Abstract
The device-free localization that locates an uncooperative target by analyzing its shadowing effect on wireless links in low-cost wireless sensor networks has become an attractive technique. Due to its ability of realizing localization without the need of equipping the target with any wireless device, device-free localization has lots of potential applications ranging from emergency rescue to patient monitoring. However, since the change of the received signal strength on links easily becomes unpredictable due to all kinds of dynamical factors, device-free localization is still a challenging problem. In this article, we propose a novel two-step sequential device-free localization method to enhance device-free localization performance. The sequential device-free localization first utilizes the geometric-based method to quickly obtain the coarse positioning result with low storage and computational requirements, and then exploits the location information of selected wireless nodes to improve the accuracy of the geometric-based localization result based on the optimization-based method, which ensures its robust performance. Experimental results in indoor and outdoor scenarios demonstrate the effectiveness and robustness of the proposed scheme.
Keywords
Introduction
Target localization and tracking techniques in wireless sensor networks have received lots of attentions during the past two decades since the position information is extremely valuable for commercial and military applications. Generally, the localization research can be divided into cooperative and non-cooperative localization. Unlike cooperative localization techniques that equip the target with a wireless device such as a radio frequency identification (RFID) tag, device-free localization (DFL) is a new concept that allows the localization and tracking for targets which neither carry any devices nor participate actively in the localization process.1,2 DFL technologies are particularly useful in a wide number of applications including intrusion detection, border protection, emergency rescue, patient or elder monitoring, and so on, where targets being tracked cannot be expected to cooperate with the localization system.
Conventional DFL methods utilize ultra-wideband (UWB) radar, video cameras, or infrared sensors to passively localize targets. These methods are limited by the deployment cost, privacy concerns, or their poor capability of penetration. Different from these techniques, the low-cost DFL which relies on received signal strength (RSS) measurements has recently become a promising technique and shown lots of potential applications. Nowadays, most wireless transceivers can easily measure the RSS during the normal communicating process, so it is convenient to use RSS measurements as coarse sensors for DFL. 1 Moreover, compared with conventional DFL methods, the RSS-based DFL approach has some merits on practical applications. It can not only work in obstructed scenarios with its ability of seeing through smoke, darkness, and walls but also avoid the privacy concerns raised by video cameras.
The basic principle of RSS-based DFL is that when a target moves into the area within a wireless network, it may cause the changes of RSS by shadowing, reflecting, diffracting, or scattering. The shadowed links will be different when a target locates at different locations, and this makes it possible to realize DFL based on the link measurements.3–9 However, due to the dynamic and sensitive nature of RSS, a slight variation of the environment will cause the changes of RSS measurements. Moreover, there are lots of other factors besides the presence of the target that can affect the variations of RSS, and therefore, the change in RSS due to target presence becomes unpredictable. To enhance the DFL performance, a number of RSS-based DFL algorithms have been proposed in recent years including the model-based method, the training-based method, the geometric-based DFL (GDFL) method, and so on. While the aforementioned methods have their respective merits, RSS-based DFL is still a challenging problem due to the uncertain and dynamic RSS character in indoor and outdoor environments. In this article, we propose a novel two-step sequential method to solve the DFL problem, which first utilizes the geometric-based method to quickly obtain the coarse positioning result and then exploits the location information of wireless nodes to improve the accuracy of the localization result based on the optimization-based method. The main contributions of this article are summarized as follows:
A robust two-step sequential DFL method (SDFL) is proposed. The algorithm uses simple geometric operations to generate the coarse estimation of the target’s position, which can keep the merits of low storage and computational requirements. On the basis of the coarse location, the low-complexity optimization-based method is used to enhance the accuracy of the localization result. Hence, this algorithm combines advantages of two different methods into a unified DFL process.
In the published DFL methods, wireless nodes mainly take charge of communicating and measuring RSS values. In fact, the location information of wireless nodes is not only known a priori but usually accurate as well, so we can use this useful information as an assisted condition to enhance the DFL accuracy. Unlike the previous DFL methods that node location information is only implicitly exploited to form line segments or represent the focus of an ellipse, the SDFL method explicitly utilizes the knowledge of nodes’ coordinates to improve the DFL accuracy.
