Abstract
As information technology (IT) advances and grows in its capabilities, employees are willing to find even more novel ways to fulfill non-work purposes while at work. Non-work-related computing (NWRC), defined as employees’ non-sanctioned personal use of the IT resources in their workplace, has attracted a fair amount of attention. In order to understand why NWRC behavior often occurs, this study adopted a dual approach considering two aspects of human nature: automatic and reflective decision-making systems. Drawing on dual thinking processes, our study aims to examine the relationships among the following: habit as a trigger of automatic thinking, neutralization as a trigger of reflective thinking, and employees’ NWRC behavior in the workplace. Our model posits that employees’ NWRC is influenced by both habit and neutralization. Survey data collected from 176 employees of several banks in Mongolia were used to test our model by using partial least squares analysis. This study found that both habit and neutralization have significant impacts on NWRC. By conducting mediated regression techniques, we also found that neutralization partially mediates the relationship between habit/neutralization and NWRC. In addition to identifying the mediating role of neutralization, the results imply that it is important to prevent NWRC from becoming habitual and to make employees internalize the importance of compliance with internet use policy.
Introduction
Most companies have increasingly leveraged the Internet to enhance their business efficiency and effectiveness. Nowadays, using the Internet is one of the activities employees naturally do in the workplace. Nevertheless, according to a study by the American Management Association (2007), more than half of an employee’s total work hours are spent on Internet uses like online gambling, online shopping, and watching YouTube, all for personal reasons. Furthermore, as information technology (IT) advances and grows in its capabilities, employees are willing to find even more novel ways to exploit IT for non-work purposes (Hojjati & Baqhi, 2016; Weatherbee, 2010). Most recent research has claimed that the rate of non-work-related computing (NWRC) in the workplace is about 60% to 80%, leading to an almost 30% to 40% decline in work productivity (Alharthi et al., 2021).
In this regard, NWRC has attracted a fair amount of attention. NWRC has been defined as employees’ non-sanctioned, personal use of IT resources in their workplace (Bock & Ho, 2009; Bock et al., 2010; Son & Park, 2016). NWRC could hamper employees’ productivity in the workplace, and can cause network congestion (Cheng et al., 2014). It can also expose companies to serious information security threats, and can put companies at risk of legal liability resulting from employees’ potentially illegal actions on the web (Pee et al., 2008). In line with the above concerns, previous studies have investigated the key elements influencing NWRC in workplaces (D’Arcy & Devaraj, 2012; Khansa et al., 2017; Lim, 2002; Pee et al., 2008; Simmers, 2002; Son & Park, 2016), and studies have also demonstrated how NWRC negatively influences employee job performance, for example, loss of productivity (Lim et al., 2002; Simmers, 2002). In addition to the above work, there were studies to find out what control mechanisms could be adopted to mitigate NWRC behavior in the workplace (Li et al., 2010, 2014; Moody et al., 2018). Since the negative effects of NWRC are prominent in previous work, it is therefore still important to find the major drivers related to employees’ NWRC behavior, and to learn how employees act in the workplace, from theoretical and practical standpoints.
Meanwhile, most NWRC studies described the NWRC mechanism based on well-designed overarching theories, like the theory of planned behavior (TPB), the theory of reasoned action (TRA), or with a cost–benefit paradigm, all of which are explainable from a rational choice perspective (Burcu Bulgurcu & Benbasat, 2010; Li et al., 2010).
Although individuals often make rational choices, this does not mean that everyone can always do this. In line with the aforementioned argument, Thaler and Sunstein (2008) insisted that people can make decisions either consciously or unconsciously. In fact, individuals frequently make intuitive decisions as well. For example, people make bets even though they know they may lose money by gambling. In this case, it is hard to explain such behaviors from the rational choice perspective. Thus, it is necessary for us to take both conscious and unconscious aspects of decision making into consideration, so as to more deeply understand individuals’ decision-making processes (Aven, 2018). In this respect, we have assumed that the rational thinking perspective does not work very well in understanding NWRC behavior in the workplace.
