Abstract
Objective
The Bring Your Own Device (BYOD) approach has promoted the usage of personal mobile devices for organizational and carrier purposes. Applying a BYOD approach might provide various challenges for healthcare organizations. This study endeavored to identify the attributes of hospitals readiness in applying BYOD and to rank these attributes in order to develop appropriate policies for dealing with challenges.
Materials and methods
This study is an explanatory sequential mixed method design that was carried out in two qualitative and quantitative phases for identifying the BYOD attributes and ranking them, respectively. Semi-structured interviews with 15 experts in the BYOD field were performed through in the qualitative phase. Purposive and snowball sampling approaches were used to choose experts. Thematic analysis was used to analyze qualitative data. The identified attributes were ranked in a quantitative phase by asking 10 experts using fuzzy hierarchical analysis.
Results
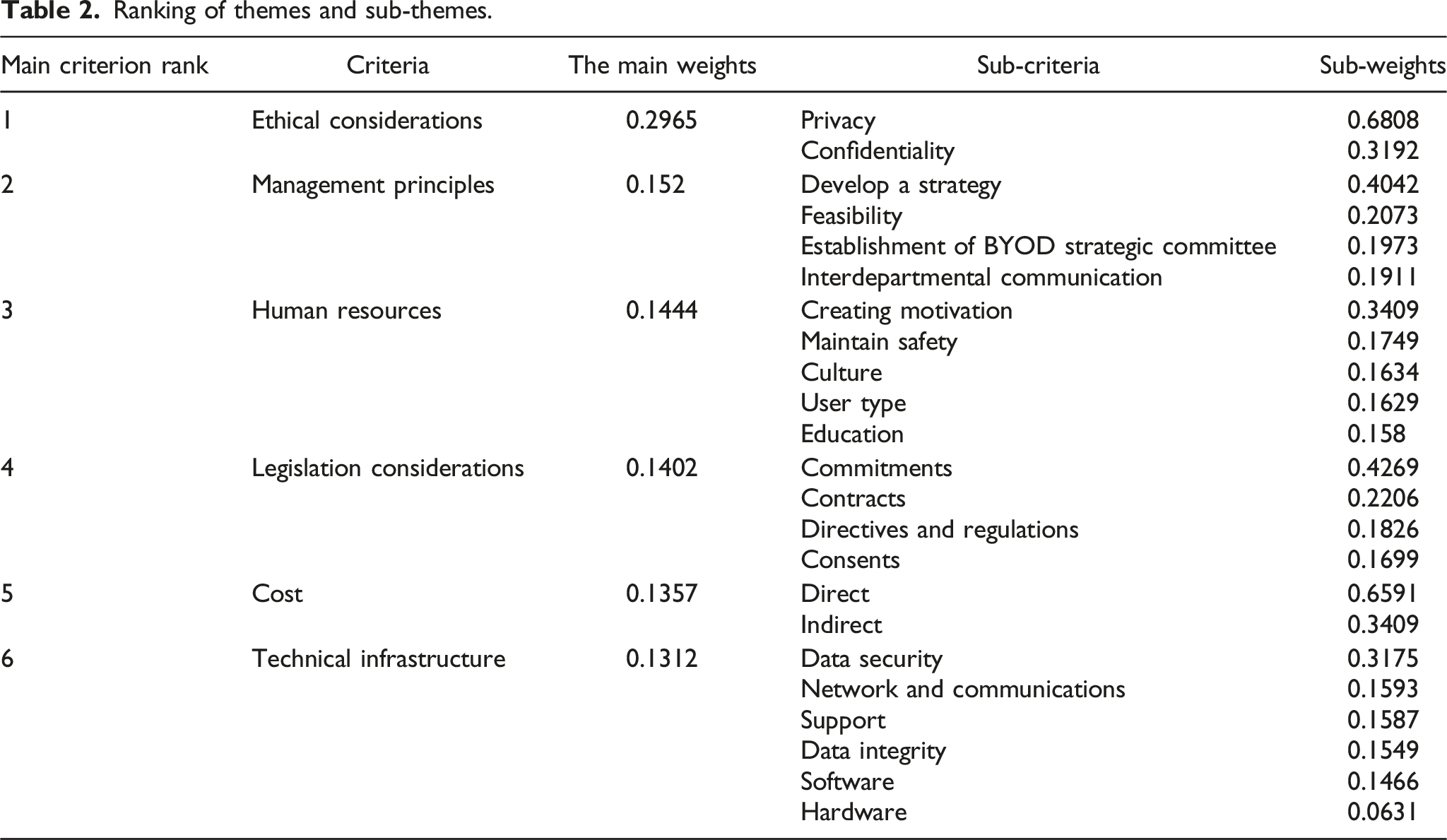
Six main themes and 23 subthemes were identified. The findings of hierarchical analysis showed that ethical considerations, management principles, human resources, legislation considerations, cost, and technical infrastructure as the six main themes, respectively, have priority in hospitals readiness for BYOD.
