Abstract
Social media, and Twitter in particular, have become important sources for journalists in times of crises. User-generated content (UGC) can provide journalists with on-site information and material they otherwise would not have access to. But how they source and verify UGC has not yet been systematically analyzed. This study analyzes sourcing and verification practices on Twitter during the Brussels attacks in March 2016. Based on quantitative content analysis, we identified (1) the journalists and news organizations sourcing during the attacks, (2) classified different forms of sourcing and verification requests, and (3) analyzed the sourced UGC. Results show that sourcing on Twitter has become a global phenomenon. During the first hours of the attack, journalists rely on UGC. Their sourcing and verification practices vary widely and often lack basic verification procedures, which leads to a discussion about the ethical implications of sourcing practices.
On 22 March 2016, just before 8:00 a.m., two bombs exploded in Zaventem Airport in Brussels. A few minutes later, the first pictures from the airport started to circulate on Twitter. One of the most shared tweets, posted by Anna Ahronheim (a journalist herself), attracted the attention of many journalists on Twitter. In the video, the destroyed front of the airport is visible, and panicked people are running away from the building. Subsequently, Anna Ahronheim received many requests from journalists who wanted to use the material in their coverage, and the video, attributed to her, quickly made its way into live coverage on TV and online news pages. A few hours later, after the video had already been aired on TV, Ahronheim tweeted again to clarify that she did not record the video herself, that it was shared with her in a WhatsApp group, and that she did not personally know the source (Galvin, 2016). However, while her original tweet had already been shared over 20,000 times at this point, her clarification did not attract much attention. Even months after the attack, the video with the wrong attribution was still visible in international media outlets such as Mail Online and Le Monde.
This example illustrates many of the aspects we are concerned with in this article. In times of crisis, journalists have always been pressed to react quickly—a pressure that has increased considerably in 24/7 online news environments, in which competition is constantly present (Van der Haak, Parks, & Castells, 2012). Being quick is seen as paramount in many news organizations—but aiming for quickness also puts journalists in a dilemma. Established criteria for journalistic quality control, of source identification, verification, and even information about being the object of coverage, are in danger of being compromised or, sometimes, even jettisoned. This loss of quality is not surprising since newsrooms have shrunk significantly in most media organizations (Klinenberg, 2005), workloads have risen, and the time available for research has decreased considerably. The pressure for journalists to react quickly and the worsened conditions to do so are particularly problematic when online sources need to be verified. “Networked journalism” (Van der Haak et al., 2012) allows journalists to access a large number of sources on the Internet and particularly on Twitter, and to do so quickly. Such online sources are often not recognized, established institutions, but individuals whose abilities, intentions, and honesty are often less clear.
Evidence for sourcing and verification on Twitter has been found in previous studies by surveying journalists (Heravi & Harrower, 2016), analyzing news organizations’ general verification, and sourcing practices of user-generated content (UGC) (Bruno, 2011) or in content analysis of tweets from a few journalists during crisis situations (Hermida, Lewis, & Zamith, 2014; Vis, 2013). Still, no study so far has analyzed journalists’ sourcing and verification practices on Twitter during a crisis event in a systematic way and on a global scale. This study attempts to do so by pursuing three goals: First, we assess to what extent the sourcing and verification on Twitter have become a global practice and how the observed media organizations and employees making use of these practices can be characterized. Second, we analyze a large sample of requests by journalists in the form of replies, thus specifically describing the sourcing and verification process on Twitter and measuring the speed of this action. 1 Third, we investigate the sourced content and explain why some content receives more attention than other. Choosing a crisis like the Brussels attacks allows us to assess whether professional norms are met when journalists source and verify over Twitter in situations of high pressure and uncertainty and to identify possible ethical conflicts that arise in such situations.
Conceptual Framework: Journalism, UGC, and Crises
Changing Journalism
Online media have changed journalists’ professional routines in various ways, two of which are related to Twitter use. First, many journalists in Western countries have a Twitter account and use it quite actively (Artwick, 2013; Vis, 2013), for example, to live-tweet news events or retweet citizen voices (Artwick, 2013; Hermida et al., 2014). Second, Twitter constitutes an additional means for journalists to source information for their daily work (Broersma & Graham, 2012). This also happened during the Brussels attacks. A recent review showed that journalists frequently use online sources for their research and that Twitter is particularly popular among those (Lecheler & Kruikemeier, 2015). Online sources like Twitter have become increasingly important, making it easier for journalists to research certain issues and quickly obtain information (Moon & Hadley, 2014). Journalists pick tweets and use them as triggers for articles or broadcasting segments, as illustrations of news events, or as stand-alone quotes (Broersma & Graham, 2012; Metag & Rauchfleisch, 2016).
Research has shown that context matters for these sourcing practices. Journalists’ attitudes toward the use of social media differ across countries (Gulyas, 2013) and organizations. Approaches to social media as news sources, for example, differ between the BBC, the Guardian, and CNN, with CNN being much more open toward UGC as a source (Bruno, 2011). Also, public relations officers at different news outlets revealed different social media strategies (Bloom, Cleary, & North, 2015).
Twitter becoming an established and widespread tool has led to frictions between professional journalistic norms and the way online and social media are being used: “Online-related norms and standards such as the prioritisation of speed and immediacy, as well as click rates, are becoming a central benchmark for the entire newsroom” (Hofstetter & Schoenhagen, 2017, p. 13). This might lead to standard journalistic practices being neglected or not being followed any longer. To solve this conflict, news outlets developed social media guidelines, including specific guidelines for journalists’ use of Twitter (Canter, 2015; Opgenhaffen & Scheerlinck, 2013).
