Abstract
Electronic health record downtimes are any period where the computer systems are unavailable, either for planned or unexpected events. During an unexpected downtime, healthcare workers are rapidly forced to use rarely-practiced, paper-based methods for healthcare delivery. In some instances, patient safety is compromised or data exposed to parties seeking profit. This review provides a foundational perspective of the current state of downtime readiness as organizations prepare to handle downtime events. A search of technical news media related to healthcare informatics and a scoping review of the research literature were conducted. Findings ranged from theoretical exploration of downtime to empirical direct comparison of downtime versus normal operation. Overall, 166 US hospitals experienced a total of 701 days of downtime in 43 events between 2012 and 2018. Almost half (48.8%) of the published downtime events involved some form of cyber-attacks. Downtime contingency planning is still predominantly considered through a top-down organizational focus. We propose that a bottom-up approach, involving the front-line clinical staff responsible for executing the downtime procedure, will be beneficial. Significant new research support for the development of contingency plans will be needed.
Introduction
Motivated by the 2009 Health Information Technology for Economic and Clinical Health or HITECH Act, 96 percent of US hospitals have installed and use an electronic health record (EHR) system.1,2 The rapid and thorough adoption of EHRs has brought a number of benefits to healthcare operations including improved efficiency, clinical decision support (CDS), and patient record portability.3–6
Despite the benefits of EHRs, their widespread adoption has also introduced potential new safety issues.7,8 One such safety issue is a downtime event, which is a period of time when the EHR and associated systems are unavailable. Downtime events occur regularly for planned maintenance and upgrades and can also be triggered by hardware issues, software errors, computer viruses, and deliberate attacks.9–11 Planned downtime events are typically scheduled for low-impact hours on evenings and weekends; clinicians are given advance notice of the downtime and patient care needs are shifted to accommodate the downtime. Unplanned downtime events occur without warning and can be significantly more severe, as the entire EHR and supporting infrastructure can be suddenly taken offline.
While downtime may affect only specific systems and departments, such connectivity issues may not be immediately visible to the rest of the organizational network. One such system that could be impacted is the CDS which generates alerts when clinician orders may induce risk to patients, during certain downtime scenarios CDS may be offline and unable to generate warnings. A clinician may be unaware of a CDS-related downtime and can mistakenly assume a lack of error notification to mean a safe order has been submitted.12,13 In reality, with the CDS and computerized physician order entry (CPOE) systems compromised, a physician could easily prescribe a medication for a patient with a known allergy, yet remain unaware until the patient experiences an adverse reaction.
During a downtime event, clinicians may be unfamiliar with downtime contingency plans and paper-based workflows.7,12 Anecdotal evidence from a large northeastern medical center in the United States suggests that in one downtime event, the loss of pharmacy connectivity and CPOE systems meant that physicians had to complete paper prescription pads. During this particular event, a number of junior physicians, who had never received prior training to use a paper prescription pad before, were on duty. As a result, several prescriptions that were included in patient discharge packets were improperly filled out (personal correspondence, anonymized for confidentiality). There were also reports of nurses devising their own unofficial downtime procedures which resulted in poor clinical decision-making, leading to high-risk, near-miss incidents involving medication overdoses and other misadministration events (personal correspondence, anonymized for confidentiality).
In light of these risks and despite the prevalence of EHR usage in US healthcare, the research literature has not provided a significant treatment for the issue of downtime. We argue that the issue merits investigation, as the results can inform and provide contextual support for administrators designing contingency plans for downtime.
Methods
This article employs two review processes in order to explore how pervasive the downtime issue may be, and how it is currently being studied in US hospitals. The pervasiveness of downtime is identified by a scoping review of relevant technical news media in order to estimate the number and severity of the downtime events publicly acknowledged by US healthcare facilities. The second approach is a scoping literature review of the current state of downtime research, specifically research involving contingency planning for downtime. The research review is focused on determining how downtime contingency plans are currently approached and the scope of relevant studies. Through the two reviews, a holistic depiction of the current state of downtime research will be established, with suggestions for continued research focus.