Conclusion
Addressing the highlighted priorities, from ethical considerations to technical infrastructure, in the formulation and implementation of formal programs and policies by health managers and authorities will prepare hospitals for the use of BYOD while decreasing the challenges associated with it.
Background
Bring your own device (BYOD) is the process of using personal mobile devices such as smart phones and tablets in the workplace for carrier purposes1,2; in recent years, the health sector has been recognized as one of the leading industries in its usage3,4 and hospitals, as one of the important health organizations, are rapidly adopting mobile device management policies. 5 Personal mobile devices are commonly used by health professionals to perform tasks such as clinical documentation, access to medical records, medication information, test results, communication with other staff or patients, and searching for reference resources. 3 Using this approach results in increased staff mobility and dynamism,2,4,6,7 greater flexibility,2,4,6,8 and competitive advantages.2,7 BYOD reduces the cost of providing devices to healthcare organizations and can even be successful in decreasing the rate of patient admission to the hospital. 9 Because of the special benefits of BYOD policies in the field of health care, this trend is constantly growing,1,3 so that staff members of organizations have been encouraged to use personal mobile devices at work, and approximately 95% of them use personal devices for career purposes.2,3 Despite the benefits mentioned, implementing a BYOD strategy for organizations poses security,2,5,6,10–13 legal 10 and financial 14 challenges, which are exacerbated when used in the health field, where patient confidentiality is especially important. Marshall 13 identified data security, governance, legal issues, device type, and internet dependency as major challenges in implementing BYOD in a healthcare setting. 13 BYOD is no longer an option for organizations and has become a business standard in the digital era. 15 Indeed, BYOD has become a pervasive phenomenon, with policies expected to be adopted by employers and managers of organizations, including healthcare organizations. 16 However, available policies in organizations that offer BYOD are frequently ambiguous or even lacking in related policies. 15 Many hospitals face the challenge of developing effective policies to reduce the risks of BYOD, 16 and its implementation is one of the most pressing concerns of healthcare information technology (IT) management. 3
Purposes
Given that the use of personal devices in healthcare organizations poses risks and challenges for health IT professionals in charge of data security, 1 the ability to control the dimensions and features of BYOD is critical for mitigating its main challenges. 17 The first step in controlling and reducing challenges is to identify attributes of hospitals readiness to apply BYOD; thus, the current study was carried out with the aim of identifying and ranking the attributes related to hospitals readiness to apply BYOD.
Hospitals setting in Iran
One of the most important types of hospitals in Iran is based on their support system, which is as follows: • Public hospitals: The government budgets serve as the foundation for hospital management and operations, and funds are received in accordance with regulations in order to produce and sell treatments to various groups, which are based on government tariffs. • Private hospitals: These are hospitals that are established by the private sector with the aim of revenue generation. Private hospital founders or owners consider special profitable medical services, and managers of such hospitals are less involved in providing treatment for erosive and unprofitable diseases. • Special Hospitals: Typically, powerful institutions and authorities establish separate hospitals for themselves that are not under the general supervision of the country and are not considered private hospitals. This complex contains a number of hospitals affiliated with political and military institutions, as well as banks, industries, and charitable organizations.
18
Structure of IT department in Iranian hospitals
The hospital IT unit reports directly to the hospital’s management and is comprised of one person in charge of the unit and one or more experts. One of the main tasks of this unit is to establish and implement a comprehensive informatics system for the organization in accordance with the hospital’s strategic policies. The main task of the IT unit is to use up-to-date information technologies to promote transparency and ensure data accuracy, as well as to create, preserve, and maintain a suitable platform to carry out current organizational affairs, increase managers’ decision-making power, and finally to achieve the organization’s main goals. 19
Method
Type of study
The current study is an explanatory sequential mixed method design 20 in which the attributes of BYOD were first identified in the qualitative phase and then ranked in the quantitative phase using the fuzzy hierarchical method.