Verification and UGC
These general changes in journalism already outline the importance of UGC in contemporary news reporting and the necessity of the respective technical expertise to make use of UGC for journalists (Thurman, Cornia, & Kunert, 2016). Surveys and interview studies have documented that sourcing and verifying UGC have become an important part of the journalistic profession (e.g., Brandtzaeg, Lüders, Spangenberg, Rath-Wiggins, & Følstad, 2015; Heravi & Harrower, 2016). However, UGC is a double-edged sword for journalists: On one hand, it gives journalists the opportunity to diversify their news reporting and offer new perspectives (Matthews, 2013; Wardle & Dubberley, 2014). On the other hand, it challenges verification as a core function of journalism. This feature is crucial because verification is “a normative practice by which journalism has sought to differentiate itself from other forms of public communication” (Zeller & Hermida, 2015, p. 111). Then again, journalists more often turn to Twitter for sourcing than verifying UGC because verification is time-consuming (Heravi & Harrower, 2016).
Confronted with this new challenge, news organizations and journalists have developed coping strategies affecting organizational as well as individual working routines (Bruno, 2011; Hermida, 2012; Hermida et al., 2014). Even traditional news organizations such as the BBC had introduced organizational changes when they were first confronted with UGC. One of the first times UGC appeared in mainstream media was during the London bombings in 2005 when the BBC, for the first time, showed images in their news reporting that were not filmed by BBC cameramen or camerawomen (Wardle & Dubberley, 2014). This event also led to the BBC establishing a permanent UGC Hub and to first discussions about the basic principles of verification practices, which were created at the time and remain the same until today (Barot, 2013). According to these rules, journalists have to establish the origin of an image, confirm the location and time a picture was taken, verify the content of the picture, and obtain the permission of the author of a picture. Similarly, the social media guidelines of other news organizations have been aimed at standardizing verification processes when Twitter is used as a source. These verification methods differ, however. Some news organizations have established a two-tier verification process which allows, for example, that unverified information can be tweeted but information that appears in the outlets of the legacy brand—for example, the newspaper itself or its website—needs to be verified in a traditional journalistic manner (Canter, 2015). These guidelines also include that journalists need to identify themselves as journalists working for a specific media outlet on Twitter (Canter, 2015).
In recent years, media organizations have started to rely on UGC sourced by news agencies, as they can guarantee verification (Matthews, 2013; Wardle & Dubberley, 2014). News agencies such as AP have approached UGC verification and its legal implications more professionally because they eventually redistribute their sourced content (Wardle & Dubberley, 2014). In addition, startup news agencies like Storyful or Fresco that specialize in UGC verification have emerged (Al Omran, 2014).
In sum, source verification is still at the core of the journalistic practice. This is not surprising as the discipline of verification separates journalism from other forms of communication such as propaganda or fiction (Kovach & Rosenstiel, 2014). Still, recent survey data show that 25% of UK journalists (Thurman et al., 2016) believe that it is justified to publish unverified content at least occasionally. Similarly, a “tweet first, verify later” approach (Bruno, 2011, p. 66) might release the time pressure journalists face nowadays, particularly online—but, as we pointed out earlier, it can have adverse legal or reputational consequences for the organization or the individual if the information proves wrong.
There is a rapidly growing literature on sourcing and verification of UGC in journalism, which indicates that the practice has reached mainstream media in the offline world (e.g., Bruno, 2011; Heravi & Harrower, 2016; Silverman, 2013). Studies mainly conducted qualitative interviews (e.g., Brandtzaeg et al., 2015; Wardle & Dubberley, 2014; Zeller & Hermida, 2015) or standardized surveys with journalists (e.g., Heravi & Harrower, 2016). Some scholars have also analyzed UGC used in the media or focused on UGC verification in news organizations (e.g., Bruno, 2011; Wardle & Dubberley, 2014).
Surprisingly, however, sourcing and verification practices during times of crisis—when the urgency to be quick and contribute to the news cycle is even more pronounced for journalists—have not received much scholarly attention yet. In one of the few studies on the use of UGC in crises, Vis (2013) analyzed the Twitter use of two journalists during the UK riots 2011. In her study, verification was only observed in a few tweets. Hermida et al. (2014), who analyzed the sourcing practice of Andy Carvin on Twitter during the Arab Spring, is one of the most detailed analyses of Twitter-based sourcing. However, while the analyzed content is vast, the study only examines one single journalist who, as a social media strategist, does not represent the average journalist on Twitter and can thus only be considered as a particular case.
Systematic analyses of journalists’ Twitter verification practices from different contexts are lacking, however. Therefore, we will focus on the sourcing and verification practices of a large number of journalists on Twitter during a crisis event. As it is challenging to identify the actual use of social media in journalists’ news routine through surveys and interviews (Zeller & Hermida, 2015), we will analyze journalists’ Twitter data, thereby adding to the understanding of how journalists use social media in news routines.
