Abstract
Cyber operations ranging from deception and espionage to disruption and high-end degradation have become a central feature of modern statecraft in the digital age, yet we lack a clear understanding of how decision-makers employ and respond to cyber operations in times of crisis. Our research provides theoretical mechanisms and empirical evidence for understanding how decision-makers react to cyber triggers and utilize cyber responses during crises. Specifically, we argue that the availability of cyber response creates off-ramps for non-escalatory engagement. Based on experimental wargames involving rival states with power parity in militarized disputes and randomized cyber triggers and response options, we find the availability of cyber response options reduces escalatory behavior via a substitution mechanism. In the absence of cyber response options, however, participants pursue more conventional, escalatory actions, regardless of the triggering mechanism. Our findings underscore how enhancing the availability of cyber response options might reduce strategic escalation risks and offer the space to bargain during periods of conflict.
Introduction
Despite over 30 years of documented cyber operations (Healey and Grindall, 2013), there is no consensus on how cyber operations affect crisis behavior during international disputes. In February 2019, India and Pakistan exchanged artillery and small arms fire while engaging in air-to-air combat and bombing runs after a terrorist attack which India blamed on Pakistan. Despite militarized escalation in this key rivalry alongside evidence of prior cyber exchanges (Valeriano and Maness, 2015), there were no observed large-scale cyber actions above the level of website defacements and temporarily taking websites offline ( Times of India, 2019). Power plants did not shut down. Dams kept working.
Alternatively, in the summer of 2019, the United States opted for cyber attacks against Iran in lieu of strikes against its air and missile defenses after Tehran shot down a Global Hawk surveillance drone (Barnes and Gibbons-Neff, 2019). The target was the same: Iran’s air and missile defense, with lines of code seeking to disable computer systems replacing missiles striking radars while cruise missiles hit command posts, launchers, and storage deports (Bender and Lubold, 2019). Reports suggested the US President opted for the option after briefers assessed conventional strikes could kill over 150 Iranians, a number the President found disproportionate (Shear et al., 2019).
These events present a puzzle: When and why do states use cyber operations to respond during a dispute or crisis? Do cyber operations tend to be associated with more or less escalatory responses in crises? More broadly for the international relations community, how does any new disruptive technology alter the cycle of competitive risk-taking at the core of strategic exchange between rival states? Answering these questions is a core task for IR scholars and policymakers in the digital age. Scholars in this Special Issue of the Journal of Peace Research, speak to the new generation of cybersecurity scholarship that makes bold, theoretically grounded, and empirically tested claims about the dynamics of cyber conflict, particularly regarding human dimensions of cybersecurity (Shandler and Canetti, 2024).
This Special Issue focuses greater attention on the behavioral, psychological, cultural, and social dimensions of the people who engage in cybersecurity practices (Akoto, 2024; Kostyuk, 2024). Our research examines the behavioral dimensions of decision-making (Jardine et al., 2024). Understanding how decision-makers utilize and respond to cyber operations is crucial to preventing attacks from escalating into broader, more destructive crises (Lonergan and Lonergan, 2023). Of particular importance is whether decision-makers, even well-trained military advisers, have psychological predispositions or ingrained biases that might predispose them to escalatory behavior.
Experimental wargames offer a means to explore this puzzle. 1 Any crisis is defined by interdependent decision-making in environments characterized by uncertainty, time pressure, and private information. New technologies and tools of coercion compound this uncertainty and create new risk vectors. Therefore, a viable research path is offered by designing exercises that replicate the context and character of national security decision-making environments, draw on players with similar backgrounds to career professionals, and utilize randomization and treatment groups that control for the impact of disruptive technologies.
To that end, we designed a strategic-level wargame that captures decisions about whether or not to escalate a crisis between two rival states. Our wargames were experimentally manipulated through random assignment of (1) a cyber triggering event to the crisis and (2) whether or not participants could respond with cyber operations alongside more traditional instruments of power (i.e. Diplomatic Information Military and Economic known as DIME). After observing 400 crisis responses via a cross-national wargame experiment, two insights emerge. First, the presence of cyber operations does not escalate militarized disputes. In experimental settings, participants did not use cyber operations to escalate a hypothetical crisis with a rival state. Second, the presence of cyber responses in a crisis increases the range of options and provides additional bargaining space. As a result, cyber options provide a means to shape the crisis while creating possible off-ramps and alternatives to the use of military force or other coercive means (Jensen and Valeriano, 2022).
To support these conclusions this article proceeds as follows. First, we examine major findings in the literature on cyber operations, escalation, and wargames. Second, we detail the wargame design and procedures used to administer our key experimental treatments. Third, we analyze the findings in relation to hypotheses grounded in the escalation literature. Fourth, we conclude by discussing additional research needed to unpack cyber escalation dynamics.
Wargaming cyber crises
Great powers increasingly rely on cyber operations to support larger coercive campaigns and to complement other instruments of power they deploy as flexible deterrents and flexible response options (CJCS, 2018a). National cyber strategies (Kostyuk, 2021) and military doctrine (CJCS, 2018b; Science of Military Strategy, 2020) all integrate cyber effects, often as a form of covert interaction and signaling (Carson, 2018; Carson and Yarhi-Milo, 2017; Jensen, 2017) into modern operational art and campaigning. Yet, just how decision-makers and planners conceptualize the utility of these operations in responding to an unfolding crisis remains a black box. The theory and planning constructs are clear, but the operational reality and decision-making calculus are opaque, creating a critical gap for scholars studying international security, conflict processes, and the prospects for peace in the 21st century.
Wargames offer a viable method for evaluating propositions on the character of escalation under the context of cyber operations and disruptive technology more generally. The use of wargames to evaluate interdependent decision-making has a long tradition in the military profession and strategic studies communities (Bartels, 2020; Bartels et al., 2013; Caffrey, 2019; Emery, 2021; Lin-Greenberg et al., 2022; McDermott et al., 2008; Perla, 1990; Reddie et al., 2018). Wargames, as a form of simulation, are a useful method for evaluating competing hypotheses, focusing data investigations, and delineating patterns otherwise unobserved (Druckman, 1994; Lin-Greenberg et al., 2022, Valeriano and Jensen, 2022; Wilkenfeld et al., 2003).
Recently, there has been a renaissance not just in wargaming but in the use of wargames to evaluate interdependent decision-making in a strategic setting (Barzashka, 2019). Pauly (2018) utilized wargames with strategic elites to examine attitudes toward nuclear weapons, finding restraint based on reputational risks (see also Goldblum et al., 2019 on the Project on Nuclear Gaming PonG). Lin-Greenberg (2022) also finds counterintuitive escalatory restraints involving the use of drones in wargames with national security experts.
