Abstract
Arrhythmia disorders are the leading cause of death worldwide and are primarily recognized by the patient’s irregular cardiac rhythms. Wearable Internet of Things (IoT) devices can reliably measure patients’ heart rhythms by producing electrocardiogram (ECG) signals. Due to their non-invasive nature, ECG signals have been frequently employed to detect arrhythmias. The manual procedure, however, takes a long time and is prone to error. Utilizing deep learning models for early automatic identification of cardiac arrhythmias is a preferable approach that will improve diagnosis and therapy. Though ECG analysis using cloud-based methods can perform satisfactorily, they still suffer from security issues. It is essential to provide secure data transmission and storage for IoT medical data because of its significant development in the healthcare system. So, this paper proposes a secure arrhythmia classification system with the help of effective encryption and a deep learning (DL) system. The proposed method mainly involved two phases: ECG signal transmission and arrhythmia disease classification. In the ECG signal transmission phase, the patient’s ECG data collected through the IoT sensors is encrypted using the optimal key-based elgamal elliptic curve cryptography (OKEGECC) mechanism, and the encrypted data is securely transmitted to the cloud. After that, in the arrhythmia disease classification phase, the system collects the data from the Massachusetts Institute of Technology-Beth Israel Hospital (MIT-BIH) database to perform training. The collected data is preprocessed by applying the continuous wavelet transform (CWT) to improve the quality of the ECG data. Next, the feature extraction is carried out by deformable attention-centered residual network 50 (DARNet-50), and finally, the classification is performed using butterfly-optimized Bi-directional long short-term memory (BOBLSTM). The experimental outcomes showed that the proposed system achieves 99.76% accuracy, which is better than the existing related schemes.
Keywords
Introduction
Recent technological advancements have enabled wireless technology and healthcare to work together beyond what is possible with traditional healthcare systems. These benefits include improved quality support for medical services and quick response times for medical intervention. In particular, the real-time parameter and variable capturing process is becoming more straightforward thanks to the IoT [1]. Based on the IoT paradigm, the so-called Internet of medical things (IoMT) allows for the seamless collection of various data streams that can be analyzed to yield pertinent details about the patient’s state [2]. The IoMT uses a few popular technologies, including wireless sensor networks, radio frequency identification (RFID) and wireless body area networks (WBANs) to transmit the patients’ sensors data to the cloud for disease analysis and decision-making [3]. The architecture of WBANs for data transmission in IoT is shown in Fig. 1. It becomes convenient to employ mobile devices to remotely monitor patients with chronic diseases’ ECG signals (for example, arrhythmia diseases). The procedure of taking an ECG involves the recording of a time-lapse of the heart’s electrical activity. Electrodes are applied to their skin to determine whether the patient’s heart is beating regularly [4].
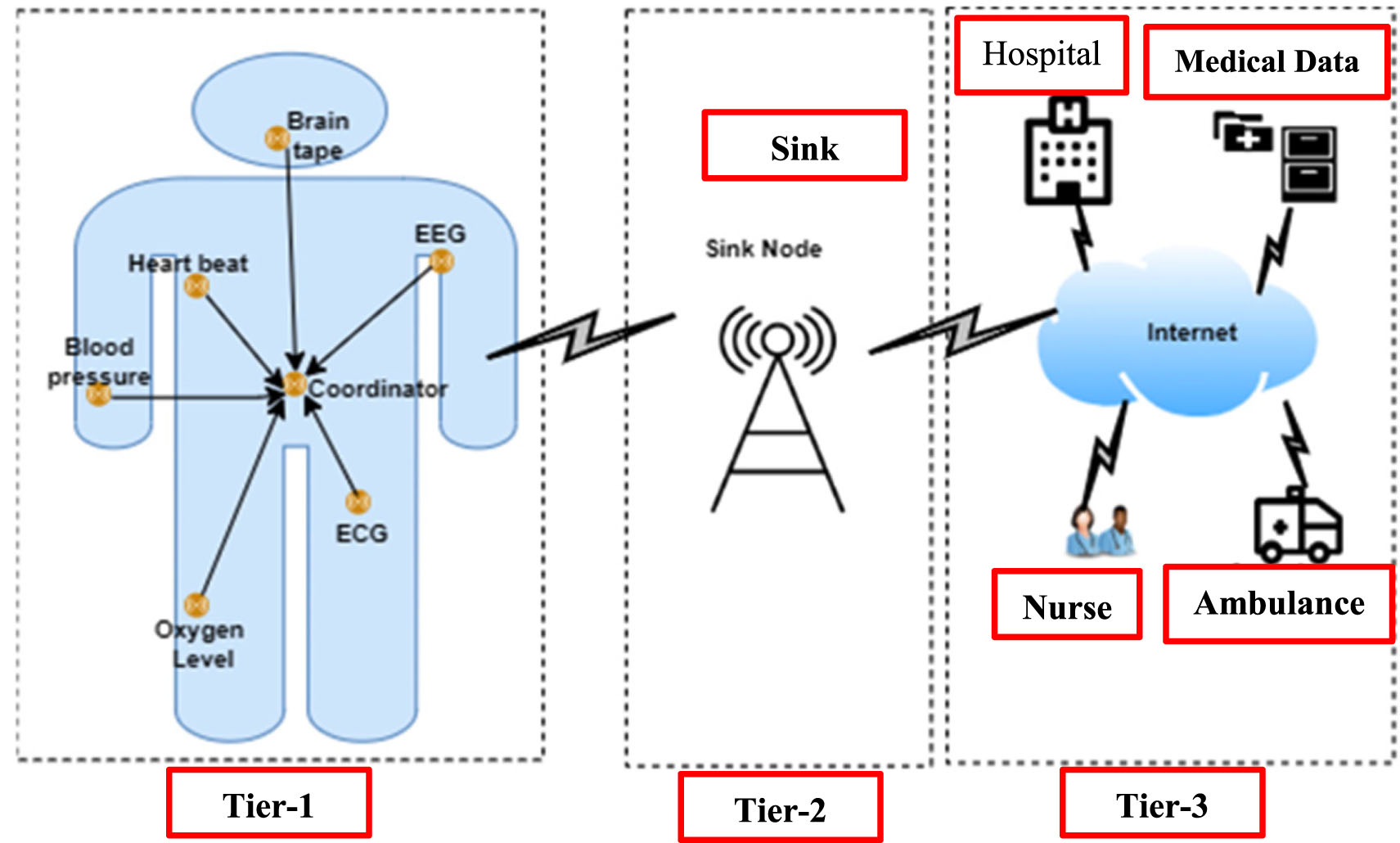
Structural design of WBANs [5].
However, hackers can easily intercept the data and make changes when the data is transmitted from sensors to the cloud via the unsecured wireless medium. Security now plays a significant role in healthcare services, particularly in preserving ECG data and the prognosis of arrhythmias [6]. Recent advances in cryptography have made computations virtually immune to attacks; the main drawback is the insecure transfer of keys. Cryptographic techniques using random key selection take more to encrypt and decrypt data and offer less security for the system. This study employs an effective asymmetric technique to address these issues and enhance security for transmitting secure ECG data to the cloud. Contrarily, according to the World Health Organization, cardiovascular disease (CVD) ranks first among all causes of death, with an estimated 32% of all global fatalities. Arrhythmias are a specific type of CVD that show irregular heartbeat patterns, such as too- or too-slow heartbeats [7, 8]. Premature ventricular contraction (PVC), ventricular fibrillation (VF), atrial fibrillation (AF), and tachycardia are a few examples of arrhythmias [9]. Early detection of arrhythmias will aid in identifying heart attack risk factors. Therefore, it makes sense to conclude that regular cardiac rhythm monitoring is crucial for preventing CVDs [10].
