Abstract
Wireless sensor networks, as a multi-hop self-organized network system formed by wireless communication, are vulnerable to malware diffusion by breaking the data confidentiality and service availability, owing to their low configuration and weak defense mechanism. To reveal the rules of malware diffusion in the really deployed wireless sensor networks, we propose a model called Malware Diffusion Based on Cellular Automaton to describe the dynamics of malware diffusion based on cellular automaton. According to the model, we first analyze and obtain the differential equations, which can reflect the various state dynamics of sensor nodes with cellular automaton. Then, we attain the equilibrium points of the model Malware Diffusion Based on Cellular Automaton to determine the threshold for whether malware will diffuse or die out in wireless sensor networks. Furthermore, we compute the basic regeneration number of the model Malware Diffusion Based on Cellular Automaton using the next-generation matrix and prove the stability of the equilibrium points. Finally, via experimental simulation, we verify the effectiveness of the model Malware Diffusion Based on Cellular Automaton, which can provide administrators with the theoretical guidance on suppressing malware diffusion in wireless sensor networks.
Introduction
Wireless sensor networks (WSNs) are extensively used in the real deployments, such as military and civil applications.1,2 WSNs are characterized by self-organization, dynamic topology, and limited capacity, and each sensor node (SN) has a limited communication range,3,4 so they are vulnerable to malware diffusion because of their low configuration and weak defense mechanism.5,6 Once WSNs are targeted by malware by exploiting network vulnerabilities, SN systems, or hardware and software vulnerabilities, the malware will quickly diffuse from one SN to another within communication range via communication.7,8
Malware is an application with malicious intent, which is intentionally developed by attackers to cause damage to SN systems by injecting malicious data, breaking data transmission, blocking the network, or exhausting the capacity of SNs to lead to the WSNs paralyzed.9–13 To solve the problem with malware diffusion in WSNs, the primary issue is to construct a malware diffusion model and to reveal the rules of malware diffusion which is helpful for suppressing malware diffusion.14–16
Epidemiology is commonly used to solve the problem with the dynamics of malware diffusion, because malware diffusion has the same characteristics as the propagation of epidemic.17,18 Researchers have presented many models,19,20 such as
To deal with the problem with malware diffusion in WSNs, we propose a model to describe the dynamics of malware diffusion based on cellular automaton (CA)21–23 that is more appropriate for describing the really deployed WSNs, compared with Markov chain. First, it can reflect the heterogeneity of WSNs by considering the networking and communication process among SNs and raising spatial-time discrete models of dynamical systems.
24
Second, the stochastic model established by Markov chain is usually in lack of space consideration and not applicable to describe the dynamics of malware diffusion, while the model based on CA can effectively overcome these problems. In the proposed model, one cellular lattice represents a cell, and the states of the cell can be obtained from the fraction of the number of SNs in states
In view of the above problem to be solved, we first propose a model called Malware Diffusion Based on Cellular Automaton (MDBCA), in which the SNs can be described by the five states
The rest of this article is presented as follows: in the second part, we review the related work. In the third section, we propose the model MDBCA and analyze and obtain differential equations of the model, which can reflect the dynamics of the fraction of SNs in states
Related work
At present, many researchers have presented various methods applicable to solve the problems with malware diffusion in WSNs. Liu et al. 25 used the stochastic game to propose a method for WSNs to predict the probability of malware adopting the spread behavior. Shen et al. 26 developed traditional epidemic theory and constructed a malware propagation model by differential equations to represent the dynamics between states. Shen et al. 27 considered heterogeneous wireless sensor networks (HWSNs) and set up a dependability assessment mechanism for HWSNs with malware diffusion. Shen et al. 20 considered a clustered WSN under epidemic-malware propagation conditions. Jiang et al. 28 considered that WSNs can prevent from malware based on Stackelberg game. Acarali et al. 29 applied the principles of epidemic modeling to IoT networks consisting of WSNs. Wang et al. 30 used the pulse differential equation and the epidemic theory to propose a method for WSNs preventing from malware diffusion.
Many researchers have studied epidemic spread using CA. Holko et al. 31 presented a new numerical, two-dimensional CA framework for simulation of the spread of an infectious disease. Sharma and Gupta 32 analyzed the SEIR (susceptible–exposed–infected–recovered) epidemic spread with time delay through a two-dimensional CA model. López et al. 33 addressed population heterogeneity and distribution in epidemics models using a CA framework for simulation of the spread of an approach. White et al. 34 introduced a theoretical model based on CA framework for simulation of the epidemic spreading.
However, some malware diffusion issues based on CA in the malware-infected WSNs still have not been considered. The first issue is the elements mapping between SNs and CA, and the second issue is how to determine the condition in which malware will diffuse or die out in the malware-infected WSNs. In this study, we solve the first issue by proposing the model MDBCA, which can reflect the dynamics of the fraction of SNs by the differential equations. Furthermore, we solve the second issue by proving the stability of the model MDBCA at the equilibrium points, which is mathematically verified for theoretical correctness.
Description of the model MDBCA
To simplify the research, we consider the malware-infected WSNs are deployed in a two-dimensional cellular lattice with a side length of
As for the application of CA to the model MDBCA, it is important to describe model elements, 35 including cell, cellular state, cellular neighbor, and cellular state transition function, under the diverse characteristics of malware diffusion.
Definition 1
CA can be described by the 5-tuplet,
Definition 2

