Abstract
In this study, image processing was combined with path-planning object-avoidance technology to determine the shortest path to the destination. The content of this article comprises two parts: in the first part, image processing was used to establish a model of obstacle distribution in the environment, and boundary sequence permutation method was used to conduct orderly arrangement of edge point coordinates of all objects, to determine linking relationship between each edge point, and to individually classify objects in the image. Then, turning point detection method was used to compare the angle size between vectors before and after each edge point and to determine vertex coordinates of polygonal obstacles. In the second part, a modified Dijkstra’s algorithm was used to turn vertices of convex-shaped obstacles into network nodes, to determine the shortest path by a cost function, and to find an obstacle avoidance path connecting the start and end points. In order to verify the feasibility of the proposed architecture, an obstacle avoidance path simulation was made by the graphical user interface of the programming language MATLAB. The results show that the proposed method in path planning not only is feasible but can also obtain good results.
Keywords
Introduction
Mobile robot navigation involves finding a reasonable path in a limited working environment, to connect the initial configuration (including location point and azimuth angle) to the final configuration, and successful avoidance of the obstacle. Some recent literature works1–6 have discussed about this issue, and how to use image processing techniques to create an obstacle distribution model plays a key role in such matters. The turning point detection methods discussed in the literature can be broadly divided into two types: edge-based shape detection methods, which include Medioni–Yasumoto’s method, 7 Beus–Tiu’s method, 8 Rosenfeld–Johnston’s method, 9 Rosenfeld–Weszka’s method, 10 and weight type k-curvature method; 11 these methods calculate the curvature value at each point of the edge coordinates after edge detection processing, thus determining the turning point of all objects in an image; and grayscale value–based detection methods. 12 This article adopted Rosenfeld–Johnston’s method to detect the turning points in an image. The practice compares the angle of edge point vectors of each object to determine the position of the turning point and calculates approximate curvature values.
So far, research on path planning has reached the mature stage. An optimal path can be found under conditions of known environment coordinates and complete road map of the obstacle distribution model. Most frequently cited methods include the following: (1) Potential fields method: 13 This method mainly uses the principles that like magnetic poles repel and opposite magnetic poles attract to convert surroundings into a potential energy equation. The car and end goal are regarded as an attractive potential, and the starting point and obstacle as a repulsive potential. Attracted to the end, the car will successfully avoid obstacles and move toward the goal. (2) Cell decomposition method: 14 This method divides free space outside the obstacle into simple areas, called cells. Description of the relationship between adjacent cells is referred to as network contact diagram. Traditionally, the shortest network path problem was solved using label correcting methods, label setting methods, and dynamic programming methods. According to different processing strategies, label correcting methods are divided into breadth-first search (BFS), depth-first search (DFS), best-first search, and other important methods. 15 The single-source shortest path algorithm, Dijkstra’s algorithm proposed by EW Dijkstra 16 in 1959, uses the strategy of best-first search to solve the shortest path. RE Bellman proposed dynamic programming 9 to convert optimization into a series of single-step decisions, providing the best strategy for implementing a recursive solution in reverse from the last step to the initial step. (3) Analytical description of curves: 17 This method is most widely used in path planning; its intuitive idea is to use analytic functions to approach any motion trajectory. The analytical description of curves directly establishes a mathematical model of obstacle avoidance path and can be used as a reference trajectory of the controller design, which drew the attention of many scholars. Analytic functions often cited in the literature include Cartesian polynomials, generalized polar polynomials, and Fourier harmonic functions. The main purpose of trajectory parameterization is to convert path planning into a matter of solving parameter optimization under certain constraints. First, the so-called cost function is defined as the shortest path, minimum energy, or least time, followed by the start point, end point, or some relay points as boundary conditions. The obstacle model is parameterized by the constraint conditions, and the engineering optimization algorithm is applied to calculate the trajectory parameter value of the analytic functions. (4) Vertices search method: 18 This method is limited to a two-dimensional plane, and the obstacle shape is a convex polygon. The vertex plus start point and end point of all obstacles constitute the nodes of the network contact diagram, and the line segment between any two nodes constitutes a path in the network contact diagram; each path can be given a corresponding cost function, and the cost function of the forbidden path between obstructions is made infinite. Used with network path selection algorithms, including Dijkstra’s algorithm and dynamic programming method, whichever cost function produces the smallest collection of line segments is the shortest path from start point to end point.
