonsignificance of the private network attribute can be interpreted as follows: The IoT service for household environmental monitoring assumed in the conjoint survey does not deal with emergencies, human life, or public disasters. Therefore, users of this service may not be concerned with the precise transport of information without delay, jitter, or distortion.
Median Marginal Willingness-to-Pay
By using Equation 2, Table 5 shows the calculated median MWTP for each attribute. This result reveals that IoT service users have the highest WTP in varied probable conditions; when they can select an IoT application, followed by when they can select the Internet network provider; when the IoT application provides solutions through Big Data analysis; and when they can select a private Internet network.
Median Marginal Willingness-to-Pay (MWTP) for Each Attribute (Unit: KRW).

Note. As of February 22nd, 2023, 1 USD is equal to 1,303 KRW.
Relative Importance
Table 6 shows the relative importance levels of the attributes of IoT services, based on Equation 3. When a consumer chooses a specific good or service, he or she is indicating the attribute’s relative importance, that is, how significant he or she considers it to be compared to other attributes. Apart from the price attribute, the relative importance levels for the other four attributes do not differ significantly, although Big Data analysis is slightly more important.
Relative Importance for Each Attribute.

We additionally conducted a t-test to determine the statistical significance of the value difference by comparing the relative importance of Big Data and each of the other attributes. The result confirms that the relative importance of Big Data is statistically greater than that of all other attributes with a 1% significance level; RI (Big Data) > RI (private network), t = 4.2392; RI (Big Data) > RI (network selection), t = 5.4995; RI (Big Data) > RI (application network), t = 8.4780.
Explanation of the Results
The imaginary IoT service assumed in the survey, that is, the household environmental monitoring service, cannot represent all IoT services in the market or those in development. However, some interesting findings are as follows.
First, IoT service users consider all four attributes as important factors in IoT services. Private network and Big Data analysis represent innovations at the network and IoT application layers, respectively. Moreover, the selection of the network provider and the IoT application explains whether the IoT device layer is vertically integrated with the network and the IoT application layer. Finally, private network represents the vertical regulation concern for IoT services to transmit information precisely, on time, and to the targeted destination. This finding implies that innovations at all three layers, vertical regulation concern, and nonvertical integration are equally important in an IoT service. With the addition of the IoT device layer to the IoT service, a new type of vertical integration is possible: vertical integration with an IoT device layer and an IoT application layer. These two layers do not directly interact; consequently, this integration case differs from others, such as the integration of IoT devices and the network or the integration of the network and an IoT application. Thus, regulatory policy instruments are required to guarantee that IoT service users can choose IoT applications. This implies that the IoT application layer should not discriminate against IoT devices.
Second, the relative importance of Big Data analysis seems slightly higher than that of the other three attributes, except for the price attribute. Moreover, the t-test result shows that the relative importance of the Big Data attribute is greater than that of the other three attributes with a 1% significance level. Additionally, the relative importance of 417 of 923 respondents is the largest for the Big Data attribute. This indicates that IoT service users expect a better solution from an IoT application. However, detailed analysis results and feedbacked solutions need more information and IoT application innovations, such as analysis methods and techniques. Thus, appropriate regulations on IoT applications that handle large amounts of data or information are also required.
Finally, the MWTP for selecting an IoT application is the highest—640 KRW or 0.5 USD, and all respondents’ MWTP for this attribute is greater than zero; that is, the minimum value of MWTP is 43 KRW or 0.02 USD. Because the preference for IoT applications is obvious when compared with other attributes, and all MWTPs are relatively low compared with telecommunication subscription fee (47,600 KRW or 36.5 USD in mobile communication and 19,700 KRW or 15.1 USD in fixed Internet, according to Korea Media Panel), firms can use this result to attract consumers. Consistent with the literature, the web browsing service—a platform for providing various applications—has the highest MWTP among other Internet services in the era of Internet diffusion (D. Lee et al., 2015). Therefore, a proactive regulatory framework should be prepared as it is anticipated that firms will use discrimination as part of their strategic conduct to maximize surplus.
Discussion
Based on the preceding empirical analysis, we can engage in the following discussion regarding IoT-related regulatory policy. First, the application layer can lead to innovation. Because the analysis indicates that potential consumers have a higher preference for application selection, the degree of related regulation should be reduced. This is consistent with the D. Lee and Kim’s (2014) finding, which states that effective application diffusion in the Internet-based industry can be achieved with relaxed regulation. Recent IoT service launches include smart contracts utilizing blockchain technology (Jamil et al., 2022), healthcare applications (Hammad et al., 2022; Sarrab & Alshohoumi, 2021), and security applications (Gaurav et al., 2023; Tewari & Gupta, 2020). Moreover, IoT offers numerous opportunities for creative services; IoT policy should be able to foster application layer innovation.
