Abstract
In this article, we consider the problem of using multiple robots (searchers) to capture intruders in an environment. Assume that a robot can access the position of an intruder in real time, that is, an intruder is visible by a robot. We simplify the environment so that robots and worst-case intruders move along a weighted graph, which is a topological map of the environment. In such settings, a worst-case intruder is characterized by unbounded speed, complete awareness of searcher location and intent, and full knowledge of the search environment. The weight of an edge or a vertex in a weighted graph is a cost describing the clearing requirement of the edge or the vertex. This article provides non-monotone search algorithms to capture every visible intruder. Our algorithms are easy to implement, thus are suitable for practical robot applications. Based on the non-monotone search algorithms, we derive the minimum number of robots required to clear a weighted tree graph. Considering a general weighted graph, we derive bounds for the number of robots required. Finally, we present switching algorithms to improve the time efficiency of capturing intruders while not increasing the number of robots. We verify the effectiveness of our approach using MATLAB simulations.
Keywords
Introduction
Monitoring and securing of an environment is an important task in sensor networks. Sensor network becomes feasible due to the development of small sensor nodes, such as the Berkeley MOTES. 1 Research advances in sensor networks 2,3 demonstrated that small sensor nodes can be positioned to monitor the entire environments while detecting intruders.
Consider the case where the sensor network is completely built in an environment (The exploration and networking strategy in the study by Kim 4,5 can be applied to build the sensor network in an unknown environment.). The network can operate for many purposes, such as detecting intruders. Deployed sensor nodes form a network enabling robots (searchers) to exchange information with other robots or nodes. Moreover, sensor networks enable a robot to access every intruder’s location in real time. For instance, in the case where a sensor node n detects an adjacent intruder, this detection event can be relayed to all robots sharing the network so that every robot can perceive that n detected an intruder. Thus, an intruder is visible by a robot assisted by the sensor network.
Traditionally, intruder capture problems were handled utilizing two approaches. The first approach uses probabilistic formulations addressing average-case behaviors. 6 –12 The probabilistic approaches is the focus of the theory of search, which has a long-standing legacy in the field of operations research (OR). 13 Measures of interest can include expected time until capturing an evader. The assumption about knowledge about the evader’s behavior allows incorporating probabilistic uncertainty in target locations, their behaviors, and/or sensor observations. Suppose the evader maneuvers in a manner which is independent of the pursuer’s motion. For example, assume that the evader performs a random walk. In this case, it is possible to capture the evader even with a stationary pursuer, since the evader will meet the pursuer in the end. The main question here is the design of an optimal strategy to capture the randomly walking evader as quickly as possible. This is the focus of probabilistic search. 7
The second approach is on developing strategies which maximize search performance to capture a worst-case intruder. 7 A worst-case evader is characterized by unbounded speed, complete awareness of searcher’s position and intent, and full knowledge of the search environment. An intruder with unbounded speed represents a worst-case scenario for a robot capturing an intruder. This article handles a worst-case scenario where an intrude can move much faster than a robot. For instance, a robot can be a ground robot which moves slowly on the ground. On the other hand, an intruder is a fast moving car.
The strategies which maximize search performance to capture a worst-case intruder guarantee the success of the search, defined, for instance, by capture of the evader in finite time. We acknowledge that the powerful adversary model may provide solutions that are too conservative in practical applications. 7 However, this article shows that the presence of the sensor network can decrease the number of required robots considerably.
This article is based on the second approach which maximizes search performance against a worst-case intruder. More specifically, this article presents the minimum number of robots (searchers) required to capture worst-case intruders on the topological map of the workspace. This article considers a simplified environment where robots and worst-case intruders move along a weighted graph, which is a topological map of the environment. The weight of an edge or a vertex in a weighted graph is a cost describing the clearing requirement of the edge or the vertex.
Many papers exist on capturing worst-case intruders on graphs. 7,14 –30 Parsons 14 defined the graph searching problem initially. In this problem, searchers and worst-case intruders move along edges of a graph. Considering a finite workspace, a topological map (graph) representing the workspace is also finite. We introduce several definitions used in this article. An edge is cleared in the case where it does not contain an intruder. An edge is contaminated in the case where it contains an intruder. A monotone strategy is an intruder capturing strategy satisfying that once an edge is cleared, then the edge is not contaminated again. A non-monotone strategy is an intruder capturing strategy which is not monotone.
There are many variants of the graph searching problem originated from the study by Parsons.
14
A closely related work to ours is the helicopter cops and robbers game.
29,30
In this game,
29,30
an intruder is visible, since the cops have complete knowledge of robbers’ positions as if the cops are using helicopters. Furthermore, the cops can be placed on or removed from the vertices of the graph. A robber is captured when a cop lands on the vertex occupied by the robber, and the robber cannot make any move to escape. Seymour and Thomas
29
proved that if k cops can catch a visible intruder, then there is a monotone search strategy using k cops. Richerby and Thilikos
30
provided an upper bound for the minimum number of searchers to clear a graph G using a monotone strategy as
There are many articles on clearing a weighted graph. 16,19,32 –34 The weight of an edge or a vertex in a weighted graph is a cost describing the clearing requirement of the edge or the vertex. The problem is to find a strategy to clear a weighted graph with the lowest cost, that is, the minimum number of searchers to execute it. This problem is NP-hard. Kolling and Carpin 16 provided an upper bound for the minimum number of searchers by presenting a monotone search strategy to clear a weighted graph.
