Abstract
This article studies the physical layer security of massive multiple-input multiple-output system in time-division-duplex mode. Specifically, a single-cell downlink massive multiple-input multiple-output communication system is considered. The resulting achievable secrecy rate is investigated in the presence of passive or active eavesdroppers. The analytical results reveal that the massive multiple-input multiple-output system is naturally immune to passive eavesdroppers, but will be dramatically degraded by active attack. On account of the risk caused by active attack, a simple and effective detection algorithm is proposed. Uplink pilots with random phases are transmitted during the detection operation. By comparing the phase deviation change of the received pilot signals’ cross product, the active eavesdroppers can be detected exactly. The closed-form expressions for probabilities of detection, false alarm, and false rejection are obtained respectively, which can demonstrate the robust performance of the proposed detection scheme. To maximize the secrecy energy efficiency of the system, the optimal power allocation strategy is studied under total power constraints. This optimization problem is efficiently solved by fractional programming. Numerical simulation results are derived to validate the secrecy performance of the massive multiple-input multiple-output system, the active pilot attacker detection performance, and the energy efficiency optimization effect.
Keywords
Introduction
The fifth-generation (5G) wireless network is expected to support a significantly large amount of mobile data capacity and achieve better quality of service (QoS) in terms of communication rate, delay, reliability, and security.1,2 Among the emerging technologies, massive multiple-input multiple-output (MIMO) as one of the most potential promising technologies has attracted much attention and has been well assessed through theoretical analysis and laboratory tests.3,4 Massive MIMO is a special MIMO technology where base station (BS) is equipped with large number of antennas, typically tens or hundreds. Combining with a time-division-duplex (TDD)-based transmission can help resolve many of the issues gaining channel state information.5,6 In TDD mode, massive MIMO systems could exploit the reciprocity to process the channel estimation on the uplink. In particular, the BS exploits law of large numbers like certainties as it serves each one over a combination of a large number of independent transmission channels. Large arrays can eliminate the noise and interference with simple signal processing, such as basic linear combination operations.7,8 So the multiplexing gain can be fully used to maximize the channel capacity. The advantages of massive MIMO include higher data rate, better reliability, and less noise and interference. Another advantage of massive MIMO is the potential of physical layer security as the huge degrees of freedom, especially against the passive eavesdroppers. 9
The open broadcast nature of wireless medium results in information leakage to some unintended receivers. Physical layer security is promoted to achieve secure transmission by exploiting the inherent uncertainties and independent of wireless channels, noise, fading, and interference.10,11 And this security is achieved through information theory security rather than traditional encryption and decryption. Accordingly, physical layer security has the potential to push the secrecy performance toward a brand new level with its theoretically uncompromisable security guarantee.
Research on physical layer security in conventional MIMO system has obtained abundant results.12–14 As a promising candidate technology for meeting the upcoming 5G era, academia and industry has paid extensive attention to massive MIMO communication recently. However, the existing literature on the combination of physical layer security and massive MIMO is not sufficient. In the studies by Zhu et al. 15 and Wu et al., 16 reliable secure downlink transmission in multi-cell multi-user massive MIMO systems with maximum ration transmission (MRT) precoding and artificial noise generation at BS was investigated in detail. A single-cell massive MIMO communication in the presence of an adversary capable of jamming and eavesdropping also have attracted attention of some researchers.9,17 These works show that massive MIMO is naturally resilient to passive eavesdroppers, but harmed by training-phase jamming. In addition, large antenna arrays can achieve excellent directional gain, so excellent beamforming design can be exploited to enhance the security performance.18,19 Moreover, Relaying is a potential technique to improve legitimate channel capacity and reduce the undesirable information leakage, so it can be introduced into massive MIMO system to improve the secrecy performance.20,21 Also few works focus some other special systems with massive MIMO, such as Internet of Things (IoT) 22 and Device-to-Device (D2D). 23 Additionally, the very large freedom of the massive MIMO system can generate extremely long secret encryption keys. Some secret keys generation methods have been proposed for massive MIMO system.24,25
