Abstract
Decisions regarding neutralizing airborne threats in the combat environment require comprehensive knowledge of resources at hand and enemy intentions. The complexity of the situation has resulted in the emergence of various models encompassing important factors of threat neutralization. Various characteristics of airborne threats considered important for their assessment have already been identified in previous literature, which include speed, distance, approach angle, maneuverability, and so on. Due to the possible extent of loss to critical assets, literature has emphasized on identifying as many useful characteristics of threats as possible. This study is also a step in this direction to improve the weapon assignment for threat neutralization. Weapon assignment based on a well-calculated threat index is a key to success in military conflicts. The purpose of this article is to identify new factors through the involvement of experts. In this study, a set of factors has been identified through a survey of relevant literature and semi-structured interviews followed by its refinement through a three-round Delphi study. The results suggest that airborne threats are considered different from other threats due to their lethality and consequences. The top-level decision-makers require a comprehensive understanding of the criticality of the situation and the effects of poor decisions. Besides other factors, weapon stock, supply chain information, and analysis of vulnerable assets/points in threat neutralization are critical to accomplish higher efficiency. The shortlisted factors yield a foundation of a comprehensive framework for decision making in a highly dynamic environment of air defense.
Keywords
Introduction
Air defense (AD) means safeguarding the country’s territorial boundaries and air space against the enemy’s threats mostly through the use of fighter aircraft and ground-based AD systems (Delaney, 1990). The prime objective of AD is to detect and deny invaders through effective and efficient resource utilization (Naseem et al., 2017). Decisions to neutralize targets in a dynamic hostile environment are assisted by various optimization algorithm implemented through decision support systems (DSS; Mardani et al., 2015; Roux & Van Vuuren, 2007). Improper decision making has severe consequences which not only result in damage to vulnerable assets/points (VA/VPs) but also loss of costly ammunition (Azimirad & Haddadnia, 2015). In the literature, various techniques have been proposed for optimal decision making, including game theory (Shan & Zhuang, 2013), Bayesian network and fuzzy logic (Johansson & Falkman, 2008), Morkov survivability model (Erlandsson & Niklasson, 2014), two-integer linear programming (Karasakal, 2008), Gray Technique for Order of Preference by Similarity to Ideal Solution (TOPSIS) method (Yun-feng et al., 2011), genetic algorithm, integer programming, greedy algorithm, brute-force algorithm (Bayrak & Polat, 2013), and so on. But the objective of this study is to identify factors which may be used as an input to any technique used or implemented.
Protection of VA/VPs effectively is a vital key performance indicator of threat neutralization (TN) deployed in an AD zone (Bayrak & Polat, 2013; Kharal, 2010). The priority of targets for opposing forces is based on their importance, value, and mobility. Therefore, careful planning and execution is required to utilize and protect these VAs/VPs effectively and efficiently (Kirby & Capey, 1997). The critical factors for making decisions to counter the aerial threats include threat evaluation (TE) and TN with the available resources (Azimirad & Haddadnia, 2015; Bell et al., 2011; Roux & Van Vuuren, 2007; Schwenn et al., 2015). TE is considered as one of the key components of TN and selection of appropriate weapons promptly is the most crucial challenge for decision-makers (Liebhaber & Feher, 2002; Naseem et al., 2017).
TE is based on the critical information of intruder’s approach (direction and speed) and type of weapon (fighter aircraft, missile, or drone) so as an effective response may be generated. The defender must keep contingent alternatives and solutions for unexpected scenarios (Dahlbom & Helldin, 2013; Nasaruddin & Latif, 2013). With advancements in technology, AD decision-makers (including commanders and operators) are assisted with modern equipment yet the whole process of TN is intrinsically risky, cumbersome, and demanding (Roux & Van Vuuren, 2007). Eventually, weapon assignment (WA) decisions are based on TE carried out by humans, assisted by technology to some extent (Deng et al., 2010; Riveiro et al., 2013). The decision-makers base their decisions on available information, understanding of objectives, prevalent strategic situation, and involved risks (Schwarber, 2005). TN efficiency in AD sector is not an easily achievable task (Azimirad & Haddadnia, 2015). Scholars and practitioners have focused on different aspects and proposed different TN models (Table 1). Search for a comprehensive model is a continuous process. This study is also an endeavor to introduce important factors for further improvement of existing TN models for effectivity and efficiency.
