Abstract
The ability of sensor nodes to enter a low power sleep mode is very useful for extending network
longevity. We show how adversary nodes can exploit clustering algorithms to ensure their selection
as cluster heads for the purpose of launching attacks that prevent victim nodes from sleeping. We
present two such attacks: the
Introduction
Power management is a major research issue in sensor networks, given that sensor nodes are constrained to operate upon limited battery supplies. In general, the total energy consumption of a sensor node can be categorized into the following three groups: 1) energy spent on computations, 2) energy used to communicate, and 3) energy spent as a result of the node's sleeping patterns. In this paper we focus on the ability of sensor nodes to enter a low power sleep mode for the purpose of extending the longevity of the network. It is widely accepted that this is an important issue, as sensor nodes spend most of their time in sleep mode, allowing the overall lifetime of the node to be greatly extended [3, 8, 11, 17, 28, 30].
The ability of sensor nodes to enter a sleep mode becomes a serious concern for sensor networks
deployed in
We present two attacks that prevent victim nodes from sleeping: the
To further analyze the sleep deprivation attack, we have used a clustering based target tracking network as the basis for our analytical model. It was the decision of the authors to utilize a specific application rather than a more general model in order to grant the reader further insight into the mechanisms of the sleep deprivation attack. Note that while our analysis was done based upon a particular implementation of target tracking, our results are readily applicable to any clustering based sensor network application. We show that for one set of network parameters, an adversary can double the power consumption of a 400 node network with as few as 20 compromised nodes. Further, we show that a single adversary node can simultaneously attack as many as 150 victims and still outlive its victims.
Given the detrimental effect of the sleep deprivation attack, we have analyzed three separate
defense mechanisms to mitigate this attack: the
The remainder of this article is organized as follows. In Section 2 we discuss related works. In Section 3 we introduce the framework used to perform our analysis. In Section 4 we compare the barrage attack and the sleep deprivation attack. In Section 5 we further analyze the sleep deprivation attack and in Section 6 we discuss methods to mitigate this attack. In Section 7 we make our conclusions.
Related Work
Sleep Deprivation Attack
The idea of the
The work by Krishnaswami is one of the few works that has attempted to quantify the impact of sleep deprivation attacks on energy-constrained devices [22]. The approach used by Krishnaswami consisted of measuring the difference between the average power consumption of laptops and PDAs while the devices were idle (but not in sleep mode) and when the devices were under attack. We find Krishnaswami's approach to be overly simplistic in how devices were attacked. The adversary gives the victim a task that is specifically designed to burn inordinately large amounts of energy. Such an attack could be easily detected given that sensor nodes are by necessity, very diligent about their power management. We claim that a much more difficult to detect attack would be to have the adversary focus on keeping the victim out sleep mode, rather than try to have the victim actively processing.
Cluster Head Selection
In sensor networks, clustering is used to organize sensor nodes into groups based in part on
their physical proximity [8]. One of the
nodes in the cluster is delegated the task of being the cluster head. The main benefit of clustering
is that it enables