We consider a searcher that moves along a weighted graph continuously, which is adequate for mobile robot applications. This distinguishes our article from other articles 29,30 on graph searching, which assumed that a searcher (on a helicopter) can land on a vertex where a visible intruder exists.
The problem tackled in this article is distinct from that in Kolling and Carpin, 16 since we consider a visible intruder. This article assumes that an intruder is visible by a robot. As far as we know, no paper on clearing a weighted graph considered a visible intruder. Since this article considers a visible intruder, the number of searchers required to clear a weighted graph can reduce considerably compared to the case where an intruder is not visible.
We introduce non-monotone algorithms to clear a weighted graph. Our algorithms are easy to implement, thus are suitable for practical robot applications. Since our algorithms are not monotone, the number of searchers required to capture all intruders does not increase as the number of intruders increases. Based on the non-monotone searching algorithms, we derive the minimum number of searchers required to clear a weighted tree graph. We further show that the upper bound for the minimum number of robots required to clear a weighted graph can be calculated by solving the weighted feedback vertex set problem (WFVP). Vineet et al. 35 considered the WFVP for undirected graphs and showed that a generalized local ratio strategy leads to an efficient approximation with the performance guarantee of twice the optimal.
Considering some special graphs, the WFVP can be solved in polynomial time or in linear time. This implies that the upper bound for the minimum number of robots required to clear a weighted graph can be calculated in polynomial time or in linear time. In the case where the weighted graph is a diamond graph in the study by Carrabs et al., 36 we can solve the WFVP in linear time. 36 Also, we can solve the WFVP in polynomial time in the case where the graph is an interval graph, 37 co-comparability graph, 38 permutation graph, 39 or convex bipartite graph. 38
We further present switching algorithms to improve the time efficiency of capturing intruders while not increasing the number of searchers (robots). We verify the effectiveness of our approach using MATLAB simulations.
The second section presents preliminary information of this article. In the third section, we present non-monotone search algorithms to capture visible intruders. The fourth section presents switching algorithms to improve the time efficiency of capturing intruders while not increasing the number of robots. The fifth section provides MATLAB simulations to verify the effectiveness of our approach. The last section provides conclusions.
Preliminary information
This section presents preliminary information of this article.
Graph theory
We review some general notions in graph theory 40 An undirected graph G is defined by a set G = (V(G), E(G)), where V(G) denotes the vertex set and E(G) is a set of unordered pairs of vertices where multiple edges between vertex pairs are allowed.
A vertex v is said to be adjacent to another vertex w if the graph contains an edge {v, w}. In this case, v is a neighbor to w. A walk is a sequence of vertices and edges v
1,
Let T denote a tree graph, which is a graph without any cycle. Suppose n is a vertex of T. Then, we define a branch of T at n as the maximal subtree of T, denoted by T′, if n has degree 1 in T′. For instance, a branch of T at u is depicted with bold line segments in Figure 1.

A branch of T at u is depicted with bold line segments.
Given G, splitting of a vertex v is an operation . Here,

Splitting of a vertex v.
Given an undirected and vertex weighted graph G, the weighted feedback vertex problem (WFVP) consists in finding a subset
Problem description
We introduce the problem considered in this article. Consider the case where one or more robots are used to capture possible intruders in a given environment. Also, sensor nodes are positioned in the environment such that a robot can access the position of an intruder in real time. This environment was also considered in the study by Kim. 4,5 Where to deploy sensor nodes to cover the entire environment was considered in the study by Kim 4,5 and is not within the scope of this article.