The diagnosis of arrhythmias has traditionally relied on a cardiologist’s ability to recognize specific kinds of arrhythmias by examining the waveform of electrical signals gathered from the heart, which frequently required patients to stay in the hospital for extended periods while receiving therapy. This method drove up healthcare expenses and placed pressure on institutions, especially in rural and distant areas [11]. The ECG signals recorded briefly might not accurately reflect the patient’s heart activity because of the intricacy and suddenness characteristics of arrhythmia [12, 13]. The patient’s bodily circumstances are continuously sensed by IoT-based ECG signals during every moment of the day, making it simple to identify arrhythmia. The cloud-stored IoT ECG data can be used to classify the arrhythmia disease using established methods. To categorize the arrhythmia disease from the ECG data [14], researchers used conventional ML techniques, including support vector machine (SVM), decision trees (DTs), and random forest (RF) [15, 16]. These techniques, however, necessitate the extraction and manipulation of artificial features. Additionally, it suffers from the system’s computational complexity. DL for automatic ECG classification is gaining popularity due to technological advancements [17, 18]. DL works better than several ML approaches when categorizing CAD based on ECG signals [19, 20]. This motivates us to use an efficient DL approach to propose an arrhythmias classification (AC) system from the IoT-based ECG signal. The main objectives of the proposed work are explained as follows: The proposed system uses the OKEGECC algorithm to secure patients’ ECG data to the cloud, in which the private key is optimally selected by employing the Gauss iterated map and Guiding weight-based Sun Flower Optimization (G2SFO) algorithm. We are employing DARNet-50 to extract the pertinent features from the pre-processed data, wherein the deformable attention module (DAM) is included in ResNet-50 for rich future representation. The proposed system uses the BOBLSTM approach to classify the disease, in which the butterfly optimization (BO) algorithm optimally chooses the parameter (weight and bias).
The remaining part of the document sis outlined as follows: Surveys the recent works related to ECG data security and classification are given in section 2. Section 3 briefly explains the phases of proposed system. The outcomes of the proposed as well as existing techniques are analyzed in section 4. Lastly, the conclusion of the paper with future research is given in section 5.
This section surveys recent encryption models for providing security to the ECG data and AC in IoT-based healthcare systems. Kristtopher Kayo Coelho et al. [21] recommended a low-memory symmetric-key generation-based group cryptography protocol (LORENA) for secure ECG data transmission in an IoT-based healthcare environment. The LORENA included the key generation module that generated the individual key for each IoT healthcare device in the network, and that can be used in point-to-point communication between the devices. The time domain ECG signals were converted into a frequency domain and quantized into a single, highly user-linked secret key. These generated keys were exchanged between the IoT devices for the key agreement process. Once authorized, the data was exchanged between the devices and received at the base station for further analysis. The model was secure, lightweight, and feasible for IoT-based healthcare environments. Farnaz Farid et al. [22] secure an IoT and cloud-based healthcare environment using an intelligent identity management system (IDMS). The system comprised three layers: device, gateway, and healthcare cloud. The authentication of the machines was carried out in the device layer based on the central gateway. The gateway layer stores the authentication credentials of the patients, and a centralized access control was carried out in this layer to protect the network from unauthorized access. The final hospital cloud layer adopted a federated IDMS procedure to make decisions. The system identified the users successfully with a 0% equal error rate.
Jamal Kh-Madhloom et al. [23] suggested multiple layers of advanced encryption standards (AES) and DNA computing for encrypting ECG data in IoT data transmission. The ECG sensor data was converted into a binary bit for performing DNA encryption that transformed the binary bits into DNA helix using variable DNA bases. The DNA sequences were encrypted using the AES model to provide better security to the ECG data. The system attained a decryption time of 5.03 sec, lower than the existing models. Zia UR Rehman et al. [24] recommended an ECG and lightweight cryptographic-based hybrid authentication scheme for IoT networks. The system generated the bio-key based on the features of ECG signals and used body area network (BAN) logic to provide mutual authentication between the devices. Finally, the system used the Internet security protocol’s automated validation and applications (AVISPA) to perform verification. The system attained a computational cost of 480b, better than the existing methods.
Ruben Enrique Canon-Clavijo et al. [25] presented ML-based arrhythmia detection in IoT. The data from the IoT sensors were preprocessed and stored based on Heroku’s PostgreSQL. The preprocessed data was passed to several machine learning (ML) classifiers to predict the patient’s arrhythmia. Finally, the clinical results were accessed by medical professionals and patients via the graphical user interface. The system used the MIT-BIH-Arrhythmia database as well as the outcomes prove the effectiveness of the ML model by achieving 93% and 97% of accuracies in normal and unclassifiable beats of arrhythmias. Peng Lu et al. [26] presented that ML frameworks say gated recurrent units and decision trees for detecting arrhythmias. The data collected from the sensors were processed using discrete wavelet transform for noise removal and R-peak value for segmentation. Then using a decision tree, some frequency domain features were extracted and given to a gated recurrent unit for classification. The system attained 98.31% of accuracy along with 96.73% of precision on the MIT-BIH arrhythmia database, which indicated its clinical significance and high reliability in disease detection. Ali Raza et al. [27] designed a federated transfer learning-based ECG monitoring system in IoT. Initially, a convolutional neural network-based autoencoder was utilized to eliminate the noise from the ECG data of the patients. Then the system used CNN with a transfer learning model to categorize the ECG data. The system used gradient-weighted class activation mapping to explain the classification outcomes reliably. The method attained an accuracy of up to 94.5% and 98.9% on the MIT-BIH Arrhythmia database, which was better than previous related schemes.
Ashwani Kumar et al. [28] introduced an IoT-based arrhythmia classification system using flamingo-optimization-based deep CNN (DCNN). The sensor data of the patients received from the base station was preprocessed and inputted to DCNN for classification, in which the parameters of the DCNN were optimized using a flamingo optimization algorithm. The features from the ECG signals were extracted and classified effectively using optimization-based DCNN to detect whether the patients had arrhythmia. The training on the MIT-BIH dataset showed 98.5% accuracy of the model for disease classification. Saroj Kumar Pandey et al. [29] developed a stacked restricted Boltzmann machine (RBM) for arrhythmia detection. Initially, the segmentation of the heartbeats from the sensed ECG data was done with its R peak values using the annotation files’ information. Then the features from the segmented ECG data were extracted using the RBM model, and finally, the classification of four kinds of heartbeats was done using a SoftMax activation function. The technique attained an accuracy of 98.61% on the MIT-BIH dataset, which was superior to the existing methods. Surbhi Bhatia et al. [30] presented a hybrid deep-learning model for ECG classification in IoT. The collected ECG data was preprocessed initially using z-score normalization, and the segmentation of the preprocessed data was done by finding data peaks based on the annotation file. The data imbalance problem in the dataset was solved using the synthetic minority oversampling technique (SMOTE), and finally, CNN was utilized for classification. The simulations on the MIT-BIH arrhythmia database showed that the hybrid model worked well for AC by achieving 98.36% accuracy, which was better compared to previous methods.
