Abstract
The purpose of the study is to examine how cybersecurity knowledge, password security, and self-perception of skill affect cybersecurity awareness issues via the mediating lens of cybersecurity attitude among university students in Bangladesh. A sample of 430 university students from two public and three private universities provided the data in Dhaka, Bangladesh. An approach known as stratified random sampling was used in this cross-sectional study. The positivist approach was used, and a hypothetical statistical induction technique was used. The research constructs, which were adopted from earlier studies, were measured using scales that had undergone validation. Smart PLS-SEM 3.3.9 was used to quantitatively analyze the data. The results indicated a positive and significant association between cybersecurity knowledge and password security with cybersecurity awareness. No conventional association was found between self-perception of skills and cybersecurity awareness. Moreover, the data analysis confirmed that cybersecurity attitudemediates the relationship between cybersecurity knowledge, password security and self-perception of skills with cybersecurity awareness. This study implies that more effort needs to be put into informing the general people likely students about cybersecurity and ethical internet use. Furthermore, the main contribution of this study is to emphasize the need of raising cybersecurity awareness among students.
Keywords
Introduction
As digital technology has been developing quickly in recent years, cybersecurity is becoming one of the most difficult concerns and a big source of worry. However, this issue has never been more pressing or important than it is right now during the COVID-19 epidemic, when working and studying online has become the only realistic option everywhere there is an internet connection (Akdeniz, 2023; Bilakeri & Kotegar, 2023; Debala et al., 2023; Garba et al., 2020; Hong et al., 2023; Wirawan et al., 2023). Such an unprecedented transition from the offline to the online world might pose serious risks to personal data protection and privacy, particularly for online teaching and learning. Attacks in higher education are considerably increasing as hackers target innovative online-learning models, according to recent figures that reveal the education sectors (An et al., 2023; Farsani & Oates, 2023; Sasikumar et al., 2023; Zhang et al., 2023).
To combat the ever-expanding digital society and culture, it is suggested to enhance Internet Security Awareness (hereinafter ISA) by teaching internet users about the numerous cyber risks and the susceptibility of computers and data (Nguyen et al., 2023; Quayyum et al., 2021; Zhang-Kennedy & Chiasson, 2022). This would cause behavioral changes. In China, the tsunami of social digital transformation has been driven by the COVID-19 epidemic from individuals, businesses, and governments in all directions (Al-Wattary & Wyness, 2023). As one-fifth of the world’s internet users, this nation witnessed cybersecurity challenges emerge as significant problems at the same time (Chandarman & Van Niekerk, 2017; Lee, 2023; Rahardja et al., 2023; Zwilling et al., 2022).
Given this situation, it is important to investigate the cybersecurity awareness of Bangladeshi university students who use the internet, especially in light of the students’ incredibly diversified educational background (Hong et al., 2023; Zwilling et al., 2022). Although there are many studies on cybersecurity risks, there is a little empirical study on cybersecurity awareness in higher education, according to the literature. To the best of the authors’ knowledge, no attempt has been made to comprehend how highly educated individuals change after they graduate and enter the workforce (Moletsane & Tsibolane, 2020). Nevertheless, a variety of techniques for evaluating cybersecurity awareness have been presented by the extensive research. The knowledge-attitude-behavior (KAB) model, which has been shown to have high internal consistency and external reliability, has been used to explain cybersecurity awareness and behaviors (Al-Nuaimi & Uzun, 2023; Butavicius et al., 2020; Masudin et al., 2023; Yan et al., 2018). The study is related to investigate cybersecurity knowledge, password security, and self-perceptions of skills.
Since peers have a significant impact on one another’s cybersecurity awareness, it is likely that the more highly educated and knowledgeable internet users with substantially superior cybersecurity awareness (such as university students) would be impacted by their less educated co-workers. This study may make a theoretical, methodological, and practical contribution by offering a novel way to quantify social influence and providing additional insights into its impact on cybersecurity awareness as given the dearth of large-scale studies on internet security awareness and the rarity of comparisons between university students and working graduates.
Literature Review and Hypotheses Development
Cybersecurity Awareness
Programs aimed at raising people’s awareness of cyber security risks and educating them about them should be well-designed in order to equip folks with a fundamental grasp of the subject (Chang & Coppel, 2020). Al-Janabi and Al-Shourbaji (2016) did a study on security awareness in the Middle East, concentrating on educational settings and studying cyber security among academic personnel, researchers, and students. The authors discovered that Middle Eastern participants have a fundamental misunderstanding of the importance of cyber security. Therefore, as part of a comprehensive safety management plan, all users and administrators should receive safety awareness and training. Ahmed et al. (2019) researched cyber security awareness among Bangladeshi citizens and used Pearson’s chi-squared test to analyze the collected data. These conclusions show that the majority of people are ignorant about the threats associated with cybercrime and cyber security.
