Abstract
This article investigates the influence of multiple-antenna deployment at access points on physical layer security under cell-free massive multiple-input multiple-output systems. To embody the concept of network multiple-input multiple-output, cell-free massive multiple-input multiple-output employs a great deal of geographically distributed access points, which jointly serve multiple users in the same frequency-time resource. Assuming a malicious active eavesdropper having knowledge of instantaneous channel state information, we derive the asymptotic closed-form expression of the achievable secrecy rate, which is used to evaluate network security performance. A distributed power allocation scheme is developed based on channel fading degrees of different users. All of access points distribute a larger proportion of local transmission power to the users with better channel conditions. We verified that the security performance of the multi-antenna access points outperforms that of the single one. Compared to equal power allocation, the proposed power control algorithm can further boost the network security performance.
Keywords
Introduction
Telatar, 1 Foschini and Gans, 2 Bell Laboratory, in their pioneering paper proposed the concept of multiple-input multiple-output (MIMO) system, which can provide spatial multiplexing and diversity gained by using multiple antennas on transmitter and receiver. Thus, MIMO systems can significantly increase spectral efficiency throughout without additional frequency, power, and time resources. As a scalable multiuser MIMO implementation, massive MIMO technology has been derived by Marzetta.3,4 Each base station (BS) is equipped with a large array of antenna elements. Massive MIMO has become one of the key technologies for 5G networks with a great capability of enhancing the spectrum and energy efficiency as well as reducing transmission power and inter-cell interference of the network through the deep mining of dimensional resources in a wireless communication environment. 5 According to the deployment of antenna arrays on BS, massive MIMO systems can fall into collocated MIMO systems and distributed ones. 6 The former is built with a compact large-scale antenna array in the BS, which has advantages of low data sharing cost and fronthaul requirements. The antenna of the latter is distributed over a wide area, which can provide uniformly good services for all authorized users as well as higher diversity against the shadow fading. 7 Multicell distributed MIMO is a generalized concept, including network MIMO, 8 coordinated multiple point (CoMP), 9 and distributed antenna systems (DASs). 10 In 2015, Nayebi et al. 11 first proposed the network architecture of cell-free massive MIMO, which has received widespread attention. The different structure of massive MIMO systems is illustrated in Figure 1. Chien et al. 12 investigated how to use power allocation to save load resources. To reduce the overhead for channel estimation, an aggregated channel estimation approach was introduced by Chien et al. 13 These studies have explored more performance advantages for cell-free massive MIMO.