In the clustering algorithm proposed in [10], clusters are formed by having each sensor node wait a random amount of time. If a node has not had the opportunity to join a cluster after this random amount of time, then it can declare itself to be a cluster head and subsequently start soliciting neighboring nodes to join its cluster. To maintain the cluster, the cluster head will select its own successor. We foresee two vulnerabilities with this approach. First, during cluster formation, an adversary could ensure its selection as cluster head by immediately soliciting other nodes to join its cluster. Second, once an adversary node has been selected as cluster head, it can remain cluster head indefinitely by never selecting a successor. Consequently, this approach readily allows an adversary to launch a sleep deprivation attack.
In [1], each node declares itself a
cluster head with a probability
There are many other distributed clustering algorithms and sensor network applications that rely upon clustering (e.g. [1, 2, 12, 14–16, 19]), each of which assumes that participating nodes will act honestly. Thus, an adversary can exploit each of these algorithms to ensure its selection as cluster head. Given that clustering is a widely used algorithm, it is crucial to make it secure.
Target Tracking
For didactic purpose, we pose our discussion of the sleep deprivation attack within the context of a sensor network executing a distributed clustering target tracking application; however, our results are more generally applicable to any algorithm that relies upon clustering.
Target tracking research has focused on such issues as increasing the fidelity of sensor data, reducing redundant data, and reducing energy consumption. Since many of these algorithms [13, 25, 27, 31, 37–39] rely on a trusted cluster head, they are all susceptible to the sleep deprivation attack.
System Modelling
Model Assumptions
Node and Network Characteristics
We consider the placement of sensor nodes to be spread uniformly at random throughout a square region. The sensor nodes operate on non-renewable batteries; once a node exhausts its battery it is considered to be dead. To preserve their battery power, sensor nodes will cycle in and out of a low-power sleep state.
We assume the presence of a publish/subscribe routing protocol [18, 20]. A publish/subscribe protocol has two network primitives, a
We assume a homogeneous network, where a cluster head is identical to any other node in the cluster in terms of capacity and resources. For simplicity we shall assume that nodes within the same cluster can communicate directly. This assumption could be relaxed by allowing multihop communication.
Security Assumption and Attack Model
We assume that sensor nodes do not have significant tamper resistance. Thus, an adversary is capable of compromising sensor nodes [8, 9, 36]. That is, the adversary can obtain data, keys, and the code inside compromised nodes. To launch attacks, the adversary reprograms the compromised nodes with malicious code and then redeploys them into the network. Compromised sensor nodes may launch attacks in different layers in the protocol stack, e.g., channel jamming in the physical layers [36], disrupting the collaboration of sensor nodes in the MAC layer protocol [7, 23, 29], attacking the routing protocol [21], jeopardizing the localization service [6, 24], or the sensor data [34]. Due to the diversity and novelty of attacks, no one-for-all solution exists. All of the aforementioned attacks have been addressed separately. As such, although compromised nodes (including cluster heads) may launch various attacks, in this work we limit our focus to identifying, analyzing, and defending against the attacks that specifically target the network's power management protocols.
We assume each sensor node is assigned a unique ID prior to deployment. Further, sensor nodes
cannot impersonate uncompromised nodes. Preventing impersonation could be accomplished by requiring
every node to authenticate its messages using pairwise keys shared with receiver nodes [26, 40]. This assumption ensures that a compromised node can only
submit a single
We consider the placement of adversary nodes to be uniformly random; this reflects the
adversary's desire to spread its nodes in order to maximize their impact. In this article the
terms
Sensor Node States
To help quantify the impact of an adversary attack we have partitioned the nonadversary sensor
nodes into three separate states:
Nonadversary Node State Space

