Abstract
With the rise of Web 2.0, microblogging has become a widely accepted phenomenon for sharing information. Moreover, the Twitter platform has become the tool of choice for universities looking to increase their digital footprint. However, scant research addresses the viability of microblogging as a tool to facilitate knowledge creation practices among higher education students. This paper proposes a model to explain how students, as digital natives, leverage the features of the Twitter microblogging for the transfer of knowledge. Finally, the paper examines the dark side of Twitter as a privacy-leaking platform and issues a call to higher institutions for specific security policies to prevent nefarious use.
Keywords
Introduction
The goal of university programs is to prepare students to face the challenges in the careers of their choice through acquisition of knowledge. Such knowledge includes both hard skills – specific training of tools, techniques and methods used in organizations, and soft skills – team building, problem solving, and leadership. With the proliferation of Web 2.0 tools and learning management systems, universities rely on a plethora of information and communication technologies to facilitate the knowledge sharing process.
This paper explores the microblogging phenomenon and analyzes its potential for knowledge creation by leveraging the information foraging, media specificity, and knowledge creation theories. The paper proposes a model to explain how the features of the Twitter microblogging platform enhance students’ conveyance and convergence practices for the purposes of acquiring and transferring tacit and explicit knowledge.
Moreover, the concept of Digital Natives is examined and the Twitter mobile application is proposed as a tool for teaching and educating the Digital Natives through sharing of best practices as identified in the Community of Inquiry theory.
Finally, the paper provides evidence of the potentiality for extraction of specific identifiable information from Twitter posts through the use of various open source tools. The paper calls for the creation of specific policies to ensure that security and privacy of students’ educational tweets are protected.
Literature review
Educational knowledge creation process
The goal of university programs is to prepare students to face the challenges in the careers of their choice through acquisition of knowledge. Such knowledge includes both hard skills – specific training of tools, techniques and methods used in organizations, and soft skills – team building, problem solving, and leadership. Nonaka (1994) categorized the knowledge that develops hard skills as explicit, since this particular type of knowledge can be captured in a written form and can be easily stored in systems. In contrast, knowledge that develops soft skills is considered tacit, since it is difficult to explicate and is ingrained in action.
To explain the educational knowledge creation process, we employ the knowledge creation theory proposed by Nonaka and Takeuchi (1995), who depicted the knowledge creation as a spiral process that winds through the various knowledge patterns (Figure 1).
Nonaka and Takeuchi’s knowledge creation model (1995).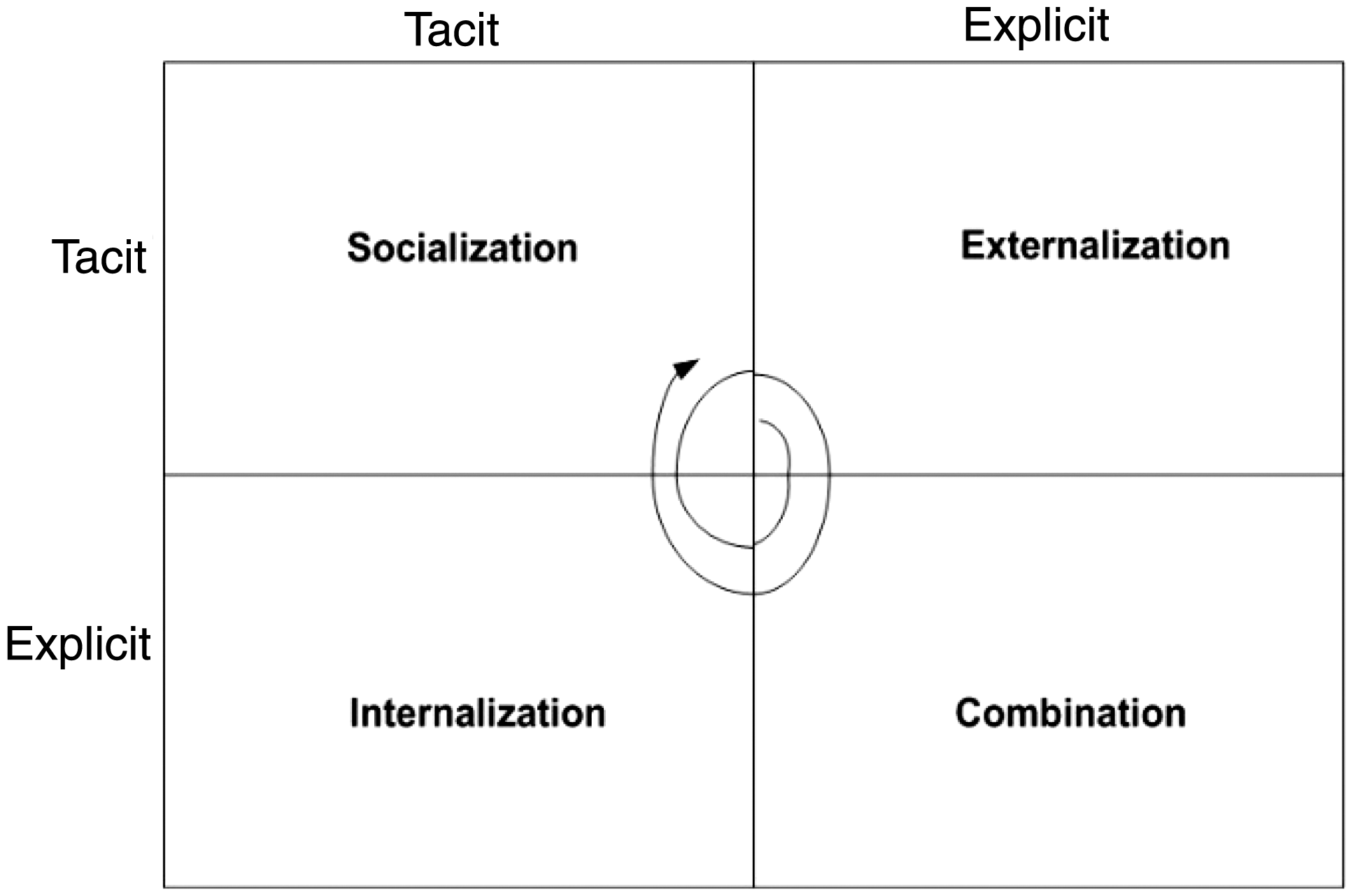
Socialization and personal notes
The theory proposes that the creation of knowledge occurs through the exchange of information through four patterns. The first pattern is known as socialization. Here, students engage in the transformation of tacit into tacit knowledge. This occurs through observation, interaction, and in some instances imitation of the professor. Moreover, the information exchange occurs through rich communication (e.g. face-to-face or through synchronous medium) in an effort to develop shared mental models.