Scoping review of technical news media
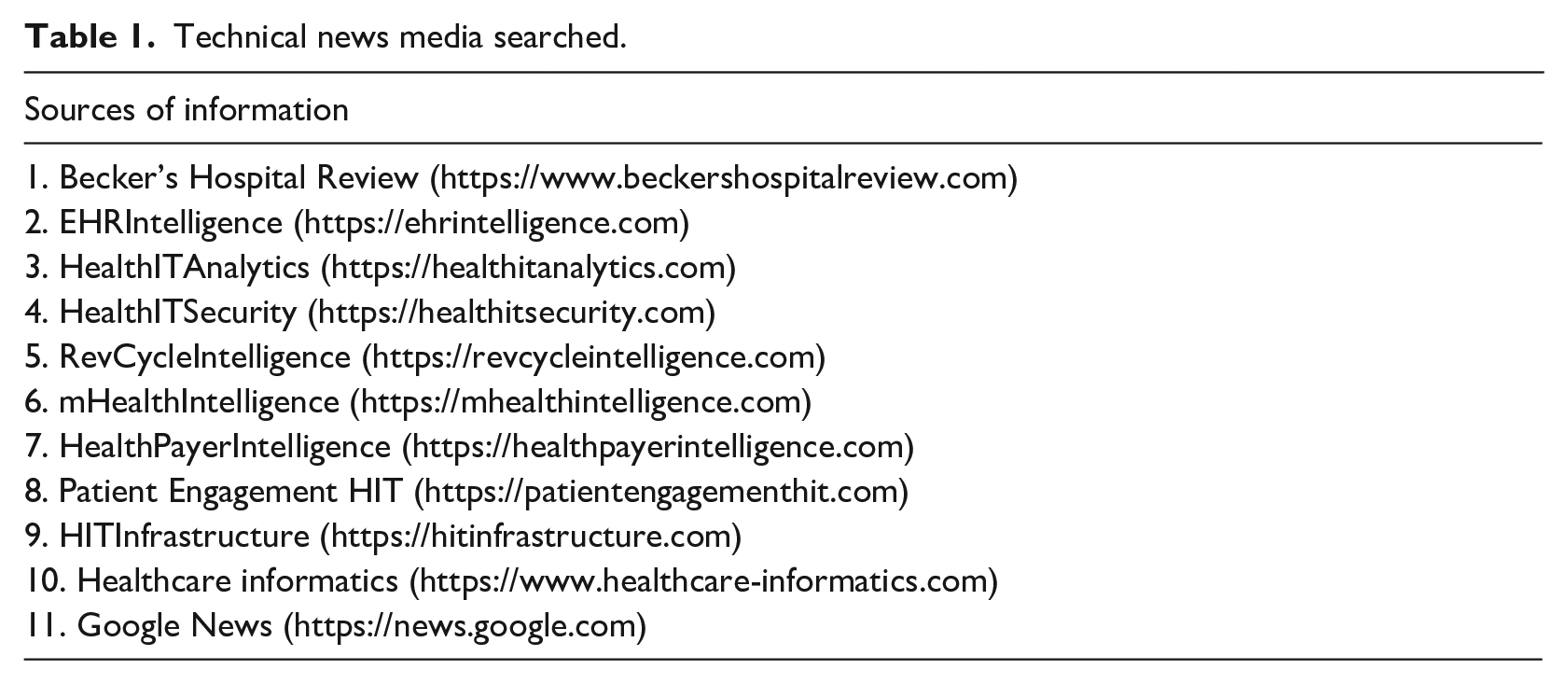
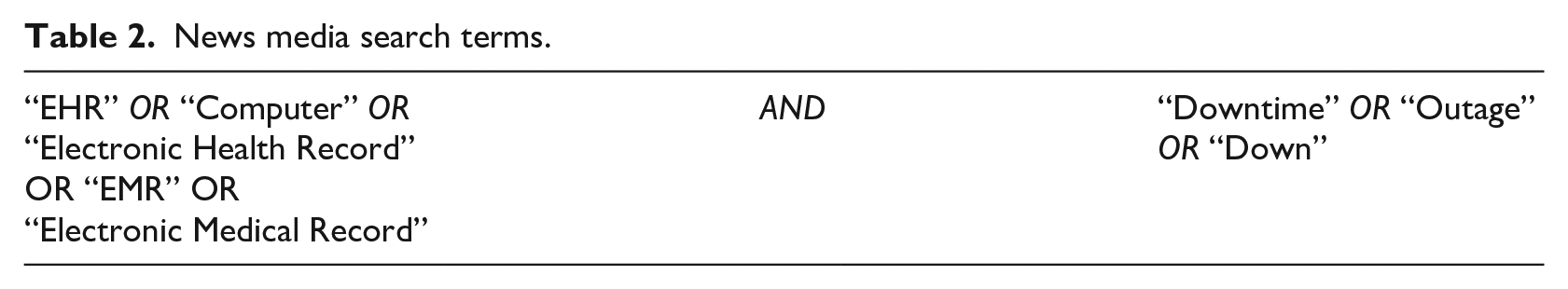
A search of downtime events at US hospitals was conducted within major healthcare informatics media listed in Table 1, as well as Google News. Healthcare informatics in news media platforms are the main source of news on EHRs, and issues with downtime are likely to be reported in such platforms to ensure a broader reach to healthcare informatics professionals, as opposed to the mainstream news media or the academic literature. The news outlets were queried with the terms listed in Table 2. All results were reviewed for relevance and included only if the content of the article contained an indication that the EHR was truly offline. Any downtime events indicated before HITECH’s launch in 2009 were excluded.
Technical news media searched.
News media search terms.
