Abstract
Online communities are one of the powerful digital sources for businesses to analyze online users’ behavioral data. In this sense, it is important for practitioners to know how to motivate community members, to keep them amused and regularly engaged in the community. But, practitioners should be aware that different user types exist in online communities, and they should understand these members’ diverse needs to manage these communities successfully and to give a better service to their members. Concordantly, this study focuses on the problem of the existence of different user types in online communities and development of different strategies for their motivation, involvement, and communication. Unlike previous studies, this study considers theories across managerial and social domains, conducts social network analysis, and considers users’ contribution patterns in an online community to identify particular user types in an online community. The study also presents motivational strategies for practitioners to keep each type of users frequently amused in online communities.
Introduction
The emergence of Web 2.0 has revolutionized the ways of communication on the Internet. Thus, social networks and online communities have gained popularity among the Internet users. These users have begun to create, modify, and discuss their contents in these digital environments (Kietzmann, Silvestre, McCarthy, & Pitt, 2012). In this way, the Internet has become a network of people rather than a network of documents (Ugander, Karrer, Backstrom, & Marlow, 2011).
In the literature, various studies define online communities. One of these definitions states that online communities are “social aggregations that emerge from the Net when enough people carry on those public discussions long enough, with sufficient human feeling, to form webs of personal relationships in cyberspace” (Rheingold, 1993, pp. 6-7). This definition implies that online communities include users who form relationships with other users due to a mutual interest or goal.
Additional to this definition, online communities have some characteristics. First, online communities require an adequate number of members engaging in the community actively and communicating with other members. Second, community members should share a mutual interest or concern to interact with each other. This joint interest can be a hobby, a common project, a common goal, or only the inclination of similar lifestyle, profession, or geographical location (Wu, 2011). Third, a collection of rules and practices should govern the behavior of the community members (Bagozzi & Dholakia, 2002; Christian Franklin, Mainelli, & Pay, 2014). Fourth, participation is the fundamental mechanism of online communities for both new and prominent members (Toral, Rocío, Martínez-Torres, Barrero, & Cortés, 2009). Finally, community members should experience a sense of community, which is “a feeling that members [of a group] have of belonging, a feeling that members matter to one another, and the group and a shared faith the members’ needs will be met through their commitment to be together” (McMillan & Chavis, 1986, p. 9).
Moreover, members’ willingness to participate, mutually exchange information with other members, and generate contents are essential for the continuity of online communities (Füller, Hutter, Hautz, & Matzler, 2014). However, different user types having different needs engage in such communities. In parallel, this study searches for these different user types in an online community by considering users’ structural positions and their contribution patterns beyond social and managerial domains. The aims of the study can be broken down into the following objectives:
to analyze whole network topology,
to detect subcommunities,
to classify user roles considering community users’ structural positions and their contribution patterns, and
to suggest administrative, design, involvement, and motivational strategies for practitioners or administrators who own or only manage an online community.
To address these objectives, this study embraces multiple theories and describes them beyond managerial and social domains. In the managerial domain, this research considers uses and gratification theory, motivational theory, common bond theory, and common identity theory, and it gives an administrative point of view of how a business can develop and align its business strategies for various user types in online communities. In the social domain, this study employs structural role theory and applies social network analysis (SNA) to detect subcommunities. In addition, this study uses additional user data to scrutinize users’ contribution patterns to be used as a part of user role identification. In this regard, an online community that has all the characteristics of an online community and serves as a discussion forum is chosen to be investigated.
In the first half of the article, the literature review is introduced and the methodology of the study is described. In the second half of the article, the study results are presented and significant study findings are discussed.
Literature Review
Social Domain
In this domain, previous studies focusing on user role identification in social networks and online communities are presented, and SNA is introduced.
User roles in online communities
Online communities are explored and investigated from different perspectives by academics in the context of community structure, community commitment, intention to participate, knowledge sharing, motivations for contribution, analysis of identities, usability, community success, word of mouth, marketing communications, and identification of psychological and social roles (Baek & Kim, 2015; Bagozzi & Dholakia, 2002; Bishop, 2007; Brown, Broderick, & Lee, 2007; Chin & Chignell, 2007; Faraj, Jarvenpaa, & Majchrzak, 2011; Harrison & Thomas, 2009; Kozinets, 2002; Kozinets, De Valck, Wojnicki, & Wilner, 2010; Lin & Lee, 2006; Ling et al., 2005; Ma & Agarwal, 2007; Sharratt & Usoro, 2003; Wang & Fesenmaier, 2003; Zhou & Amin, 2014).
In the context of user type identification, previous studies focus on different types of online communities or social networking sites. For example, Füller et al. (2014) examine innovation contest communities to find several types of user roles. Moreover, Arazy, Ortega, Nov, Yeo, and Balila (2015) and Welser et al. (2011) investigate Wikipedia; Lorenzo-Romero, Constantinides, and Alarcón-del-Amo (2010) focus on consumer communities; and Choi et al. (2015) concentrate on Reddit, which is a social news aggregation. In addition, whereas Hacker, Bodendorf, and Lorenz (2017) and Muller, Shami, Millen, and Feinberg (2010) consider enterprise online communities, Han et al. (2012) explore health communities. However, Brandtzaeg and Heim (2011) and Çiçek and Eren-Erdogmus (2013) investigate social networking sites.