To provide obstacle detection in the environment, the Sobel edge detection boundary sequence arrangement of eight close neighbors search method was combined with Rosenfeld–Johnston’s corner detection method to detect all obstacles and the turning point in the image, and to construct an obstacle distribution model. Second, a convex-shaped anti-collision safety net was added on the boundary of each obstacle on the network, and a modified Dijkstra’s algorithm proposed in this study was used with the cost function for the shortest path to find an optimized obstacle avoidance path.
Turning point detection of polygon obstacles
Grayscale conversion
Each pixel in the color images captured by charge-coupled device (CCD) is composed of three bytes, which represent three kinds of color information, red (R), green (G), and blue (B). First, the grayscale conversion process was conducted on the input image to turn the color pixel into a 0–255 gray level value; 0 represents black and 255 represents white. The conversion formula is as follows
wherein Y is the converted gray level value.
Image binarization
The so-called image binarization converts the gray level pixels through the selected threshold into value of 0 or 1. The purpose of image binarization is to segment the detection object and background information, which can significantly save memory space and image processing time. Image information is assumed to be a two-dimensional matrix
The Otsu algorithm can obtain the selection of best threshold. 19
Edge detection
The edge, which contains important image information, can be used to measure the object size in the image and recognize the object shape or carry out object classification. This article adopted the Sobel edge detection method; refer to correlation detection principle.
19
The main function is to find edge coordinates of the image object. The corresponding pixel data
Boundary sequential method
The so-called orderly arrangement of edge point coordinates of all objects was conducted after edge detection. In addition, the linking relationship between each edge point was determined, and which edge points belonged to the same object and which edge points belonged to image noise were confirmed. Image information after binarization and edge detection was collected by scanning from left to right and from top to bottom. If pixel content is “0,” it is defined as background; otherwise, as prospects. The entire scanning process can be distinguished as two processes: object detection and edge point detection, which can determine at the same time the number of objects and the edge point coordinates each object contains.
The ith edge point coordinates contained in jth object are defined as
Once an object is detected in the scanning process, the edge point detection process begins. This article adopted eight-neighbor searching to find the edge point coordinates in sequence and record them in edge point collection
Step 1: First, detection scan of object is conducted. The detection of foreground pixels indicates the existence of objects; background pixels are ignored. Then, edge point detection process in Step 2 begins. In this step, the foreground pixels found in the jth time are defined as edge point starting coordinates of the jth number of object, expressed as
Step 2: Based on the edge point starting coordinates
Step 3: If the edge of the object is a closed curve, Step 2 is repeated. When edge point coordinate
Step 4: The image often contains some minor noise. A threshold value

Search order of eight neighbors.
Step 1 is repeated until scanning of all pixels in the image is complete. After that the process of the boundary sequence permutation method on all objects is complete.
Figure 2 illustrates the eight-neighbor searching algorithm. The left icon is observed first. The detection of foreground pixels ☆ in the scan indicates the presence of an object. The eight-neighbor searching algorithm then sequentially detects whether “1, 2, …, 8” are edge point coordinates (or foreground pixels) of that object. Once checked, its next edge point is “3,” and its coordinates are immediately saved to the edge point collection of that object. The new foreground pixel 3 is regarded as the reference point ☆ of the next eight-neighbor scan, and the previous pixel ☆ is set as background data, as shown in the diagram on the right.

Eight-neighbor searching procedures.