Surprisingly, despite the rise of studies regarding individuals’ behaviors from two perspectives respectively (Kahneman, 2011; Samson & Voyer, 2012; Thaler & Sunstein, 2008), little research which integrates both conscious and unconscious decision approaches has been conducted in the NWRC context. In this sense, rather than focus on rationally based theories, it may be more helpful to consider both rational thinking and intuitive thinking perspectives in order to find major drivers contributing to NWRC behavior. Accordingly, it is necessary to consider the two different thinking systems as theoretical lenses to explain why employee NWRC occurs. Thus, in this study, we consider thinking systems from two aspects—automatic and reflective decision-making. According to Kahneman (2011), because the mechanisms relevant to the human brain are complex and mysterious, the behavior of human beings is frequently paradoxical, appearing simultaneously smart and dumb. In order to systematically approach this complexity, Thaler and Sunstein (2008) proposed two systems of thinking: the
Based on the dual thinking–system approach (Samson & Voyer, 2012), we considered habit from system 1 and neutralization from system 2 as the two major triggers of NWRC behavior. More specifically, this study attempts to provide a more complete picture by examining the key reasons for NWRC, and it attempts to fill the gaps in the previous relevant literature by answering the following questions:
By addressing the above questions, we anticipate that this study will make at least two important contributions to the current body of knowledge regarding an individual’s NWRC in many organizations. Theoretically, this is the first study in which an individual’s behavioral outcome, such as NWRC, has been evaluated from a dual-decision approach that includes both automatic and reflective decision-making perspectives. A clear understanding of both of these perspectives may result in more accurate representation and improved management of complex individuals’ NWRC behavior.
Practically speaking, if companies acknowledge the existence of uncontrollable NWRC behaviors that might potentially lead to an addiction, they take more responsibility for the monitoring and regulation of the NWRC. As we point out the efficacy of the automatic and reflective factors, our study provides some insights to help companies develop and maintain control mechanisms for mitigating NWRC.
The remainder of this paper is organized as follows. The next section provides a brief background on NWRC by classifying dual thinking–system perspectives. Then, we introduce our research model and hypotheses, followed by a data analysis and the results of our study. The implications of our findings are then discussed.
Literature Review
In this section, we first present the literature relevant to NWRC with regard to classification of the dual thinking perspectives. Next, we introduce the concept of dual thinking systems, and explain NWRC from a theoretical perspective. This study then describes the theoretical linkages between the two triggers (habit and neutralization) and the dual thinking systems.
Non-Work-Related Computing
In reviewing prior work on NWRC, we confirmed there are two sides of the research stream offering contradictory results on the impact of NWRC on employees (Bock & Ho, 2009). On one hand, NWRC could generate positive outcomes, such as fostering employee productivity by facilitating creativity, learning, and well-being for a short time (Belanger & Van Slyke, 2002; Oravec, 2002; Stanton, 2002). It also could aid in recovering employees’ energy, which ultimately increases their creative performance. On the other hand, NWRC has a negative impact on individual performance (Bock & Ho, 2009) and violates the internet use policy in the workplace (Li et al., 2010). For instance, NWRC such as personal emails, and online shopping could lead to a decrease in performance (Bock & Ho, 2009; Lim & Chen, 2012). Although the effect of NWRC in the workplace remains controversial, a large amount of research has still focused on the negative effects.
Considering either positive or negative effects, previous studies investigated the antecedents of NWRC (Bock et al., 2010; Chun & Bock, 2006; Khansa et al., 2017; Lim, 2002; Moody & Siponen, 2013) and examined the relationships between key antecedents of NWRC and its consequences (Bock & Ho, 2009; Lim & Chen, 2012; Pee et al., 2008; Son & Park, 2016). Table 1 contains a brief review of several studies and the main constructs affecting NWRC behavior from our research perspective.
Summary of Previous Studies on NWRC.