Nonadversary Node State Space

Similarly, we have partitioned the adversary nodes into two states:
Adversary Node State Space

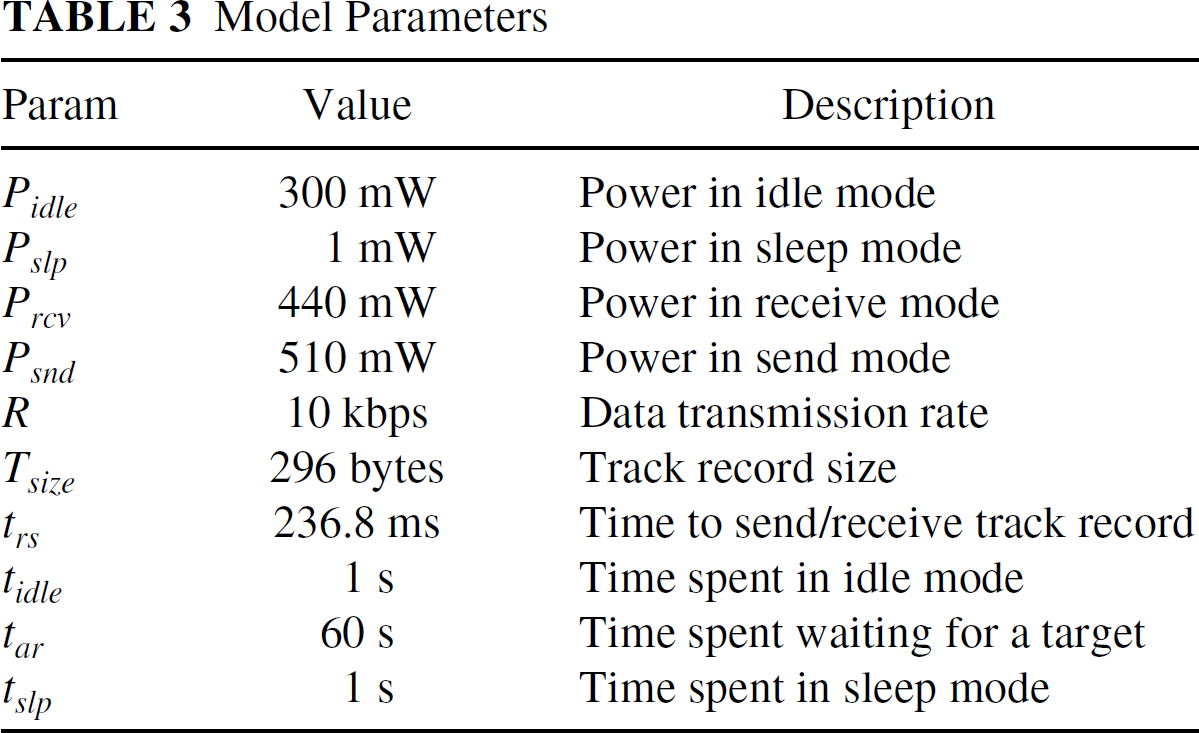
To make our analysis realistic we have used values taken from actual sensor node specifications
as seen in Table 3. We were able to
obtain actual values for power, data rate [8], and packet size [5]. Given
symmetric upload and download speeds for each link, we derived
Model Parameters
In Fig. 1 we illustrate what we consider
normal sensor node behavior when no tracking is occuring. A sensor node alternates between sleep
mode for
In Fig. 2 we illustrate the behavior
that a sensor node would exhibit upon receiving a single track record (represented pictorially by
“TR” in the figure). Initially the sensor node is alternating between sleep and idle
states, until its idle state is cut short by receipt of a track record. After

