Abstract
This article introduces multi-robot strategies making multiple robots explore an unknown environment in a cooperative manner. Our exploration strategies do not require global localization of a robot or a node. Multiple robots build a Voronoi diagram as a topological map of the environment, while deploying sensor nodes which can sense and communicate. As the sensor network built by one robot meets the network built by another robot, both robots can exchange data with each other. The robots then use the merged sensor network to protect the environment. We introduce an intruder capture algorithm assuming that a robot is able to access any intruder’s location utilizing the sensor network. This algorithm is robust to time delay in information sharing utilizing the sensor network. Utilizing the algorithm, we derive upper bounds on the number of robots needed to capture every intruder in the environment. This article proves that the minimum number of robots needed can be computed by finding proper edge covers of the dual graph of the Voronoi diagram.
Keywords
Introduction
Operating multiple robots in a complex and dangerous environment needs the support from a sensor network that can detect environmental changes and also relay data among the robots. Sensor network becomes feasible due to the development of small sensor nodes, such as the Berkeley Motes. 1 Research advances in sensor networking 2,3 showed that small sensor nodes can be positioned to construct a sensor network for supporting rescue workers.
However, building a sensor network in dangerous environments is not easy. As an autonomous method for building a sensor network, mobile sensor nodes can be used. 4 But, considering the time spent and power loss due to the maneuver of each node, it is desirable to minimize the maneuver of a sensor node.
As a method to construct a sensor network efficiently, this article presents the multi-robot networking and exploration strategy called the Simultaneous Cooperative Networking and exploration (SCN) strategies. 5 In SCN strategies, each robot uses the boundary expansion (BE) algorithms in our previous work 6 to construct a Voronoi diagram of the environment while deploying sensor nodes (Voronoi diagrams were widely used as a topological map. 7 –11 Also, a Voronoi diagram was used in coverage problems of sensor networks. 12 ). The robots start exploration at arbitrary locations, thus they may not be able to exchange data with each other initially. Deployed sensor nodes form a network allowing the robots to exchange data with other robots. Moreover, sensor deployment enables time-efficient networking while exploration. Our exploration strategies do not need global localization of a robot or a node (Localization of a robot or a sensor node is a critical problem to solve in both robotics and sensor networks. 13 –21 ). As a result of SCN strategies, a sensor network and a topological map are created simultaneously.
The resulting sensor network and the topological map, represented by Voronoi diagrams, are utilized by the robots to coordinate their motions to secure the environment. Because of obstacles, both intruders and robots are restricted to traverse a passage between two obstacles. This article considers the case in which the weapons on robots are powerful sufficient to cover the width of a passage between obstacles. This case, we can consider a simplified scenario where searchers and intruders traverse Voronoi edges. We present an intruder capturing game in the Voronoi diagram, assuming that a robot is able to access any intruder’s location utilizing the sensor network.
Previous research on pursuit-evasion games on graphs, as presented in the study by Parsons 22 and Kolling and Carpin, 23 mentioned that successful capturing strategies require guarding a passage to block escape of an intruder. In this article, we obtain bounds on the number of guards needed to capture every intruder on a Voronoi diagram assisted by the sensor network. The problem tackled in this article is similar to that in the study by Seymour and Thomas 24 and Richerby and Thilikos, 25 since an intruder is visible to a robot. Here, a robot uses the sensor network to detect an intruder.
While general graphs were considered in the works of Seymour and Thomas 24 and Richerby and Thilikos, 25 we focus on capturing intruders in a Voronoi diagram. We introduce an intruder capture algorithm assuming that a robot is able to access any intruder’s location utilizing the sensor network. This algorithm is robust to time delay in information sharing utilizing the sensor network. Based on the algorithm, we prove that the minimum number of searchers needed can be computed by finding proper edge covers of the dual graph of the Voronoi diagram. As far as we know, our article is novel in deriving the relationship between the number of robots needed and a Voronoi diagram.
The article is organized as follows: Second section reviews works related to our article. Third section reviews preliminaries and background information. Fourth section presents how to build the sensor network in a cooperative manner. Fifth section provides the intruder capture algorithm based on sensor networks. Next, sixth section presents MATLAB simulation results. Finally, seventh section presents conclusions.
Related works
Our article is closely related to multi-robot networking strategies introduced in the literature. 5,26 –28 Multi-robot networking algorithms in the literature 5,26 –28 require that a robot stores the adjacency matrix associated to all vertices and searches for a closest unexplored vertex utilizing the matrix. Searching for a closest unexplored vertex can be computationally burdensome especially in the case where there are many vertices.
In SCN algorithms, each robot only stores the circularly linked list structure, called the enclosing boundary (EB; “BE algorithm” section presents the rigorous definition of the EB), representing the boundary of the explored area thus far. Since a robot does not have to store the adjacency matrix associated to all vertices, our algorithms require less memory compared to other multi-robot networking algorithms in the literature. 5,26,27 Also, a robot does not have to search for a closest unexplored vertex. 5,26,27 As far as we know, our article is novel in not searching for a closest unexplored vertex, in the literature on multi-robot exploration.
Complexity analysis section analyzes the computational complexity of both our algorithms and other algorithms searching for a closest unexplored vertex. We show that as the network size increases, the complexity of our algorithms decreases compared to other algorithms searching for a closest unexplored vertex.
The EB was also used in our previous papers. 5,6 Kim et al. 6 considered one robot exploration, while Kim et al. 5 considered multi-robot exploration and networking. Note that both SCN algorithm in this article and the algorithm in Kim et al. 6 do not require that a robot stores the adjacency matrix associated to all vertices. Our article extends Kim et al.’s 6 work to multi-robot exploration and networking by letting multiple robots construct the sensor network in a cooperative manner. The multi-robot networking strategy in Kim et al. 5 requires that a robot stores the adjacency matrix associated to all vertices. Kim et al. 5 require this full adjacency matrix, since a robot has to search for a closest unexplored vertex in the case where a blocking of EB occurs. Utilizing SCN algorithm in this article, this blocking does not happen, since we merge two EBs if they intersect while satisfying certain conditions. Under SCN algorithm, a robot does not have to search for a closest unexplored vertex, as in the study by Kim et al. 5
Suppose that the sensor network is completely built utilizing multiple robots. We further present an intruder capture algorithm in the Voronoi diagram of the environment, assuming that a robot is able to access any intruder’s location utilizing the sensor network.
The graph searching problem was originated from Parsons’ study. 22 There are many papers on graph search problems. 22,24 –26,29 –40 Several authors tackled clearing a weighted graph. 23,30,33,41,42 In a weighted graph, the weight of an edge or a vertex is a cost describing the clearing requirement of the edge or the vertex. Among many papers, our article is closely related to the helicopter cops game in the study by Seymour and Thomas 24 and Richerby and Thilikos. 25 In this game, 24,25 a cop is able to access robbers’ locations as if the cop utilizes a helicopter. Thus, an intruder is visible by a cop. Furthermore, a cop can jump from one vertex to another. We say that a cop captures a robber if the cop visits the node on which the robber exists.
The problem formulated in this article is similar to that in the study by Seymour and Thomas 24 and Richerby and Thilikos, 25 since this article assumes that an intruder is visible to a searcher utilizing the sensor network. In this article, a robot traverses graph edges continuously, which is distinct from the study by Seymour and Thomas 24 and Richerby and Thilikos. 25
While general graphs were considered in the works of Seymour and Thomas 24 and Richerby and Thilikos, 25 this article is focused on capturing intruders on a Voronoi diagram. A Voronoi diagram has been widely used to represent a plane structure such as a floor in buildings. 41 A Voronoi diagram has also been used as a topological map representing a workspace with many obstacles. 6,8,41 We introduce an intruder capture algorithm assuming that a robot is able to access any intruder’s location utilizing the sensor network. This algorithm is robust to time delay in information sharing utilizing the sensor network. Utilizing the algorithm, we prove that the minimum number of robots needed can be computed by finding proper edge covers of the dual graph of the Voronoi diagram. As far as we know, our article is novel in deriving the relationship between the number of robots needed and a Voronoi diagram.
Preliminaries and background
In this section, we discuss background information which are used to present our contributions.
Graphs
We review graph theory
43
used in this article. A graph G is a set
A plane graph is a graph embedded in the plane without crossing edges. A face of a plane graph is the maximal region of the plane that is surrounded by a cycle of edges but contains no vertex which belongs to any edge of the embedded graph. For example, a two-dimesional Voronoi diagram is a plane graph in which each Voronoi cell is a face. G* is called the dual graph of a plane graph G in the case where G* is constructed as follows: each face of G is represented by a node in G*, and each edge shared by two adjacent faces of G is represented by an edge in G*. G* is also a plane graph. For any plane graph G, its boundary ∂G is a set of edges and nodes that separate the region enclosed by the graph with the rest of the plane. A cycle in a plane graph separates the plane into two regions, the region inside the cycle and the region outside the cycle. If a plane graph contains a cycle, then its boundary must also contain a cycle. If G contains no cycles, then all edges and nodes are on the boundary, for example, ∂G = G.
A matching M in G is defined as a set of pairwise non-adjacent edges. In other words, no two edges are adjacent to a common vertex. A maximum matching is a matching having the largest possible number of edges. A maximum matching can be calculated in polynomial time utilizing the Edmonds’ Blossom algorithm. 44,45
An edge cover of a plane graph G, represented by
A perfect matching in G is a minimum edge cover in which no vertex is shared by any pair of edges. If a perfect matching exists, then its cardinality is
The environment and its Voronoi diagram
Consider an environment
Obeying the conventions in the literature on Voronoi diagrams, 8,10,46 –49 a Voronoi cell Vi for an obstacle Oi is the set of points which are closer to Oi than to Oj where j ≠ i. ∂Vi is the boundary of the Voronoi cell Vi. This definition on Voronoi cells was also used in the study by Kim et al. 5,6
The following assumptions, which were also used in the study by Kim et al., 5,6 are used.
Assumption 1
∂Vi of every Voronoi cell Vi is closed and simple.
Assumption 2
The Voronoi diagram G is a plane graph and denotes the union of all cell boundaries. A Voronoi edge Eij is an edge shared by two Voronoi cells Vi and Vj. A Voronoi vertex is a node where more than two Voronoi edges meet.
BE algorithms
Kim et al. 6 introduced the BE algorithms to build the Voronoi diagram of the environment utilizing one robot.
We reviewed BE algorithms in Kim et al. 6 briefly. We need to introduce several definitions in the study by Kim et al. 6 An intersection P is a point satisfying the following conditions:
There exists a circle, whose center is P, intersecting obstacle boundary at more than two points. These points are denoted as the closest points at the intersection. In the case where the robot is located at an intersection, the closest points are the points which have local minimal distances to the robot.
The interior of the circle does not contain a point of an obstacle, that is, the circle is tangential to an obstacle.
An intersection circle is a circle satisfying the above conditions (see Figure 1). The line segments connecting the intersection and the closest points divide the intersection circle into sectors. Each sector is the “pie-shaped area” inside the intersection circle (see Figure 1).

