Abstract
Traditional conceptions of state-sponsored cyber economic espionage suggest that countries with different product profiles should experience high levels of espionage between them. However, this is not what we observe empirically. Incidence of economic espionage tends to be prevalent between countries with similar product and manufacturing profiles. This suggests that we may be missing critical parts of what drives state-sponsored cyber economic espionage. To help unravel this puzzle, I develop a novel theoretical framework that proposes that because attackers seek to maximize the expected utility of stolen information, they target countries that possess similar productive capabilities as themselves. Consequently, countries with dissimilar product profiles should avoid targeting each other for espionage. I test this argument using data on states’ product complexities and cyber economic espionage for a global sample of countries in a dyadic analytical framework. The results robustly show that for any pair of countries, as the complexities of their products diverge, they become significantly less likely to aim espionage attempts at each other. This study thus contributes new insights to explain why cyber economic espionage appears restricted to only a small number of advanced economies. It also illustrates the utility of large-N dyadic approaches in studying state-sponsored cyber espionage.
Introduction
Espionage generally involves clandestine efforts by government agencies to collect protected or classified information. Information targeted is often useful in some way to furthering the state’s national security interests and dealing with threats from real or perceived adversaries (Lotrionte, 2015). Within this context, economic espionage is a particular form of espionage that targets information relevant to the state’s economy. This includes company trade secrets, proprietary software, product design blueprints, development plans, prototypes and marketing strategies. This information can be leveraged by state-owned and favoured private enterprises to boost economic competitiveness at the expense of adversaries (Wagner, 2011).
In conventional espionage, the value of information lies in its scarcity and exclusivity. This gives those who possess it a strategic advantage over those who do not, creating an incentive for the have-nots to acquire this information. We thus expect that espionage attempts flow from those that lack the requisite information to those who possess it. This is largely consistent with what we observe in practice. In military intelligence, for instance, espionage typically involves gathering information about enemy plans, capabilities and intentions that can be used to gain strategic advantages or thwart enemy actions. An example is Operation Echelon, a global surveillance programme established by the United States and some of its allies during the Cold War which involved intercepting and analysing adversary electronic communications (Webb, 2007).
This logic is often extended to economic espionage. States can leverage their innovations to develop superior goods and to dominate global markets, giving highly innovative states coercive advantage over their rivals. This gives other states a strong incentive to pursue their own innovative efforts and to engage in state-sponsored economic espionage operations to acquire proprietary information and other trade secrets (e.g. Cheung, 2018; Knickmeier, 2020).
We thus expect that countries with different product and manufacturing profiles should experience high levels of espionage between them, with spying attempts flowing from those that lack the requisite proprietary information to those who possess it. However, this is not what we observe empirically. Several studies show instead that incidence of economic espionage is most prevalent between countries with similar product profiles (e.g. Button, 2020; Glitz and Meyersson, 2020).
This puzzle has attracted some attention in the literature, with scholars positing a myriad of explanations for the observed behaviour. Gilli & Gilli (2019) for instance question the extent to which imitators can leapfrog innovation leaders via imitation. They argue that the increase in the complexity of technology has prompted a change in production systems that make imitating and replicating the performance of state-of-the-art military technology difficult. This limits the value of espionage. The limited value of espionage appears to be driving a decline in the use of espionage among some states. For instance, China, one country known for its state-sponsored economic espionage operations, appears to be steadily ramping down its economic espionage operations. Data compiled by the United States cybersecurity firm Mandiant shows that incidence of economic espionage from Chinese operatives have been on the decline since mid-2014, with the government shifting resources towards incentivizing home-grown innovation efforts, potentially in realization of the limits of imitation as a strategy for fuelling economic growth and development (Mandiant, 2016). Other scholars highlight the reproducible nature of cyber espionage tools as a potential explanation. The speed with which targets can patch up system vulnerabilities and reproduce or modify the attacker’s code potentially reduces the utility of espionage operations (Rid, 2012; Valeriano, Jensen and Maness, 2018).
While undoubtedly useful, the logic underlying these explanations relate to how the potential difficulties of economic espionage might limit who is able to spy. However, such difficulty-based constraints do not fully explain the limited incidence of economic espionage between countries because they do not address the underlying incentives that states have to engage in espionage in the first place. This suggests that we might be missing a critical part of the puzzle of what drives the limited use of economic espionage by many countries who otherwise have strong incentives to engage in the practice.
In this article, I fill in the gaps in these difficulty-based explanations by introducing a potentially overlooked contributor – the expected utility of stolen information. I contend that stolen information is most useful to a country where it can be leveraged for the immediate benefit of domestic firms and industries. As such, attackers are careful to select targets where the expected utility of stolen information is highest. As a result, targeted countries tend to be states that produce goods similar in complexity and sophistication to the attacker. Consequently, for any pair of states, those with dissimilar levels of product complexities should have little benefit from mutual espionage and should avoid targeting each other for espionage.