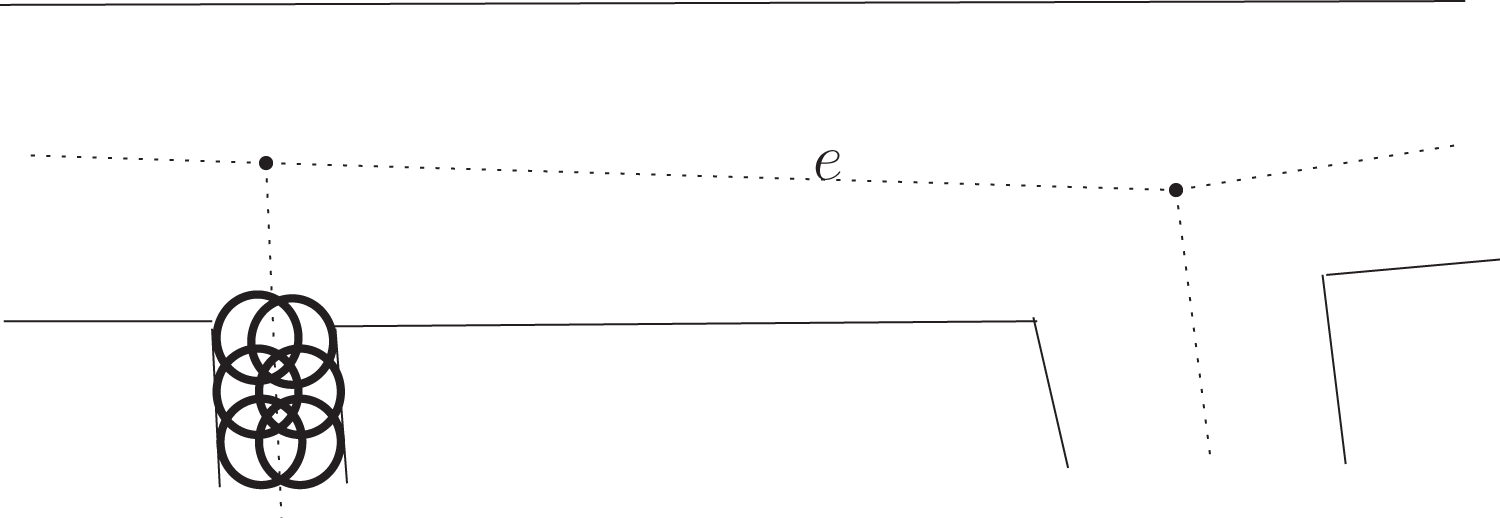
We consider a robot which is equipped with finite range weapons to capture (destroy) a nearby intruder. We say that an intruder is captured in the case where it is inside the maximum range of weapons of a robot. Even a very fast intruder (intruder with unbounded speed) is captured by a robot once the intruder is inside the maximum range of weapons of the robot. In Figure 3, a circle illustrates the maximum weapon range of a robot. The center of a circle represents the position of the robot associated to the circle.
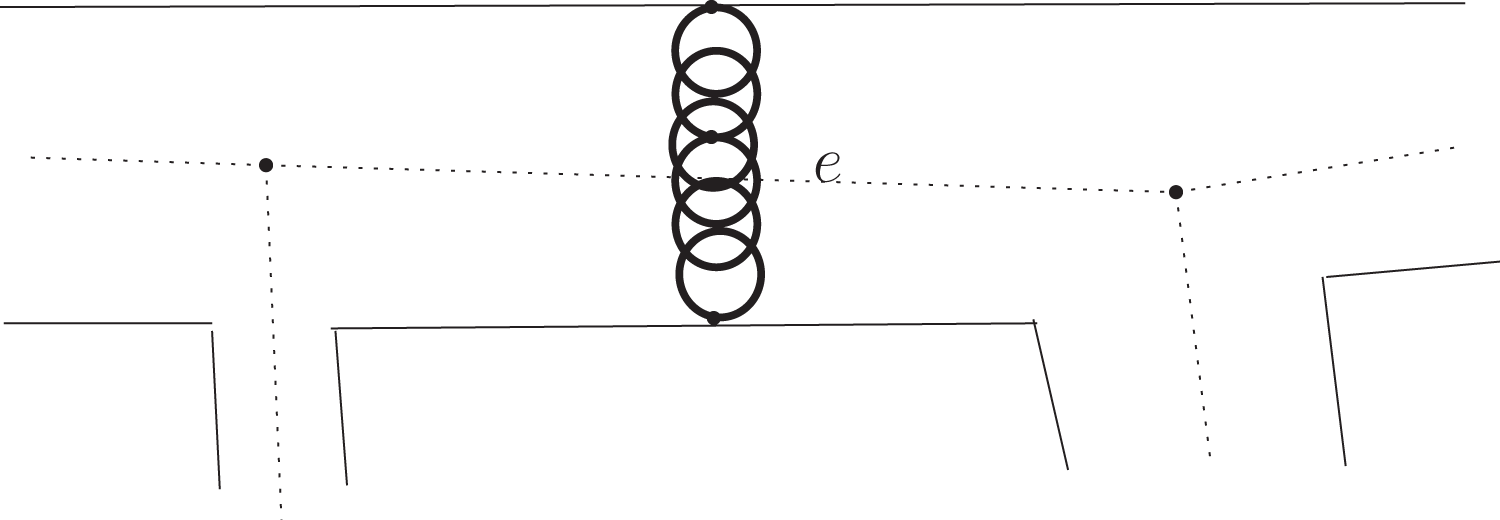
A circle illustrates the maximum weapon range of a robot. The center of a circle represents the position of the robot associated to the circle.
We summarize the assumptions in this article as follows.
A1: A robot has full knowledge of the search environment. A2: Sensor nodes are positioned in the environment such that a robot can access the position of an intruder in real time. In other words, an intruder is visible. A3: A robot is equipped with finite range weapons to capture (destroy) a nearby intruder which is inside the maximum range of weapons of the robot.
We propose a capture strategy based on the above assumptions. Using assumption (A1), we deploy guard robots at intersections in the workspace to block the escape of an intruder with unbounded speed. Using A3, a robot is equipped with finite range weapons to capture a nearby intruder. Even a very fast intruder (intruder with unbounded speed) is captured by a robot once the intruder is inside the maximum range of weapons of the robot. Considering the finite range, we make multiple robots (driving robots) form a dense formation so that they can drive an intruder until it is captured.
Using A2, an intruder is visible to the driving robots. The driving robots select one intruder as a target and chase the target while maintaining a dense formation. The robots form a dense formation so that the target cannot move through the formation without being caught. Since an intruder cannot move through the formation without being caught, we say that the driving robots sweep a passage.
