Abstract
In recent years, data leakage incidents have been frequently exposed, and personal privacy protection has become a major issue. To explore the laws of data leakage and solve practical problems, the reasons for data leakage and the evolution of players’ strategy in the game are discussed. After sorting out the interest relationship of data leakage incidents, a three-party evolution model of invaders, operators, and regulators is established to analyze the evolution path from the perspective of a single party. The Lyapunov theory is used to analyze the stability of equilibrium points of the system and then verified by MATLAB simulation. The influence relationship of various parameters on the system is analyzed. Finally, the ideal state is defined and the system is attempted to be modified. The results demonstrate that under the current system, the evolution direction cannot be changed by the initial intention of players. The game result will eventually form a situation with a strong attack from invaders, advanced defense from operators, and extensive management from regulators. The attack level can be reduced by adjusting the controllable parameters, modifying the evolution path, and calculating the parameter range.
Keywords
Introduction
With the advancement of social informatization, the demand for intelligence is constantly increasing in many industries, and user data is surging from “geometric level” to “exponential level.” People's awareness of information protection lags behind the development of big data, 1 which is reflected in the random storage of enterprise data, lack of protection measures, and inadequate supervision of government departments, creating external invading conditions for hackers. As the illegal income from data leakage far exceeds the criminal cost, hackers have inherent motivation to invade. In recent years, data leakage has become a major social problem worldwide because of frequent exposure of incidents. 2 It was reported that from illegal data theft at the upstream to data trading and fraud at the downstream, a complete black industrial chain has been formed, creating huge illegal profit space. A large amount of information is sold on the dark web. Data leakage makes information crimes be more accurate and seriously threatens personal, corporate and even national security. 3 As such, studying the process of data leakage has important practical significance for information management and control.
Due to the information asymmetry of all parties, data security protection is a game process in which all stakeholders make dynamic and irrational decisions. To this end, this paper mainly discusses the three-party game of data leakage, aiming to address the following key questions: Question 1, how does the existing three-party game system evolve? Question 2, how does operators adjust their strategies to maximize data protection at the lowest possible cost? Question 3, how does the supervisors adjust punishment measures to ensure the benign development of the industry?
The main contributions are as follows: (a) In data leakage cases, there is information asymmetry between operators and consumers, and consumers cannot participate in the game (in reality, few consumers defend their rights due to data leakage). As a result, on the basis of clarifying information leakage events, the uncertain value is quantified, and a new three-party evolutionary game model consisting of invaders, operators and regulators is constructed; (b) The system is analyzed and verified from two aspects: the evolution path analysis from the perspective of one party of the game and the stability analysis from the perspective of the whole; (c) The simulation is combined with the data leakage cost report and the general data protection regulations to complete data selection and verify the results that are close to reality; (d) The significance of modifying the evolutionary game path by changing the investment is that the optimal strategy of players, the value range of relevant parameters and the minimum investment of operators can be selected.
The rest chapters are as follows: Section 2 presents relevant research; Section 3 constructs the three-party game evolution model; Section 4 explores and analyzes the stable strategy and equilibrium point of the three-party; Section 5 implements simulation, validation, sensitivity analysis, and evolutionary path correction, and Section 6 presents the conclusion.
Related work
Information security has been a difficult problem for all governments around the world. As a main content of information security, information leakage has become a hotspot of scholars. In fact, the information leakage event is mainly a series of activities carried out by the four parties involved with invaders (hackers), operators (enterprises), regulators (local government, industry association, and more), and victims (consumers). Current research mainly focuses on the infringement mechanism of personal information and the game between the players of information leakage.
Invasion mechanism of personal information
The macro level includes the generation mechanism of personal information leakage,2,3 transmission process, 4 and governance countermeasures.5–9 Based on 650 cases of personal information infringement, Ye and Zhao 3 analyzed and explained the mechanism using an economic model and concluded that personal information infringement was characterized by high quantity, low risk, low cost, light punishment, high crime success rate, and high income. Based on the dissemination theory, Ma and Xu 4 improved the Rathwell model and thought that the communication included two sources of hackers and moles, two communication modes of platform leakage and individual trafficking, and five leakage consequences of promotion, illegal business competition, and criminal crimes. Van der Kleij et al. 5 analyzed the interaction of employee knowledge, opportunity, and motivation based on the data leakage prevention behaviors of 384 bank employees and proposed a framework to shape a corporate culture to prevent data leakage of employees. In view of the problem of accidental data leakage caused by mail, network, and more, Guri et al. 6 proposed a method to simulate the leakage scenario of real network topology. Eom and Huh 7 studied the problem of leaking users’ personal information by the internet of things system (IoTSyS) and proposed an anonymous scheme taking into account information protection and legitimate user confirmation to provide a solution for the privacy protection of IoTSyS. Alneyadi et al. 8 thought that traditional data protection measures such as firewall, VPN, and intrusion detection lack initiative. They defined a data leakage prevention system and implemented its deployment on the network to provide a solution for proactive data prevention. Schwarzbach et al. 9 studied information sharing and data sensitivity between supply chains and proposed privacy-preserving business process execution architecture. In terms of data protection, Stergiou et al. 10 proposed a new cloud computing system for privacy. This system integrates with IOT and establishes a network security-based architecture by installing a security “wall” between cloud servers and different users on the Internet, aiming at improving the security and privacy issues. Tewari and Gupta 11 proposed a new ultra-lightweight IoT device tag mutual authentication protocol to protect RFID tags through encryption mechanisms and timestamps, to prevent adversary desynchronization behavior and overcome data security and privacy issues.