Existing Models for TN.
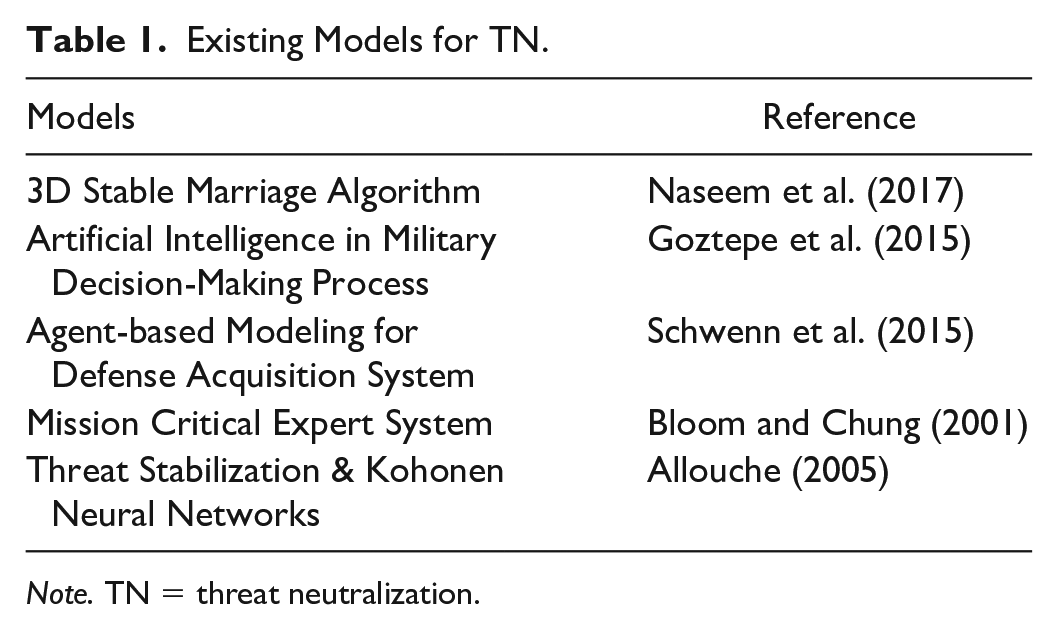
Note. TN = threat neutralization.
TN is performed in a complex time constraint environment during conflicts. The primary goal of TN is to proficiently evaluate the threat and subsequently assign weapons keeping in view the objectives, intent, and capabilities of the enemy’s attack (Hausken & Zhuang, 2012). It comprises two phases: TE and WA. TE is undertaken in three stages: (a) threat perception (TP), (b) evaluation, and (c) prioritization. TP is based on various factors, which include radar-cross section, height, speed, thermal signature, attack approach, heat signatures, dive angle, and maneuvering capability of threat. TE is a complex task which is accomplished by catering to multiple factors including distance, speed, altitude, heading, height, formation, type, and carrying weapons (Govindan et al., 2015; Naseem et al., 2017). Threat maneuvering further adds complexity in evaluation, making it cumbersome and complex task in time constraint environment (Allouche, 2005). It becomes extremely difficult to precisely ascertain the exact destination or target with the maneuverability of threat (Erlandsson & Niklasson, 2013; Phillips-Wren et al., 2009). Threat index (TI) is calculated by incorporating a maximum of TE factors for neutralization of prioritized threats (Azimirad & Haddadnia, 2015; Malik, 2012).
The second stage of TN is WA accomplished in two steps, initially the weapon selection (WS) and then WA (Malik, 2012). The decision regarding WS is made by evaluating various factors, some of which include profile match to threat type, capability, kill probability, and range to neutralize the threat. WA is accomplished under constrained environment by employing multiple sources of information. During time-constrained situations, decision-makers are assisted by using fuzzy decision-making techniques to make efficient and effective decisions (Liebhaber & Feher, 2002). Appropriate weapon is assigned to a threat based on TI and characteristics of weapon (Azimirad & Haddadnia, 2015; Malik, 2012; Naeem & Masood, 2010).