See Figure 3 for an illustration of the case where six robots sweep a passage. In this figure, a circle illustrates the maximum weapon range of a robot. Only one robot cannot sweep this passage, since this passage is much wider than the weapon range of a robot. Similarly, multiple robots may be needed to guard an intersection.
As a topological map of an environment, we introduce a weighted graph Gl . Each vertex in Gl is associated to an intersection, and each edge in Gl is associated to a passage in the environment. Each vertex and edge in Gl has its weight. The weight of an edge or a vertex in Gl is a cost describing the clearing requirement of the edge or the vertex. To clear an edge e, at least w(e) robots must move along e as one group.
Figure 3 illustrates Gl
. In Figure 3, vertices in V(Gl
) are depicted with dots at the center of intersections. In this figure, edges in E(Gl
) are depicted with dotted line segments. In this figure, one group of six robots sweeps a passage while maintaining a dense formation. Thus, w(e) = 6 for the edge
We introduce non-monotone algorithms to clear Gl , considering both the number of robots required and the time efficiency. Based on the algorithms, we derive bounds for the minimum number of robots required to capture all intruders.
Non-monotone searching algorithms
In this section, we introduce non-monotone searching algorithms to capture visible intruders. Based on the searching algorithms, we derive bounds for the number of robots required to capture all intruders.
We first introduce definitions before presenting the strategy. We say that Gl is cleared in the case where no intruder is in Gl . Gl is contaminated in the case where at least one intruder is in Gl . Let us denote the minimum number of robots to capture all visible intruders in Gl as sl (Gl ).
We introduce a driving robot, whose role is to chase an intruder in Gl . We further introduce a guard, whose role is to guard a vertex in Gl . We say that a vertex v is guarded in the case where at least w(v) guards are deployed to guard v. In the case where v is guarded, no intruder can pass through v without being captured.
We define H as
Here, MAX(α, β) indicates the larger one between α and β. H in equation (1) indicates the maximum weight in the graph. H driving robots move as one group and move along Gl to capture intruders. H is a lower bound for sl (Gl ), as presented in the next lemma.
Lemma 1
Proof
Recall that
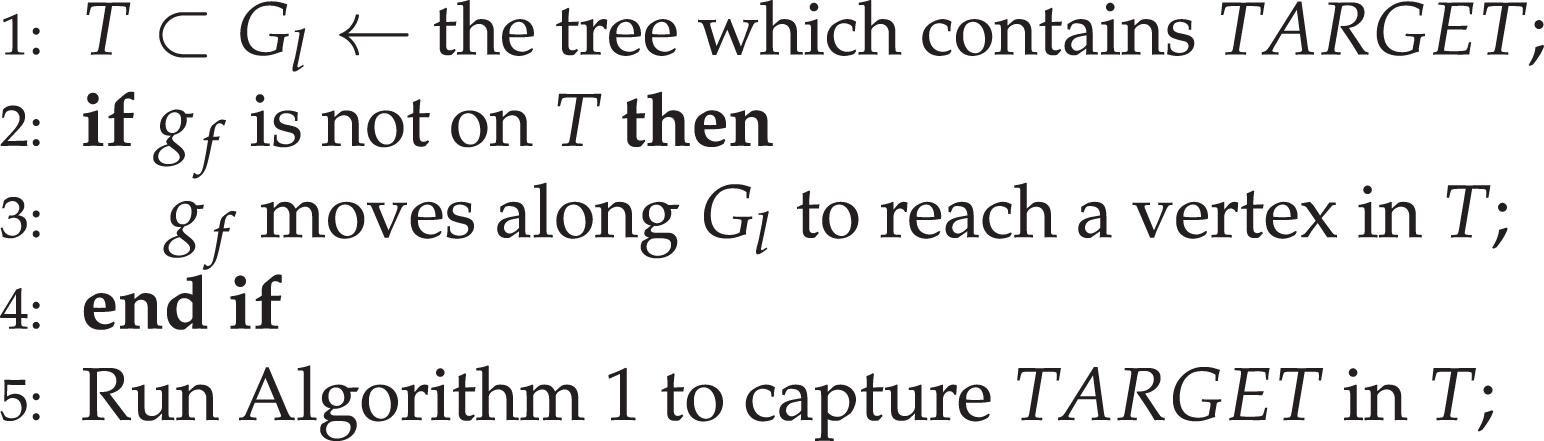
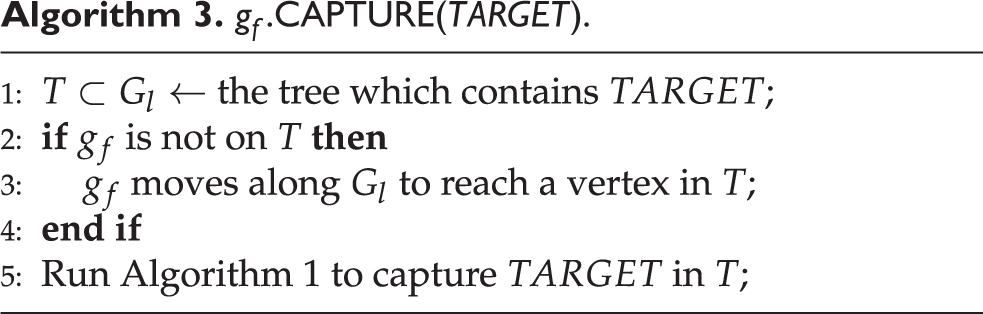
We first introduce a search algorithm to capture one intruder in the case where Gl is a tree graph, say T. Algorithm 1 provides the searching strategy using H driving robots. To capture the intruder, H driving robots move as one group. This coordinated strategy will be extended to a strategy of capturing multiple intruders contained in a general graph, later in Algorithm 2.