The game between information leakage subjects
The main content includes strategy selection of all parties, investment of defenders, protection of consumer rights, and punishment intensity of regulators. For specific practical problems, different subject behaviors are simulated, which can be divided into three categories according to the subjects involved:
Game between attack and defense. Based on the actual background of the conflict between two parties, Liu et al.
12
built a game model and simulated the dynamic process of network attack and defense simulation parameters under different situations, aiming to provide a theoretical basis for the study of network information security conflict. However, there is no research on how to adjust the income function for effective control. Sun
13
analyzed the information security of cloud services through an established game model and improved the classical dynamic replication equations by incentive coefficients. To deal with the strategic choice in the case of Distributed Denial of Service (DDoS), Aydeger et al.
14
established a defense signal game model to obtain the best defense strategy by solving the game equilibrium, thereby effectively mitigating SLFA (Stealthy Link Flooding Attacks, a variant of DDoS). Abass et al.
15
thought that data centers and cloud storage were subjected to advanced persistent threats (APTs). They established a network attack and defense game model for optimal defense strategy choice under APTs attack, to deduce the ESS of APTs defense game and provide the conditions for each ESS. Kandoussi et al.
16
proposed an integrated defense method combining virtual machine migration with honeypot technology and used random game theory to determine potential attack paths under attack and defense conditions. Jakóbik
17
proposed a game decision-making model based on a cloud computing system and established two types of players: cloud computing providers and attackers. Moreover, an artificial neural network is also applied to obtain the utility function and simulate the optimal defense strategy. According to a Bayesian game-based DDoS Defense mechanism, Dahiya and Gupta
18
calculated the probability of malicious nodes by sharing information between users to fight against malicious users in the network and established a Bayesian pricing and auction mechanism to achieve Bayesian Nash equilibrium points in different scenarios. De Witte et al.
19
detailed a policy defense configuration model in which defenders share sensitive information in the network and invest to defend against cyberattacks. They also analyzed how the attack type of the opponent affects the investment of agents. The game model with attack and defense as the main body can effectively deal with the network confrontation, but it ignores the players such as user data leakage and government supervision who have limitations in the choice of game parties. Two-sided game around information security subjects. Li
20
studied the information security investment of information-sharing platforms through evolutionary games and analyzed the strategic evolution of the platforms and its influencing factors. Regrettably, only two companies were modeled. Li et al.
21
proposed an evolutionary game model for privacy protection between e-commerce enterprises and consumers and adjusted the initial intention, privacy protection cost, and commodity price to make the system develop in a win-win direction. Zou et al.
22
believed that the game subject of information security is operators and the regulators. They built a game model for operations and regulators and analyzed the influence of the strategy choice and punishment intensity, and found that heavy punishment intensity can accelerate the convergence speed. The two-sided game around the information security subject has been deeply studied, but the composition of the game players is not comprehensive enough. Game between consumers, operators, and regulators. Combined with the actual situation, Qu and Hou (2020) constructed an evolutionary game model for users and governments. The influence of subjects’ intention on user right protection, user information platform disclosure, and government punishment was analyzed. In the face of a large number of data leakage, users are rarely able to protect their personal rights. Generally, data leakage events can be simplified into invaders’ attack, operators’ defenses, consumer information leakage, and regulators’ management. In fact, even if data leakage is reported, the public does not know the details of the leaked information. On the other hand, when consumers suffer from telecom fraud, it is impossible for them to accurately know which operator leaked their privacy. Obviously, there is asymmetric information between operators and consumers. Among the numerous data leakage incidents, there are few cases where the protection of consumers’ personal rights can be realized.
Industry application of game theory
In recent years, game theory has been widely used in various industries. Zheng et al. 23 applied the incomplete information dynamic game to the recycling supply chain of construction and demolition waste (CDW), revealing the impact of information sharing on the recycler market. Ma et al. 24 built a duopoly game model between green and traditional developers and applied it to the building carbon emissions to study the pricing decisions, profits of green developers and carbon emission reduction of green housing. Yu and Rehman et al. 25 applied the evolutionary game model to the financing decision-making of agricultural product suppliers and studied the evolution of green agricultural product supply chain financing system. Hosseini et al. 26 proposed a profit plus distribution (PSD) mechanism for supply chain coordination using evolutionary game theory and explored how the long-term behavior of supply chains (SCs) members would affect coordinated decision-making. Li et al. 27 introduced enterprise leadership into the evolutionary game model and studied the optimal decision-making of the recovery supply chain of CDW under different conditions. To explore the influence of group behavior for the spread of misinformation, Xianyong Li et al. (2022) constructed a tripartite evolutionary game model for the spread of misinformation and effectively analyzed the influence of network media, government, and Internet users’ decisions on the spread of misinformation. 28
In this way, the three-party game that leads to a data leakage event includes invaders, operators, and regulators. Throughout the research on the information security evolutionary game, the players mainly focus on the attackers and defenders, operators and regulators, or regulators, operators, and consumers. The first two types of research are not comprehensive enough. The third is less reasonable in the selection of players, leading to an unclear game mechanism and limited practical significance. Few scholars combine the game situation of invaders, operators, and regulators. On the basis of redefining the game subject, this paper constructs a three-party evolutionary game model, aiming to select the optimal strategy of players and calculate the relevant parameter range of operators. According to a large number of data leakage cases in reality and the practical significance introduced in Table 1, adopting the evolutionary game method is a good measure.
Role information of data leakage in the three-party game.