A quasi-distance localization approach based on the optimal selected nodes is proposed to merge node location information into the SDFL method. The quasi-distance-based algorithm in the second step still does not assume any prior knowledge of the shadowing model or need any offline training, so it keep the merits of the geometric-based method in the first step.
The remainder of the article is organized as follows. “Related works” section presents the related works. The problem formulation is described in “Problem formulation” section. The details of the two-step SDFL algorithm are addressed in “Two-step sequential DFL algorithm” section. “Experimental results” section gives the experimental setup and experimental results. Finally, “Conclusion” section concludes the article.
Related works
In past decades, lots of research works have been carried out to realize the cooperative localization or tracking technique that requires the target to equip with a wireless device like a smartphone or a RFID tag and to cooperate with the special localization system. Various approaches have been proposed and tested in different scenarios of practical interest.10–12 Besides numerous works dedicated to applications in cooperative localization or tracking, there already exist some surveys13–15 that provide a comprehensive analysis about the cooperative positioning technology. The interesting readers can refer to these literature.
In this section, we primarily summarize the most relevant research on the DFL. As a promising technique, many RSS-based DFL approaches have been developed, and most of them can be classified into three categories. One main approach of DFL is to model the RSS variation, due to the shadowing or reflection of the target, as a function of the target’s position. In Wilson and Patwari, 3 an elliptical model is introduced to describe the spatial impact area when a target appears on a wireless link. This elliptical model assumes that the RSS of the link will change when a target locates inside the ellipse. Otherwise, the RSS will remain unchanged. Based on this elliptical model and motivated by computed tomography, Wilson and Patwari formulates a method termed as radio tomographic imaging (RTI) that estimates the RSS changes in the radio frequency (RF) propagation field of the interested area and then forms an image of the target-affected field by using a regularization method. This image is then used to infer the targets’ location within the deployed network. The localization performance of RTI may be further enhanced with the assisted techniques, such as frequency diversity, 4 antenna diversity, 5 power diversity, 6 and compressive sensing.7,8 Furthermore, some recent work explores the use of radio tomography in highly obstructed areas for the purpose of tracking moving objects through walls.16,17 To improve the elliptical model, Hamilton et al. 18 proposed a novel inverse area elliptical model (IAEM), which defines that the shadowing effect of a target on a wireless link is inversely proportional to the size of the smallest ellipse that contains the target. Based on the diffraction theory or extensive experimental data, the exponential-Rayleigh model (ERM), 19 the diffraction model (DM), 20 and the saddle surface model (SaS) 21 are recently proposed to model the RSS changes, and they are all incorporated into the particle filter framework to realize DFL. Although these novel models significantly enrich the research of the model-based DFL, lots of experiments have demonstrated that RSS is time-varying at different locations within the spatial impact area, and RSS even may change without human motion in the deployment area. Since most previous models that are obtained empirically or constructed according to the diffraction theory only describe the shadowing effect under the ideal conditions, they generally cannot be accurate enough to model RSS variations in real dynamical environments. Therefore, model errors are unavoidable when these models are directly used to realize RTI.
Another RSS-based DFL method is the training-based method, which matches the RSS samples collected online with the offline-constructed radio map. The procedure is similar to the fingerprinting in cooperative localization. 22 This method for DFL is originally proposed by Youssef et al., 2 and then is further developed by Seifeldin et al. 23 and Sabek et al. 24 Recently, channel state information (CSI) that can provide a higher dimensional measurement per link is utilized to generalize the radio map for improving DFL performance. 25 To enhance DFL performance in the time-varying environment, the training-based method proposed by Mager et al. 26 performed lots of experiments to quantify how changes in an environment affect the DFL accuracy. The training-based DFL method can naturally avoid model errors, but the training process is time consuming and labor intensive. Moreover, the radio map needs to be updated once the monitored area changes.