The techniques above for providing secure healthcare monitoring in IoT attain satisfactory performance. However, they need the following limitations. The authors [21, 23] use symmetric key encryption techniques to secure the IoT data in the cloud, whereas it uses only one key for performing both encryption and decryption. So, it is easily vulnerable to many kinds of network attacks, and the security of the network is questionable. When surveying the classification models for AC, the author [25, 26] developed an ML scheme which performs quicker and attains satisfactory outcomes in disease classification. However, they could serve better when the data size is large, and they need human participation for the feature learning process, which sometimes leads to lower detection accuracy. To overcome the drawbacks of ML, several authors use DL schemes in disease classification [27–30], and they attain comparatively better outcomes than the ML frameworks. However, they did focus on any selective feature learning mechanism for improving the prediction performance. In addition, the real-time ECG data we received from the sensors are noisy, so if they are directly fed into the ML or DL model, they did not provide interpretability of the outcomes. So, to address the above limitations, this paper proposes a secure IoT-based ECG monitoring scheme using OKEGECC and a DL system.
Proposed methodology
The structural design of the proposed system is shown in Fig. 2. As shown, the patient ECG data is collected from the sensors attached to the patient’s body, and they are securely transmitted to the medical cloud server using the OKEGECC algorithm that uses the G2SFO model for optimally choosing the private key. The encrypted data is stored in the cloud, and then the disease classification stage is carried out for the patient’s ECG data. In the training process, the proposed system uses the MIT-BIH database and the preprocessing is performed on the collected dataset using CWT. From that, features are extracted with the help of DARNet-50, and finally, classification is performed by BOBLSTM, in which the BO algorithm optimally chooses the parameter (weights and bias).
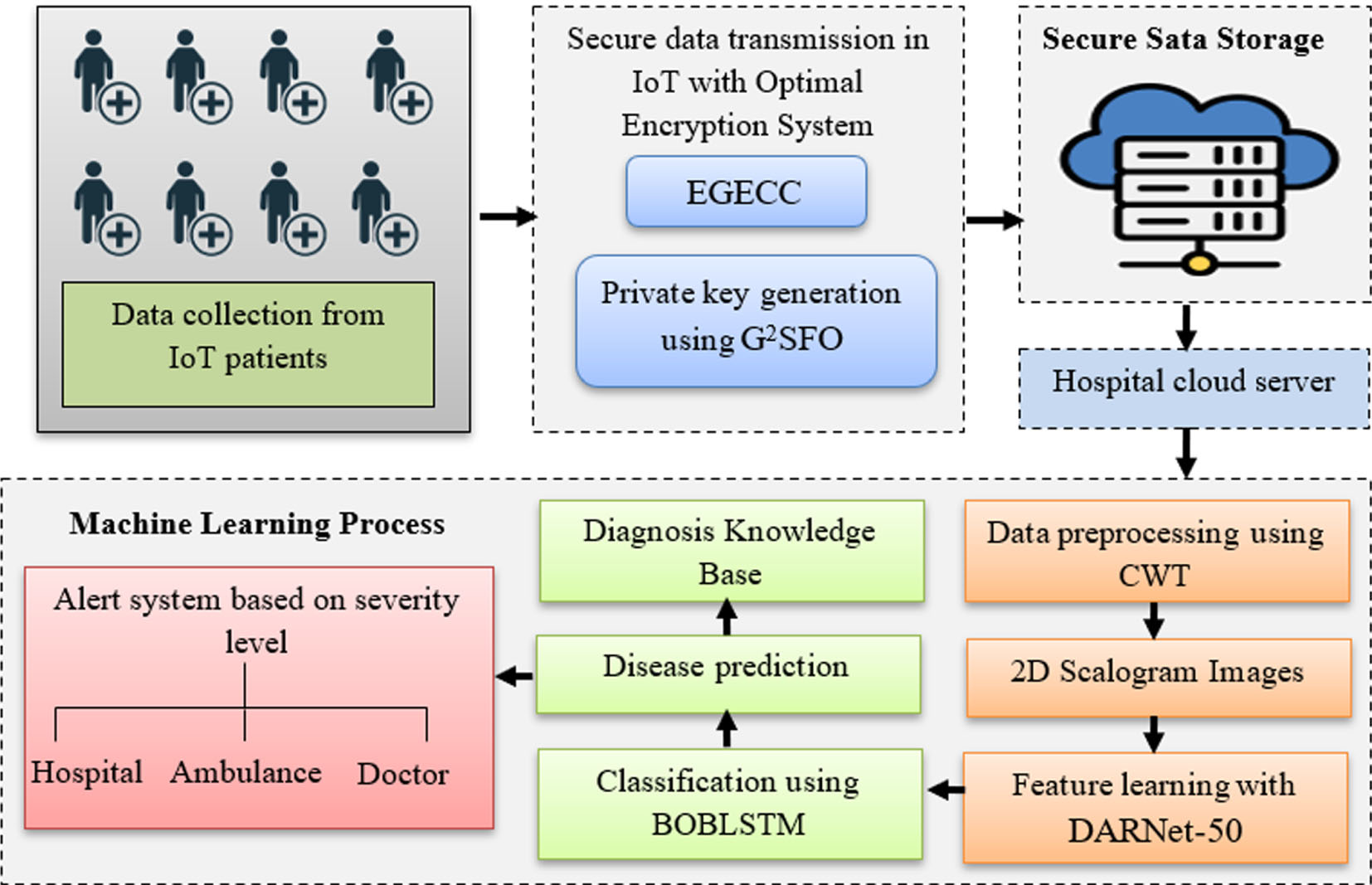
Proposed method’s structural design.
At first, IoT devices and sensors use a wireless communication network to collect patient ECG data and transmit it to the cloud. However, if the ECG signal is transferred directly to the cloud, unauthorized individuals could attack or crash. Hence, the proposed system uses the OKEGECC algorithm to encrypt the ECG signal before transmitting it to the cloud. ElGamal Elliptical curve cryptography (EGECC) is the development of the elliptic curve over a finite prime field-based ElGamal public key cryptographic scheme. It utilizes public and private keys to perform encryption and decryption processes. Choosing the private key in the EGECC algorithm is a constant challenge. The security of the entire algorithm is compromised if the tiny values are selected at random. Since the private key is utilized to estimate the public key, the result will always be infinite if the keys are not chosen appropriately. So, the proposed system uses G2SFO algorithm to determine the private key optimally. Thus, the optimal key selection process involved in the classical EGECC algorithm is termed OKEGECC, and this modification will improve the level of security in the ElGamal ECC cryptosystem and maintain the system’s efficiency. The OKEGECC mainly includes three processes, key generation, encryption, and decryption, and these phases are briefly explained as follows:
a) Key generation
As EGECC is an asymmetric cryptographic mechanism that uses two keys, say private and public keys. Initially the algorithm choses a prime number
First, the initialization of the search agents in the G2SFO is described using GIM. It is a nonlinear iterated map of the real into a real interval given by the Gaussian function. It mainly increases the population diversity of the model and aids early convergence. It is mathematically described as follows:
Where, β1 and β2 indicates the real parameters,
Where,
Where,
Where,
Where,
Where,
Where,
Where,
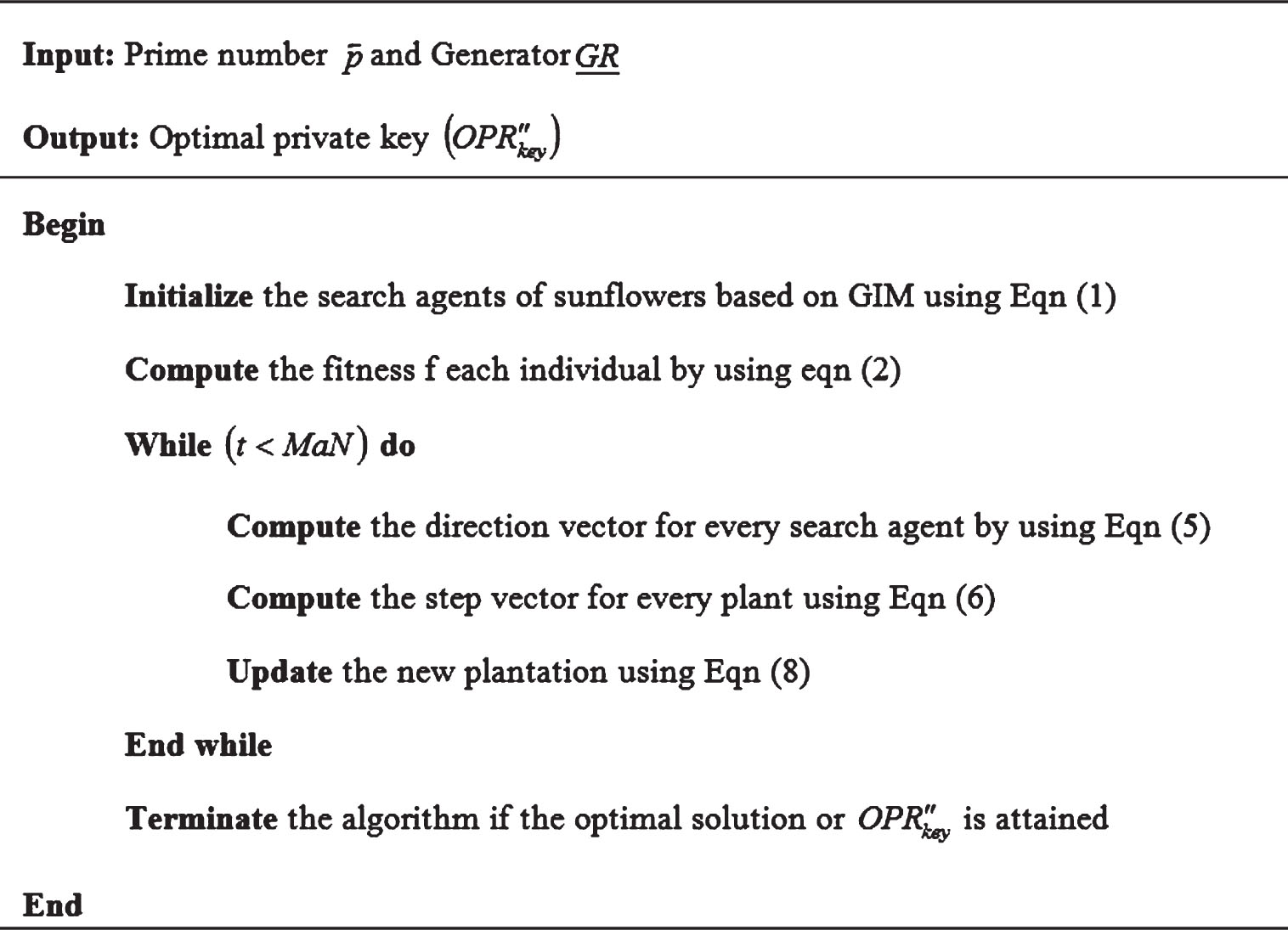
Pseudocode of the G2SFO algorithm.
Once optimal private key
Where,
Once the key generation process is completed, the ECG signal is encrypted. Encryption is the process of encoding a message into a code that is not understood. The mathematical model of the encryption is shown below:
Where,
The decryption process performs the reverse operation of encryption to get the original data back, in which the optimally chosen private keys are used in the place of data decryption. The process is mathematically expressed as