There is an increasing interest in using wargames and simulations to uncover the micro-foundations of interdependent decision-making in cyber exchanges (Gomez and Villar, 2018; Gross et al., 2017; Schneider, 2018; Schneider et al., 2022). In particular, Schneider (2018) has used a longitudinal analysis of wargames between 2011 and 2016 to study crisis dynamics, revealing that government officials were reluctant to use high-end cyber offensive capabilities. Of note, Schneider (2018) found that participants only used offensive cyber capabilities after conventional military strikes, and expressed concerns that using offensive cyber would increase the risk of nuclear escalation. Jensen and Banks (2018) found similar patterns in a series of wargames analyzing how decision-makers integrated cyber operations into crises with both great power competitors and non-state actors.
Recent wargaming studies by Schneider, Schechter and Shaffer (2022) provide additional confirmation that escalation is the exception, not the rule with cyber operations. Schneider, Schechter and Shaffer (2022) utilized multiple levels of escalation in their wargame design: a low-intensity scenario at the beginning of an armed conflict and a high-intensity scenario involving armed invasion and prospects of nuclear war. The first scenario shows how cyber operations are used conservatively, where cyber operations generally functioned to support other actions (diplomacy, crisis bargaining), and complement actions (such as intelligence gathering). The second scenario, involving much higher levels of escalation, reveals broader use of offensive cyber operations by wargaming teams in support and substitution roles. Rather than act as a decisive move up the escalation ladder, cyber operations appear to serve more as a means of shaping a larger strategic interaction.
Our wargame builds upon the existing literature and presents an important design precursor to understanding cyber behavior at the early stages of disputes. We focus on the use of cyber operations at the initial stages of low-level militarized interstate disputes to understand how cyber triggers and cyber responses serve to escalate or de-escalate emerging crises relative to conventional diplomatic, intelligence, military, and economic (DIME) operations. Our main contribution to the literature involves parsing out the effects of cyber triggers from cyber responses in escalating low-intensity militarized disputes. We find that cyber response options are especially critical to providing off-ramps for escalation. We now turn to our key hypotheses.
Cyber triggers and cyber responses in crisis escalation
For conceptual clarity, we utilize Brecher’s (2008) definition of crisis escalation where an international crisis is ‘a change in type and/or increase in intensity of disruptive interactions between two or more states with a heightened probability of military hostilities’ (2008: 7), and escalation is a phase of crisis following onset that involves ‘more intense disruption’ and ‘a qualitative increase in the likelihood of military hostilities’ such as a shift from either non-violence to violence or if violent from the onset, then from low to high-intensity violence (2008: 11). We define cyber triggers as actions or events involving the use or perceived use of cyber technology that is associated with the onset or escalation of a crisis, while cyber responses are actions or events involving the use or perceived use of cyber technology following the onset of a crisis and the crisis-triggering event. We note that our definition encompasses dual-use objective and socially constructed understandings of cyber technology consistent with Lehto et al. (2011).
What role do cyber operations, including triggers and responses, play in crisis escalation? Cyber operations ranging from deception and espionage to disruption and high-end degradation have become a central feature of modern statecraft (Gartzke and Lindsay, 2015; Valeriano et al., 2018). From long-term espionage campaigns like the OPM hack (Nakasima, 2015) and SolarWinds (Peisert et al., 2021) to targeted strikes involving malware like the famous Stuxnet effort to degrade Iranian nuclear capabilities (Lindsay, 2013), cyber operations are part of modern strategic competition. Despite these high-profile cases, cyber operations tend to have weak and often limited effects across domains (Borghard and Lonergan, 2017; Gartzke and Lindsay, 2019; Kostyuk and Zhukov, 2019). Rather than decisive weapons of war, cyberspace more often tends to support long-term competition beneath the threshold of armed conflict (Fischerkeller et al., 2022; Valeriano et al., 2018). Cyber operations thus function as a disruptive technology, altering but not transforming the dynamics of strategic exchange (Brantly, 2016; Gartzke and Lindsay, 2015; Maschmeyer, 2021; Rid, 2012; Rovner, 2019). 2
We view cyber operations as a form of sub-crisis maneuvering – a combination of ambiguous signals used to manage competition (Carson, 2018), or a means of conducting operational preparation of the environment. As an instrument of power and influence, we argue that cyber capabilities do not cross – at least not yet – the threshold of escalation to armed conflict. In a crisis, when decision-makers have access to cyber response options, they are more likely to use them to conduct responses beneath the threshold of armed conflict while taking defensive actions that prepare them for future interactions with an adversary.
From a broader perspective, our argument explores how disruptive capabilities alter bargaining processes and crisis dynamics. Beyond reducing capabilities to pre-determined offense or defensive attributes (Jervis, 1978) or ascribing independent preferences to actors consistent with the recent turn to Bayesian realism (Kydd, 2005), how do new technologies alter information and uncertainty during a crisis? The effects observed in crises involving the use or potential use of cyber capabilities may have similar dynamics to satellites, electronic warfare, and other systems that blur the lines between intelligence, offense, and defense. If a state perceives it has an advantage in these indirect, more shaping-oriented, activities, the asymmetry provides them an expanded set of options. This expanded set of options should be associated with higher rates of de-escalation since the state establishes an advantage that it can use in both the present and the future. This promise of future escalation options allows for more conciliatory behavior in the present. The traditional logic associated with the commitment issues and the shadow of the future in bargaining literature is inverted allowing state decision-makers to accept delaying decisions to escalate.
In theorizing cyber capabilities and escalation, we focus on two distinct applications – cyber operations as potential triggers and responses. We argue that whether cyber triggers are less likely to escalate a crisis than non-cyber-related triggering events depends on the response options available to decision-makers. Our hypotheses can be summarized in the following 2×2 table (Table I).
Likelihood of escalation
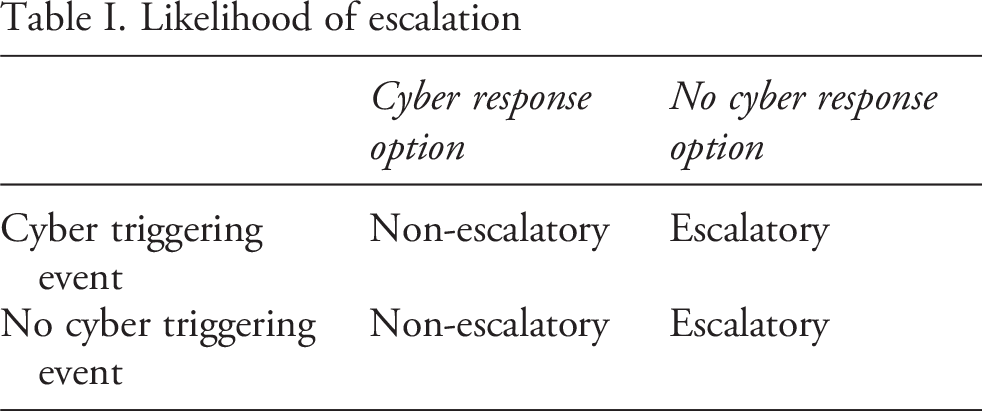
Hypothesis 1: Cyber response options reduce crisis escalation. 3
Hypothesis 2: Cyber response options reduce crisis escalation even in the absence of cyber-triggering events.