The third category is the GDFL method. Instead of using the shadowing model or the offline training, the GDFL method exploits the link line information affected by targets and simple geometric operations to realize DFL. Zhang et al. 27 proposed a particular deployment of wireless nodes and used the overlap of areas formed by shadowed links to estimate the target’s position. However, this method does not exploit spatial prior information about the target’s possible position to filter outlier points, thereby making it sensitive to noise. In order to overcome this shortcoming, Xiao et al. 28 proposed a novel nonlinear optimization approach with outlier link rejection for RSS-based DFL. In the geometric-filter (GF) method, 29 a threshold value was used to detect the shadowing links, and then a circular prior region was utilized to remove outlier links and points. Finally, the estimate of the target’s position was obtained by the weighted mean of the coordinates of all possible points inside the prior region. Furthermore, an enhanced GF algorithm was proposed by exploiting multichannel RSS measurements to enhance the DFL accuracy in cluttered environments. 30 The GF method neither needs to solve the underdetermined problem in model-based DFL nor needs to store the offline fingerprint database, so these characteristics reduce the algorithm’s storage and computational load. However, the weighted mean of all possible intersection points of shadowed links is a coarse approximation. More importantly, the suitable weight values in the GF algorithm are not easily generated, and some empirical weight values sometimes may be unreasonable. Hence, the localization performance of the GF algorithm is not very stable and particularly sensitive to the multipath effects.
Problem formulation
A DFL system is composed of M wireless nodes with known locations deployed around the area of interest, such as that shown in Figure 1. Each wireless node can transmit or receive radio signals at each time instant, and thus there are L = M(M – 1)/2 bidirectional links traveling through the monitored region. As shown in Figure 1, the links traveling through a target are shadowed due to scattering, reflection, diffraction, or absorption. Obviously, the target-affected links due to the target’s presence will be different when a target locates at different locations. Hence, it is possible to realize DFL based on the link information involved in the RSS measurements.1,2
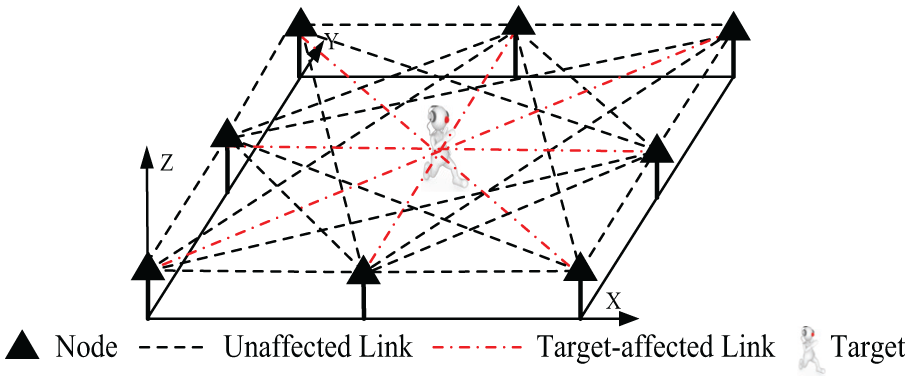
A DFL system made up of eight nodes.
In this article, all wireless nodes are coplanar with the single target to be tracked and are assumed within radio range of each other. Let the line segment li represent the link i from the node
Generally, the RSS of link i measured at time t can be represented as 3
where Pi represents the transmitted power, Si(t) represents the shadowing loss of link i due to the attenuation caused by the target, Fi(t) represents the fading loss, and Ji is the static losses because of antenna patterns or device inconsistencies. vi(t) represents other losses affected by noise. Thus, the RSS variation at time t can be represented as
where
The aim of a DFL system is to acquire the high-precision target coordinates at time t, with the information of RSS measurements
Two-step sequential DFL algorithm
This section introduces the proposed SDFL algorithm in detail. As shown in Figure 2, the SDFL algorithm includes the GDFL part and the optimization-based DFL part. While the geometric-based part of the SDFL algorithm shares some features with the previous GDFL algorithm,29,30,32 the concrete approach is definitely different. Moreover, the subsequent optimization-based DFL part based on the location information of wireless nodes is not included in these methods.

Algorithm framework for localizing a target.
GDFL method
The basic idea of the GDFL method is that the shadowed links affected by a target tend to intersect with each other at points near the target’s true position, and therefore, the key step of GDFL is to find the target-affected links. Due to the presence of noise and multipath effects, RSS variations are not stable and even RSS may vary without human motion in the monitored area. Therefore, even if some links do not go through the target’s vicinity, the RSS measurements of these links may obviously vary. Hence, it is necessary for the geometric-based method to remove outlier links before estimating the target’s position. Based on the above analysis, the geometric-based part of the SDFL algorithm includes the following steps: effective links identification, removing outlier links via spatial prior information, and generating a position estimate. Unlike the earlier work,29,30,32 we adopt the non-weighted mean method to estimate the target’s position for avoiding the difficulty of acquiring the reasonable weights. Moreover, the spatial prior region is modified in “Removing outlier links via spatial prior information” subsection.