Where,
The decryption output was classified as normal or abnormal arrhythmia disease, which supports the medical expert in achieving the desired deduction and aids the analyst in further analysis. The proposed system uses the MIT-BIH database to train the system, which includes preprocessing, feature extraction, and classification phases. The decrypted data is tested based on these trained results to provide desired outcomes. The training process is briefly explained as follows:
Preprocessing
It might be challenging to extract usable data from the raw ECG signal since the sensor’s acquired ECG signal is typically distorted with numerous noises, say baseline wandering, power line interference and electromyography disturbance. Consequently,iltering is necessary before further processing. Herein, the proposed system uses CWT which helps to get high-quality data for accurate prediction results. A new two-dimensional colored scalogram image is created using the CWT to transform a one-dimensional ECG signal. The most popular time-frequency analysis technique is CWT, which employs a variety of wavelet functions for decomposing a signal into a set of time-frequency components. The mathematical formula of CWT for an input ECG signal
Where,
The signal’s wavelet coefficient function at different scales is obtained using different scale factors of CWT. These wavelet coefficients are the E signal’s time-frequency 2D scalogram.
Fture extraction is the most vital task in accurate. Proper selection of the correct features results in high diagnostic accuracy. In this paper, the proposed system uses DARNet-50 to attain the global feature representation of the ECG signals. Residual network-50 (RNet-50) is a Resnet network’s variant that includes 48 convolutions, 1 max pooling and 1 average pooling layer. It extracts relevant features at each provided 2D scalogram image. But it didn’t take any deep features for classification. This may lead to classification errors, which could have given more accurate results. So, the classification rate of arrhythmia disease is low and has more error rate. So, the proposed system introduces a deformable attention mechanism to extract deeper features from the given 2D scalogram images and to minimize the misclassification error. Deformable attention permits the multi-head-attention mechanism to concentrate on pertinent regions to acquire more informative and deeper information from the input data. Thus, the deformable attention included in the conventional RNet-50 is renamed DARNet-50. The proposed DARNet-50 mainly consists of four modules: convolutional module, deformable attention module, pooling module, and fully connected module. Each module’s functions are explained as follows:
The convolution module, sometimes called the transformation layer, is the network’s uppermost layer. During convolution, a filter is moved across the entire image. This layer’s goal is to create feature maps for the convolution module. A 28×28 feature vector is generated for each input image after the convolution of the input image with the filter. A 7×7 kernel filter is employed at the convolutional layer with 64 additional kernels with a 2-sized stride. The mathematical formulation of the convolutional module is given in Equation (16).
Where,
Where,
After convolution, the obtained feature maps are passed to the deformable attention module (DAM) to extract deep features. The structure of DAM is shown in Fig. 4. The deformable attention can be considered a spatial adaptive mechanism that works with crucial feature map regions to depict the relationship between tokens aurately. These regions are calculated from collections of distorted points that an offset n has learned from the queries. Bilinear interpolation is used to sample features from the feature maps once the areas have been obtained, and the tested features are then input into multi-head attention to retrieve the deeper features of the related images. The previous layer output is passed to depth-wise convolution for local feature extraction. The previous layer oput is passed to depth-wise convolution for local feature extraction. To extract, the offsets(
Where,
The deeper feature maps from the deformable attention module are passed to the pooling module. The pooling module is sandwiched between successive deformable attention layers to compress the amount of data and parameters that reduce overfitting in the network. The max-pooling with a 2-sized stride is used to reduce the feature dimensionality. The feature maps from the pooling layer are considered the final feature vectors of the ECG data, fed into BOBLSTM for AC.