Timing diagram of normal node behavior when no tracking is occurring.

Timing diagram of normal node behavior after receiving track record.

Timing diagram of node under sleep deprivation attack.
Figure 3 illustrates a sensor node being
victimized by a sleep deprivation attack. The attacker sends the victim a track record every
Figure 4 shows a sensor node that is
under a barrage attack. Notice that the adversary sends the victim track records as rapidly as
possible (i.e., every

Timing diagram of node under barrage attack.
In this section we explain the tradeoffs between the sleep deprivation attack and the barrage attack. Further, we explain why the sleep deprivation attack would be the preferable method of attack from the perspective of the attacker.
In both the sleep deprivation attack and the barrage attack the victim will never enter its low
power sleep mode. The difference between the two attacks is that the victim of a barrage attack will
be actively performing work, whereas the victim of a sleep deprivation attack will, for the most
part, remain idle. In this section we investigate the difference between these two attacks based
upon the following:
Power Consumption of Victim
Consider the following scenario. A particular sensor node cycles in and out of its low power
sleep mode. The proportion of time that the sensor node is asleep versus awake is denoted by the
variable 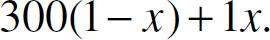
Thus this node spends 1 mw of power when
Now consider if this same node was victimized by a sleep deprivation attack or a barrage attack.
In the sleep deprivation attack, the adversary will interact with the sensor node intermittently so
that it will never go to sleep, thus the victim will spend an average of 300 mW of power.
Alternatively, if the adversary was to utilize a barrage attack, the victim will be constantly
receiving messages, causing it to spend 440 mW of power. Clearly the victim of a sleep deprivation
attack spends slightly less power than the victim of a barrage attack. It is also clear that the
relative impact of either attack is directly proportional to
An energy draining attack must remain undetected for as long as possible in order to waste a maximum amount of energy. An easily detected attack allows the victim to rapidly take remedial action, such as ignoring the requests of a detected attacker, before the attack can cause significant damage.
We speculate that the sleep deprivation attack would be much more difficult to detect than the barrage attack based on the observation that it generates messages at relatively infrequent rate. Using the parameters in Table 3, the barrage attack requires 254 messages to be sent every minute, whereas the sleep deprivation attack only requires a single message to be sent.
Energy Required of Attacker
Since the adversary nodes are compromised sensor nodes, they would be more likely to perform an attack that can cause a lot of damage without requiring a lot of energy to perform.
In a barrage attack the adversary has to transmit a network message every
Sleep Deprivation Attack
In Section 4 we showed that the sleep deprivation attack is a serious threat to a sensor network given that it nullifies any energy savings that would have been obtained by the victim's low power sleep mode. In this section we illustrate how an adversary can utilize the security vulnerabilities inherent to distributed cluster formation for the purpose of launching a sleep deprivation attack. We show that the sleep deprivation attack can as much as double the overall power consumption of a 400 node network. Further, we find that this can be accomplished with as few as 20 adversary nodes.
To quantify the impact of this attack we measure the average node's power consumption. This is a useful metric because it measures the network-wide impact of the adversary's attack. As a point of clarification, only the power consumption of non-adversary nodes will be measured in this metric.
Derivation of Model
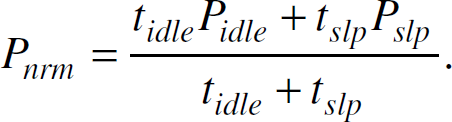
We now derive the equations that we have used to analyze the impact of the sleep deprivation attack.
Probability of Subscribing to an Adversary Node
Using a geometric argument, the probability that a sensor node will be subscribed to an adversary
cluster head, given that each node is deployed in a square region of length 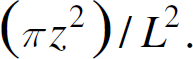
The complement of this equation gives the probability that a sensor node is not subscribed to a
particular adversary node. Given 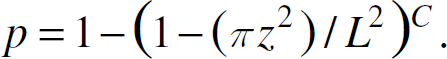
Note that this analysis will be slightly skewed due to fringe effects. Nodes on the edges of the network are less likely to be in contact with a adversary cluster head. However, only for small networks will these fringe effects be substantial, and thus we shall ignore their effects in our analysis.
To determine the average node's power consumption we have partitioned sensor nodes into two groups: those that are subscribed to adversary cluster heads and those that are not.
Nodes that are not subscribed to an adversary cluster head alternate between the idle state for
Nodes that are subscribed to an adversary cluster head alternate between an extended idle state
for 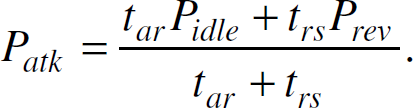
Utilizing the equations for 
Assume each adversary node goes through two states: first it sends out a track record to each of
its subscribed nodes and then it sleeps. Adversary nodes send these messages as rapidly as possible
in order to maximize sleep time. This is modeled by each adversary node sending 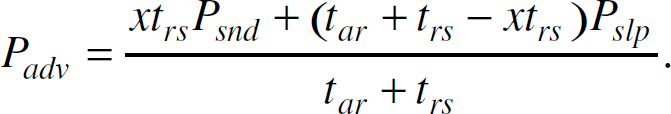
Figure 5 illustrates the effect of
malicious nodes on a network containing 400 legitimate nodes for different subscription radii (i.e.,

Effect of subscription radius in sleep deprivation attack.
To show that the attack is viable for an adversary to perform, we utilize the equation for