Effective links identification
Some previous DFL experiments have demonstrated that the RSS on a wireless link may be distinctly attenuated or amplified since the appearance of the target will cause some links to be shadowed.4,6 Therefore, if the link i is shadowed by a target, the corresponding RSS change of the ith link must be above the shadowing detection threshold. To pick out the target-affected links, let yth represent the shadowing detection threshold which can be obtained experimentally. Thus, the set
Since the RSS fluctuation affected by noise is usually less than the detection threshold yth, the noise influence is alleviated by using the simple threshold detection method, and only the significant links that the RSS measurements evidently vary are selected.
Removing outlier links via spatial prior information
Although the last step of GDFL alleviates the negative effect of noise, the RSS variations in some wireless links that are not near the target may be also above the threshold value yth because of multipath effects.27,28 As shown in the work of Talampas and Low,29,30 outlier links may intersect with other effective links at points far away from the target, so outlier links that are not excluded from the localization process will result in large tracking errors. To remove the negative effect of such outlier links on the target position estimate, there are two kinds of approach to distinguish the target-affected links and the outlier links. One approach exploits the spatial prior information to choose the target-affected links,29,33,34 while another approach identifies the outlier links based on the standard variance of the measurement noise.
35
In this article, we also make use of the same idea in the work of Talampas and Low
29
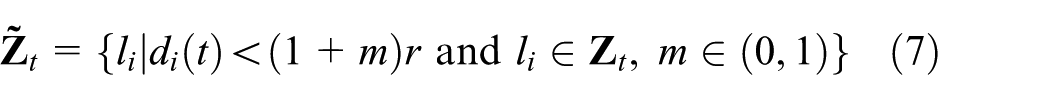
and Wang et al.33,34 that spatial prior information is used to pick out the real target-affected links from the set
where
Since the shortest distance between the outlier link and the circular center
However, as shown in Figure 3, if the target locates at the boundary of the prior region
where m is a positive decimal fraction between 0 and 1. The equation (7) means that when di(t) > (1 + m)r, the link i can be considered as a outlier link.

Illustration of effective links and the circular prior region.
Using triangle centroids to generate a position estimate
After identifying the effective links and removing the outlier links, assume that there are J (J ≤ L) links remaining in
To avoid the difficulty of generating proper weights, in this article, we seek an approximate result by using the non-weighted mean method. The experimental results in “Experimental results” section will demonstrate that the non-weighted GDFL method can provide the almost same localization performance as the weighted mean method. Meanwhile, different from solving for the link intersections in the work of Talampas and Low,
29
we use centroid points of virtual triangles consisting of effective links to represent the target’s potential positions. This is based on the consideration that a target will affect its ambient links rather than only two links. Since there are a total of J effective links in
where (xj, yj) is the centroid coordinate of the jth virtual triangle. Figure 4 depicts an example of how to acquire the estimated position of the target by averaging the centroids’ coordinates of three triangles.
As shown in Figure 4, it can be observed that not all centroids of triangles lie inside the circular prior region. The position of each centroid represents a potential position of the target, so those centroids that locate outside the prior region should be regarded as the outlier target points. Similarly, the circular prior region can be used again to remove these outlier points. In other words, when

Illustration of the non-weighted triangle localization method.
Optimization-based DFL method
Improving the geometric localization result by using node location information
Although the above GDFL method only needs using elementary geometric operations to realize DFL, the estimated result from the GDFL method is only a coarse approximation due to simply using the mean of the triangle centroids as the target location. In addition, the GDFL is particularly sensitive to multipath effects. Therefore, the geometric localization result
In order to improve the geometric-based localization result, the basic idea of the optimization-based DFL method is to merge node position information into the DFL process based on the fact that generally the position information of wireless nodes is accurately known before they begin to work. Under the constrained least squares (LS) framework, 36 in this article, a quasi-distance-based DFL method is proposed by exploiting node position information to enhance the DFL accuracy. It should be noted that in this step, the target still does not carry any device. Hence, different from the device-based localization that can directly measure distances between the target and nodes by using the device-to-device method, we use the estimated distances between the coarse position of the target and wireless nodes to substitute the measuring distances in the device-based localization. We refer to this kind of distance as quasi-distance. Thus, this method can continue to maintain the merit of DFL that need not carry any device, and at the same time the accurate position information of nodes is utilized to improve the geometric-based localization result. In addition, in order to determine which node is better to participate in the optimization, we exploit the geometry effects of node configurations to select most suitable nodes in each optimization.