In the context of online communities, previous research helps us to understand the identification of different user types in online communities. For example, Pluempavarn et al. (2011) identify social roles and their importance in an ideological and a nonideological online community. In addition, they propose models including the movement of these roles in other online communities over time. Choi et al. (2015) also identify user roles in Reddit regarding users’ behaviors in the community. As a result, they identify four different user types, which are
However, Brandtzaeg and Heim (2011) identify five different user roles (
Furthermore, Arazy et al. (2015) and Welser et al. (2011) investigate Wikipedia. Welser et al. (2011) examine comments posted on community-oriented pages qualitatively in addition to users’ wiki project memberships and user talk pages. As a result, authors figure out four different user types, which are
In addition to these studies, Muller et al. (2010) analyze lurkers and uploaders who upload files and contributors who contribute to metadata about files lurking behaviors in an enterprise file-sharing service. In addition, Risser and Bottoms (2014) identify
In addition, some studies introduce different approaches or methods to classify user roles in online communities in the literature. For example, Wu, Zhou, Jin, Lin, and Leung (2017) propose a three-layer model that examines user types in a hierarchical order. Moreover, Lee, Yang, Tsai, and Lai (2014) investigate user roles and user role change motifs in social networking sites by analyzing user-generated content and behavior motifs. Chan, Hayes, and Daly (2010) also apply a two-phase clustering and group users in a medium-sized bulletin board by considering various characteristics of users.
However, there are also some studies that use SNA as an approach to find user types or roles in online communities. For example, Buntain and Golbeck (2014) figure out the existence of
In addition, some studies benefit from SNA as an additional approach to investigate user types in online communities. For example, Pfeil, Svangstu, Ang, and Zaphiris (2011) find out six different user types, which are
Summary of Studies Focusing on User Role Identification.

SNA enables researchers to investigate both individuals and their relationships (Marin & Wellman, 2011; Martino & Spoto, 2006), and it provides an opportunity for academics to characterize and form human behavior models (Lewis, Kaufman, Gonzalez, Wimmer, & Christakis, 2008; Takhteyev, Gruzd, & Wellman, 2012). Muldoon (2013) also highlights that if you are thinking about people, you should also consider social norms that are affected by people’s behaviors and decisions. SNA explains that “a social network consists of a finite set or sets of actors and the relation or relations defined on them” (Wasserman & Faust, 1994, p. 20). In addition, Feicheng and Yating (2014) define SNA as a “quantitative method of analysis developed by sociologists, based on mathematical models and graph theory” (p. 232).
In the simplest terms, a social network consists of a set of people or things known as actors and links among them (Koçak, 2014). In a social network, nodes also called vertices to represent individual actors and links also called edges or ties describe relationships among nodes. Nodes can be a person, firm, country, journal article, department, position, webpage, and so forth; and edges can be friendship, competition, and so forth (Borgatti & Li, 2009; Marin & Wellman, 2011).
In the scope of the study, degree distribution, the characteristics of power-law, scale-free, small-world networks; network centralities; and subcommunities are investigated regarding network topology. The degree is a property of a node. Mislove (2009) states the degree of actors is calculated as the number of actors connected directly to the given node. Mislove (2009) states that degree distribution shows how the links are distributed among the actors in the network. It shows a frequency count of the occurrence of each degree.
Moreover, Mislove (2009) defines power-law networks as “where the probability that a node has degree k is proportional to k-α, for large k >1” (p. 30). It implies that the degrees in a power-law network are exponentially distributed. The parameter α is called a power-law coefficient. For example, World Wide Web contains a few high-degree vertices and the number of these vertices decreases exponentially (Van Steen, 2010). Scale-free networks indicate that they have the characteristics of power-law networks where the high-degree vertices tend to be connected to other high-degree vertices and the low-degree vertices tend to be connected to other low-degree vertices (Mislove, 2009). However, the starting point of small-world phenomenon is that Stanly Milgram, who was a professor at Harvard at that time, wanted to know the probability that two randomly selected individuals would know each other in 1967 (Van Steen, 2010). The result of the experiment indicated that letters were received by targets by taking an average of only 5.5 hops and it leads to the emergence of famous phrase six degrees of separation. The idea behind the experiment is that if an individual who is the source does not know the target individual, then the source must send the letter to one of his or her connections by assuming that his or her connection knows the target better than him or her. In social networks, more clues can be found in how people fit together in larger structures (Easley & Kleinberg, 2010). It allows the process of search for distant targets. In addition, individuals tend to group into small clusters in social networks, and an individual’s connections also know each other (Van Steen, 2010). In this sense, most of the social networks tend to have high clustering coefficient and small diameter, and they can be considered as small worlds (Cheng, Dale, & Liu, 2008; Mislove, Marcon, Gummadi, Druschel, & Bhattacharjee, 2007).
Furthermore, centrality aims the identification of most important actors within the given network (Haythornthwaite, 1996; Wasserman & Faust, 1994). Wasserman and Faust (1994) define the centrality as “actors who are the most important or the most prominent are usually located in strategic locations within the network” (p. 169). Most frequently used centralities are degree, closeness, and betweenness (Valente, Coronges, Lakon, & Costenbader, 2008), and are proposed by Freeman (1979).
Degree centrality indicates the influence of an individual in the network by counting the number of edges that an individual has (Baek & Kim, 2015). It shows how active or popular an individual is. An individual having high degree centrality states that he or she can be the leader or the hub in the network. In addition, that individual can easily access more information and be reached by other individuals easily. However, closeness centrality measures the length of paths of nodes to other nodes within the network, and it finds “how close an actor is to all the other actors in the network” (Catanese, De Meo, Ferrara, Fiumara, & Provetti, 2012, p. 312; Jamali & Abolhassani, 2006). Freeman (1979) states that if a node is, on average, the nearest position to all other nodes, it obtains the information efficiently and sooner. In other words, an individual having high closeness centrality may disseminate information and ideas to other individuals in the network quickly, and he or she may control most individuals in the network directly (Baek & Kim, 2015). Another centrality is betweenness centrality. Catanese et al. (2012) say that betweenness centrality is the most appropriate measure to identify the critical actors in the network. Wasserman and Faust (1994) define it as “how important an actor is at bridging the gap between other actors in the network.” In other words, it implies “the number of times that a participant needs another given actor to reach any other participant by the shortest path” (Baek & Kim, 2015, p. 667). Individuals having high betweenness centrality have the power to control the information between two nonadjacent points (Latora & Marchiori, 2007). The difference of betweenness centrality from degree and closeness centralities is that an individual having high betweenness can reach weakly connected subgroups (Baek & Kim, 2015). In this sense, these individuals play the role of gatekeeper (Freeman, 1979). If a node having high betweenness is removed from the network, it disturbs the flow of information through the network (Lewis et al., 2008; Warmbrodt, Sheng, & Hall, 2008).