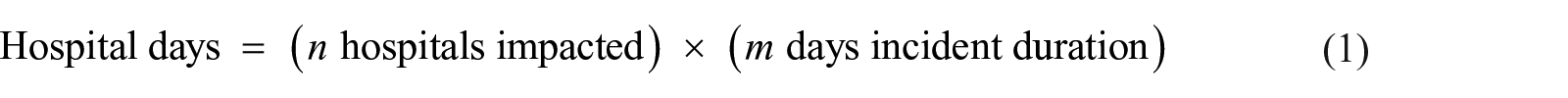
The news stories identified through the search were reviewed for any indications of the downtime origin, duration, and extent. Some downtime events have the ability to impact an entire system of the hospitals simultaneously, so a simple tally of downtime events does not represent the entire situation. To understand the full extent, the duration as the sum total of days a US hospital experienced downtime must be captured. The hospital-day unit is intended to represent the sum of all days all hospitals encountered downtime whether independently or simultaneously. For example, if a five-hospital system experienced a system-wide 2-day downtime, that downtime event would have impacted five hospitals for 2 days, or a hospital-day measure of 10 hospital-days of downtime
Scoping literature review of downtime contingency planning
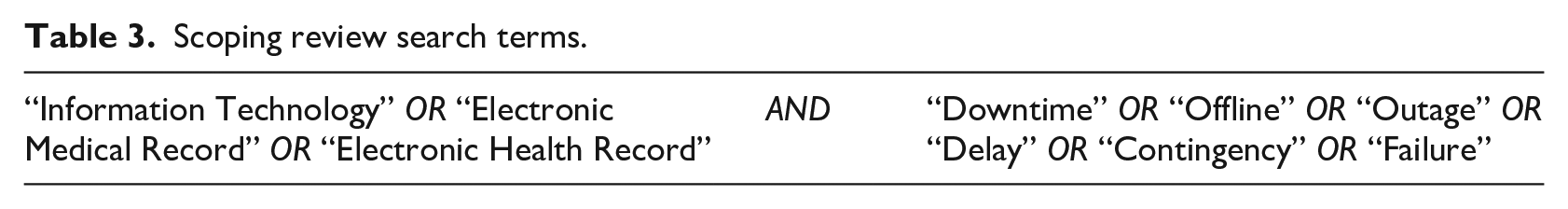
In order to understand the current state and scope of downtime research and hospital readiness for downtime events, as well as current gaps in research, a scoping literature review was conducted. The review was structured using the PRISMA-ScR checklist, an extension of the original PRISMA guidance for systematic reviews designed for scoping review exercises. 14 A pre-planned search strategy was developed to query MEDLINE and CINAHL databases using search terms identified in Table 3. A summary of the data study collection and inclusion process is illustrated in the PRISMA diagram in Figure 1. 15
Scoping review search terms.
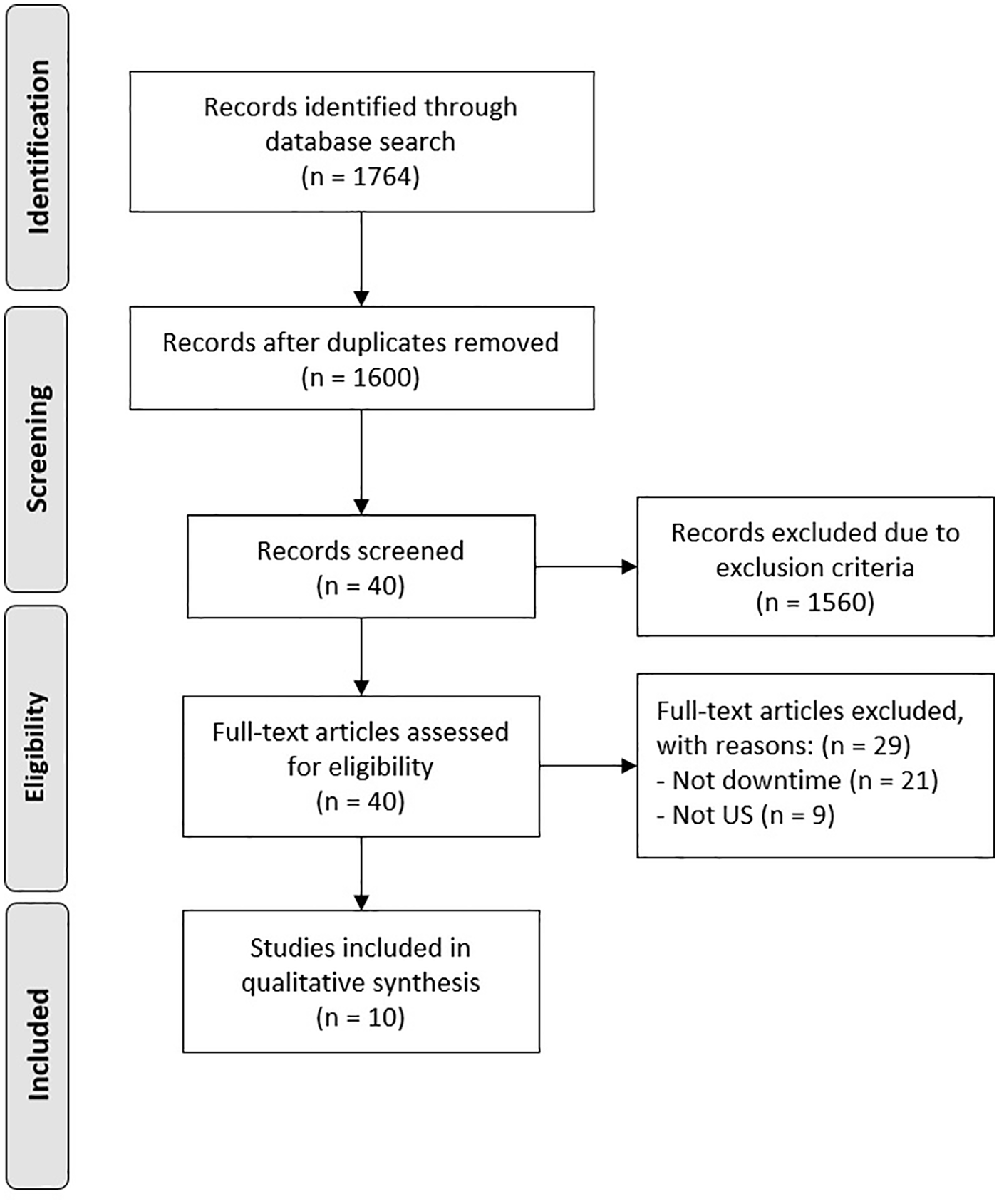
PRISMA-ScR flow diagram.