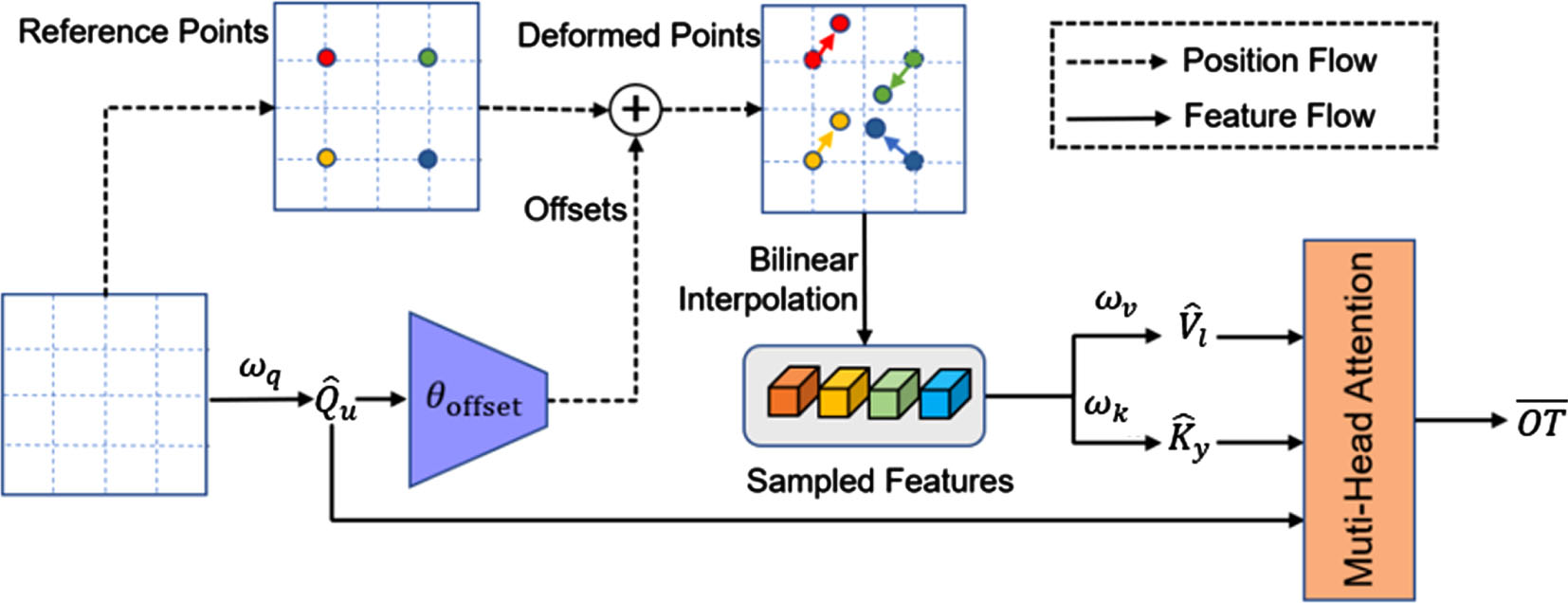
Structure of DAM.
Finally, the arrhythmia disease classification uses the butterfly-optimized bi-directional long short-term memory (BOBLSTM). Bidirectional long short-term memory (BLSTM) is an extension of long short-term memory, which works in both forward and backward directions to learn the sequence information from the data. The network attains better performance than the unidirectional networks by solving long-term dependency problems. However, random parameters (weights and bias) of a BLSTM model affect the learning process and are set empirically. It is necessary to tune or optimize the hyperparameters of the network to get optimal results in classification and minimize the loss function. Henceforth, the proposed system uses the butterfly optimization (BO) algorithm to optimally select the network’s hyperparameters (weights and biases). So, the model is called BOBLSTM, and the architecture diagram of BOBLSTM is shown in Fig. 5.
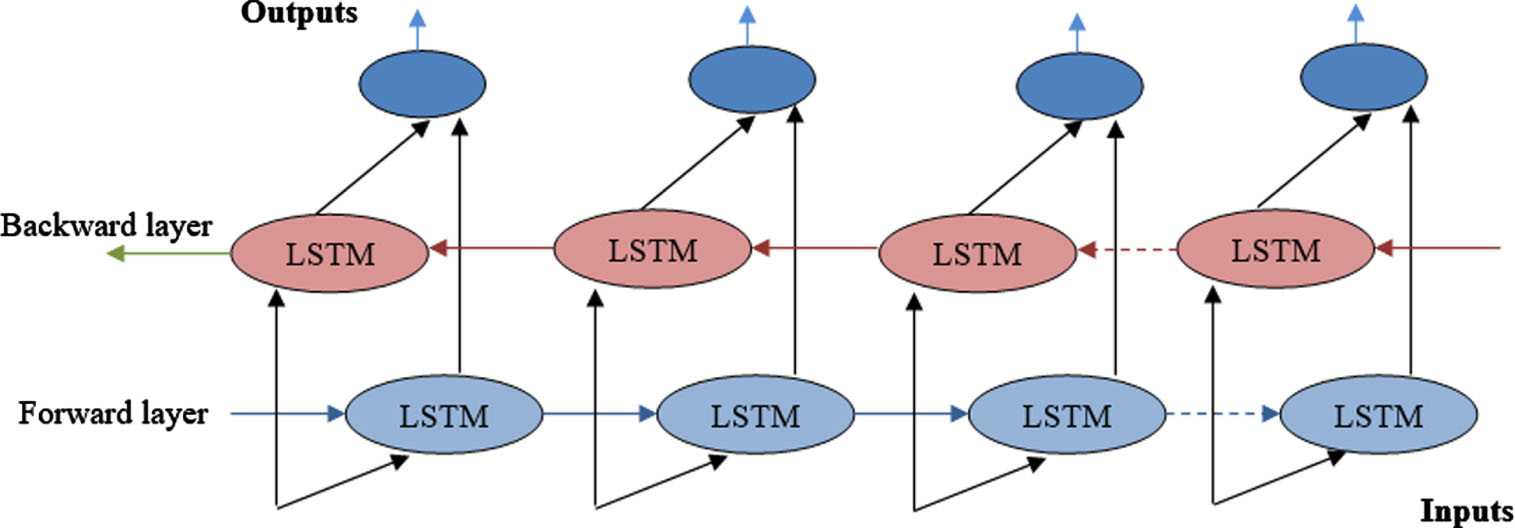
Structure of BLSTM.
The structure includes forward and Backward LSTM for learning the long-term dependencies in the data. Each forward as well as backward LSTM has an input gate, forget gate, output gate, and cell state, respectively.
Forget gate
These values are chosen optimally using butterfly optimization (BO). Due to its simplicity, BO has drawn the interest of numerous researchers and outperforms several other optimization techniques. It was created by modelling the way butterflies find food. When optimizing the search space, each butterfly in BO is taken to be a search agent. In the wild, butterflies can distinguish between various levels of smell intensity. Every butterfly releases a scent at a specific intensity that communicates information about the suitability of the food. Using local and global searches, the BO chooses the parameters optimally and helps to improve the prediction performance. The mathematical model of forward LSTM is shown below:
Where,
Where,
Here, the outcomes of the proposed system are compared with existing related schemes regarding some metrics to determine the proposed model’effectiveness in data security and disease classification. The system is simulated in MATLAB with Windows 10 operating system (64bit) and 8GB main memory at a 2 GHz dual-core PC. The method is validated using the standard annotated dataset, MIT-BIH, accessible via https://www.physionet.org/content/mitdb/1.0.0/. Samples of two-channel ambulatory ECG recordings from 47 patients were collected for this database by Boston’s Beth Israel Hospital Laboratory. The electrodes are positioned on the chest to generate a modified limb lead II (MLII), the channel observed in most records. In contrast, the other channel is typically V1, with minor contributions from V2, V4, or V5. The recordings, which continue for roughly 30 minutes, contain details of complex ventricular, junctional, and supraventricular arrhythmias and conduction abnormalities using the rhythm characteristics and QRS alterations. Here we use only lead MLII because normal QRS complexes are typically more prominent than V5. The AAMI protocol is approved in this study, and all ECG heartbeat markers are correctly mapped to the AAMI names by the mapping data shown in Table 1. Five types of beats—Normal beats (N), Supra Ventricular Ectopic (SVEBs), Ventricular Ectopic (VEBs), Combination of Ventricular and Ordinary (F), and Unknown Beats (Q) of the dataset are used for this analysis. From the records, 70% of the data is used for training, and 30% is used for testing.