I test this argument using data on states’ product complexities and cyber economic espionage operations for a global sample of countries in a dyadic analytical framework over the period 2000–2020. Employing logistic and mixed-effects models in combination with specification curve analysis (SCA), the results robustly show that for any pair of countries, as the complexities of their products diverge, they become significantly less likely to aim espionage attempts at each other. This expands the range of factors thought to explain why economic espionage appears restricted to only a small number of advanced economies.
This study also illustrates the utility of using a large-N dyadic approach to study state-sponsored cyber operations. Large-N dyadic approaches offer several advantages. For one, they allow conclusions to be drawn with greater statistical certainty because the large number of dyads included enables researchers to detect small effects that may be missed in studies based on single cases or smaller samples. This is particularly useful for espionage scholars because the phenomena we study are clandestine and their effects are often subtle. Moreover, large-N dyadic approaches offer greater generalizability as the large number of dyads allow researchers to examine patterns of behaviour and relationships that are more representative of the underlying population (Diehl and Wright, 2016). This can contribute to testing the empirical validity of previous theoretical frameworks and the generation of new insights that help to advance the field.
In the sections that follow, I examine existing explanations for the puzzle of why economic espionage is restrained and why these explanations fall short. I then develop a theoretical framework where I leverage insights from the international economics and business literature to explain how considerations relating to the expected utility of stolen information potentially contribute to restricting the set of countries that engage in economic espionage. I then present the analytical framework. Results and conclusions follow that.
State-sponsored cyber economic espionage
As highlighted earlier, prior research shows that incidence of state-sponsored economic espionage is limited to a small set of countries (e.g. Button, 2020; Glitz and Meyersson, 2020). This is particularly the case when there is a strong link between the state and industrial firms. As an example, in the former Soviet Union (and now Russia), there were close links between the state and the manufacturing and industrial bases of the economy, often with very little distinction between the state apparatus and these sectors of the economy. As such, there was free flow of information between state intelligence agencies such as the KGB and the heads of various industries, particularly when it comes to stolen information that can be exploited by these industries, such as the details of contract bids by foreign firms, marketing strategies, etc. (Haynes, Klehr and Klehr, 1999; Parrish, 2001).
A similar dynamic is prevalent in France, where the state holds a significant share of the industrial base and the government is perceived to be an extension of major French corporate interests. The government has been active in helping French firms acquire proprietary information (Harris, 2017). In early 2015 for instance, Canadian security experts discovered the Snow Globe or Babar malware, which was later traced back to French intelligence agencies. The malware had the purpose of gathering proprietary information from infected computers and was detected on the systems of several Canadian entities, such as businesses, universities and research institutes (Hatamoto, 2020).
Researchers have attempted to explain the restrained use of economic espionage by appealing to the difficulties encountered in pulling off successful spying operations. For instance, to succeed, cyber espionage tools should be able to exploit flaws in the target’s computer systems while evading anti-malware and other cyber defences that the target has in place. This depends on detailed knowledge about the target systems and requires significant investment in coding expertise, time, money and other resources to pull off (Gartzke, 2013). In addition, small architectural differences in networked systems such as the structure or configuration of the targeted system can result in dramatically different outcomes for similar exploits. The success of cyber espionage operations is also significantly dependent on the organizational structure, cybersecurity standards and policies of the target and the functional behaviour of its computer systems (Jang-Jaccard and Nepal, 2014).
One issue with such difficulty-based explanations is that they cannot fully account for the restrained use of economic espionage by states, particularly if we factor in rapid advancements in computer intrusion technology and their wide availability that has significantly reduced the cost of engaging in cyber espionage operations. For instance, the increased proliferation of new types of malware designed to evade traditional security measures has made it significantly easier to infiltrate computer systems (Wangen, 2015).
These types of malware include advanced persistent threats, designed to infiltrate computer systems and remain undetected for long periods of time. The use of such automated tools and bots enables attacks to be carried out at scale and with greater speed and precision than possible using just human attackers. Artificial intelligence systems are also increasingly being leveraged by hackers to develop more sophisticated attacks that are harder to detect and defend against (Brundage et al., 2018).
Advancements in machine learning have also contributed to the effectiveness of cyber espionage. Machine learning enables attackers to analyze vast amounts of data and identify patterns and vulnerabilities that may be exploited (Ch et al., 2020). Machine learning algorithms can also be used to develop more sophisticated attacks that are harder to detect and defend against. Other technological advancements that make cyber espionage easier and more cost-effective include the growth of cloud computing and the proliferation of the Internet of Things, the network of connected devices and sensors for collecting and transmitting data over the Internet. Cloud computing allows users to access and store data over the Internet, rather than on local computers or servers. Hackers that target these cloud storage systems can conduct espionage operations at scale as they can target and gain access to large amounts of data with a single attack (Brundage et al., 2018).
Even without leveraging these advancements, countries can reduce the cost of engaging in economic espionage and increase the chances of success by hiring cyber proxies to conduct espionage operations on their behalf. This is particularly appealing for states that do not possess the necessary technical capabilities within state security agencies. Moreover, cyber proxies operate outside the bounds of the international political system, an important draw for states who may want to deny involvement in espionage operations that are discovered (Akoto, 2022).