Illustration of the network architecture of collocated and distributed massive MIMO.
With the dramatic array gain, massive MIMO has great potential in physical layer security (PLS). Also, this topic has been developed in recent years. 14 Due to the stronger directivity of the signal beam, the massive MIMO system has natural robustness to passive eavesdropping. 15 To obtain more favorable information, smart eavesdroppers usually take action not only by overhearing but also by jamming. Time-division duplexing (TDD) mode has the advantage of making forward and reverse channels under massive MIMO systems reciprocal. 16 It allows that only the uplink is used for channel estimation to acquire channel state information (CSI), dispensing with downlink estimation. At the same time, it provides a huge opportunity for active eavesdroppers to send spoofing pilot sequences, also called pilot spoofing attacks. The damage is to decrease the accuracy of channel estimation, and bring correlated precoding vectors between eavesdroppers and legitimate users, 17 resulting in severe leaking of information. To mitigate the impact of active eavesdropping in massive MIMO systems, power control methods are commonly applied, such as trying to ensure the minimum transmit power required for reliable and secure communication, 18 minimizing the signal-to-interference and -noise ratio (SINR) of eavesdroppers, 19 and using game theory to maximize the SINR of legitimate users. 20
The security aspect of the cell-free massive MIMO network under pilot spoofing attacks was first explored by Hoang et al., 21 which proposed a simple detection mechanism and designed power control schemes with the aim of security rate maximization and power consumption minimization. To continue handling the crisis of the active eavesdropper, Zhang et al. 22 analyzed the security performance for the multigroup multicasting scenario. Besides, a comparison about the lower bound on security capacity between the collocated and cell-free massive MIMO has been presented by Timilsina et al. 23 The achievable rate on legitimate users and the rate leaked to active eavesdroppers have been driven within the range of limited and unlimited numbers of APs. Research on security performance was expanded by introducing novel technologies.24,25 Alageli et al. 24 have delved into the problem of secure communication assuming that there is an untrusted dual-antenna energy harvester in the network. One antenna is used to harvest energy, whereas the other one intercepts information signals as an active eavesdropper. Elhoushy et al. 25 have enhanced the robustness of network security against pilot spoofing attacks by applying reconfigurable intelligent surface, which reconfigures the wireless propagation channels through software-controlled reflections. Based on more realistic consideration of low-resolution analog-to-digital converters, secure communication with active eavesdroppers has been studied by Zhang et al. 26 However, the abovementioned research on PLS is all limited to single-antenna APs.
To the best of the authors knowledge, there are no fruitful results with the cell-free massive MIMO system model established in multi-antenna APs. However, it is easier to realize channel hardening when each AP is deployed with 5–10 antennas. 27 By channel hardening, fading multi-antenna channels can behave almost as deterministic scalar channels. This basic property simplifies the resource allocation 28 and assists to deliver higher performance 29 in the cellular massive MIMO system. Ngo et al. 7 proved that the cell-free massive MIMO can also utilize channel hardening, but Chen and Bjoernson 30 have proved that channel hardening is not always available to adopt in the cell-free massive MIMO network. So the studies on cell-free massive MIMO should deploy multi-antenna APs in the pursuit of relying on channel hardening. Vu et al. 31 proposed a novel full-duplex mode, wherein the plurality of multi-antenna APs provided uplink and downlink services for multiple single-antenna users in the same frequency band. Considering imperfect CSI, non-orthogonal pilots, and power control, the spectral efficiency with respect to numbers of APs antennas and the users in cell-free massive MIMO system has been investigated by Mai et al. 32
Motivated by the aforementioned discussion, we explore the PLS of cell-free massive MIMO systems with multi-antenna APs in the presence of an active eavesdropper. First of all, the closed-form expressions of downlink achievable rates at the legitimate users and the rate leaked to the wiretapper are derived. Second, we propose a distributed power control scheme that allocates power factors by estimated channel quality. This simple and feasible scheme puts power control operations locally. Moreover, the effect of the number of the antennas per AP is analyzed by the achievable secrecy rate. Simulation results show that the security improved by the multi-antenna APs consistently outperforms that of the single one in terms of achievable security rate. And dense nodes of APs cooperative with the aforesaid power allocation scheme can provide a respectable security performance.
The remainder of this article is organized as follows. In the section “Channel and System Model,” the system model including uplink channel estimation and downlink information transmission phase are presented. In section “Security Performance Analysis,” we carry out a set of general mathematical closed formulas for security performance analysis. In addition, we optimize the total downlink transmission power here. This is followed by the section “Numerical Results and Discussion,” where numerical results and discussion are presented. Finally, we provide our conclusion in the section “Conclusions.”
Channel and system model
Channel model
We consider a cell-free massive MIMO system with

where
In addition, we discuss the Rayleigh fading channel, that is,
System model
The system model of the cell-free massive MIMO network is shown in Figure 2. We assume that the system is operated in TDD mode. The length of a TDD coherent interval is

System model of the cell-free massive MIMO network.
In detail, the system design

where
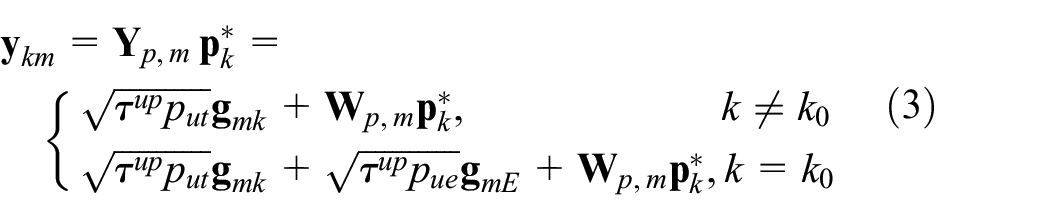
The MMSE estimation of


where

To facilitate later calculations, let us define

and
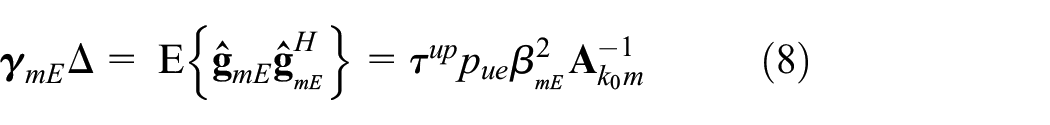
We can see that

where

where
As such, Eve will receive the information signal as

where
Security performance analysis
In this section, we analyze the security performance by achievable security rate. The security rate can be defined as the difference between the information rate of legitimate users and Eve. Also, the achievable rate of legitimate users and the information leakage rate into Eve are deduced.
Achievable rate of legitimate users
On the basis of information theory, the achievable rate of the user can be given as

where

As the
Lemma 1
Let
Theorem 1
When an active eavesdropper conducts a pilot spoofing attack, and all APs are configured with multi-antenna and conjugate beamforming technology, the closed-form expression of the

Information rate leaked into Eve
In this article, we focus on the worst-case scenario in terms of network security. The Eve has knowledge of instantaneous channel gain to get a genie-aided rate. Based on Jensen’s inequality,

