Abstract
In this article, the secure communication in cell-free massive multiple-input multiple-output system with low-resolution analog-to-digital converters is investigated in the presence of an active eavesdropper. Specifically, in this article, the deterioration caused by the analog-to-digital converter imperfections on the accuracy of the channel estimation and secure transmission performance is studied. Besides, the additive quantization noise model is utilized to analyze the impacts of the low-resolution analog-to-digital converters. The minimum mean square error channel estimation results show that there is a nonzero floor caused by the coarse analog-to-digital converters. Then, the closed-form expressions for both the legitimate users achievable ergodic rate and the information leakage to the eavesdropper are derived, respectively. Moreover, tight approximated ergodic secrecy rate expression is also presented with respect to analog-to-digital converters quantization bits, number of antennas, pilot power, and so on. To degrade the impacts of the pilot spoofing attack, an active attack detection approach based on random matrix theory is proposed which can only be operated at one access point. Simulation results are provided to corroborate the obtained results and analyze the impacts of various parameters on system secrecy performance. Also, the superiority of the proposed active attacks detection method is confirmed via simulation results.
Keywords
Introduction
Massive multiple-input multiple-output (MIMO) is regarded as a promising wireless access technology for 5G and B5G wireless communication which can provide high spectral efficiency and high energy efficiency with simple signal processing.1,2 Cellular massive MIMO equips the large number of the antennas on a single base station (BS) which has been analyzed widely and deeply on various respects, such as performance analysis, beamforming, power control, secure communication, and so on.2–4 However, the performance of such cellular system is inevitably limited by the intercell interferences and channel correlation. One practical alternative is to install several antenna sets onto distributed physical locations which is also called distributed massive MIMO.5,6 As a scalable distributed massive MIMO concept, cell-free massive MIMO has been proved to be a promising wireless network architecture which can provide coherent service by geographically distributed access points (APs) for future wireless communication systems. 7 Since its proposal, various works on performance evaluations and transmission schemes over cell-free massive MIMO have been investigated.8–10 Due to the broadcast nature of wireless channels, facilitating secure and reliable wireless transmission is a critical topic for future wireless communication systems.11–13 Despite the robustness of massive MIMO against passive eavesdropping, the active eavesdropping attacks are more relevant.14,15
Currently, most related literatures merely focused on the secure transmission in co-located massive MIMO systems,16–18 while secrecy provisions for cell-free massive MIMO have not been well explored. Hoang et al. 19 discussed the secrecy performance and power allocation for cell-free massive MIMO with active eavesdropper. The effect of hardware impairments over secure cell-free massive MIMO system with active spoofing attack has been investigated in Zhang et al. 20 However, all aforementioned works are based on adopting high-resolution analog-to-digital converters (ADCs) in massive MIMO systems. To reduce energy consumption and physical hardware costs, implementing finite-resolution ADCs in massive MIMO systems has been regarded as an effective approach. Several researchers have devoted to the implementation of finite-resolution ADCs in cell-free massive MIMO systems recently.21–23 Besides, the secure co-located massive MIMO with finite-resolution ADCs has been studied in Teeti. 24 Nevertheless, the impact of ADCs quality on secrecy performance in cell-free massive MIMO has not been considered in existing research.