Sampling
Purposive sampling was used to select interviewees during the qualitative phase. To complete the human network, snowball sampling was also used. At this point, sampling was carried out until saturation was reached. Interviewees were selected based on their familiarity with the concept of BYOD, work experience in the IT sector in the field of health, and familiarity with the technical and other features of devices and mobile phones. During the quantitative phase, ten interviewees were chosen at random and included in the study.
Data collection
Data for the qualitative phase were gathered through semi-structured face-to-face interviews. The interview was conducted using the interview guide (Appendix 1). The research team developed this guide based on reviewing studies related to the research topic during three two-hour sessions.
The interviews were conducted by a six-step process proposed by Cohen et.al. 21 As a result, after obtaining verbal consent from the interviewees, the interviews were conducted in person or over the phone at the time and place of his/her choice by one trained member of the study team (M.S). The interview guide and the purpose of the research implementation were provided to the interviewees prior to the start of the interview. The conversations were completely recorded during the interview (with the permission of the interviewees) and the interviewer took notes on the important points. The recorded interviews were then transcribed without interruption and converted into written text in a Word file by the researcher herself in a short period of time after the interview. Finally, the interview file was distributed to the interviewees for correction and completion as needed. After 15 interviews, data saturation was achieved. The interviews were conducted from May 2020 to August 2020, and ranged in length from 25 min to 1 hour.
The required data were collected in the quantitative phase using a questionnaire based on the qualitative phase results. To that end, the qualitative phase’s themes and sub-themes were arranged two to two in a 9-degree hourly spectrum to compare with each other. Between October 2020 and March 2021, quantitative phase of data collection was carried out.
Data analysis
Qualitative phase
The data were analyzed using thematic analysis, which was based on the step-by-step thematic analysis method proposed by Braun and Clarke, as follows.
22
: • Familiarization: By listening to the recorded sounds, reading and re-reading the transcribed data, and reading the interviewer notes, specific meanings and patterns that may be related to the attributes of hospitals readiness to apply BYOD were identified. • Coding: After studying and reviewing the data and becoming acquainted with it, a list of information related to hospital readiness that seemed important and key was selected and coded. • Search for themes: The codes obtained in the previous step were classified as the themes of hospital readiness attributes. • Theme review: Several subthemes containing the same concepts and meanings related to BYOD were grouped together to form main themes. • Naming of (sub)theme: Each theme and sub-theme was named based on the relevance of the (sub)theme in relation to hospital readiness. • Writing a report: Finally, the qualitative data analysis was written up as a scientific article.
In this step, MAXQDA Plus version 12 (Release 12.3.0, VERBI GmbH Berlin) was used to manage, categorize and encode the data.
Quantitative phase
The data obtained from the quantitative phase were analyzed using fuzzy hierarchical method. Fuzzy hierarchical analysis is used in the same way of hierarchical analysis, except that the fuzzy method places hierarchical analysis on a fuzzy triangle scale to determine priorities. As a result, in order to deal with the ambiguities of hierarchical analysis,
23
in this study, the fuzzy method was applied to rank the criteria. Following the completion of the questionnaires, the weights of each attribute were determined using the fuzzy hierarchical analysis method via Excel software, and the criteria obtained from the first stage were ranked. To summarize paired comparisons in this study, the following equation
24
was used:
Finally, local and general weights of criteria and sub-criteria were determined and ranked.
Results
Characteristics of the interviewees (n = 15).

The analysis of qualitative data yielded six themes and 22 sub-themes (Supplementary Table).
Management principles
Interviewees who were asked about management of BYOD readiness mentioned issues such as strategy formulation, the formation of a BYOD strategic committee, a feasibility study, and inter-sectoral communications. As one of the interviewees stated, it is critical to pay attention to the important technical and operational strategies when developing the strategy: “It is very important for me to have a strategy or methodology that can make decisions based on it…” (interviewee 7).
The establishment of a special committee to determine the vision and missions, as well as appointing the project manager and team members, and finally formulating a strategic plan, are among the duties of this committee in order to monitor the activities related to the BYOD approach. The majority of interviewees mentioned the importance of conducting feasibility studies, particularly in the operational, technical, and financial fields, prior to the start of the project. One of the participants stated the following:
“Before that, you should conduct a feasibility study to determine what percentage of your staff has acceptable hardware and how willing they are to use their own device.” (Interviewee 6).
