Abstract
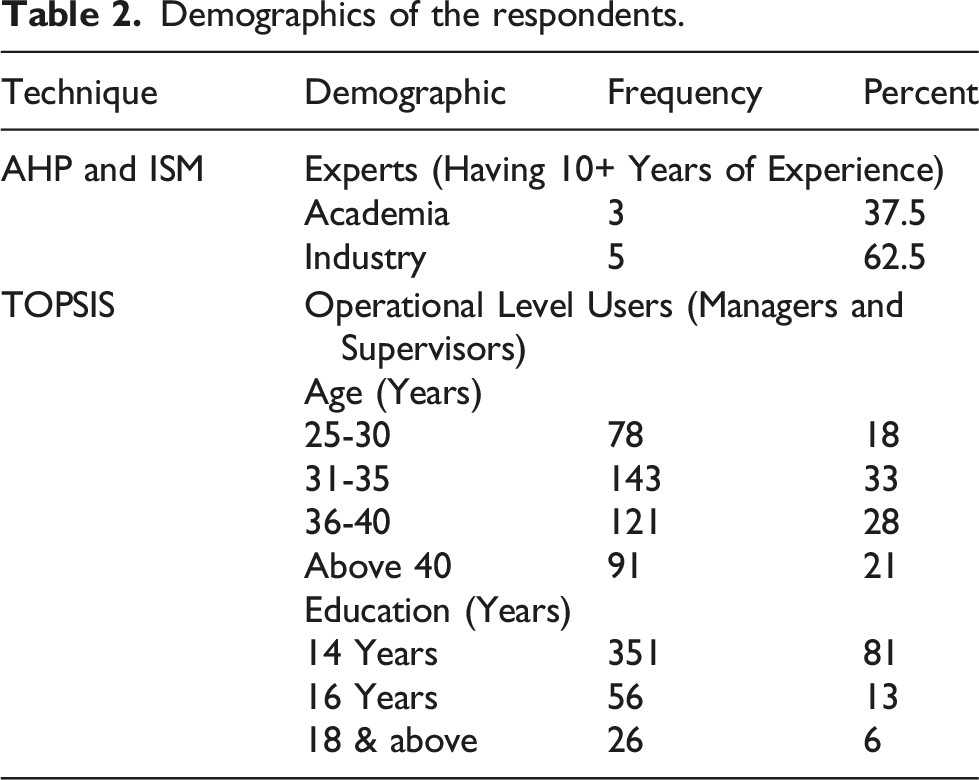
In order to remain competitive in a post-COVID-19 scenario, manufacturing organizations should use the pandemic scenario as a lever to make IoT adoption more agile and faster by reinventing their business models. Although, IoT has vast potential in multiple sensors’ direct integration without human intervention, its adoption has observed significant barriers during COVID-19. In this context, the current research aims to identify, prioritize, categorize, and investigate inter-dependencies among the significant barriers to adopting IoT technologies in the manufacturing industry. The analysis used two-stage integrated AHP-TOPSIS (Analytical Hierarchy Process-Technique for Order Preference by Similarity to Ideal Solution) and ISM (Interpretative Structural Modeling) techniques. For AHP and ISM techniques, a group of 8 experts from academia and industry with at least 10 years of experience was surveyed to capture their perceptions. Whereas, for TOPSIS, data were collected from 433 operational-level users. The research discloses that the significant driver barriers that hamper the adoption of IoT technologies are: poor internet infrastructure, high adoption & operating costs and lack of government regulations. This study will assist practitioners, decision-makers and organizations in understanding the significant barriers to seamless IoT implementation.