The robot is at P. The closest points divide the intersection circle into sectors. Sector i is adjacent to the sector i − 1 in the counter-clockwise direction.
Consider the case in which the robot traverses Eij until it meets P, as depicted in Figure 1. Then, the robot encounters two closest points on ∂Oi and ∂Oj, respectively, since
In the case where two end points of a sector exist on the identical obstacle boundary, then the sector is a blocked sector (see Figure 1). An open sector (sectors 1 and 3 in Figure 1) is a sector that is neither sector 0 nor a blocked sector. If an intersection has an open sector which has not been visited by the robot, then the intersection is set as unexplored. Otherwise, the intersection is set as explored.
In BE algorithms, the robot circles around an obstacle, say Oj, to its right while traversing ∂Vj. To enable this circling, the robot applies the sector selection rule as follows:
In the case where the robot meets an intersection that is not on the EB, then the robot searches for an open sector in the counter-clockwise direction starting from sector 0. In the case where an open sector is found, the robot moves through the found open sector.
For example, consider the case in which the robot reaches P as depicted in Figure 1. Then, under the sector selection rule, the robot chooses sector 1 to circle around Oj to its right.
Consider the case in which the robot traverses Voronoi edges utilizing the tracking controller in Kim et al. 6 Utilizing the above sector selection rule, the robot can circle around an obstacle, say Oj, to its right while traversing ∂Vj. We denote this cycle as the initial enclosing boundary B0.
Bk denotes EB that is updated with k + 1 steps. Since one obstacle is added at each step, Bk encloses k + 1 obstacles.
To update the EB, the robot traverses EB until it visits an unexplored vertex, say head. Then, the robot at the head traverses an unexplored edge out of EB, followed by circling around an obstacle to its right. Here, the sector selection rule is used to circle around an obstacle to its right. Since each Voronoi cell boundary is a cycle, the robot meets EB again. Let tail denote the point where the robot intersects EB again. Let candidate segment (CS) denote the robot’s path out of EB such that two end nodes of the path are on EB. See Figure 2 for an illustration.