Given the availability of advanced intrusion technology and for-hire cyber proxies, difficulty- based explanations for why states refrain from engaging in economic espionage fall short. In this article, I aim to augment existing explanations for the restrained use of economic espionage by appealing to an overlooked aspect of states’ calculus to engage in economic espionage operations – the expected utility of stolen information to the attacker.
Theoretical framework
Countries differ in terms of their ability to make profitable use of stolen information. As an example, stolen information on the latest techniques to produce solar panels is of no use to a country that is not already producing solar panels or a closely related product. This is a significant limitation because it is difficult for countries to pivot to the production of goods that they do not already have the capacity to produce. For instance, it is difficult for a country to pivot to the production of electric vehicles (even if it were to acquire trade secrets on the latest production techniques) unless it already has the necessary infrastructure to make such vehicles.
A country’s ability to make effective use of stolen information is shaped by the underlying resource endowments of its economy, which determines the pattern of specialization in terms of the goods it can produce (Deardorff, 1982). Consequently, changes in these factor endowments over time should be reflected in changes in the products a country can make. The Ricardian model from the international economics literature extends this idea, showing that differences in comparative advantage across countries is determined by technological difference between them and so changes in states’ product mix (i.e. the goods a country produces) will depend on the relative factor endowments and evolution of productivity across different products (Davis, 1995).
Furthermore, Hidalgo et al. (2007) show that over time, countries tend to develop comparative advantage preferentially in goods related to those that they already produce. They attribute this to the imperfect substitutability of human capital in the production of specific goods. Because of this, the labour capabilities required to produce a good cannot be perfectly substituted in the production of another good. Consequently, states that want to expand the range of goods that they produce are limited to expanding to related goods. Their model is like one by Jovanovic & Nyarko (1998) who develop a model of individual-level experiential learning. In their model, learning by doing and technological advancements provides agents with new knowledge that improves their productivity. However, gains in this dimension are limited since agents can only profitably apply this new knowledge to the production of goods that use a similar knowledge base.
Given these limitations, attackers would want to aim espionage attempts where the stolen information is likely to be most beneficial to their own productive efforts. But which targets are most likely to yield such useful information? The international business literature provides some insights in this regard. Evidence shows that espionage attempts are frequently aimed at the most innovative firms (Crass et al., 2019; Ettredge, Guo and Li, 2018). This suggests that operatives look for signals of innovation embedded in the products that targeted entities produce. Such information is often not patented and thus not in the public domain. For example, aerospace company Lockheed Martin profits from trade secrets relating to technical details of its Integrated Lift Fan Propulsion System used in the production of F-35 fighter jets. Firms prefer to rely on trade secret protection instead of patenting because patents must be publicly disclosed while trade secrets can remain confidential (Crass et al., 2019; Png, 2017).
Companies that produce innovative products using trade secrets can thus dominate the market and realize immense profits as a result. Unsurprisingly, this makes such companies attractive targets for espionage. Ettredge, Guo & Li (2018) for instance, study the association between firms’ possession of trade secrets and their propensity to be targeted for cyber espionage. Specifically, they examine mentions of the term “trade secrets” in Form 10-K fillings with the United States Securities and Exchange Commission and then analyze which firms are subsequently targeted with cyber espionage attempts. They find that firms that possess trade secrets are significantly more likely to experience espionage attempts. Extending this logic to the state level, we can surmise that countries that concentrate a lot of innovative firms are more likely to be targeted for economic espionage.
The above considerations thus suggest that countries that produce goods similar or related to those of the attacker are most likely to be targeted. 1 Consequently, I contend that for any pair of states, countries that produce similarly sophisticated goods should have a higher expected utility from mutual espionage since they possess the necessary productive resources, skills and infrastructure to profitably leverage that information for immediate advantage. In the same way, countries with dissimilar levels of product sophistication should have little benefit from mutual espionage and so should largely avoid targeting each other for espionage.
Analytical framework
I test the argument that attackers aim espionage operations at countries that produce goods of similar sophistication and complexity as their own since this offers the highest expected utility that stolen information can be profitably leveraged. In this regard, I make the case that for any pair of countries, as their product complexities diverge, they become less likely to aim espionage attempts at each other. For the empirical analysis, I draw on a global sample of states in a non-directed dyad-year analytical framework over the period 2000–2020. 2 In selecting the sample of countries for the analysis, I am guided by the existing literature which shows that espionage activity tends to be most common among geopolitical rivals (Valeriano and Maness, 2014). Such rivals often share a common border (e.g. North and South Korea, India and Pakistan) or involve a major power (e.g. China, Russia, United States). Consequently, I focus the analysis on politically relevant dyads, defined as those that share a contiguous land border or dyads involving at least one major power (Lemke and Reed, 2001). Data on politically relevant dyads come from Miller (2022).