Keywords
Introduction
The world has witnessed unforeseen disruptions in industrialized operations due to coronavirus outbursts. The COVID-19 pandemic has hit worldwide trade at a matchless rapidity due to lockdowns. 1 The situation has forced firms, particularly those depending on manual processes, to transform their operations into robust, agile, smarter ways 2 and achieve resilience to recover quickly from misfortune and change, allowing them to continue operations. It is important to note that the ability of an enterprise to change from failure to success is considered resilience. 3 Whereas, robustness measures the insensitivity to disturbances of the system and focuses on the ability of a system to withstand variations whereas manufacturing focuses on the systematic creation of products from raw material. 4 Furthermore, Seric and Winkler, 5 Javaid, Haleem 6 stressed that digitalization could be significant in managing hazards and restoring operations in the post-COVID 19 era. In fact, COVID-19 has accelerated the inevitable digital transformation through the Internet of Things (IoT). 7 The aim of IoT is to use predictive analytics and big data technologies to increase efficiency, profitability and productivity, and it is broadly spread in an entrenched grid of autonomous and intelligent devices. 8 It is a digital virtual transformation from the physical business ecosystem into a smart and advanced entity. Conceptually, IoT aims to connect any “Thing” through error-free networks without considering the time, place and motion. 9 Things mean sensor devices that result in efficient collaboration among stakeholders and more agile manufacturing operations. 10 Information is exchanged in a secure and robust way through IoT in both kinds of businesses (manufacturing and services). 11 Robustness measures the insensitivity of the system to disturbances, and focuses on the ability of a system to withstand variations, whereas manufacturing focuses on the systematic creation of products from raw materials. 3
IoT adoption offers tangible commercial benefits such as low cost and risk, and enhanced operational processes, as well as additional benefits of virtualization, flexibility, adaption, transparency and visibility in operations.12,13 In addition, the proactive resilience of different network systems, including holistic supply chain networks, is enhanced through IoT in different ways: real-time monitoring of goods in transit, prediction of potential disruptions, speedy identification of problems aiding quicker responses to troubles and provision of insight into each node’s performance. 14 For achieving sustainable success in today’s manufacturing system, the development of resilience is imperative because, in the face of various disruptions, resilient manufacturing systems can withstand and navigate uncertainties, confirming continued operations while maintaining their core functionality. Also, to accommodate product demand changes and supply chain disruptions, the processes of resilient manufacturing systems can be easily adapted. 3 The trend of this technology is vast, covering all business sectors and major industries, and no industry is left out from the influence of the overall emergence of IoT technology. 15
Organizations must consider IT and IoT as fundamental enablers for agile and next-generation advanced manufacturing.16,17 Thus, interpreting barriers and facilitators to agile manufacturing is essential for manufacturing organizations to enhance organizational agility. 18 However, the literature lacks studies on IoT adoption in agile manufacturing; several obstacles exist while implementing IoT in agile manufacturing. Therefore, eradication of such barriers is essential for the operative employment of IoT in the manufacturing industry, especially in the COVID-19 scenario.
In this context, the current paper is one of the earliest studies that attempt to prioritize the IoT adoption barriers and catch the communal affiliation among the several IoT application barriers from the perspective of agile manufacturing in the post-COVID-19 period. The prioritization of the prevailing obstacles to IoT execution was carried out using AHP-TOPSIS, while an investigation of the causative association amid barriers was performed using the Interpretive Structural Modeling (ISM) technique. The remaining paper has been sequenced as follows: section 2 is a literature review on IoT and agile manufacturing, and offers a deep insight into the barriers to IoT adoption; section 3 discusses the research methodology; section 4 deliberates the meticulous execution of the AHP-TOPSIS and ISM techniques, and presents the findings; section 5 discusses the results and the implications, while conclusions and study limitations are presented in section 6.
Literature review
Internet of things
The internet has advanced into a real-world solicitation in a broader platform of IoT using routine and daily objects. At various stages, there are virtual connections among the physical items like products, equipment and machines, and such devices are controlled and monitored through cyber systems. 19 Based on protocols and standards, there are capabilities to self-configure itself in an active network infrastructure of IoT, 20 and it recognizes every entity as “Things”. There must be a seamless integration of this cyber-physical interface of IoT system architecture, as all the things are connected in the system. The set of connections, security, and business processes and models are the various factors of IoT architectures. There is a need to consider the multiple aspects of interoperability, scalability, and extensibility in IoT architecture designing for integrating the existing heterogeneous network devices and smooth transition. 21 IoT harmonizes how people connect to the physical world using public services such as cloud computing. 15
Due to the integration of digital technologies into physical systems, IoT and cyber-physical systems look like interchangeable concepts, but their focuses and characteristics are distinct. IoT is a broader concept that minimizes human intervention and focuses on system-to-system interactions. Whereas, the cyber-physical system emphasizes human-to-system interactions. 22 However, the application of both concepts is to detect security threats, network intrusion, attack paths and malware. In recent years, both have witnessed a number of success stories and rapid development. 23
Internet of things technologies
IoT technologies.