Turning point detection method
The discontinuous change in tangent direction of a certain point at the edge of an object is called the turning point. Rosenfeld–Johnston’s method 3 was adopted in this study to detect the turning point in the image by comparing the angles between edge point vectors of each object to determine the position of the turning point. In order to calculate the more continuous approximate curvature value, as well as smoothly distinguish the angle of adjacent edge points, and prevent digitizing errors causing an erroneous turning point, this study introduced a smooth scaling k. The method is described below (hereinafter, indicator j is omitted).
Aimed at the edge point coordinates
wherein κ is a natural number, and the sampling length of the edge point has a smoothing effect, which can give the approximate curvature values of each edge point of the objects a more continuous effect.
Selection of
value
The κ value selection affects the approximate curvature calculation results. As much as possible, a smaller k value should be chosen to reduce the number of points abandoned, so as to reduce the loss of information; however, too small a k value will cause curvature value deviation because of the impact by digitizing errors; refer to Figure 3. Clemens et al. 5 propose that the preferable range of k values for selection is 4–6; herewith, k value of 4 was selected in the simulation software. Different k values will affect the standard for judgment of the turning point.

Smooth scaling used to reduce the impact of digitizing errors.
Curvature threshold
calculation
The breakpoint of the object on the two-dimensional plane by k-curvature is detected by a sudden change of the angle in the tangent direction. When the approximate curvature value is greater than the threshold value
Neighbor radius selection
As the computer image adopted the digitized images, digital image by binarization produced a series of non-continuous real points, leading to digitizing errors. As a result, some pixels neighboring the turning point will be identical, producing a curvature greater than the threshold value and multiple pseudo turning points. This study puts forward an adjacent interval practice, which uses the radius r to determine the interval range in which pseudo turning points may exist. When the area of the object is large, the number of edge pixels is greater; a larger value can be selected for r. Conversely, when the area of the object is small, a relatively smaller r value can be selected. Again, precision search was conducted in the radius range to further calculate the largest curvature values of the pseudo turning points; the real turning point is the point that we are looking for. Here, the simulation program is set to r = 6.
Obstacle objects distribution model
Safety boundary design
The obstacle avoidance path design is based on the vertices of the obstacle as graphical nodes to prevent the vehicle going over the vertex to collide with an obstacle, introducing the security boundary design. Regardless of the appearance of the obstacle, a layer of protective nets was fixed on its border. In addition to security concerns, the concave-shaped obstacles were made convex-shaped in appearance in order to meet the requirements of Dijkstra’s algorithm shortest path search. In the safety boundary design, the following two parameters must be considered:
1. Turning curvature restrictions: Consider the turning restrictions of the four-wheel mobile robot, as shown in Figure 4, wherein
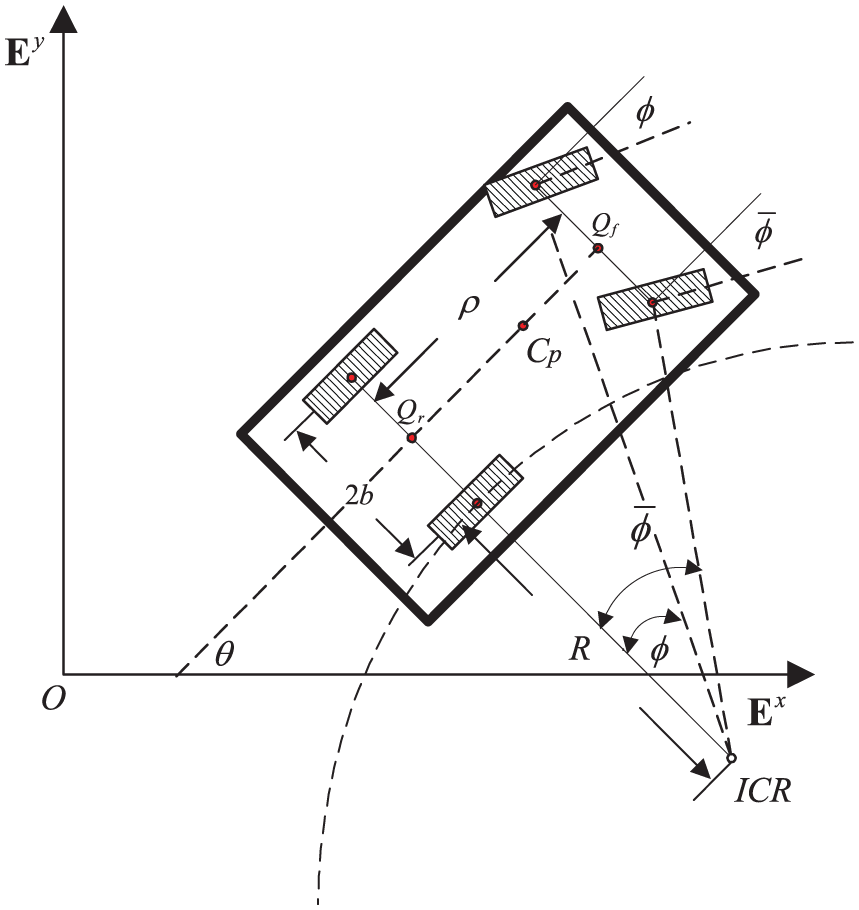
The mobile robot’s turning restrictions.