One useful tool to capture and reflect on shared mental models is through the use of personal notes. Personal notes have been shown as information storage methods to portray solution of problems, as archival tools to refresh the memory, and as information sharing tools to encourage interaction among individuals (Koskinen and Aramo-Immonen, 2008). For example, the Read, Encode, Annotate, and Ponder note-taking technique has been shown to increase learning success and to facilitate common understanding among individuals (Tasdemir, 2010).
Externalization and stories
The next pattern of knowledge creation is called externalization. Here, instructors use metaphors and analogies to portray knowledge elements such as the know-how, know-why, and care-why. At the same time, students transfer the shared tacit into explicit knowledge via the use of written documents.
One tool that has been proven to facilitate learning through the externalization process is the story. The story is essential in the recombination of personal and shared knowledge through the process of collective- and self-reflection. Stories are textual representations of lessons interwoven into a series of events and constrained by specific timelines. A story is used to portray specific identity, facilitate a decision making process, and boost a social bond between the storyteller and the listeners. For example, Jonassen and Hernandez-Serrano (2002) found that stories can serve as problem-solving tools that reinforced the retrieval of past experiences and used the lessons to address new problems. Furthermore, learning from stories has been demonstrated to facilitate knowledge transfer among teams, since teams frequently engage in the exchange of metaphors and storytelling to share lessons (Goffin and Koners, 2011; Newell, 2004; Whyte and Classen, 2012). Through the art of storytelling, students are able to catalogue past lessons and convert them into new mental models.
Combination and reflection
The third pattern is known as combination. Here, students transform explicit into explicit knowledge through categorization and sorting of written and digital documents, best practices, and methodologies. One tool to facilitate this process is through personal reflection. Extant literature has demonstrated that reflection enables learning through the acquisition of lessons, promotion of innovation, capture of best practices, and creation of soft skills (Knipfer et al., 2013; Loo, 2002; Matturro and Silva, 2010).
Internalization and lessons learned
Finally, during the internalization pattern, students convert explicit to tacit knowledge through the process of collective reflection by joining the acquired knowledge to validate and augment their individual mental models.
One method to facilitate this process is the collective assessment of lessons learned, typically performed at the completion of a course. The use of lessons learned is widespread in the project management domain, but its applicability is universal to other domains as well. In higher education, lessons learned documents can serve as valuable knowledge tools to foster conversion of tacit into explicit knowledge, increase competency, and improve learning strategy (Cleveland, 2013; Williams, 2008).
Student knowledge seeking behavior
The knowledge seeking behavior involves an active searching of information in order to satisfy a specific information need (Xu et al., 2006). Students engage in knowledge seeking as a result of gaps that exist in their mental models. Such gaps represent problems that require specific courses of action (Pirolli and Card, 1999). To explain the knowledge seeking behavior, Pirolli and Card (1999) developed the information foraging theory, in which they argued that missing knowledge can be regarded as prey that is hidden in various sources (e.g. people, systems, archives). In an effort to achieve the maximum value of information relevant to their knowledge gap, information foragers will engage in knowledge seeking of the most valuable information that will take the least amount of time and effort to locate. To apply the theory to the education setting, it can be argued that a student who is seeking specific text that describes a concept discussed in the class will seek to spend the least amount of time to locate the source while dedicating more time to converting the knowledge from its explicit into its tacit state. As a result, information located in hard to locate sources (e.g. file drawers, archives, etc.) is expected to take a longer time and more energy to locate versus information stored in online databases. Students forced to make decisions whether to hunt for hard-to-locate information will focus on locating information which will require the least amount of time and effort to locate.
To explain student knowledge seeking behavior, we apply the knowledge seeking process model proposed by Savolainen (2006) (Figure 2). We propose that students’ knowledge seeking behavior is triggered by the existence of a specific gap in their knowledge in relation to proposed concepts in the classroom. Next, the students consider potential sources of information and evaluate the ease of locating the most valuable information for the least amount of effort. Upon locating specific information, students engage in the evaluation and interpretation of the information. The process involves the weighing of whether 1) the information successfully addresses the knowledge gap, or 2) further information is necessary to bridge the gap. Based on the analysis, the seeking behavior may be repeated by students, where additional information is sought for the same channel. The behavior will be terminated if the discovered knowledge satisfies the knowledge gap.
Students’ knowledge seeking process model (adapted from Savolainen (2006)).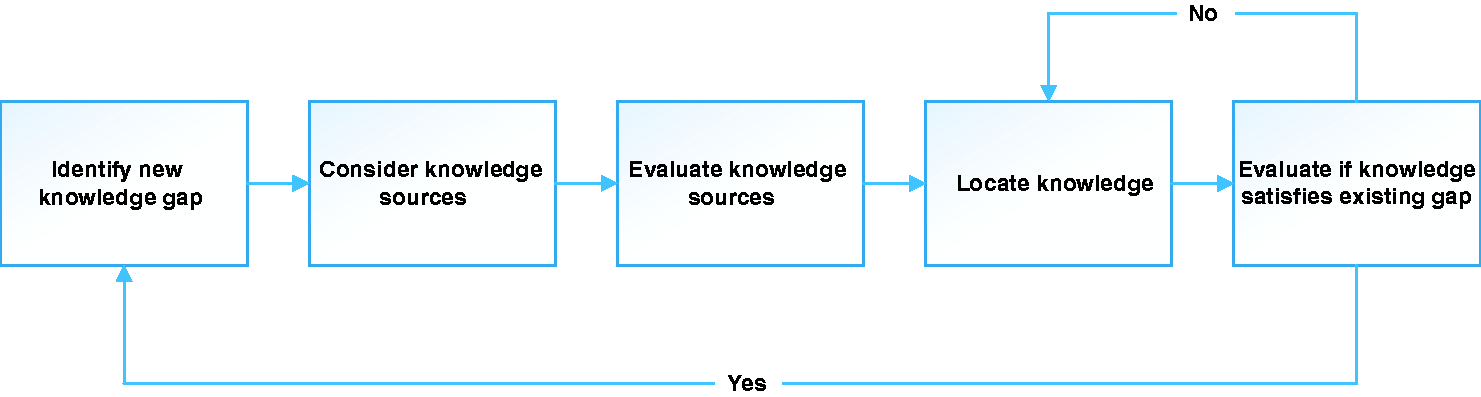
Knowledge dimensions and interactions
Extant literature proposes that knowledge consists of four dimensions: situational, conceptual, procedural, and strategic (De Jong and Ferguson-Hessler, 1996). The situational dimension contains information associated with specific conditions. Such knowledge is mostly superficial in nature and contains explicit properties. Its structure contains awareness of an applicable model to resolve the problem of a specific case, is already automated (e.g. step-based process), lends itself to verbal explication, and contains general properties acquired through formal training.