Internet of things for agile manufacturing
In the global economy, more data are generated by manufacturing than in any other sector. However, due to a lack of support systems and technology, most of the data are used to its curtailed potential or lost. However, IoT can contribute substantially to task automation, quality assurance, effective monitoring, and proactive maintenance of the machine's systems when combined with data analytics. Manufacturing organizations like Toyota are already shifting from traditional manufacturing to more digitized ones to meet market demand. 15
Numerous enterprises intend to implement lean manufacturing systems in their manufacturing processes to meet the customization demands, increase product variety, reduce lead customer times, and eliminate waste. Furthermore, to encounter highly volatile market demand, companies aim to keep the system more agile. 29 Machine and mechanical setups could be made agile up to some extent by enhancing the combinatory sets of electrical, mechanical and software parameters. 30 Agility means “capacity to move easily and quickly.” Agile manufacturing is characterized by satisfying individual customer preferences where fluctuations may happen in the roles of competitor firms, suppliers and customers. Agile manufacturing is a significant attempt to respond to the threat of newly industrialized nations. 31 Traditional manufacturing is the conventional production method and depends on established processes and technology, whereas agile manufacturing augments efficiency and adaptability to provide customer-driven products and services by embracing advanced automation and prompt prototyping. 32 There is a need for continuous development of new technological approaches for an agile manufacturing base, and IT is argued to be the essential condition to realize real agile manufacturing. 33 Information is a more important constraining factor in complex global organizations than labor. Without an efficient infrastructure of information access, sharing and distribution among all stakeholders, concurrent development of products cannot be achieved. The supportive role of IT is a novel feature of an agile environment. 34
Currently, all successful enterprises invariably rely on IT, but real agile manufacturing is a strategic process of thriving in the competitive environment by excellently responding to changing markets. 33 One of the key enlisted strategies and fundamental enablers for agile manufacturing is “automation and information technology”. There is a lot of change in the working culture of organizations with advancements in IT, and organizations are spending a large budget on constructing IT infrastructure to attain higher levels of firm agility. 35 In order to enhance the consumers’ experience and make it more convenient, personalized and engaging, digital technologies such as IoT play an important role 36 as the advancement of IT supports all key shifts of the manufacturing paradigm. IoT gives speedy access to information about physical objects, leading to state-of-the-art services with high productivity and high efficacy. IoT changed the methods of handling and operating production, delivery, maintenance, transportation and product recycling. Hence, IoT is competent in offering robust solutions at all levels. 37 IoT competencies are imperative for organizations to sense and grab business opportunities and challenges. 35 In short, by adopting IoT infrastructure, manufacturing organizations can benefit significantly in all aspects. 37 Moreover, the application of IoT in manufacturing enterprises advances the competence of production processes, followed by fulfilment of customer specifications. 38
Barriers prone to the Internet of Things adoption
IoT is supposed to have an enormous influence in the future on the global economic platform. 39 It is specified that the optimization and transformation of the international economy will depend merely on the implementation level of IoT devices. 15 The current study surveyed accessible literature to ascertain possible barriers to adopting IoT in the following.
Lack of standardization
Over the entire IoT network, to ensure data safety and efficient and smooth integration between various vendors, IoT communication protocol established global standards. IoT is proficient in handling end-user platforms, cloud networks and sensitive devices because of the existence of global standards. 40 Standardization is useful for information interchanging, composting, controlling, and surveying. 41 Various standards like communication, identification and security play a serious role in implementing IoT successfully. A common adoption barrier has been identified as a lack of standardization for most of the new technologies. 42 For IoT practitioners, every day makes a difficult situation because of the fragmentation of standards with new ones. 43 Furthermore, standardization will be required to avoid chaos. 44
Inadequate internet connectivity
Poor internet connectivity challenges developing countries. 45 In IoT adoption and diffusion, one of the key challenges is electricity problems and poor internet connectivity. The Internet must be available to all partners.8,43
Lack of mobility/reliability
Mostly, IoT objects have a certain degree of mobility and are not fixed. This is of paramount importance to efficiently manage and support the mobility of this large amount of objects. 46 Reliability challenges are enhanced due to the massive number of smart technologies and widespread participation. The failure risk is superior and the interconnections among them are less trustworthy with mobility.47,48
Security and privacy
There are substantial fluctuations regarding cybersecurity in the companies’ perception in a post-COVID-19 world. 49 IoT security challenges must be closely considered and nullified to enhance public trust and experience a significant adoption rate. 15 There may be calls for efficient security mechanisms because billions of devices are connected through IoT. In employing IoT networks, a major concern is the personal privacy issue (data ownership) because it can be easy to trace and hack connected objects and devices. 43 Security issues are central in IoT, and a series of properties, such as privacy, non-repudiation, availability, integrity, confidentiality and authentication, must be guaranteed to ensure the security of data and the entire IoT system. 46 IoT systems are vulnerable to external security risks due to different issues like authorization, software protection, internet connectivity, and data encryption. 24 Client privacy, access control, data authentication and resilience to attacks are also challenges in security and privacy protection. 21 When the user’s signals are interrupted, his or her privacy may be compromised, and this issue should be addressed to provide user confidence in terms of privacy. 50 In order to ensure control over the flow and exchange of sensitive information and safeguarding of personal data across the manufacturing chains, holistic multi-layer approaches to security are required. 51
High adoption and operating costs
There may be irreversibility of investments and technological risk related to financial loss because high-end technical infrastructure support is required for IoT solution implementation.24,52 Moreover, the maintenance cost of these devices will rise in the future. 53 Manufacturers need benchmarks about IoT’s ability to lead to improvements across cost, time, and quality axes to provide a compelling proposition for IoT adoption. 51 In addition, many sensing and triggering devices are employed in IoT applications, which raises their cost. 43
Lack of government regulations
An important consideration within the IoT industry is effective governance, and the effective governance plan is harder to achieve with the involvement of heterogeneous technologies. 54 Legal information systems need to be developed to support the expansion of IoT and massive development as it ensures security standards. Judicial laws should be guided by the limitations of sensitive frequency bands. 41 Organizations and governments must work synchronously to support and promote technological initiatives and resolutions. 55 There is a continual downward trend because of weak governance in IoT networks and devices’ security, and the absence of effective regulation and standards. 54
Long payback period
Massive series of sensing and stimulating devices are required in manufacturing organizations. There may be an increase in the payback period, depending on the finances and IoT implementation size. 43 Due to the long payback period and unawareness of capturing the potential of IoT, small and medium enterprises may be discouraged from upgrading their systems. 13 Furthermore, being financially unstable, many organizations do not believe in long-term payback and investment 56 because investment in IoT always carries a substantial risk of monetary loss. 24
Lack of long-term vision and top management commitment
An organization will lose its competitive advantage and fail to leverage the opportunities without a good long-term vision. 57 Employee commitment and involvement are crucial for implementing any new process or upgradation program in an enterprise. Therefore, it is essential to frame an efficient policy for human resources from the management team as it includes molding the mentality of employees to trust the organization, and for the betterment of the organization, changing the beliefs, outlook, and routines of employees.24,29 Due to a lack of familiarity, perceived complexity, cultural resistance to change, security apprehensions, and high cost, top leaders may face challenges in understanding IoT. 58
Compatibility issues and seamless integration
Compatibility and integration problems prevail while embracing IoT due to heterogeneity in technology adoption. 50 Integration of existing legacy systems with IoT technologies acts as an IoT adoption barrier. Conformity with the current industrial automation is necessary for smooth integration between systems. 59 Haddud, DeSouza 24 also confirmed that integrating IoT with used strategic, analytics, and operational technologies is the greatest barrier to successfully adopting IoT.