The majority of academic groups do not actively pursue measures to increase cyber security awareness and training (Scholefield & Shepherd, 2019). At the California State University, Los Angeles, USA, College of Business and Economics, Slusky and Partow-Navid (2012) looked at the outcomes of security testing for a set of students. They found that, contrary to what one might believe, students’ strategies for handling these problems in practical settings are the primary problem with cyber security awareness, not a lack of fundamental understanding. The outcomes were intended to help the college enhance its curriculum, which also included more information security training.
Cybersecurity Knowledge
The understanding of cyber security among college students was examined by Alotaibi et al. (2021). They found that most Saudi university students were not aware of their data protection, which indicated that there is a lack of understanding of cyber security among Saudi university students. Senthilkumar and Easwaramoorthy (2017) investigated university students’ attention to cyber security by looking at them in several of Tamil Nadu’s major cities. They mainly focused on specific cyber security threats including phishing, malware-infected websites, and data theft. Their research revealed that students had a higher than usual level of knowledge of cyber security issues and related threat issues, with 70% of respondents having a fundamental comprehension of the risks involved. In order to ensure that learners can defend their data from cyberattacks, the authors suggested that security awareness and training programs be introduced at a higher level.
In Silicon Valley, California, Moallem (2018) looked into what college students thought about cyber security. The author evaluated the degree of cyber security in the largest and most important technological environment since learners’ behavior is unpredictable. College students were unaware that their data was not securely transmitted between university systems, even while they were aware that their behaviors were being observed and recorded. Institutions should thus routinely give training to students in order to affect their behavior and raise their understanding of the fundamentals of cyber security and cyber dangers (Jia et al., 2018; Kennison & Chan-Tin, 2020; Švábenský et al., 2021). Additionally, Moallem (2018) covered the topic of theft mindfulness and security awareness. According to the author, fraudsters could not always employ the same cyber-attacks. Instead, they alternate between phishing scams, network activity, and other lies. To increase cyber security awareness and secure important data, a strategy must be created. Zwilling et al. (2022) looked into the association between cyber security activity, comprehension, and awareness among users of protection products in Turkey, Israel, Poland, and Slovenia. The results showed that while familiar users had a sufficient understanding of cyber security, it was rarely applied in real-world situations. Students in Nigerian colleges had a rudimentary understanding of cyber security, according to preliminary research findings, but they were unaware of how to protect their data(Catal et al., 2023; Dawson et al., 2022).Several authors have shown experimentally that students with little knowledge may easily be tricked (Aloul, 2012; Gratian et al., 2018). Thus, it was hypothesized that:
H1: Cybersecurity knowledge has a positive and significant effect on cybersecurity awareness among university students.
Password Security
Due to the growing number of passcodes they must remember, users either select straightforward default passcodes (Moallem, 2018) or reprocess their potentially robust passcodes (Szumski, 2018), often with minor tweaks or only by carrying out planned construction activities (Moletsane & Tsibolane, 2020). Data theft is one of the most serious security challenges brought on by passcode repetition. The General Data Protection Regulation (GDPR) of the European Union informs users that they are strongly urged to change their passcodes in the event that a website they often visit is hacked (Mamonov & Benbunan-Fich, 2018; Rathod & Potdar, 2019). Students have a distorted understanding of safety features, according to an American study of users from various backgrounds and ages (Yıldırım & Mackie, 2019). The results of this study show that participants overestimated the security improvement offered by adding digits to their passcodes while underestimated the dependability of using keyboard rhythms and common words. People not only overestimated the increased security provided by adding characters or digits to the end of passcodes, but they also often repeated passcodes or parts of passcodes. The inclusion of personal information in user-selected passcodes is another frequent occurrence (Giannakas et al., 2019; Hartwig & Reuter, 2022).
In a study that looked at over 20 million informational pieces from Chinese users, it was found that professionals employed passcodes with a normal size of 8 to 11 characters whereas students used shorter passcodes. They discovered that less than a third of customers had a mix of unusual typescripts in their passcodes, and that more than half of consumers only had passcodes made up of digits (Wang et al., 2019). According to the report, more than 12% of business users use their birthdays and mobile phone numbers as part of their passcodes, while 11.5% create their passcodes using their login and email. Chinese characters were used 26% of the time in a different study of Chinese passcodes (Wang et al., 2019), either by themselves or in combination with dates and numbers, indicating that English alphabets are most commonly used. Additionally, it was observed that authentic Chinese character logins were made using just two to four Chinese characters (Hatzivasilis et al., 2020; Neigel et al., 2020; Scholefield & Shepherd, 2019). Thus, it was hypothesized that:
H2: Password security has a positive and significant effect on cybersecurity awareness among university students.
Self-Perception of Skills
Self-perception refers to our view of us, our qualities, and our judgments of those features (Arnedo-Moreno & Garcia-Font, 2021). Our self-concept, or the mental image of who we are, and our self-esteem, or how we rate and evaluate those traits, is the two primary perceptual processes that comprise self-perception. Recent studies (Heidt et al., 2019; Herbst, 2020; Singh & Singh, 2022) on self-perception focus on cyber security awareness and decision making demonstrate the topic’s relevance for information system research. However, there is still little study connecting self-perception with information security. The effect of self-perceived and cyber security awareness on the technology usage behavior of business people from India is examined (Aggarwal et al., 2015). The authors demonstrate that there is an association between actual and self-perceived cyber security awareness that is U-shaped. As a result, the Dunning Kruger effect affects those who have the lowest levels of cyber security awareness, who perceive them to be IT experts (Othman et al., 2021).