Relationship between ECG heartbeat labels to ANSI-AAMI Standards
Relationship between ECG heartbeat labels to ANSI-AAMI Standards
The data and label fields in the database are organized as an array. Each recording has 65,536 samples in total. The data is therefore represented as a 162 65,536 matrix, which denotes that it contains a total of 162 ECG signals having a sample size of 65,536 and is re-sampled at a standard rate of 128 hertz. ARR signals are found from the first to the 96th row of an array, while CHF signals are found from the 97th to the 126th row. In contrast, the NSR signals are represented from the 127th to the 162nd row. The preprocessing outcomes of the input signals using CWT are shown in Fig. 6.
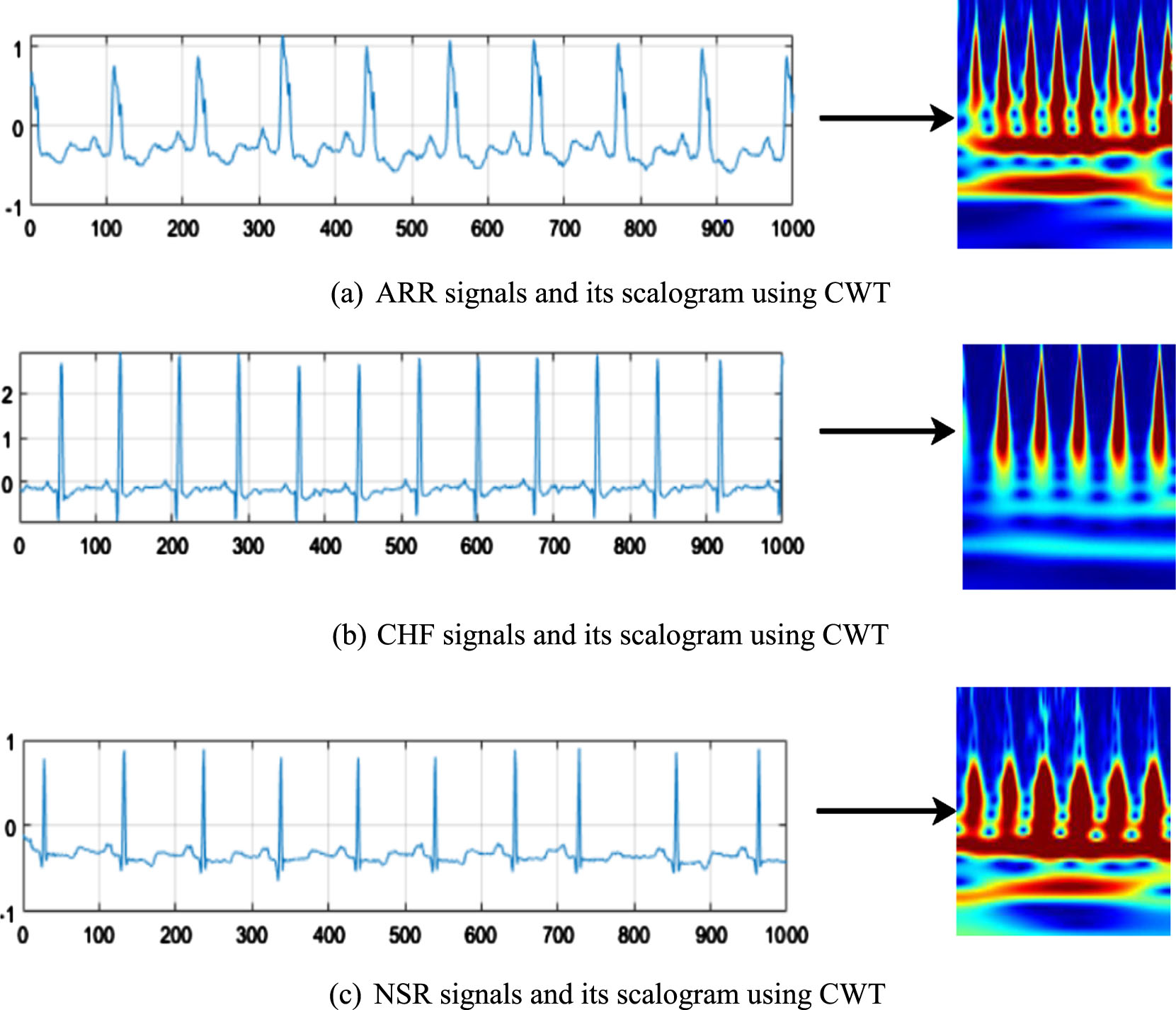
The preprocessed outcomes of the input ECG data.
The outcomes of the proposed OKEGECC are investigated against the existing Elliptic Curve Cryptography (ECC), Rivest Shamir Adelman (RSA), Advanced Encryption Standard (AES), and Blowfish algorithm regarding encryption time (ET), decryption time (DT), and key breaking time (KBT). Table 2 lists the ET and DT attained by the techniques for various file sizes. ET is the time the scheme takes to encrypt a particular amount of user data, and DT is the time to convert the encrypted data into its original format. For the file size of 10kb, the blowfish takes ET and DT of 626.12 s and 114.43 s, the AES takes ET and DT of 589.43 s and 104.41 s, the RSA takes ET and DT of 562.12 s and 97.12 s, and the ECC takes ET and DT of 526.41 s and 74.51 s. But the proposed OKEGECC takes the ET and DT of 413.12 and 42.11 s for the 10kb file size. Also, when comparing the results of the models for other file sizes, the proposed method attains the lowest ET and DT than others, which shows its ease of encryption and decryption process for the ECG data. The diagrammatic representation of Table 2 is shown in Fig. 7. Next, the outcomes of the techniques regarding KBT are plotted in Fig. 8.