In a time-division duplex (TDD) massive MIMO system, the BS always acquires the channel state information (CSI) of the legitimate users via uplink training based on the reciprocity of the downlink and uplink channels. All legal users are required to send the redesigned and assigned pilot (training) signals to the BS in uplink training phase. Since all pilot signals are repeatedly used and publicly known by the BS and all users, a smart malicious eavesdropper can easily learn the target user’s pilot signals and transmit an identical pilot signal as that of a legitimate target user which is also called spoofing attack. 25 Due to the spoofing attack operated by the active eavesdropper, the adversary could manipulate the CSI estimation which is the weighted sum of the target legitimate user and the eavesdropper’s channels. Consequently, the beamforming based on the estimated CSI during the data transmission results in information leakage to the eavesdropper. Some existing literatures show that the massive MIMO is robust against passive eavesdropping while the secrecy performance of the massive MIMO system is dramatically degraded by active attacks.14,15,26 Thus, detection of the active eavesdropper can be considered as an effective countermeasure to weaken the influence of active spoofing attacks. Kapetanović et al. 27 proposed a detection scheme via random training pilots for massive MIMO system. However, some special pilot sequences are required to do the detection in this proposed method. Then, different schemes for active attack detection have been presented in Kapetanović et al. 28 which are operated at different locations and based on different system parameters. It is noted that the precoder normalization is crucially important for these active eavesdropper detection schemes. Moreover, a simple detection protocol based on the statistical properties of the channel estimation has been provided in Al-Nahari, 15 which is also determined by the correctness of the channel estimation. Besides, the minimum description length (MDL) source enumeration algorithm has been utilized for active eavesdropper detection in Tugnait,29,30 which can greatly improve the detection performance using short pilot sequences. According to Kritchman and Nadler 31 and Tugnait, 32 the random matrix theory (RMT) detection approach can achieve more precise results compared with MDL algorithm and has been proved to be highly effective in traditional MIMO system.
Motivated by the aforementioned observations, this article presents the first study of the security problem in cell-free massive MIMO system with finite-resolution ADCs against active eavesdropper. Furthermore, the tight asymptotic lower bound of achievable secrecy rate has been provided to enable the effects of ADC resolution, number of APs, each AP’s antenna number, and so on. Also, an active eavesdropping detection algorithm based on RMT is presented. And the proposed detection algorithm can be operated at one AP which only needs a simple procedure. The specific contributions of this article can be summarized as follows:
To capture the aggregate impacts of low-resolution ADCs, the additive quantization noise model (AQNM) is utilized to analyze the performance of the secure cell-free massive MIMO system. Specifically, this article operates the channel estimation via uplink training under minimum mean square error (MMSE) criterion. Moreover, the results show that the low-quality ADCs lead to a nonzero floor on the channel estimation. Also, more pilot power of the eavesdropper would bring larger damnification for channel estimation.
The downlink secrecy communication has been considered with the low-resolution ADCs. Based on the AQNM and the imperfect CSI, the closed-form expression of the secrecy rate has been derived with respect to key system parameters, including the quantization bits of the ADCs, the number of the total antennas, the pilot and data transmission power, and so on. These novel results can provide a effective tool to quantitatively analyze the impacts of system parameters on system secrecy performance.
To weaken the impacts taken by the active eavesdropping, an active attacks detection scheme based on the pilot self-contamination has been proposed which can only be operated at one AP. The detection is employed via determining the signal subspace rank which is estimated by RMT source enumeration approach. Also, the proposed detection approach has been illustrated accurate and effective via simulations.
The outline of the article is organized as follows. Section “System model” introduces the considered secure cell-free massive MIMO system model. Section “Uplink training” details the procedure of the uplink MMSE channel estimation. Section “Secrecy performance analysis” derives the achievable secrecy rate of the considered system. The RMT-based active eavesdropping detection is discussed in section “RMT-based pilot spoofing attack detection.” Simulation results are presented in section “Numerical results.” Finally, the article is concluded in section “Conclusion.”
Notation
Throughout this article, boldface lower case and upper case letters are utilized to represent vectors and matrices, for example,
System model
As illustrated in Figure 1, the cell-free massive MIMO system comprising
where