The main originalities of this paper are as follows: (a) In view of the uncertainty of the degree of data leakage after intrusion, the profit and loss coefficients of attack and defense are set to quantify the leakage degree; (b) The interests of players are analyzed and a new three-party game model is established; (c) The data in the “A cost of Data Breach Report” and “General Data Protection Regulation” are selected for actual verification; (d) The simulation experiments find that changing the initial choice will not break the relationship of interests, and eventually lead to invaders’ strong attacks, operators’ advanced defense, and regulators’ extensive supervision. Increasing the investment of operators can significantly improve this situation, whereas the investment cannot be too high, which has a critical value.
Main steps of the three-party evolutionary game model
The main methods are as follows: (a) Define the game players of information leakage; (b) Analyze the interest relationship of the game players (invaders, operators, and regulatory departments) and find out the key influencing factors; (c) Put forward the preconditions and assumptions of the model and complete the analysis and quantification of cost-benefit indicators; (d) Build an evolutionary game model, including constructing a payoff matrix, calculating the expected return, average return and replicating the dynamic equations of the strategy; (e) Model analysis and simulation.
The application of the Lyapunov stability criterion is as follows: a three-dimensional replication dynamic system equation is established by simultaneous replication dynamic equations, and the Jacobian determinant
Game model hypothesis and construction
Problem description
The development of data leakage can be summarized, as shown in Figure 1. To obtain the hidden value of the data (e.g. data analysis, peddling in the dark web), the invader attacks the system through certain technical to obtain system permissions and steal user data.27,29 Because of different security principles, 30 technology, and tools, invaders have different invasion abilities. 31 To prevent data from intrusion, operators take certain measures (such as installing external security devices, updating technologies, and optimizing management) to achieve information systems for data security protection, and different defense capabilities are affected by the investment of enterprises.32–34 During the attack and defense process, according to the development plan, regulators adopt different management methods (extensive management, and fine management) to invest corresponding manpower, material, and financial resources to manage citizens and enterprises and protect the rights of economic subjects. This measure can ensure the security of enterprise information and promote the benign operation of society for positive and orderly development.35,36