To examine one’s notion of one’s own familiarity with computer virus, Schmidt et al. (2007) conduct a study involving 64 college students in USA. The students must first complete a survey to measure their self-perceived familiarity with Trojans, spyware, and viruses. Multiple choice questions are then used to assess their real danger awareness. The findings imply that many pupils have a false sense of security. However, the researchers do not discover any signs of overconfidence when they turn their attention to business experts. Wang et al. (2019) explore overestimation and over-precision in the context of phishing email detection. Subjects must distinguish between phishing and legitimate emails. The findings demonstrate that varying attention allocation, dispositional optimism, and familiarity with business entities increase overconfidence, cognitive effort decreases self-perception, while self-efficacy only had a minor impact on the participants’ overconfidence in their ability to detect phishing emails. Accurate detection cannot be predicted by general perception alone. Information security managers’ exaggerated optimism is a topic of research. Thesurvey of business leaders demonstrates an optimistic bias in how they see risk. Those in charge have a false perception of reality because they are unaware of the dangers, believing that their business is less susceptible than others and is better prepared to manage information security risks (Chandarman & Van Niekerk, 2017; Freund et al., 2013; Ortega-Sánchez et al., 2020). Thus, it was hypothesized that:
H3:Self-perception of skills has a positive and significant effect on cybersecurity awareness among university students.
The Role of Cybersecurity Attitude
Research on attitudes has shown associations between positive views regarding cybersecurity awarenessand risky online behavior (Hadlington, 2017; Wong et al., 2022). Higher levels of cybersecurity awareness are associated with cybersecurity knowledge, self-perception skills, and pleasant, open, and conscientious personality traits (Antunes et al., 2021; Jeong et al., 2019). Furthermore, positive attitudes regarding cybersecurity knowledge, coupled with societal and personal standards, might improve one’s ability to perceive one’s own skills and intention to adhere to password security. Attitudes toward employee risky behavior behavior, cybersecurity knowledge, and cybercrime also are noticed in the workplace (Hong et al., 2023). A second revalidation research confirmed the high association between attitudes and self-perception skills to cybersecurity awareness. Additionally, attitudes regarding cybersecurity are important indicators of intention and ultimately lead to pre-conforming action (Jeong et al., 2019; Nunes et al., 2021).
Awareness related to information security, such as students’ perceptions of a privacy breach, may have an impact on attitudes toward awareness (Bhatnagar & Pry, 2020; Pollini et al., 2022). Students’ perception of privacy invasion may raise with greater cybersecurity knowledge capacities. In firms that place a high priority on technological security, attitude has a greater influence on cybersecurity awareness (Li et al., 2019; Onumo et al., 2021). Further evidence that risk perception is domain-specific comes from the positive association between computer use attitudes and self-perception skills. These findings demonstrate that risk attitudes among computer users differ from other, more intimately related self-perceptions and rely on the degree of sensation-seeking the user may be used to (Liu et al., 2020; Creese et al., 2021). Malware-infected machines were typically owned by cusers who felt less risk when utilizing IT. These results demonstrated an unmistakable link between attitudes, risk perception, and computer compromise (Back & Guerette, 2021; McEvoy & Kowalski, 2019). Thus, it was hypothesized that:
H4: Cybersecurity attitude mediates the relationship between cybersecurity knowledge and cybersecurity awareness among university students.
H5: Cybersecurity attitude mediates the relationship between password security and cybersecurity awareness awareness among university students.
H6: Cybersecurity attitude mediates the relationship between self-perception of skills and cybersecurity awareness awareness among university students.
Methodology of the Study
Sample and Data
The study data was adopted from 411 students from five public and private Universities in Dhaka, Bangladesh. A stratified random sample was employed for this cross-sectional study. In this study, smart technology users in the digital transformation phase were chosen as sample respondents. The stratification of a population into smaller subgroups known as strata is an important feature of the sampling approach known as stratified random sampling. The strata are determined by the individuals’ common features or attributes, such as their income or level of education. The strata were selected using educational level criteria.
Data were gathered by research assistants with local training. Before completing the final survey, we distributed this questionnaire to seven academics and academic specialists to measure its readability and reliability. At this time, a few items underwent minor revisions based on feedback from the survey’s pre-test. Ten students looked over the survey to make sure no questions were impossible to respond to. The items, which were adapted from prior studies, were measured using 29 items: four for cybersecurity knowledge, four for password security, four for self-perception skills, five for cybersecurity attitude, and six for cybersecurity Awareness. Each item was rated on a five-point Likert scale, with 1 denoting “strongly disagree” and 5 denoting “strongly agree.” Additionally, section A of the questionnaires contained six demographic details for survey participants. Instructions and a statement outlining the objectives of the study, how data was collected, and how respondents’ privacy would be protected were included with the survey.