The architecture of the considered secure cell-free massive MIMO transmission system.
Since secure downlink transmission is investigated in this article, each time slot consists of uplink training and downlink transmission phases.
Uplink training
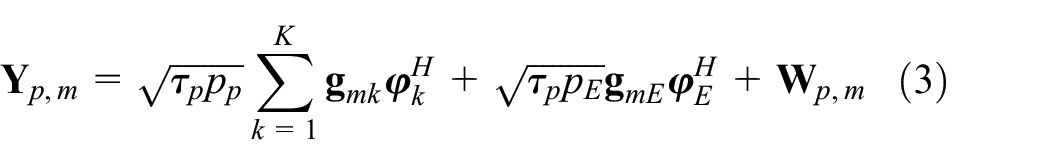
Due to the channel reciprocity, the CSI can be only acquired by uplink training. During this phase, all legitimate users send mutually orthogonal pilot sequences of length
where
where
Corresponding scaling factors for different ADC quantization bits.

Also,

Then, projecting

where
By utilizing the MMSE estimation, the estimated channels can be written by16,21


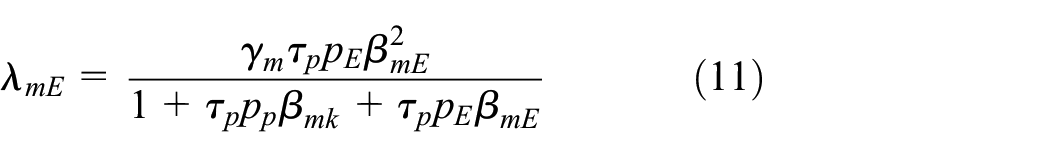
where the estimate
Moreover, the channel estimation

Then, one important theorem can be given as follows.
Theorem 1
The variances

Proof
Please see Appendix 1.
Since the downlink beamformer is based on the estimated CSI via uplink training, the accuracy of the channel estimation is crucially important. Then, the normalized minimum square error (NMSE) of the target user can be used to evaluate the estimation performance which is defined as

To achieve some valuable insights, one limit behavior of the NMSE can be considered as follows. As

Thus, there is a nonzero floor on the channel estimation error NMSE caused by the ADCs imperfection. Besides, this zero floor cannot be compensated by increasing the pilot power of the legitimate users.
Secrecy performance analysis
In this section, we will focus on the performance analysis as a measure to evaluate the performance of the considered secure communication system.33–37 All APs perform conjugate beamforming to simultaneously transmit data to all users with the same time-frequency resource. Then, the signal transmitted by the

where

Then, the received signal at the


where

where

We consider the realistic case that the target user cannot obtain its instantaneous CSI. Hence, the

where


In this article, the ergodic secrecy rate is chosen to evaluate the secrecy performance of the considered system. By considering the difference of the channel capacities between the target user and the Eve, the ergodic secrecy rate is given by

where


Subsequently, the closed-form expressions of
Theorem 2
In the considered cell-free massive MIMO system, the SINRs at the
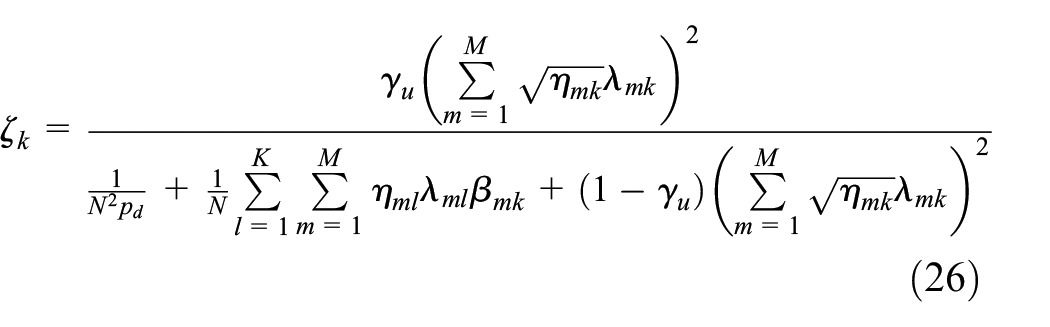

Proof
Please refer to Appendix 2.
RMT-based pilot spoofing attack detection
According to some existing papers, it is reasonable to operate the pilot spoofing attack detection based on the uplink training. Our proposed detection scheme is to perform source enumeration using RMT algorithm which is based on both the distribution of the signal eigenvalues and noise eigenvalues with the presence of noise. Also, to improve the detection accuracy, the uplink training can be divided into two phases: uplink training and uplink active attack detection. In the detection, it is set that only the legitimate target user send the pilot signal which can be designed that a fraction

To keep the detection processing confidential, the random sequence

where
Obviously, the received signals under these two hypotheses can be modeled as Gaussian variable with different expectation. According to the existing literature,29–32 the deterministic signals can be used for source enumeration to detect the existing active attacks.
Then, we can define that the correlation matrix of the received signal as

Furthermore, the correlation matrix of the source signals is given by

As such, the matrix

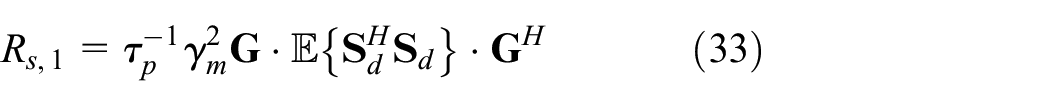
where the matrices

It is noted that
Moreover, we can derive that

where

Thus, the two hypotheses can be distinguished by estimating the dimension

The RMT approach considers distribution of the noise eigenvalues of

The eigenvalues of

where


Then, we should consider the behavior of correlation matrix adding the signals. In this case, the eigenvalue of matrix