We now turn to our research design which involves an original wargame with experimental treatments to test our hypotheses.
Research design
We begin with a general discussion of our design strategy and research goals followed by a detailed description of our wargame protocols and analytical strategy. Following design recommendations by Lin-Greenberg et al. (2022), our key research question focuses on the effects of cyber triggers and responses on crisis escalation. Our research goals involve causal inference, so we utilize an experimental rather than observational wargame. We use a single-iteration game to establish a baseline causal effect of cyber triggers and responses which can be tested through multiple iterations in future research. Lin-Greenberg et al. (2022) also note that attrition becomes increasingly a problem with iterations in complex wargames with significant time and cognitive demands. Our design maximizes compliance among participants with a wargame requiring less than 45 minutes to complete.
Regarding sample selection, our research examines decision-making among a range of national security experts and non-expert sub-groups. In each wargame, participants were either experts or non-experts but not on the same team. The inclusion of non-experts helped to boost the sample size, while the expert samples increase the external validity of the wargame outcomes to national security elite decision-making in practice.
Next, our game involved standardized, pre-selected response actions which included randomized cyber response options alongside other diplomatic, intelligence, military, and economic (DIME) options. The advantage of standardized outcomes includes a high degree of adjudication or control, which is essential for estimating causal effects. Standardized response options also help mitigate against Stable Unit Treatment Value Assumptions (SUTVA) violations or ‘spillover effects’ across treatment groups (Rubin, 1986), such as selecting cyber response options by teams not part of the cyber response options treatment.
Also, our game utilizes a one-sided design. We gauge the escalatory tendencies of cyber triggers and responses only on one side of a wargame involving two rival states with relative power parity. While technically a single-move game, we allow respondents to select from among a range of standardized DIME and cyber response options within their single move. We do not assess iterated responses between gaming groups in a two-sided game as we are focused primarily on the initial effects of cyber triggers and the presence of cyber responses on initial decisions to escalate a crisis.
Next, our research uses an abstract/general scenario involving fictional states because we are interested in broadly generalizable effects of cyber triggers and responses on escalatory behavior. Using specific, real-world scenarios involving real countries may enhance external validity but could also introduce context-dependent qualifiers on treatment effects (conditional to USA–China or USA–Russia rivalries, for example). We seek to avoid those context dependencies in this early design. Using hypothetical states helped remove participants from pre-existing biases about current international relations.
Finally, we collect data on game outcomes as well as deliberative data on motivations. Our key outcome variables involve response plans (DIME and cyber-related response options) but we also collect deliberative data involving assessments of the adversary’s intent (hostile/not hostile) and an assessment of escalatory risk (low–high). We focus our analysis on the individual, though we control for the size of wargame teams which ranged from single individual players to upwards of five team players. However, even in team games, each player completes an individual response plan to the crisis. We now present our detailed gaming protocols.
Wargame protocols
To examine the escalatory effects of cyber triggers and responses, we develop a wargame involving two hypothetical states with power parity: a Green state and a Purple state, with wargame participants acting on behalf of the Green state. 4 Participants were given packets modeled after documents used in the US National Security Council (NSC). 5 The briefing packet provided an overview of the crisis and asked participants to select response options organized in relation to different instruments of power (i.e. diplomatic, information, military, and economic). Participants were randomly assigned one of four different packets with cyber trigger or cyber response treatments, neither, or both. Each packet had the following: (1) a tasking memo providing background on the current crisis (2) a J2 or Intelligence Update (see Figure 1) (3) a response packet with pre-approved flexible response options and (4) a post-game survey. 6
The tasking memo (see Online appendix for details) informs participants that ‘an escalating crisis with long-term rival Purple started 14 OCT 20XX’ and that ‘the incident marks the fourth major crisis in the last six years involving Purple.’ Participants are also informed that the ‘The National Executive wants options for a coordinated response for the principals meeting scheduled 18 OCT 20XX. The meeting will determine whether to escalate, conduct a proportional response, or de-escalate in the current crisis.’ Participants are told that the purpose of the wargame is to ‘prepare a Crisis Strategy Template in preparation for the 18 OCT 20XX principals’ meeting’ which includes ‘recommended crisis response options for countering Purple.’
Next, participants receive a J2 update. Figure 1 illustrates a sample J2 or intelligence update from one of the treatments. (ES//NF) is a clearance designation used by the US intelligence community for secret intelligence documents not to be shared with foreign nationals. The title ‘Green J2’ indicates that this is an intelligence update for the Green Country. The figure provides a map showing the outline of Purple Country’s maritime boundary waters and indicates recent crisis events in the area with Green. The relative military capabilities of Purple and Green are also displayed in a table. These capabilities are held constant for all wargaming teams and are consistent with major power parity, where Purple or Green possesses a slight advantage on one or more capabilities, but no clear absolute advantage.