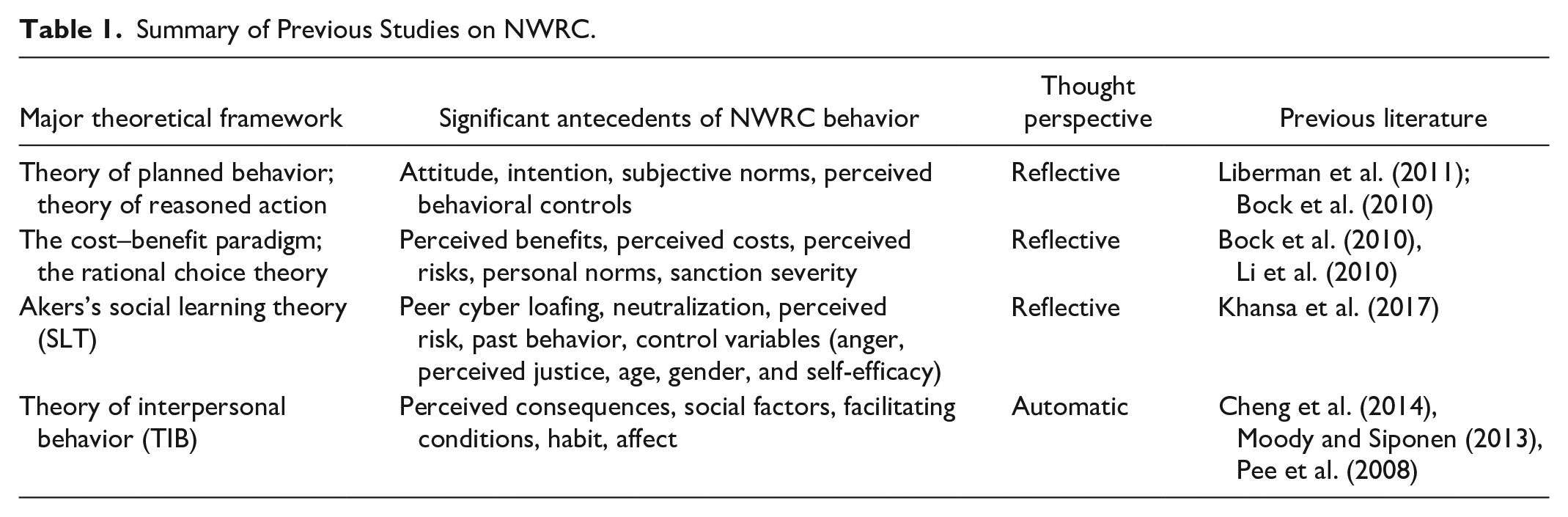
Numerous works on NWRC were mainly based on rational choice models, which consist of attitudes, subjective norms, or behavioral controls to explain NWRC behavior (Li et al., 2010; Son & Park, 2016). This stream offers insights into the recognition of why individuals engage in NWRC, assuming a
Dual Thinking Systems
The information processing approach is a framework that includes the characteristics of perception, memory, decision, and attention. Schneider and Shiffrin (1977) asserted that human performance is the consequence of two different thinking processes: the automatic thinking system (system 1) and the reflective thinking system (system 2). Automatic thinking involves a rapid and parallel process, and also requires little effort and control (Moors & De Houwer, 2006). On the other hand, reflective thinking requires higher-order mental operations that include executive functions, such as making deliberate judgments and evaluations (Strack & Deutsch, 2004).
Furthermore, Aven (2018) presented a distinction between the automatic system and the reflective system as follows. The automatic system involves more rapid processing, is oriented toward immediate action, is self-evidently valid, and uses minimal attention capacity. Meanwhile, the reflective system involves slower processing, is oriented toward delayed action, and also requires justification via logic and evidence. Specifically, behaviors activated by the automatic thinking system remain unconscious until they receive attention. Behaviors executed by the reflective thinking system are controlled by multiple processes, such as monitoring the appropriateness of the behavior in a social context, and checking the validity of a logical inference. An approach to dual thinking systems, as shown in Table 2, could apply the characteristics of both automatic and reflective systems to find the key triggers of NWRC behavior.
Applications of the Two Thinking Processes to NWRC.