From the subcommunity detection perspective, this study embraces the structural role theory by focusing on members with certain social positions “who share the same, patterned behaviors (roles) that are directed towards other sets of persons in the structure” (Biddle, 1986, p. 73, as cited in Pfeil et al., 2011) and by demonstrating how SNA can complement this theory. Structural role theory associates individuals’ social positions with the roles (Pfeil et al., 2011), and SNA helps us to find the structure of individuals’ patterns and interactions, and the strength of them in the online community in the context of an online discussion forum.
Managerial Domain
The emergence and popularity of online communities have compelled businesses to manage these platforms like other traditional media platforms to meet their business goals (Peters, Chen, Kaplan, Ognibeni, & Pauwels, 2013). Doubtlessly, online communities are different from traditional media because of their dynamic nature. Companies should consider these differences for better and successful management. In the context of online communities, managers, practitioners, or administrators should know how to motivate community members, keep them amused and regularly engaged in the community to maintain these communities well and accomplish their business goals (Kraut & Resnick, 2012).
The uses and gratification theory developed by Katz (1959) investigates media effects from the standpoint of users, and it proposes that people use media to satisfy their needs and reach their goals. In parallel with that theory, social influence, search for information, entertainment, trust, and reward can be one of the needs or goals of online community users that motivate them and influence their interactions in the community (Azar, Machado, Vacas-de-Carvalho, & Mendes, 2016).
Social influence states that people become the user of the community to make good impressions on other Internet users or to connect with other users (Azar et al., 2016). Another motivation for users is searching for information within the community. This motivation driver explains that users want to gain knowledge and expertise of other users to learn about any topic. However, entertainment is the strongest driver influencing users’ intention to use community website and recommend it to other users. The main reason is that the Internet users mainly involve in social networking sites to escape from daily problems or routines, to relax, to feel emotional relief or social enjoyment (Azar et al., 2016; Muntinga, Moorman, & Smit, 2011).
Moreover, managers should consider trust and reward to increase their users’ involvement. The more trust in both community website and other users can enhance the motivation of users to engage in community-related activities (Ridings, Gefen, & Arinze, 2002). In addition, community users want to gain monetary rewards, time savings, prizes, or incentives due to their engagements in the community (Azar et al., 2016). In this sense, managers should encourage contribution by designing reward systems. For example, eBay uses a reward system for its users with highest feedback scores (Kim, 2000). With a rewarding system, managers can take the attention of their users and show them what a superior performance is, and how they can be successful in the community.
These motivational drivers can also be considered as extrinsic motivation and intrinsic motivation from the standpoint of motivational theory (Ning Shen & Khalifa, 2008). Whereas extrinsic motivations are managed by community administrators, intrinsic motivations involve users’ perceptions (Garnefeld, Iseke, & Krebs, 2012). In this regard, whereas social influence, information search, and reward can be extrinsic motivations, entertainment, trust, relational development and maintenance, social and emotional support can be intrinsic motivations (Wang, Chung, Park, McLaughlin, & Fulk, 2012).
Furthermore, online community website design is an important dimension to increase users’ motivation to participate (Ning Shen & Khalifa, 2008). Managers, owners, or designers should make decisions by considering some trade-offs to construct and maintain the community website and satisfy each user type (Ren, Kraut, & Kiesler, 2007). These trade-offs can be better explained by common identity and common bond theories. A user becomes a user of the community because he or she likes the group as a whole and feels a commitment to the community’s purpose or topic based on common identity theory or because he or she wants the other users of the group and attaches them socially and emotionally based on common bond theory (Back, 1951). For example, whether to allow off-topic discussion or not is a trade-off for managers because whereas off-topic discussion enables users to establish friendship by talking with others, it can discourage users who are seeking specific information (Ren et al., 2007).
To increase users’ common bond, managers should provide a private space for their users to build long-term relationships with other users (Preece, 1999). For example, managers can provide private messaging or personal profile pages to allow users to add their profile pictures or personal information. They can also keep the record of past behaviors of users on their profile pages (Kollock, 1999; Zimmer & Alexander, 1996). However, managers can provide a clear purpose and common goal to increase users’ common identity, so the users know what to expect from the community (Preece, 2000). For example, managers can limit the effects of bad behaviors for the good health of the community (Kraut & Resnick, 2012) by assigning moderators to check user-generated contents and users’ behaviors in the community (Collins & Berge, 1997; Salmon, 2000).
In summary, online community users differ significantly in their motivation to participate and involve actively in the community (Garnefeld et al., 2012). In this sense, it is essential for businesses to understand what kinds of users exist, what roles they take, and what special needs they require in the community, so that managers can develop high motivational and successful design strategies to accomplish their goals.
Method
In the context of online communities, İnci Sözlük, which is serving as an online discussion forum, is selected to be examined. The community, which is the 44th popular website in Turkey, has 918,299 by January 2017 (Alexa, n.d.). In this community, members express themselves by opening topics about anything such as daily life, education, sports, and so forth, and adding contents. Globally, this community can be considered as the Turkish version of 4chan (Leyden, 2010; Trend Micro, 2010), and it can be considered as one of the representatives of online discussion forums in general.
The main idea behind the community’s purpose is content or opinion sharing. It indicates that users communicate with each other by sharing their contents or opinions, and so, they form relationships with each other. In this regard, SNA allows us to focus on and analyze these relationships in depth. In addition, if two community users frequently communicate with each other or exchange content or opinion, it is obvious that their relationship gets stronger. Thus, SNA prevents us not to ignore the strength or weight of this relationship. It allows us to examine the relationships between users by evaluating the strength of the communication.