Clear strategy using one group of H driving robots (Gl is a tree T)

Capturing all intruders.

Considering a tree graph, we have the following theorem.
Theorem 1
Consider the case where Gl is a tree graph sl (Gl ) = H.
Proof
Lemma 1 proved that sl (Gl ) ≥ H. We also prove that sl (Gl ) ≤ H. Algorithm 3 provides a searching strategy using H driving robots. Since this algorithm works to capture every intruder in a tree graph, sl (Gl ) ≤ H.
Suppose that H = 6 and that one edge, say e 1, requires w(e 1) = 2 robots to sweep the edge. Recall that the driving robots form a dense formation so that an intruder cannot move through the formation without being caught. Suppose that the driving robots sweep a passage where only two robots are needed to clear the passage. In this case, the driving robots form a denser formation (decrease the relative distance between each other) to sweep the passage. Formation change of the driving robots is not within the scope of this article. The control laws in the study by Alonso-Mora et al. 42 can be used for formation control considering obstacles. See Figure 4 for an illustration of the case where six robots sweep a passage which requires only two robots for sweeping the passage. In Figure 4, a circle illustrates the maximum weapon range of a robot.
A circle illustrates the maximum weapon range of a robot. The center of a circle represents the position of the robot associated to the circle. Six robots sweep a passage which requires only two robots for sweeping the passage.
Next, let us consider Gl which is not a tree. Recall that we consider a worst-case intruder. Hence, an intruder can move at unbounded speed to avoid both the driving robots and guards. To block escape of an intruder, we guard vertices in Gl . We say that a cycle C is blocked if any vertex in V(C) is guarded.
We define Ng as the minimum number of guards to block all cycles in Gl . Computational method to derive Ng corresponds to the WFVP in the study by Carrabs et al. 36 The WFVP for a general graph is known to be NP-hard in computer science. 36 In the case where Gl is a general graph, approximation algorithms returning near-optimal solutions exist. 43
Considering some special graphs, Ng can be derived in polynomial time or in linear time. In the case where Gl is a diamond graph in the study by Carrabs et al., 36 we can derive Ng in linear time. 36 Also, we can derive Ng in polynomial time in the case where Gl is an interval graph, 37 co-comparability graph, 38 permutation graph, 39 or convex bipartite graph. 38
Suppose Ng guards are deployed to block all cycles in Gl . H driving robots capture every intruder one by one using Algorithm 2. Algorithm 2 describes our searching strategy considering the case where there are many intruders. Let gf denote one group of H driving robots. Among all intruders that are detected using sensor networks, gf selects one as TARGET. Then, gf chases TARGET until TARGET is captured. While gf chases TARGET, gf keeps sweeping edges to avoid the escape of. Since all cycles in Gl are blocked, any targeted intruder cannot escape from gf . In this way, we can decrease the number of intruders until all intruders are captured.
There may be a case where an intruder, say
Since we need H driving robots and Ng guards to capture all intruders on Gl , sl (Gl ) ≤ H+ Ng follows. Moreover, we have sl (Gl ) ≥ H using Lemma 1. Therefore, we have the following theorem.
Theorem 2
In the case where
The switching search algorithms
In Algorithm 2, only driving robots move, while other robots guard their designated locations. Considering the efficiency of capturing intruders, it is desirable to make a guard move if necessary. We present switching algorithms to make a guard move to capture intruders if the movement of the guard does not allow an intruder to escape.
Before presenting our switching algorithms (see Algorithm 4), we need to introduce a new graph GT representing the available set of points for an intruder.
Time-efficient capturing strategy using

Suppose we deploy Ng guards to block all cycles in Gl . Since all cycles in Gl are blocked, an intruder cannot escape from the driving robots.
By splitting guarded vertices in Gl , we obtain GT . GT is composed of several disjoint tree graphs, since all cycles in Gl are blocked. In other words, GT = {T 1,…,TL } where Ti denotes the ith tree graph. A robot is adjacent to a tree graph Ti if the robot guards a vertex of Ti .
In the case where Ng is zero, there is no cycle to block in Gl . This implies that Gl is a tree. Thus, GT = {T 1}, where T 1 is identical to Gl .
Figure 5 illustrates Gl with corresponding GT . In this figure, v 1 and v 2 in Gl are guarded to block all cycles in Gl . By splitting v 1 and v 2 in Gl , we obtain GT . GT is composed of two disjoint tree graphs T 1 and T 2, since all cycles in Gl are blocked. Ng = w(v 1) + w(v 2) = 3, since w(v 1) = 1 and w(v 2) = 2.