Limited skilled workforce
High-end functional and technical skills are required in IoT systems to make certain system’s adaptable, and there should be a user-friendly interface, installation, and management of the IoT network.8,44 So, acquiring the desirable supportive staff with the right skills and familiarity for designing and deploying IoT solutions is another key IoT adoption barrier. 24 The system is adversely influenced by the lack of technical skills in the workforce. 59
Lack of identification and validation
Mainly, the literature on IoT covers technological and functional challenges, while multi-application research is still in the emerging stage. 59 It discourages small enterprises from adopting innovative & troublesome technology and implementing new business models24,44 because the top challenge to IoT adoption was perceived as a lack of clear comprehension of the IoT benefits. 24
Complex Architecture
Currently, there is a non-existence of universally acceptable IoT architecture. 50 Compliance with the IoT philosophy and the requirements and constraints of the manufacturing environment to manage the devices and services is the role of architecture. 30 The upgraded technology can be adopted only with the proper architecture. 48 In the case of wireless systems, there is a critical challenge of initial plan, design and IoT architecture selection. 24 There is a need for standards-based reference architecture implementation to integrate digital enterprise systems in the manufacturing chain and for industrial automation. 51 Designing an efficient, flexible, and secure architecture that is able to cope with complex IoT scenarios is a major challenge for sensor networking and storage. In this concern, the service-oriented architecture (SOA) approach has often been followed in the last couple of years. 54
High energy consumption
The critical area of concern is efficient power consumption for IoT implementation. Energy efficiency is a crucial need for an operational Internet of Things device. Power is a significant concern for IoT’s commercial applications. 46 System power consumption can be enhanced in a way that various alternative power storage devices lower the power usage of the electronic module. There will be a rising call for energy with the increase in the number of data centers, networks and IoT devices. Consequently, energy costs are expected to increase continuously.48,60
Transparency and trust
At every production stage, transparency and trust are important for agile manufacturing. IoT adoption creates the problem of trust as the cloud architecture is centralized, 61 and trust issues are typically associated with emergent technologies. 62 That is why most stakeholders did not trust the provided IoT system. 63 For IoT acceptance, adoption and continued use, trust remains the number one barrier and is a central policy concern that needs to be handled. 62
Displacement of human resources and employees’ resistance to new technologies
IoT adoption at social and organizational levels will create relevant challenges concerning reorganizing skilled manpower. 44 The displacement of human resources will be crucial when organizations implement disruptive technologies. 24 Thus, instead of displacing or replacing them, the involvement of existing human resources is important. 64 Therefore, employees always resist new technologies and practices. It is challenging to change the mentality of workers from their old way of working and basic principles and to recognize employees who are not relaxed with the use of new technologies. 29
Scalability issues
In order to address the significant issue of scalability, organizations must keep themselves updated as more physical devices are assessed to get joined in the forthcoming time with the increase in the size of the IoT network. 8
Research methodology
Research design
The present study uses integrated AHP-TOPSIS and ISM techniques to better understand the identified 16 IoT adoption barriers. For evaluating the relative importance of each barrier and assigning weights, AHP is useful. While ranking the identified alternatives or barriers, the weights obtained from AHP are used as inputs in TOPSIS. Then, the ISM method was used to describe the relationship among various barriers. Finally, to classify these barriers, MICMAC analysis was carried out.
Sample and procedure
In the current study, the manufacturing sector of Pakistan and top-ranked educational institutions were the sources of data collection. The authors painstakingly nominated modern manufacturing firms from the country's largest provinces where the IoT concept has been implemented. To prompt expert opinions while using AHP and ISM, there were invitations to experienced managers and academicians with more than ten years of experience. Researchers can choose experts based on their knowledge, so the purposive sampling technique was applied here. Five from industry and three from academia (a total of eight experts) participated among the 18 contacted experts. In the case of ISM, three rounds of (Delphi) discussions were executed to come to a consensus about the association amongst barriers.