The interviewees discussed the importance of effective and stable communication between different sectors, including relevant ministries and institutions out of health system, when it came to inter-sectoral communications. For example, consider the following statement from one of the participants: “The Ministry of Health should establish good relations with other organizations that have an impact on this issue, such as the Ministry of Information and Communication.” (Interviewee 10).
Human resources
Human resources are one of the most crucial components of any organization that requires special attention in order to make any change. According to the interviewees, determining the type of users, which includes identifying hospital processes and wards, as well as identifying and categorizing hospital staff (process-based and role-based mechanisms), is critical before implementing the BYOD approach. One point of view in this regard was:
“We need segmentation, which is typically based on role. It could also be based on a specific process or department within the hospital…” (Interviewee 14).
Creating positive financial and non-financial motivations, on the other hand, is regarded as critical for BYOD users. As one person put it:
“Those who bring their personal laptops (rather than using computers in the organization) should, for example, be given a trip at the end of the month. We must encourage this person so that bringing his/her device compensates.” (Interviewee 13).
One of the topics of interest in the interviews was maintaining people’s safety in order to prevent the transmission of nosocomial infections by bringing personal devices to the home when using BYOD, which necessitates relevant policies to reduce pollution and ensure the safety of the workforce. “Safety in both organizational and personal equipment, as well as cleaning it with authorized detergents.” one person stated in this regard (Interviewee 11).
Another issue raised by interviewees was the importance of paying attention to organizational culture issues, such as culturalization and reducing resistance to change; specifically, that this method may create more resistance due to the creation of a monitoring mode for users. Another issue is staff and workforce training and awareness, which is especially important when using the BYOD approach. One person stated:
“Perhaps the most important issue is staff training and awareness…” (Interviewee 7).
Cost
According to the interviewees, there are two types of costs associated with using BYOD: direct and indirect. Per this classification, the costs of setup and payment are classified as direct costs, while the costs of depreciation and maintenance of personal devices are classified as indirect costs. One of the quotations in this regard is:
“The useful lifetime of electronic devices is determined by two factors: duration and rate of usage. When I, as a user, bring my personal electronic device to the organization and use it, its useful lifetime is naturally reduced. As a result, BYOD should result in a financial gain for me to cover my costs…” (Interviewee 2).
Technical infrastructure
The BYOD approach is undeniably linked to technical issues, both in terms of organizational structures and personal devices, and interviewees mentioned various aspects of it. They mentioned the need for technical support for BYOD users, for example, and considered the provision of hardware and software support services to be necessary. In this regard, one person stated: “The necessary technical support for this work should be provided by the organization for individuals, and personal devices should receive this support in the same way that organizational devices do.” (Interviewee 7).
The following item is data integrity, which must be present in all key aspects such as design, implementation, and application of any system that stores, processes, or retrieves data, and interviewees emphasized that this integrity must be in data, software, and databases to avoid working as an island.
The issue of data security in the field of healthcare has been raised repeatedly by interviewees because patient confidentiality is critical, and the establishment of standard and reliable solutions to implement this process in the hospital is required.
One of the participants stated: “The issue of information security is one of the most important factors.” In my opinion, we should create a category based on the application of the software that is installed on this system and not allow any software to be installed and applied on people’s devices, depending on the type of user. We require a cloud-based space, and our cloud-based tool, without a doubt, must be private…” (Interviewee 10).
Because of the large volume of personal devices used by employees when implementing BYOD, many interviewees have focused on networking and communication. People suggested, for example, that the method of wireless or wired connection be specified, and that facilities be provided for each of them to connect personal devices. The interviewees stated that in the field of software, the development of a set of features, behavior, and performance of software related to the BYOD approach should be determined and specified, as well as software compatibility with a variety of systems. One example of a related quote is as follows: “When working on a Windows-based system, you cannot bring an Android tablet unless the software and database are not dependent on the type of system or are also designed for Android systems. This is at the operating system level, but it is also considered at the database level…” (Interviewee 12).
Furthermore, in order to efficiently implement BYOD, the interviewees emphasized the importance of all hardware related to system software compliance with the prerequisites of that system, as well as the importance of device registration. According to one interviewee, “every personal device that a person brings with him should be registered, for example, his MAC address should be registered…” (Interviewee 2).