7
The title also references the ‘Corcyra Crisis’ which is described in further detail in the events section at the bottom of the figure. In our wargame, Corcyra LLC is an international Wargame crisis intelligence update with cyber trigger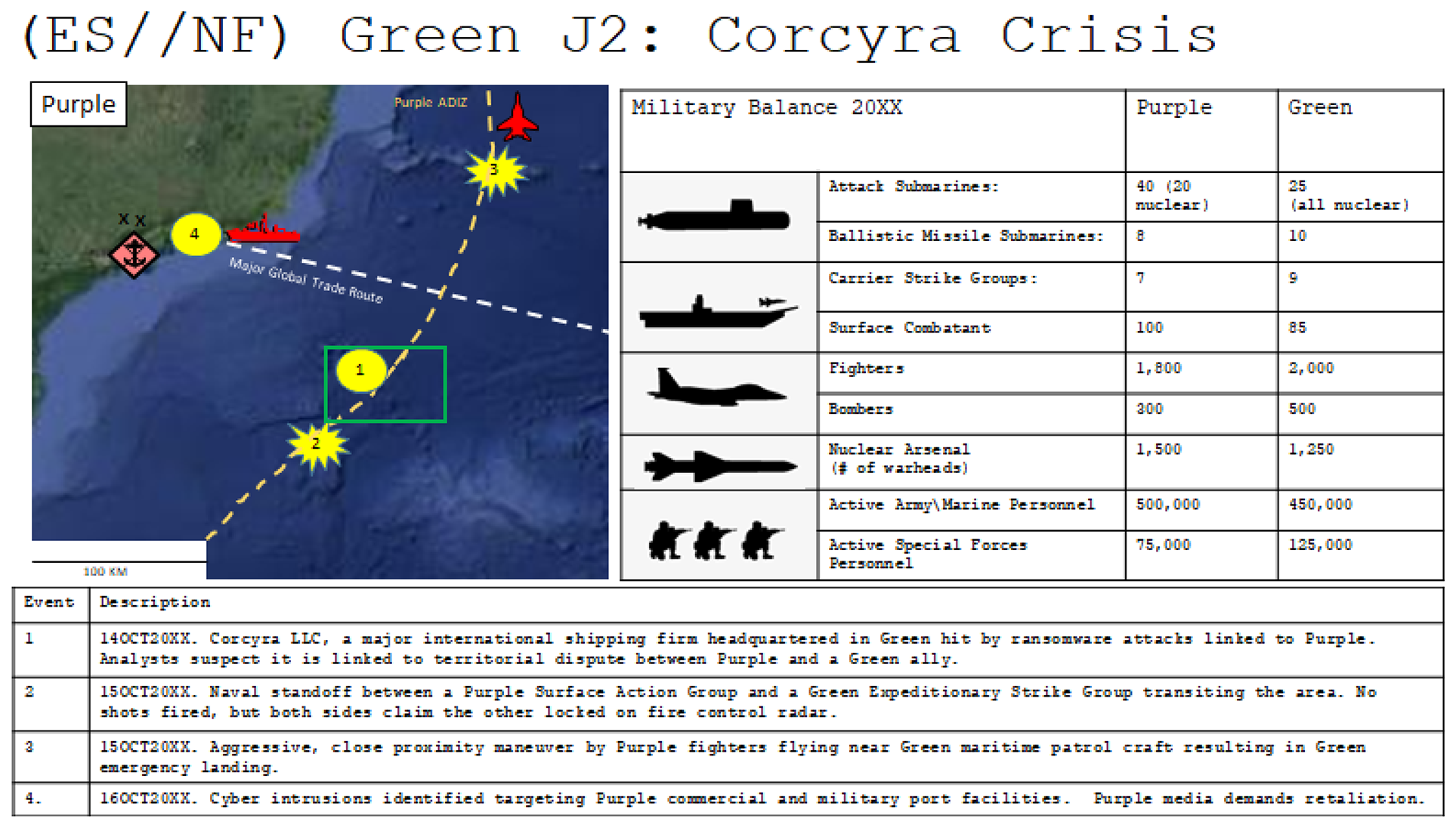
After evaluating the J2 intelligence update, participants receive a response packet with standardized response options. First, respondents were asked to indicate their assessment of Purple’s intentions as either unknown, signaling not hostile (not likely to escalate), signaling hostile (likely to escalate), or hostile with crisis escalation imminent. They were also asked to select response options to Purple based on standardized diplomatic, intelligence, military, and economic response options. Table II provides standardized military response options (See Online appendix for diplomatic, intelligence, and economic response tables). Participants can select as many as three response options from a given diplomatic, intelligence, military, or economic response table. 9 In all variables of the wargame, participants have the left-hand side response options, but only in the variants with cyber response options are the right-hand side options included as they are cyber-related. 10 Respondents were also asked whether they consider their overall crisis response to be de-escalatory, proportional, escalatory, or if they were unsure.
In summary, we have a single-shot game that is nested within a series of preceding crisis events involving Green Country and Purple Country. There is no sequential or simultaneous battle taking place or adjudication. Green is preparing a crisis response plan, but the plan is not acted upon during the game, and Purple Country does not respond during the game. Because these conditions are held constant across treatment groups, they do not bias treatment effects across cyber trigger and response wargaming groups. 11
Finally, we include a brief post-game survey collecting data on gender, age, occupation (government, military, business, academic), citizenship (US or foreign), an assessment of their comfort with using technology, and an assessment of the escalation risk of the crisis, which we utilize as control variables in our subsequent analysis.
Defense Ministry approved flexible response and deterrent options (Military)
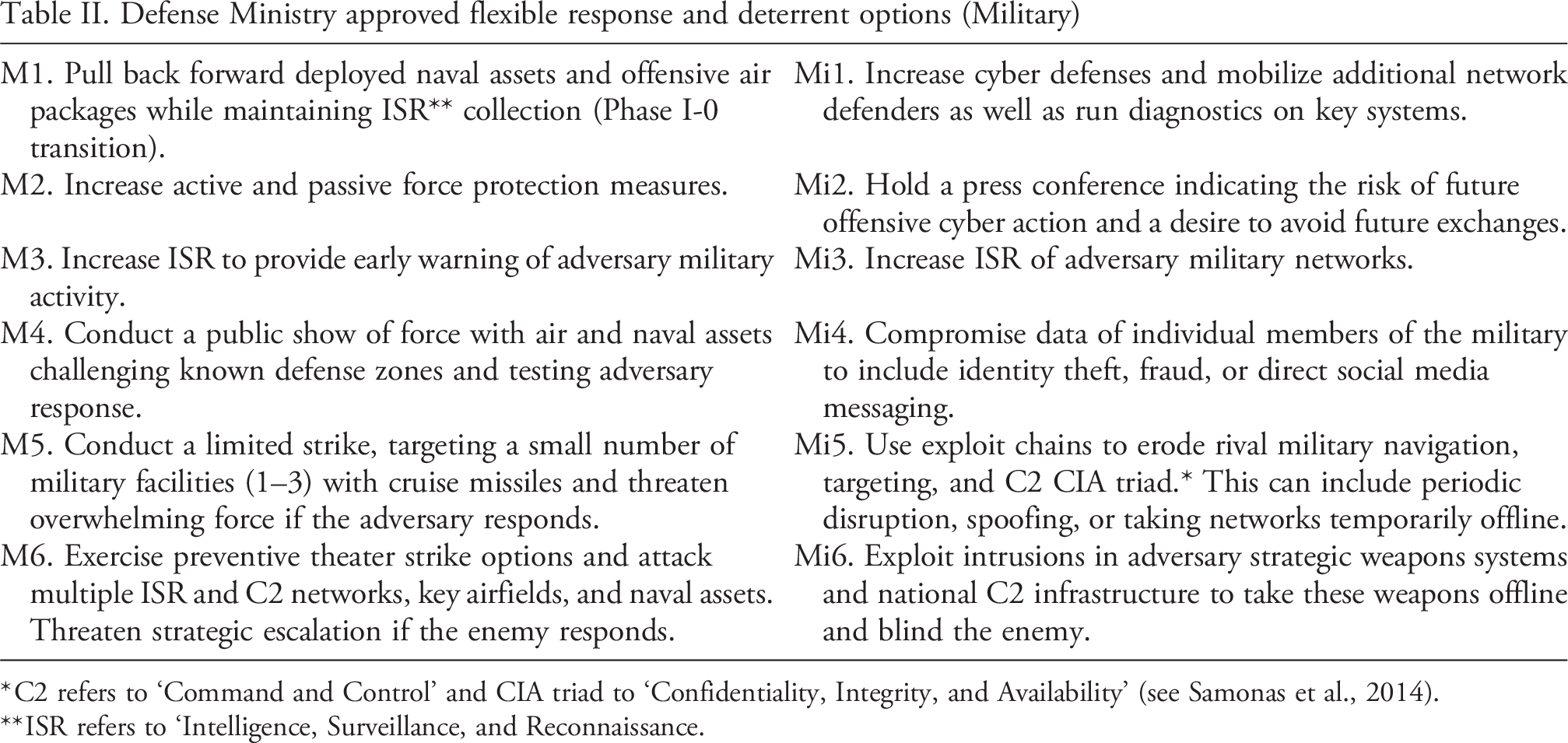
* C2 refers to ‘Command and Control’ and CIA triad to ‘Confidentiality, Integrity, and Availability’ (see Samonas et al., 2014).