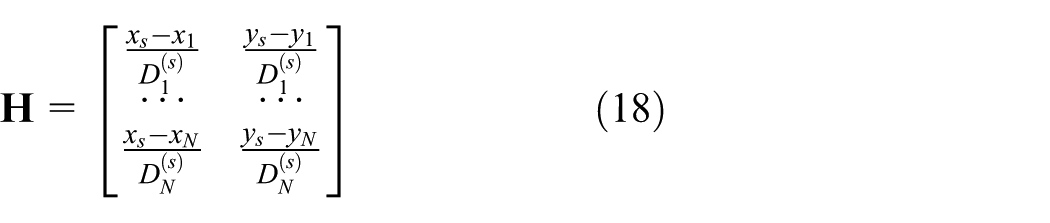
Based on the position coordinate
where
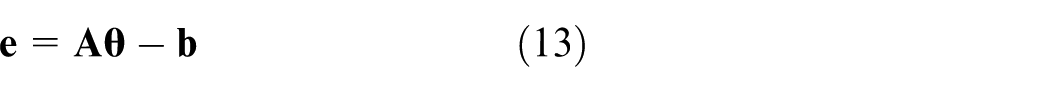
Thus, the error between the estimated and accurate distances can be represented as
where
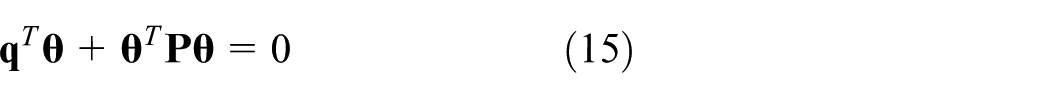
where
subject to a quadratic constraint
where
where λ is determined in Appendix 1.
Node selection
The remaining problem of the optimization-based DFL is how to determine which node is better to participate in the optimization. In fact, the scheme that all M nodes join in the optimization process is not a good method, because it will result in high computational load due to the high dimensions of matrix
Based on the GDOP analysis in the work of Levanon 37 and Sharp et al., 38 the GDOP will be given by
where G11 and G22 are the diagonal elements of the matrix
Once the matrix
However, it should be emphasized that the GDOP value should be computed for every new position, while it can reduce the size of matrix
Experimental results
Experimental setup
To demonstrate the applicability of the SDFL method, we develop a prototype DFL system which is made up of 24 wireless nodes in an open outdoor environment (Scene 1) or 16 wireless nodes in a rich multipath indoor scenario (Scene 2) to carry out extensive experiments. The photographs and layout of the deployment area are shown in Figure 5, where a target (a person) moves clockwise along a predefined trajectory and its location is estimated once per second. A metronome and uniformly placed markings on the floor help the experimenter to take constant-sized steps at a regular time interval, and the target’ moving speed is about 1.0 m/s. In the outdoor experimental environment, wireless nodes are placed 1.5 m apart along the perimeter of a 9 × 9 m square area being free from obstructions, while 16 nodes are deployed to cover a 8 × 8 m laboratory area where there are numerous obstructions such as tables and other equipment. Although it is not necessary to place the nodes in a uniform spacing, in this article, all wireless nodes are evenly spaced at the perimeter of the deployment region for simplicity. In all experiments presented in the following sections, the baseline RSS measurements are first taken for calibration. The calibration stage lasts for approximately 60 s when the target is not inside the monitored area.

Experimental networks: (a) photograph of the uncluttered outdoor environment, (b) geometry of the uncluttered outdoor environment, (c) photograph of the highly cluttered indoor environment, and (d) geometry of the highly cluttered indoor environment.