where

The above RMT approach can be used for signal subspace rank estimation based on the fact whether
Numerical results
In the simulations, all APs, users, and the Eve are randomly located over a circle cell of radius 300 m. A simplified path-loss model has been used as
Figure 2 depicts the NMSE of the channel estimation versus the SNR of the legitimate user pilot signal as a function of the quantization bits and Eve’s pilot power. It is noted that NMSE is monotonically increasing for decreasing the quantization bits
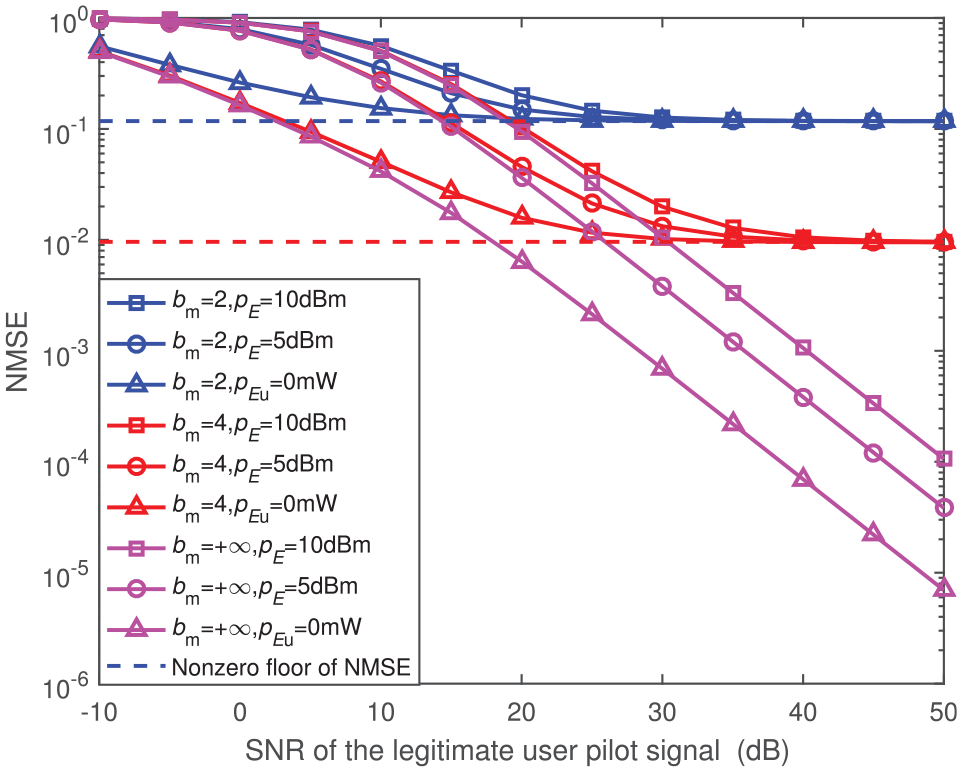
The NMSE versus the pilot power of the legitimate users.
Since the derived secrecy rate expression in Theorem 1 is an appropriate tool for secrecy performance measure, the tightness of expression (23) should be verified via numerical results. Figure 3 shows the analytical and numerical results versus the number of the APs

Analytical and simulated results of the achievable secrecy rate versus the number of the APs.
Figure 4 shows the achievable ergodic secrecy rate versus different ADC quantization bits with

The achievable secrecy rates versus ADC quantization bits.
Figure 5 depicts the achievable secrecy rate as a function of the pilot power ratio between the Eve and the legitimate user, where

The achievable secrecy rates versus pilot power difference.
In Figure 6, the active attacks detection probability versus the pilot power of the Eve with various parameters are depicted when

Probability of the active attack detection versus the pilot power of the Eve.
Figure 7 shows the detection probability of the proposed RMT-based approach versus the power allocation factor

Probability of the active attack detection versus the pilot power allocation ratio
Conclusion
This article adopted the well-established distortion model (AQNM) to reveal the secure performance of cell-free massive MIMO system with low-resolution ADCs. Uplink MMSE channel estimation has been operated in the presence of active eavesdropping attack which shows that there was a nonzero floor on the channel estimation error brought by the ADC impairments. Based on the imperfect CSI, conjugate beamforming has been performed for downlink transmission. Then, we derived the closed-form expression of the achievable ergodic secrecy rate. To weaken the influence of the active attacks, any effective resisting measure was to detect the presence of the active eavesdropper. This article exploited the RMT-based detection approach to detect the dimension of the signals embedded in noise space. Finally, numerical results have been presented to verify derived results and the effectiveness of the active attack detection scheme.
Footnotes
Appendix 1
Appendix 2
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by China Postdoctoral Science Foundation under Grant 2021MD703980, in part by the National Natural Science Foundation of China under Grant 61901502.