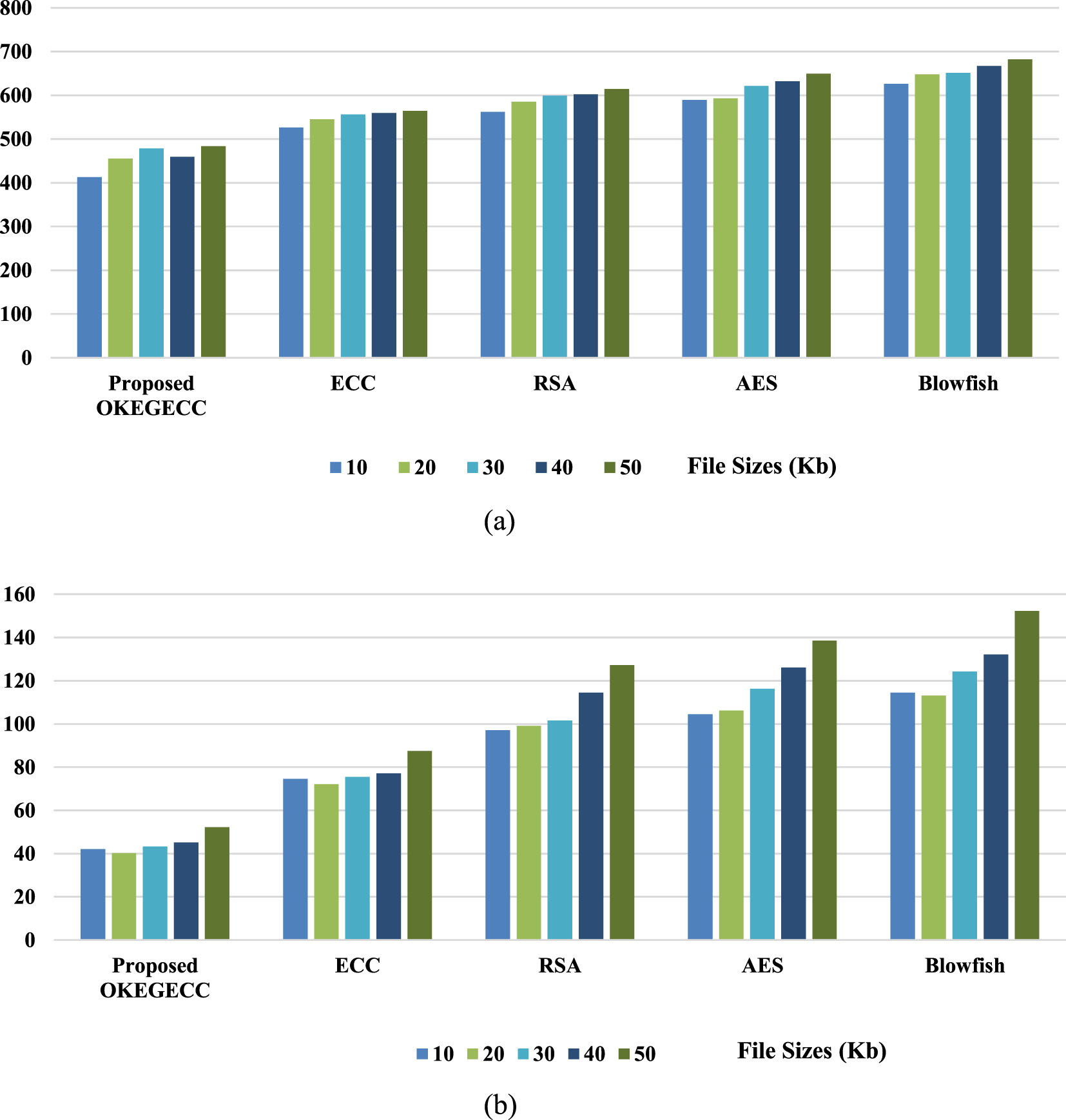
Encryption and decryption time analysis.
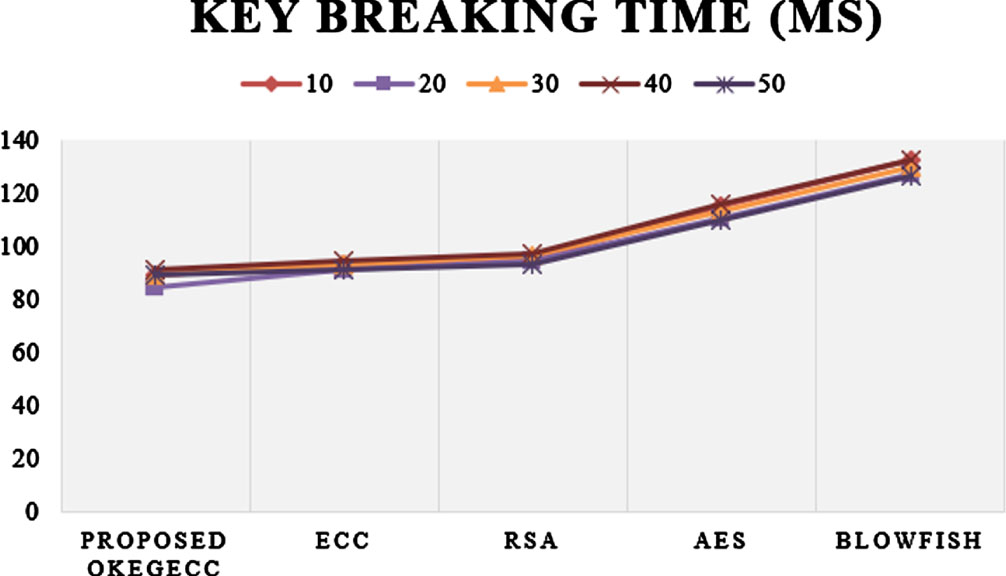
Key breaking time analysis.
Analysis based on Encryption and Decryption Time
For a 10kb file, the proposed one has acquired a lower KBT of 89.25 ms, whereas the existing ECC, RSA, AES, and blowfish have attained the KBT of 93.32 ms, 95.42 ms, 115.13 ms, and 132.41 ms, correspondingly. Similarly, for the remaining file sizes (20kb–50kb), the proposed one also takes less KBT of 84.47 ms, 89.38 ms, 91.42 ms, and 89.65 ms than the existing approaches. Thus, the proposed one achieves more high-level outcomes than the existing methods. The reason is that the current ECC, RSA, AES, and Blowfish approaches randomly select the key for encryption and decryption, so it takes more time for encryption, decryption, and key breaking process. The proposed system optimally sets the key instead of choosing random keys using an efficient G2SFO algorithm, so only the proposed one takes less time for encryption, decryption, and key-breaking process and provides better outcomes than the existing methods.
The confusion matrix of the proposed system for five class labels in the dataset is provided in Fig. 9. It was observed that the system attains a higher level of true positives in all class labels of the database, and only a lower number of true negatives are attained in cross classes of the databases. The outcomes achieved by the proposed system for five heartbeat types (N, S, V, F, and Q) are tabulated (Table 3) regarding precision, recall, f-measure, and accuracy. The method attains higher classification outcomes for Q heartbeat (99.76% -precision, 99.96% -recall, 99.87% -f-measure and the overall accuracy achieved by the proposed system for classifying all dataset classes is 99.14%. Then the average outcomes of the proposed BOBLSTM are weighted against the existing BLSTM, recurrent neural network (RNN), RF, and SVM based on accuracy, precision, recall, f-measure, root mean squared error (RMSE), mean absolute error (MAE), and area under the curve (AUC), which are plotted in Fig. 10 and 11.
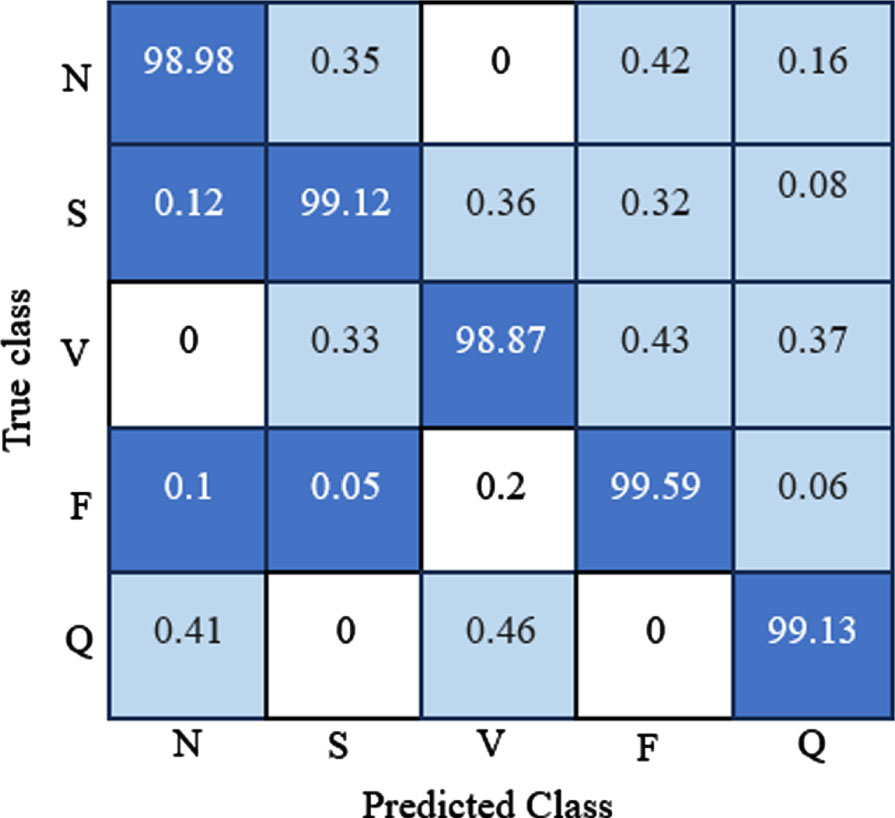
Confusion matrix of the proposed system.