The Role of Twitter in Crisis Journalism—And the Case of Terrorist Attacks
Social media and Twitter, in particular, have become important sources for journalists, especially in times of crises. They can provide eyewitness images and videos, provided by “citizen journalists” or “citizen photographers” (Patrick & Allan, 2013), which have become a major part of crisis reporting (Anden-Papadopoulos & Pantti, 2013). During catastrophes, conflicts, or wars, journalists are confronted with high degrees of uncertainty, often have fewer sources available, are sometimes unable to be on the ground as events unfold, and therefore turn to social media such as Twitter for information and perspective (Hermida et al., 2014; Papacharissi & de Fatima Oliveira, 2012). In conflicts like in Syria or Iraq, journalists rely (more) on colleagues who are in place or on domestic sources (e.g., Plotkowiak, Stanoevska-Slabeva, Ebermann, Meckel, & Fleck, 2012). This is even more pronounced for unexpected, breaking news events for which journalists cannot prepare in advance. In such situations, Twitter can become an especially valuable reporting tool (Bruno, 2011; Vis, 2013; Wardle & Dubberley, 2014). Some events appear on social media before they are taken up by newswires (Petrovic, Osborne, Mccreadie, Macdonald, & Ounis, 2013), enabling journalists to react more quickly to them.
Terrorist attacks—that is, the intentional use of physical force by non-state actors against “soft targets” such as civilians (cf. Gerhards & Schäfer, 2014; Tuman, 2003)—are particularly relevant and fitting cases for such analyses. First, they intend to be more than mere acts of violence. Terrorist attacks have been described as a “communication strategy in which messages are sent in a spectacular way” (Münkler, 2005, p. 177) to politicians and citizens or particular countries and regions. These messages aim to resonate beyond the immediate victims of the attacks; they are intended to frighten populations and by doing so, often, to influence decision-makers and elites (e.g., Meggle, 2005; Tuman, 2003). The distribution of these messages relied to a significant degree on legacy media previously but increasingly relies on online and social media. Second, terrorist attacks are unexpected crises for which journalists cannot prepare. Accordingly, they provide excellent cases along which journalists’ sourcing and validation patterns can be analyzed.
Research Interest and Research Questions
Since a systematic analysis of UGC and Twitter verification practices of a larger population of journalists during crises events is still missing, we will provide a study of global journalists’ Twitter communication on the terrorist attacks at Brussels in March 2016. It is an appropriate case because most of the pictures and videos of the event that media used in the early stages of their coverage originated from Twitter. Additionally, the timing of the event made it more likely to observe journalists from all around the world. With today’s 24-hr news cycle and the high level of professionalization of newsrooms in the United States, we can also expect many US journalists in our sample. 2 The first two bombs detonated 7:58 a.m. CET in the departure hall of Zaventem Airport in Brussels. The second attack followed at 9:11 a.m. CET in Maalbeek Metro station. UGC content appeared quickly in the media after the detonation of the first bomb (Galvin, 2016). Scrutinizing Twitter communication around the Brussels bombings, we will focus on three research questions.
Large news organizations from the West, which are at the forefront of digitalization, have already adapted their organizational structure to cope with UGC and adopted different verification procedures (Bruno, 2011). However, similar trends can also be observed in the Chinese context where journalists and citizen journalists use Weibo to source and verify content (Cui & Lin, 2014; Rauchfleisch & Schäfer, 2015). Besides geographical differences, we also expect organizational diversity as previous studies indicated (e.g., Wardle & Dubberley, 2014):
RQ1: Which media organizations and journalists used Twitter actively to source and verify content during the Brussels attack?
We analyze whether verification and sourcing practice matches the proposed best practice (Barot, 2013; Silverman, 2013) and whether different types of sourcing practice can be identified. As we argued before, during crisis events, sourcing of UGC becomes most likely a priority because information through more traditional channels is not available (Wardle & Dubberley, 2014). Furthermore, previous case studies have shown that in the aftermath of a crisis fake pictures circulate in the online space (cf. Matthews, 2013; Zubiaga & Ji, 2014). Therefore, verification is of utmost importance during crisis events. Still, Twitter is mostly used by journalists for sourcing without a strong focus on verification (Heravi & Harrower, 2016). In our study, we are specifically interested in the breaking news phase when speed is crucial, which might pose an even greater challenge for journalists to adhere to their usual verification norms:
RQ2: How did journalists verify and source UGC on Twitter during the Brussels attack?
Finally, we analyze what content is being sought and potentially verified on Twitter. In light of studies showing that media coverage of terrorism focuses on specific attacks (e.g., Weimann & Brosius, 1991) and portrays them using depictions of victims and destruction, of the (potential) perpetrators, and of political and societal elites evaluating and condemning terrorist attacks (e.g., Gerhards & Schäfer, 2014), we will analyze what specific UGC journalists request and aim to verify:
RQ3: What content and information were sourced over Twitter during the Brussels attack?
Data and Method
Data Collection: Analyzing Twitter Communication During the Brussels Terrorist Attacks
The data collection for our study was quite challenging because sourcing requests from journalists cannot be identified through hashtags or keywords. Using a sample of journalists is a more feasible strategy but would probably not have given us access to all replies during an event because we hardly know in advance which journalists in the world will be actively sourcing tweets during the event. Therefore, we decided to use highly demanded tweets containing UGC during the incident as a starting point to identify journalists. Through multiple steps, this strategy eventually allowed us to access even source tweets that could not have been collected through a keyword search.