Logic diagram of three-party game.
When information leakage occurs, regulators shall take some measures such as investigation, interview, and rectification to impose penalties on both sides according to the actual situation.
Model assumptions
Game subjects (player)
The game subjects include three players: invaders, operators, and regulators. An invader represents an individual or organization that attacks a network system; an operator represents an enterprise and institution that takes measures to prevent intrusion, and a regulator represents the department that supervises citizens and organizations. The practical significance 22 of game parties is shown in Table 1.37–40
Economic man hypothesis
The main purpose of the game subjects is to maximize their own interests. First, invaders are trying to gain access under limited conditions to achieve more data for profit. Then, to reduce security costs as much as possible, operators protect their data resources and business positions to avoid punishment by regulators. Finally, to guide enterprises to standardize the development of information security, regulators supervise citizens and enterprises to achieve the highest management efficiency.
Bounded rationality hypothesis
The players (invaders, operators, regulators) are bounded rational. Due to the complexity of information security supervision, network attacks, data leakage, and the cognitive differences among the three-party of the game, each player has to find the most favorable strategy through constant trial and error.
Game strategy
The strategy selection space of invaders, operators, and regulators is {strong attack, general attack}, {advanced defense, basic defense}, and {extensive management, fine management}, respectively. The practical significance of specific strategies is shown in Table 2.
Strategy space of players and its significance.