In the months of February and March 2022, the survey was conducted. The survey includes a number of factors that affect how university students use technology. During the data collection, every student was personally approached and asked about their knowledge of cybersecurity. Unfamiliar participants with information technology were not permitted to participate. By using this process, the authors were able to get replies from 430 students; however, 19 of those responses had to be rejected since some of the questions hadn’t been addressed. As a consequence, 411 valid questionnaires (86% of the respondents) were acquired from them.
Measurement
A questionnaire that was developed utilizing scales that had already been approved and used in the pertinent literature was used to collect the data. The final survey, which had 29 items, employed a total of five variables. According to Hair et al. (2014), our 29-item survey meets the minimal requirements for a rigorous instrument. The cybersecurity knowledge construct was measured using four items that were taken from Chandarman and Van Niekerk (2017), Kennison and Chan-Tin (2020). To test password security, four items from Alharbi and Tassaddiq (2021) were chosen. Four items from Chandarman and Van Niekerk (2017) were also used to test the concept of self-perception skills. To test the cybersecurity attitude, five items from Chandarman and Van Niekerk (2017) were used. Six additional items from Taha and Dahabiyeh (2021), Al-Janabi and Al-Shourbaji (2016) were also adopted to measure cybersecurity awareness.
Data Analysis Technique
The PLS-SEM technique with Smart PLS 3.3.9 software was used to evaluate the survey data because of the “small sample size,”“non-normal data,” and “complicated models.” Despite the existence of other data analysis methods including correlation, regression, and analysis of variance (Hair et al., 2014), PLS-SEM is often used for quantitative data analysis.
It allows researchers to study the relationship between observed (measured) and latent variables, which cannot be examined using conventional approaches (Hair et al., 2014). The mediator effects may also be computed and immediately incorporated into the model using the PLS-SEM (Hair et al., 2014). A two-stage model comprising measurement model and structural model is used to examine the data. The structural model measures the hypotheses based on the path analysis, whereas the measurement model measures latent variables.
Findings and Discussion
Respondents’ Profile
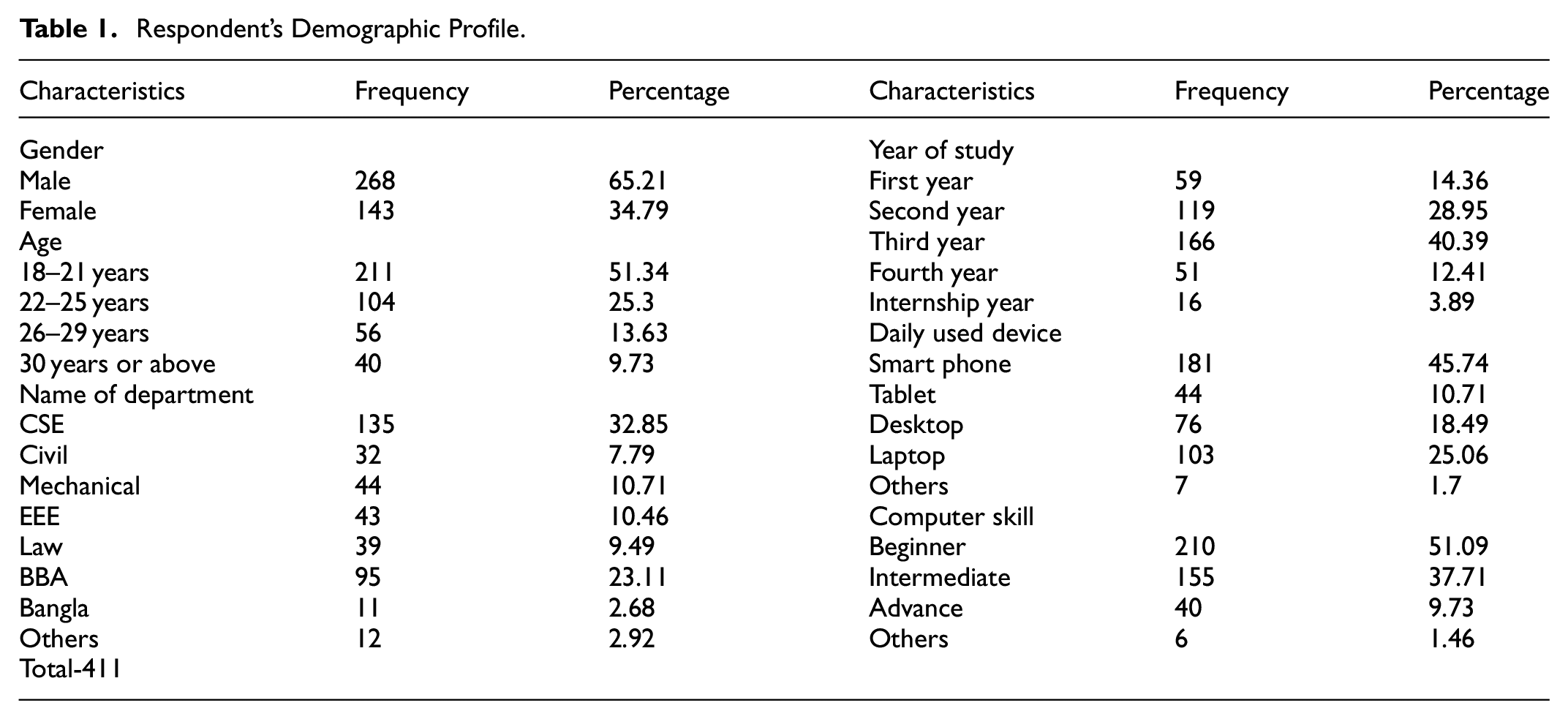
Table 1 paints the demographic profile of the respondents. The study model and findings were verified using data obtained from 411 students at five public and private universities in Dhaka (Bangladesh’s capital city) using Smart PLS 3.3.9. In this experiment, an innovative data collection strategy was used. According to Table 1, 65.21% of respondents were men, 51.34% were between the ages of 18 and 21 years, 32.85% respondents are from CSE department, 40.39% respondent are currently at their third year of academic life, most of the respondents used smart phones daily consisting 45.74%, and 51.09% respondents are the Beginner in relation to computer skill.