The community administration maintained an application programming interface and data were obtained by using this interface directly on October 27, 2016 (Akar, Mardikyan, & Dalgic, 2018). In this sense, measurement errors such as interviewer effects occurring in survey research are eliminated (J. Brewer, 2000; D. D. Brewer & Webster, 2000; Marsden, 2003). In addition, data were open to the public and any Internet user could view the associated contents without registration for the community. Hence, a consent from the community members was not required to collect data from the ethical standpoint (Eysenbach & Till, 2001; Frankel & Siang, 1999, as cited in Pfeil et al., 2011). However, the consent from the owner of the community was obtained according to the community’s terms of use and privacy policy to collect any personal data associated with the community members. In addition, members’ identities were protected, so any member could not be identified within the network.
The methodology of the study includes five steps (Akar et al., 2018). The first three steps show how the network was designed. In the first step, topics, which were opened between September 26, 2016, and October 26, 2016, were included in the data set to focus on only active users in the community; 11,609 topics, which are containing more than one content, were extracted. After that, relationships between these topics and members who wrote any content to the given topic were identified and, as a result, 387,418 relationships were obtained. In the second step, relationship weights that show the strength of a relationship were calculated by aggregating the relationships between the same member and the same topic (Haythornthwaite, 1996), because a member can include more than one content to the given topic. After calculation, 288,898 different relationships out of 387,418 relationships were gathered.
In the third step, the bipartite network containing two different actors (topics and members) was converted into a one-mode network (Borgatti & Everett, 1997). Community members were chosen as the primary node set and the network was converted with the bipartite projection function in R. As a result, a weighted and one-mode network including only 28,715 members and 21,739,690 relationships were obtained. A relationship between any two members indicates that those two members included a content to the same topic. In addition, any two members can include a content to the one or more same topics, so the function also gives us relationship weights. In the fourth step, fast-greedy community detection algorithm (Clauset, Newman, & Moore, 2004) was chosen to identify subcommunities because of its calculation speed in R (Mislove, 2009). In the last step, members’ attributes including members’ membership age; the total number of topics opened by members between September 26, 2016, and October 26, 2016; the total number of contents added by user between September 26, 2016, and October 26, 2016; and the total number of members’ website visits between September 26, 2016, and October 26, 2016 were investigated to describe and classify the detected subcommunities.
Results
Network Topology
Table 2 shows the descriptive statistics of the whole network. Table 2 states that a user submits almost 14 contents to the community on average, opens 0.40 topics, and visits the community website 8.40 times in a month. Table 2 further reveals that a user submits contents to the same 1,514 topics, on average, along with other community users. In addition, a user has about 0.5 and 0.00004 closeness and betweenness centralities on average, respectively. When analyzing the number of opened topics per user, the median of zero highlights that a massive portion of community users did not contribute to the community by opening a topic but only through sharing contents under the existing topics. In addition, the large standard deviation of degree centrality indicates that users’ degrees are more spread out.
Descriptive Statistics.

In addition, Figure 1 shows the community network after the projection as described in the third step of the methodology. It includes 400 nodes having degree greater than 4 and 1,283 edges for better a visualization. Node sizes are proportional to the degree of a given node, and edge thickness is proportional to the edge weight.
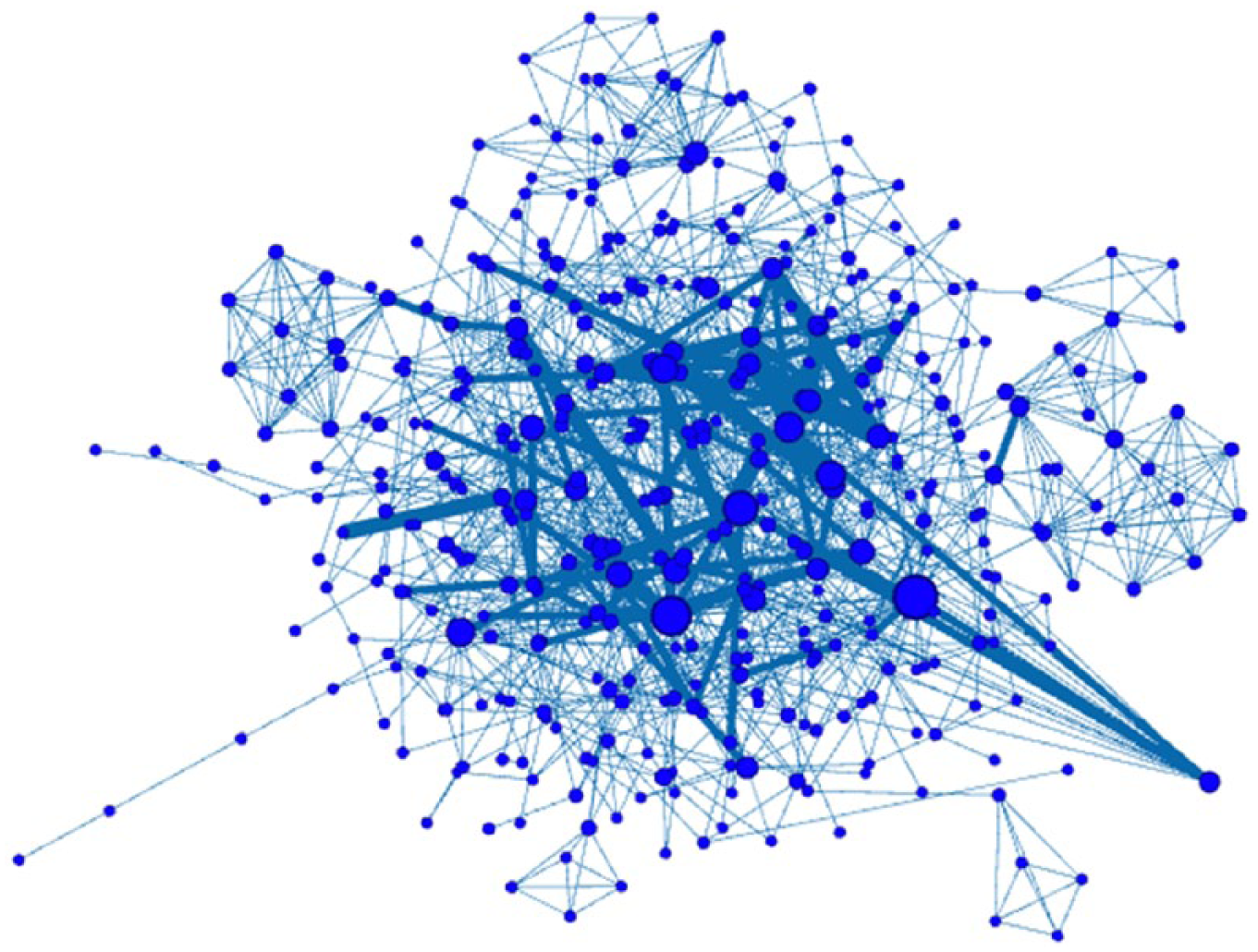
Network of the community.