Parameter settings
Proportion of strategy selection
The proportion of invaders choosing strong attack strategy is x and that of a general attack strategy is
Invaders parameters
The cost for invaders to choose a strong attack is
Attack and defense profit and loss coefficient table.

Operator parameters
The investment required by an operator to choose advanced defense is
Parameters of regulators
The fine management cost required by regulators is
Parameter symbols and meanings of the three-party in the game.

According to the above assumptions, the mixed strategy game matrix among invaders, operators, and regulators can be obtained, as shown in Table 5, where the benefit values represent invaders, operators, and regulators in turn.
Benefit statement in the three-party game.

Solution and analysis of the model
Game model solution
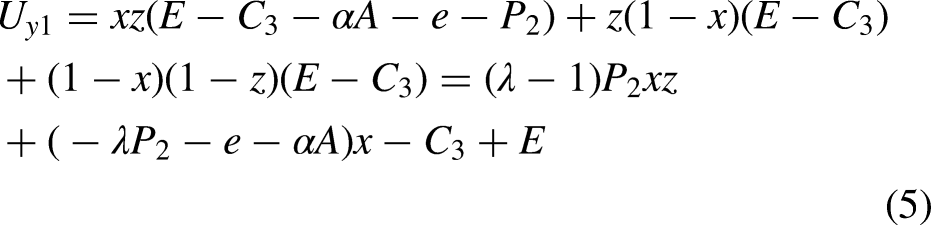
Replication dynamics equations of invaders
The expected benefits of invaders choosing a strong attack are as follows:
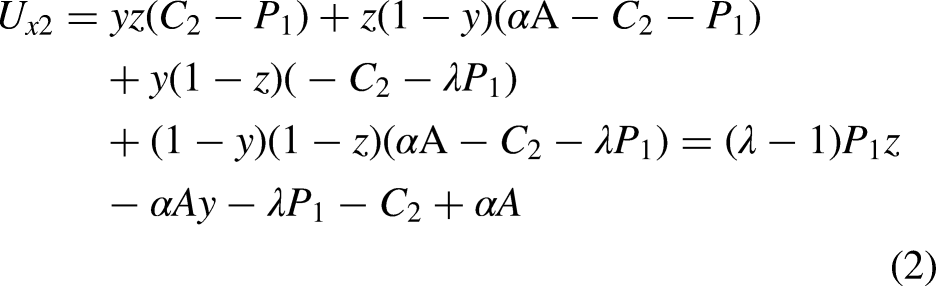

Replication dynamics equations of operators
The expected benefits of operators choosing advanced defense are as follows:



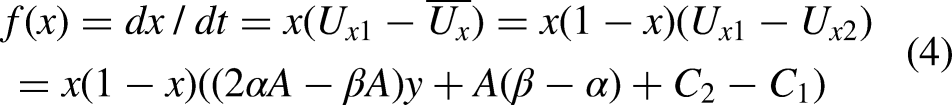
Replication dynamic equations of regulators
The expected benefits of regulators choosing fine management are as follows:


Tripartite evolutionary path analysis based on unilateral perspective
Evolutionary path analysis of invaders
The zero case of
Distribution of stable points of invaders’ evolution under different conditions.

When the operator's strategy and profit and loss coefficient meet I
Evolutionary path analysis of operators
The zero case of
Stable point distribution of operator evolution under different conditions.

When
Evolutionary path analysis of regulators
The zero case of
Distribution of regulatory evolution stability points under different conditions.
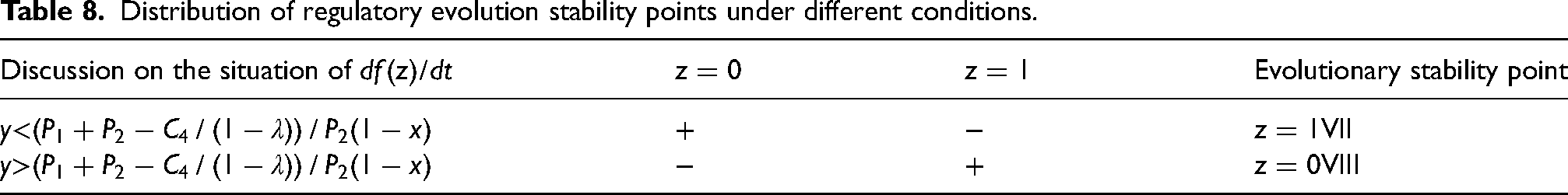
When
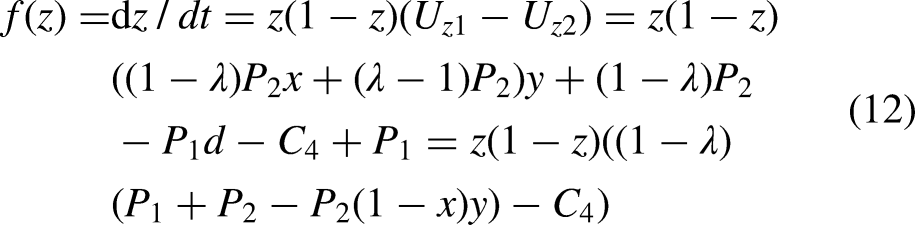
Stability analysis of equilibrium points in the three-party evolutionary game system
Combining the replication dynamic equations of invaders, operators, and regulators, a three-dimensional replication dynamic system is obtained in the evolutionary game process of three players.