The transceiver of each node is a TI CC2530 device operating on the 2.4 GHz ISM band with IEEE 802.15.4 standard, which is placed on a tripod that is 1 m above the ground. To ensure regular network transmission, a token ring protocol is adopted to guarantee the stability of the networks and control transmissions. Every node has its ID number and broadcasts its link information in turn with the transmission interval 5 ms in our experiments. During the transmitting period of each node, all other nodes receive data packets and measure the RSS of the link from the transmitter to themselves. The information packets of each transmitting node includes the ID of the node and the most recent RSS measurements of the links between all other nodes and itself. A data-acquisition node listens to all network broadcasts from the measurement nodes and transfers the RSS data to a laptop computer with 3.5 GHz processor and 8 GB memory via a UART port.
Performance evaluation and comparison
Here, we compare the performance of the two-step SDFL method with two types of algorithms, that is, the geometric-based GF algorithm 29 and the model-based RTI algorithm 3 in both outdoor and indoor scenarios. For the sake of fairness, the one-step GDFL algorithm without using the node location information is also used in the following experiments for comparisons. The default parameters are summarized as follows: the radius of the prior region is set as 1.5 m, and the detection threshold is 4 dB in GF, GDFL, and SDFL. In the SDFL method, four nodes are selected to participate in the optimization according to the analysis in Figure 7(c) and m is 0.2. The parameters used in the RTI algorithms are summarized as follows: the width of the ellipse is 0.15 m, regularization parameter is 4.5, and the number of grids is 3600. For high reliability, all the localization results are obtained from the average of 50 independent experiments.
Figure 6(a) and (b) show the tracking errors of the SDFL, GDFL, GF, and RTI methods, respectively. In Figure 6, it can be observed that the two-step SDFL algorithm has the least tracking error in both indoor and outdoor scenarios. Especially, the SDFL algorithm is superior to the one-step GDFL method, which proves the effectiveness of the proposed optimization-based method by exploiting the position information of nodes. Meanwhile, it should be noted that the tracking error is periodically relatively large for some seconds. This can be attributed to the fact that when the target locates at the corners, there will be fewer target-affected links.

The comparisons of tracking errors: (a) Scene 1 and (b) Scene 2.
The detailed statistical data about tracking errors are summarized in Tables 1 and 2. In Table 1, we can see that the tracking performance of the SDFL algorithm is better compared with the GDFL, GF, and RTI methods in the uncluttered outdoor environment, with the mean tracking error reduced by 0.171, 0.191, and 0.378 m, respectively. Meanwhile, we can see that although the GDFL uses the non-weighted method to calculate the position of the target, the tracking performance of the GDFL method is similar with that of the GF algorithm.
Comparisons of tracking errors—Scene 1.

RMSE: root mean square error; SDFL; sequential device-free localization; GDFL: geometric-based device-free localization; GF: geometric-filter; RTI: radio tomographic imaging.
Comparisons of tracking errors—Scene 2.
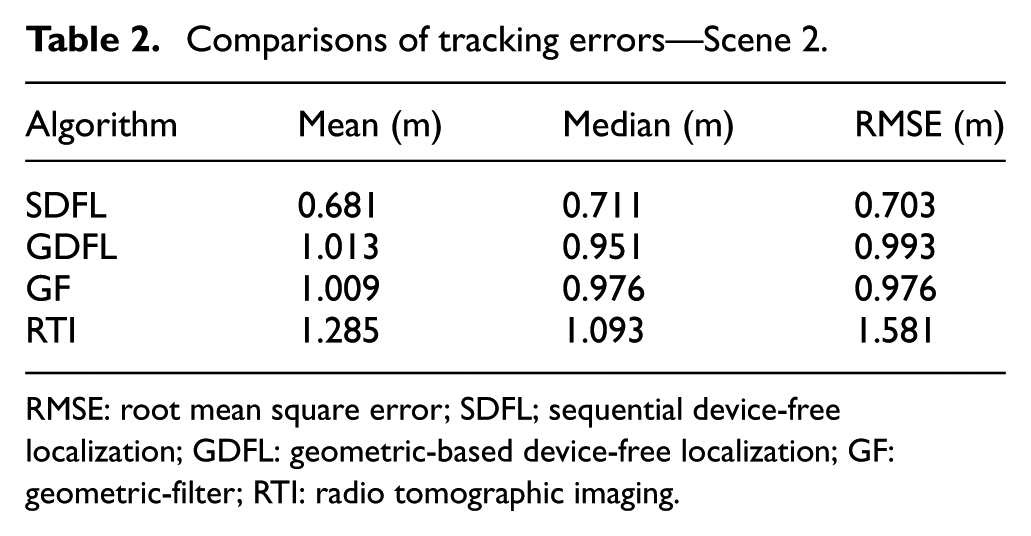
RMSE: root mean square error; SDFL; sequential device-free localization; GDFL: geometric-based device-free localization; GF: geometric-filter; RTI: radio tomographic imaging.