Definition 3
Definition 4
Note that

State transform rates of SNs.
In Figure 1, the symbol
The state of the cell

Definition 5
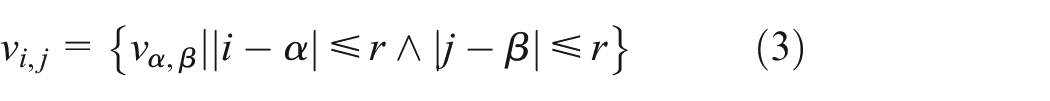
where
Definition 6
Since the state transition function of the cell

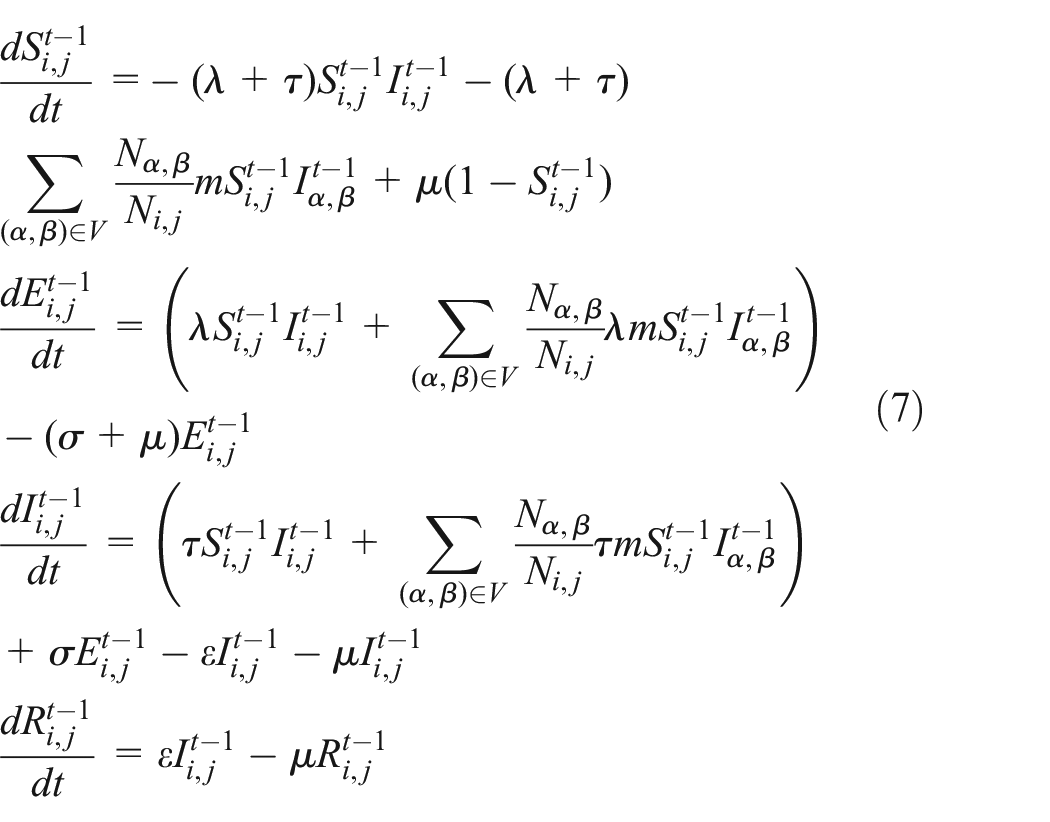
With the effect of the state transition functions and the transition rate among SNs, the dynamic transition relationship among SNs of the cell can be summarized as system (5), which is the local transition system of predicting

subject to
Here, the parameter
Stability analysis of the model MDBCA
System equilibrium points of the model MDBCA
System equilibrium points mean that the system finally converges to a stable state over time. As shown in system (5) above, the system reaches a stable state, when the
Performing Taylor expansion on the system (5) and keeping only the first two terms, we obtain system (6)