Energy required for attacker to launch attack upon differing numbers of victims.
We have shown that the sleep deprivation attack greatly increases the sensor network's power consumption without requiring excessive power to be consumed by the adversary. To launch this attack, the adversary nodes must become cluster heads, which we have shown to be exceptionally easy. In this section we propose several algorithms that make it much more difficult for the adversary to become a cluster head, and consequently, these techniques greatly reduce the impact of the sleep deprivation attack. We assume adversary nodes are interested in increasing their chances at becoming cluster heads. Thus, we do not consider an attack where the adversary intentionally delays cluster head selection.
Random Vote Cluster Head Selection
We have observed that clustering algorithms rely on the honesty of all participating nodes,
allowing a malicious node to generate false information to ensure its selection as cluster head. The
Overview of Random Vote Scheme
A group of local nodes using the random vote scheme form a cluster by performing the following
steps: Each node locally broadcasts its unique ID. Each node uses a pseudorandom number generator to pick the ID of the local node it desires to
become the next cluster head. Nodes locally broadcast the ID of their desired cluster head. Each node repeats step 2 until a single node attains a majority of votes. This node will become
the next cluster head.
Each sensor node is only allowed to cast one vote at a time. However, in the case of a tie, the
nodes will restart the algorithm at step 2. We refer to the execution of steps 2 through 4 as a
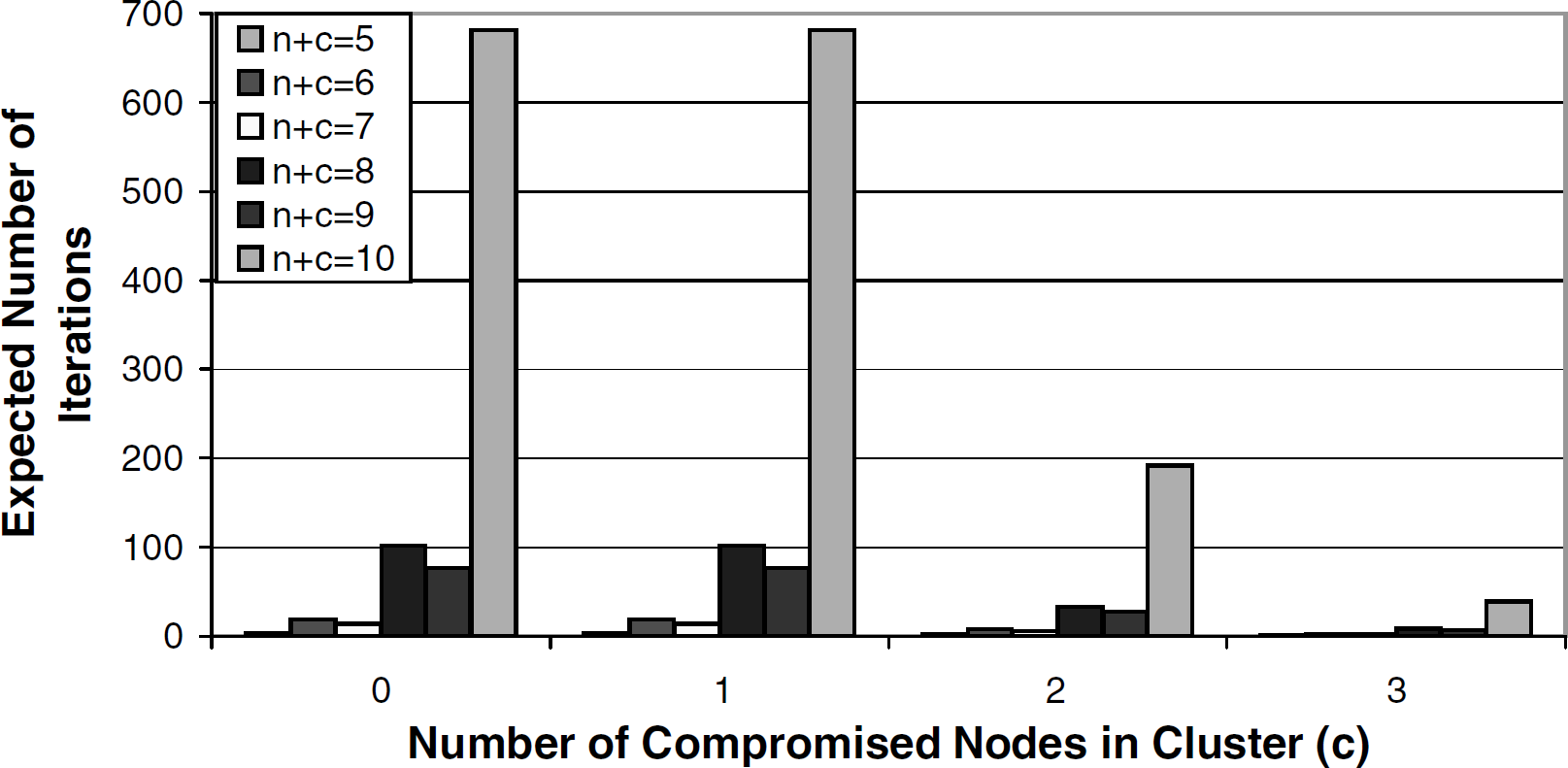
Analysis of Random Vote's Effectiveness at Increasing Attack Tolerance
For simplicity we have assumed that the
To determine the effectiveness of the random vote scheme, we have derived an equation indicating
the probability that any of the malicious nodes in the cluster will be selected as cluster head,
given that 
Similarly, the probability that any of the 
The equations for

Markov chain representation of random selection of cluster heads.
In an argument similar to what was used to formulate 
The product of 
Without any defense mechanism in place, a malicious node is selected as cluster head with a
probability of 1. In Fig. 8 we illustrate

Probability that the random vote scheme selects an adversary cluster head.
In order for this algorithm to be complete, any of the 
In Fig. 9 we utilized equation
Time required for random vote algorithm to complete.
The lack of scalability in the random vote clustering algorithm of Section 6.1 caused us to consider another approach to secure
cluster formation. The
The round robin scheme operates in two phases. The first phase is a bootstrapping phase where the initial clusters are formed. The second phase is a maintenance phase, during which the precise membership of each cluster is updated due to node mobility, addition of new nodes to the network, and removal of nodes from the network.
Analytical Model
Assuming an average of 
In Fig. 10 we have used the equation
for