With the advancement in weapons technology, TN has become a challenging task for decision-makers. To counter modern threats, solutions also need to incorporate sophisticated advanced techniques for responding in time-critical situations. Dynamic decision support-based optimal TE and defensive resource scheduling algorithms have gained importance due to effective and efficient results. Threat Evaluation and Weapon Assignment (TEWA) based on such algorithms assures low probability of errors (Naeem et al., 2009). Although several factors for TEWA have been identified in previous studies (Azimirad & Haddadnia, 2015; Dahlbom & Helldin, 2013; Schwenn et al., 2015), yet there exists a room for inclusion and integration of additional factors for better results. Factors such as cost and availability of counter weapons and ammunition have been discussed in previous studies (Bayrak & Polat, 2013; Govindan et al., 2015; Xiaofeng & Shifei, 2012; Zhang et al., 2015), but integrating these factors in TEWA decision-making process remains an area of interest to achieve efficiency (Naseem et al., 2017). Although the cost of safeguarding an important VA/VP may not be given much consideration for wealthy nations but for countries with meager resources, this factor gains considerable importance (Naseem et al., 2017).
Countering the airborne threat has become a challenging task due to rapid advancements in technology (Sahoo, 2016). Efforts are made for early detection of threat with respect to its make and type so as its neutralization may be accomplished through timely WA. Effective radar and weapon deployment (WD) plan can only be made once VA/VPs are determined and prioritized during the peacetime (Malik, 2012; Naeem & Masood, 2010). WD, in general, is scarcely been discussed in the literature due to confidentiality issues (Naseem et al., 2017). It is well recognized that the countermeasures based on the early preparation can decrease the loss to a defender and increase the cost-effectiveness (Paulson et al., 2016). It is generally not possible to determine the exact cost of defending VA/VP in terms of monetary value due to intangible factors of security and safety of life and infrastructure (Yıldırım et al., 2009). Every country makes endeavors to configure and design its AD system so as minimum loss of life and property is assured with the security of VA/VPs at least cost (Hausken & Zhuang, 2012). TN systems have remained in discussion by practitioners and academicians but a comprehensive model to cater for all factors has remained a utopia. The need to incorporate more factors exists for improvement in the decision-making process for TN systems and this study attempts to fill this gap by identification and verification of TN factors through interviews and Delphi study.
Selection of Literature
A systematic search strategy was used to find the maximum studies that have already been done in the last many years directly or indirectly related to TN systems in particular and AD systems in general. While searching the literature, it has been observed that most of the theories for TN have been proposed from the 1980s onwards. Therefore, it was decided to conduct research from 1980 to 2019. The various bibliographic databases were searched including ISI, ProQuest, JSTOR, and Scopus. For the collection of literature, journal publications by famous publishing houses including Sage, ScienceDirect, Elsevier, Emerald, Wiley Online Library, Springer, and Oxford Journals were consulted. To find the maximum relevant studies, selected conference proceedings were also reviewed. The specific keywords for searching TN critical factors included “threat neutralization,” “military studies,” “weapon deployment,” “weapon assignment,” “threat evaluation,” “criticality of VA/VPs,” “weapon selection,” “threat perception,” “logistics,” “air defense,” and “logistics.” To narrow the scope of the literature search, Boolean operator “AND” was used in finding the relevant studies in the search process. The literature from peer-reviewed journals and conferences in the English language were considered. Primarily a total of 63 articles were collected during the search process, with 39 articles identified as potentially relevant to the subject of critical factors of TN. All 39 relevant articles were acquired in full length. Initially, the articles with more citations were analyzed. While analyzing these articles, approximately seven additional references were added to the list by checking the reference sections of cited articles. Thus, a total of 46 articles were reviewed for the study.
Research Method
The methodology to find the TN factors consists of three steps:
Identifying TN factors for decision making (DM) through literature review and developing the first version of the conceptual framework.
Refining the first version of the conceptual framework through inputs and opinions by experts with significant experience in the field of AD using semi-structured interviews.
Conducting three-round Delphi study.
The research process (Figure 1) for the study follows the method used by Frinsdorf et al. (2014) to study critical factors for efficiency in a military environment.

Research process.