Different from the outdoor environment, multipath effects cause higher RSS fluctuations in the cluttered indoor scenario, and thus, the tracking errors of all algorithms become larger in the indoor environment by comparison between Tables 1 and 2. However, the two-step SDFL method can still achieve the highest tracking accuracy, and the mean tracking error of SDFL is still less than 1 m. In addition, the RMSE of the two-step SDFL algorithm is improved by 29.2%, 28.0%, and 55.5% when compared with the GDFL, GF, and RTI methods, respectively. These results show that the two-step SDFL approach can provide the stablest localization performance among all the methods in the highly cluttered indoor environment.
Discussion
In this subsection, to further evaluate the robustness of the two-step SDFL algorithm, we examine the impact of different parameters including radius of the circular prior region, detection threshold, and the number of nodes that take part in the optimization-based process. Figure 7(a) shows the effects of the different radius r on the tracking performance for both scenes. From Figure 7(a), we can clearly find that the tracking error is large when the radius r is big, because too many outlier links are allowed to be involved in the GDFL process under this condition. On the contrary, since the target may travel outside the prior region when the radius r is too small, the tracking error will also increase due to the misuse of spatial prior information. These phenomena are consistent with the description of equation (7), which has shown that the radius of the prior region determines how many outlier links are removed. In Figure 7(a), the tracking performance of SDFL is good when the radius r is between 1.2 and 1.7 m for Scene 1 and between 1 and 1.6 m for Scene 2. The tracking errors will increase when the value of radius is outside the above scopes.

Performance comparisons under different parameters: (a) tracking performance under different radius of the circular prior region, (b) effects of different detection threshold values, and (c) effects of the different number of nodes that take part in the optimization-based process.
Then, the performance of the SDFL algorithm is evaluated under different threshold values. From Figure 7(b), the tracking performance of SDFL is good when the threshold value is between 3 and 7 dB for Scene 1 and between 3 and 5 dB for Scene 2. This attributes to the fact that the higher detection threshold will result in fewer detected effective links and then generate less centroids that can be regarded as the target’s possible positions. On the contrary, if the threshold value is set too low, the geometric-based algorithm will become more susceptible to noise, especially in the rich multipath indoor scenario. In addition, from Figure 7(b), we can find that the range of good threshold values in Scene 1 is larger than that in Scene 2. For Scene 1 with M = 24 nodes and the monitored area S = 81 m2, the average link density ρ is 3.41/m2, while the average link density ρ = 1.88/m2 in Scene 2 with M = 16 nodes and the monitored area S = 64 m2. Therefore, with the same radius r = 1.5 m in both scenes, the average number of links crossing prior region NL = πr2ρ are 24.07 for Scene 1 and 13.25 for Scene 2, respectively. Due to the higher average link density, even if the high threshold value is set in Scene 1, there are similar number of effective links as the low threshold value in Scene 2.
The tracking errors under different numbers of nodes that take part in the optimization process of SDFL are illustrated in Figure 7(c). We can find from Figure 7(c) that it is not conspicuous for the improvement of the tracking accuracy when more nodes participate in the optimization process. Moreover, the tracking accuracy decreases slightly when the number of nodes increases to seven or higher. Generally, the position information of four to six nodes are enough to enhance the localization precision, which can help to have a good trade-off between the tracking performance and computational complexity.
At last, Figure 8 gives the average running time required to generate one position estimate for four algorithms in both indoor and outdoor scenes. Although the RTI method has the need of solving the matrix inverse problem, the matrix inverse operation of RTI needs only to be calculated once. Therefore, the matrix inverse time of RTI is not included in the total running time of RTI. Thus, what the RTI technique needs to perform in each execution is the multiplication of a known matrix and a measurement vector. Therefore, its running time can be very low in Figure 8. Since the geometric-based algorithms’ execution time scales with the number of links in the network, the running time of the GF and GDFL algorithms in Scene 2 is less than that in Scene 1. Due to adding the constrained LS and GDOP step in the SDFL algorithm, the running time of the proposed method is a bit larger than the pure geometric-based method such as the GDFL algorithm. However, since the GDOP values can be calculated in advance, the proposed SDFL algorithm only introduces the small additional computation load. Although the mean execution time for SDFL is higher than the benchmark schemes, the less 0.1 s average execution time for both scenarios can still satisfy the real-time requirement for most DFL applications. Moreover, by optimizing the parameters and reducing the number of nodes, the average execution time of SDFL can be further reduced.