Legislation considerations
When implementing a new process in any organization, there are important legal issues that must be addressed prior to implementation or the process will fail. These include consent forms, which experts believe are critical, and organizations are required to fully explain relevant information and specific conditions, including access to people’s personal tools if necessary, and obtain permission from them in this regard. Furthermore, employees should be able to make their own decisions in order to complete the consent form. Contracts are another critical issue.
Contracts are another critical issue. A contract is a legally binding agreement between individuals or organizations that specifies the rights and obligations of both parties in a specific issue. As a result, the interviewees believed that it was necessary to draft an appropriate contract in accordance with the intended activities. One participant stated in this regard: “Discussion of the contract, which includes issues of support and purchase of software training, as well as the issue of determining the server.” (Interviewee 15).
Additionally, the interviewees stated that when implementing BYOD, organizations must make specific commitments to their employees as well as the ministry in order to maintain the process’s quality. Furthermore, the user’s commitments to maintain security and use personal tools for carrier purposes are required. “The important thing is that the non-disclosure commitments that need to be taken more seriously…” says one of the comments (Interviewee 2).
In the discussion of directives and regulations, it is stated that the relevant rules in the use of BYOD should be developed at an appropriate level, and appropriate guidelines should be determined in the form of a directive for its proper implementation, which include items such as assessment levels, data protection, and how to pay.
Ethical considerations
Concerns about privacy and confidentiality are raised during the discussion of ethical considerations. According to the interviewees, privacy is critical when applying BYOD because, on the one hand, we are dealing with patient information and, on the other hand, it is possible to publish their personal files due to the use of personal devices. As a result, privacy concerns should be addressed in both the staff and patient fields. According to one interviewee: “The two-way principles are respected, i.e., both the hospital’s and the individual’s level, because personal and private items on the person’s computer may exist…” (interviewee 12).
Another topic of interest for interviewees was information confidentiality in the healthcare field, which is critical given the existence of patient health data. We come across one of the related quotes: “The greatest risk is that people’s privacy will be violated. Assume I have a picture of a patient on my cell phone and my child accidently sends some cell phone information to another person while playing with the phone.” (Interviewee 4).
Ranking of themes and sub-themes.
Discussion
Attributes related to hospital readiness to apply BYOD were classified into six major themes: ethical considerations, management principles, human resources, legislative considerations, cost, and technical infrastructure, in that order. To express the details of each concept, related sub-themes were presented, along with their priority. Furthermore, specific codes for each sub-theme were provided to present appropriate strategies for the implementation of BYOD policies based on interviewee opinions. According to Aguboshim and Udobi, 25 effective BYOD policies and mobile device management strategies are effective in protecting user privacy and the confidentiality of information on employees’ personal devices. These findings are consistent with our findings regarding user privacy and the confidentiality of ethical considerations. In the Marshall’s study, 13 three recommendations are provided to help healthcare organizations develop and implement a successful strategy in the field of BYOD, including the collaboration of top managers and IT professionals in creating strong security systems, identifying potential risks, and anticipating innovative changes in the organization’s routine. These cases are consistent with the findings of our research in the field of management principles, particularly the development of technical strategies and the formation of a strategic committee. Brodin et al. 26 emphasize the importance of setting analysis in their research on the challenges of managing BYOD, which is consistent with the findings of our study about feasibility. Furthermore, Brodin mentioned the importance of communication in the implementation of BYOD strategies in another study, 12 which is consistent with our findings on inter-sectoral communication. According to Krey’s study, the four main dimensions of the BYOD acceptance framework are technology, security, stakeholders, and organization. 27 The inclusion of stakeholders as one of the main pillars of program implementation does not correspond to the findings of this study and is not mentioned; however, other concepts in other dimensions are consistent with the findings of this study. Of course, the emphasis is on establishing stable and appropriate communication between related organizations, but the stakeholders are not specified in detail. According to a study by Wani et al., 3 human resource management policies and practices such as a strong security culture and staff awareness and training lead to improve staff commitments about protecting hospital data, which these results are consistent with the sub-themes obtained in human resources of this research. Zahadat et al. have pointed to the main role of the people or the same human resources along with policy and technology management in their framework presenting on the security of BYOD, 28 which is in line with the findings related to human resources in the results of current study. Moyer in a study conducted on mobile device management in hospitals, 5 considered the approach of users training as more practical, instead of trying to control technology in the short term and introduced it as an opportunity for hospitals to be actively involved in managing cell phone applying in the hospital. Refer to the staff training in our research is in line with the results of Moyer study. Brodin, 12 in the framework of BYOD management, has highlighted the importance of training existence and communication development to better understand the process of BYOD approach implementation, which is consistent with the results of the current study in relation to human resources. We have specifically highlighted the significance of employee training and cultural factors. Of course, it should be noted that education has received less priority in the current study than other human resource sub-themes.