Step 1: Identification of TN Factors
TN is a dynamic problem because of the diversity of scenarios, constraints, and evaluation criteria. The prior research on the subject has been consulted to generate an exhaustive list of factors used for decision making. The review of relevant literature resulted in a total of 21 factors broadly categorized in TE, WS, and WA (Table 2).
Factors Extracted From Literature.

Note. TN = threat neutralization; TE = threat evaluation; TI = threat index.
Step 2: Interviews With AD Experts
Semi-structured interviews with experts having extensive experience were arranged to discuss the applicability of factors extracted from literature and identify other factors considered important based on their experience in the field. Because this study has potential to help decision making at the strategic level, efforts were made to select experts for interviews having requisite experience of working at strategic, tactical, and operational levels to have wholesome point of view. These face-to-face interviews helped to establish synchronous communication, which is an instant communiqué between interviewees and interviewers offering clarity and reliability (Conway et al., 1996; Opdenakker, 2006). The interview questions included information about VA/VPs, WD, TP, TE, WS, and WA. The interview questionnaire was developed through consensus of a panel of three experts (not part of interviewees’ panel later on) selected on their experience. The experience-based interview questions generate the higher levels of validity (Pulakos & Schmitt, 1995). A total of eight experts were selected for interviews initially with profiles shown in Table 3. The experience of experts ranged from 11 to 25 years with six out of eight interviewees had worked as commanders at different tiers. Although the interviewees G and H did not work as commanders, they were selected due to being foreign qualified with credible research publications in the relevant field. Both have remained part of a Research & Development department in an AD organization.
Summary of Interviewees’ Profile.

Note. AD = air defense.
Initially, the interviewees were asked to elaborate TN in general. The interviewees D, E, and H referred to the specific definition of TN as accomplishing mission without any consideration of cost (i.e., no matter how much cost is incurred to neutralize the threat). However, all other interviewees agreed that cost-effectiveness must be considered for WA in neutralizing threats. The interviewees A and C raised the concern about appropriate weapon’s availability in inventory and its supply from depot to the required place in a combat situation. Interviewees A and B emphasized on formulating a viable strategy in peacetime to safeguard VA/VPs in war scenario as inappropriate contingency planning and improper categorization of VA/VP result in massive damage.
There was consensus among interviewees that criticality of VA/VPs is a significant parameter for effective WD. This dimension consists of various factors as extracted from literature but interviewees (E and G) emphasized on additional factors like civil infrastructure, power grids, and public buildings. Interviewees D, E, and G pointed out that previous research has mostly focused on TE and WA and less attention has been given to WD which is an important area to achieve success in TN. Interviewees A, B, C, D, and F supported the factors of TP and TE previously identified through literature review, but they also added two more factors (potency of threat and expected damage to an asset if the threat is not neutralized). Interviewees E and H highlighted that WS is more complex than WA and must be given more importance to achieve success. These interviewees emphasized that WS has a critical link with weapons’ inventory and supply information for optimum and cost-effective TN solutions. Their input resulted in adding two more factors to WS list (weapons’ inventory and supply chain). The interviewees A, D, and F endorsed the concept of linking weapons’ inventory and supply with the decision-making process of TN. These factors gain more importance in resource constraint environment (especially time). Interviewee E stated that the national defense matters are not valued in monetary terms, hence minimum consideration is given to cost-effective solutions under threat. Interviewees A, D, E, G, and H attributed the mission failures to poor resource selection of weapons and/or non-availability of the appropriate ones in a combat situation. The interviewees agreed that proper planning in the identification of critical VA/VPs and WD is critical to achieving success in TN. The interviewees also pointed out that significant factors related to cost-effectiveness, WD, and VA/VPs are missing in existing models of TN in AD sector. The input by interviewees resulted in adding more factors related to cost-effectiveness in TN models. In the end, a list of factors related to TN decision-making process was compiled based on literature survey and interviews. The factors extracted from the literature were shared with interviewees before interviews for their information and analysis. Additional factors considered important by experts were categorized and presented in Table 4. Moreover, it was discussed that the factors of TP should be separately analyzed. In TP and TE, four factors are the same, while four factors (identified from literature) were moved from TE to TP. In the next step, Delphi study was performed to finalize and prioritize the TN factors.
TN Factors Extracted Through Semi-Structured Interviews.