Respondent’s Demographic Profile.
Descriptive Correlations
The Table 2 above enumerates the stylized facts of the sampled responses. Of particular interests are the mean, correlation, and standard deviation values. As seen in Table 2, the major research factors (cybersecurity knowledge, password security; self-perception skills; cybersecurity Attitude cybersecurity awareness) have positive relationships with each other.
Descriptive Correlations.

Correlation is significant at the .01 level (two-tailed).
Correlation is significant at the .05 level (two-tailed).
Measurement, Validity and Reliability
Table 3 presents the Measurement, Validity and Reliability of the study model. Each component’s AVE approximation is greater than 0.50, as are the CR and Cronbach’s Alpha numbers, as well as the indicator loadings, which are higher than the acceptable threshold of .60 (Vinzi et al., 2010) (see Table 3). Table 3 reveals that Cybersecurity Attitude has a large effect on exogenous variables (0.535% or 53.5%). Cybersecurity Awareness (0.723% or 72.3%) demonstrates a large influence on exogenous variables (Falk & Miller, 1992). The NFI value is close to 1, indicating that the model satisfies the study’s objectives. The model fit is good as indicated by the SRMR score of 0.08 as well (see Table 3).
Measurement of Model Assessment.

Note. AVE = average variance extracted; CR = composite reliability; NFI = normed fit index; SRMR = standardized root mean square residual.
Table 4 shows that Q2 values are greater than zero which indicates that the model remains predictive relevance (Chin, 1998). The effect sizes (f2) verified that cybersecurity attitude has a medium effect, and cybersecurity knowledge, password security and self-perception of skills have small effects oncybersecurity awareness. Furthermore, cybersecurity knowledge and self-perception of skills have small effects and password security has a medium effect on attitude. Overall, the model determines acceptable fitness and high predictive significance.
Values of the Stone Geisser Indicator (Q2) and Cohen’s Indicator (f2) of the Model in the SEM.
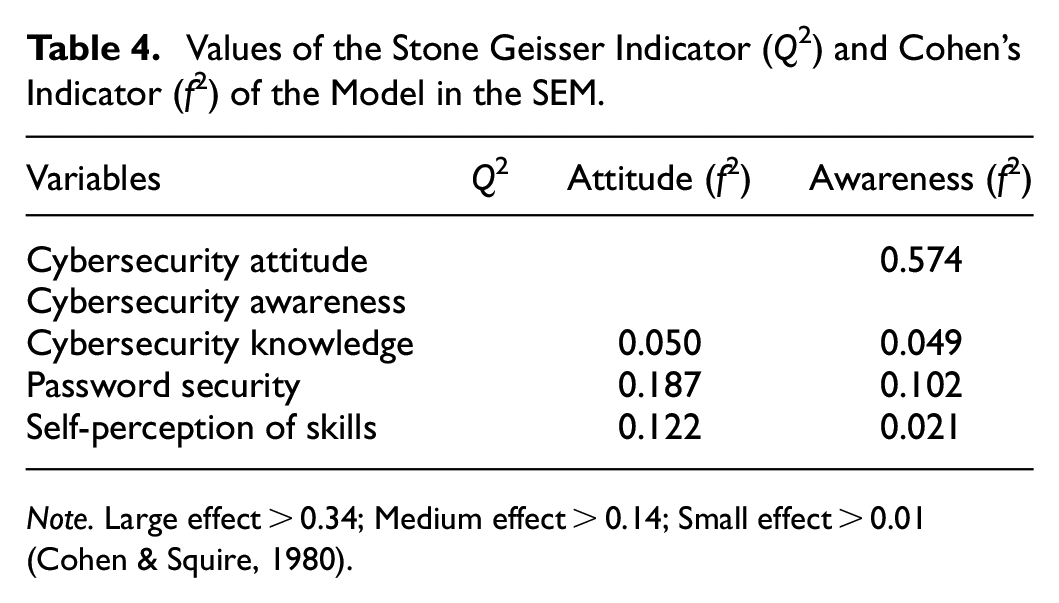
Note. Large effect > 0.34; Medium effect > 0.14; Small effect > 0.01 (Cohen & Squire, 1980).