Probability that round robin scheme selects an adversary cluster head.
A nice property of the round robin scheme is that it only requires a single iteration to select a cluster head. Each node must keep track of exactly which nodes are in the cluster and which node is the current cluster head. Thus, when a new cluster head is needed, each node can independently determine who the new cluster head should be. However, this scheme requires that each sensor node must maintain a list indicating which nodes are in its cluster at all times. Such a list would require an unrealistic amount of per-node storage for larger clusters.
The lack of scalability that daunts the random vote scheme in Section 6.1 and the excessive overhead inherent to the round
robin scheme in Section 6.2 motivated
us to come up with the
Hashed Clustering Overview
In this scheme, each node generates a random number and then broadcasts their number's
hash. This allows each node to
To prevent a malicious node from claiming to be multiple nodes, we assume that every message has been authenticated using an authenticated broadcast scheme such as μTESLA [26].
The hash algorithm operates by having each participating node execute the following steps: Generate an integer, Wait for enough time to pass, For each For each Wait for Verify each Wait for Any node that has a verified Given

The key observation regarding the security of this scheme is that every participating node must
send out its
Likelihood of an Adversary Cluster Head
In this section we analyze the likelihood of an adversary node being elected cluster head in the hash-based scheme.
Notice that the output of the hash-based scheme (i.e., step 9) will be a random integer so long
as at least one of the participating nodes is not an adversary node. This is because a random number
added to a nonrandom number yields a random number. Thus, the malicious nodes will not affect the
random output of the hash-based scheme by colluding. As the following equation indicates, the
probability that a adversary node is selected to become a cluster head is the same as any node in
the cluster: 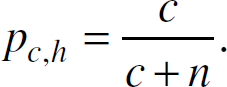
Notice that the probability that an adversary becomes cluster head in the hash-based scheme is
the same as in the round robin scheme (i.e.,
In this section we derive a timing model to show that the hash scheme is capable of forming
clusters in a reasonable amount of time. Consider the hashing scheme within the context of a simple
communication model, where 
The probability that a given message is not received by at least one of the 
Each of the 
There is sufficient redundancy in having each node generate a
Each 
The sum of all 
We estimate 
While not included in our model, the actual value for 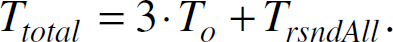
In Fig. 11 we used the equation for