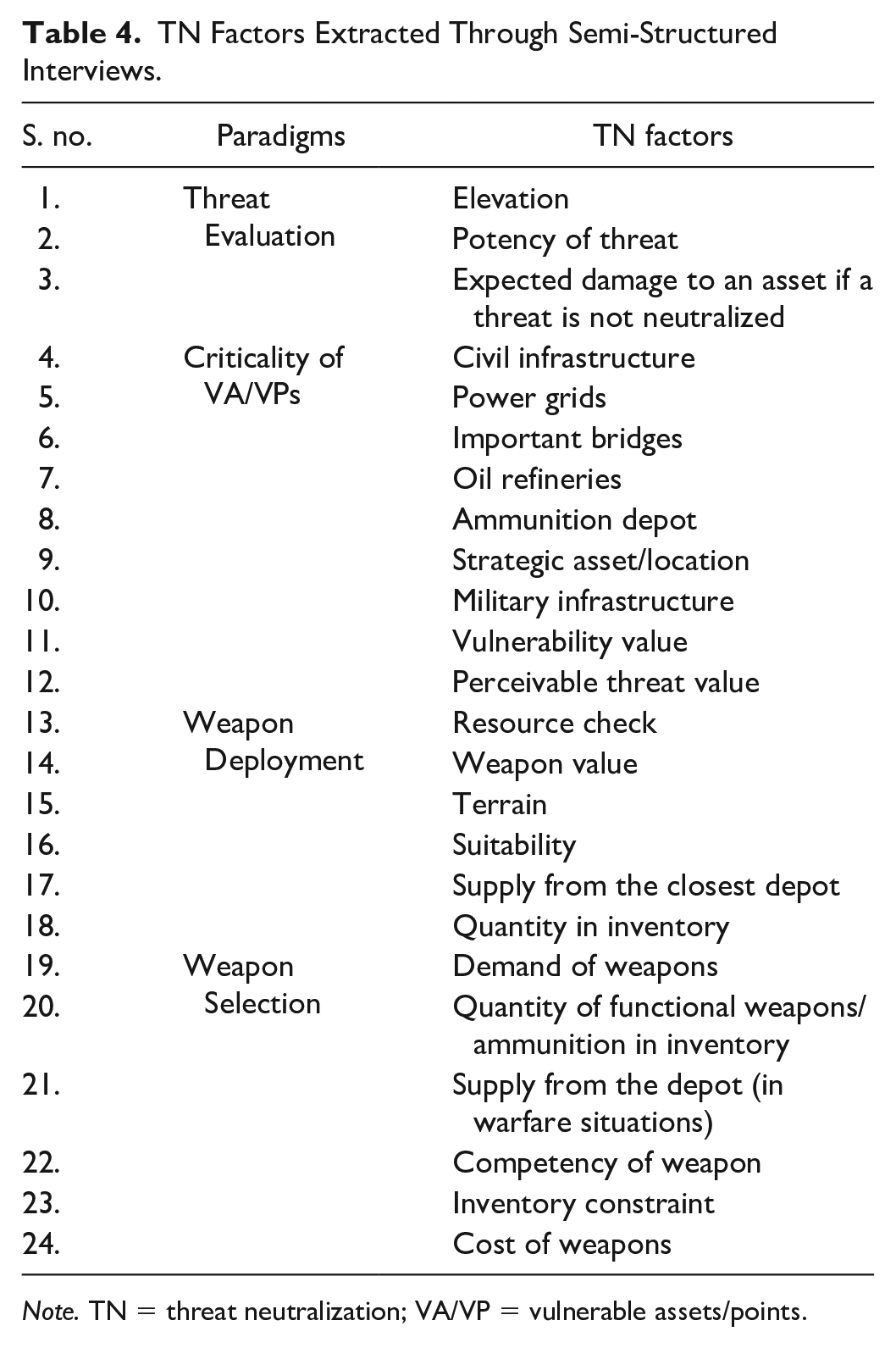
Note. TN = threat neutralization; VA/VP = vulnerable assets/points.