The conceptual knowledge is factual in nature and is based on specific principles within a domain. This knowledge is relational, structured through symbols, independent concepts, and has verbalizable properties, but lends itself to transfer through diagrams, models, and pictures due to its tacit nature. The procedural knowledge dimension is action oriented within a specific domain. This knowledge comprises rules related to specific principles, can be explicated through step-by-step processes or figures, and is domain specific.
Finally, the strategic knowledge dimension requires a deeper cognitive understanding of specific concepts and abstractions, because it consists of unique plans and actions. Such knowledge is transferred through demonstrations, pictures, and graphs, and requires deep analysis.
To understand how technology can facilitate the transfer of each knowledge dimension, we leverage the media synchronicity theory (MST). According to the MST (Dennis et al., 2008), communication is essential for the seeking and acquisition of information. Moreover, the communication process between individuals consists of numerous interactions, through a variety of communication mediums, in order to satisfy the information gap. The theory posited that these interactions come in two flavors: 1) conveyance – where individuals share “new” knowledge to create new mental models, and 2) convergence – the sharing of “known” knowledge to validate existing mental models.
Dennis et al. (2008) argued that in the instances where new mental models need to be created, the exchange of knowledge between the knowledge seeker and knowledge provider needs to occur through a rich communication medium. In such instances, the parties need to be highly in-sync with one another for longer periods of time, so that the seeker of knowledge can soak up large volumes of transferred knowledge from the knowledge provider. As a result, the media synchronicity theory proposes that the conveyance process necessitates communication channels characterized by capabilities for high synchronicity between the parties (e.g. video/audio interactions). As a result, it is argued that such technology mediums are more suitable for the transfer of the conceptual and strategic knowledge dimensions.
To facilitate the convergence process for the purposes of validation of existing mental models, Dennis et al. (2008) argued that frequent interactions with relatively small amounts of information exchange are required between individuals. For this purpose, technology mediums that foster low synchronicity are necessary (e.g. short textual messages, web links), and they are most suitable for the transfer of situational and procedural knowledge dimensions.
These interactions are best illustrated by the process model shown in Figure 3, adapted from Cleveland et al. (2015).
Knowledge dimensions and interaction model (adapted from Cleveland et al. (2015)).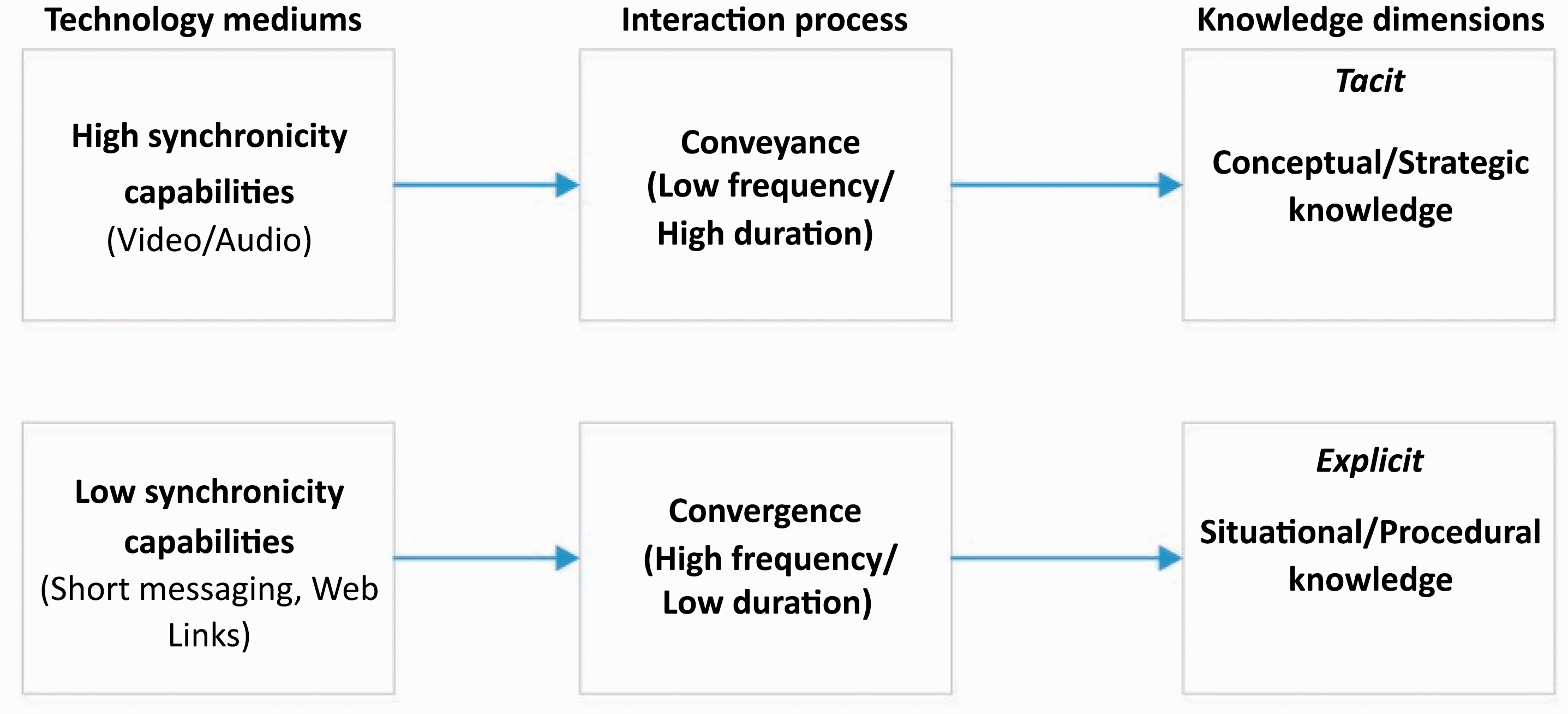
Microblogging
Universities are investing in numerous information and communication technologies in order to facilitate the educational knowledge creation process. By some estimates, the learning management systems (LMSs) market is expected to reach US$8 billion by 2018 (McIntosh, 2014). Research demonstrates that such technologies positively influence the processes of socialization, externalization, combination, and internalization (Collins et al., 2015; Lopez-Nicolas and Soto-Acosta, 2010). While many of these robust LMSs offer a variety of rich communication channels for students to interact, the use of microblogging for search and dissemination of knowledge is still rather scant.
Microblogging has been demonstrated to facilitate the distribution of knowledge practices (Hanseth and Lyytinen, 2004; Seebach, 2012). It provides users with the ability to post short messages through a variety of devices (Java et al., 2007). Users set up personal profiles, subscribe and follow other users, interact with them through brief discussions, and share web links, videos, and photos with their followers (Java et al., 2007). One of the most popular microblogging platforms today is Twitter, which has over 320 million registered users and one billion unique visits monthly to sites embedded in the Twitter message (Twitter.com, 2016).