The case in which the EB expands. EB: enclosing boundary.
We next present the boundary updating rule, which decides when we update EB utilizing the CS. The rule is given as follows:
Consider the case in which no unexplored intersection exists strictly between head and tail along the segment of EB in the clockwise direction. In this case, the segment of EB from head to tail is replaced by CS.
Consider the case in which the current EB is Bk. Figure 2 depicts the case in which no unexplored intersection exists strictly between head and tail along the segment of EB in the clockwise direction. This implies that the boundary updating rule is met. In this case, we update Bk to
During the process of updating EB, all unexplored vertices only exist on or outside EB. The algorithms end as EB encircles all obstacles except for OM. Thus, BE algorithms end in finite time resulting in a complete Voronoi diagram. Because of page limits, we do not present entire BE algorithms in this article. See Kim et al. 6 for a detailed explanation of BE algorithms.
Exploring while networking
BE algorithms can be performed by multiple robots at the same time to cooperatively explore an environment. Nv denotes the number of robots. Let us denote each robot as
Every robot vj carries sensor nodes that can detect a neighborhood around each node, while communicating with a robot or a node nearby. Here, note that a node deployed by a robot vj can communicate with a nearby node deployed by vq, where q ≠ j. Sensor nodes are positioned at Voronoi vertices or on long Voronoi edges to relay data between things (including both robots and nodes). These sensor nodes then form a sensor network that serves two purposes: (1) to relay data between things (including both robots and nodes) and (2) to provide a movement direction for a robot visiting the node.
Based on the results in the study by Souryal et al. 2 and Liu et al., 3 we assume that the sensor network operates once the nodes are deployed. We also assume that each sensor node has its unique ID. Thus, a robot visiting a node can localize itself based on the node’s ID.
Each sensor node stores data regarding whether the node has been explored or not. Each node at an intersection on EB stores the Voronoi edge direction along EB. By checking the Voronoi edge direction along EB, a robot can expand its EB, as presented in Algorithms 1 and 2.
Note that global localization of a node or a robot is not required in our algorithms.
Boundary merge
Two sensor nodes laid out by distinct robots are connected once the nodes are close to each other. When a robot vj encounters a sensor node which can communicate with a node laid out by another robot vq, vj can use the sensor network built by vq. Thus, vj can communicate with vq utilizing the network. Note that vj does not have to meet vq to exchange data with each other.
Each robot vj maintains Bj and expands Bj such that the area inside Bj does not overlap with that inside Bq, where q ≠ j. It may happen that Bj intersects with Bq, where q ≠ j. Consider the case in which Bj intersects Bq along Voronoi edges, say