There are different opinions about the sample size, and a minimum of eight experts is recommended because of the absence of a significant correlation between the panel members. 65 Hyun, Cho 66 selected seven experts for their research to efficiently evaluate various alternatives, as the Delphi method requires extensive knowledge and experience. Bolaños, Fontela 67 and Govindan, Azevedo 68 stated that in case of ISM participation, there should not be too many participators. Therefore, Etemadi, Van Gelder 69 and Kumar, Bhamu 70 engaged five and eight experts, respectively, to answer the questions. Similarly, in the study of Deshpande and Nagendra 71 only five experts participated. While using Delphi, most studies engaged the number of eight panelists. 72 Also, in the current study, the views of eight-panel members with expertise were considered effective for analysis.
Demographics of the respondents.
Techniques used in the study
Analytical hierarchy process
Following are the steps of AHP:73–75
After goal setting, a decision hierarchy is designed. The 1st level is about prioritizing the IoT implementation barriers. There are attributes-based groups of all barriers at 2nd level. The 3rd level is about all barriers.
Now, to create matrices of pairwise comparisons of all the barriers and groups, experts are solicited using a 1-9 preference scale described by Saaty.
76
There is the start of the mathematical process for normalizing each matrix. A normalized matrix is obtained when each entry in the column of a matrix is divided by a respective column sum. The eigenvector of a matrix is obtained by averaging all values in a normalized matrix row. Then, the principal eigenvalue known as λmax is obtained by adding the product of the eigenvector and the sum of the columns of the reciprocal matrix.
A consistency test is conducted to verify the assessment of experts: (e.g., the value of RI for a 4 × 4 matrix is 0.89).
77
A review is required if 

TOPSIS
Based on 16 IoT adoption barriers, a questionnaire was developed for TOPSIS to determine the final ranking. The principal notion in the TOPSIS approach is that the most preferred alternative should be farthest away from the negative ideal solution (NIS) and closest to the positive ideal solution (PIS). 78 Quick identification of the best alternative and from decision-makers, only limited subjective input is needed are the benefits of TOPSIS. 79 Following are the steps involved in TOPSIS:
Initially, normalize that decision matrix ( where, i = 1,…..,m and j = 1,……,n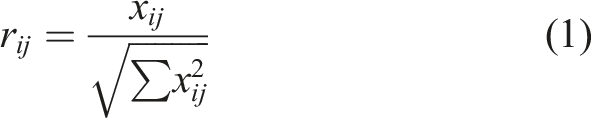
In this step, the weighted normalized decision matrix is constructed by using equation (2): Where 
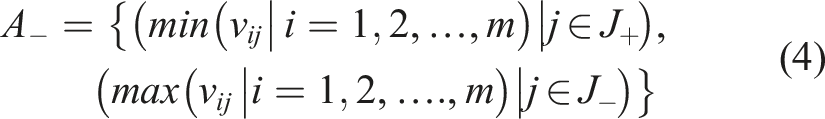
Here, the positive ideal solution V+ and the negative ideal solution V- are determined. In each column of the weighted normalized decision matrix, maximum and minimum values are denoted by 
Now, a separation measure is planned for each alternative. From a positive ideal alternative, separation is computed as: From a negative ideal alternative, separation is computed as: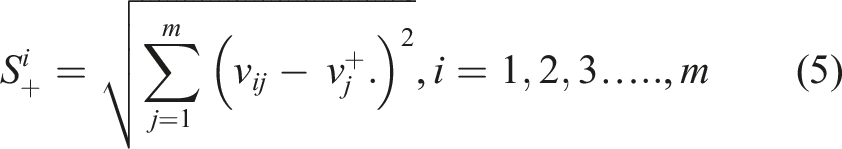

Now, for each barrier, relative closeness 
On the basis of relative closeness values, barriers are ranked in decreasing order of preference.
Interpretive Structural Modeling
Interpretive Structural Modeling (ISM) is considered a well-established methodology than Fuzzy Cognition Maps, DEMATEL, Graph Theory, Structural Equation Modeling (SEM) and Analytical Network Process (ANP) for ascertaining the relationships between distinct variables.72,80 ISM approach was proposed by Warfield. 81 The main logic behind this approach is to build a structural model by using the practical experience and knowledge of experts. Finding the interrelationship among elements is the focus of ISM, which is helpful for individuals. This approach develops a well-defined hierarchal model from unclear and poorly articulated data. ISM is helpful for both individuals and groups to provide a clear picture of the interrelationships.82,83
Following are the steps of the ISM methodology:84,85 1. Documents the IoT adoption barriers through the survey. 2. Establish the contextual relationships among identified elements to show the leading role of each element. 3. To show a pairwise relationship between elements, develop the structural self-interaction matrix (SSIM). 4. From SSIM, form the Initial Reachability Matrix (IRM) by converting the information in each entry of SSIM into 1s and 0s. Now, develop the Final Reachability Matrix (FRM) after detecting transitivity. 5. Partitioning the FRM into different levels. 6. Draw a directed graph based on FRM. 7. Build the ISM model after replacing the nodal elements with statements. 8. Analyze the ISM model to check for any inconsistency.