Presently, Twitter limits users’ posts to 140 characters. Extant studies show that this word limit is sufficient for users to foster reflective information sharing in order to facilitate collaboration (Cleveland and Ellis, 2013; Yang and Chang, 2011). Moreover, studies have demonstrated that, in some instances, the microblogging interaction supports the exchange of knowledge and the development of learning (Ebner and Mauerer, 2008; Ebner et al., 2010). As a result, it is argued that through its features, microblogging can aid users in the process of educational knowledge creation.
In this paper, we propose the knowledge creation process illustrated in Figure 4 to explain the conversion of information into learning through the various knowledge patterns.
Microblogging knowledge creation process.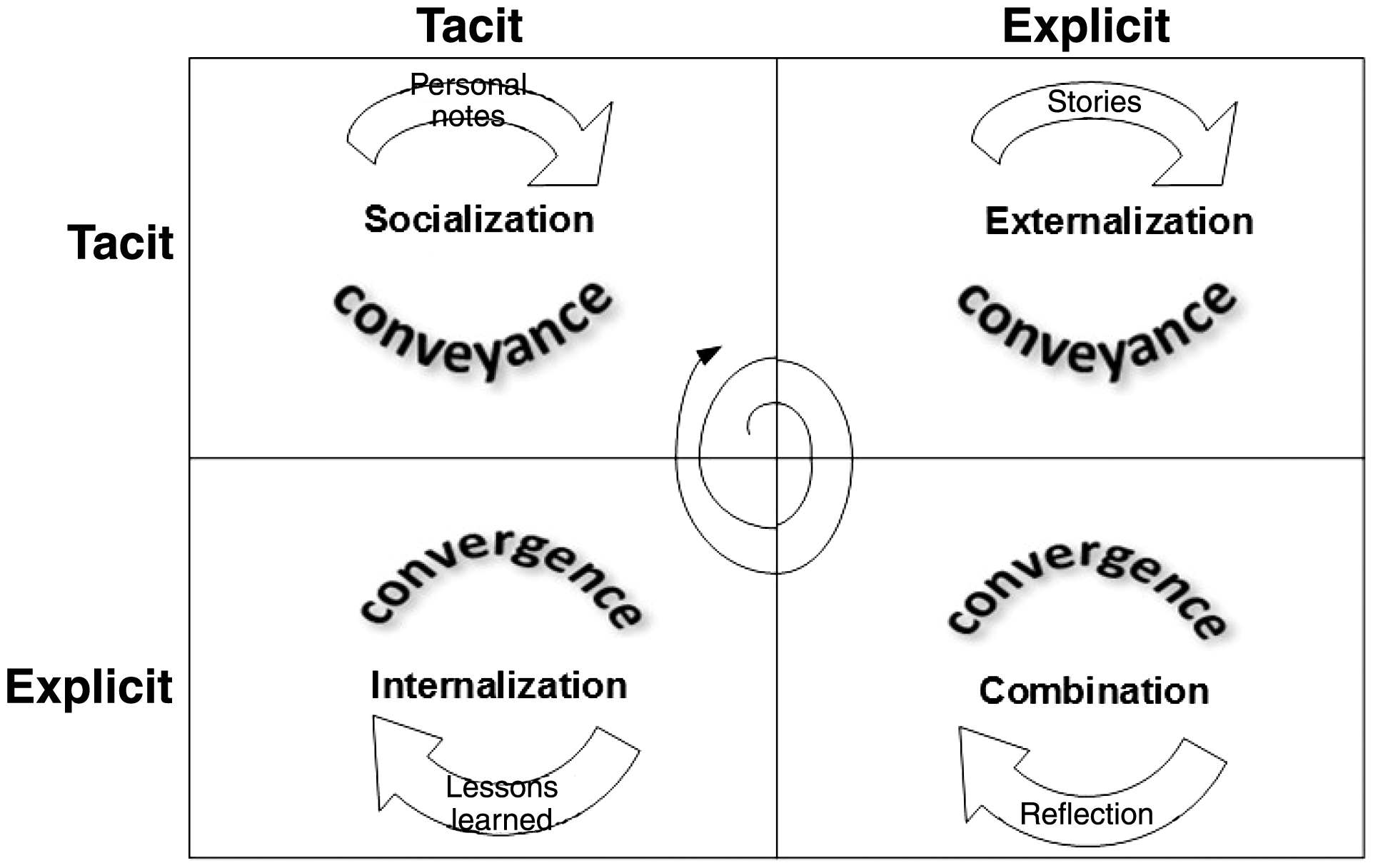
Microblogging convergence through lessons learned and reflection
Communication channels such as emails or discussion boards allow users the ability to develop their ideas without word limit. In contrast, the microblogging platforms typically constrain each post to a predefined character length, where users are forced to exercise creativity in constructing concise posts. Moreover, posted content is broadened since numerous users contribute to the same conversation topic. The interactions between users occurs through frequent exchanges of messages that contain position statements, questions, and specific answers. The exchanges can be one-to-one, where two users communicate with one another; one-to-many, where one user converses with either two or more participants at the same time; and many-to-many, where a group of users communicate and collaborate on a specific topic (Cleveland et al., 2015).
Twitter provides users with the ability to re-post (retweet) other users’ posts in their own network. As a result, this exchange propagates knowledge exchange with new audiences. For example, in their study, Zhang et al. (2010) found that users relied on microblogging to share different types of information through frequent and lengthy conversations. The shared knowledge assisted the participants with clarification on the type of work performed by others and location of knowledge for the purposes of solving specific situational questions.
In their microblogging study, Zhao et al. (2011) found that over 90% of the posts were work-relevant, lending further proof to the argument that microblogging facilitates the transfer of situational and procedural knowledge. For example, nearly half of the information exchanges (44%) concerned task statuses. The researchers determined that microblogging served as a tool to exchange information related to daily work activities. In a similar study, Riemer et al. (2011) found that microblogging facilitated transfer of knowledge related to task coordination, delegation of specific work, work-related questions, meeting coordination, meeting agendas, statements of opinions and feedback on ideas, and replies to messages.
Studies demonstrate that microblogging has been used to facilitate user interaction for the purpose of sharing lessons. For example, in their study on microblogging in an educational setting, Ebner et al. (2010) showed that the platform is utilized for the capture of lesson-related communication, by allowing one user to become part of another user’s learning process. The platform was shown to enable collective user participation for the purposes of specific problem solving.
In a related study, Carpenter (2014) found that nearly half of microblogging student use was for the purposes of distributing links to education sources and related articles (24% of peer-interaction tweets) and curriculum materials and lesson plans (23%). Moreover, Müller and Stocker (2011) demonstrated that microblogging helped users to acquire best practices, access standards/quality procedures, and use and improve documentation standards, document quality, and document processes. The researchers also discovered that the platform led to an improved information flow, promotion of learning and knowledge management practices and learning, and diffusion of rich experiences, leading to more innovative thinking.