An illustration of Gl with corresponding GT . Ng = w(v 1) + w(v 2) = 3, since w(v 1) = 1 and w(v 2) = 2.
Considering the Gl in Figure 5, we need to split at least two vertices in Gl to remove all cycles in Gl . Figure 6 illustrates Gl with corresponding GT . In Figure 6, v 1 and v 3 in Gl are guarded to block all cycles in Gl . By splitting v 1 and v 3 in Gl , we obtain two disjoint tree graphs GT . Ng = w(v 1) + w(v 3) = 4, since w(v 1) = 1 and w(v 3) = 3. Ng in Figure 6 is larger than Ng in Figure 5. Thus, splitting two vertices as in Figure 5 is more desirable than splitting two vertices as in Figure 6.

In this figure, v 1 and v 3 in Gl are guarded to block all cycles in Gl . Ng = w(v 1) + w(v 3) = 4, since w(v 1) = 1 and w(v 3) = 3.
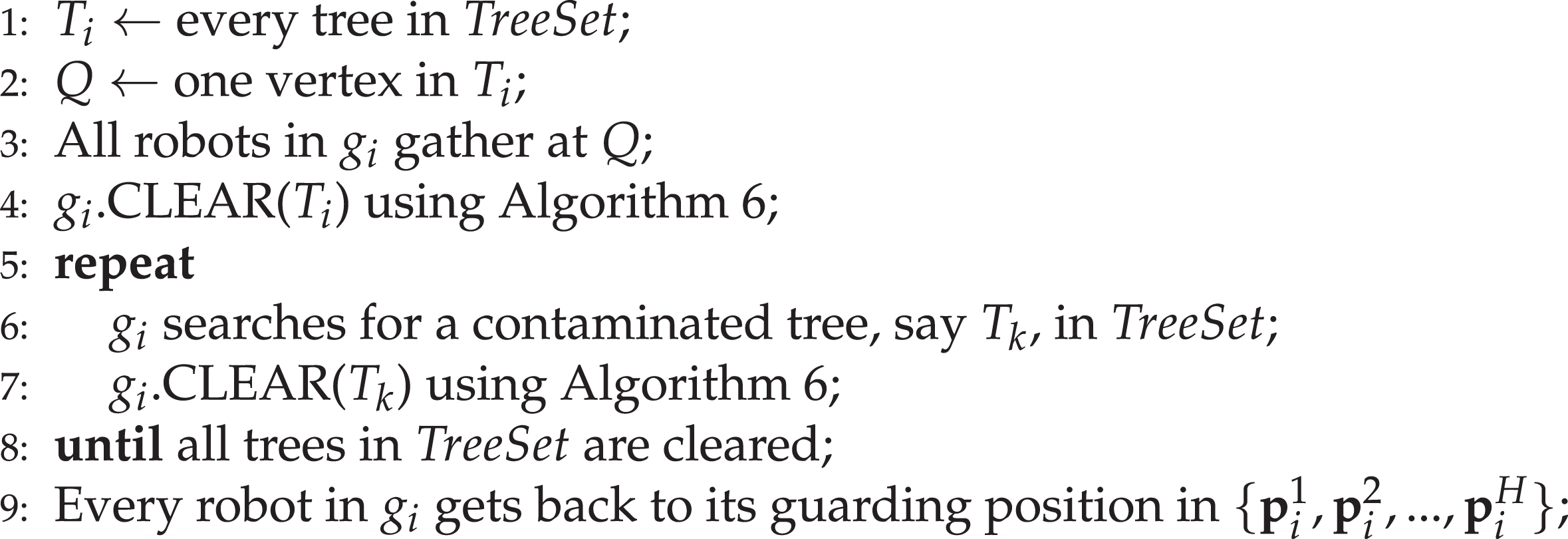
The idea of our switching algorithms (see Algorithm 4) is as follows. As time goes on, the number of cleared trees increases. The guards which are not adjacent to any contaminated tree do not have to guard their designated locations anymore. In this case, we can let guards maneuver to improve the time efficiency of graph clear operation considerably.
Algorithm 4 requires H + Ng robots to capture all intruders. Note that the number of robots required to capture intruders using Algorithm 4 is equal to that required using Algorithm 2. Algorithm 4 was developed to improve the time efficiency of capturing intruders compared to Algorithm 2. Algorithm 4 lets a guarding robot move to capture intruders if the movement of the guard does not allow an intruder to escape.
Algorithm 4 is time efficient, since every tree graph in TreeSet can be cleared simultaneously using Algorithm 5. See line 28 in Algorithm 4. For example, assume that there are n tree graphs in TreeSet. Correspondingly, n groups of robots are selected to clear n tree graphs, respectively. n groups can run Algorithm 5 simultaneously to clear n tree graphs. In this way, time efficiency of Algorithm 4 increases significantly compared to the case where only H driving robots maneuver.
Simultaneous clearing of every tree in

Algorithm 4 is designed not to make a robot idle. Suppose that Ti is in TreeSet and that gi is selected to clear Ti . Suppose that there are only a few intruders in Ti and that Ti is cleared before all trees in TreeSet are cleared. In this case, gi must not be idle. Therefore, once gi finishes clearing Ti , gi begins to clear another contaminated tree in TreeSet. This process is presented in lines 5–8 of Algorithm 5.