We collected the data from Twitter during the Brussels attack in four steps. In a first step, we used Twitter’s application programming interface (API) to download all tweets from 22 March 2016 that contained “Brussels” as a word (n = 4,068,904 tweets). Subsequently, we identified the two most popular (received number of retweets) tweets for both attacks which were posted in the first 30 min after each attack and contained UGC. Additionally, we included a tweet that was posted later than 30 min after the first attack but included one of the most widely used pictures in the press. In a second step, we downloaded all replies that were addressed to these five tweets and filtered out all replies with general comments from non-journalistic accounts that were not relevant for our analysis. Based on this collection of tweets, we downloaded all user information which was used as a data set for RQ1. Of the 115 users, 105 were journalists or media organizations. In a third step, we downloaded all replies written by these journalistic accounts on March 22, 2016, and used it as a data set for RQ2 (n = 617 relevant replies). In the last step, we downloaded all unique tweets that were addressed by these 617 relevant replies. This last step provided us with a data set of 243 unique tweets that contained potential UGC for RQ3.
Methods: Content Analysis of Twitter Communication
For each of our three datasets, we created a specific codebook.
RQ1: Journalists
In our first content analysis, we analyzed the journalistic accounts. First, we coded the type of account, the gender, the location of the person (first location in account), media type, country of media organization, job position (if mentioned in the description), and the professional area of responsibility.
RQ2: Replies
After filtering out all irrelevant replies (not related to the Brussels attack), we coded in a first step what the journalists requested. This could be content—(1) video, (2) picture, or (3) text—or (4) a general request for information.
For the content analysis of the replies from journalists, we used the recommended verification steps for UGC by the BBC that have emerged as basic, platform-independent principles: (1) establish the source (owner) of an image or video, (2) confirm the location and time the image was taken, (3) confirm the content of the picture, and (4) obtain the permission and rights to use the image or video (for an overview, see Barot, 2013).
Additionally, we also coded the politeness of a request. We differentiated between (1) normal and (2) polite. We classified a tweet as polite if a journalist also asked about the safety and general well-being of a user. The last characteristic is an aspect that is also highlighted by the BBC for situations in which a user could still be in danger (Barot, 2013).
Journalists had no direct follower relationship with citizens before the event and had to rely on replies as a first communication channel. Twitter’s character limitation makes it difficult to use it for longer conversations. Therefore, we also coded what other direct contact information journalists added in the replies—(1) email address, (2) direct messages/following back, or (3) phone number—as an indicator of their willingness to engage with their sources for the sake of research and verification.
RQ3: Sources
In this part of the content analysis, we coded all relevant tweets that received replies from journalists. We used some variables from prior studies about terrorism (Gerhards & Schäfer, 2014; Weimann & Brosius, 1991). We first coded the type of user who wrote the original tweet. Then, we focused on the three possible source elements of a tweet: text, picture, and video. Apart from the location variable, all following variables were coded as binary variables (0 = not mentioned/depicted, 1 = mentioned/ depicted). Our first variable was the authentic on-site perspective. For text, we assessed whether the tweets indicated that a person is on-site. Pictures and videos had to have an on-site perspective to be classified “on-site.” Victims as a general category were coded if people were running and/or showed strong negative emotions (e.g., were crying or showed strong signs of despair). Additionally, we also coded fatal victims (e.g., if dead body remains were visible or it was explicitly stated in the text of a tweet) and injured victims. For videos and pictures, we also coded if the victims depicted could be identified (e.g., the face is clearly visible).
In a next step, we analyzed whether the bomb was mentioned/depicted, whether indicators of the attack were mentioned/depicted (e.g., fire, smoke, debris, injured victims, etc.), and for pictures or videos if they showed a chaotic situation (e.g., panic and non-normal behavior, destruction). For the text, we coded whether affective language was used (e.g., “Horrible scenery”). Eventually, we coded whether helpers and security personnel were mentioned or depicted: non-professional helper (civilians), professional rescue workers, security force (police), and military.
Intercoder Reliability
One coder mainly coded the data for all three analyses. In a pretest, two coders coded a sample of tweets. 3 Variables with low intercoder reliability were additionally reviewed after the initial test, and some clarifications were added to the codebooks. 4 To measure intercoder reliability and assess the validity of the data analysis, we then randomly selected 10% of the cases from each data set that were coded by both coders (12 accounts, 62 replies, and 25 original tweets). Almost all of our variables for all three parts yielded reliable measurements (Krippendorff’s alphas >.8). 5
Results
RQ1: Characteristics of Journalists Using UGC on Twitter
We identified relevant journalists by their replies to the most relevant tweets about the Brussels attacks. This led us to 105 Twitter accounts, 14 of which were organizational accounts (e.g., BBC) and 89 of which were accounts of individual journalists (two were categorized as “other”). Of the individual journalists, 54% were female and 47% male users.
These accounts mainly originated from the Northern hemisphere and English-speaking countries. Most requests for information or content came from UK-based media organizations (40%). With 30 unique accounts (97%), London was the most frequent city. US-based media organizations were second (17%), followed by France (12%) and Ireland (6%). Paris with nine journalists and New York as well as Dublin with five are other noteworthy locations (see Figure 1).

Color indicates the number of media organizations in a country; points show the location of journalists, and word clouds visualize all names of media organizations from Northern America, Europe, and the Asia-Pacific Region. The size of the names visualizes the relative frequency of a news organization in each word cloud. E.g., BBC was active with four individual accounts.
Most of the journalists work for TV (44%), followed by print media outlets (22%). Newswire and online only media are equally often represented (12%). The majority of the journalists (66%) describe themselves as general journalists, with 14% specializing in video journalism and 13% in pictures.