According to some existing related studies,9,17 massive MIMO has potentiality of physical layer security against passive eavesdropping attacks. So smart eavesdroppers should switch from a passive mode to an active mode by pretending to be an intended user and transmitting pilot sequences of its own. The impact of this pilot contamination attack is that it will reduce the accuracy of BS’s channel estimation, which will infect the precoding filter design at transmitter to implicitly beamform toward active eavesdropper, leading to information leakage. 26 So it is crucial to detect the active eavesdropper for the secure communication. Some simple detection strategy can be used during the training phase. For instance, BS can detect the active attacker by some slowly changing parameters, such as signal power, large-scale fading, or certain statistics. 9 As the large-scale fading and noise power changes slowly at a long period, the received power will converge to some fixed value. If an active attacker exists, the received power will increase, so the active attacker can be detected. 17 Unfortunately, the eavesdropper can adapt its transmitted power over several coherence intervals and emulate the natural change of the channel propagation environment. Through these operations, the eavesdroppers cannot be detected. Besides, when the eavesdroppers are absent, the covariance matrix of the received pilot signal converges to a rank-one matrix. Otherwise, the matrix will converge to a full rank matrix with a large probability when some eavesdroppers are present. So the eavesdropper can be detected by comparing the largest and second eigenvalues of the covariance matrix. This scheme can provide significant performance, but it needs some more observations and also needs a good estimation of the noise power. As we know, the inner product of the different received signals would converge to a fixed phase value if the pilots adopted phase-shift keying (PSK) signals. 27 If any eavesdropper is present, this inner product value will converge to a different phase at a large probability. This scheme is easy, but the false alarm probability depends on the PSK constellation scale. Only when the size is very large, the detection probability can be close to 1. This scheme is hard for the actual system due to its low energy efficiency and high symbol error rate. In the study by Hou et al., 28 some random orthogonal pilot signals were used to operate the detection, and this scheme was robust even without any prior channel knowledge. However, these pilots should be designed carefully, which improves the complexity of the system.
Energy efficiency is a crucial design objective to reduce operating costs for mobile operators. 4 The development of massive antennas array can achieve diversity gain with some simple beamforming techniques, such as maximum ratio transmission (MRT), zero forcing (ZF), and minimum mean square error (MMSE). Meanwhile, massive MIMO technology can provide high energy efficiency which is suitable for the future wireless communication network. Ngo et al. 7 analyzed potential of energy efficiency of the massive MIMO in detail. In secure communication system, due to the simultaneous impact of legitimate users’ and eavesdroppers’ signal quality, transmit power has a bidirectional effect on the secrecy performance. Hence, power allocation scheme is significant for enhancing wireless security. Power allocation between desired signal and artificial noise is investigated by maximizing a lower bound on the achievable secrecy rate. 29 In the study by Chen et al., 30 a joint optimization of source and amplify-and-forward (AF) relay power allocation scheme had been proposed to maximize the secrecy energy efficiency (SEE). And the optimal source and decode-and-forward (DF) massive array relay power allocation was analyzed in the study by Chen et al. 31 Moreover, the optimal energy efficient power allocation for secure communication in massive MIMO had also been studied. 32 These analysis methods and mathematical tools also can be used to analyze the SEE of the system in this article.
Active attacker detection and power allocation are all crucial factors that affect physical layer security performance in massive MIMO system. To the best of our knowledge, overall there is limited attention to these problems in existing works. 33 In this article, we consider all these issues and give some valuable formulas, data, and conclusions. The contributions of this article are as follows:
The secrecy capacity analysis for the basic three-node massive MIMO model is provided. It reveals that the massive MIMO is robust against the passive eavesdroppers and harmed by active pilot attack. Also the nonnegative secrecy capacity condition is obtained. Results suggest that the secrecy capacity increases with the number of antennas. Moreover, the limit of the secure rate has been obtained as antenna number increase toward infinity.
A new active eavesdropping detection scheme based on pilots with random phases is proposed at training phase. The scheme only needs uplink pilots with random phases. If an active eavesdropper are present, the phase of the received signals’ cross product will converge to a fixed value. So the detection can be operated by comparing the cross product’s phase to some threshold. System overhead will be very small. Then, the probabilities of detection, false alarm, and false rejection are analyzed respectively.
To maximize the SEE under some constraints, the optimal source power allocation scheme is studied in this article. The fractional programming and Lagrange multiplier method are adopted to solve the fractional programming problem. And the optimal value can be easily gained by limited iterations.
The remainder of this article is organized as follows. The system model and the secrecy performance are described in section “System model.” The proposed active attacker detection algorithm is presented in detail in section “Detection for active eavesdropper.” In section “SEE analysis,” the energy-efficient power allocation scheme is analyzed. In section “Numerical results,” the numerical and simulation results are presented to validate the effectiveness of the schemes in the article. Finally, section “Conclusion” draws the concluding remarks.
System model
We consider a typical three-node transmission system, consisting a legitimate transmitter (Alice), an intended receiver (Bob), an eavesdropper (Eve). The TDD massive MIMO system is considered, in which channel reciprocity holds perfectly in data block (one slot at least). As depicted in Figure 1, Alice is a massive antenna BS equipped with