When
After directly solving system (7), we can identify two equilibrium points:




From the viewpoint of epidemiology, the equilibrium point
Stability analysis of the malware-free equilibrium point of the model MDBCA
In order to verify the stability of system (7) at the malware-free equilibrium point
If
If
In this article, the basic reproduction number

Theorem 1
If
Proof
According to stability theory for ordinary differential equations, if and only all the eigenvalues of the Jacobian matrix of an equilibrium point are less than zero, the equilibrium point is locally asymptotically stable. When system (7) is subjected to Taylor series expansion at

Here,


The submatrix of matrix (15) and its determinant value are evaluated as follows





Therefore, when
Theorem 1 indicates that when
Simulations and verification
The experimental simulation and data analysis in this article are completed by VC6.0 and MATLAB R2013a. The key parameters of the experimental simulation are set as follows: 30,000 SNs are distributed in the two-dimensional square area with a side of 100 × 100, and each square lattice is a cell, and all cells are fully connected with a communication radius 1. The Moore neighborhoods of each cell are its surrounding eight cells, and the
When
Case 1: the SNs uniformly distributed in cells
Validating stability of the malware-free equilibrium point
In this section, the initial state
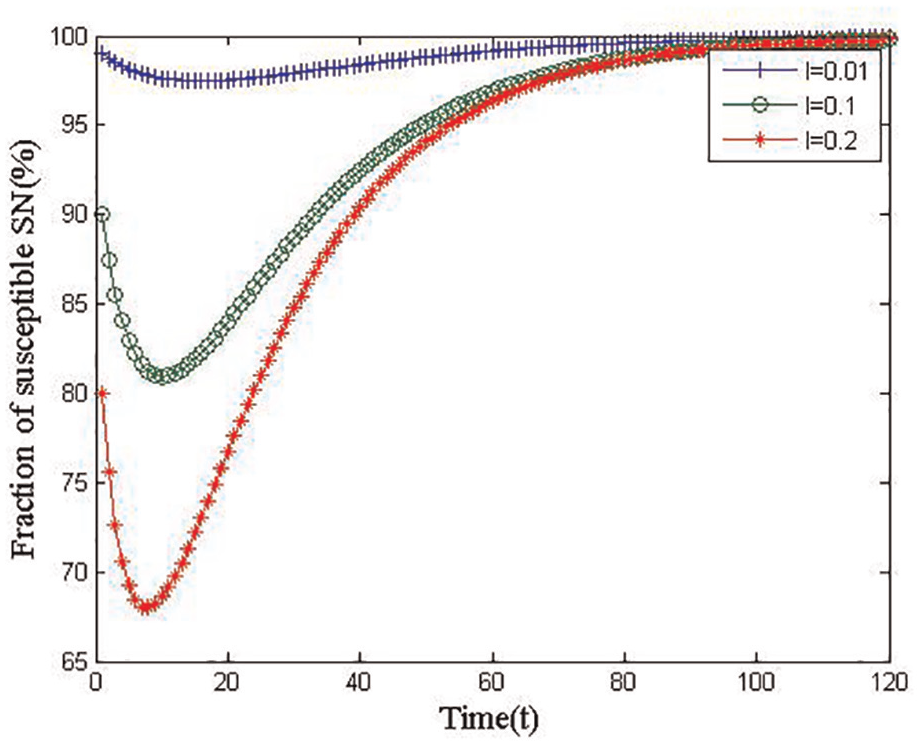
Changeable fraction trends of susceptible SNs under the condition of Theorem 1 with uniform distribution in the cells.
Figure 3 shows the changeable fraction trends of infectious SNs under the condition of Theorem 1 for

Changeable fraction trends of infectious SNs under the condition of Theorem 1 with uniform distribution in the cells.
Figure 4 shows the changeable fraction trends of exposed SNs under the condition of Theorem 1 for