Analysis of proposed system for five classes of arrythmias
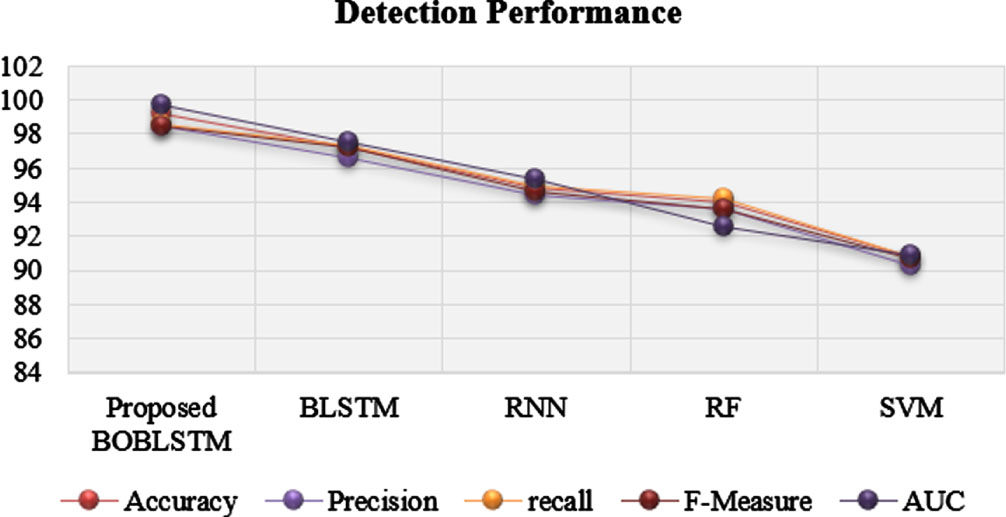
Detection performance of the classifiers.
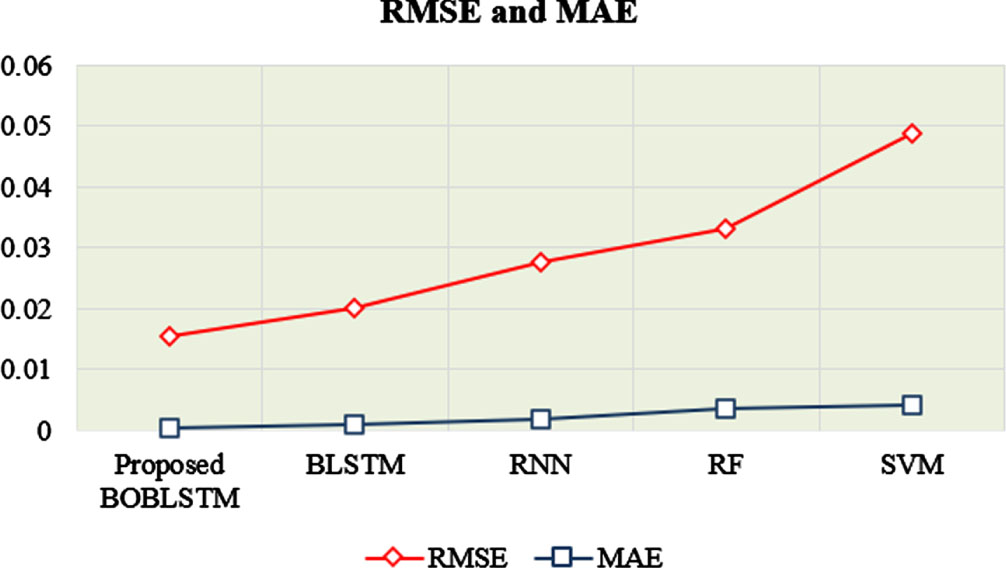
Analysis based on RMSE and MAE.
Comparative Analysis
When considering the accuracy metric, the proposed one achieves 99.14% of accuracy, which is higher than the existing methods because the existing BLSTM, RNN, RF, and SVM offer accuracies of 97.17%, 94.85%, 93.99%, and 90.74% for disease classification. Similarly, considering the other metrics, the proposed one achieves 98.43% precision, 98.59% recall, 98.46% f-measure, and 99.75% AUC, better than the existing methods. Figure 10 shows the RMSE and MAE obtained by the classifiers for AC. These metrics show the loss of information attained by the techniques when performing classification.
The proposed method attained an average RMSE of 0.0154 for AC. In contrast, the existing BSLTM, RNN, RF, and SVM models achieve the RMSE of 0.0201, 0.0275, 0.0332, and 0.0489, which are higher than the proposed system. Likewise, when comparing the MAE of the models, the proposed system attains the lowest MAE of other existing techniques. So, from the outcomes, it was observed that the proposed system beats existing classifiers in terms of classification and loss metrics.
Here, the outcomes of the proposed work are contrasted against the existing related works, which use the MIT-BIH database. The comparison is done based on accuracy and is tabulated in Table 3. The existing ML [25], GRU [26], CNN [27], DCNN [28], RBM [29], and CNN [30] proffers accuracy of 97%, 98.31%, 98.9%, 98.5%, 98.61%, and 98.36%, which is lower when compared to the proposed one, because the proposed one attains higher prediction accuracy of 99.76%. Thus, the overall experimental analysis shows that the proposed one performs better than the existing methods. The reason is that it initially preprocesses the collected signal using the CWT algorithm, improving the data quality for further analysis. From that, the deeper features are extracted using the DARNet-50 model, which improves the prediction accuracy of the classifier with minimal training time. Finally, the parameter (weights and bias) tuned BLSTM model learns the data’s long-term dependencies in both forward and backward directions. This leads to the model’s higher prediction accuracy with minimal classification loss (error).
Conclusion
This paper proposes a secure arrhythmia classification system for IoT-based healthcare systems. The system’s security is achieved by offering a novel optimal key-based EGECC approach, and accurate classification of arrhythmias is performed using the DL system. The system was trained and tested using the MIT-BIH database. Compared to the existing approaches, the proposed encryption system attains less time to encrypt and decrypt the data. The outcomes of the proposed and existing classification schemes for arrhythmia classification are compared based on accuracy, precision, recall, f-measure, RMSE, MAE, AUC, and classification time. The proposed system achieves 99.76% accuracy, 99.86% precision, 99.98% recall, 99.56% f-measure, 0.0154 RMSE, 0.0004 MAE, 99.75% AUC, and 4 ms classification time, which are also better than the existing methods. Moreover, the proposed work is contrasted with the previous works reported in the literature; herein, also the proposed work attains maximal outcomes. Thus, it concluded that the proposed work achieves outstanding results than the state-of-the-art methodologies. The work will be prolonged for further investigation in this area to find out kinds of attacks faced by the IoT heath care system in data transmission using artificial intelligence system.