** ISR refers to ‘Intelligence, Surveillance, and Reconnaissance.
Randomized treatment-control groups
During the wargame, facilitators then let individuals work through the scenario packet. This step usually took 30 to 45 minutes. The treatment groups then convened to discuss their responses. Facilitators wandered between groups taking notes on how groups discussed various options. Each group then briefed their recommended response options to the rest of the assembled group. At this point, the facilitator would reveal that groups had different response options and transition to a general conversation about strategy, cyber response options, and contemporary crises. The design is thus best characterized as a seminar-style, table-top exercise (Pournelle, 2017). We now turn to a discussion of the randomization of cyber triggers and controls and our identification strategy.
Identification strategy
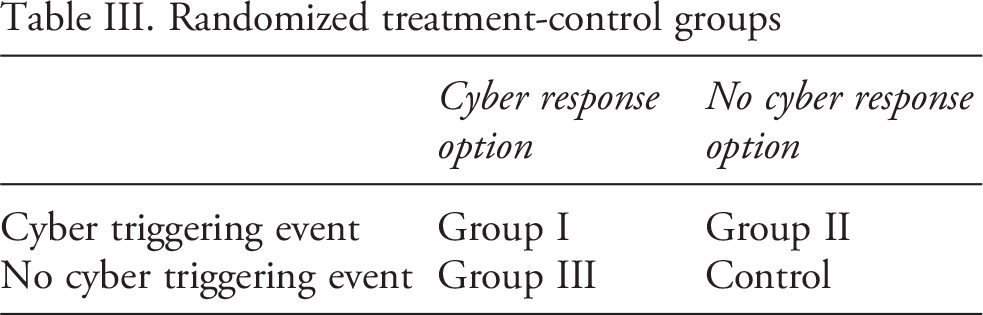
Participants were randomly separated into groups to examine the effects of cyber triggers and responses on crisis escalation and given a crisis response packet containing cyber triggers, cyber response options, both or neither. The groups reflected the different treatments listed in Table III differentiating between cyber response options and cyber-triggering events to the recent crisis.
To assess escalation, the response packet builds in three unique measures. First, respondents were asked whether they wanted to escalate, conduct a proportional response, or de-escalate. Second, the response options were arrayed in a manner that differentiated between three de-escalatory options and three escalatory options for each instrument of power. The researchers coded an event as escalatory if any single response option was escalatory. That is, even if the respondent thought they were being proportional and selected three responses – a request for backchannel diplomacy (de-escalatory), a public call for calm (de-escalatory), and a threat of economic sanctions (escalatory) – the response was coded as escalatory. 12 The responses were listed moving from least to most escalatory but avoided offering the participants the option of using nuclear weapons. Response options also differentiated between traditional instruments and cyber options. This allowed the researchers to vary the treatments and offer participants cyber response options and no cyber response options. Last, each participant was asked to rate the overall escalation risk at the end of the wargame.
To assess the treatment effects of cyber triggers and responses on escalation (Hypotheses 1 and 2), we utilize the following logit regression model:
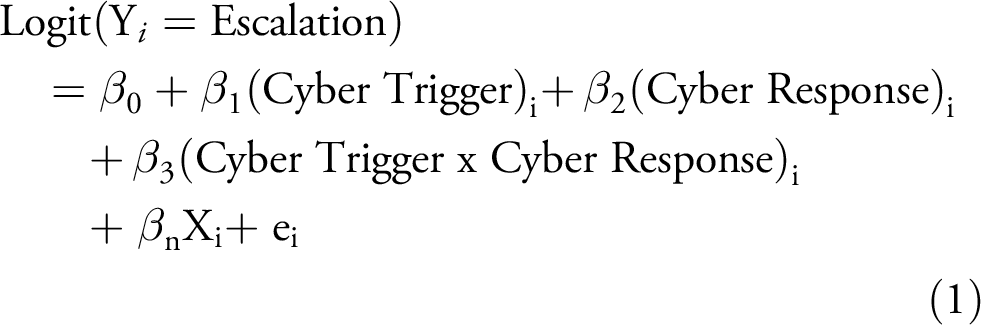
where the dependent variable is the logistic transformation of the probability that individual (i) will choose to escalate the crisis using the second measure of escalation as a binary categorical variable (escalation, no escalation) based on players’ selected response options. We then assess the likelihood of escalation based on binary treatment variables for the presence or absence of a Cyber Trigger and/or Cyber Response. 13 In the model, we utilize β0-3 to test Hypothesis 1 that cyber response options reduce crisis escalation, and Hypothesis 2 that cyber response options reduce crisis escalation even in the absence of cyber-triggering events. We also include a number of extended controls βn for demographics and other relevant data on adversary intent and risk assessments provided by participants during the wargame.
Finally, regarding the use of cyber options as supplements or substitutions, we note that respondents could choose from a range of diplomatic, intelligence, military, and/or economic responses that include or do not include cyber options (if cyber options are included in the treatment group). Hence, cyber can supplement, support, or complement other response options. Using cyber response options as a substitute for more conventional DIME options could be inferred from cross-treatment comparisons. We can evaluate whether respondents make use of cyber response options as a substitute for conventional responses when given the option.
Data collection and analysis
Our wargame involved a target audience of 400 international professionals including international relations professors and graduate students (44%), military officers (25%), government officials (10%), private sector employees (5%), as well as a small sample of international relations undergraduate students (9%). Our sample includes participants who completed the wargame as individuals (27%) rather than in teams, while the remaining completed the simulation in teams of 2 to 5 players with an average of 2.67 (SD=0.97) for games involving more than one player. Teams were largely of the same cohorts (professionals or academics) which varied by location. We did not have undergraduates playing in teams with or against senior military personnel. Individual players were randomly assigned to different wargame treatment groups. Groups of 2–5 were also randomly assigned but group deliberations were run separately to prevent SUTVA violations (spillover effects) between treatment groups during deliberations (Rubin, 1986). For example, we did not run groups with a cyber trigger and non-cyber triggers or cyber responses/non-cyber response options, in the same seminar at the same time. The sample was primarily US-based (83% of the sample was from locations in Virginia, Washington DC, North Carolina, California, and New Jersey) while the remaining participants were from the United Kingdom, Denmark, Norway, and Canada. This population mix avoids the external validity questions raised by only using college students (Schechter et al., 2021). Data collection took place between 4 May 2018, and 15 October 2019. 14
To evaluate our hypotheses, we first produce a contingency table and compare the observed frequencies of escalation for each treatment group relative to the expected frequencies if there was no association (i.e. the null hypothesis). We classify escalation using our theory-informed coding of escalatory actions rather than the participant’s self-assessment of escalation 15 or their estimate of the likelihood of escalation. 16 Specifically, we test whether the decision to escalate is independent of the scenario treatments based on whether the actor has cyber response options and whether there was a cyber trigger to the crisis.