Economic espionage
Data on state-sponsored cyber economic espionage come from the Dyadic Cyber Incident and Campaign Dataset (DCID) version 2.0 compiled by Maness et al. (2023). The DCID dataset identifies state-sponsored cyber operations based on published news and cybersecurity reports about the incidents, particularly if the tools, procedures and techniques used conform to what is known about a state’s prior espionage operations.
Economic espionage operations are typically directed towards commercial firms, think tanks and research institutes. As such, I focus on attacks aimed at these kinds of institutions. Commercial firms usually invest significant resources in research and development to create new products and improve manufacturing processes that generates trade secrets, patents and other valuable information that can be highly valuable to competitors, foreign governments, or criminal organizations. Similarly, think tanks and research institutes conduct extensive research in various fields such as science, technology and medicine and they frequently produce academic articles and scientific reports that can have significant commercial or strategic value. Moreover, these entities tend to have weaker cybersecurity measures than government agencies, making them easier targets for economic espionage.
They may also have a wider network of international partners and collaborators, making it easier for foreign agents to infiltrate their organizations and obtain sensitive information.
To code incidents of economic espionage, I examine the description of each cyber incident captured in the DCID dataset. I create a dichotomous variable – cyber economic espionage – coded 1 (0 otherwise) for each cyber incident aimed at a commercial firm, think tank or research institute (including university affiliated ones) that involve the stealing of confidential information such as trade secrets, technical reports and customer data.
One general caveat to note – studying state-sponsored cyber economic espionage poses some unique challenges. For one, espionage is typically conducted clandestinely, with the perpetrators often going to great lengths to prevent their actions from being discovered. States do not typically reveal economic espionage operations against other states and have strong incentives to deny any operations that do come to light as they seek to mitigate the foreign policy and international relations fallout. Moreover, good cyber espionage operations are hard to detect and even inept attempts that are discovered are frequently difficult to attribute to any specific actor. It is often not immediately obvious who is behind espionage attempts or the origin of attacks.
Most cyber espionage operations are undetectable while they are in progress, coming to light weeks, months and even years after the attack. Furthermore, victims, particularly private companies with a stock market presence are frequently reluctant to disclose that they have been attacked given the stock market implications of such disclosures and the public relations nightmare that often follows (Ettredge, Guo and Li, 2018). For these reasons, incidents of state-sponsored cyber economic espionage operations (as captured by the DCID or any comparable current or future dataset) are almost certainly under- counted. This could introduce uncertain biases into the analysis so the results should be interpreted with these limitations in mind.
Product complexity
My theoretical framework suggests that countries that possess proprietary information and other trade secrets should be able to leverage this information to give them a market competitive advantage over other states. Within the context of market competition, they should be able to produce and export relatively complex products that very few other countries are able to match. In the same vein, relatively unsophisticated economies are mainly able to produce common goods that most other countries also manufacture. Since the ability to produce highly complex products is dependent on the quality and quantity of the proprietary information they possess, dyadic differences in the complexity of goods and services produced should closely approximate differences between the quality and quantity of proprietary information and other trade secrets between the states. Within this framework, I capture information differences between states by examining differences in the complexity of their produced goods and services.
To capture the complexity and sophistication of a country’s products, I draw on the Economic Complexity Index (ECI) from Harvard’s Atlas of Economic Complexity (Hidalgo and Hausmann, 2009; Hausmann et al., 2014; Observatory of Economic Complexity, 2019). The ECI provides a measure of the diversity of a country’s products while adjusting for the ubiquity of those products (the number of other countries that also produce those goods). 3 Two countries with the same ECI score thus produce goods of similar complexity and sophistication. 4 As per our theoretical framework, mutual espionage should be beneficial to such states. For the analysis, I create a variable – product complexity differential – that captures the absolute difference between the ECI scores of the dyad for the relevant year. If my theoretical propositions are correct, increases in this differential should be negatively correlated with economic espionage incidents between the pair.
Controls
I include a range of control variables. Countries are more likely to engage in espionage when they are involved in a militarized interstate dispute (Valeriano and Maness, 2014). In such cases, cyber economic espionage may just be part of a broader effort to gather intelligence on adversaries. To account for this, I include a dichotomous variable coded 1 (0 otherwise) for years in which either member of the dyad is engaged in an interstate militarized conflict. Conflict data comes from the Uppsala Conflict Data Program/Peace Research Institute Oslo Armed Conflict Dataset (Gleditsch et al., 2002; Pettersson, Högbladh and Öberg, 2019). I also account for the existence of a land border between the pair. Data on border contiguity come from Stinnett et al. (2002).
Furthermore, I account for the effect of differences in dyadic regime type because autocratic dyads might have different baseline propensities for espionage relative to democratic dyads (Valeriano and Maness, 2014). I create a variable – Democracy – a product of the electoral competitiveness index for both countries from the Varieties of Democracy (V-Dem) dataset (Lindberg et al., 2014). The electoral competitiveness index measures the degree of responsiveness and accountability between leaders and citizens as reflected by the competitiveness of elections. The score is higher for democratic dyads. I also include a measure for the combined fraction of the population in each country that has access to the internet. Data for this variable – Internet access – come from the World Bank’s World Development Indicators database (World Bank, 2020). The Online appendix has descriptive statistics for selected variables.