Finally, Wright (2010) found that microblogging posts made by students were used for the purposes of reflective thinking. Users reported that the platform helped them overcome social isolation, while the character limit focused their attention on purposeful reflection with regard to their experiences.
Microblogging conveyance through stories and personal notes
Earlier, we argued that personal stories and notes are useful tools for the conversion of tacit into tacit and tacit into explicit knowledge. Here we demonstrate the ability of the microblogging features to facilitate the use of such tools.
Microblogging platforms provide users with the ability to group microblogging posts into stories. These events are called social curation and deliver considerable value to the microblogging community. Web services sites such as Storify and Togetter allow content organizers to formulate a story from a list of microblogging posts. For example, Duh et al. (2012) demonstrated that a sample of 10.2 million microblogging posts from 800,000 users contained 96,000 lists consisting of diaries (9%), problem solving (16%), collections of long articles (19%), and conversations on specific topics (19%). This multiplicity of interactions demonstrates that users are able to transcend the character limitation and engage in uniform storytelling for the purposes of information exchange.
Furthermore, Reinhardt et al. (2009) found that over 40% of users in their Twitter study used the platform to capture personal notes for the purposes of knowledge building and information sharing with others. Similarly, in their study of microblogging use, Pepe and Mayernik (2012) demonstrated that the platform is used by scientists to document field research data in the form of notes. Their results demonstrated that microblogging notes taken on the spot as short text messages can facilitate the transfer of tacit into explicit knowledge.
Microblogging and Digital Natives
The birthdate for Digital Natives is 1980. Digital Natives are children who have grown up with technology (Prensky, 2001). Others have referred to Digital Natives as “Gen C, Gen I, Net Gen, Gen Y, Gen Z, and Internet Generation” (Howell, 2012). Another name for this generation is “Net Generation” or “Net Geners” (Tapscott, 1998). Tapscott (2008) backdated the “Net Generation” or “Net Geners” date of birth to 1977. Jukes et al. (2010) refer to these Digital Natives simply as the “Digital Generation.” For the purpose of this paper, Digital Natives is used.
Because these students have grown up in the Information Age, it is believed that these students learn and think differently from non-Digital Native students. Despite this notion, a large number of faculty members are using traditional teaching methods. It was found that 90% of students own laptops and 86% own Smart Phones. Use of mobile devices may be banned in the classroom (Dahlstrom et al., 2013).
Digital Natives and Digital Immigrants were initially introduced to distinguish the difference between young people today and their elders (Prensky, 2001). As time passed, it was believed that the idea of Digital Natives and Digital Immigrants would become less relevant because people would have grown up in the era of digital technology. To that end, Prensky (2009) introduced a new term, Digital Wisdom, and defined it as a twofold concept. He referred to Digital Wisdom as the use of technology to access cognitive power beyond our innate capacity and as a means to enhance our capabilities.
In contrast to mobile devices being banned, learning with mobile devices has been proven to further engage Digital Natives in how they want to learn (Gikas and Grant, 2013). The cost of providing mobile functionality for the LMS could be a barrier to this type of learning. The mobile module is not a part of the baseline LMS provided by the vendor.
Dahlstrom et al. (2013) demonstrated that students learn best when the learning environment is blended. While most faculty members are knowledgeable about traditional teaching and learning approaches, he or she may need to learn best practices in teaching for online learning to create an environment the students learn best in (Prensky, 2001). A widely used theory for design and delivery of online courses is the Community of Inquiry (CoI) theory. The need for the theory was driven by the need to understand computer-mediated communication and computer conferencing in supporting an education experience (Garrison et al., 1999).
While Twitter’s intended use is as social media, Twitter can be used as a tool for teaching and learning in an educational environment. Twitter’s features and functions allow for Digital Natives to learn in the way they want to learn using technology, in a blended learning environment, and on a mobile device. Twitter also allows for faculty to put in practice online teaching and learning best practices identified in the CoI theory. Twitter’s mobile app can be used as an alternative to purchasing LMS vendors’ mobile modules to offset the cost.
As one can see, using Twitter in education can yield multiple benefits in teaching today’s students; therefore, the purpose of this section is to further discuss why Twitter is a legitimate tool for teaching and learning. As mentioned above, Digital Natives learn best in a blended learning environment; therefore, first Twitter and CoI will be discussed.
Twitter and CoI
The idea behind the CoI is computer-mediated communication and computer conferencing in supporting an education experience (Garrison et al., 1999). The CoI constructs are: teacher presence, cognitive presences, and social presences. Cognitive presence is the extent to which participants in any particular configuration of a community of inquiry are able to construct meaning through sustained communication (Garrison et al., 2001). Social presence is the ability of learners to project their personal characteristics into the community of inquiry, thereby presenting themselves as “real people” (Rourke et al., 2007). Teaching presence is defined as the design, facilitation, and direction of cognitive and social processes for the purpose of realizing personally meaningful and educational worthwhile learning outcomes (Anderson et al., 2001). The overarching idea behind the CoI is that the three constructs must be present in the learning space in order for an education transaction to take place.
Twitter allows for the CoI to be put into practice because faculty has the ability to allow students to follow them. Once students are following the faculty member, teacher presences can be addressed by the faculty member tweeting. Tweeting is posting content of no more than 140 characters that followers can see. Content can be text, pictures, and videos. For example, faculty could post a video or link to an article related to the learning objectives that the faculty member is teaching about. The faculty can also facilitate social and cognitive presences by making sure students are tweeting with one another in a timely manner and by making sure the students’ tweets are contributing to the learning process.
Twitter allows for faculty to address social presence, because students can post content, like pictures and videos, that will project him or her as real. Students are also able to follow their peers and instructor and reply to tweets. Tweeting is important to the social presence construct because it allows a conversation to happen with real people.
Cognitive presence can be addressed using Twitter by students exchanging information related to the learning objective. Students can add new knowledge that may not be a part of the discussion. Students are also able to get immediate feedback from peers if the instructor is not available to respond.
The fact that Digital Natives like learning in a blended learning environment and faculty are able to address Digital Natives’ learning style using Twitter by putting CoI online learning best practices in practice, Twitter is appropriate for teaching and learning in education.
In addition to addressing the needs of Digital Natives, Digital Wisdom is addressed when Twitter and CoI are married together. Twitter is the technology that houses the information that allows users to become wiser because the information is readily available when users are ready to absorb it. The use of Twitter and CoI enhances students’ capabilities because students have to research new information to create a cognizant connection noted as a fact of the CoI framework. Students’ capacity increases because research skills and content knowledge are heightened. Because students are using technology, their self-efficacy is developed; therefore, the students become better disseminators of information. Moreover, the students become adept and are able to repeat the information gathering and information dissemination processes again for new information discovery.
Next, Digital Natives and Twitter are discussed in more detail.