Table IV reports the number of response options that escalated in relation to each of the four treatments with percentages. When wargame participants had cyber response options and the scenario involved a cyber trigger, they escalated only 34% of the time. Of note, this number is below the rate of reciprocated escalation in prior studies of militarized disputes (49%). 17 The largest rate of escalation by percentage was in treatment 2, where respondents were confronted with a cyber-triggering event but lacked cyber response options. When a state faced a cyber intrusion alongside more traditional forms of escalation and lacked the ability to respond with cyber options, the participants opted to escalate more frequently (55%) than in other treatments. The lowest observed escalation level was in the treatment where the crisis did not involve a cyber trigger and participants had cyber response options. That is, participants used cyber options to respond beneath the threshold of escalation. The distribution of escalation responses across the four treatment groups was statistically significant in terms of the observed differences.
Escalation outcomes by treatment group
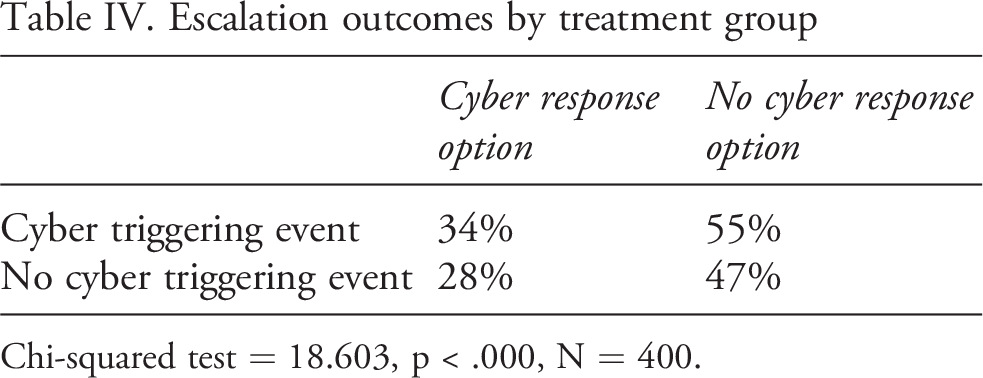
Chi-squared test = 18.603, p < .000, N = 400.
Predictors of escalation (OLS, Logit regression)
Robust standard errors in parentheses.
** p<0.01, * p<0.05, † p<0.1.
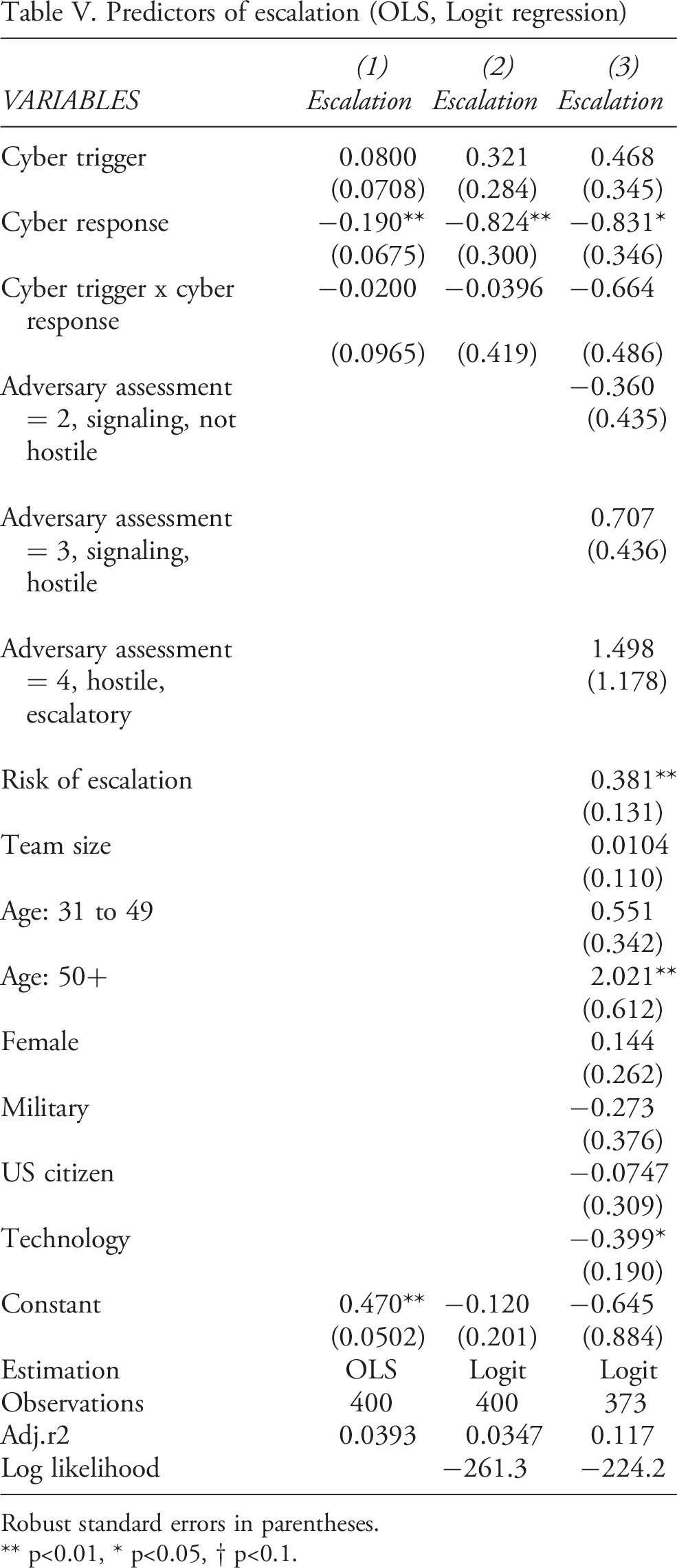
We also provide additional confirmation of treatment effects using logit regression analysis in Table V. First, we follow Gomila (2021) in reporting ordinary least squares regression for estimating Average Treatment Effects (ATEs). Model 1 shows that 47% of participants in the treatment group without cyber triggers or responses (reflected in the constant term) escalate the crisis. By comparison, escalation is reduced by 19% in treatment groups with cyber response options. Finally, we see no differences in escalation from control among groups with cyber trigger options or interaction effects between cyber trigger and response options. Model 2 provides logit coefficient estimates on the probability of escalation by treatment group. Consistent with H1, Models 1–2 indicate that treatment groups with cyber response options are less escalatory than the treatment group without cyber response options. Models 1–2 also show that the probability of escalation is reduced even when cyber responses are available for non-cyber-related triggering events, consistent with H2. Model 3 indicates that these treatment effects are robust to the inclusion of extended controls to include assessments of the adversary’s intent (hostile or not hostile), beliefs about the risk of escalation (which are positively correlated with escalatory behavior), the size of the crisis response team (a control for experimental group size effects), age (positively correlated with escalation), gender, military vs non-military participants, US vs. European citizenship, and comfort with technology (a proxy for cyber-related education) which shows that more tech-savvy respondents are less escalatory. All regression models are robust to locational fixed effects, which were not significant (see Online appendix for additional information). We also provide additional robustness checks in an Online appendix to the manuscript, including balance tests, power calculations, and estimation of treatment effects with inverse probability weighting to account for imbalances on observables across treatment arms.