Analysis
For the estimation, I draw on a variety of methodological approaches. Panel logistic regression is the baseline estimation model but the time series–cross-sectional structure of the dataset means that dyad-year observations are likely interdependent. To examine if this interdependence is consequential, I estimate mixed-effects models that include year fixed and random effects to account for temporal trends in dyadic espionage propensity. This is important because factors such as technological advancements and the evolving dynamics of interstate rivalries may make economic espionage against certain targets more likely in some years relative to others. The mixed-effects models help account for such tendencies and help capture the effect of year-specific omitted variables.
Product complexity and cyber economic espionage
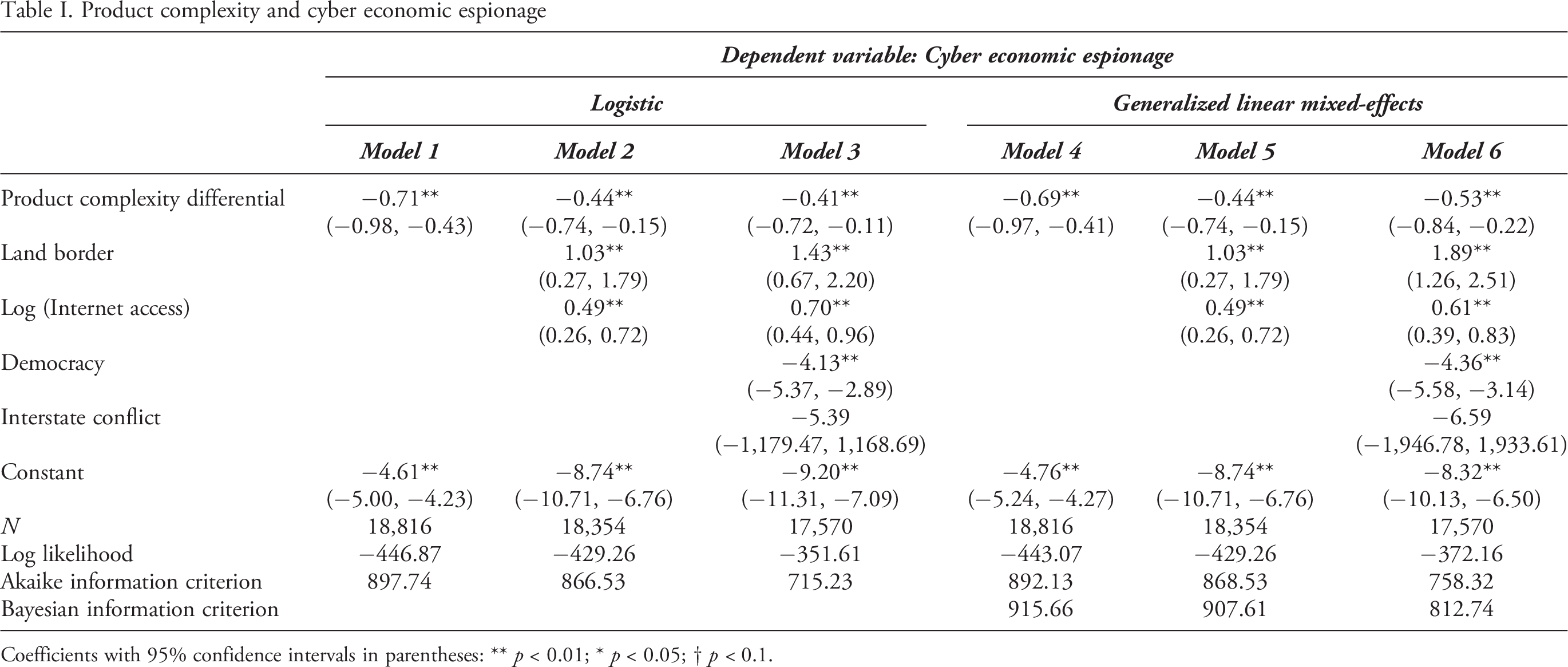
Coefficients with 95% confidence intervals in parentheses: ** p < 0.01; * p < 0.05; † p < 0.1.