Study selection
Studies were considered for inclusion if they were (1) published between 2009 and September 2018; (2) written in English; (3) conducted in a US-based facility; and (4) studying aspects of EHR downtime events. Aspects of method, hospital domain, or scope were not restricted. A study was excluded if one or more inclusion criteria were missing. The assembled studies were initially screened by their abstracts for potential inclusion. The search strings returned a significant number of papers related to biomedical studies which were rapidly excluded based on review of the titles and the abstracts. The full text of the remaining 40 articles was screened manually by the lead author for inclusion, domain, and scope. The identified papers were analyzed thematically for focus, subject, methods, and conclusions.
Results and discussion
Scoping review of news media
Since the initiation of HITECH in 2009, there have been 43 reported instances of EHR-related downtime in US hospitals. Based on the available information, the identified events were classified by their origin, outlined in Table 4.
Origins of unplanned EHR downtime events.
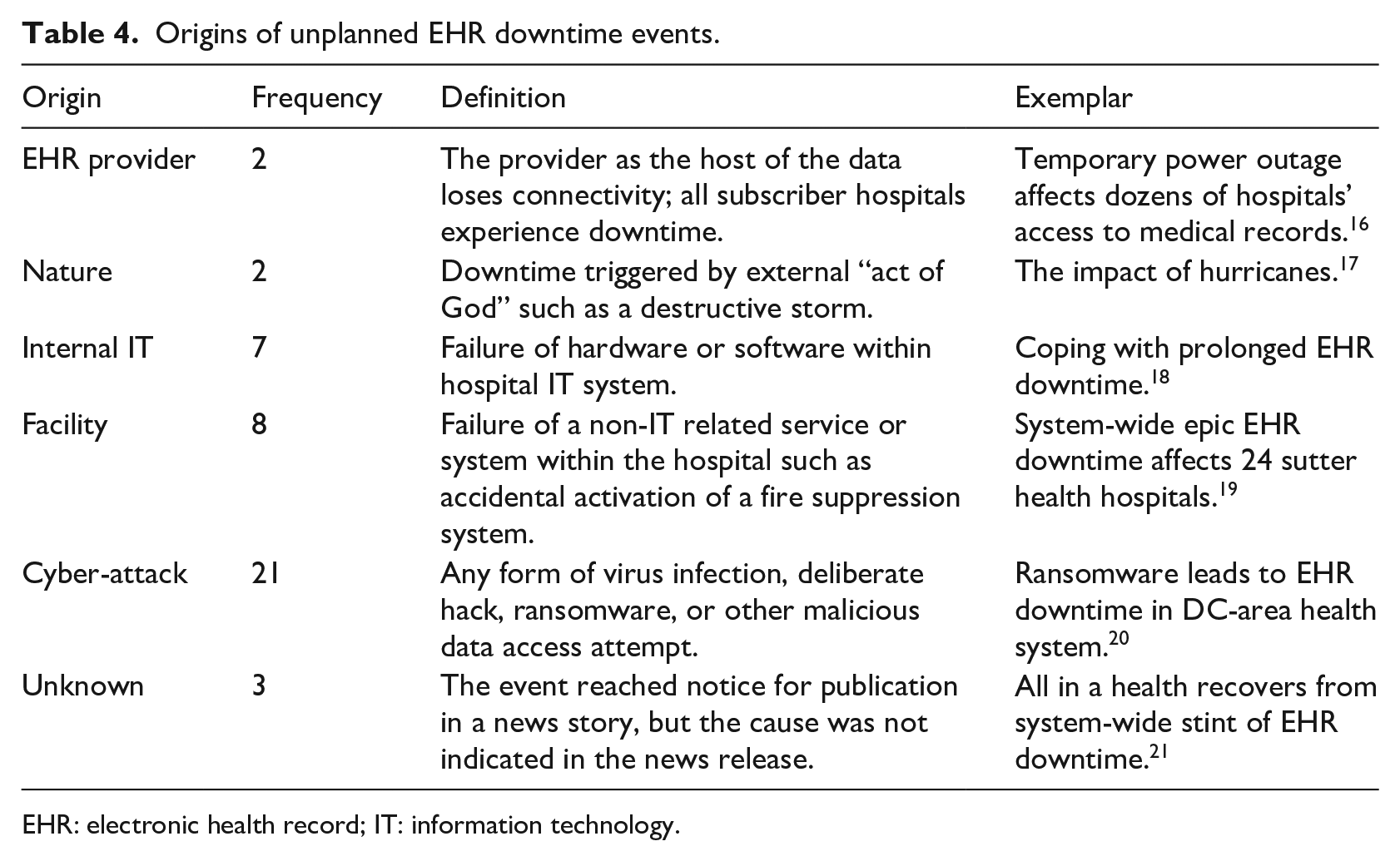
EHR: electronic health record; IT: information technology.