Additionally, we captured the job titles of the journalists if they were mentioned in their account descriptions. Even though it is difficult to compare the job positions in different media and newsroom cultures, the data clearly show that most of the analyzed accounts belong to journalists beyond entry- or junior-level in their respective organization. For example, among the journalists working for TV, one-third of the journalists work at least at the level of a producer in our sample, whereas only one journalist on the assistant level could be identified. Only three journalists in the entire sample were interns or trainees. Summing up, we are mainly talking about Anglophone male and female general journalists working mostly for TV, print, or news agencies who tried to get information and content from Twitter during the attacks in Brussels.
RQ2: Sourcing and Verification
For the content analysis, we identified 617 relevant tweets. 6 In 555 (90%) of these tweets, journalists requested information or content. Additionally, we identified 62 (10%) tweets in which journalists thanked users after they had agreed to a journalist’s request. As shown in Figure 2, a large share of all sourcing and verification activity occurred very quickly, within the first 3 hr after the initial attacks. Almost 80% of all replies were written before 11:00 a.m. Of the journalists, 70% were already using Twitter to request content after the first attacks and before the next attack in the Maalbeek metro station. After 11:00 a.m., only 5% of new unique journalists wrote replies in our sample (see Figure 2).
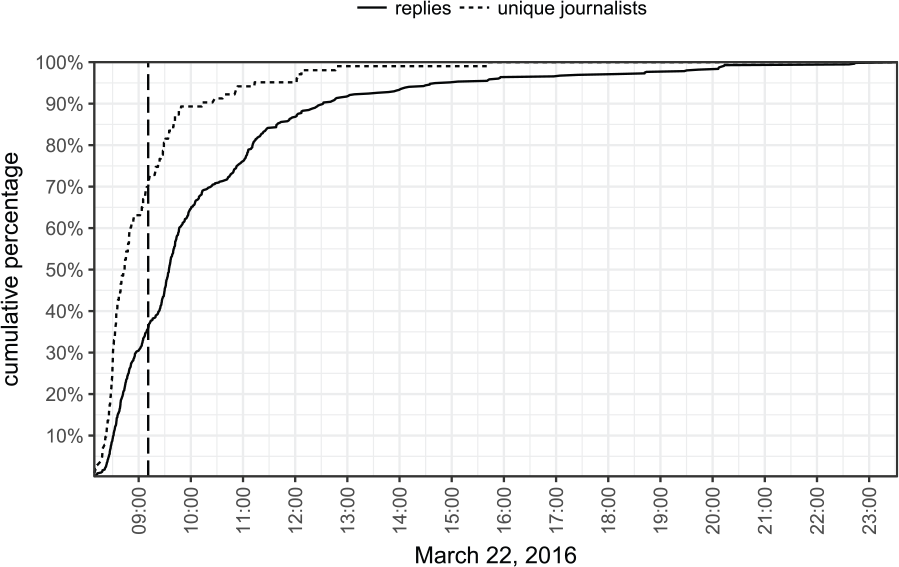
Cumulative percentage of the relevant replies and unique journalist. Dashed horizontal line indicates the moment of the second attack in the Maalbeek metro station.
The most requested content category was pictures (44%), followed by videos (26%). In 37% of the replies, journalists asked for general information about the attacks. We coded up to three verification requests per reply. In 62% of the tweets, journalists requested the right to use a picture or a video. Of the tweets, 7% had additionally a legal information attached to the tweet in the form of an image (see Figure 6) or as a hyperlink leading to a page from the news organization with detailed legal information. In 25% of the replies, journalists tried to verify the source of the content, for example, asking the person who posted a picture or a video whether they took it themselves. For example, one journalist tweeted, “Hi I work for @NBCNews. Did you take this? Does NBCU have permission to use for all partners + platforms?” A few organizations even tried to purchase UGC: “Hi! Journalist at Ruptly News Agency. Do you own the rights of the video? We’ve [sic!] interested in purchasing your video.” In contrast, verification of the location of a source could only be observed in as few as 9% of the replies. 7 Typically, such requests asked specifically about the current location of a user: “Are you outside the metro station? I am a producer with @CNBCi. Can we talk?” Only in 1% of the replies journalists attempted to verify the content. In such replies journalists tried, for example, to verify the location of the depicted content (e.g., “is this your video, is it the Maalbeek metro station?”) 8 or tried to verify when the picture was taken (e.g., “can you confirm that this picture is from today”).
In a next step, we analyzed whether contact methods were evenly distributed over the different forms of request. Our results clearly show that very few contact information was added to requests for pictures (10%) or videos (10%), whereas in over half of the replies requesting general information (56%) contact information appeared. Overall, however, only a small number of journalists, 36, added contact information: 18 unique journalists added their phone number at least once, 4 included their email address, and 18 asked for direct messages as a private form of Twitter communication.
In Table 1, we combined the sourcing and verification requests with the different content and information requests. A comparison of the two results reveals that most replies sourcing pictures or videos requested the right to use the content. Replies with a verification attempt of the source, however, appeared only in one-third of responses requesting videos or pictures. By contrast, only a few instances of content verification were observed. Verification of the location of a user appeared, if at all, in 21% of the replies asking for general information, but almost never in replies asking for videos or pictures. Legal information was only added by five different journalists, who are mostly working for (digital) news agencies, in around 10% of the replies asking for videos or pictures.