Theorem 2
The closed-form expression of the active eavesdropper’s SINR when every AP has multi-antenna and adopts conjugate beamforming is

Achievable secrecy rate
The above analysis lays the foundation for the derivation of the lower-bound secrecy rate at the

where the notation is
Power allocation scheme
In this subsection, we present a distributed power allocation (DPA) scheme, which is simple to implement for cell-free massive MIMO. Most power control algorithms take a certain utility metric as the optimization goal, depending on the powerful computing capability of the CPU, huge backhaul capacity, and perfect calibration of the hardware chains. Backhaul overhead is defined as the execution cost of computation task among cooperating APs.
35
Because distributed antenna networks increase in size and density, it is urgent to reduce backhaul overhead.
36
When the backhaul load is heavily limited, it is an alternative approach to conduct power control to APs locally. Assuming that the network does not detect the presence of active eavesdropping, each AP divides their power by the channel strength of different users. In this scenario, the influence of the unauthorized access of the active eavesdropper on the network can be more intuitive, credible, and persuasive. In our power allocation schemes, channel strength is measured on the basis of

where
Dealing with power control, it is traditional to adopt equal power allocation (EPA) scheme in collocated massive MIMO systems. Because the distance is so close among antennas in the BS, all are regarded to be set up in the same place. The channel quality between each antenna and users is in equilibrium. While CPU supports distributed scenarios in cell-free massive MIMO systems, APs have widely divergent locations. If a certain AP is relatively far from some users, or has serious interferences, it will be sensible to make these power control factors smaller. In consideration of the above, DPA is more appropriate in the light of the distribution network traits. It is also easy to implement after CSI estimated by each AP.
Numerical results and discussions
In this section, we present the numerical results of the security performance under the multi-antenna cell-free massive MIMO network in the presence of an active eavesdropper. Unless noted additionally, system parameters are set as shown in Table 1.
Setting of simulation parameters.
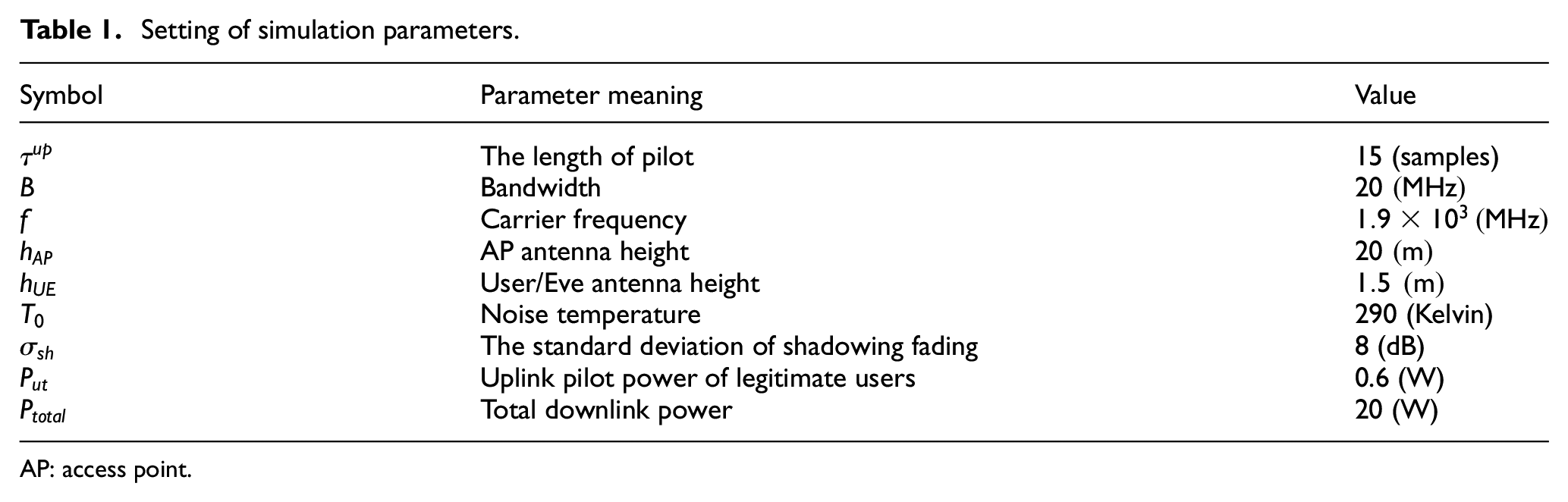
AP: access point.
Besides, the amount of APs, users, and Eve nodes are uniformly distributed over the area of