Step 3: Delphi Study
The Delphi technique is an analytical technique based on the judgment of a group of experts with its origin from defense industry (Loo, 2002). The experts’ opinions are carried out in successive, anonymous rounds to achieve a consensus (Turoff & Linstone, 1975). Many researchers have used this method specifically for the framework development, decision making and forecasting, and so on (Chan et al., 2001; Lopez-Catalan & Bañuls, 2017). The Delphi process involves anonymous and controlled feedback of a selected panel of experts (Ameyaw et al., 2016). The factors of TN identified earlier in this study became an input to this Delphi process.
Selection of experts for Delphi Study
There is little agreement in the literature about the size of an expert panel (Keeney et al., 2001). Studies have used different number of experts in Delphi technique ranging from 8 to 40 (Sitlington & Coetzer, 2015). The number of experts depends on numerous factors, such as scope of the problem, the time frame of research, the volume of targeted data, available resources in terms of time, money, and number of available experts in the field (Turoff & Linstone, 1975). The unbiased and accurate selection of expert panelist is one of the most significant aspects of successful Delphi studies (Chan et al., 2001) so special attention was given in choosing the experts. The chosen experts must fulfill certain requirements, such as professional qualifications, working experience, working appointments, and relevant publications (Hallowell, 2008). This study has used expert evaluation system as proposed by Hallowell and Gambatese (2010). Identification of experts was made using snowball sampling technique. The criteria included holding of decision-making position in AD sector, qualification in the requisite field, and academic contribution in the form of articles, book chapters, or editorials. A total of 24 experts were shortlisted according to the criteria and contacted through personal calls and emails. Out of these identified experts, eight experts gave their consent for participation in the study.
Number of rounds/iterations
The Delphi study is generally conducted in multiple rounds. There are two main reasons for it: (a) reaching consensus by decreasing variance and (b) improving precision. The panel experts reach the consensus through anonymous and the controlled feedback process (Hallowell & Gambatese, 2010). No consent on the optimal number of rounds could be found in previous studies. The researchers have conducted various number of rounds based on the required level of consensus ranging from 2 to 6 (Campos-Climent et al., 2012; Turoff & Linstone, 1975). In this study, the Delphi method is conducted in two rounds of data collection and a third round to cross-validate the results. In the first round, open-ended questions were asked to validate the already identified TN factors (through literature review and interviews) and making the list comprehensive by adding additional factors based on the experience of experts. In the second round, experts were asked to rate the factors on a Likert-type scale (1–5). In the third round, experts were asked to evaluate the ratings after randomizing the factors.
First-round Delphi study
In this first round, an open-ended questionnaire was sent to experts and asked to verify the list of critical factors relating to VA/VPs, WD, TE, and WA and write additional factors based on their experience and understanding with brief rationale. The experts completed the first round within 2 weeks resulted in a total of 49 factors critical to TN in AD environment as shown in Table 5. This round helped to expand the number of factors considered essential by the panel of experts in Step 2.
List of TN Factors (Round 1 Delphi Study).

Note. TN = threat neutralization; VA/VP = vulnerable assets/vulnerable points; TE = threat evaluation; TI = threat index.
The redundancy was removed by eliminating the similar factors. Direction of threat factor was removed and only the dive angle of threat was retained in the list. Similarly, threat type (100%) and potency of threat (75%) were found to be similar and so the potency of threat factor was removed. The updated list of factors was prepared and shared with the panel of experts in the second round with the rationale for elimination of factors.
Second-round Delphi study
In the second round of Delphi study, importance rating of factors was carried out by experts using 5-point Likert-type scale from 1 to 5 (1 = not at all important, 2 = slightly important, 3 = fairly important, 4 = quite important, 5 = very important) for the updated list of TN factors prepared after first Round. In Delphi studies, there is no universally defined or agreed cut-off point for the consensus. The applicable measure is to use the mean score as a cut-off point (Choi & Sirakaya, 2006). The average score of all factors is 3.5 and therefore it is adopted as a cut-off point. After this second round, 41 TN factors having the mean scores equal to or more than 3.5 (overall mean) were selected to be included in the final third round for re-evaluation as shown in Table 6.
List of TN Factors (Round 1 Delphi Study).

Note. TN = threat neutralization; VA/VP = vulnerable assets/vulnerable points; TE = threat evaluation; TI = threat index.