Changeable fraction trends of exposed SNs under the condition of Theorem 1 with uniform distribution in the cells.
Figure 5 shows the changeable fraction trends of recovered SNs under the condition of Theorem 1 for

Changeable fraction trends of recovered SNs under the condition of Theorem 1 with uniform distribution in the cells.
According to the simulation experiments shown in Figures 2–5, we can conclude that when the SNs uniformly distribute in the cells, the fractions of susceptible, infectious, exposed, and recovered SNs all converge to the malware-free equilibrium
Case 2: the SNs randomly distributed in cells
Validating stability of the malware-free equilibrium point
In this section, the initial state

Changeable fraction trends of susceptible SNs under the condition of Theorem 1 with random distribution in the cells.
Figure 7 shows the changeable fraction trends of infectious SNs under the condition of Theorem 1 for

Changeable fraction trends of Infectious SNs under the condition of Theorem 1 with random distribution in the cells.
Figure 8 shows the changeable fraction trends of exposed SNs under the condition of Theorem 1 for

Changeable fraction trends of exposed SNs under the condition of Theorem 1 with random distribution in the cells.
Figure 9 shows the changeable fraction trends of recovered SNs under the condition of Theorem 1 for
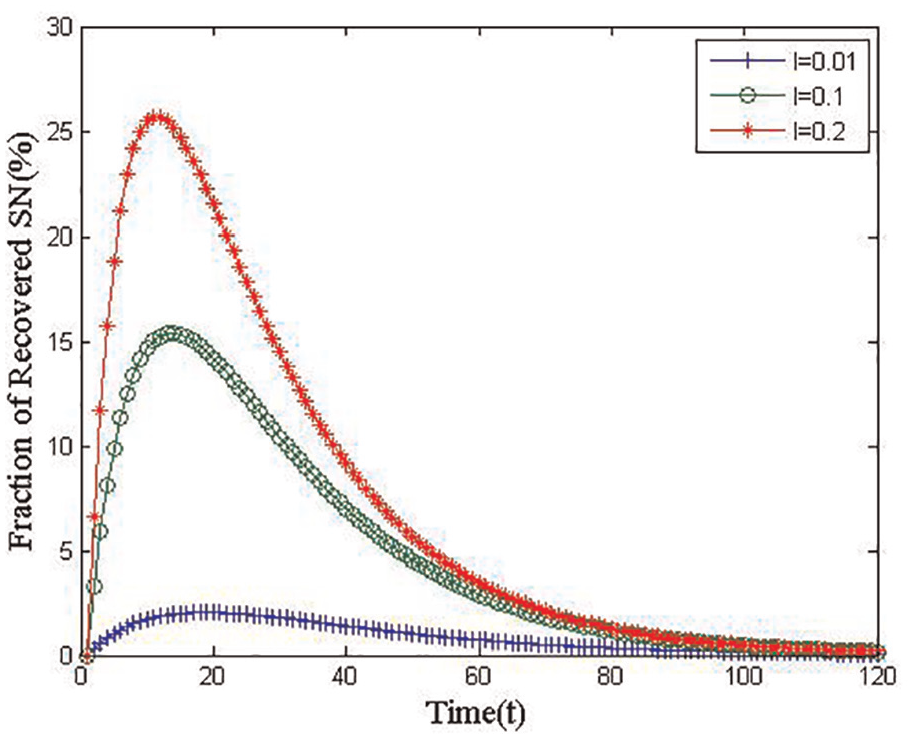
Changeable fraction trends of recovered SNs under the condition of Theorem 1 with random distribution in the cells.
According to the simulation experiments shown in Figures 6–9, we conclude that while the SNs randomly distribute in cells, regardless of the initial state distribution of the SNs in state
From these two cases, regardless of the SNs distributed in cells (randomly or uniformly) and the initial state distribution of the SNs in state
Conclusion
To discover the rules of malware diffusion in WSNs, this article proposes the model MDBCA, which is more appropriate for describing the really deployed WSNs, and can reflect the networking among SNs more realistically. First, after the elements of SNs in the malware-infected WSNs are mapped to the model elements of CA, we obtained the differential equations, which can reflect the various state dynamics of the SNs. Then, we attain two equilibrium points of the model MDBCA: one is the malware-free equilibrium point and the other is the endemic equilibrium point. Finally, we prove the stability of the malware-free equilibrium points by the basic regeneration number
Footnotes
Handling Editor: Yanjiao Chen
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by National Natural Science Foundation of China under grant No. 61772018.