Eigenvalue matrix of the three dimensional replicative dynamical system.

For asymmetric games, if the equilibrium of an evolutionary game is asymptotically stable, the result must satisfy that the equilibrium is a strict Nash equilibrium, which is pure strategy equilibrium.
43
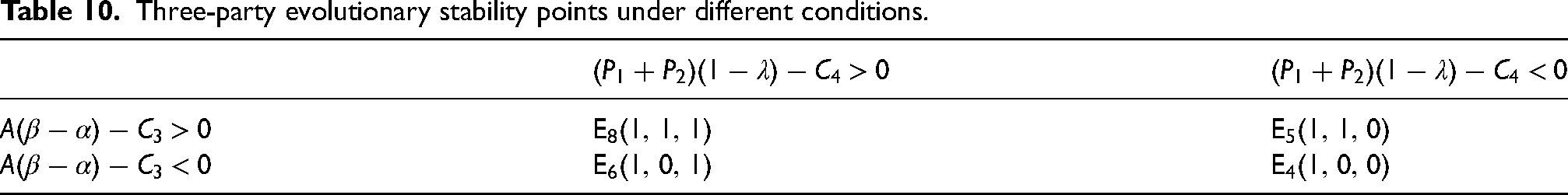
To analyze the asymptotic stability of equilibrium points of the replication dynamic equation, we only need to discuss the asymptotic stability of the equilibrium point in the replication dynamic equations involving pure strategies, and the equilibrium points that satisfy the conditions include
Three-party evolutionary stability points under different conditions.
Simulation analysis and evolution correction
The evolutionary game process of the behavior of the three players is simulated using MATLAB 2015 software and the evolutionary stability is verified.
Selection of initial simulation data
According to the Global Data Breach Cost Report released by IBM in 2020, the average total cost of data leakage events is 3.86 million dollars in 2020. As such, $3.5-$4 million is a reasonable range of average total cost. Since catastrophic large-scale data leakage is not universal and persuasive, the average total cost in this report is no more than 100,000 records of data leakage events as the research target. This paper continues to use the data volume of 100,000 copies (Ponemon Institute).
44
According to the General Data Protection Regulation implemented by the European Union, Internet companies that illegally collect personal information can be fined up to 20 million Euros, which is equivalent to about 17 million dollars at the exchange rate of USD and Euro 0.85. Thereby 15–20 million yuan is the reasonable range of punishment. Suppose the time and energy cost of a strong attack of an invader is $2 million, and the time and energy cost of the general attack is $500,000. The value of own assets is $150 per piece; the fixed income of data resources is $300 per piece, and the individual penalty is
According to the report, the average leakage cost caused by malicious attacks that destroy data with destructive/wiper attacks is $4.52 million, and the cost of hacking is much less than the cost of operators
Based on the above analysis, the initial parameters that are in line with the actual situation are finally determined, as shown in Table 11. Except for coefficients, all parameters are in units of millions (
Initial simulation parameters.

Influence factors and evolution path of game
To explore the impact of initial intention on the system, the values in [0, 1] are uniformly selected to observe the change of strategy choice. Specifically, according to observing Eq. (13) of the three-dimensional replication dynamic system and comparing the parameter settings of the three-party in Table 4, it can be seen that the game evolution of the three-party has nothing to do with the fixed profit value of the operator and the political profit and loss value of the government. The choice of invaders’ behavior strategy is related to the profit and loss coefficient, the data assets of operators, and the cost of different intrusions. The choice of operators’ behavior strategy is related to the punishment of regulators, the investment of defense measures, the investment of public relations, and the profit and loss coefficient. The choice of regulator's behavior strategy is related to the punishment and management investment. In addition, the choice of the three-party behavioral strategy is affected by the choice of other players in the derivate Eq. (13).
According to Table 11, the dynamic evolution process of the game under this state is simulated as shown in Figure 2. In Figure 2(a), the horizontal axis represents the evolution time and the vertical axis represents the proportion of strategy selection. Figure 2(b) shows the trend of the three-party strategy over time. The results show that when the initial condition of the three-party is (0.5, 0.5, 0.5), they will fall into the dilemma of “strong attack by invaders, advanced defense by operators and extensive management by regulators” to maximize their own interests. Taking