We also merge two enclosing boundaries in the following situation: B0 constructed by one robot is identical to B0 constructed by another robot. This situation may happen in the case where an obstacle to the right of one robot vj is identical to an obstacle to the right of another robot vq. In this case, Bj and Bq are merged to get
In summary, we introduce the boundary merging rule as follows: Consider the case in which In the case where
Once vj and vq are merged, both vj and vq traverse
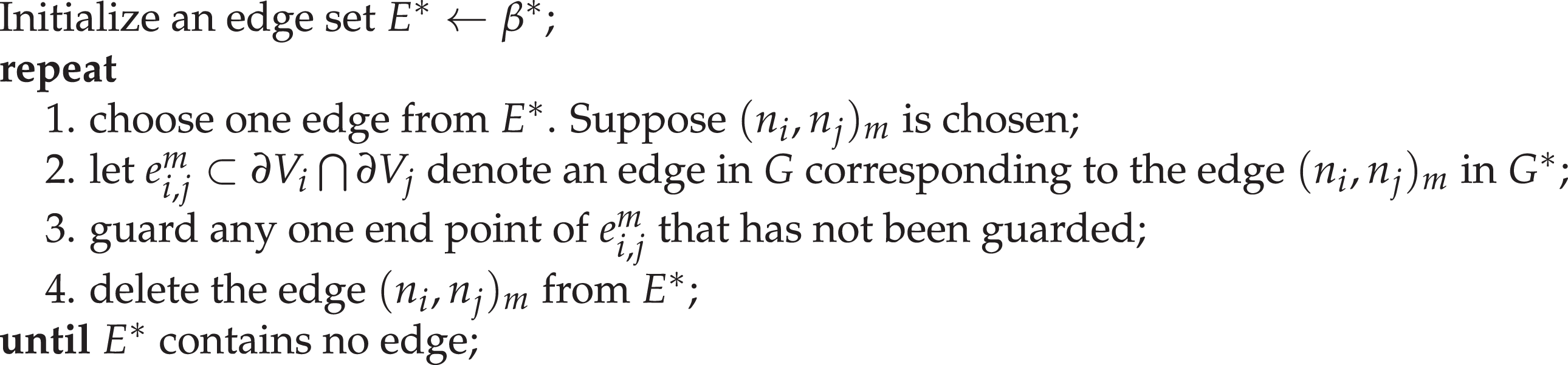
SCN algorithms are presented in Algorithms 1 and 2. Table 1 shows the data structures and operations used in these algorithms. Intersection, sector, sector selection rule, and disabled intersection set in these algorithms are presented in Kim et al. 6 Algorithms 2 and 3 do not present how to build the CS in detail. See Algorithm 2 in Kim et al. 6 for a detailed explanation of how to build the CS.
Construct the initial enclosing boundary for vi.

Expand the enclosing boundary for vi.
Data Structure.

Guarding at most
Complexity analysis
We analyze the complexity of SCN algorithms in the case where a robot vi is connected to N nodes utilizing multi-hop communication.
Other multi-robot networking algorithms in the literature
5,26,27
require that vi stores the adjacency matrix associated to all vertices and searches for a closest unexplored vertex utilizing the matrix. Searching for a closest unexplored vertex can be costly especially in the case where there are many vertices. Dijkstra’s algorithm is commonly used for this search. Since vi is connected to N vertices, the complexity of this Dijkstra’s algorithm is
In SCN algorithms, a robot vi does not store the adjacency matrix associated to all vertices. vi only stores the data on vertices along Bi and updates Bi if necessary. Thus, our algorithms require less memory compared to other multi-robot networking algorithms in the literature. 5,26,27
SCN algorithms use two rules for exploration and networking: boundary updating rule and boundary merging rule. These two rules search for an unexplored vertex along EB, thus can be implemented utilizing the data of vertices on EB, whose structure is a circularly linked list. vi does not require the data of vertices strictly inside EB.
Since vi is connected to N vertices, there are at most N vertices inside EB. Considering a rectangular boundary, the number of vertices along EB can be approximated as
Performance analysis
We estimate the exploration time utilizing our algorithms. Consider unit speed robots exploring W. T denotes the maximum time required for a robot to circle around one Voronoi cell.
Lemma 1 considers the case in which we use a single robot for exploration. The proof of Lemma 1 is similar to that of Theorem 3 in the study by Kim et al. 6 Thus, we omit the proof here.
Lemma 1
Consider a robot that has constructed an enclosing boundary enclosing M obstacles. The time spent is bounded by
Next, we consider the case in which two robots vi and vj are deployed. We prove the following theorem.
Theorem 1
Consider the case in which two robots vi and vj are deployed in W with M obstacles. Suppose that Bi expands with k1 steps and that Bj expands with k2 steps before they are merged. Let
Proof
Suppose that Bi expands with k1 steps and that Bj expands with k2 steps before they are merged. Once Bi expands with k1 steps, it encloses
Since
Next, we derive the time spent to generate
Utilizing Theorem 2 in Kim et al.,
6
at least one Voronoi cell, which exists outside

in which

There exist k + 1 obstacles enclosed by Bk, and M − 1 obstacles enclosed by

Therefore, as we replace k in equation (2) by M − 2, we can derive the bound on time required to construct Voronoi diagrams as