The system model, one base station with massive antennas (Alice), one single antenna receiver (Bob), and one single antenna eavesdropper (Eve).
Channel estimation and precoding
The goal of the system is to provide reliable communication between Alice and Bob. Due to TDD model, it is effective for transmitter Alice to focus on the user Bob by precoding or beamforming design. That design requires the knowledge of
During this training phase, Bob sends the pilot sequence

where

We note that parameter
Then Alice treats the estimated channel

where


where
Secrecy performance analysis
Accordingly, the instantaneous signal-to-noise ratio (SNR) at Bob is given by

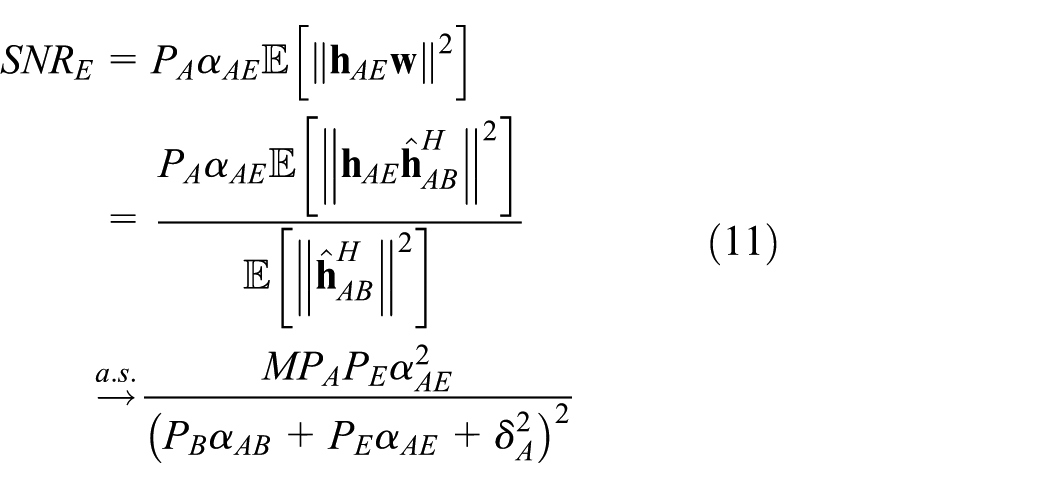
Similarly, the SNR at Eve can be expressed as

In the massive MIMO system, the antenna arrays’ distance and the distance between Bob and Eve are typically longer than the half of the wave length

as
In addition, according to the Lindeberg-Levy central limit theorem, we get this

where the
Using the above conclusions, we can simplify the

Similar to Bob, average SNR at Eve is given by
As a result, the achievable secrecy rate is formulated as

where
We can observe that if Eve is passive,
The first-order derivative of

From equation (13), it can be derived easily that
Meanwhile, we can get the upper limiting secrecy capacity when BS antennas number reach infinity