The primary cause for the reported downtimes is cyber-attack compromising the EHR, accounting for 48.8 percent (n = 21) of downtime events (Figure 2). The second most prevalent source was identified as the facility, accounting for 18.6 percent (n = 8) of events, which included failures of non-health IT (HIT) systems such as when the fire suppression system was activated in the server room of the hospital. Provider-driven outages, while accounting for about 4.7 percent (n = 2) of events, are notable due to the data structure typically used in hospitals—the EHR provider is also the data host, so if the EHR provider loses connectivity, all subscriber hospitals also lose connectivity.
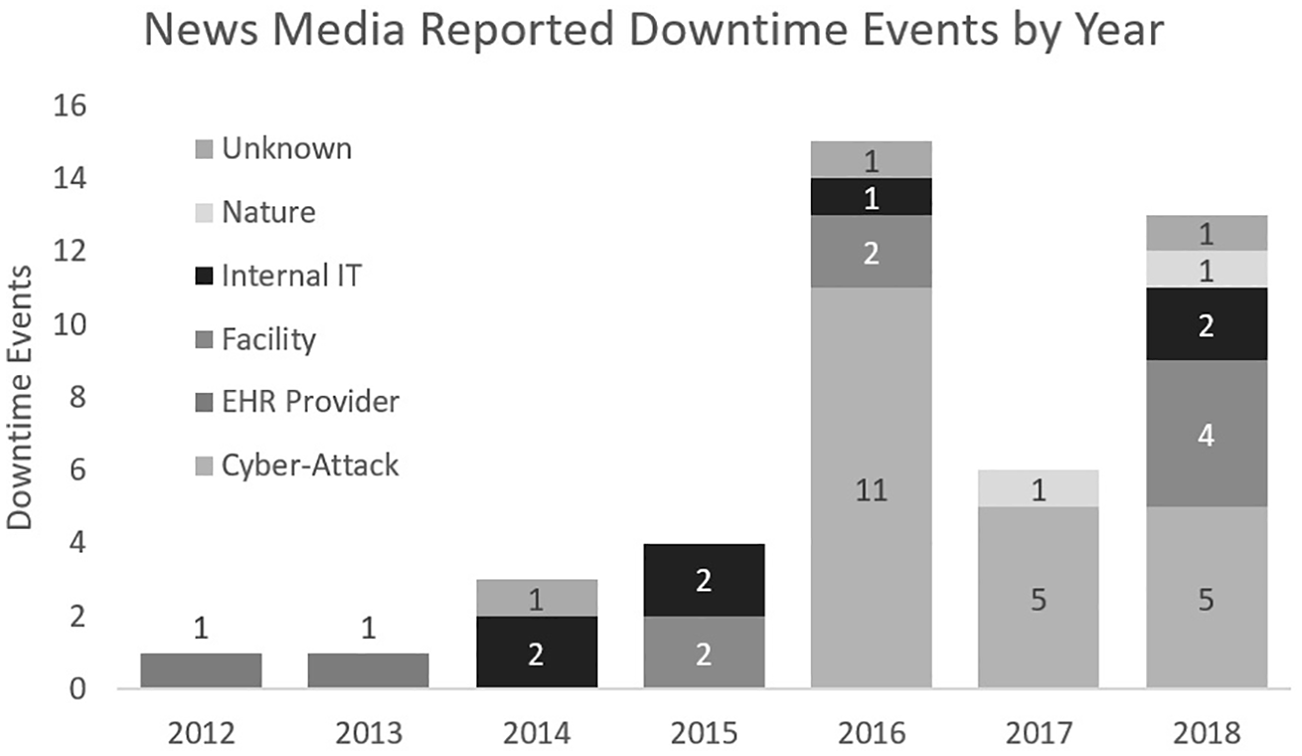
Downtime events in the US news 2012–2018 (categories defined in Table 4).