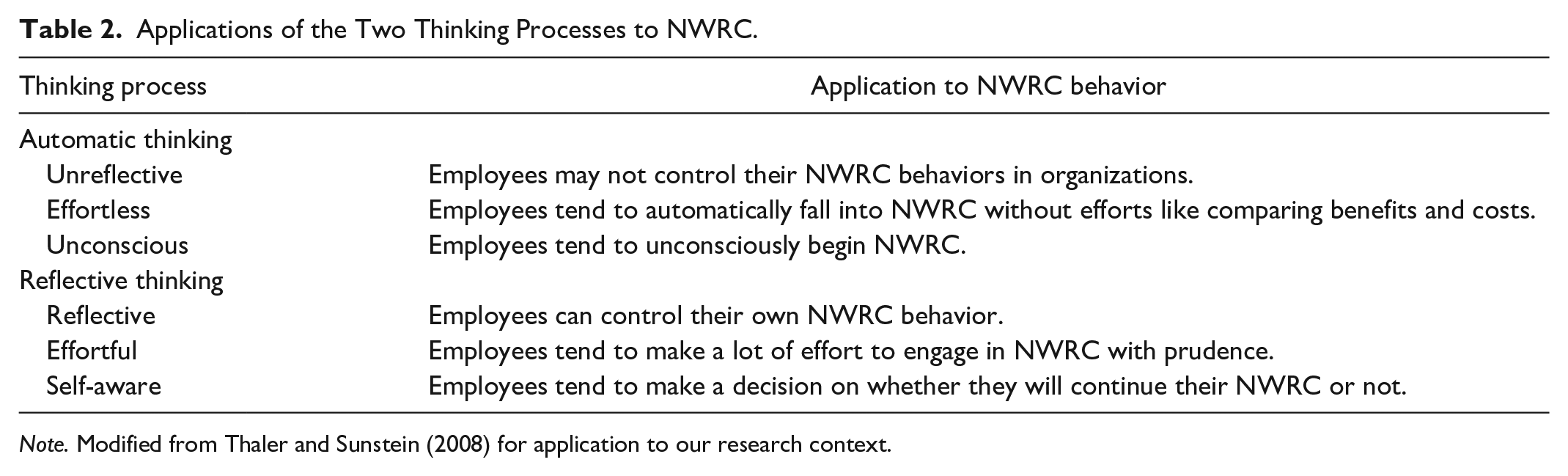
The automatic perspective is responsible for generating habitual behavior (Pee et al., 2008; Soror et al., 2015). If employees have formed a habit of using IT resources for NWRC in the workplace, NWRC is an automatic process in response to stimulus (Strack & Deutsch, 2004). These associative clusters in long-term memory by stimulus have been created or strengthened gradually by co-activation of external cues. This approach permits association with the habitual aspects of NWRC behavior.
Next, the reflective perspective serves regulatory goals that complement the function of neutralization. Strack and Deutsch (2004) suggested that reflective thinking is responsible for higher-order mental goals, as well as for making deliberate judgments and evaluations, monitoring, and self-regulation. These operations are achieved through relatively slow, controlled processes based on symbolic representations and operations. The typical example of a trigger for the reflective thinking perspective in this context can be neutralization, which has been represented by individuals’ justifications to avoid feelings of guilt before acting. Thus, neutralization is a significant aspect that needs to be considered in modeling individuals’ intentions and behaviors. Since neutralization significantly influences internet security (IS) policy violations (Siponen & Vance, 2010), this rationalizing behavior is likely to be relevant in explaining NWRC.
Considering the characteristics of both automatic and reflective thinking perspectives, we identified two key triggers of NWRC behavior (habit and neutralization) from each of the thinking systems. Specifically, this study considers habit as the trigger from the automatic thinking perspective, whereas neutralization is the trigger from the reflective thinking perspective.
As one trigger of the automatic system (system 1) in our study, habit has been defined as “learned sequences of acts that have become automatic responses to specific cues” (Polites & Karahanna, 2012). This occurs outside of consciousness, in that the person may be unaware of the specific situational cues leading them into the behavior (Hofmann et al., 2009). For example, in our study’s context, employees often unconsciously use computer resources in the workplace for shopping, banking, visiting personal sites, chatting on a social networking site (SNS), and more, during work (Soror et al., 2015). In addition, without weighing the costs and benefits associated with NWRC behavior, employees may be inclined to engage in NWRC. When this occurs, it is often because they have an automatic reaction to using the Internet for personal purposes. In this sense, habit can be viewed as an automatic thinking trigger that operates at a subconscious level. Thus, we present habit as the trigger for automatic thinking, which may lead to NWRC.
As the trigger of the reflective system (system 2) in our study, neutralization has been referred to as rationalizations that individuals invoke to convince themselves and others that their deviant behaviors are justifiable and/or excusable (Lim, 2002; Siponen & Vance, 2010; Sykes & Matza, 1957). In the NWRC context, neutralization associated with using computer resources for personal purposes may cause employees to simply become so absorbed in what they are doing.
In short, this study attempts to explain how NWRC occurs in the workplace by employing dual thinking perspectives. While most of the relevant studies have examined NWRC behavior based on the reflective thinking perspective, our study aims to examine how NWRC behavior is activated from both the automatic and the reflective thinking perspectives. Specifically, we have extracted key triggers from previous studies to examine how each trigger affects NWRC. In our study, we considered habit as a trigger from the automatic thinking perspective, while neutralization is regarded as a trigger from the reflective thinking perspective.