MICMAC
Duperrin and Godet 86 developed MICMAC (Cross-Impact Matrix Multiplication Applied to Classification) analysis, “an indirect classification technique”, which is helpful for critically investigating the scope of each barrier. This technique addresses the driving and dependence power of all obstacles individually. There are four clusters in MICMAC, namely, Autonomous, Dependent, Linkage and Independent, in which different IoT adoption barriers have been placed. Many ISM-based studies use the MICMAC approach to categorize elements because the ISM lacks this capability. 87
A real-case application of the proposed model (data analysis and results)
Selection of the most prominent IoT adoption barriers among numerous alternatives that dominate each other in different characteristics is difficult, so the proposed model is applied. The numeric application with the results has been described here based on the steps in the previous section.
Computation of weights
Groups of barriers.

The importance weights of all barriers.

Determination of final ranking
Initial decision matrix.

Normalized decision matrix.

Weighted normalized decision matrix.

Ideal best and negative ideal solution matrix.

Euclidean separation distance.

Barriers with the maximum Ci values were the major causal IoT adoption barriers. IoT adoption barriers can be ranked as B2-B5-B9-B1-B6-B12-B13-B4-B11-B7-B8-B10-B16-B15-B3-B14 in the decreasing order of preference.
Making of causal model showing the relationship among barriers
Renaming of barriers’ sequence.

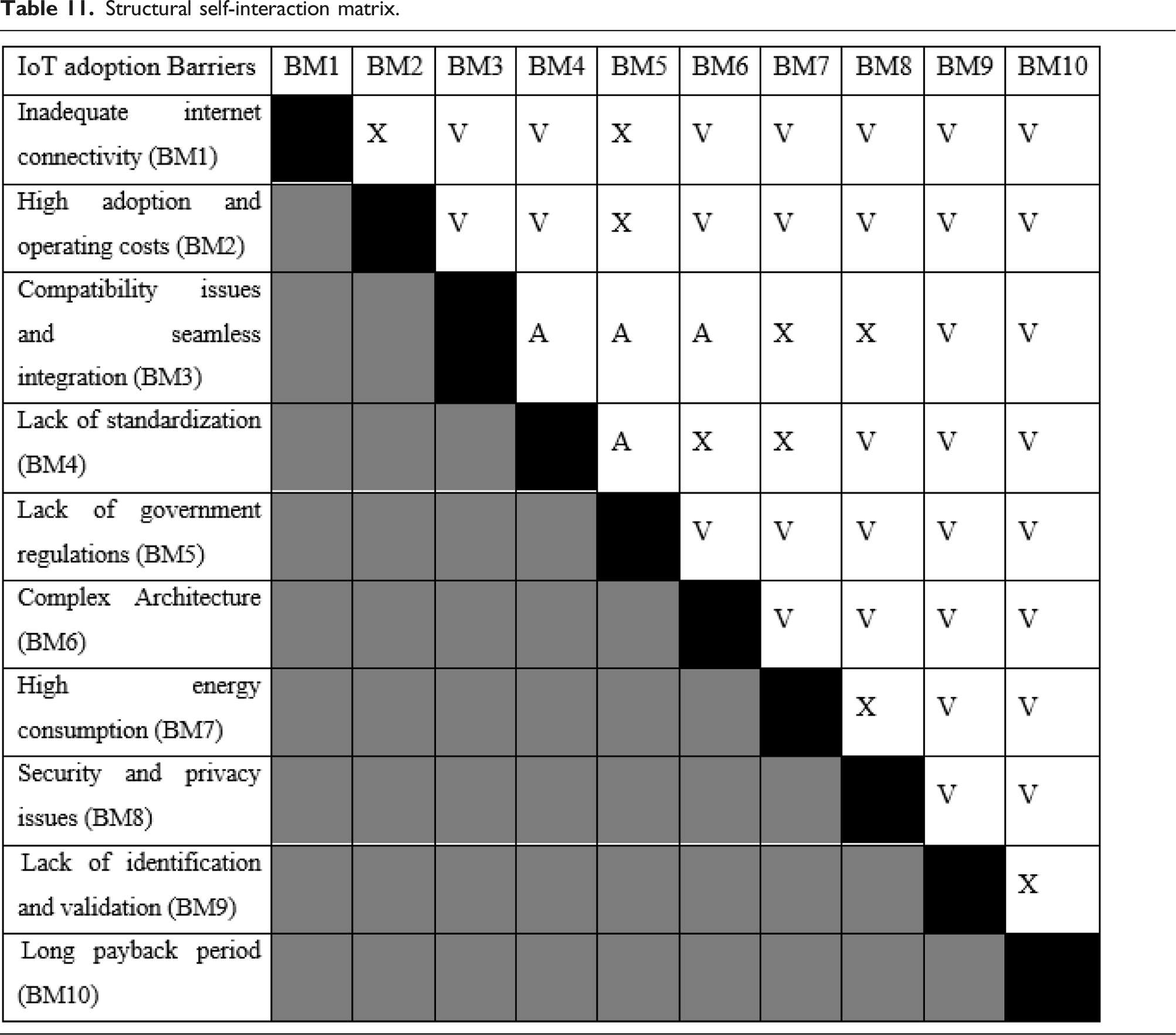
Structural self-interaction matrix development
Between any two barriers, a value of V, A, X or O was used to categorize the relationship in the structured questionnaire: V = barrier A = barrier X = interrelationship between O = between
Structural self-interaction matrix.