Figure 2 shows degree distribution of the network. It indicates that although degree values increase, frequency decreases, and, in some cases, it also increases. In the network, each node has at least one edge. The member having the highest degree has 18,351 edges. It indicates that this member has added entries to 18,351 common topics along with the other community users. The second and the third highest degree values are 16,749 and 16,438, respectively. The results also indicate that 0.731% of the nodes have a degree of 1,533.

Log–log degree distribution.
Figure 3 shows that network deviates significantly. The main reason can be that only a part of the network data are collected, so, nodes can be undersampled with a lower degree, and it can explain the flat head of the distribution (Mislove, 2009). In addition to Figure 3, power-law statistics are also checked. They indicate that Kolmogorov–Smirnov statistic is 0.0449 and

Power-law functions vs. cumulative degree distribution.
Mislove et al. (2007) and Cheng et al. (2008) state that small-world phenomena indicate a small diameter and high clustering coefficient. Whereas diameter refers to “the largest distance between any two nodes in the network” (Acemoglu & Ozdaglar, 2013, p. 14), clustering coefficient indicates “the probability of connections between one vertex’s neighboring friends” (Tang & Liu, 2010, p. 492). For example, Mislove (2009) finds that the diameters of Flickr, LiveJournal, Orkut, and YouTube are 27, 20, 9, and 21, respectively. In addition, the clustering coefficients of Flickr, LiveJournal, Orkut, and YouTube are 0.313, 0.330, 0.171, and 0.136, respectively. The diameter (5.0) of the network is very small, and the clustering coefficient (0.3748) is higher than the clustering coefficients of Flickr, LiveJournal, Orkut, and YouTube. It suggests that the topic–member network is a small-world network.
Degree distribution also gives degree centralities of nodes. As mentioned above, the results show that the most central user regarding degree centrality has 18,351 relationships with other community users. The second and the third highest degree centrality values are 16,749 and 16,438, respectively.
Figure 4 depicts the top 1% of nodes ranked by normalized closeness centrality value in the network. The highest closeness centrality values of the first three members are 0.572128796, 0.568864411, and 0.5685828, respectively. Closeness centrality results also show that 0.72%, 0.49%, and 0.37% of nodes have 0.507448971, 0.510480186, and 0.507171118 closeness centrality values, respectively.

Top 1% of nodes ranked by normalized closeness centrality.
Figure 5 shows that a user having the highest betweenness has 0.00366354939 value, the second most central user has 0.00338082622 betweenness, and the third most central user has 0.00263333342 betweenness. The results also show that 0.72%, 0.46%, and 0.35% of the nodes have 0.00000032092, 0.00000069419, and 0.00000058865 betweenness centrality values.

Top 1% of nodes ranked by betweenness centrality.
Community Detection
The network is an undirected and weighted network. The proper community detection algorithms are edge betweenness, fast-greedy, multilevel, Walktrap, label propagation, spin-glass, leading eigenvector, and Infomap. The spin-glass algorithm is very central processing unit (CPU) intensive (Orman, Labatut, & Cherifi, 2011). This problem limits its use on large networks, and it performs worse when the network size increases. In this sense, the spin-glass algorithm is excluded from the scope of the study. In addition, edge betweenness algorithm is excluded from the scope of the study due to its slow speed (Newman, 2004). Furthermore, Walktrap algorithm divides the whole network into 356 subcommunities with the modularity of 0.13. However, 54.49% of the subcommunities include only one member, and 86.51% of the subcommunities involve less than 10 members. Moreover, Infomap algorithm divides the community into 42 subcommunities with the modularity of 0.0011; 73.80% of the subcommunities include less than 20 members, and 28.57% of the subcommunities consist of only two members. In addition, the modularity values achieved by label propagation and leading eigenvector algorithms are both zero. It is stated that zero modularity “indicates that the community structure is no stronger than would be expected by random chance” (Newman, 2004, p. 327). It can be concluded that if the network is undivided or does not have underlying community structure, the modularity equals to zero.