We proved that the expected building time increases in the order of M2.
□
Securing the environment
As a result of SCN algorithms, both the sensor network and the Voronoi diagram are built. The robots can then utilize the constructed sensor network to access any intruder’s location in real time. Because of obstacles, both intruders and robots are restricted to traverse a passage between obstacles. This article considers the case in which the weapons on robots are powerful enough to cover the width of a passage between obstacles. In this case, we can consider a simplified scenario in which both robots and intruders traverse Voronoi edges.
Let G denote the Voronoi diagram where both robots and intruders exist. Every vertex in G is associated to a sensor node deployed in the environment. An edge in G is cleared if the edge contains no intruder. Also, an edge in G is contaminated if the edge contains an intruder.
We introduce a guarding robot (guard for short), whose task is guarding a node in G. In addition, one robot, called the free robot, can move along any edge in G continuously. This article assumes that the free robot utilizes the sensor network as the basis to detect the location of an intruder in real time. The free robot can access the location of any intruder whenever the robot meets a node in G. This is feasible, since sensor nodes are positioned to cover the entire environment.
Utilizing the assumptions in the graph clear literature, 29,36 –39 this article assumes that an intruder can maneuver with unlimited speed to avoid both the free robot and guards. An intruder is captured in the case where it is on an edge or a vertex where a robot exists. s(G) is the minimum number of robots needed to capture all intruders on G. In this article, we derive an upper bound for s(G) by presenting an intruder capture algorithm.
Clearing a tree graph
Lemma 2 provides an intruder capture algorithm, so that the free robot captures one intruder in a tree graph.
Lemma 2
Consider the case where one intruder and one free robot traverses a tree graph T. This case, the intruder is captured by the robot utilizing the following algorithm:
Whenever the robot visits a node, the robot accesses the branch containing the intruder. Note that the sensor network enables this access. Thereafter, the robot traverses the edge contained in the branch until meeting another node. Iterate this maneuver until the intruder is captured.
Lemma 3
Utilizing the capture algorithm in Lemma 2, the intruder is captured regardless of time delay in information sharing utilizing the sensor network.
Proof
Consider the case where the free robot is located at a node n. An intruder is located on a branch, say b. Assume that a sensor node detects the intruder at time step t1. The node relays the detection event to the free robot at time step t2. n is the only node connecting b with T\b, utilizing the definition of a branch. Since the free robot is positioned at n, the intruder cannot get out of b from t1 to t2. Therefore, the intruder cannot get out of b as the free robot moves along the edge contained in b. Iterating this maneuver, the intruder must be captured. □
Clearing a Voronoi diagram