Time required for hash-based scheme to select a cluster head.
To determine the energy consumed by the hash scheme, we perform an average case analysis upon a single node. Note that we assume that communication energy dominates computational energy.
Given that a sensor node on average transmits a total of 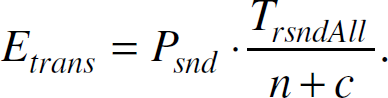
We assume that a node not sending a message is actively listening to the network: and the amount
of energy spent receiving is: 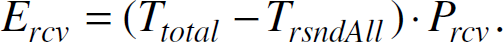
Thus, the total energy spent by a single node in the hash algorithm is: 
In Fig. 12 we have utilized equation
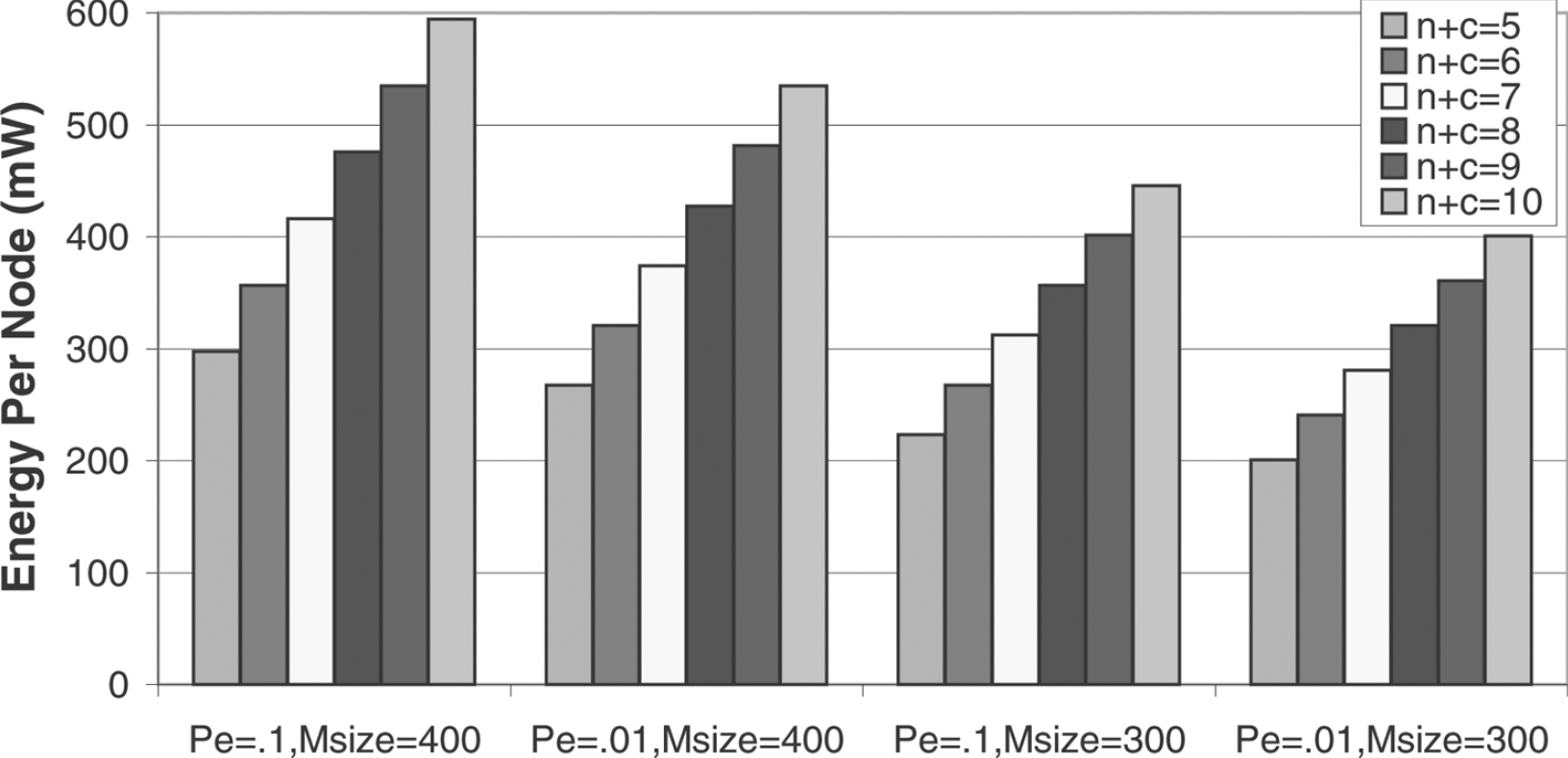
Per-node energy required for hash-based scheme to select a cluster head.
In this paper we have shown a novel attack that an adversary can exploit upon sensor network applications that utilize distributed clustering. This attack, called the sleep deprivation attack, exploits the fact that conventional clustering algorithms rely upon the honesty of participating nodes. Thus, a malicious node can ensure its selection as cluster head, and consequently, it can launch a sleep deprivation attack against the network. In this attack, a malicious cluster head sends vietim nodes seemingly legitimate messages; however, the purpose of these messages is to keep its victims out of their low power sleep mode. The end result of this attack is greatly reduced node lifetime, potentially partitioning the network into disjointed pieces.
We also explain why an adversary would utilize a sleep depriation attack, by comparing it to a more aggressive attack where the victim nodes are barraged with requests. We have found that the sleep deprivation attack is attractive (from the perspective of an attacker) due to its low cost in terms of energy and communication. Further, this attack is not readily detected.
Given the dire consequences of this attack, we have proposed three schemes by which its impact
can be reduced:
Footnotes
Acknowledgments
This research is sponsored by the Defense Advance Research Projects Agency (DARPA), and administered by the Army Research Office under Emergent Surveillance Plexus MURI Award No. DAAD19-01-1-0504. Any opinions, findings, and conclusions or recommendations expressed in this publication are those of the authors and do not necessarily reflect the views of the sponsoring agencies. This work is also supported by NSF CAREER 0093085 and DARPA/MARCO GSRC Grant. Sencun Zhu's work is supported by NSF Grant CNS-0524156.