Research Model and Hypotheses
Drawing on the dual thinking systems, this study attempts to examine the relationship between key triggers and NWRC behavior. More specifically, both habit as a trigger of automatic thinking and neutralization as a trigger of reflective thinking will be positively related to NWRC behavior. Figure 1 illustrates our proposed research model.

Research model.
According to previous work, habit is related to self-starting and automatic orientation; thus, it occurs without the need for mindful decision making in order to respond to specific cues (Triandis, 1980). In this study, we assume that NWRC could be generated without employees’ conscious effort and consideration. Namely, employees’ habits could increase the degree of NWRC in the workplace because they repeat it routinely, without conscious effort and the usual consideration of implications. Thus, when the effect of habit on NWRC is strong, the enactment of NWRC behavior becomes the employees’ goal in itself rather than an imagined possible outcome associated with attitudes and subjective norms (Ajzen, 2002; Askew et al., 2014). Unless other key considerations prevent employees from engaging in their habitual NWRC behavior (e.g., a severe internet use policy, electronic surveillance) habit can be a powerful predictor of NWRC. In addition, prior work has provided empirical evidence that habit is a key driver generating NWRC behavior (Koay et al., 2017; Moody & Siponen, 2013; Pee et al., 2008). Based on these arguments, the following hypothesis is postulated.
H1:
Although NWRC behavior is not strictly criminal, it could be considered a kind of violation of social norms in the workplace. Since NWRC behavior is usually represented as non-productive behavior, or a kind of deviant behavior in the workplace, it is necessary for organizations to find techniques to control NWRC. Despite organizations’ efforts to control NWRC behavior, employees try to engage in NWRC in an effort to find justifications for it. According to prior studies, employees engaging in NWRC have a tendency to apply the techniques of neutralization to evade the organization’s control (Cheng et al., 2014). In previous studies, neutralization has been referred to as a rationalization that allows individuals to invoke self-justificatory excuses to convince themselves and others that their deviant or criminal behavior is justifiable (Lim, 2002; Siponen & Vance, 2010; Sykes & Matza, 1957). In addition, since employees with such a habit cannot regulate their own NWRC behavior, resulting in rule-breaking consequences, they may be subject to stimulus control from situations in which an inducement provokes an uncontrollable automatic response (Mischel et al., 2011). Such regulation failure means that the individuals failed to adjust their own behavior. This kind of situation tends to produce a reaction to bypass self-regulatory controls, which eventually results in applying the techniques of neutralization (Soror et al., 2015). Hence, the following hypothesis is postulated.
H2:
The underlying tenet of neutralization is that individuals make excuses and give reasons for mitigating feelings of guilt and shame associated with their insecure behaviors (Willison & Warkentin, 2013). When employees undertake these neutralization techniques to protect themselves from self-blame and guilt regarding NWRC, neutralization makes it easier for them to engage in NWRC (Lim, 2002). Extant studies have consistently reported that neutralization is a prominent predictor of NWRC behavior (Cheng et al., 2014; Siponen & Vance, 2010; Willison & Warkentin, 2013). Based on these arguments, we propose the following hypothesis.
H3:
Research Methodology
Sample and Data Collection
This study used a scenario-based survey method for collecting data and testing the proposed hypotheses. The hypothetical scenario is expected to trigger an employee’s decision-making process regarding behavior ( Appendix A ). The scenario-based questionnaire for our study had two sections: the first was designed to capture NWRC using a scenario; the second included measures of the respondents’ demographics, habits, and neutralization. Measurement scales validated in prior studies were adapted to fit the research context of our study ( Appendix B ). All the items were measured on a seven-point Likert scale, ranging from 1 (strongly disagree) to 7 (strongly agree).
Survey data were collected from employees working for banks in Mongolia. Mongolia was specifically chosen for several reasons. First, according to a report of the Communications Regulatory Commission of Mongolia (2018), a remarkable increase in internet subscribers has occurred since 2014. Engaging in NWRC has become common behavior among employees in Mongolia. Second, the International Telecommunications Union (2018) reported that Mongolia is ranked 104 out of 134 countries on the Global Cybersecurity Index 2017. Lastly, most banks in Mongolia have an internet use policy that clearly states personal use of information and communications technologies (ICT) resources is prohibited.