Detection for active eavesdropper
From the above analysis, we can understand that if Eve attempt to eavesdrop the useful message in massive MIMO system, a more effective strategy is to actively contaminate the pilot training phase. For fixed training scheme and most practical applications, as the cellular communication, the pilot set is public and used repeatedly. The eavesdroppers can easily survey and imitate the pilot signals. And once if Eve emits the same pilots as Bob, then the uplink channel estimation
As described previously, detection of an active attacker is crucial for secure communication in massive MIMO system. Since the channel vectors
The large-scale fading changes very slowly at a long period, while the small-scale fading changes rapidly. The antenna number is very large, so the statistics of Alice’s received vector will converge to some fixed numerical value. In this section, we utilize phase of some statistics to detect the existence of active eavesdroppers.
In the detection scheme, Bob sends the normal uplink pilot signals to BS (Alice) in the training phase, but delivers some changed pilots with a known random phase symbol occasionally when BS tries to detect presence of active eavesdroppers. We assume two training slots are used for detection.

where the superscripts 1 and 2 represent different pilot moments.
Then, we can derive a statistical quantity (scaled cross product of the received vectors
The scalar product can also be denoted as equation (16)
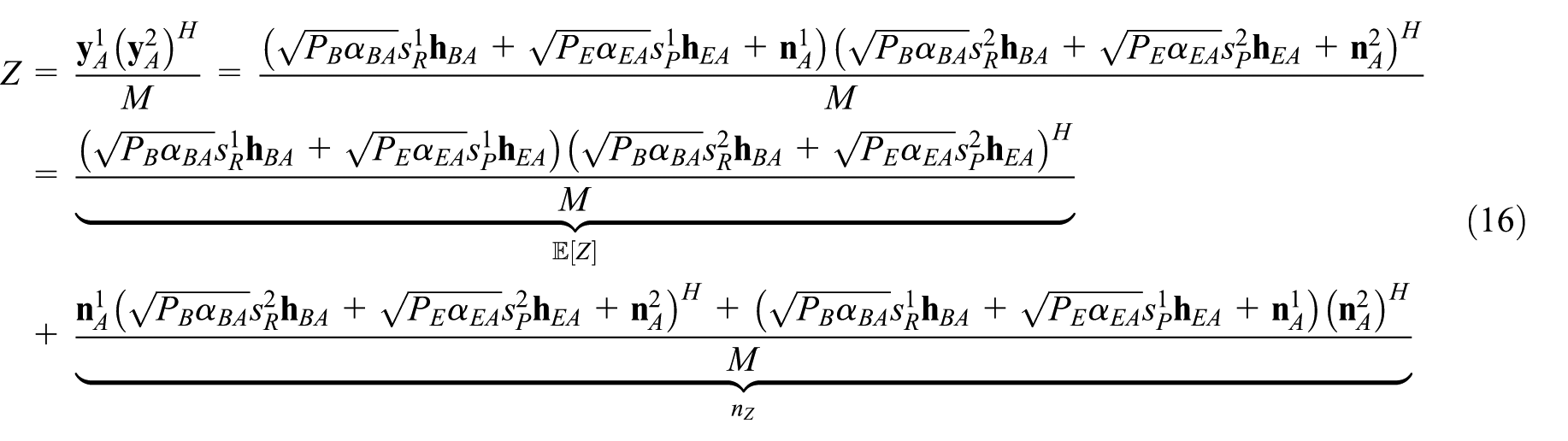
Recalling channel reciprocity and equation (8), we can simplify this statistic as equation (17)