Discriminant Validity
Fornell-Larcker Criterion Analysis
Table 5 shows the estimations of the relationships between the AVE square roots and the LV (Latent Variables) in the main diagonal of the SEM. According to the square root of the AVE (bolded), that is larger than the correlations between variables and is in the range of 0.724 to 0.848, the Fornell and Larcker (1981) criteria evaluation results in a satisfying discriminant validity assessment.
Fornell-Larcker criterion Analysis for Discriminant Validity.

Note. The diagonal are the square root of the AVE (in bold) of the latent variables and indicates the highest in any column or raw. LV = latent variable.
Heterotrait-Monotrait (HTMT) Analysis
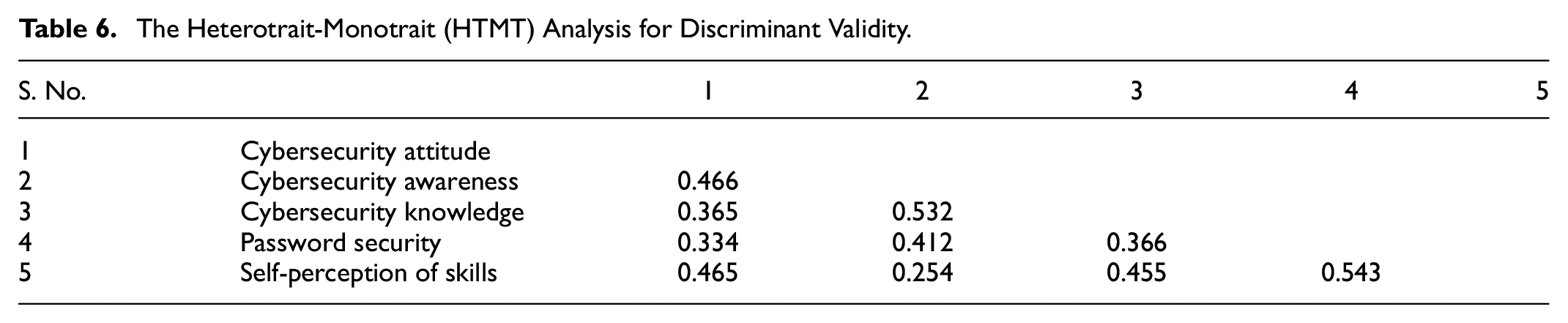
Table 6 shows the heterotrait-monotrait (HTMT) analysis for discriminant validity. To cross-validate the discriminant validity, HTMT values must be less than 0.85. If the HTMT value is less than 0.85, the variables’ discriminant validity has been proved (Henseler et al., 2005).
The Heterotrait-Monotrait (HTMT) Analysis for Discriminant Validity.
Structural Model Assessment
The evaluation of the structural model is yet another crucial step in the validation process. Moreover, t-values and R2 values have also been calculated using the bootstrapping procedure with 4,999 resamples. Figure 2 displays the results of the standard SEM measurement using Smart PLS 3.3.9. All items typically had outer loads that were higher than permitted. Most variables have excellent direction coefficients.

The framework of the study.Note. Figure 1 indicates that each and every variable in the framework influences (namely cybersecuty knowledge, password security, and self-perception of skills) on the cybersecurity awareness among the university students. Later, it is also indicated that cybersecurity attitude mediates the relationships between cybersecuty knowledge, password security, and self-perception of skills with cybersecurity awareness.