The relationship between the deviation angle of the left and right wheel can be deduced by the geometrical relationship in the figure
By the deviation angle drive specification
Assuming that the maximum angle of deviation of the actual vehicle is
In this way, the minimum turning radius specifications can be used to design the width of the obstacle safety boundary.
2. Boundary width design: The design of the safety boundary should not be too wide or too narrow. Too narrow will make collision with obstacles easy and fail to achieve safety protection; too wide will take up too much space to reach the demand of optimization. For example, Figure 5 illustrates how a car’s turning angle at

Safe boundary width design.
In the figure,
The safe boundary width design is
wherein
Clearly, to make a car turn smoothly without colliding with an obstacle, boundary width L and turning radius of the vehicle are related to the turning angle.
Convex model of obstacle distribution
This study proposed a modified Dijkstra’s algorithm, combined with the safety boundary concept, to directly use vertices of the convex-shaped obstacle as network nodes. Aimed at the nodes of each obstacle, the cost function assessment was conducted to search for the shortest path. The model information of the obstacles, including the working environment of the robot having m number of convex-shaped obstacles, was obtained by boundary sequence permutation method and turning point detection method. Each obstacle included ri (i = 1, …, m) number of vertices (or turning points), and its coordinates were expressed as
1. Start point, vertices of each convex-shaped obstacle, and end points in total were
To form network nodes, start point coordinates were defined as
The coordinate vector was repressed as follows
2. The distance between each network node forms a matrix called the distance matrix, defined as
If obstacles between two network nodes cannot connect with each other, then the corresponding elements in the distance matrix M are defined as
3. The cost function from the start point
4. To search in a clockwise direction, all paths including
5. At the same time, the search path was also defined in a counterclockwise direction. Based on the Di node for network node
The forbidden path judgment
It is assumed that the mobile robot moves in the
wherein
wherein “∩” stands for the significance of “and.”

Indication of linear equation cutting plane.

Indication of polygon obstacle model.
The use of the polygon obstacle model (Figure 7) is conducive to the resolution of the problem whether or not the forbidden path lies between two nodes. The judgment criterion and the relevant steps are stated as follows:
Step 1: Via the turning point detection, the vertex coordinates of each obstacle were found to be
Step 2: For the two turning points of each obstacle (called vertices), a linear equation was determined. For example, in the ith obstacle, formula (14) using
Step 3: Regarding the start point, vertices of all obstacles, and end points in the image as network nodes
Step 4: Any two nodes
then it was called the detection point

Using detection point for discrimination of forbidden path.
Modified Dijkstra’s algorithm
Consider k number of network nodes
After execution, c is smallest element value in the x-vector; I is the indicator value of the smallest element located in the x-vector.