Our initial analysis shows that cyber responses have a dampening effect on escalation in our wargame. Next, we consider a substitution mechanism to explain why. The substitution mechanism holds that cyber operations reduce escalation by offering an off-ramp from Incidence of escalation by treatment group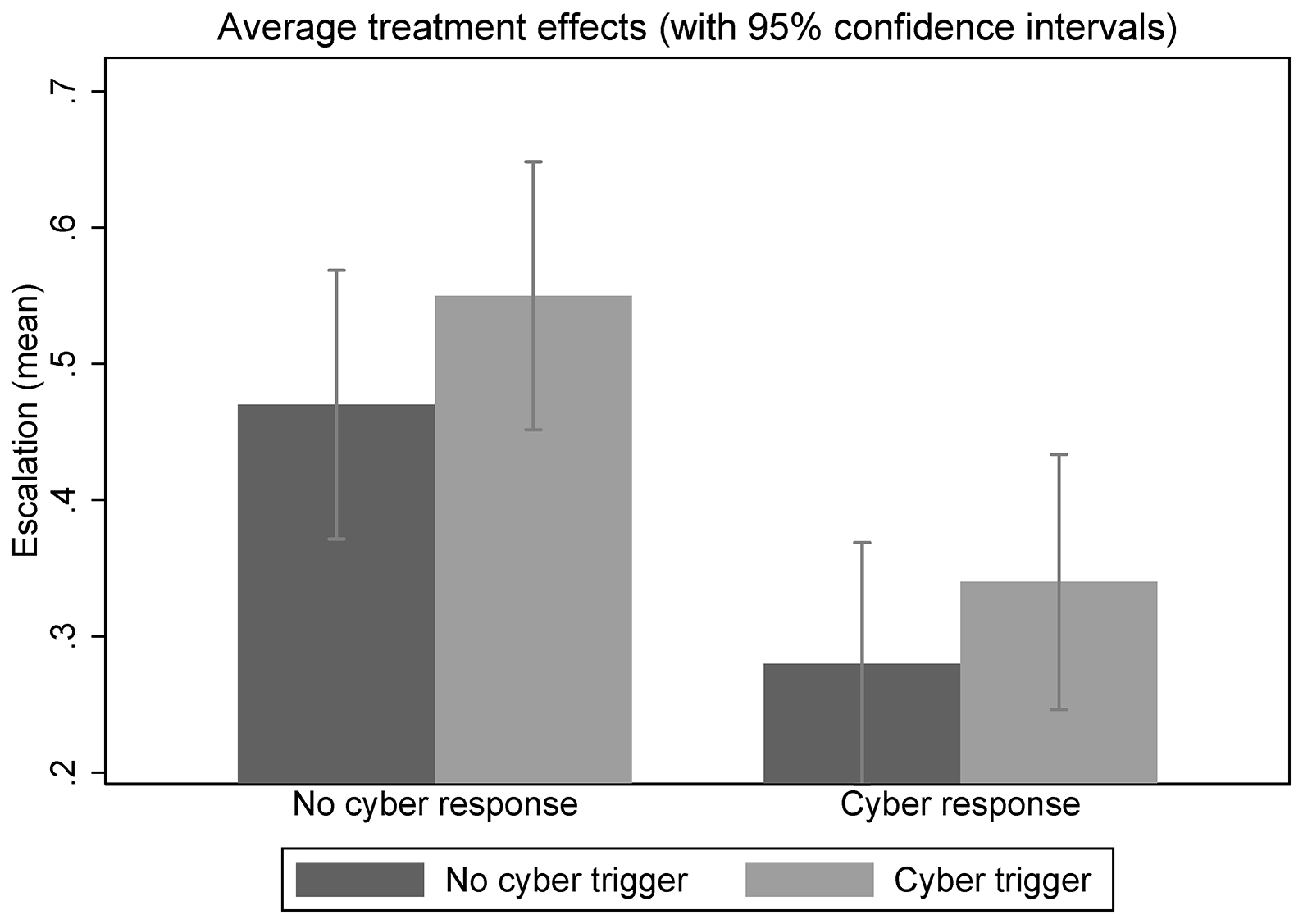
In our design, we juxtapose conventional diplomatic, intelligence, military, and economic response options alongside cyber response options. To probe for substitution versus complementarity in decision-making, we ask (1) do decision-makers actually select cyber response options when given the option? And (2) do they select cyber response options in tandem or as a replacement for conventional response options?