Next, we consider the general case where G is not a tree. An intruder with infinite speed can run away from the free robot utilizing a cycle in G. To block the escape, guards are positioned at nodes in G. Once a guard is deployed at a node, then an intruder cannot reach the node without being captured. Hence, as a guard is located at a node, then we say that the node is guarded. A cycle C is blocked in the case where any vertex in C is guarded.
Consider the case where Nmin vertices of G are guarded to block all cycles in G. Since all cycles in G are blocked, available set of points for an intruder is a tree. This case, the free robot can capture every intruder one by one utilizing the algorithm in Lemma 2. Since one free robot and Nmin guards can capture every intruder on G, we have Lemma 4.
Lemma 4
We next compute Nmin. Recall that G* is connected and that G* is the dual graph of G with the vertex presenting the unbounded face removed. If G* is one node, then G has a single cycle. Thus,
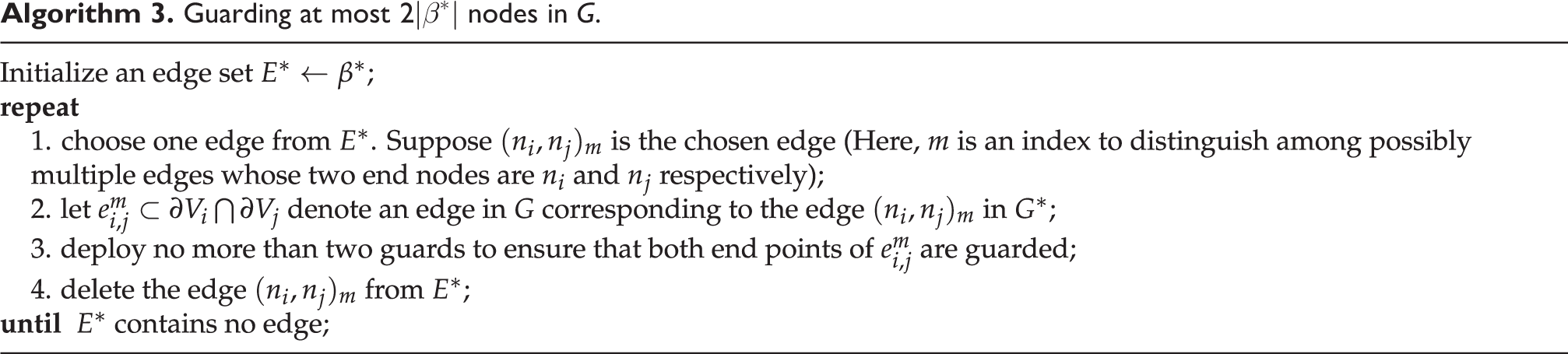
Before presenting the general case in which G* is a graph having multiple nodes, we introduce a new concept called the cycle-removing edge cover. Let
An example to illustrate a cycle-removing edge cover is given in Figure 4. In this figure, bold lines indicate edges which are not in an edge cover of G*. The left figure shows an edge cover of G* that is cycle-removing. In the right figure, see that a cycle composed of n1, n4, n6, and n2 is depicted with bold lines. Thus, the right figure presents an edge cover of G* that is not cycle-removing.
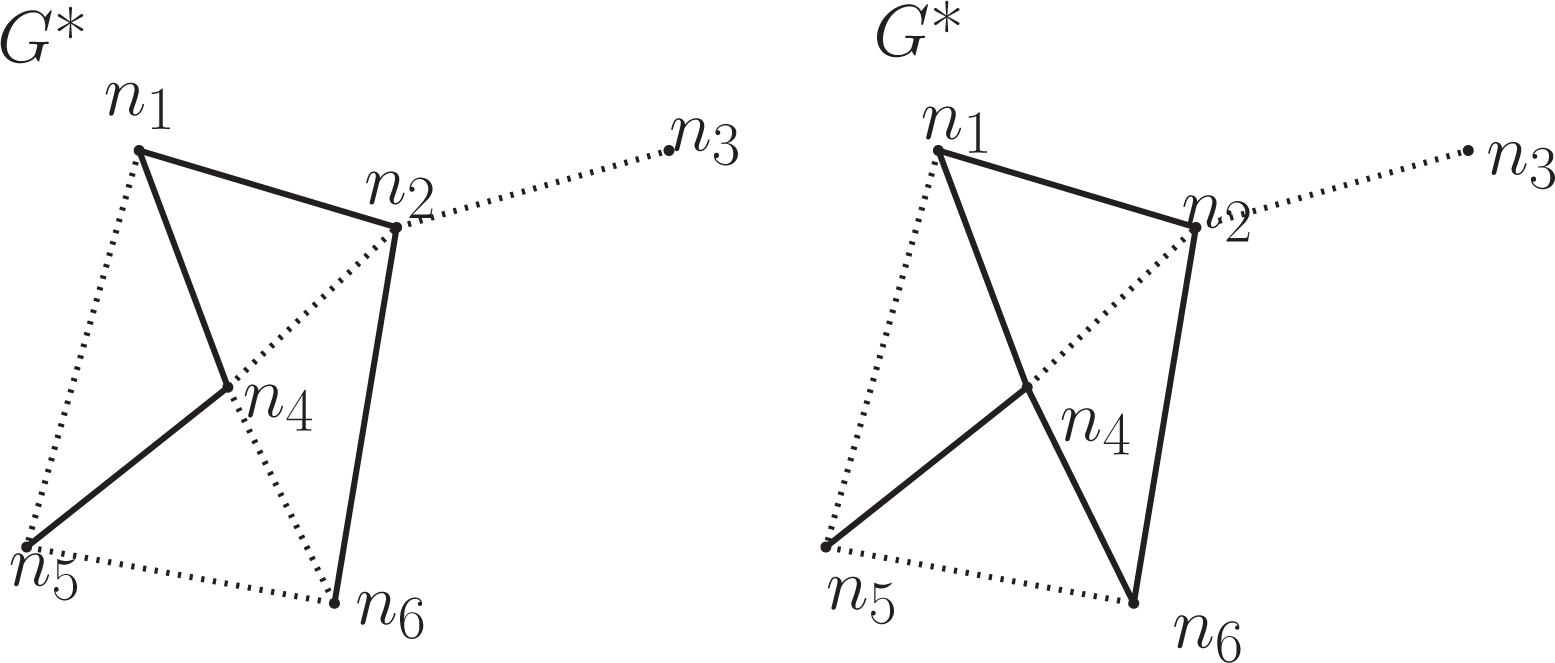
In the left figure, dotted lines present a cycle-removing edge cover of G*. In the right figure, dotted lines present an edge cover of G* that is not cycle-removing.
We prove the following statement:
Theorem 2
Consider a Voronoi diagram G such that G* is a connected graph with multiple nodes.
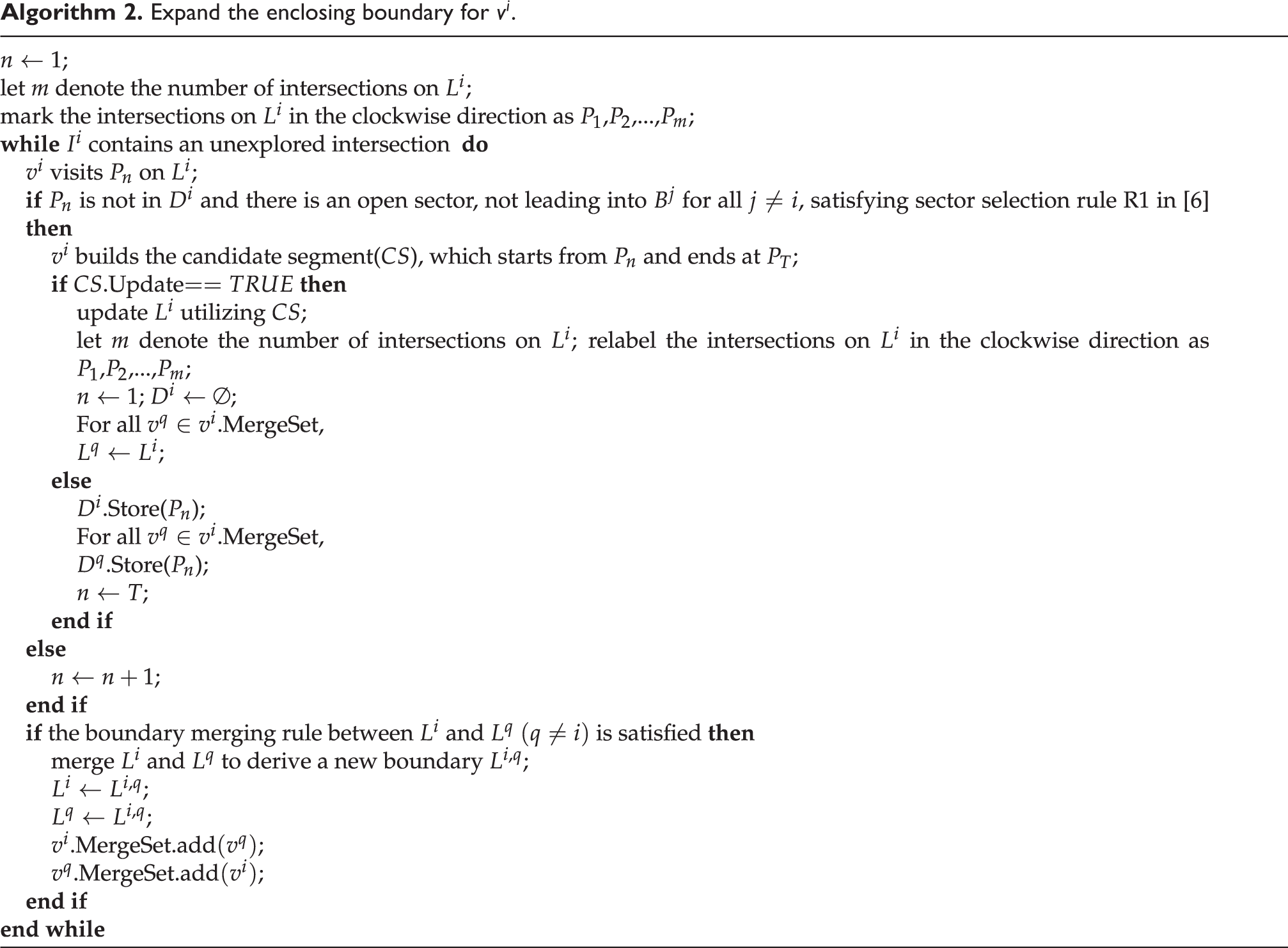
We present a proof of Theorem 2 by introducing Algorithm 3. Utilizing Algorithm 3, at most
Consider a cycle C of the Voronoi diagram G. C will enclose a region that is a connected subgraph of G. We denote this subgraph as
Lemma 5
If C encloses a single cell, then guards positioned by Algorithm 3 block C.
Proof
The dual graph
Lemma 6
If C encloses multiple cells, then guards positioned by Algorithm 3 block C.
Proof
Consider the dual graph G*. If an edge in β* connects a node that belongs to
On the other hand, suppose the edges in β* that cover the nodes of
We now show that there exists at least one edge in β* that connects two boundary nodes of
We next prove Theorem 2:
Proof
According to Lemmas 5 and 6, any cycle C in G will be blocked by Algorithm 3. Then, the minimum number of guards needed to block all cycles in G is not bigger than
A special case
We next consider the case in which G* is a tree and show that the number of guards needed can be significantly reduced. A typical environment in which G* is a tree graph is a corridor in a building. We have the following theorem.
Theorem 3
Consider the Voronoi diagram G whose dual graph G* is a tree.
Since there is no cycle in the dual graph G* because of its tree structure, the minimum cycle-removing edge cover β* coincides with the minimum edge cover of G*. This is desirable considering computational complexity, since the minimum edge cover of G* can be calculated in polynomial time. The proof is based on Algorithm 4. We will show that Algorithm 4 removes all cycles in G.
Guarding at most