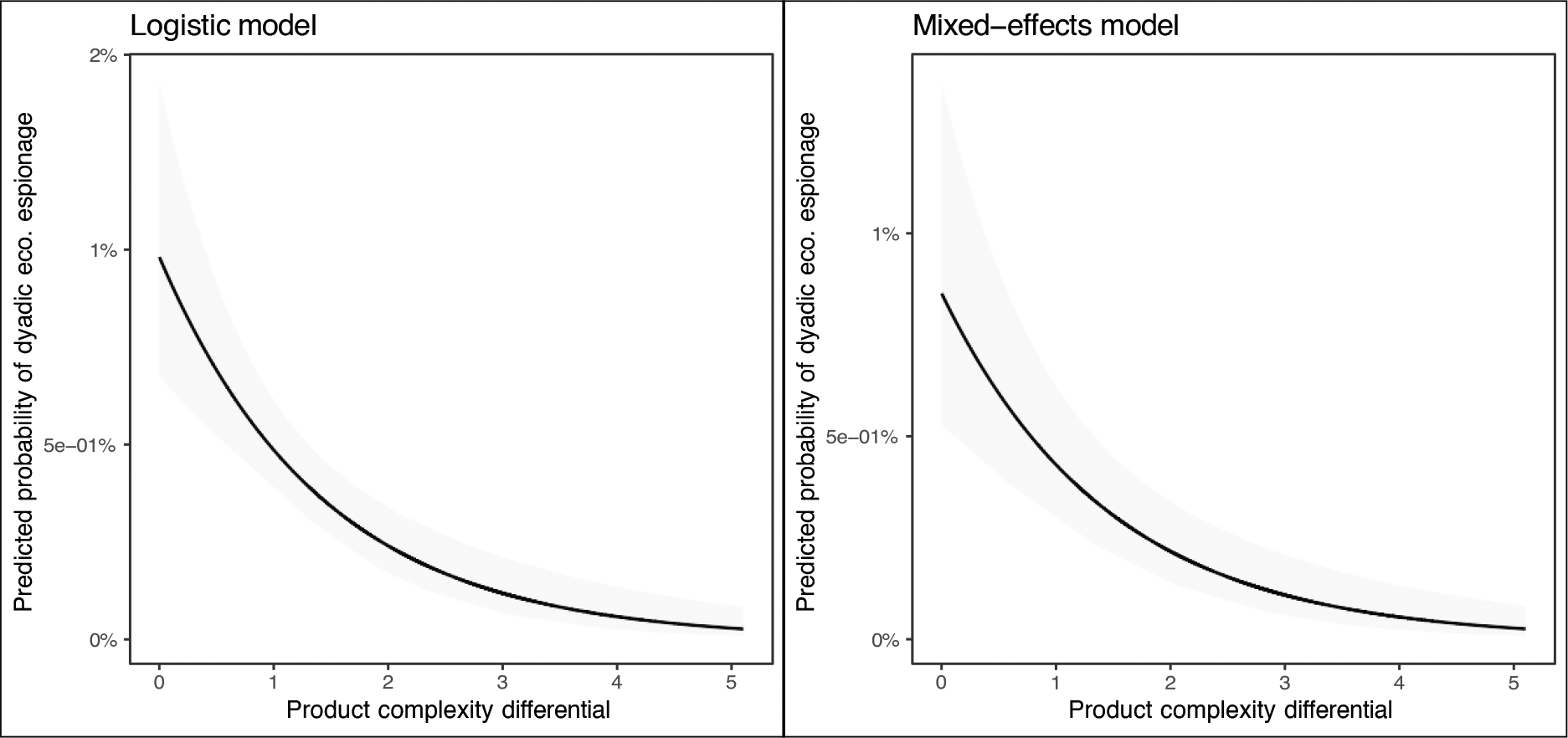
Substantive effects of increased product complexity differences on dyadic cyber espionage
Results
I start by examining how product complexity differences affects the probability of dyadic economic espionage. The results of this analysis are presented in Table I. I estimate six different specifications. Models 1 - 3 are logistic while Models 4 - 6 are mixed-effects models.
Models 1 and 4 show the baseline effect of the complexity differential on espionage. In line with our theoretical expectations, the results show that higher dyadic differences in product complexity are associated with a significantly lower probability of dyadic economic espionage. In Models 2 and 5, I add controls for land border contiguity and dyadic Internet access (logged). The effect of the complexity differential remains negative and significant.
In Models 3 and 6, I add additional controls for dyadic democracy and interstate conflict. The complexity differential maintains its significant negative effect. Overall, the analysis robustly supports my assertions that increased product complexity differences are associated with fewer incidents of dyadic cyber economic espionage. In terms of the effects of the controls, contiguity and dyadic Internet access increase economic espionage while democratic dyads tend to be associated with fewer espionage incidents. Similarly, ongoing interstate conflict is negatively associated with cyber economic espionage, although this effect does not rise to conventional levels of statistical significance.
Given the unique position of the United States, as a prominent target for espionage attempts, I repeat the analysis presented in Table I but this time, I eliminate all dyads that involve the United States to see if the results remain robust. This is presented in the Online appendix (Table III). Even with the United States removed from the sample of countries, the negative effect of the product complexity differential remains robust across all the estimated models. Indeed, the negative effect of the product complexity differential becomes even stronger in the sample that does not contain the United States.
To get a sense of the substantive effect of product complexity differences, I plot the base line results from Models 1 (left panel) and 3 (right panel) in Figure 1. The horizontal axis tracks increasing product complexity differences while the vertical axis tracks the predicted probability of dyadic economic espionage. The shaded region around the curves represents the 95% confidence interval. The results show that dyadic espionage steadily decreases as product complexity differences increase.