Although there were no publicly reported downtime events found in the news media before 2012, 43 downtime events impacted 166 US hospitals between 2012 and 2018 (Figure 2) with a total of 701 hospital-days of EHR downtime. Many of the downtime events impacted multiple hospitals at the same time. Though a positive trend in the number of downtime events is apparent, inference of specific trends may be limited since the availability of data may be affected by the lack of events rising to national-level attention, and by reluctance to report publicly due to liability concerns.
These results show that downtime events are a growing issue in healthcare. They originate from sources that are difficult to control and can be highly disruptive. Even the accidental activation of fire suppression systems in a server room would likely entail a process of hardware rescue and data reconstruction, triggering a slowdown as backup systems are called into action. The performance and patient care threats of any unplanned downtime event are always present and should be accounted for in the downtime procedures.
We found that cyber-attacks represented a large proportion of the reported downtime events noted in the technical literature. Ransomware viruses encrypt the entire file system and display messages demanding monetary ransom in exchange for the decryption key.11,22 Defending against ransomware is even more challenging, as some variants have embedded code that enables silent duplication through all connected computers within a network, remaining dormant until an activation signal encrypts all infected systems at once. Many hospitals have chosen to shut down all computers during a ransomware attack; these shutdowns stop all electronic transmission of information, forcing fallback to rarely-practiced paper workflows.
According to the Identity Theft Resource Center, which tracks and reports data breaches annually, healthcare industry data breaches represented the highest proportion—at 44 percent (n = 374)—of all compromised records reported in 2016 (n = 1091). 23 Healthcare- and non-finance-based businesses led the overall proportion of breach events, reported at 55 percent (n = 870) and 23 percent (n = 374) of 2017 breaches, respectively, and such breaches have seen continued growth.23–27 It is likely that hospital data will continue to be a desirable target for cyber-attack and compromise. While not all healthcare downtime events include a related data breach, the growing interest and value placed on healthcare data suggests that the data breach issue will continue to grow. The upward trends in cyber-breaches may make healthcare systems prone to excessive amounts of downtime during which alternative methods and contingency plans need to be utilized.
Recent trends suggest cyber-attacks on hospital and EHR data systems are likely to increase. EHR systems are expanding both in terms of extent of patient information and recent integration of interconnected mobile technologies, providing new avenues for access. The EHR information is comprehensive enough that it could be possible for a “medically insured identity” to be compromised and sold, similar to how credit card numbers and legal identities have been compromised and sold in the past. A recent white paper suggests that an individual’s basic identity information such as a social security number is valued at US$1 on the black market, while an individual’s healthcare data are valued at US$50, and some indicate the value disparity may be even greater. 28 Also, a breach of this nature would constitute a Health Insurance Portability and Accountability Act (HIPAA) privacy violation for failure to protect the patient’s information and incur significant fines and potential lawsuits for the institution found to be responsible for protecting that data. In most of the downtime events to date, cyber-criminals have elected to disrupt operations and hold the computer systems hostage, often demanding monetary ransom to allow the hospital to regain control of its computers.29–31 Some of the hospitals targeted for cyber-attack have admitted to potential breaches of their patient information databases.32–34 Currently, authorities do not advise hospitals to pay the ransom demand, because it is not always assured that the hackers will return control of the systems, as the Kansas Heart Hospital encountered in 2016.35,36 As hackers evolve their methods with security developments, and as Internet-connected healthcare devices increase, it is unlikely that the cyber-attack threat will ever be completely eliminated.
Scoping review of downtime research
In Figure 1, 1764 studies were found to be potentially related to downtime; 1724 studies were found to be related to biomedical research where the search strings returned false positives. After elimination of the false positives, 40 studies were reviewed in full, with 29 removed based on failure to meet all inclusion criteria, and 10 studies were included within the scope of this review. Table 5 summarizes the reviewed papers using the criteria described above.
Scoping review summary.