Lemma 2
Consider the intruder capturing strategy using Algorithm 4. Suppose we choose n groups of robots (g
1,g
2,…,gn
) to clear every tree graph (T
1,T
2,…,Tn
) in TreeSet. The role of gi
, ith group of robots, is to capture intruders in Ti
where i ≤ n. Using Algorithm 5, gi
,
Proof
Suppose we choose n groups of robots (g
1,g
2,…,gn
) to clear every tree graph (T
1,T
2,…,Tn
) in TreeSet. The role of gi
, ith group of robots, is to capture intruders in Ti
where i ≤ n. The location of each robot in gi
,

Lemma 3
Consider the intruder capturing strategy using Algorithm 4. Once a tree graph is cleared, no intruder can sneak into the tree graph again.
Proof
Suppose we choose one group of robots, say gu
, to capture all intruders in one contaminated tree graph, say
Thus, once a tree graph is cleared, no intruder can sneak into the tree graph again.
Theorem 3
Using Algorithm 4, all intruders are captured in finite time.
Proof
Suppose we choose one group of robots, say gi
, to capture all intruders in one contaminated tree graph, say
Suppose that there is at least one contaminated tree as i in Algorithm 4 is set to 1. We prove that as i in Algorithm 4 changes from 1 to L + 1, TreeSet contains at least one contaminated tree. This further indicates that the number of cleared trees increases, since every tree in TreeSet is cleared simultaneously using Algorithm 5.
We prove that as i in Algorithm 4 increases from 1 to L + 1, TreeSet contains at least one contaminated tree. Suppose that i in Algorithm 4 has been increasing from 1 to l. Suppose that Tl
is contaminated and that TreeSet has been empty until i reaches l. Whenever TreeSet is empty, S contains Sf
, additional H driving robots which are not adjacent to any tree graph in GT
. See line 7 in Algorithm 4. Driving robots in Sf
are not adjacent to any tree graph in
Recall that we have
Theorem 4
The number of robots required to clear Gl is between H and H + Ng .
MATLAB simulations
We provide MATLAB simulations to verify the effectiveness of our approach. This article considers a simplified environment where robots and worst-case intruders move along a weighted graph, which is a topological map of the environment. As a topological map of the environment, this article utilizes the Voronoi diagram in the study by Kim et al. 44 In robotics, Voronoi diagrams have been widely utilized as topological maps. 44 –46 In the Voronoi diagram, a Voronoi edge is the set of points which are equidistant from the two closest obstacles. A Voronoi vertex is a point where more than two Voronoi edges meet. See Kim et al. 44 for the definition of the Voronoi diagram.
Simple obstacle environments
We first consider simple obstacle environments. The obstacle boundaries are shown in thick red curves in Figure 7. We build the Voronoi edge (green circles in Figure 7) using the exploration algorithms in the study by Kim et al. 44

We build the Voronoi edge (green circles) using the exploration algorithms in the study by Kim et al. 44
Figure 8 shows the weight of each Voronoi edge. Each Voronoi edge has its associated number as depicted in Figure 7. We first present several concepts before presenting how we set the weight of every edge e in Figure 8. Let O indicate an obstacle boundary.

The weight of each Voronoi edge, considering the scenario in Figure 7.
In Figure 8, the weight of an edge e is set as follows.

Here,
Considering the Voronoi diagram in Figures 7 and 8, we have H = 5, and Ng = 2. In Figure 7, a guarded vertex is marked with blue color. We can let H = 5 robots move to capture a visible intruder one by one, while two robots guard two vertices with blue color. In total, we use Ng + H = 7 robots to capture every intruder. Since H = 5 robots cannot clear the Voronoi diagram due to a cycle in the graph, we need at least 6 robots to clear the graph.
We next verify the effectiveness of our intruder capturing algorithms. We generate one worst-case intruder in the Voronoi diagram Gl in Figure 7. Since all cycles are blocked, the intruder is constrained to stay in a tree, say Ti . gf moves along Ti and visit vertices sequentially to capture the intruder. On the other hand, the intruder moves along Ti with unbounded speed to escape from gf . Whenever gf visits a Voronoi vertex, the intruder moves along Ti with unbounded speed to maximize its distance from gf . Since Ti is a tree, the intruder must be captured in finite time. The total traversal distance of gf until capturing this intruder is 38 distance units.
Complicated obstacle environments
We next consider complicated obstacle environments. The obstacle boundaries are shown in thick red curves in Figure 9. We build the Voronoi edge (green circles in Figure 9) using BE algorithms in the study by Kim et al. 44

We consider complicated obstacle environments. We build the Voronoi edge (green circles) using BE algorithms in the study by Kim et al. 44
Figure 10 shows the weight of each Voronoi edge. Each Voronoi edge has its associated number as depicted in Figure 9. The weight of a Voronoi edge is set using equation (2). Also, we set the weight of a Voronoi vertex as one.