Third-round Delphi study
To proceed further, the results of second round were shared with the panel of experts. They were asked to review their previous rating and provide the rating again on the same Likert-type scale. Experts reconsidered their evaluation for a few factors and adjusted their ratings resulted in slightly higher mean scores than the last round. Most of the rankings of TN factors remained stable from second to third round as shown in Table 7. To find out the inter-group comparison, a non-parametric method of correlation analysis (Spearman rank correlation coefficient) is used. The value of Spearman’s rank correlation coefficient beyond the critical value at a certain significance level (e.g., say .01, .02, or .05) shows that there is a harmony between the responses of different groups. This method is used to calculate the degree of consensus between the ratings achieved in second and third rounds. A high number reflects a high degree of consensus (Von der Gracht, 2012). Computed values show a significant relationship and a high degree of consensus between the ranking of second and third rounds.
Analysis of Delphi Round 3.

Note. TN = threat neutralization; VA/VP = vulnerable assets/vulnerable points; TE = threat evaluation; TI = threat index.
Discussion
The purpose of this study was to further the research related to decision factors for efficient and effective TN. The study used the input of experts through interviews and Delphi method. The results not only validate the previous research but also add more factors to be considered for making decision regarding TN. The paradigms related to the traditional concept of mission success including TE, WD, criticality of VA/VPs, WS, and WA for TN were acknowledged by the interviewees and panel experts. The most important factors include “radar-cross section” in TP and TE, “military infrastructure” in the criticality of VA/VPs, “perceivable threat value” in WD, “profile match to threat type” in WS, and “weapon is assigned to a threat based on TE” in WA. The Delphi process helped in the validation of these factors and provided a ranking of these critical factors for making a TN strategy.
The factor of “radar-cross section” is recognized as one of the most important factors in TE which is critical to identify and locate the threat. The wrong perception and/or evaluation of a threat cause worst-case scenario (Dahlbom & Helldin, 2013; Riveiro et al., 2013). Other important factors of TP and TE for getting accurate information of threat include “attack approach,” “dive angle,” “height of threat,” and “maneuvering capability.” The panel of experts also ranked the “identification of friend and foe” high. Similarly, the factors of “speed,” “height,” “distance,” “type,” “formation,” “carrying weapons,” and “threat lethality” are significant in TE. These factors are important for TI to prioritize threats. This reinforces the finding of the literature review that the threats are prioritized based on TE (Malik, 2012; Naeem & Masood, 2010).
The interviewees highlighted the criticality of VA/VPs as an important paradigm. This factor is considered vital for its contribution toward WD affecting whole TN process. The study also ranks different VA/VPs (military infrastructure, ammunition depot, civil infrastructure, power grids, oil refineries, important bridges, etc.) for their criticality and importance. The study highlights various critical factors in WS and WA which include “profile match to threat type,” “range to neutralize threat,” “kill probability,” “capability,” “quantity in inventory,” and “supply from depot.” Deployed AD system needs to consider the interdependencies of these factors so as a response to incoming threats may be made depending on the available resources.
Conclusion
In the rapidly changing world of technology, the concept of TN in AD sector is evolving continuously, thus extending from a traditional concept to more agile and rapid response considering the orientation of WD and criticality of VA/VPs. TN, in wartime, is a crucial and time-critical activity and there is a dearth of studies exclusively in the field. Although previous studies have suggested various models, findings of this study provide information relating to additional factors which if incorporated in the model will enhance the effectivity of model. This study investigates TN efficiency issues in the AD environment via semi-structured interviews and the Delphi study. These results show that it is no longer sufficient to simply focus on TE and WA factors to achieve efficiency and effectiveness in TN. Rather, it is also important to pay attention to the criticality of VA/VPs and WD. Indeed, efforts are required to develop an efficient and effective TN model based on the identified factors to increase the success rate with the best utilization of available resources. The limitations of the study are related to data and validation. The empirical data for the study was not available due to the sensitive nature of information, which could have been used for the formulation of a model based on results. The other limitation is related to validation which could only be possible if the model is implemented in AD system. Nevertheless, this study provides a useful reference for the improvement of decision making in AD sector. Identification of TN factors for DSS has been carried out through the involvement of experts in the study. In future, DSS based on optimization algorithms may be tested using identified factors and simulation results may help to eliminate redundant factors.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