Twitter and Digital Natives
It is believed that Digital Natives learn differently (Kelly et al., 2008; Prensky, 2001), and K-12 institutions and Higher Education institutions haven’t changed teaching and learning practices to capitalize on how Digital Natives want to learn (Kelly et al., 2008).
Research shows that students want to email, chat with instant messaging, surf the internet, read and publish blogs, text with cell phones, take and send pictures with cell phones, play electronic and online games, and listen to, watch and create podcasts (Kelly et al., 2008).
One way education institutions can improve the educating of Digital Natives is to embrace applications like Twitter. While Twitter does not address every way that Digital Natives want to learn, Twitter does allow Digital Natives to learn with technology and in an environment that they want to learn in. Similar to text messaging, blogging, and sending and taking pictures with a cell phone, Twitter allows for students to engage in similar types of tasks when tweeting.
Twitter allows for learning to take place anytime anywhere via a mobile device using Twitter’s mobile app. Research shows that 86% of Digital Natives have smartphones and are more engaged in learning when utilizing mobile devices (Hudson, 2011). To that end, these observations further validate Twitter as an appropriate tool for teaching and learning in education. Next, the benefits of Twitter’s having a mobile app are further discussed.
Twitter’s mobile application benefits
Studies show that over 50% of faculty believe that mobile devices can enhance learning, while students reported that the use of mobile devices increased communication among them (Gikas and Grant, 2013). By using mobile devices, students can quickly access course documents and upload and post course content anywhere (Sharples et al., 2010; Traxler, 2007, 2010).
While learning with mobile devices yields a positive impact on student success, mobile modules are not a part of the LMS base package. Schools are facing funding issues due to states implementing performance-based funding, low enrollment, and student retention. As a result of lack of funding, educational institutions faced with investment decisions on whether to acquire a mobile module may reconsider such expenditures; however, for education to reap the benefits of mobile teaching and learning, Twitter can be used as an alternative. Twitter has mobile apps for Apple and Android users.
Mobile code and device security
Cyber security has been a growing concern as there have been major headlines concerning poor Information Assurance posture with the Department of Defense (DoD), Target, Sony, and more. The used mobile device itself contains vulnerabilities resulting from inherent weaknesses that even users may not be aware of (Vigna, 2003). This makes it difficult to protect users, as they wish to use mobile devices for educational tweets.
Social engineering and intelligence analysis on educational tweets
With the rise of Web 2.0, Twitter has become a tool of choice for universities looking to increase their digital footprint. However, there is not much guidance given on the protections of these tweets or the secure integration of Twitter into other Web 2.0 applications. As a result, this paper explores methods with which Twitter and its data can be exploited for nefarious uses (Dawson and Omar, 2015). Explored in this paper are the methods with which Twitter and its data can be exploited for nefarious uses.
Open Source Intelligence
The intelligence field of Open Source Intelligence (OSINT) relies on data that is freely available on the public domain to conduct an analysis. OSINT is conducted by collecting data in an overt manner. OSINT has been defined by the United States (US) DoD and the US Director of National Intelligence as analysis produced from publicly available information that is collected, exploited, and disseminated for the purpose of addressing a specific intelligence requirement (Congress, 2006). Displayed in Subtitle D – intelligence – Related Matters SEC. 931., 932., and 933 are findings by Congress for the DoD strategy for OSINT (Congress, 2006). These findings provide a basis for the importance of OSINT as it relates to intelligence.
Geolocation
Twitter allows geolocation tags in tweets through a geotagging feature in the Twitter Application Programing Interface (API) (Twitter, 2014). Twitter provides terms of Twitter’s Developer Policy regarding aggregation, caching, and storing of geographic information (Twitter, 2014). However, anyone who develops an application using this API can tweak items, providing even more granularity of its users. Even without modification of tweets, simply adding the location will provide details such as neighborhood, city, state, or country. This publication information can be used to start an analysis. In iOS version 6.26+ and Android version 5.55+, precise location can be shared if elected to do so. Also, third party applications or websites may share precise tweet locations as well.
Personal Twitter accounts provide the ability to associate a specific location (Figure 5). This location over time can provide trends of locations visited with time/date stamps. This can be used to start developing a full analysis on tweeting trends from particular locations, frequency of location visits, and content analysis through text mining.
Twitter location example.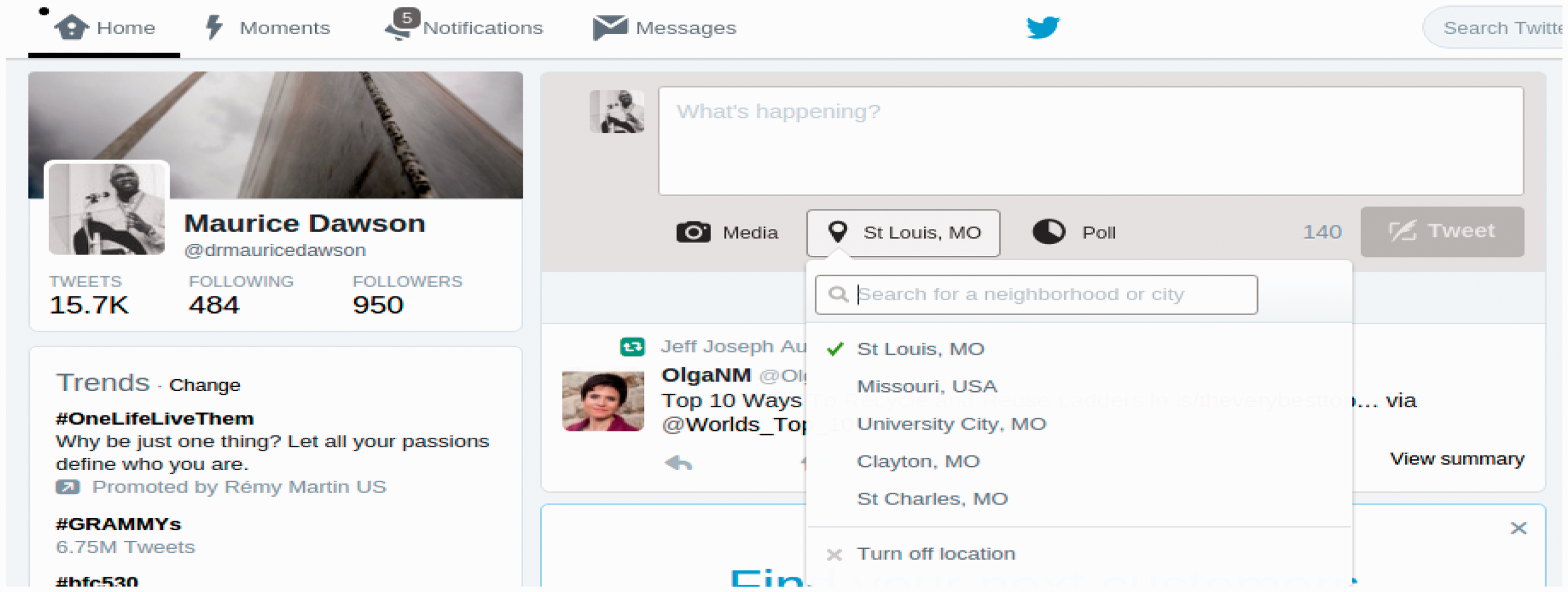
Exchange Image File Format
Exchange Image File Format (EXIF) data is a standard that specifies the formats for images, sounds, and ancillary tags used by digital cameras. The EXIF digital image standard specifies the following: the basic structure of digital image data files, tags and JPEG marker segments the standard uses, and how to define and manage format versions (Tešić, 2005). Research has been conducted on how to effectively extract EXIF data for prosecuting those involved in child pornography (Alvarez, 2004).