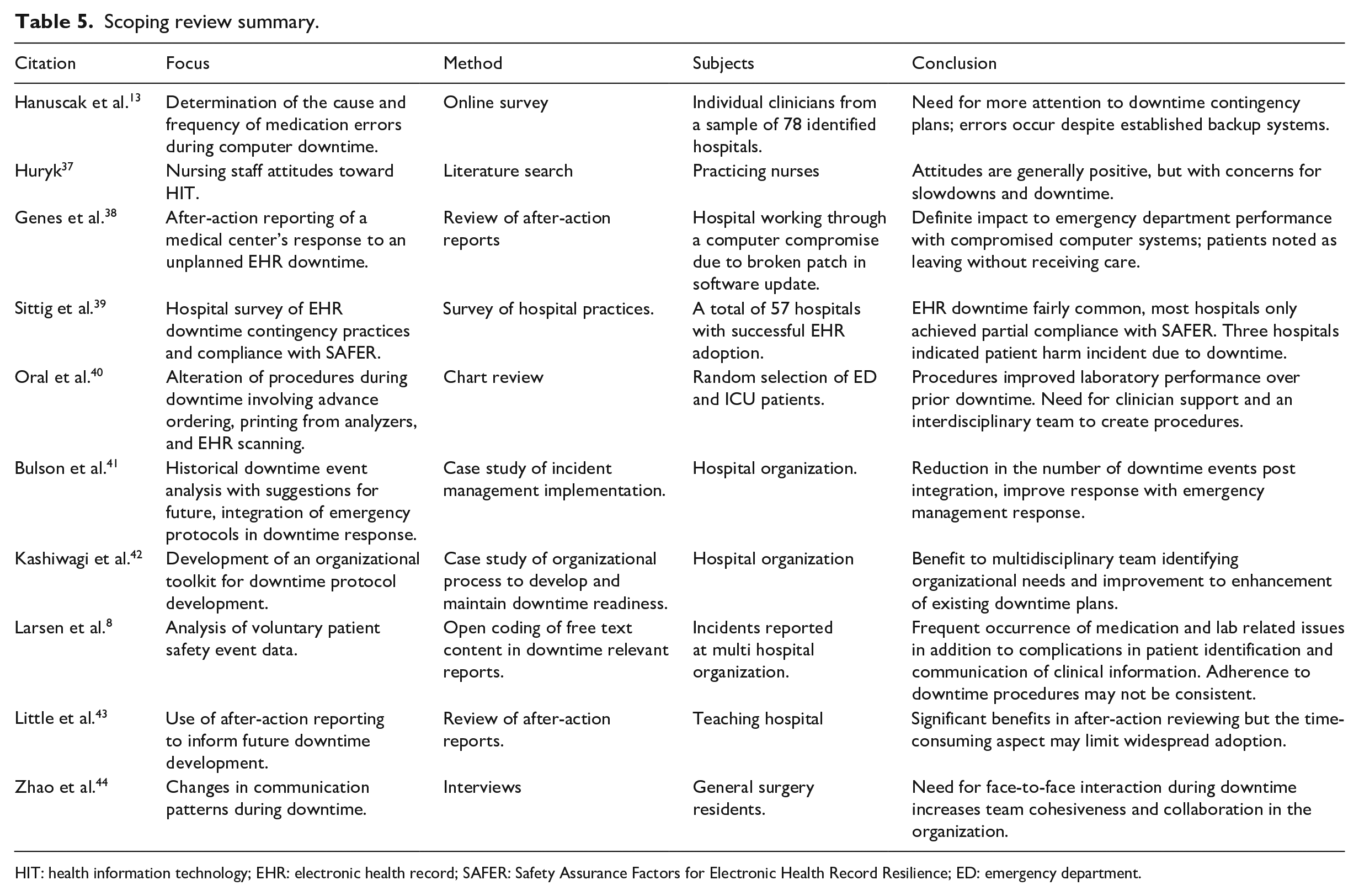
HIT: health information technology; EHR: electronic health record; SAFER: Safety Assurance Factors for Electronic Health Record Resilience; ED: emergency department.
A concentration on specific downtime events was present in 70 percent (n = 7) of the literature, potentially related to growing interest in the area. However, this review suggests a general gap in quantifying the impacts of downtime on healthcare systems and patient safety despite the apparent high frequency of events. One possible reason could be the lack of, or limited access to, sufficient viable data from downtime events to statistically test hypotheses. 10 In particular, only two studies13,39 studied the outcomes of downtimes. Hanuscak et al. 13 surveyed pharmacy staff who had experienced an EHR downtime to uncover the nature and the frequency of medication errors during downtime events. The study found a total of 39 medication errors occurring during downtime events in 1 year, 14 of which impacted the patient, with one mistake resulting in an increased length of stay. Sittig et al. 39 surveyed 50 hospitals that had successfully implemented an EHR into their system; 96 percent of the hospitals responded that they had experienced at least one unplanned downtime event within the prior 3 years. In addition, three hospitals were able to attribute some form of patient harm in one or more patients during a downtime event of any type. Despite the predominantly negative presentation of downtime, Zhao et al. 44 indicate that downtime events can have a positive impact, suggesting that the lack of computer systems forces face-to-face interactions and collegiality to increase in the opinion of surgical residents.
Current state of downtime preparation from research literature
The current body of research supports contingency planning for downtime events of any origin; however, in the face of the growing cyber-attack-based threat, robust downtime contingency planning is becoming more critical and warrants more attention. 10 The approaches recently published8,39–42,45 vary in departmental scope, technical approach, and healthcare worker involvement. In most reviewed downtime events, clinical staff had been reported as making their own downtime procedures and exposing patients to new risks, such as delay in care, increase incidence of wrong dose, and wrong medication administration.8,10,46 While the reasons for these unsanctioned adaptations are unknown, possible reasons could be the absence of official downtime procedures that support continuing necessary work and perception among front-line staff that the unsanctioned adaptation is better than existing procedures. Human-centered efforts focused on the front-line staff behaviors, adaptations, and obstacles could shed more light on this issue.