Probability diagram of strategy selection (a) and change trend of the three-party strategy over time (b).
Analysis of central equilibrium point
Substituting the simulation parameter set into Eq. (14) in Section 4.3, the solution is
Under the above assumptions, there is no stable central equilibrium in the current three-party game system, and the evolutionary game results can only be pure Nash equilibrium strategy.
Influence of players’ initial intention on the system evolution path
Due to
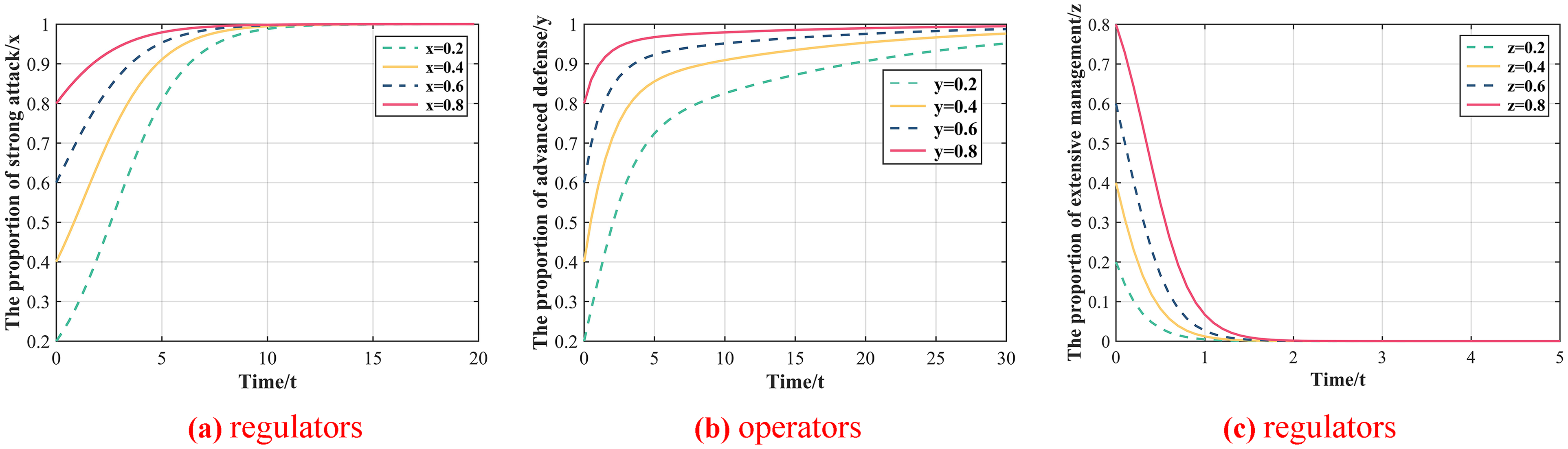
Influence of the initial intention of the three-party game players on the system evolution path.
For invaders, when x is 0.2, 0.4, 0.6, and 0.8, respectively, the evolutionary game is stable at
Based on the above analysis, it is concluded that under the current system, the initial intention of the three-party in the game changes the convergence speed without changing the evolution direction, which means that the information leakage is serious. Regardless of the percentage of initial intention, the result will translate into powerful attacks by invaders and widespread government-managed chaos. This means that the current situation is not optimistic and individual intentions cannot control the final result. Due to the interest tendency of all parties, an unfavorable situation will eventually be formed: Invaders choose strong attacks to bring greater benefits; operators choose advanced defense to mitigate property losses, and regulators choose extensive management to greatly save management costs.
Influence of controllable parameters on the system evolution
In the three-party game, each game can adjust some parameters according to the needs. For example, the invader can adjust the profit and loss coefficient
For the influence of the controllable parameters
Influence of invaders controllable parameters
and
on the system evolution
Let other conditions be unchanged, two groups of data satisfying condition I:
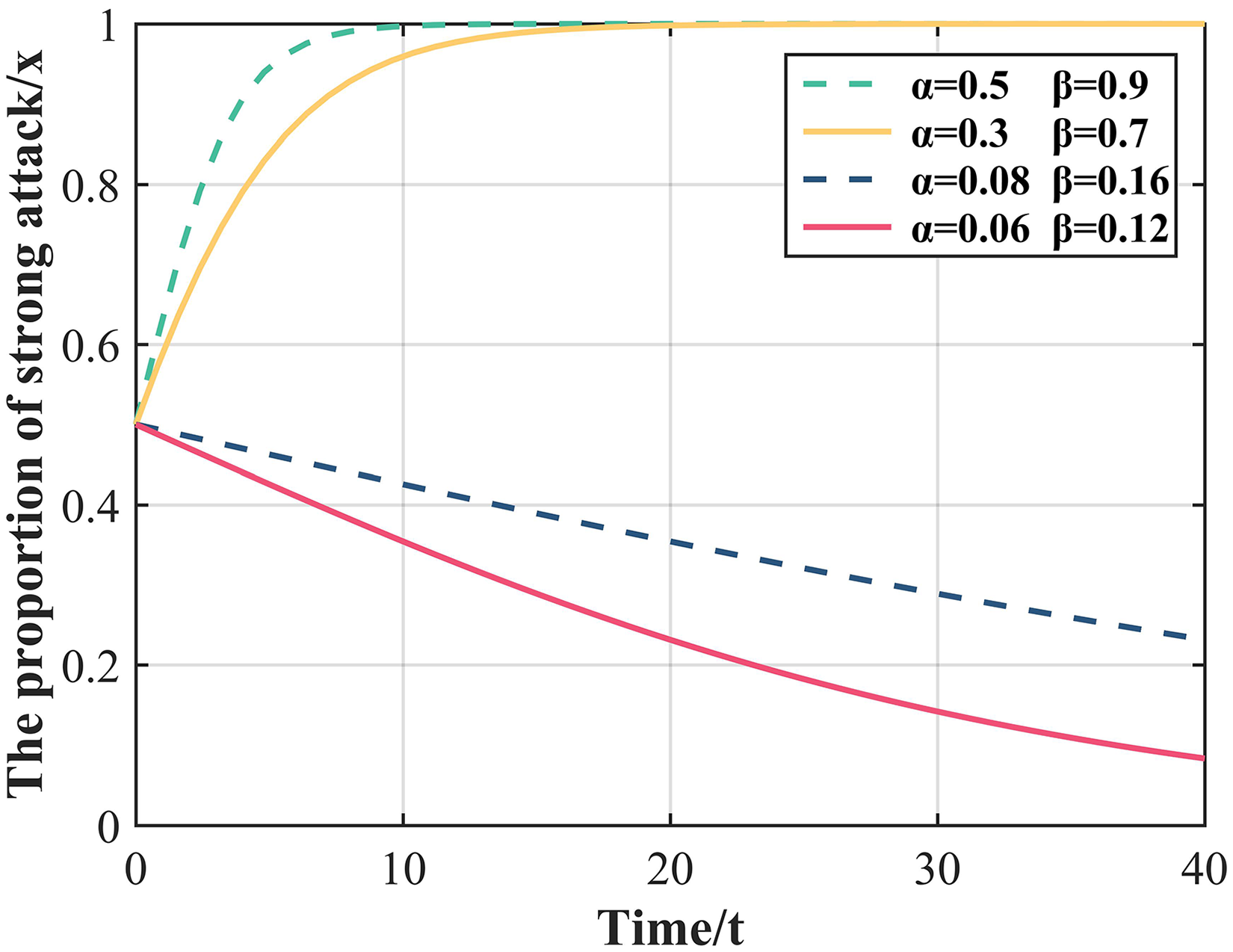
Influence of invaders’ controllable parameters
The four curves represent the changes of invader strategy selection over time under different conditions. The simulation results are consistent with the game analysis of conditions I and III, which eventually evolve to
Influence of operators’ controllable parameters
on the system evolution
Similarly, other control conditions remain unchanged, and four sets of data satisfying conditions V and VI are taken respectively as