According to the findings of the Marshall study, 13 the main challenges of BYOD in health that policymakers should consider are the legislation, as well as issues such as confidentiality, governance, device type, and Internet dependency. As a result, it is consistent with the findings of our research, which identified legislation as one of the key dimensions of the formal BYOD program. Alansari et al. 29 mentioned the importance of developing cost payment policies in their study, emphasizing that the organization should determine the amount and method of payment for personnel equipment costs, communications, information exchange, and taxes. These findings are consistent with the findings of our study, which identified direct and indirect costs as important factors in hospital readiness. Vorakulpipat et al. 30 considered the encryption and security of the operating system level to maintain the security and confidentiality of a number of aspects in information security and related techniques such as policies, location privacy, and centralized control in order to maintain the security and confidentiality of a number of aspects in information security and related techniques such as policies, location privacy, and centralized control, which is consistent with the attributes obtained in data security in this study. Sobers believes that the most effective way to implement BYOD is to combine security and technology with related policies in a comprehensive framework and strike a balance between them. 11 This issue has been raised in the current research in the field of technical infrastructure, particularly data security, indicating that the findings are consistent. The main factors in Alansari et al.’s study, which was conducted in relation to the framework of effective factors in organizational acceptance of BYOD, 29 are divided into two categories: behavioral intention of using technology and policy-specific criteria. In the behavioral intention, references to issues such as management support and technical support are consistent with the findings of our study. Specific policy criteria refer to the various types of policies required regarding payments, employee agreements, device support, and information security, which is also consistent with our findings. According to Alansari et al.'s study, in terms of criterion ranking, information security policies (with a final weight of 0.186) were ranked first, and technical complexities (with a final weight of 0.008) were ranked last. In this regard, our study includes legal considerations related to information security and privacy policies, as well as security policies in accordance with the sub-themes of each theme, so our study confirms the findings of previous research.
Conclusion
In light of recent advancements in communication and information technologies, approaches such as BYOD are unavoidable. As a result, in order to apply it properly and minimize the associated challenges as much as possible, it is necessary to develop formal BYOD programs and right policies, which necessitates the attention of relevant managers. In this regard, this study identified technical infrastructures, management principles, workforce, costs, and ethical considerations as the primary requirements for developing BYOD policies, particularly in hospitals. Furthermore, ranking these requirements, which include ethical considerations, management principles, human resources, legislative considerations, cost, and technical infrastructure, can provide a clear path, allowing policymakers and hospital managers to address them based on the priorities of each issue and fully benefit from BYOD approach.
Supplemental Material
Supplemental Material - Identifying and ranking the attributes of hospitals readiness to apply bring your own device: an explanatory sequential mixed study
Supplemental Material for Identifying and ranking the attributes of hospitals readiness to apply bring your own device: an explanatory sequential mixed study by Maryam Jahanbakhsh, Mostafa Amini Rarani, Shahram Tahmasebian and Masoumeh Shahbazi in Proceedings of Singapore Healthcare
Footnotes
Acknowledgements
We would like to appreciate Mr. Majid Jangi, Mr. Seyed Mehdi Hejazi, Mr. Alireza Jabbari and Ms. Maryam Moini for their presenting valuable comments during the data collection and information interpretation.
Author contribution
All authors contributed materially to the creation of the manuscript. The first author assisted in the ideation, design, drafting of the manuscript, critical revision, and technical, and material support. The second and forth authors collaborated in interpreting the data, implementation, and material support. The third author collaborated in critical revisions.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This study was funded by Isfahan University of Medical Sciences, Isfahan, Iran.
Ethical approval
This study received the required ethics approval from Isfahan University of Medical SciencesResearch Ethics Committee, Isfahan, Iran with ethics code no:IR.MUI.RESEARCH.REC.1398.743.
Supplemental Material
Supplemental material for this article is available online.
Interview guide
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.