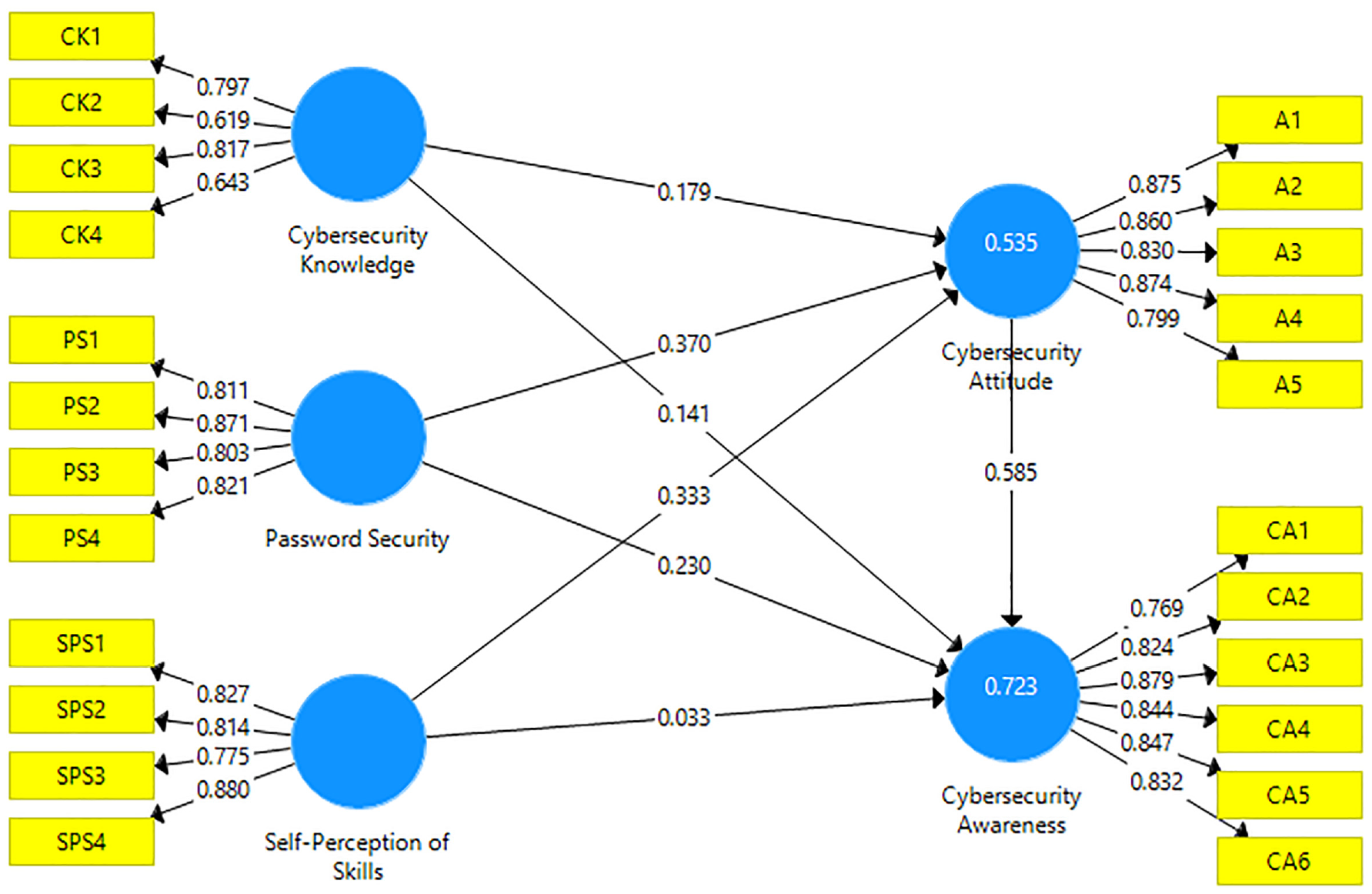
Standardized results of SEM calculations.
Hypotheses Testing (Direct and Indirect Relationships)
The results of the verification of hypotheses are shown in Table 7. In the first hypothesis, it was assumed that cybersecurity knowledge has a positive and significant effect on cybersecurity awareness. As expected, a positive and significant relationship between cybersecurity knowledge and cybersecurity awareness was evidenced (β = .137, t = 2.212, p < .01, see Table 7), supporting Hypothesis 1. The studies of Alharbi and Tassaddiq (2021), Zwilling et al. (2022), and Hong et al. (2023) support this hypothesis.
Results of Direct & Indirect Effect Hypotheses.

Note. CA = cybersecurity awareness.
In the second hypothesis, it was assumed that password security has a positive and significant effect on cybersecurity awareness. The data supported the second hypothesis by demonstrating a positive and significant association between password security and cybersecurity awareness (β = .223, t = 2.262, p < .01, see Table 7). The studies of Senthilkumar and Easwaramoorthy (2017), Alharbi and Tassaddiq (2021), Zwilling et al. (2022) support this hypothesis.
In the third hypothesis, it was assumed that self-perception of skills has a positive and significant effect on cybersecurity awareness. As a consequence of the lack of a significant and positive relationship between self-perception of skills and cybersecurity awareness, hypothesis three was not validated (β = .038, t = 0.401, p > .05, see Table 7). The studies of Chandarman and Van Niekerk (2017), Alharbi and Tassaddiq (2021), Mutunhu et al. (2022) support this hypothesis.
The outcomes of indirect hypotheses are displayed in Table 7. The hypotheses were tested using the PROCESS MACRO software, created by Preacher and Hayes (2004) and Hayes (2013). The PROCESS uses a bootstrapping method to establish confidence intervals for these conditional direct and indirect effects. More specifically, we determined the bootstrapping sample size to be 5,000 and utilized Model 4 from Hayes (2013) to estimate the mediating function, which completely fits our study model.