Influence of operators controllable parameters
The four curves represent the changes of operator strategy choice over time under different conditions. The simulation results are in line with the game analysis of conditions V and VI and finally evolve to
Influence of regulators controllable parameters
and
on the system evolution
Other conditions remain unchanged, and two sets of data satisfying condition VII are taken, respectively, as

Influence of regulators controllable parameters
The four curves represent the changes of regulators strategy choice over time under different conditions. The simulation results are consistent with the game analysis of VII and VIII, and eventually evolve to
In the three-party game, based on the unilateral perspective (only changing the controllable parameters of one party), each game can adjust the parameter by changing its own technical means and measures to affect the evolution direction of the game, so that the game can evolve in its own favorable direction. This means that the gradual increase of investment by operators and the increase of punishment by regulators can effectively suppress intrusion. In addition, when the regulators change from extensive management to refined management, the increase of regulatory intensity will be strengthened to improve the probability of detecting invaders.
Ideal state definition and evolution path modification
According to the behaviors of the three-party game strategy, combined with the practical significance (social development needs), the evolution path that managers hope is that invaders’ strategy is a general attack; the operators’ strategy is advanced defense, and the regulators’ strategy is fine management to improve the low level of operators’ defense and regulatory management. Accordingly, (0, 1, 1) is the most ideal state.
Through the above analysis and simulation, the correctness of the model can be verified and the evolution results of some game systems can be obtained: the game status of the current system is (1, 1, 0), where invaders launch strong attacks, operators have advanced defenses and regulators have extensive management. However, this is far from the ideal state. To achieve the ideal state, the controllable parameters need to be adjusted to form a new evolutionary game system. Taking the controllable parameters as variables and restricting the evolutionary conditions to conditions II, V, VII or III, V, VII, Eq. (16) is obtained by simultaneously replicating the kinetic equations.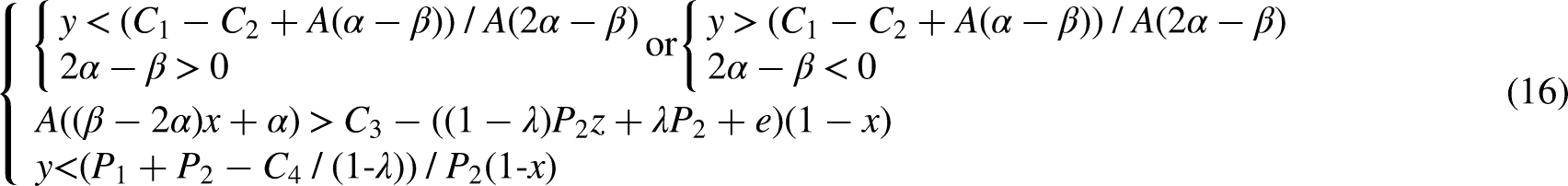
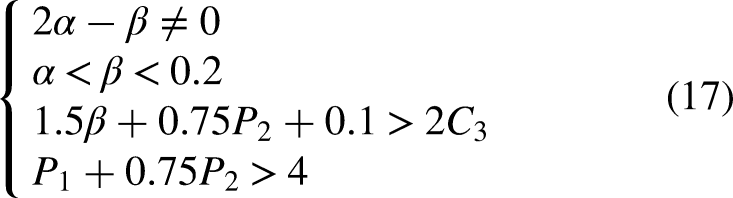
The new parameters

Strategy selection probability (a); Change trend of the three-party strategy over time (b).
As shown in Figure 7, the game result can be realized as (01,1) under the new system with modified parameters, where invaders evolve into general attacks, operators evolve into advanced defenses, and regulators evolve into fine management.
Scheme comparison
To prove the advantages of this model, the comparison between this model and other models is shown in Table 12. This model has advantages in the selection of game players, game theory analysis, and system correction and has greater practical significance.
Comparison of models and methods.

Conclusion
This article discusses how to reduce hacker attack level and reduce the investment of regulators and operators to achieve maximum protection of data security and development of information security. Based on the three-party evolutionary game model, a three-dimensional replication dynamic system is constructed, and the system stability is analyzed from the perspective of individual and the whole entity. Finally, the analysis results are verified by parameter simulation, and the evolution path is modified.
Under the assumptions of the model, that is economic man hypothesis, bounded rationality hypothesis, behavioral strategy hypothesis, and interest relationship hypothesis, the following conclusions are drawn:
(a) The profit and loss coefficients of attack and defense are set according to the uncertainty of the damage of intrusion system and data leakage to quantify the degree of leakage; (b) The evolution of the three-party game is not related to the fixed profit of operators and the profit and loss of government performance. There is no stable central equilibrium point in the game system, which means there is no mixed strategy to balance the interests of the three-party (the evolutionary game result will be a pure Nash equilibrium strategy); (c) In the current system, the initial intention of the three-party in the game will not change the evolution direction. Changing the original intention cannot break the interest relationship, and the profit drive and evolution direction are unchanged, the game results will eventually form the stability of invaders’ strong attack, operators’ advanced defense, and regulators’ extensive management; (d) From the perspective of unilateral (only changing the controllable parameter of one party), the stolen data of invaders, the investment of data protection, and the punishment intensity of regulators can be adjusted to make the game evolve in its favorable direction; (e) From the perspective of the whole system, the game result (01,1) can be achieved in the new system after parameter modification, that is, invaders evolve into general attack, operators evolve into advanced defense, and regulators evolve into refined management. At the same time, the evolution should satisfy the following four conditions:
According to research, some management enlightenment for operators and regulators is obtained as follows:
For operators, the choice of operators’ behavior strategy is related to the punishment
For regulators, the choice of regulators’ behavior strategies is related to the punishment
The limitations of this paper are as follows: (a) In terms of evolutionary process, players’ strategic orientation is profitable, and in reality, they will give up the strategy when the benefits fail to reach the expectation; (b) The range of punishment
Footnotes
Acknowledgments
This work was supported by Hebei Higher Education Teaching Reform Research and Practice Project (2020GJJG441) and Hebei Innovation Capability Enhancement Project (22550103D).
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the Hebei Innovation Capability Enhancement Project, Hebei Higher Education Teaching Reform Research and Practice Project, (grant number 22550103D, 2020GJJG441).