Extracting EXIF data using the ImageMagick application is rather simple in Debian based Linux operating systems. First, the following command is run: “sudo apt-get install imagemagick.” Next, the following command is run to extract the EXIF data: “identify -verbose/usr/share/backgrounds/sample_exif.jpg | grep “exif:”.” The EXIF data output for Figure 6 is displayed in Figure 7.
Twitter photo example. Exchange Image File Format data output.
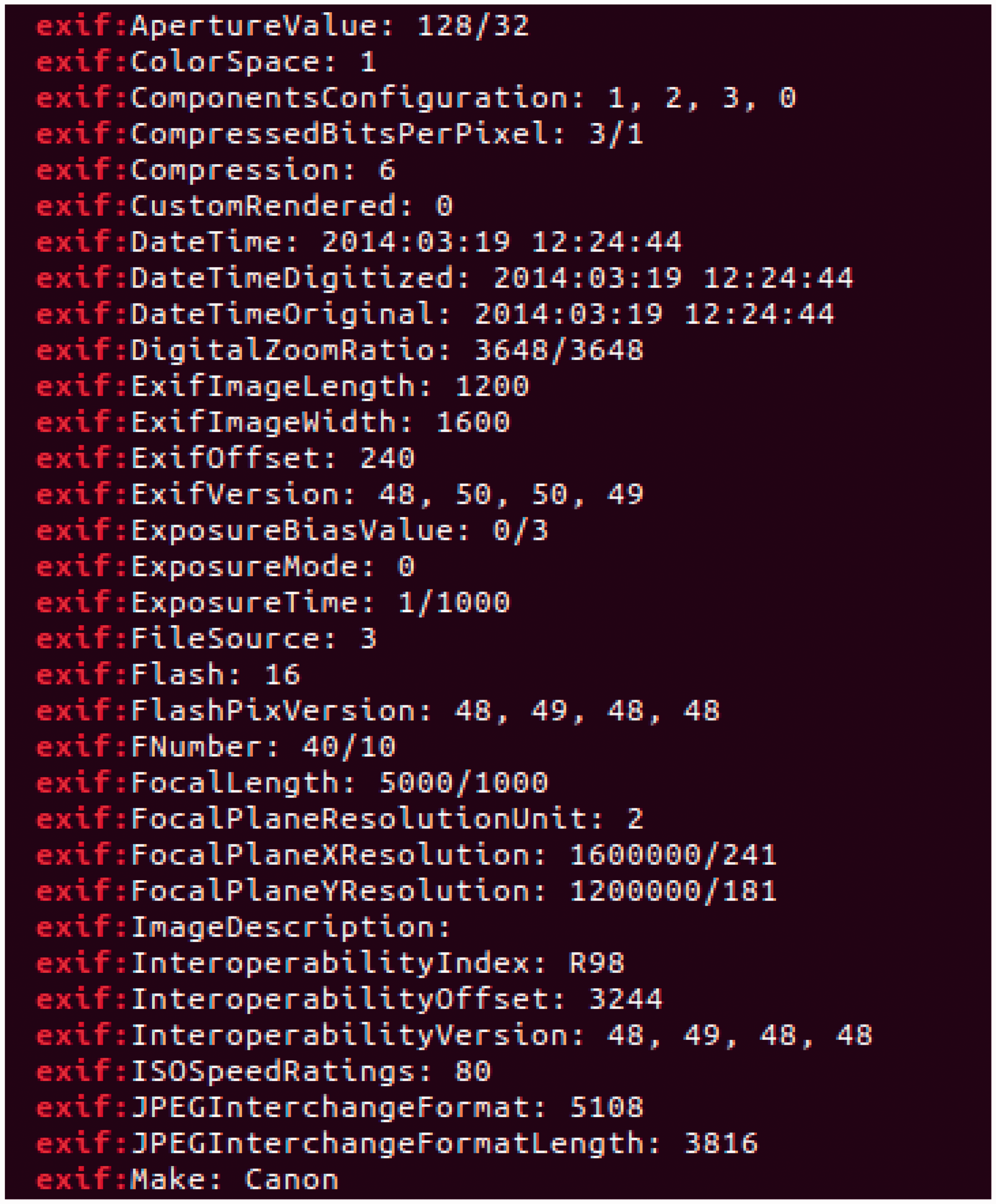
The data that is provided includes date and time of photo taken, camera used, and other properties that allow for a more detailed analysis over time. There are more programs than ImageMagick that allow the viewing of EXIF data. This includes applications that can be added to the Chrome browser, Firefox browser, and downloadable applications.
Stenography
Tweets can contains photos that have compressed and encrypted embedded data. Data can be hidden in image and audio files, making it nearly impossible for institutions to look at files that could contain information that is geared towards radical, extremist, or terrorist ideologies. Researchers uncover the validity of tweets used by political reports which can be correlated to use by nefarious organizations (Coddington et al., 2014). This means that students, professors, or staff could be unknowingly retweeting images that can be used for communication propaganda or illicit instructions. Figure 8 displays an example of the extraction of a photo using Steghide, where a simple text, 123456, was embedded using the command “steghide extract -sf pic.jpeg.”