Cross table with sourcing and verification requests.
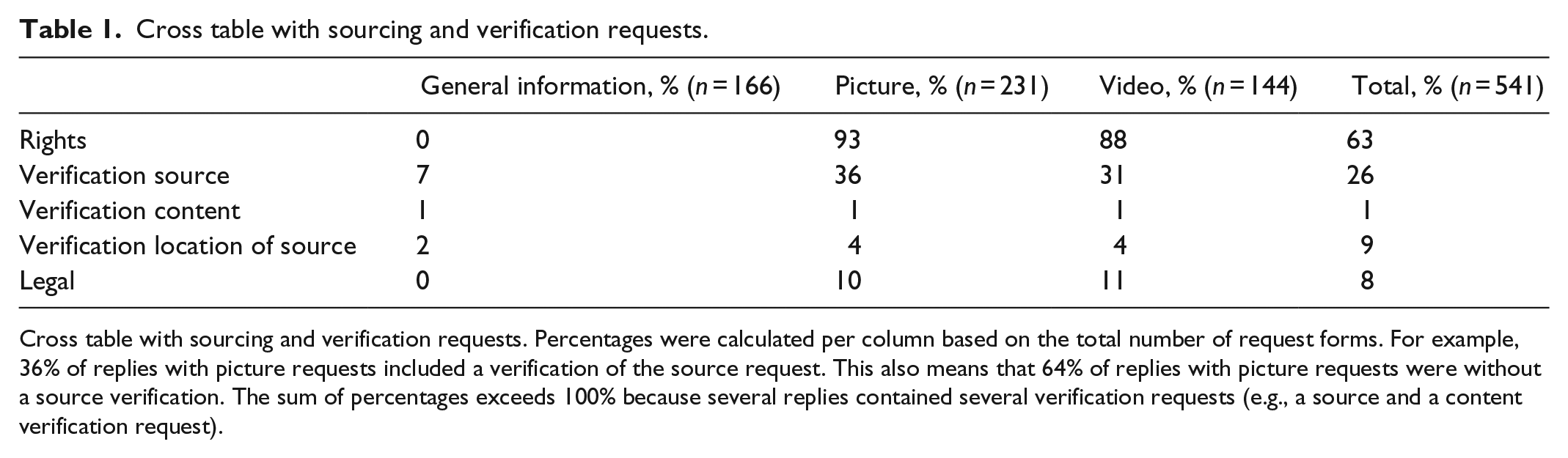
Cross table with sourcing and verification requests. Percentages were calculated per column based on the total number of request forms. For example, 36% of replies with picture requests included a verification of the source request. This also means that 64% of replies with picture requests were without a source verification. The sum of percentages exceeds 100% because several replies contained several verification requests (e.g., a source and a content verification request).
In a penultimate step, we conducted a multiple correspondence analysis (MCA; for an overview, see Di Franco, 2016) to summarize all measured variables. Correspondence analysis is particularly useful when more than two categorical variables are studied, as it allows mapping these variables in one figure and, thus, detecting patterns within them. The more frequently specific options appear together in the same tweets, the closer they are plotted in Figure 3.

MCA with two dimensions. Dimension 1 (30% explained variance) covers mainly the content (general information vs. content), contact information, and rights. Dimension 2 (15% explained variance) includes mostly the politeness. Points visualize replies, color the different categorical variables. n = 541 replies. Circles indicate density. For each quadrant, an example reply was added.
Apart from the distribution in the MCA plot, its axes can also be interpreted. In Figure 3, the x-axis largely represents the different kinds of requests journalists make. No rights and general information contribute to the positive pole of the axis, whereas content (picture or video) requests and rights contribute to the negative pole. Similarly, direct contact (e.g., phone) and no contact also have an important contribution to this dimension. The y-axis is mainly organized along the politeness of the replies: Polite contributes to the positive, whereas normal contributes to the negative pole of the axis. Verification of the location of the source is another variable which contributes considerably to the y-axis.
Verification of the location of a source was mostly used in replies with general requests that included additionally direct contact requests. Most of the replies on the right-hand side in Figure 3 were written by journalists from broadcasting organizations. 9 Replies on the left in Figure 3 were all requests for content. Print or online news wrote most of the replies in the lower part without any additional politeness, whereas news agencies wrote most of the polite replies in the upper part.
In conclusion, two general types of replies could be identified that differ regarding the politeness: First, there are replies with general information requests that include direct contact information and sometimes try to verify the location of the source. Second, there are replies with video or picture requests, which ask for the rights to use the material, lack further contact information, and do not include a verification of the location of the source. The latter kind of tweets was more prominent in our sample as the density in Figure 3 indicates.
RQ3: Sourced Tweets
In our third content analysis, we analyzed the content of the tweets. Figure 4 shows that most requested tweets depict chaos, and/or capture the moment of the actual bombings, and/or include remains of the attack such as debris. These pictures and videos were mostly taken from an on-the-ground, eyewitness perspective. Almost a quarter of the tweets across all content types include security forces. Non-professional helpers (30%), as well as victims (55%), were the most prominent people in videos. Injured victims appeared most often in pictures (27%) and videos (21%). In all videos, and in almost one-third of the pictures with injured persons, the victims could be identified. In tweets only including text, users mostly mentioned indicators of the attack (47%) and/or tweeted just after the attack had occurred (65%). If people were mentioned, this was mainly the police (20%).