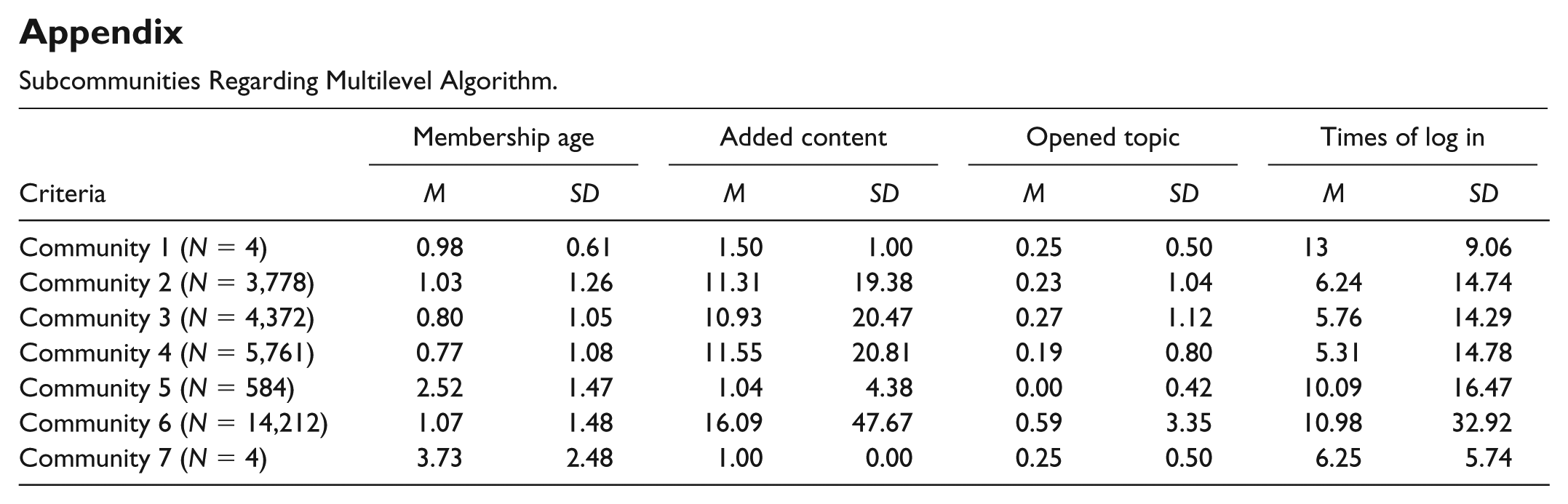
However, the fast-greedy algorithm divides the whole network into four subcommunities with the modularity of 0.1952174 (Akar et al., 2018). The first subcommunity includes 4,611 members, the second one involves 17,444 members, the third one consists of 6,594 members, and the last subcommunity includes only 66 members. Moreover, the multilevel algorithm finds out seven subcommunities with the modularity of 0.2313101. The subcommunities include four, 3,788, 4,372, 5,761, 584, 14,212, and four members, respectively.
Role Identification
Users’ attributes (membership age, added content, opened topic, and times of log in) are used to discriminate subcommunities in a meaningful way. The integration of structural data and interpretive techniques allows us to describe the roles in a more relevant way (Gleave, Welser, Lento, & Smith, 2009). As a result, it is revealed that the subcommunities generated by the fast-greedy algorithm are discriminated in a more meaningful way than the subcommunities detected by other community detection algorithms including multilevel, Infomap, and Walktrap by considering these attributes (see also the appendix). Table 3 presents contribution patterns and centralities of each subcommunity.
Characteristics of Subcommunities.

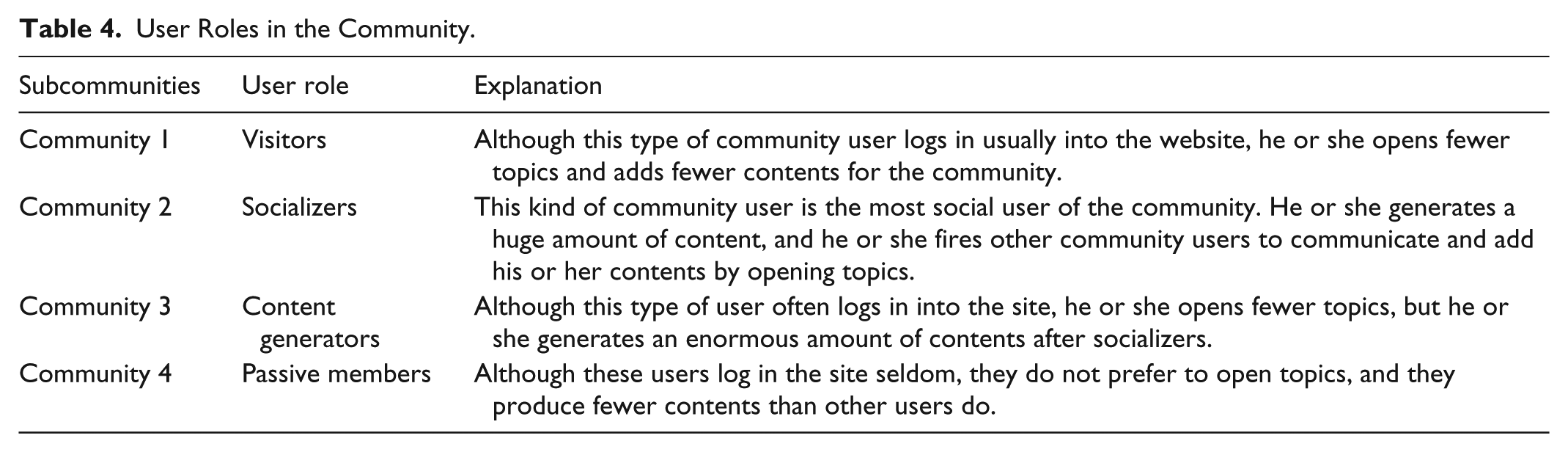
Furthermore, Table 4 summarizes the identified user roles in the community. It shows that the first community is called
User Roles in the Community.
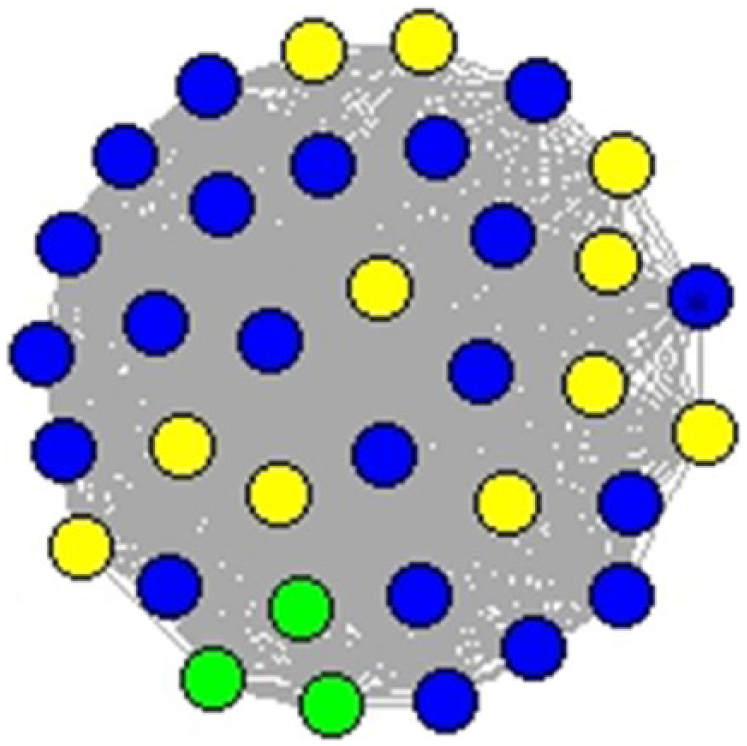
Furthermore, Figures 6 to 9 visualize the egocentric networks of the user roles chosen by randomly. In the figures, green nodes represent

Visitor (ID 665235), Degree 8, Entry 1, Topic 1, Session 27.