The fragmented and relatively sparse literature retrieved in this scoping review indicates that there is significant opportunity for numerous and simultaneous mixed-methods explorations into downtime planning. The literature retrieved ranged from a systematic review of sentiments published regarding healthcare informatics seen in the works of Huryk 37 to Zhao et al., 44 conducting interviews directly with surgical residents who had to work through a downtime event during their residency.
Opportunities to improve future downtime handling
In terms of developing regulatory guidance, Sittig et al. 39 utilized organizational survey responses about downtime handling. The responses helped to inform the Safety Assurance Factors for Electronic Health Record Resilience (SAFER) guides which are currently the accepted best practices for EHR implementation. 47 Also significant is the study of Little et al. 43 in which the after-action sessions from a downtime event formally guided revision to procedures to be implemented in future downtimes. Larsen et al. 8 utilized voluntarily submitted downtime incident reports from a range of departments to develop suggestions for improvements to downtime, finding interdepartmental communication of downtime and formal downtime training to be recurring issues. Bulson et al. 41 proposed that hospitals should deploy their incident command procedures in response to a downtime event (similar to deploying procedures for a hurricane) and demonstrated that such actions could reduce downtime event duration by as much as 48 percent per month.
The recent increase in the number of downtime events in the last decade, while unfortunate, has yielded sufficient organizational data and employee experiences to encourage in-depth downtime studies in the future. However, this review shows that the wealth of organizational experiences is not well leveraged yet. Future studies should focus on and utilize the experiential knowledge that most, if not all, hospitals possess from downtimes. This experiential knowledge may be obtained using techniques similar to the after-action reporting analysis from Genes et al. 38 and Little et al., 43 the general historical review from Bulson et al., 41 or the survey data collection from Sittig et al. 39 Continued research into the abstract concept of downtime events without regarding the available concrete experiences misses an opportunity to expand our knowledge of downtime. Similarly, in order to move beyond the accepted belief that downtime events impact safety and performance in general, analyzing records of prior events can identify specific areas of the hospital that are heavily impacted and, therefore, should be the focus for improvement efforts.
Expanding current best practice and guidelines
In its current iteration, the SAFER guides indicate that procedures be developed for downtime events, that the procedures encompass communication plans, and that they are made readily available, with staff aware of and trained on those procedures. Despite these guidelines, the SAFER falls short in specifying how the downtime procedures should be developed. The present regulatory and guideline instructions to have a plan in place and to practice it are insufficient for downtime readiness, especially when faced with increasing threats as the valuation of health information increases. Work is needed to provide detailed best practice guidance on downtime plan development and assessment.
Limitations
The scoping review of news media articles is limited to publicly acknowledged downtime events. It is likely that there are other events outside the public record. Many hospitals may choose to protect the knowledge that an incident has even occurred. Without a news media report of the event, external stakeholders may not become aware of the frequency and severity of downtime events and may develop a biased risk perception related to downtimes. The same concerns for acknowledging a downtime event may also hinder researchers from gaining access to better study the downtime issue. Furthermore, any existing data from a downtime event are likely from a period of significant organizational and technological disruption, making data quality an issue.
Conclusion
The risk of a hospital experiencing an EHR downtime event is ever-present and potentially growing. Present research efforts are starting to examine downtime readiness and planning, but many studies may miss the mark by not incorporating the organizational knowledge available from prior events. The base of healthcare workers who now have experience working through downtime events and any associated records from those prior events should be leveraged where possible in holistic user-centered frameworks for study and improvement.
Regardless of the origin, downtime events should be planned for and those plans practiced. While a downtime event is complicated and chaotic, the risk in waiting to determine the origin before reacting—especially when there is potential breach of patient data ongoing—places patients’ information and the hospital at significant financial risk. Hospitals need to be prepared to identify the origin rapidly and respond appropriately. While ideally the shutdown of computer systems should be avoided, it may be necessary. Delays in enacting such a response could result in significant breach of patient data and financial cost to the organization.
Researchers should make use of the existing organizational knowledge to understand the downtime events in detail. While each event is unique, the healthcare workers and event documentation can be utilized to explore aspects of resilience, for example, in the context of work-as-imagined versus work-as-performed.48–51 This approach would be particularly useful to unpack the issues surrounding unsanctioned downtime procedures enacted by individuals, to identify why the procedures are being employed, and what gaps motivate them.
The study of downtime procedures and development of operational contingency plans to continue care are critical to modern healthcare. While information technology specialists may develop more secure data systems and detection programs, those who seek to compromise or disrupt healthcare information technology systems will continue to advance their methods as well. There will always be motivation to compromise healthcare data, and so cyber-attack based-downtimes in particular will likely continue indefinitely. These findings from the limited relevant literature highlight the importance of proactive measures and resilience to address potentially complex downtime scenarios to come.
Footnotes
Acknowledgements
The authors would like to thank Jacob M. Kolman for his editorial assistance in the preparation of this manuscript.
Author contributions
Each author contributed to the conception or design of the work, data analysis and interpretation, critical revision of the article, and final approval of the version to be published.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