Second, rather than the vertically integrated services that were predetermined, potential customers prefer their own service combinations. When firms can provide vertically integrated services, they will concentrate on such service bundles to seize market dominance. In such a scenario, the regulatory policy should be able to protect the consumers’ right to choose a service combination, such as by limiting discounts on existing bundles and mandating the delivery of newly integrated services. Specifically, new bundled products and services from the device layer and application layer can be an alternative for promoting consumers’ own combinations. Consistent with the argument of Na et al. (2018), it is expected that the emerging business models resulting from the convergence of heterogeneous product and service will be launched within a balanced but differentiated regulatory framework.
Third, as preferences for Big Data analysis are the most important attribute of potential consumers, and even MWTP for Big Data analysis is not so expensive, from 179 KRW or 0.15 USD, an adequate data regulation policy is required. Fundamentally, efforts to secure private information are essential. However, such personal information should be easily shared and traded on the data market as an individual’s asset. For example, MyData is an ongoing trend for promoting the use of personal data in conventional industries (Hwangbo et al., 2021). To use a variety of Big Data application services, collected data in an IoT environment can be transacted for sufficient compensation. Specifically, the incorporation of semantics into IoT applications can broaden the scope of Big Data applications for intelligent data-based convergence services (Sejdiu et al., 2020).
Conclusion
This study conducted an empirical analysis using a mixed logit analysis with a conjoint survey to investigate users’ preferences for IoT services and incorporate them into IoT regulations to address the issue that regulatory concerns regarding IoT services are limited to the protection of personal information and privacy. According to the estimation results, all attributes of IoT services, including a dedicated network, the ability to select the network, the ability to select the application, and Big Data analysis, are important to potential consumers, with Big Data analysis being the most crucial in terms of MWTP and relative importance. According to MWTP, potential customers are willing to pay 640 KRW or 0.5 USD for selection of IoT application, 440 KRW or 0.35 USD for selection of network, 179 KRW or 0.15 USD for Big Data analysis, and 22 KRW or 0.15 USD for private network.
The following practical contributions to the IoT regulation can be derived from the analysis result. First, IoT users consider the precise and on-time delivery of information as equally important as the other attributes. This implies the necessity of a regulatory framework, such as the vertical regulatory framework, to ensure timely and exact transmission of data, especially when dealing with sensitive information, such as in the healthcare field. Second, Big Data analysis is the most important attribute for IoT users, implying that users will need more detailed and precise analysis and feedback. For more detailed Big Data analysis, IoT devices need to sensor more raw data, and IoT applications need to collect more information from other sources. Numerous studies, such as Na et al. (2020) and W. Kim et al. (2022), have argued that privacy and security issues are critical in this situation. Thus, regulations addressing these concerns should be implemented at the device and application layers. Lastly, the IoT service users’ WTP is the highest in the absence of integration between the IoT device and the application layers. The IoT device layer and the application layer do not make a direct interface with each other; however, they are two end points of the IoT network layer. Nonetheless, IoT service users hope to select their IoT application providers after they purchase an IoT device. This implies that the nondiscrimination regulation against IoT device layers should be imposed on the IoT application layer.
It may appear that because IoT is an emerging service tool and the life cycle is still in the nascent stage, discussing additional regulations on IoT may act as a burden to its growth. Indeed, numerous studies and policy directions primarily argued that personal information and privacy protection are the main concerns and issues in the IoT era. However, the transition from traditional telecommunications to the Internet has led to much confusion regarding the regulatory framework. Hence, anticipative discussions or efforts to develop mature IoT services without regulatory confusion are presently required, and this study can therefore contribute to the growth of IoT services in a policy perspective.
This study has certain limitations. First, despite the importance of fee collection for IoT services, this study did not consider this perspective. As the purchase of IoT applications and IoT devices and the subscription to a network are distinct, the IoT diffusion and its policy, including promotion and regulation, should consider the relationships among application providers, device manufacturers, and telecommunication companies. Second, the attributes for IoT preferences appear to be simple, which may be detrimental to the IoT regulations discussion. Although the attributes were selected based on IoT issues, associated attributes are more complicated than ever due to the convergence of industries and services. By employing additional attributes, policy issues that are more pertinent to the current IoT ecosystem will be addressed. With these perspectives, future works will be practical and interesting.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Data Availability Statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.