Socializer (ID 629286), Degree 15, Entry 3, Topic 1, Session 34.
Content generator (ID 1678650), Degree 34, Entry 50, Topic 1, Session 17.

Passive member (ID 528551), Degree 8, Entry 2, Topic 0, Session 1.
Figure 7 visualizes the ego network of a random
Figure 8 visualizes the ego network of a random
Finally, Figure 9 shows the ego network of a random
When the centralities of each type of users are considered in Table 3, the average closeness of each user type is around 0.50. The reason can be that the network is strongly connected, so each user is almost equally close to the other. However, betweenness centralities (0.00004) indicate that
Furthermore, Kruskal–Wallis analysis is conducted to test the difference between user roles regarding seven criteria in Table 3 (Zikmund, Babin, Carr, & Griffin, 2013). This test does not assume normality in the data, and it is much less sensitive to outliers, so, Kruskal–Wallis can be used as a substitute when the assumptions of one-way ANOVA have been violated (Lehman, 1991; Pagano, 1994; Welkowitz, Ewen, & Cohen, 1991, as cited in Vargha and Delaney, 1998). Table 5 shows the results of Kruskal–Wallis test. Test results indicate that user roles are significantly different from each other based on seven criteria.
Kruskal–Wallis Results.

In addition, a post hoc analysis for Kruskal–Wallis is conducted to analyze pairwise group differences. Table 6 involves post hoc results and pairwise comparisons between user roles. It shows how user types significantly differ from each other based on seven criteria.
Post Hoc Analysis of Kruskal–Wallis.

Conclusion
Theoretical Implications
This study embeds users’ contribution behaviors and structural patterns from the structural role theory perspective along with SNA. In this sense, this study shows that theories and methods can become widely used by employing the integration of different theories and methods, and supports that the mixture of theories and methods improves the trustworthiness and reliability of the data (Fullerton, Linster, McKee, & Slate, 1999).
This study contributes to the literature by presenting a network structure of an online community, serving as an online discussion forum and identifying user roles in this community by applying SNA. The network structure of the community shows that users in the community are very close to each other, there is no sparsity and reduced communication between community users. In addition, in parallel with the indication that online social networks show power-law degree distribution such as offline networks (Mislove, 2009), it can be concluded that online communities also show a similar structure such as online social networks. The community is also a small-world network, which indicates that information can travel more quickly within the community (Hanneman & Riddle, 2005).
In addition to these findings, vital members are determined from different centrality perspectives involving degree, closeness, and betweenness. In the network, the user having the highest degree and betweenness centralities is the same user. He or she also has the second closeness centrality. It indicates that he or she is one of the critical members and he or she can reach to other community members and can be reached by other community members at shorter path lengths, and he or she obtains the information efficiently and sooner (Freeman, 1979; Hanneman & Riddle, 2005).
In contrast to previous studies (Angeletou et al., 2011; Chan et al., 2010; Füller et al., 2014; Hecking et al., 2015; Pfeil et al., 2011), this study employs a community detection algorithm to analyze users’ structural positions and to find subcommunities in the network. This study also considers the strength of the relationships between users as a different perspective. In addition, this research synthesizes these positions with users’ contribution patterns for user role identification and investigates each user type’s centrality distributions. This integration allows us to apply a more comprehensive and productive approach than following only one theory and method, and it also helps us to improve the understanding of user roles in online communities serving as discussion forums (Gleave et al., 2009; Hanneman & Riddle, 2005). The results show that the network mainly consists of socializers, content generators, visitors, and passive members regarding their contribution levels in the community, respectively. In this regard, this study presents different user roles in the context of online discussion forums regarding previous studies by considering different perspectives (Chan et al., 2010; Choi et al., 2015; Füller et al., 2014; Pfeil et al., 2011).
In such communities, socializers flame the contribution and keep the discussion in the community by opening new topics. Content generators who are the youngest prefer submitting entries to opening topics. It indicates that socializers and content generators are responsible for the flow of information through the network. However, visitors visit the website more times than entry generators, they open few topics and add few contents. In addition, passive members who are the oldest members of the community take up the small part of the whole community, and they make very few contributions to the community. These results indicate that the network does not include high percentage of passive users who are not actively contributing or communicating in contrast to previous studies (Clauset et al., 2004; Kozinets, 1999; Nolker & Zhou, 2005; Nonnecke & Preece, 2000; Toral et al., 2009; Ye & Kishida, 2003). It can be inferred that this kind of inactive members can be commonly found in online communities rather than in the context of discussion forums.
When the centralities of each user type are investigated, the results figure out that content generators who are the youngest prefer adding contents to opening topics during their visit. They also have the most average degree distribution, because they add more contents than other users and it leads them to establish more relationships with other users. However, socializers flame the contribution and keep the discussion by opening new topics. An interesting result is that socializers have fewer relationships than visitors have. It can be concluded that although visitors add few contents and open few topics, they mostly communicate with active members when they visit the community website. Furthermore, centralities also prove that socializers and content generators play the role of gatekeeper in the network (Freeman, 2004). If these members are removed from the network, it disturbs the flow of information through the network as expected (Lewis et al., 2008; Warmbrodt et al., 2008).