Reachability matrix formation


Final reachability matrix.

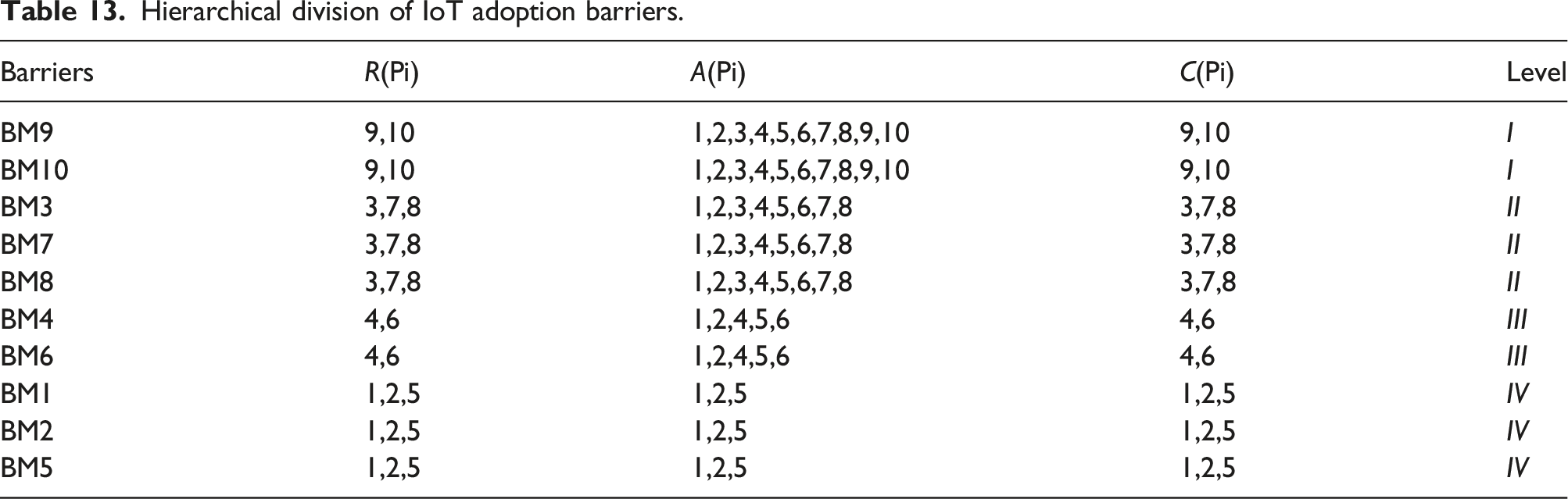
Hierarchical analysis
Hierarchical division of IoT adoption barriers.
Based on the above-defined interactions, a digraph was drawn, and by removing transitivity links, this digraph was converted to an interpretive structural model of barriers, as shown in Figure 1. Figure 1 shows that barriers have been placed in the same layer, which is at a similar level in the analysis mentioned above. Hierarchical structure of barriers (ISM graph).
Clustering of barriers (MICMAC analysis)
For investigating the scope of each barrier, MICMAC analysis is used. Analyzing each barrier's driving and dependence power is the key objective of MICMAC.
89
A diagram was built, as shown in Figure 2, and barriers have been categorized into four clusters. 1. Autonomous barriers are in the first cluster with weak driving and dependence powers. Because of weak links among them, such barriers are considered detached. In the current case, the autonomous cluster is empty, meaning the administration should pay severe devotion to all IoT adoption barriers. 2. The second cluster is about dependent barriers with strong dependence and weak driving power, and based on other barriers, their development mainly occurs. Such barriers are plotted in the right-bottom portion of the graph and exhibit the attributes of output variables. Five barriers, viz., Compatibility issues and seamless integration (BM3), High energy consumption (BM7), Security and privacy issues (BM8), Lack of identification and validation (BM9) and long payback period (BM10) are placed in this cluster. 3. Linkage barriers establish the third cluster with strong dependence as well as strong driving powers. They are placed in the right-top portion on both scales, and their values are above the middle. Such barriers not only drive the system but are also dependent on other barriers. In our study, Lack of standardization (BM4) and Complex Architecture (BM6) are in this cluster. 4. Independent barriers constitute the last cluster and are referred to as driver barriers. These barriers influence all the other barriers in the system considerably. In this research, Inadequate internet connectivity (BM1), High adoption and operating costs (BM2) and Lack of government regulations (BM5) are driving barriers. Driver power–dependence diagram.