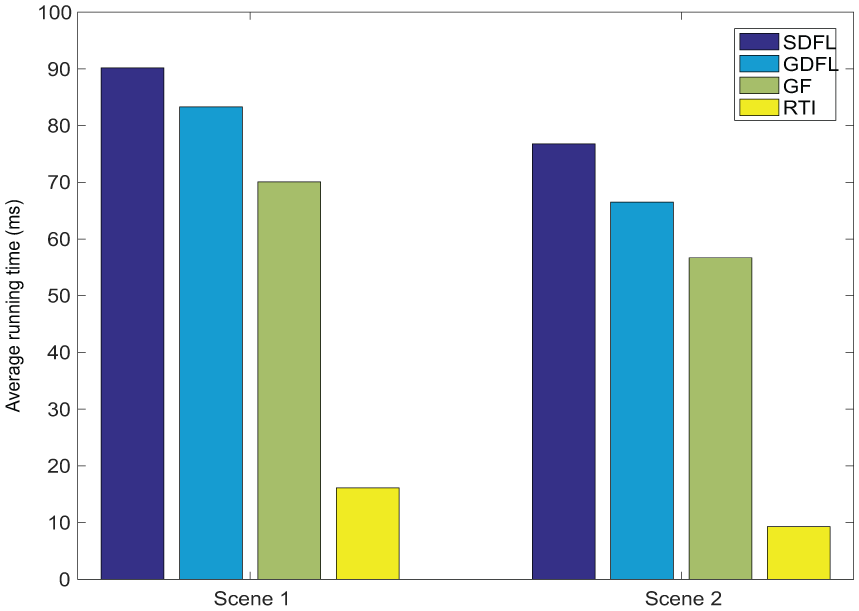
Running times of different algorithms.
Conclusion
To realize high tracking accuracy and suitable computational cost at the same time, a novel two-step SDFL approach is proposed which combines advantages of the geometric-based and the optimization-based DFL methods. In the GDFL part, the shadowed links that are really affected by the target are exploited to create virtual triangles whose centroids are regarded as the potential target positions. In the optimization-based DFL part, the location information of wireless nodes is exploited as an assisted condition to enhance the DFL accuracy. The experimental results in open outdoor and cluttered indoor environments show that the tracking accuracy is improved by using the proposed SDFL method.
It should be mentioned that there are still some problems to be solved. One challenging problem is how to obtain the baseline RSS measurements in the realistic applications. It is difficult to provide vacant deployment area for the baseline RSS measurements such as in the rescue or emergency response operations. Meanwhile, in the proposed scheme, we consider only the scene of tracking one target. How to realize multitarget localization is still an open problem for future research. In addition, the Cramer–Rao lower bound (CRLB) on the position estimation precision needs be considered in the future.
Footnotes
Appendix 1
The minimum of equation (14) under the constraint condition (equation (15)) is obtained by the technique of Lagrange multipliers
where λ is the Lagrange multiplier. Necessary conditions for minimizing equation (20) can be obtained by taking the gradient of
Solving for
where only λ is yet to be determined. In order to find λ, we can impose the quadratic constraint directly by substituting equation (22) into equation (15), so that
By using the eigenvalue factorization, the matrix
where
where
where
Therefore, the function of the Lagrange multiplier λ is a polynomial. Due to its complexity, numerical methods have to be used for root searching. After obtaining the Lagrange multiplier λ, the quadratic constraint (equation (15)) is imposed on the final solution.
Handling Editor: Paolo Barsocchi
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the National Natural Science Foundation of China under Grant No. 61405094, in part by the National Key Research and Development Program of China (2017YFB0503500), Jiangsu overseas visiting scholar program for university prominent young and middle-aged teachers and presidents, and Jiangsu Government Scholarship for overseas study.