Meanwhile, according to the central limit theorem, we can get that
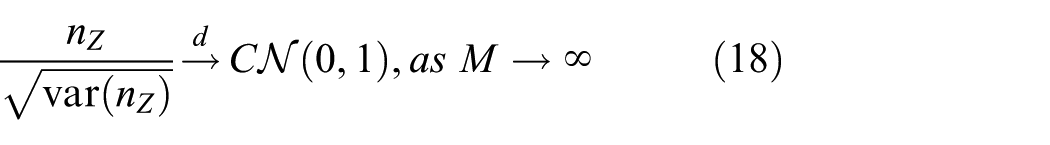
where the variance
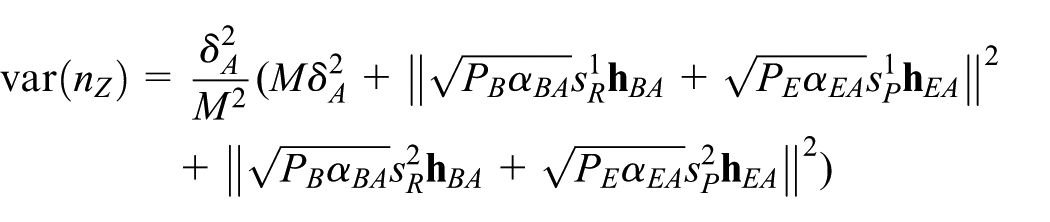
Furthermore, we can easily get that

When

From equations (16), (18), and (21), we know that the variance of
Now we set that
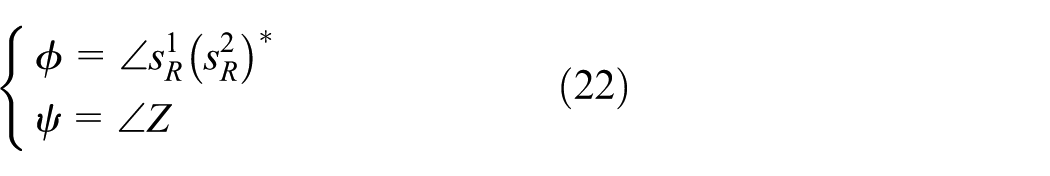
To summarize, the procedure of the detection algorithm is as follows:
Bob send the pilots
Compute the cross product
Compare the phase
According to the phase difference, we can make a judgment. If
From the above analysis, we can realize that


Without loss of generality, we can assume
Detection algorithm depends on whether the scalar product

Illustration of the detection for active pilot attacker.
Under the hypothesis that there is no active eavesdropper in the cell, the product

Moreover, if
The detection probability and false rejection probability can also be analyzed using vector graph, as depicted in Figure 2. If Eve’s effective energy
Based on above description and discussion, we can easily obtain the probability of false rejection, which is given by

As the above analysis, we can easily derive the detection probability, that is,
From these expressions, we can get the following conclusions:
The threshold phase
Only when the antenna number is extremely large, we can ignore the influence of noise and obtain the detection performance. So this detection is naturally suitable for the massive MIMO system.
Eve’s effective power
In addition, if the probability of false rejection cannot exceed a certain proportion

Evidently, the above results provide valuable reference for the pilot signal design of massive MIMO.
SEE analysis
The development of massive number of antennas can significantly enhance the spectral and energy efficiency of the future wireless network.3–7 We provide performance analysis of the secure massive MIMO system in previous section. The results suggest that powers of Alice and Bob are interrelated under a total power limit, and both of them have a major influence on the secrecy performance. So an optimal power allocation scheme is preferred. In this section, the SEE is considered, which is defined as sum secrecy rate divided by transmit power.
As a matter of fact, we derive the spectral efficiency capacity (bits/s/Hz) in section “System model,” as we have not considered the width of the system. Without loss of generality, we can replace the secrecy rate with the spectral efficiency capacity to calculate the SEE (bits/J/Hz).
In the first place, total power consumption of the system should be investigated prior to analysis. According to some existing related literatures,30,32 we can model the total energy consumption as a sum of some components, which can be given by

where
The SEE can be expressed as

Recalling equations (12), (28), and (29), both powers of Alice and Bob have a great impact on SEE. In this article, we only focus on maximizing SEE in the scenario where the total power is constrained, which can be formulated as