Steghide stenography example.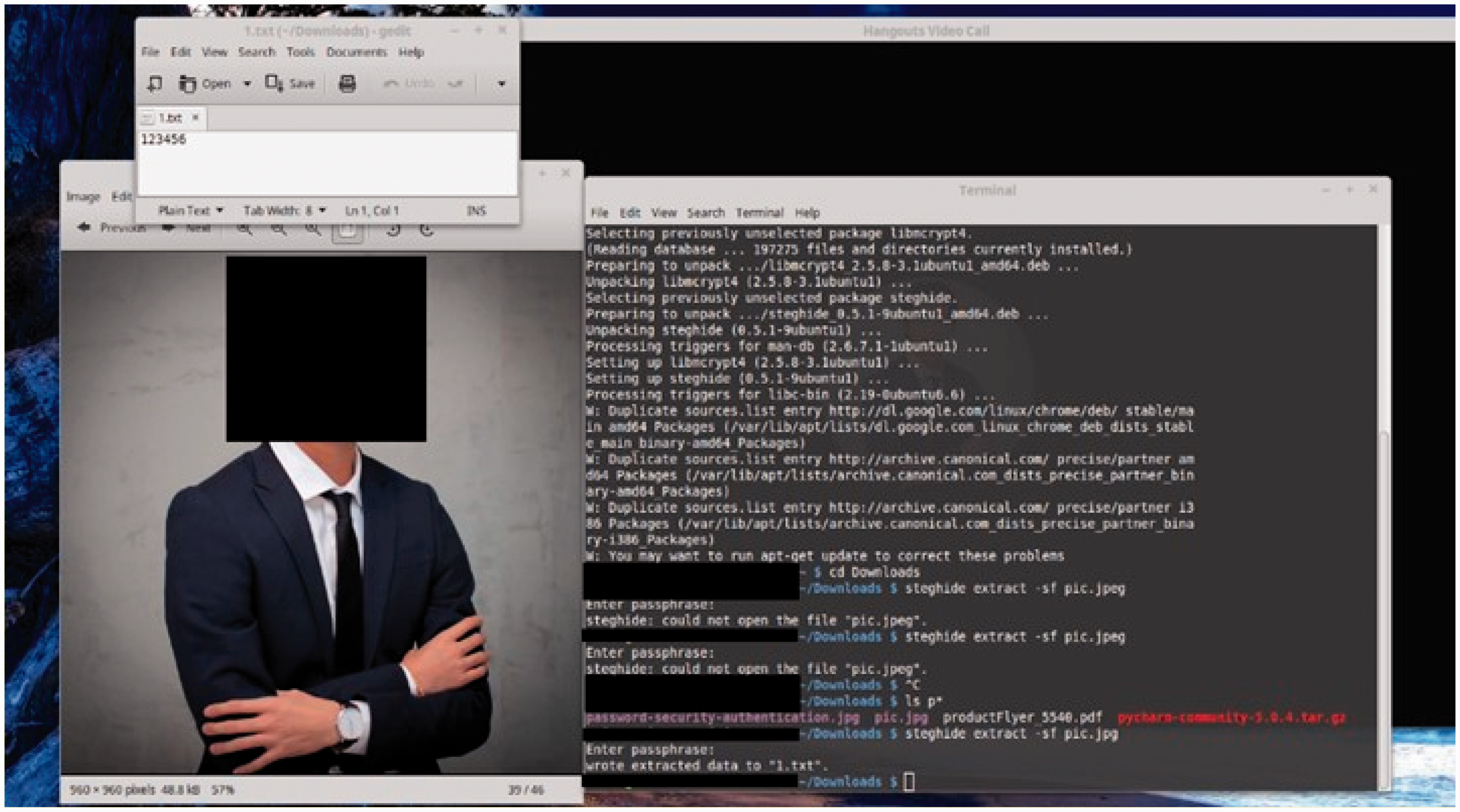
Text mining
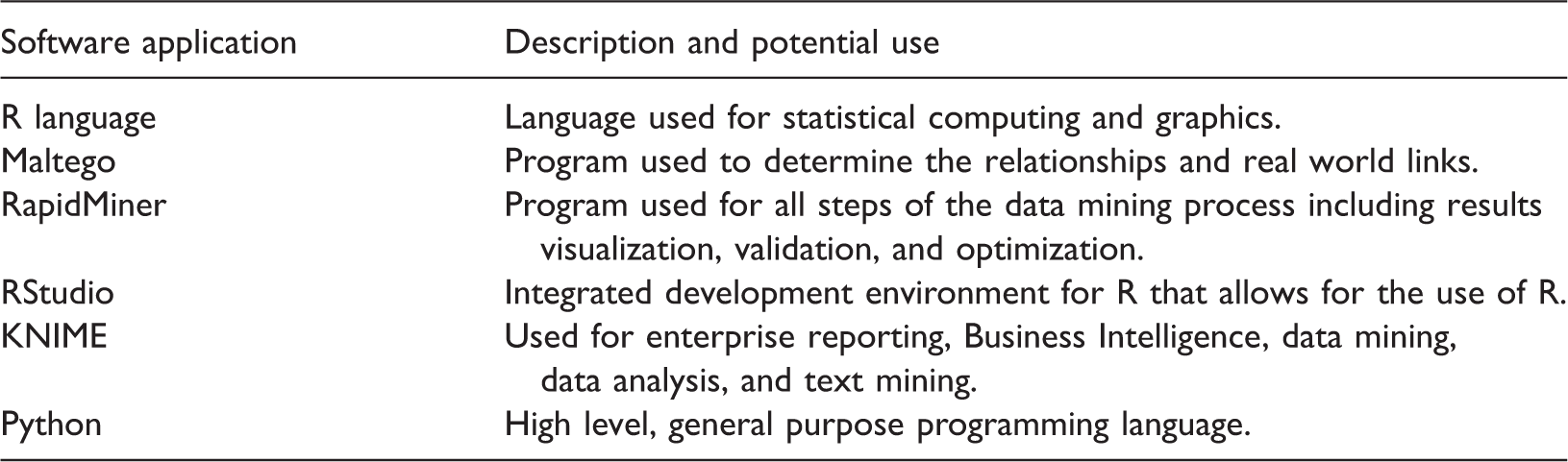
Open source mining tools.
Conclusion
This paper demonstrates the viability for microblogging to facilitate student knowledge creation practices. It proposes a model to describe how specific microblogging features can enhance the conveyance and convergence practices for the purposes of acquiring and transferring tacit and explicit knowledge among Twitter users.
Moreover, Twitter is proposed as a legitimate tool for teaching and learning. The fact that the use of Twitter can address several best practices when teaching today’s students/Digital Natives further validates Twitter as a quality teaching tool. Individuals responsible for educating Digital Natives should act now by sharing with their respective institutions how Twitter can be used to put online teaching best practices like CoI into practice, how Twitter can be used as a mobile app alternative, and how Twitter can be used to create a blended learning environment desired by today’s students.
Finally, while higher education institutions continue to increase the use of Web 2.0 in the classroom, this article provides evidence of the potential extraction of specific identifiable information that Twitter posts contain. As there are a number of proprietary and open source applications that allow for the extraction of images, the images should have the metadata removed. The current concern of universities is the type of content shared and not the data contained. This needs to change to ensure the overall privacy of the individual sending out the tweets. As a result, higher education institutions are encouraged to create policies to ensure that security and privacy of students’ educational tweets are protected.
Footnotes
Declaration of conflicting interests
The authors declare that there is no conflict of interest.
Funding
This research received no specific grant from any funding agency in the public, commercial, or not-for-profit sectors.