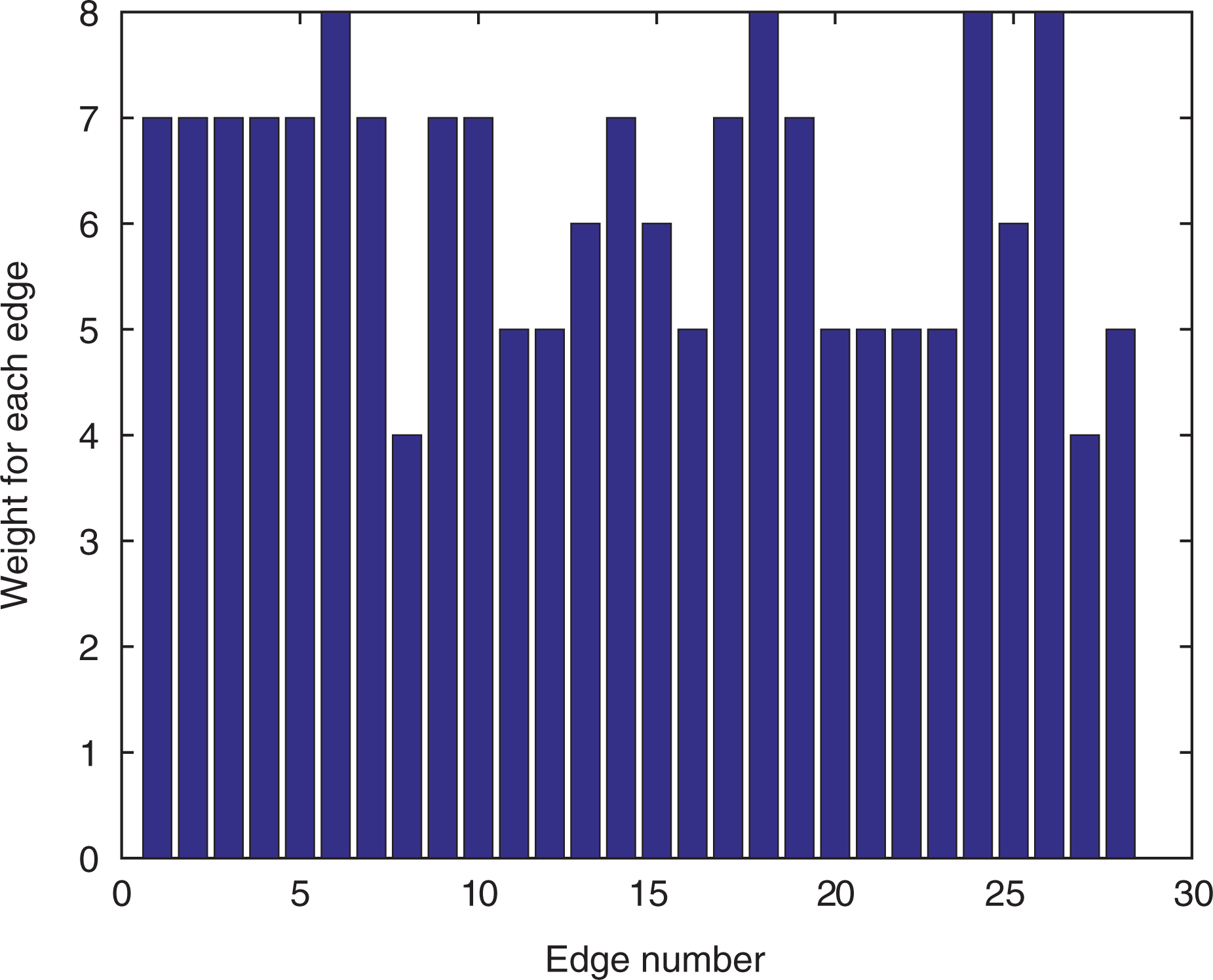
The weight of each Voronoi edge, considering the scenario in Figure 9.
Considering the Voronoi diagram in Figures 9 and 10, we have H = 8, and Ng = 3. In Figure 9, a guarded vertex is marked with blue color. We can let H = 8 robots move to capture a visible intruder one by one, while three robots guard three vertices with blue color.
In total, we use Ng + H = 11 robots to capture every intruder. Since H = 8 robots cannot clear the Voronoi diagram due to a cycle in the graph, we need at least 9 robots to clear the graph.
We next verify the effectiveness of our intruder capturing algorithms. We generate one worst-case intruder in the Voronoi diagram Gl in Figure 9. Since all cycles are blocked, the intruder is constrained to stay in a tree, say Ti . gf moves along Ti and visit vertices sequentially to capture the intruder. Whenever gf visits a Voronoi vertex, the intruder moves along Ti with unbounded speed to maximize its distance from gf . The total traversal distance of gf until capturing this intruder is 73 distance units.
Conclusions
Consider a team of robots deployed to capture worst-case intruders in an environment. We simplify the scenario such that robots and intruders move along a topological map of the environment, represented by a weighted graph Gl . We introduce weighted graph searching algorithms to capture every visible intruder. We then derive the minimum number of robots required to clear a weighted tree graph. Considering a general weighted graph, we derive bounds for the number of robots required. Finally, we present switching algorithms to improve the time efficiency of capturing intruders while not increasing the number of robots.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by Cooperative RnD between Industry, Academy, and Research Institute funded Korea Ministry of SMEs and Startups in 2019 [Grant No. S2658135].