Discussion
Figures 1 and 2 in the previous section summarize the studies' findings. Figure 1 shows the interactive relations between the barriers, whereas the distribution of these barriers with respect to their driving and dependence power is reflected in Figure 2. From the hierarchy structure shown in Figure 1, "driving barriers” can be seen at the lowest level. Including ‘Inadequate internet connectivity (BM1)’, ‘High adoption and operating costs (BM2)’ and ‘Lack of government regulations (BM5)’. The outcomes agree with the preceding studies that ‘Inadequate internet connectivity (BM1)’ is the main cause of IoT adoption and triggers the other barriers. 8 The findings are also aligned with Sharma, Joshi 48 study, which states that ‘Inadequate internet connectivity (BM1)’ and ‘Lack of government regulations (BM5)’ represent the consistent behavior of being greatly influential. Furthermore, ‘High adoption and operating costs (BM2)’ is another important driving barrier. The previous study by Luthra, Garg 90 is similar to the current result.
‘Lack of standardization’ (BM4) and ‘Complex Architecture’ (BM6) are classified as linkage barriers in Figure 2. From the driving barriers, they receive the influence and, in turn, apply effects on dependent barriers. BM4 and BM6 will be triggered and affected by driving barriers (BM1, BM2 and BM5). The literature also suggests that BM1 (Inadequate internet connectivity) and BM5 (Lack of government regulations) influence BM4 (Lack of standardization) and BM6 (Complex Architecture).8,48 The findings are also aligned with Luthra, Garg 43 study, which states that BM4 (Lack of standardization) and BM6 (Complex Architecture & IT infrastructure) capture third and fourth place, respectively, in IoT adoption challenges.
In turn, BM4 and BM6 will exert influence on the dependent barriers such as ‘Compatibility issues and seamless integration (BM3)’, ‘High energy consumption (BM7)’, ‘Security and privacy issues (BM8)’, ‘Lack of identification and validation (BM9)’ and ‘Long payback period (BM10)’. Such barriers display the attributes of output variables within the entire system. The findings of Kamble, Gunasekaran 8 also indicate that BM10, BM9 and BM7 are highly energetic and dependent on the other barriers included in the system. These outcomes also align with Kamble, Gunasekaran, 91 who referred to the ‘Lack of identification and validation & lack of a clear comprehension about the IoT benefits (BM9)’ as a dependent barrier. Consistent with earlier studies, 48 this study also shows that ‘Security and privacy issues (BM8)’ are perennial concerns when discussing IoT adoption and treating it as a barrier. This outcome also concurs with prior empirical studies, 92 which show that security and privacy issues are dependent barriers. Tackling these barriers will spur and foster the IoT adoption process.
Theoretical and managerial implications
Manufacturing organizations are searching for different sustainability programs to beat the growing competitive pressure, and IoT adoption is an emerging technology initiative. Identifying the most prominent IoT adoption barriers for agile manufacturing in the post-COVID-19 scenarios was the main contribution of the present study because barriers overshadow most firms' opportunities for IoT-related investment. Ordinarily, managing all barriers at a similar time is not feasible for top management because of the absence of adequate assets. In this regard, the current study shows an entire framework of critical barriers they must first work on. It implies that policymakers should pay serious attention to three causal barriers of Inadequate internet connectivity (BM1)’, ‘High adoption and operating costs (BM2)’ and ‘Lack of government regulations (BM5) as they directly or indirectly control every other barrier. And to track down these obstacles, practitioners can extrapolate this model. By proposing implications for policymakers, this work helps manufacturing organizations reduce complexities in IoT adoption, and compliance with this framework will also boost consumer trust. At a massive scale, this study would enhance and foster IoT adoption both in social platforms and academic institutions.
Conclusion
This research aimed to classify the significant barriers associated with adopting IoT technologies in the manufacturing sector in the post-COVID-19 lockdown scenario through an expert survey of industry leaders. Using an extensive literature survey, 16 IoT adoption barriers were identified and validated by academicians and industry experts. To study IoT adoption barriers, 3 data analysis techniques, AHP, TOPSIS and ISM, have been uniquely employed. These techniques highlight the substantial driver barriers that might serve as a major stimulus in IoT adoption. These barriers were categorized into four classes based on their driving and dependence powers, and because of high driving power and less dependence, independent barriers are of crucial significance. Finally, a unique causal model was developed with the support of top-listed IoT adoption barriers to facilitate the root cause analysis.
For practitioners and policymakers, current research is invaluable in understanding the implementation of IoT and the barriers obstructing its application. Future researchers should replicate the study and collect data from other regions besides the manufacturing sector. As each country has different economic, political, social and environmental conditions, it is imperative to mention that different countries might generate different results. Also, there may be some other obstacles that have not been identified and included in this paper. In addition, probing ways to overcome the examined barriers may be the theme of further studies. Furthermore, through Structural Equation Modeling (SEM), the final model should be validated statistically.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.