Lemma 7
If C encloses a single cell, then guards positioned by Algorithm 4 block C.
The proof is similar to the proof for Lemma 5. One guard is enough to block the cycle C.
Lemma 8
Let C be a cycle in G enclosing at least two Voronoi cells V1 and V2. Suppose
Proof
Let n1 and n2 be the nodes of G* that correspond to V1 and V2, respectively. Because of the tree structure of G*, the edge connecting n1 and n2 is the only path between n1 and n2, since otherwise
Suppose one end of e1,2 is not on C. Denote this end point as E1. E1 must be inside the cycle C. According to the definition of a Voronoi vertex, there exist at least two Voronoi edges other than e1,2 that share E1 as an end point. If there are exactly two Voronoi edges other than e1,2, then the two edges belong to one Voronoi cell, say V3, that is adjacent to both V1 and V2. On the dual graph

The Voronoi vertex E1 is inside C, and e1,2 (the bold line) is the common edge shared by V1 and V2 that corresponds to the edge connecting n1 and n2 on the dual graph
Lemma 9
If C encloses multiple cells, then guards positioned by Algorithm 4 block C.
The proof of Lemma 9 is similar to the proof of Lemma 6, except Lemma 8 should be used to argue that the cycle C is blocked by guarding a single end node of
Theorem 3 is then proved since Algorithm 4 removes all cycles in G.
The relationship between the number of guards required and the number of obstacles
We derive the relationship between Nmin and the number of obstacles if there exists a perfect matching for G*.
Lemma 10
Consider a Voronoi diagram G modeling the environment W satisfying assumptions (1) and (2). Let M be the number of obstacles where the M th obstacle is the boundary obstacle. If a cycle-removing edge cover of G* is a perfect matching in G*, then
Proof
Since the perfect matching is a minimum cycle-removing edge cover, we have
Simulation results
Multi-robot exploration algorithms
Utilizing MATLAB simulations, we compare the performance of our multi-robot exploration algorithms with BE algorithms in the study by Kim et al. 6 We consider the environment identical to the environment in the study by Kim et al. 6 The obstacle boundaries are depicted with thick red curves in all figures. Along the trajectory of a robot, Voronoi vertices are shown as large dots. The robot speed is 10 distance units per unit time. To make the robot traverse a Voronoi edge, we use the controller of the work by Kim et al. 6 We consider the case in which the robot’s sensor range is long enough to detect a blocked sector. Therefore, the robot does not move through a blocked sector.
Figure 6 shows the trajectory of one robot under BE algorithms in the study by Kim et al. 6 Initially, the robot is at (2, 20). Also, the robot’s trajectory is shown with green circles.