Furthermore, banks in developing countries such as Mongolia have fundamentally transformed form traditional banking to cyber banking (Khatoon et al., 2020). Such transformation helped banks to develop their IT capabilities. In this industry context, NWRC can reduce the performance of the business.
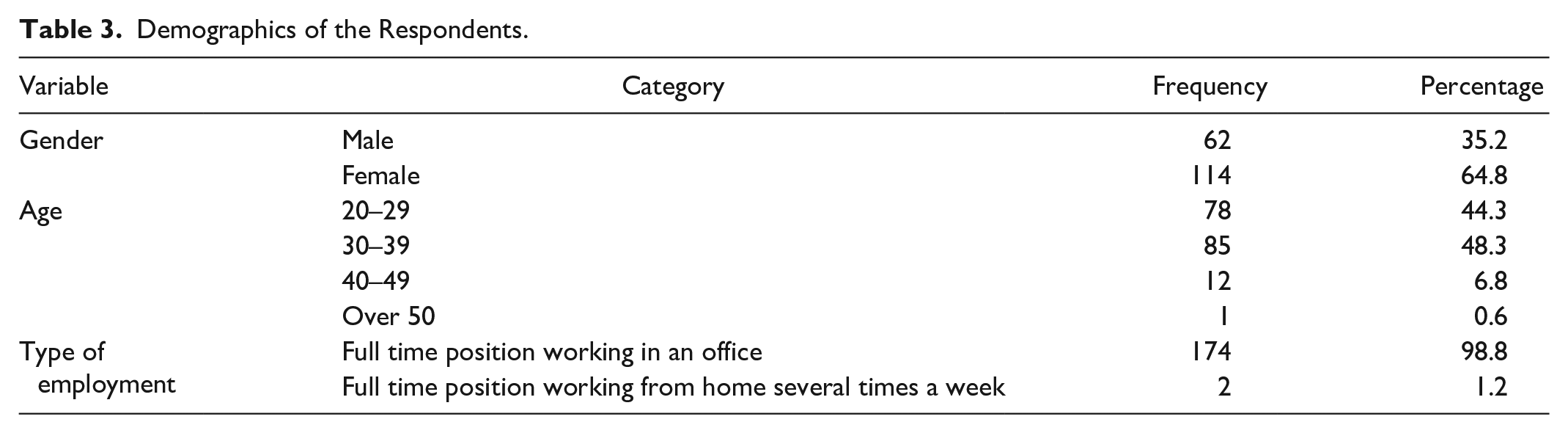
In order to collect the data, we distributed the questionnaires to human resources managers for seven banks in Mongolia that mostly use Internet-based technologies. We received 223 completed questionnaires out of 400 randomly selected contacts, yielding a response rate of 55.75%. Excluding 47 responses owing to missing data on the main constructs, the final sample for this study consisted of 176 responses. Table 3 shows the demographics of the respondents. Analysis of respondent demographics indicates that nearly 65% were female. The average respondent age was 30.70 years (
Demographics of the Respondents.
Construct Operationalization
All measurement items were adapted from the measurement scales used in previous studies and were modified to fit the context of NWRC behavior. Consistent with prior research by Chatterjee et al. (2015), we operationalized NWRC as the likelihood of engaging in NWRC. From Moody et al. (2018),
Data Analysis and Results
Measurement Model
In this study, the properties of the measurement scales were checked in terms of convergent validity, reliability, and discriminant validity (Gefen & Straub, 2005; Hair et al., 2014). Convergent validity detects whether the items for a construct show a higher correlation with the corresponding construct than with the other constructs (Gefen et al., 2000). According to Hair et al. (2009), convergent validity can be established if item loadings exceed 0.70. On the basis of factor analysis, one item of NWRC behavior that exhibited loadings lower than 0.70 (marked with an asterisk in Appendix B ) was dropped. As shown in Table 4, the lowest item loading was 0.724 for all samples, and 0.743 and 0.723 for male and female groups, respectively. These results suggest satisfactory convergent validity for the scales.
Item-Factor Loadings and Cross-Loadings.

As a way to test construct reliability, Cronbach’s alpha (Cronbach’s α), composite reliability (CR), and average variance extracted (AVE) were examined. Reliability is considered adequate if CR is 0.70 or higher, if AVE is 0.50 or higher, and if Cronbach’s α is 0.70 or higher (Chehimi et al., 2019; Gefen et al., 2000). Table 5 indicates that all factors met the three criteria for acceptable reliability by exhibiting CR of 0.907 or higher, Cronbach’s α of .848 or higher, and AVE of 0.731 or higher.