Next, I examine how product complexity differences affect dyadic economic espionage using SCA. Recall that
Specification curve analysis (SCA) examining product complexity differences and dyadic economic espionage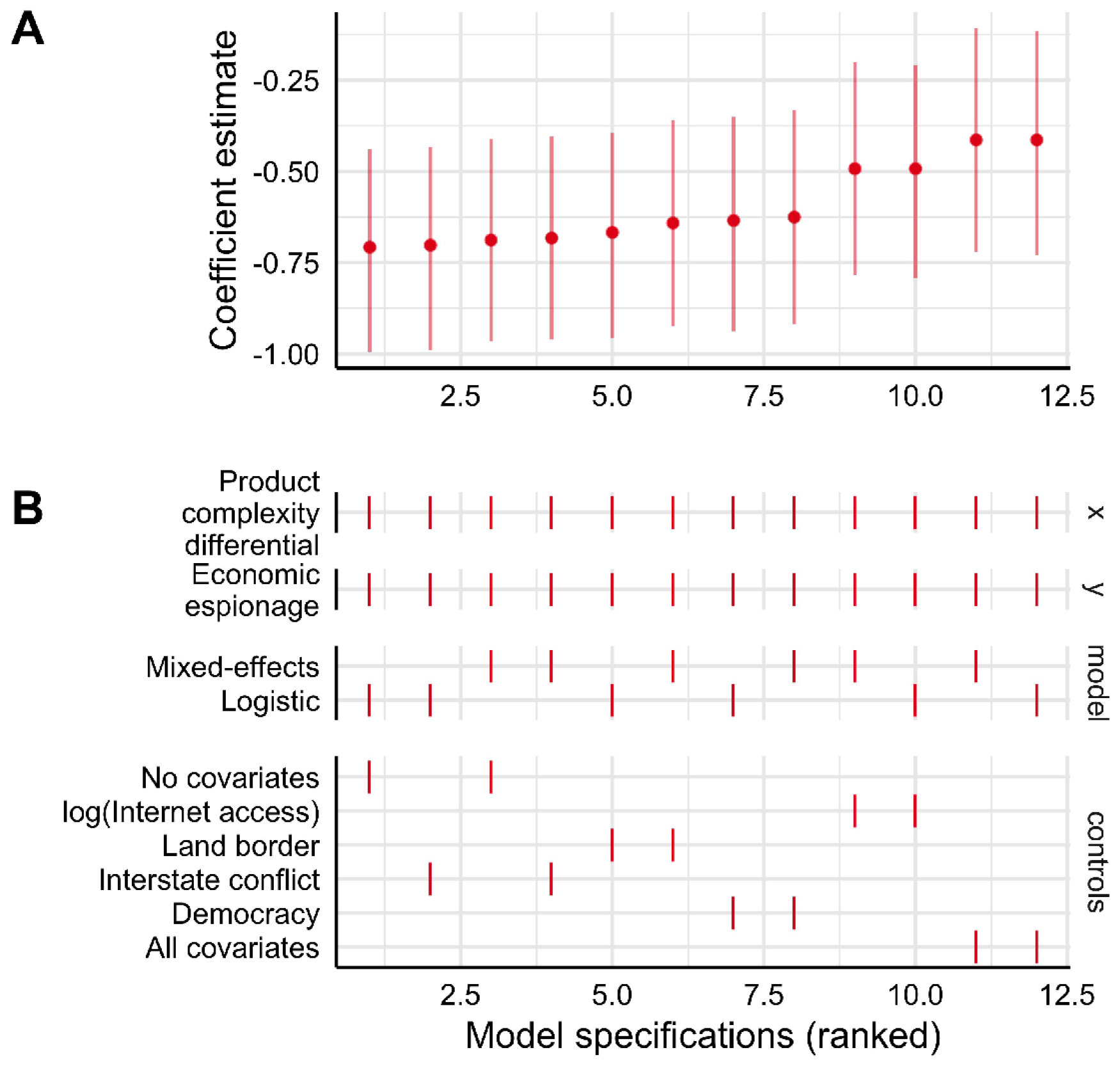
The top panel (Panel A) of Figure 2 shows the beta estimates (and 95% confidence intervals) from the estimated regression coefficients across the different specifications. The specifications are ordered from least to greatest based on the magnitude of estimated coefficients. Significant negative associations are coloured red. Estimated coefficients for all models are less than 0, indicating a robust negative relationship between product complexity differences and dyadic economic espionage. Estimates from all the specifications are red, indicating significant negative estimates (i.e. our alphas are less than 0.05 and the 95% confidence interval excludes 0).
The bottom panel (Panel B) presents the details for each specification. The colour scheme is the same as in Panel A – red for significant estimates. Details for each specification can be obtained by following down vertically from Panel A to Panel B. On the horizontal lines in Panel B, a vertical tick (|) indicates that the option (labelled on the y-axis) was selected for the corresponding estimate in Panel A. Analogously, a blank space on the horizontal line in Panel B means that option was not selected for the corresponding estimate in Panel A.