where
According to some previous related works,30,32 problem
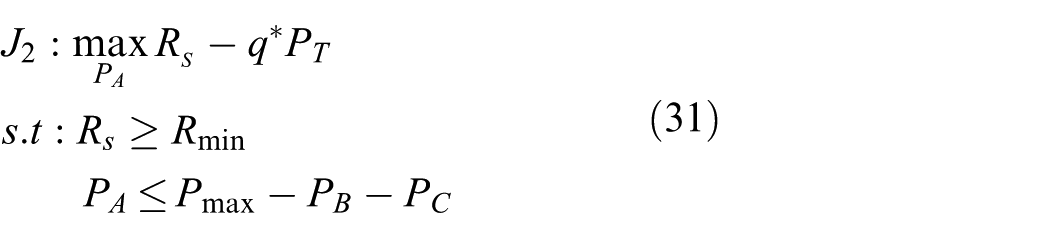
This optimization problem
Proof
Intuitively, since

We define a new function

Since these parameters satisfy that
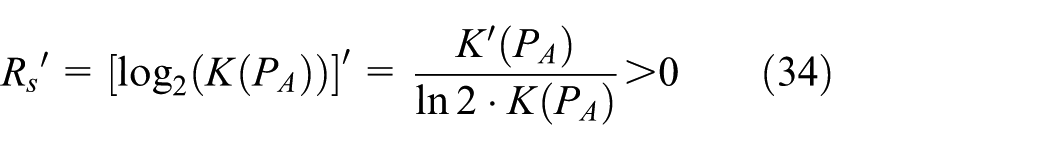

Thus,
As proved before, the objective function is concave with the feasible set of
Similar to previous works, 32 we can use the Lagrange multipliers algorithm to resolve this problem. The objective function can be replaced with

where the Lagrange multipliers
Meanwhile, the dual optimization problem is represented by

The optimal power

Then, the optimal solution can be denoted by

where parameters are given by
Then, SEE can be obtained by

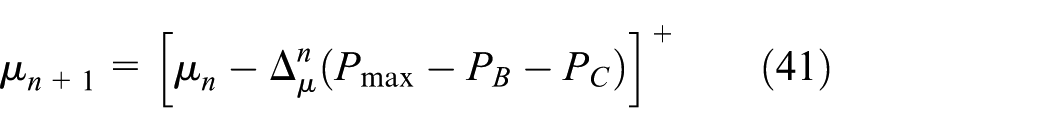
where
We need repeated computing of the optimal solution
Numerical results
To examine and evaluate the accuracy and effectiveness of the results in our massive MIMO secure system, Monte Carlo simulations are operated in this section. In all simulations, we set the noise power is
First, we show the secure capacity of the massive MIMO system with the increasing of the Alice’s antenna number

Achievable secrecy rate against antenna number
To evaluate our new active pilot attack detection algorithm, we simulate the detection probability, the false alarm probability, and false rejection probability. A high probability of false alarm bring pointless communication pause event. Additional false rejection will impair the communication quality severely. As we know, parameter

Detection probability and false rejection probability versus parameter

Detection probability versus the parameter

Correct decision probability and false alarm probability versus antennas number
Finally, some simulation results are presented to verify effectiveness of the energy-efficient power allocation scheme. Parameters are set to

Illustration of the energy efficiency optimization iterative process and the energy efficiency curve versus Alice’s power
Conclusion
In this article, we investigate the secure downlink transmission in massive MIMO system. For the considered system model, we provide the secrecy capacity analysis in closed form. From the analysis results, we know that massive MIMO is robust against passive eavesdroppers, but will be damaged by active pilot attack. Detection of the active attack is important for secure communication. A new detection scheme is presented. The legitimate receiver sends uplink pilots with random phases, then the detection can be operated comparing phase deviation change of the received pilot signals cross product. To maximize the SEE, an optimization scheme of power allocation is presented in detail. Simulation results validate the secrecy performance, effect of the detection scheme, and SEE of this massive MIMO system.
Footnotes
Acknowledgements
The authors would like to thank all anonymous reviewers for valuable and helpful comments and suggestions, which largely improve and clarify this paper.
Handling Editor: Miguel A Zamora
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Jiangsu Provincial Natural Science Foundation of China (No. BK20141069).