Results from Testing Reliability.

Discriminant validity was assessed by comparing the square root of the AVE for each construct with all of the cross-correlations of other constructs. Table 6 shows that the values of the square root of the AVE, which are reported on the diagonals, are greater than the inter-construct correlations, which are the off-diagonal entries, thus showing a satisfactory level of discriminant validity (i.e., the lowest value for the square root of the AVE is 0.855, and the highest correlation value between construct pairs is 0.519). Furthermore, as shown in Table 6, the cross-loadings on the items of other constructs are lower than their hypothesized constructs. Taken together, the results showed adequate measurement properties for all indicators.
Correlations Among Constructs and the Square Root of the AVE.

Structural Model
After confirming the measurement model, we tested the structural model using the component-based partial least squares (PLS) approach to test our hypothesis (Gefen et al., 2000; Hair et al., 2014). The path coefficients were computed using 500 sub-samplings with SmartPLS to test all the hypotheses.
Figure 2 presents the results of the model estimation, including standardized path coefficients, the significance of the paths based on a two-tailed

Path analysis results.
Post hoc Mediation Analysis
In order to drill down deeper on the mediation implied by our PLS analysis, we also applied regression analysis techniques based on Baron and Kenny (1986) and Preacher and Hayes (2004) that were widely used to test for mediation.
Based on the Baron and Kenny (1986) approach, we conducted mediation analysis by using a three-step process. First, the mediator (NEUT) was regressed on the independent variable (HAB). Second, the dependent variable (NWRC) was also regressed on the independent variable (HAB). Third, the dependent variable (NWRC) was regressed on both the independent variable (HAB) and the mediator (NEUT). As shown in Table 7, the results suggest that neutralization partially mediates the effect of habit on NWRC (
Mediation Test Results Following the Baron and Kenny (1986) Approach.

***
We also used the SPSS macro PROCESS used by Preacher and Hayes (2004) to analyze 5000 bootstrap resamples to test the mediation. The regression of habit on NWRC, ignoring the mediator, was significant (
Discussion and Conclusion
Research Findings and Implications
While employees’ NWRC in the workplace has been considered the important issue in the IT area, there has been very little empirical work from a dual thinking perspective. In this study, we attempted to explain why NWRC occurs in the workplace by looking at both the automatic and the reflective thinking perspectives, which are related to individuals’ specific behaviors.
In this study, we applied the dual thinking perspective (automatic and reflective thinking) as a meta-theoretical lens to explain how employees’ NWRC could be generated by both habit as a trigger of automatic thinking and neutralization as a trigger of reflective thinking. Our proposed perspective allowed us to generate insights into one possible mechanism underlying employees’ NWRC. In this respect, our study has prominent theoretical contributions to the extant literature on NWRC behavior.
First, we investigated key triggers of NWRC from dual thinking–systems perspectives. Since human behavior involves the use of both automatic and reflective processes (Stanovich & West, 2000), it is necessary to consider different antecedents from each process to explain employees’ NWRC behavior in the workplace. Therefore, in this study, we identified two antecedents of NWRC from automatic and reflective processes: habit as the trigger of the automatic thinking perspective, and neutralization as the trigger of the reflective thinking perspective.
Second, we found both habit and neutralization to be significant antecedents of employees’ NWRC behavior. This result supports our argument that NWRC might be affected by employees’ dual thinking systems. This finding suggests that implementing a dual systems perspective in the existing literature will help us to gain a deeper understanding of employees’ NWRC behavior in the workplace. By developing and testing the NWRC model, which are based on the dual thinking systems, we provide an alternative theoretical base to relevant research on NWRC. We expect that both habit and neutralization could be salient factors to describe individuals’ NWRC behavior in organizations.
Finally, this study provides empirical evidence that neutralization as trigger of reflective thinking can mediate the relationship between habit and the employees’ NWRC behavior. Our findings suggest it is important to prevent NWRC from becoming habitual and to make employees internalize the importance of compliance with internet use policy (Siponen & Vance, 2010).
In addition, our findings have implications for practitioners.