We analyzed 42 tweets with a video, 107 with pictures and 49 with only text. The percentage was calculated in each content category.
For all relevant sourced tweets (n = 198), we calculated the correlation between the number of received replies as a measure of popularity among journalists and the number of received likes or retweets as a measure of popularity among the general Twitter population. Both audience popularity measurements (liked: r = .78, n = 198, p > .001; retweeted: r = .81, n = 198, p > .001) strongly correlate with the number of replies each tweet received from journalists. The more popular a tweet was in the general Twitter population, the more replies it received from journalists.
We further investigated the relationship between the popularity of a tweet based on single examples. In Figure 5, we visualized the cumulative percentage of replies (n = 46) from journalists and of the number of retweets (n = 17,365) 10 for one of the most popular tweets in our sample. In this tweet, posted at 8:23 a.m., a user shared a video that shows people running out of the airport building. The first journalist contacted the user 3 min later at 8:26. Up to this point, the tweet had been retweeted 39 times. At 8:39 a.m., 15 min after the original tweet had been published, already half of the replies from journalists were posted. At that time, the tweet had already been retweeted 2,687 times.
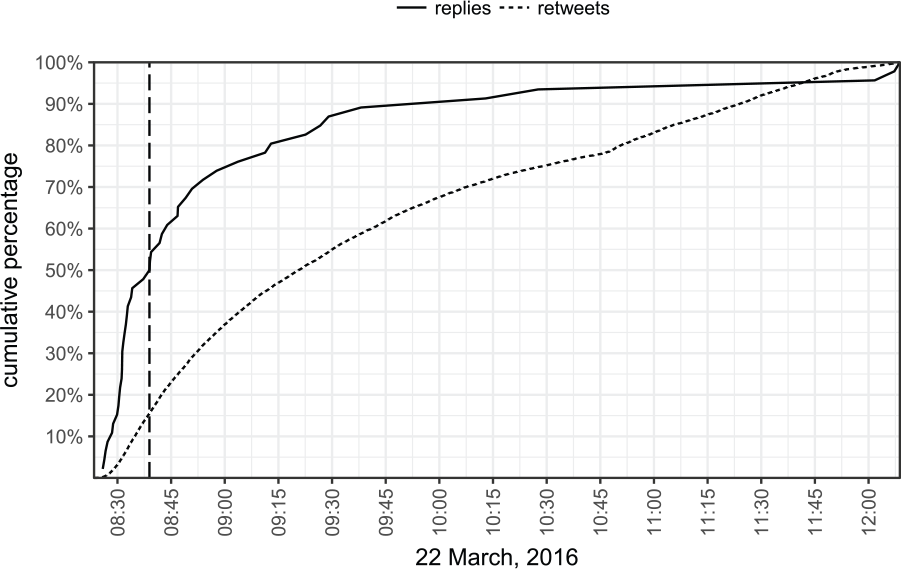
Cumulative percentage of the number of received replies and retweets for the most popular tweet. Dashed horizontal line indicates the moment half of all replies had been written.
Most of the tweets that received replies were written by accounts connected with media (35%) or professionals (34%) that explicitly mention their job position in the description. Only 22% of the tweets were from normal users without any connection to the media industry or a professional role.
Discussion
Sourcing and Verification on Twitter During the Brussels Attacks
Our study shows, first of all, that sourcing over Twitter has become a global phenomenon. Even though European journalists were most strongly represented in our sample, most likely due to the geographic closeness to the event, requests for UGC were not limited to the continent. Second, the high number of general journalists without a particular job task is a clear sign of the increased importance of “multiskilling” (Van der Haak et al., 2012; Wallace, 2013) in newsrooms. The many TV producers in our study that covered the Brussels attacks and used Twitter as a source to obtain the first pictures directly from the location of the attack also exemplify the importance of “multiskilling.” Finally, the identified organizations, especially the startup news agencies, and the job titles of journalists that indicate their level of experience, are a strong sign of professionalization in the context of UGC sourcing.
We identified two types of requests for UGC. In the first type, all kinds of media organizations requested content. Most journalists sourcing content only asked for the right to use the content but did not ask whether the user actually owned the content. News services and large organizations such as the BBC were among the few identified organizations that regularly inquired about ownership of the material as well. Furthermore, legal information was only included in few requests even though this constitutes a problematic aspect of UGC sourcing (Wardle & Dubberley, 2014). Therefore, it was not surprising that only news agencies such as AP and the startup Storyful used additional legal forms in their requests (e.g., Figure 6). The high level of professionalism of news agencies is also reflected in their polite replies asking for UGC. The second type of request came mostly from broadcasting companies that were additionally interested in the users as sources in their live coverage (e.g., via telephone interviews).

Reply with an attached Social Media Release Form from an AP editor to one of the first pictures from the airport after the attack.
The location of the source was almost never verified over replies. In the context of a crisis event at an early stage, this is less problematic as the results of our third analysis indicate: Most tweets included a description of the location and the sourced users were either media-related people or professionals. Furthermore, most sourced tweets appeared in the first hour after the attack, when the risk of fake content is lower. 11 The location can also be verified through the timelines of the user or the information in the account description, as described by Wardle (2013). The content itself, however, was also almost never verified, even though this is the most problematic aspect of UGC. In our case, the missing content verification is less problematic because in most pictures or videos the location could be easily verified through visual indicators. Moreover, most sourced users did appear on Twitter in their professional role and not anonymous and were thus more trustworthy.