The Voronoi diagram constructed by BE algorithms. BE: boundary expansion.
In Figure 7, two robots build the Voronoi diagram in the environment that is identical to that in Figure 6. Initially, two robots are at (2, 20) and (2, 15), respectively. This implies that the initial enclosing boundaries B0 built by two robots are identical. Moreover, the robots’ trajectories are shown with points and circles, respectively.

Two robots building the Voronoi diagram under SCN algorithms. The initial enclosing boundaries built by two robots are identical. SCN: Simultaneous Cooperative Networking and exploration.
In Figure 8, two robots build the Voronoi diagram in the environment that is identical to that in Figure 6. Two robots’ initial locations are (2, 20) and (45, 2), respectively. Moreover, the trajectories of two robots are shown as points and circles, respectively.

Two robots building the Voronoi diagram under SCN algorithms. SCN: Simultaneous Cooperative Networking and exploration.
We also simulated the case in which three robots construct the Voronoi diagram in the environment that is identical to that in Figure 6. Figure 9 shows three robots building the Voronoi diagram in the environment that is identical to that in Figure 6. Initially, three robots are at (2, 20), (20, 3), and (45, 2), respectively.

Three robots building the Voronoi diagram under SCN algorithms. SCN: Simultaneous Cooperative Networking and exploration.
Table 2 shows the exploration time in the case where the number of deployed robots varies. As we increase the number of deployed robots, the exploration time decreases.
Exploration time as we vary Nv, the number of robots.

Figure 10 shows both the Voronoi diagram D and obstacle environments with four circular obstacles. Thick red curves imply obstacle boundaries. Utilizing SCN algorithms, two robots build D. One robot starts from (2, 4), while another robot starts from (19, 6). See that D contains four cycles.

The Voronoi diagram D and obstacle environments. D* is a line graph with four nodes. Deployed guards are depicted as two red dots.
Table 3 shows the exploration time as we vary the number of deployed robots. We simulated the case in which one robot, which starts from (2, 4), builds D utilizing BE algorithms in the study by Kim et al. 6 Also, we simulated the case in which two robots, which start from (2, 4) and (19, 6), respectively, build D utilizing SCN algorithms. We further simulated the case in which three robots, which start from (2, 4), (19, 6), and (28, 5), respectively, build D utilizing SCN algorithms. As we increase the number of deployed robots, the exploration time decreases in general. However, in the case where we increase Nv from 2 to 3, the exploration time does not decrease anymore.
Exploration time as we vary Nv, the number of robots (D* is a line graph).

Intruder capture algorithm
Since we assume that every robot’s weapons are powerful enough to cover the width of a passage between obstacles, we can simplify our scenario such that a searcher and an intruder traverse Voronoi edges. In Figure 10, guards are depicted as large red dots. In the figure, two guards are located at two vertices in D, so that all cycles are blocked. D*, the dual graph of D, in Figure 10 is a line graph with four nodes. Thus, Algorithm 4 is used to deploy guards. Once two guards are located at two vertices, so that all cycles are blocked, then one free robot can chase one intruder at a time until every intruder is captured. Because of two guards, no intruder can run away from the free robot no matter how fast the intruder is. Our intruder capture algorithm works regardless of the number of worst-case intruders.
Recall D* is a line graph with four nodes. The minimum edge cover of this line graph is two. Thus, Nmin is equal to or less than two utilizing Theorem 3. See that one guard cannot block all cycles in D. Thus,
Conclusions
The central idea of SCN algorithms is that each robot explores by gradually expanding the explored parts of the environment. At the same time, every robot deploys nodes and, as a result, a sensor network based on Voronoi diagrams is built. We prove that such a cooperative exploration results in efficient construction of the Voronoi diagram. Once the sensor network is completely constructed, this network can then be utilized by the robots to secure the environment. Guarding robots can be positioned at locations to ensure that no intruder can escape, while one free robot can capture every intruder one by one. In our future works, we will do experiments to verify the effectiveness of both our SCN algorithms and our intruder capture algorithm based on sensor networks.
Footnotes
Author’s note
All figures and tables are created by Jonghoek Kim.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed following financial support for the research, authorship, and/or publication of this article: This work was supported by the Hongik University new faculty research support fund.