In the hypotheses fourth, fifth, and sixth, it was assumed that cybersecurity attitude mediates the relationships between cybersecurity knowledge, password security and self-perception of skills with cybersecurity awareness. The finding that cybersecurity attitude mediates the link between cybersecurity knowledge and cybersecurity awareness was verified (β = .114, t = 2.144, p < .01, see Table 7), and this finding supports hypothesis 4. The next hypothesis assumed that cybersecurity attitude mediates the association between password security and cybersecurity awareness, was similarly supported by the data (β = .214, t = 4.509, p < .01, see Table 7). In the final hypothesis, the mediation of cybersecurity attitude on the association between self-perception of skills and cybersecurity awareness is significant (β = .194, t = 3.085, p < .01, see Table 7), hence hypothesis 6 was validated.
Conclusion
The current study has developed a model that takes into account the amount of cybersecurity knowledge, perceived security, and self-perception of skills as well as the linkages of cybersecurity attitude that mediate between those three variables. As a result, depending on the various circumstances of the respondents, three direct hypotheses and three mediation hypotheses were developed.
Research of this kind is becoming more and more crucial as the battle against cybercrime susceptibility and the prevention of cyberattacks with university students shifts focus away from technology. The current study demonstrates how various cybersecurity knowledge, perceived security, and skill perception factors might affect one’s ability to engage in effective cybersecurity awareness. Clearer communications materials or techniques to spread these further may be produced when a more systematic understanding of how people choose to engage (or not) in good cybersecurity awareness practices is developed. For instance, the researchers pointed out that cybersecurity awareness on information security has to go beyond that. It is proposed that in order to get around this, knowledge needs to be relevant, actionable, and focused, and feedback needs to be given so that people may gage how well they are doing. These measures also offer the opportunity to identify those people who pose a larger danger to an organization due to a disregard for proper cybersecurity procedures, allowing for further education or training instead of punishment for these people.
Implications of the Study
While teaching undergraduates about cybersecurity is crucial, this study implies a bigger effort needs to be made to educate the general population about cybersecurity and safe internet usage. Given that they make up the majority of the population and have the power to alter the cybersecurity awareness of the educated, special emphasis should be placed on educating individuals without a higher education. Universities must to take into account providing students with greater training, for instance. They should be aware that students ICT knowledge is important. Given their limited resources, maintaining a campaign to raise awareness of cybersecurity might be a viable plan, as would educate people who lack the necessary ICT expertise. Recent grads, which likely have more expertise about cybersecurity, might be used to persuade more experienced students who may have developed harmful cybersecurity behaviors over time. They could even take on the duty of guiding others toward online safety. However, due to Bangladeshis’ high value of seniority (i.e., length of service) at work, which is also the reason why without such deliberate effort, graduates are obligated to adopt the senior’s working style; this would require significant organizational support.
It would be unrealistic to anticipate rapid fixes for increased cybersecurity awareness given that the quality of national education can only rise over time (Herbst, 2020). Bangladesh’s current plan is to train the public in ICT so that they can impact the next generation. However, it is crucial that the government educate the general population about safe online practices through social media, online marketing, television, government-led speeches and workshops, etc. Existing promotional efforts are insufficient, and risky internet behaviors are widespread in China. Contagious behaviors include reading illicit content and using unsafe websites as sources of information. Even those with advanced degrees may follow suit if enough individuals in the community do the same (Hartwig & Reuter, 2022). In developing countries, social influence is more significant than in developed countries, and it is suggested that governments should be more proactive in promoting cybersecurity awareness on social media, establishing cybersecurity policies, and working with businesses to bring about social change. In Bangladesh, there is still much to be done.
Limitations and Future Directions
This study has limitations, much as previous studies. The current study made an effort to gather a bigger sample in order to address the issue of non-random sampling. The number of responders was varied, nonetheless, as a result of several data gathering challenges. However, the suitably big sample should help to reduce any statistical consequences. Last but not least, it should be remembered that as students go through their academic years, they can have more options to work part-time employment. This element is not taken into account since undergraduate part-time occupations sometimes differ from full-time internships or jobs in terms of character, intensity, and frequency. This study was conducted on one country only. Future studies should consider more countries to compare the cybersecurity awareness. More cities should be considered for further studies that will provide more unique findings.
Footnotes
Appendix A
Author Contributions
Methodology, B.A.; research study, MR.H.P. and results, M.R.H.P.; introduction—review, A.I.K. and A.S.M.S.Z; conclusions, A.I.K. and A.A.F; writing—original draft preparation, M.R.H.P.; writing—review and editing, A.I.K. and management of research project and research resources, S.C.; and M.R.D. All authors have read and agreed to the published version of the manuscript.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The authors would like to thank the Institute for Advanced Research (IAR) of United International University for supporting the research, authorship, and publication of this article (Institute for Advanced Research Publication Grant Ref. No. IAR-2024-Pub-001).
Institutional Review Board Statement
The study was conducted according to the guidelines of the Declaration of Sonargaon University (SU) and approved by the Institutional Review Board (or Ethics Committee) of the Center for Research Consultancy and Training.
Informed Consent Statement
Informed consent was obtained from all subjects involved in the study.
Data Availability
Data is available on request to corresponding author.