The ticks on the product complexity differential line in Panel B for example indicate that the variable was included in the regression for the corresponding estimates in Panel A. The Y section of Panel B (labelled on the right) indicate the dependent variable for the regression. The model section of the plot indicates which analytical model was used for the specification while the controls section indicates which controls were included.
Consistent with our theoretical expectations, the analysis indicates that product complexity differential has a robustly significant negative effect on economic espionage.
Conclusion
In this article, I seek to contribute to efforts to unravel the puzzle of why the use of cyber economic espionage is restricted by highlighting one factor that directly acts on the incentives attackers have to engage in economic espionage. I argue that attackers pick their targets to maximize the expected utility of stolen proprietary information. I hypothesize that for any pair of states, countries that produce similarly complex goods should have a higher expected utility from mutual espionage since they possess the necessary productive resources, skills and infrastructure to profitably leverage that information for immediate advantage. Stated differently, countries with dissimilar levels of product complexities should have little benefit from mutual espionage and so should largely avoid targeting each other for espionage. I test this proposition for a global sample of countries in a dyadic analytical framework and robustly show that dyadic economic espionage decreases as states’ product complexities diverge.
The results have important implications. For one, by demonstrating the importance of expected utility of stolen information in driving economic espionage, this article expands the set of factors thought to motivate state-sponsored cyber espionage operations. This broadens our collective understanding of the dynamics of interstate cyber espionage and enlarges possible options for countering the practice. Analytically, this article demonstrates the utility of using a large cross-national dyadic-analytic approach to study interstate cyber activity. This is an important complement to the more-established descriptive, case-study and other qualitative approaches typically used to study state-sponsored cyber activity (Shandler and Canetti, 2024).
Moreover, while this article suggests an intrinsic self-interest behind cyber espionage, Kostyuk (2024), which forms a part of this special issue, elucidates that alliances and collaborations in cybersecurity emerge not just from threats but also a mutual enhancement of overall alliance security. The synergy between both articles implies that as states optimize their cyber-espionage strategies, they may simultaneously be sowing and nurturing alliances that can safeguard them against potential retaliations and bolster their military cyber capacities.
This article underscores the utility of conceptualizing state-sponsored economic espionage as an extension of interstate intelligence contests (Rovner, 2019). Whereas Cold War-era geopolitical rivalry was waged primarily on military, political and ideological grounds, recent interstate rivalry is increasingly playing out in the tightly networked global economy. In this rapidly evolving setting, states are increasingly realizing that failure to accelerate economic growth and development risks dooming the state to various hardships and possible loss of prestige and power on the global stage. States are thus increasingly playing strong roles in administering and supervising the accumulation or ownership of capital. National and regional development banks, sovereign wealth funds and various state-owned enterprises are becoming leading vehicles through which governments exert influence in the global economy (Alami et al., 2022).
Within this context, state-sponsored cyber economic espionage has taken on new significance. Conceptualizing cyber economic espionage as an intelligence contest draws sharp attention to the strategic and economic dimensions of cyber conflict and underscores the importance of understanding the motivations and incentives of state actors in this arena. This enables researchers to build a more comprehensive understanding of the growing challenge of state-sponsored cyber activity and develop more effective strategies for mitigating its impact on the global economy.
This article opens several new avenues for future research. My exploration of the dynamics involved in the strategic targeting of state-sponsored cyber economic espionage offers a valuable springboard into exploring the psychological and societal impacts of cyber-attacks. For instance, Shandler, Gross & Canetti (2023) underscore the significant psychological distress caused by cyber-attacks, equating it to the impact of conventional political violence. The linkage between the tactical espionage activities discussed in this article and the psychological fallout explored by Shandler, Gross & Canetti (2023) opens an avenue for contemplating the ethical and humanitarian considerations of cyber espionage.
Furthermore, my findings on the strategic nature of cyber espionage complements the findings of Arsenault et al. (forthcoming), showing the public’s generally supportive stance towards surveillance policies after cyber-attacks. This highlights a gap in the field’s understanding of how states might balance their cyber espionage activities with domestic and international policy considerations. Future research should thus explore how states navigate the dichotomy of practising cyber espionage while also safeguarding their own cyber domains.
Future scholars could also explore how the effect of product complexity varies by industry. Is state-sponsored economic espionage less or more likely if product complexities deepen (i.e. if countries incrementally innovate in a few products) as opposed to widening product complexities (i.e. countries innovate across several products)? Researchers might also investigate how espionage propensities differ relative to the ease with which countries can outsource their cyber operations to non-state cyber proxies. Countries home to several hacker groups may be more likely to outsource as opposed to those where such hacker groups are scarce, with important implications for target selection. Cross-national analyses of these under-explored dynamics of interstate cyber espionage may provide further groundbreaking insights.
Footnotes
Replication data
The dataset and replication files, along with the Online appendix, are available at http://www.prio.org/jpr/datasets and the author’s website ![]()
Acknowledgements
My appreciation to the editors, anonymous referees, and participants at the ISSS-IS Annual Conference 2019 (Denver) and colleagues at Fordham University for helpful comments.
Funding
The author received no financial support for the research, authorship, and/or publication of this article.