Managerial Implications
It is essential for practitioners to enhance members’ participation and stimulate members’ motivations, and so design the community website (Chi, Munson, Fischer, Vieweg, & Parr, 2010). In this context, this study introduces some managerial strategies for administrators or practitioners to keep different types of members as satisfied considering uses and gratification theory, motivation theory, common bond theory, and common identity theory.
The study results indicate that passive members and visitors make fewer contributions than socializers and content generators do. The primary goal of managers should be turning passive members and visitors into socializers or content generators, so managers should practically communicate with these members to deliver valuable content and motivate them (Azar et al., 2016). Passive members and visitors must be aware that many users prefer to be members of the community. For instance, if administrators enhance word-of-mouth communication among new and older members and increase the visibility of new members to the majority, it can take the attention of passive members and visitors, and they can think that many users want to be part of this community (Lim, 2014). In addition, administrators can offer additional features to the community members to expand the critical mass. For example, they can provide sharing, like, or follow buttons, and community members can share their contents on other platforms.
Moreover, if administrators show the value of the community and the benefits that the community members get from the community by including a reward or incentive system for the members who generate huge amount of content, it can also attract the attention of passive members and visitors (Geddes, 2011) and these types of users can achieve a status in the community by feeling important for other community members (Pfeil et al., 2011). In addition, administrators must be careful that Internet users do not prefer to be a part of a silent community (Füller et al., 2014), so they must pay attention to the number of passive members who cannot be increased. Notably, managers offer financial rewards to passive members and visitors who do not often make contributions because they do not receive any gratifications during contribution (Garnefeld et al., 2012).
In addition, visitors and passive members can have security concerns and consider trust as an influential factor in the community. In this sense, administrators should prove that members live in a secure community, and any information associated with them is protected by the community administration. For example, the administration can protect members’ private messages from third parties, and they can include a privacy policy and terms of use to guarantee the security of member-related data in the community. Furthermore, the administration can provide a list of frequently asked questions to make any problems in community members’ minds clear and so increase members’ confidence (Preece & Shneiderman, 2009).
Playfulness can be also another important point to increase the participation of passive members and visitors. In this regard, administrators can provide features to increase these types of users’ playfulness and fun in the community (Sledgianowski & Kulviwat, 2009). For instance, interactive games, contests, and other tools can be generated (Yeh, Chuan-Chuan, Lin, & Lu, 2011). They may organize not only virtual activities but also real-life events to keep their members continuously connected and to allow them to establish healthy relationships.
Administrators should keep in their minds that socializers and content generators are the backbones of the community. The value and experience that these members get from the community are important to draw the attention of other types of users. The engagement of socializers and content generators fosters a dynamic community where members continuously interact and collaborate online. For instance, administrators can offer more features such as instant messaging to enhance sociability of these types of users and to help them to establish strong relationships (Qin, Kim, Hsu, & Tan, 2011; Yeh et al., 2011).
In addition, the appreciation of the members can also lead to an increase in members’ participation in the community (Preece & Shneiderman, 2009). For example, administrators can list members who generate more contents. However, quality of contents is as important as quantity of contents (Palmer, 2002). In this regard, administrators can provide a rating system and community members can assess each member’s contents. If the quality of contents improved, this can have an influence on the increase of return of visitors and passive members (Preece & Shneiderman, 2009).
In addition to these important points, administrators can also provide a reliable and responsive platform and they can also offer user-friendly interfaces, easy-to-navigate web layouts, comprehensible sitemaps, and search features to increase members’ ease of use, usefulness, and participation in the community (Yeh et al., 2011).
Furthermore, managers should think about the trade-offs, whether to increase common bond or common identities of each user type. Managers may provide user profiles that help users to know more about the community and awareness of tools that show who is online and help users attach socially to the community, or a personalized signature for users to add below their contents to increase common bond (Kollock, 1999; Preece, 1999; Zimmer & Alexander, 1996). In addition, managers may allow the off-topic discussion to allow users to establish friendship by talking with others to increase common bond (Ren et al., 2007).
However, managers may define a common and clear purpose or joint tasks, and so, they may encourage users to attend the community boundaries and increase users’ commitment to the community’s purpose (Back, 1951). For example, a community may highlight the competition with similar communities to position itself and foster the common identity of users.
Limitations
Some study limitations must be mentioned within the extent of the study. The first limitation is that if different samples from different online communities operating in different countries can be collected, cultural differences can also be analyzed. Another limitation is that this study considers a discussion forum in the context of online communities. Thus, analysis of different types of online communities can expand the results. Finally, the study omits the evolvement of community members in the network.
Footnotes
Appendix
Subcommunities Regarding Multilevel Algorithm.
| Criteria | Membership age |
Added content |
Opened topic |
Times of log in |
||||
|---|---|---|---|---|---|---|---|---|
|
|
|
|
|
|
|
|
|
|
| Community 1 ( |
0.98 | 0.61 | 1.50 | 1.00 | 0.25 | 0.50 | 13 | 9.06 |
| Community 2 ( |
1.03 | 1.26 | 11.31 | 19.38 | 0.23 | 1.04 | 6.24 | 14.74 |
| Community 3 ( |
0.80 | 1.05 | 10.93 | 20.47 | 0.27 | 1.12 | 5.76 | 14.29 |
| Community 4 ( |
0.77 | 1.08 | 11.55 | 20.81 | 0.19 | 0.80 | 5.31 | 14.78 |
| Community 5 ( |
2.52 | 1.47 | 1.04 | 4.38 | 0.00 | 0.42 | 10.09 | 16.47 |
| Community 6 ( |
1.07 | 1.48 | 16.09 | 47.67 | 0.59 | 3.35 | 10.98 | 32.92 |
| Community 7 ( |
3.73 | 2.48 | 1.00 | 0.00 | 0.25 | 0.50 | 6.25 | 5.74 |
Acknowledgements
We also thank Serkan Inci, the founder of
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This study is supported by Bogazici University Research Fund with Grant Number 12751.