Figure 3 provides subgroup analysis of participant decision-making in the cyber response treatment groups (N=200) vis-à-vis the treatment groups without cyber response options (N=200). The bar graph depicts the frequency of cyber versus conventional DIME response options chosen by the two groups. Participants in the cyber response treatment groups are represented by the shaded bars while the non-cyber response groups are depicted in the white bars. First, we find that participants in the cyber response groups select those options at a rate of approximately 18–30% across DIME categories. Second, we find evidence of cyber substitution. While a plurality in the cyber response treatment groups still selects conventional response options (33–53%), it is a significant reduction from the level of conventional response options chosen by the groups without cyber options (57–85%). Within-DIME substitution is bolstered by the fact that total response options chosen remain relatively constant between the cyber and non-cyber response groups in the diplomatic and intelligence-gathering response categories. However, we may also see across-DIME substitution taking place as well. Among military response options, there is an overall rise of 10% in participants selecting military options in the cyber response option groups (67% vs 57%), suggesting that cyber provides an attractive alternative form of military engagement relative to conventional options. More decision-makers chose military response options when cyber is on the table, yet the net result is reduced escalation, consistent with a cyber off-ramp, while maintaining military engagement. Conversely, among economic response options, we observe a comparable decline in the cyber response groups (51.5% vs 60.5%), which suggests that providing cyber alternatives leads not only to cyber substitution away from conventional response options in the economic dimension but also potential shifting of response strategy into other response dimensions. Substitution mechanisms in cyber response options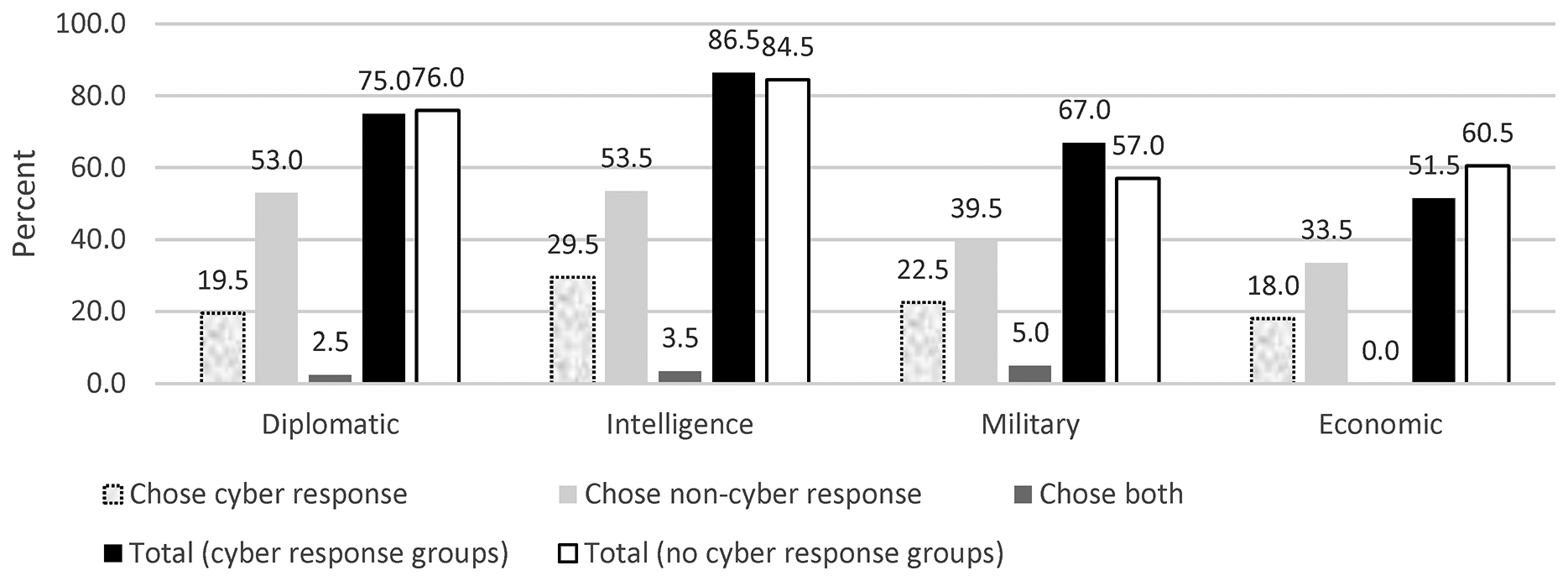
Conclusion
This research provides an overview of a cross-national wargame designed as an experiment to test how the presence of cyber capabilities alters human decision-making dynamics during crises. The results indicate that cyber response options can moderate crisis responses in scenarios involving rival states with power parity. The results also indicate that new capabilities can create uncertainty. When participants were confronted with situations involving a cyber-triggering event but lacked cyber response options, they opted to signal resolve and pursue more conventional responses. Cyber operations do affect the contours of human decision-making during international crises, mainly in ways unexpected by conventional wisdom.
These findings add to the larger literature on emergent technology and crisis behavior. They show that great power competition tends to revolve more around politics than disruptive technologies, casting doubt on scholarship that sees cyberspace as revolutionary. The findings also support the growing literature that tends to see technology not necessarily as a force multiplier: cyber operations are more defined by espionage, persistent interactions, and limited coercion (Fischerkeller et al., 2022).
Future research should unpack these results along three axes. First, what would it take for decision-makers to cross the Rubicon? That is, it appears cyber capabilities can limit escalation, but not in all cases or conditions. The key question is what conditions cause participants to engage in more risk-taking and pursue significant escalation events using cyber capabilities? While to date cyber options appear to reflect a form of sub-crisis maneuvering (Jensen, 2017; Valeriano et al., 2018), the question remains what sequence of events would cause participants to break the operative norms against escalatory strategic retaliation? Future research might focus on the covert nature of cyber triggers and responses. Covert operations, in general, are considered fickle, prone to failure, and potentially escalatory (Corke, 2008; O’Rourke, 2018; Johnson, 2022; Treverton, 1989). When exactly would cyber operations result in escalation within and across the domain?
Second, what combinations of cyber capabilities and conventional power projection moves, alongside traditional instruments of statecraft, prove the most stable signaling mechanisms in a crisis? This question requires iterating crisis interactions over multiple turns and testing different combinations. Future wargaming designs should consider further juxtaposition of cyber versus non-cyber response options to see how the disruptive technologies alter the strategic instruments employed for political violence (Brantly, 2016; Gartzke and Lindsay, 2015; Rid, 2012; Rovner, 2019). This question is especially important to disentangle from the effects of nuclear weapons. Most cyber powers are nuclear powers (Valeriano et al., 2018). As cyber capabilities proliferate, and non-nuclear states use them, will crisis stability hold?
Third, how do new actors complicate traditional state interactions in cyberspace (Vicic and Gartzke, 2024)? This question revolves around a new research agenda in cyber civil-military-commercial relations (Watts et al., 2019) and exploring how the prominent role of the private sector in cyberspace alters bargaining processes at the core of international crises. It is also critical to note that the sample under examination matters. While many prior studies focus on handy student samples, our sample was multinational, geographically dispersed, and represents a limited number of student participants. A follow-on examination with a sample of 3000 respondents facilitated by YouGov demonstrates a similar tendency for cyber restraint in exercises, but there are also cross-national differences that are important to tease out with the Russians exhibiting min-maximalist behavior (more likely to escalate and back down) while the US sample exhibits more proportional responses (Jensen and Valeriano, 2019).
The impact of disruptive technology often animates international relations scholarship. Yet, expectations of revolutionary change often run smack into the reality of empirical observation. Our contribution to this Special Issue offers further experimental evidence of the human dimension to cyber operations decision-making and reveals how advanced technology might actually reduce strategic escalation risks providing space for decision-makers to bargain during periods of conflict.
Footnotes
Replication data
Acknowledgements
We thank the anonymous reviewers and editors of this Special Issue for guidance on this manuscript. Any errors are ours alone.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