First, our findings could give practitioners insight into ways in which the problem of NWRC could be adequately managed by controlling habit and neutralization. Based on our findings, organizations may consider deploying deterrence-based rules to reduce employees’ engagement in NWRC. For example, the deterrent value of formal sanctions like IT security policies and monitoring mechanisms could control neutralization as the trigger of reflective thinking. Thus, organizations could make efforts to detect violations of rules prohibiting NWRC, and to impose serious penalties on those who break the NWRC rules. In addition, given the findings of this study, organizations may consider a way to relax the NWRC rules into the NWRC rules for controlling employees’ habits as a trigger of automatic thinking. In this case, organizations need to prevent NWRC behavior from becoming habitual by reducing the chances of employees engaging in NWRC. A clear message informing new employees of the organizational rules on NWRC could reduce NWRC from the start. In order to do that, the role of human resource department is very important. By conducting regular training program which are designed by the human resource department, managers need to focus on developing the morality of employees as a means of reducing negative interruption and distraction from NWRC (D’Arcy & Devaraj, 2012). Security awareness programs and acceptable NWRC guidelines could be a good example to increase moral development.
Second, because our results indicate that both habit and neutralization have a significant influence on employees’ NWRC, organizations should be cognizant of the individual characteristics of employees who engage in NWRC. Based upon our findings, we can suggest that coverage of the internet use policy in organizations should consider both rational and intuitive characteristics of employees’ internet use. When organizations attempt to design an internet use policy, they should consider all characteristics of dual thinking about NWRC behavior with regard to what is acceptable, and what not acceptable, internet use is. For instance, security awareness programs could include a module on moral responsibilities when employees are faced with opportunities to engage in NWRC. By doing so, employees may be better able to exert self-control, and regulate their own NWRC behavior.
Third, like both sides of a coin, the NWRC has both negative and positive sides. Some researchers showed that NWRC could have positive effects on employee productivity by fostering creativity and well-being (Son & Park, 2016). If we allow employees to engage in NWRC freely to take the social responsibility of employees’ needs, a habitual NWRC could increase the motivation of employees (Farooq et al., 2019). For example, organizations could design both proactive and reactive strategies to manage employees who are engaged in NWRC. According to Son and Park (2016)’s practical suggestions, organizations should inform their employees what kinds of individual information may be collected while they involved in NWRC as the proactive approach. In addition, organizations could develop compliant-handling programs for their employees who have complaints regarding invasion of personal privacy when the employees are engaged in NWRC as one of the reactive strategies.
Finally, this study also suggests that organizations could use two types of control mechanism in parallel to deter NWRC. One is formal control mechanisms including information security policies and monitoring technologies for detecting NWRC, such as checking computer histories and network logs. By doing this, employees could be made aware of the existence of the computer/network surveillance implemented. It will help them to correct habitual NWRC in the workplace. The other approach is informal control mechanism to formulate an organizational climate against NWRC through regular employee training to reduce neutralization. When the moral climate in the organization is more likely to formulate strong personal norms against NWRC, ultimately, there will be compliance with the NWRC policy.
Limitations and Directions for Future Research
This study has shown that both habit (as a trigger of automatic thinking) and neutralization (as a trigger of reflective thinking) have a significant impact on NWRC in the workplace, and it holds important implications for research and in practice. However, as is the case with all studies, ours is also subject to limitations, and it is important to point these out.
Since our study used data samples from self-reporting questionnaires with a cross-sectional research design, there is the potential for common method bias (CMB) (Podsakoff et al., 2003). To assess whether there is such a concern with the data, we adopted the marker variable technique recommended by Lindell and Whitney (2001). As a marker variable, an organizational commitment that refers to the extent to which employees want to continue their organizational membership was selected. It was adapted from a six-item questionnaire by Posey et al. (2015). We assessed CMB by calculating the correlation (
Like any empirical study, our study has limitations associated with the generalization of the result because the sample of this study consists of employees in a single industry (bank industry). To generalize the external validity of the findings of our study, responses of employees from other industries need be examined.
Another limitation is that we did not consider situational factors in the relationship between triggers and NWRC. NWRC behavior can be generated by various external factors in the workplace. Thus, future research needs to consider situational factors, such as work environments and relationships with colleagues, as potential moderators in the relationships between our triggers and NWRC behavior. Despite the aforementioned limitations, we believe our research has meaningful implications for both research and practice.
Footnotes
Appendix A
Appendix B
Appendix C
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