where

where
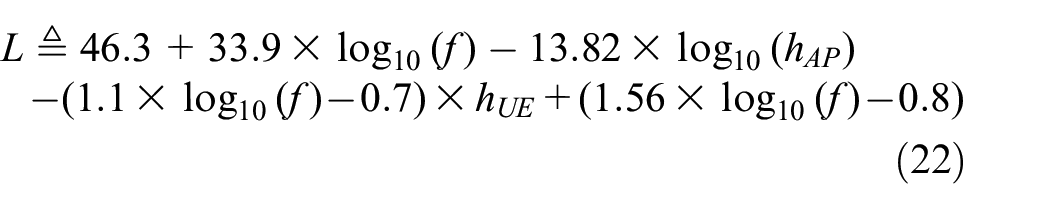
and where
Moreover, the noise power can be given by
where
Figure 3 shows the cumulative distribution function (CDF) of the achievable secrecy rate by the
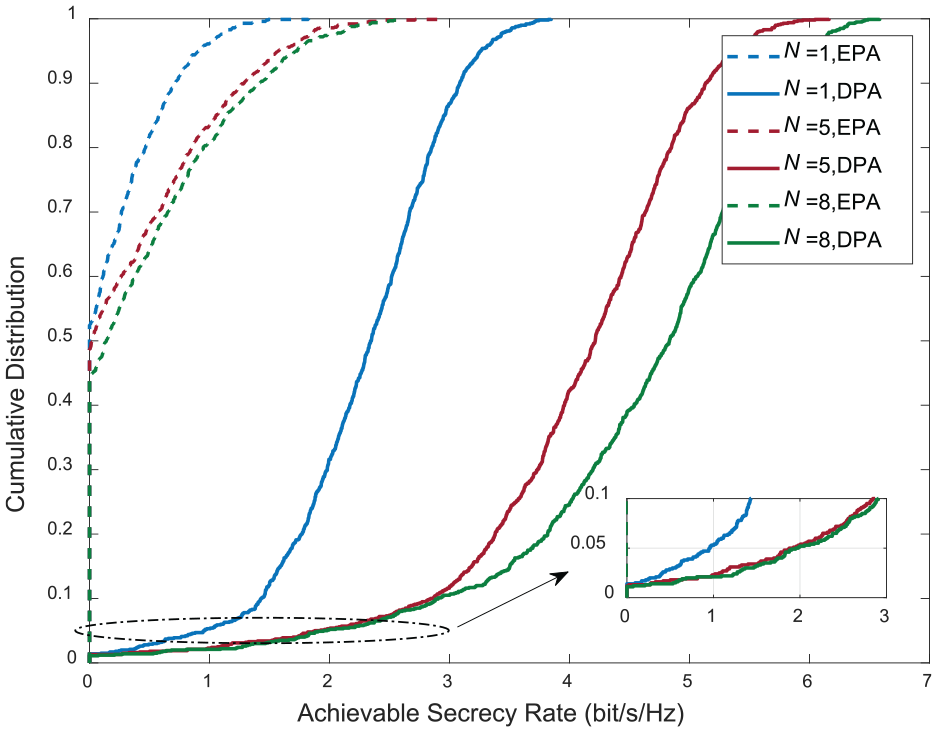
Cumulative distribution of achievable secrecy rate with
As shown in Figure 4, we explore the intuitive influence on multi-antenna APs. As the amount of antennas by APs increases from 1 to 10, the achievable secrecy rate increases proportionally. With EPA, the number of antennas by APs and the number of legitimate users within the supported range, that is,

Achievable secrecy rate versus the number of antennas per AP with
In Figure 5, the achievable secrecy rate is plotted as a function of spoofing pilot power by Eve. If Eve cannot transmit training pilots, that is,

Achievable secrecy rate versus spoofing pilot power of Eve with
Specifically, the achievable secrecy rate with single-antenna AP ranges from 1.769 bit/s/Hz with
The achievable secrecy rate is depicted as a function of

Achievable secrecy rate versus the number of APs with
Conclusion
In this article, we have studied a cell-free massive MIMO network in the presence of an active eavesdropper, which is a smart attacker imitating the legitimate users’ training pilots and sending the same one to all APs. Combined with previous research, it has proven the channel hardening that exists when multiple antennas are configured at APs. Therefore, it is imperative to consider the scenario of multi-antenna APs under cell-free massive MIMO networks, which is also the first time to focus on the security with arbitrary finite number of antennas deployed by APs. Taking MMSE estimation method and conjugate beamforming technology into accounts, we derive general closed-form expressions of the achievable rate at the legitimate user nodes, the information rate leaked into the eavesdropper, and the achievable secrecy rate. Moreover, a DPA scheme is proposed and contrasts with EPA. This power control algorithm could be used as a prototype for the user-centric network. Taking achievable secrecy rate as the performance security evaluation in simulations, our results reveal that it is superb to employ multi-antenna APs to enhance the security of wireless communication networks. That also corresponds with the application condition of the channel hardening mentioned above.
Footnotes
Appendix 1
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by China Postdoctoral Science Foundation (Grant No. 2021MD703980).