Journalists mostly sourced videos and pictures that had an on-site perspective and depicted a chaotic situation with indicators of the attack visible in the images. The results of our time analysis clearly indicate that most journalists are extremely quick in sourcing because they profit from Twitter’s platform specific speed. When the sourcing started, tweets usually had not been retweeted a lot, but they had already an extreme acceleration (as can be seen in Figure 5) and were thus most likely prioritized by the Twitter algorithm in keyword searches.
Some of the pictures in our sample were re-shared pictures with pixelation of fatal or injured victims. Despite this occasional pixelation in images, which was mostly done by the journalists re-sharing them, videos did not have pixelation even when victims could be identified. Finally, almost one-third of the tweets were written by media-related users. Some of the journalists just shared content from other users without any further information. As these tweets were just shared without any additional verification-related information, most of them received requests from other journalists (e.g., the example with the video in the introduction). Other journalists were at the airport as travelers or near the metro station when the attacks occurred and shared their content. Choosing Brussels, the de facto capital of the European Union where many international journalists and professionals are stationed, as a target helped the terrorists to increase the mediated impact of their attack.
Ethical Implications
From these results, several ethical questions arise. For journalists, crisis events such as terrorist attacks, catastrophes, or accidents are cases of heightened uncertainty. In such situations, journalists must gather information about the events quickly and without preparation, and tell their audiences what has happened, where, why, and how. At the same time, journalists have to make sure this information is accurate.
Twitter can be a useful tool for journalists in such situations to gather information and cross-validate judgments with other users. Our analysis showed, however, that many journalists do not try to verify the information in other users’ tweets. At least in their direct exchanges with their sources, many do not attempt to check the authenticity of the pictures or information obtained. This has a number of problematic implications. Journalists can get information wrong or could even make themselves vulnerable to manipulations. This problem is aggravated by journalists’ “group orientation” (Donsbach, 2004, p. 139): Journalists tend to watch their colleagues closely to cross-validate their news decisions, particularly in situations of uncertainty. Such a tendency was clearly visible in our introductory case where one journalist, Anna Ahronheim, tweeted unverified information and other journalists distributed it in their news coverage on TV and online news pages without validating it.
Cases such as this indicate that, as of yet, journalists’ UGC sourcing and verification practices, as well as potentially the respective editorial guidelines, are not sufficient. First, verification procedures differ across newsrooms in general (Shapiro, Brin, Bédard-Brûlé, & Mychajlowycz, 2013) and with respect to the use of information on Twitter in particular (Canter, 2015). In other words, there is no commonly approved method to verify information from social media in journalism, which makes it hard for journalists to effectively bypass the risks of spreading unverified information, for example, due to group processes, time pressure, or competition (Post, 2013). Second, a two-tier system verification—whereby journalists can tweet unverified information but must not distribute it in their actual news publications—can only be effective and prevent unverified information from entering the news if journalists make unverified information transparent in their tweets. At present, no such commonly accepted labeling exists. Thus, even using their colleagues’ tweets, journalists cannot distinguish unverified from verified information. All in all, journalists should be aware of the fact that they can only distinguish themselves from so-called citizen journalists and maintain their credibility as a profession by adhering to a set of professionally approved standards to ensure accuracy in reporting (Mothes, 2016). Such standards should be further developed for the use of Twitter—not just in individual newsrooms but also in journalism in general.
Apart from the journalists’ duty to inform their audiences as accurately as possible, there are other ethical problems they need to be aware of. For example, journalists’ distribution of videos or photographs frequently identifies the people involved—for instance, individuals in grief or panic, fatal or injured victims. Such practices do not only touch upon people’s personality rights, but journalists should be aware that they might even promote terrorists’ agendas because a crucial strategy of terrorism is the “intimidation of a large audience, beyond that of the immediate victims” (Sandler & Enders, 2007, p. 288). When events are still unfolding, posting pictures might also reveal useful tactical information to the perpetrators, such as the police’s position on site, as was the case in the Munich attacks in July 2016. 12
Generalizability of the Results and Future Research
Even though we have only analyzed one event, our results can be generalized to quite an extent. Journalists from our sample were also sourcing during other crisis events in Nice and Turkey in July 2016, even though those crises happened in the evening. 13 Of course, we could not analyze all journalists in the world sourcing during crisis events, but we covered at least all journalists on duty on the morning of the Brussels attacks that attracted global attention. When we additionally checked other sourced tweets besides our original five tweets, we could only identify a few journalists that were not included in our sample.
While the speed, the type of requests, and the scale of the sourcing and verification observed in this study can be generalized for other crisis events, different ethical questions arise. In revolutions, wars, or situations with ongoing active terrorist attacks, possible sources have to be protected, and the publication of pictures might have direct negative effects (e.g., the tactical position of the police during the Munich attacks).
Future research should further investigate how sourcing practice is changing and what coping strategies will emerge (e.g., labeling of verified UGC). Also, it would be fruitful to analyze the use of the sourced UGC in the media and to evaluate whether it was verified. Quantitative studies, such as ours, could be combined with interviews with journalists to learn more about their reasoning and possible ethical concerns. Finally, future research should extend our research with other platforms such as Periscope, Instagram, or Snapchat. 14
Footnotes
Acknowledgements
The co-authors have equally contributed to this publication and are listed in alphabetical order.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