Figure 9 shows two obstacles,
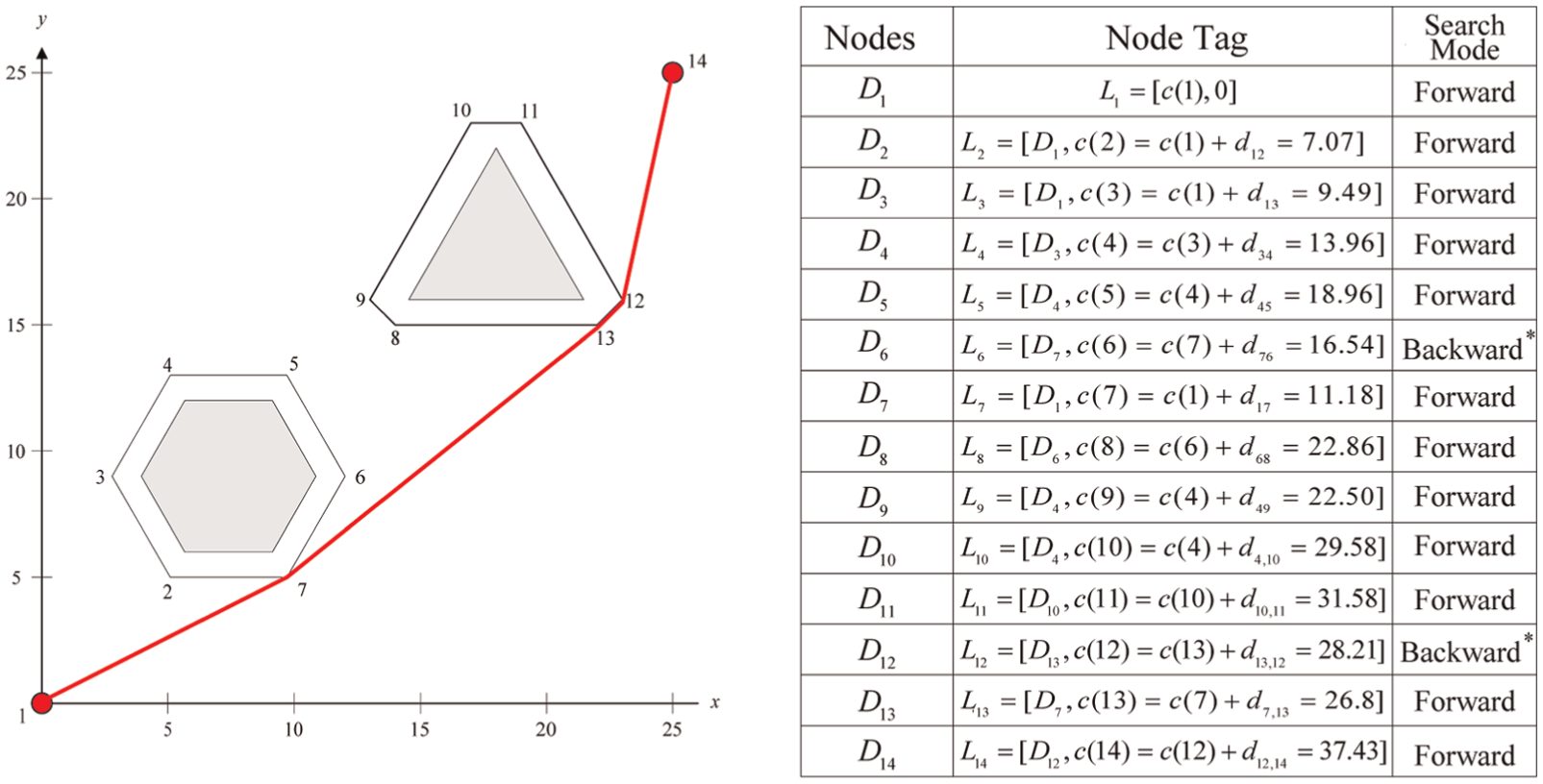
Modified Dijkstra’s algorithm hand count process.
Simulation results
Case 1
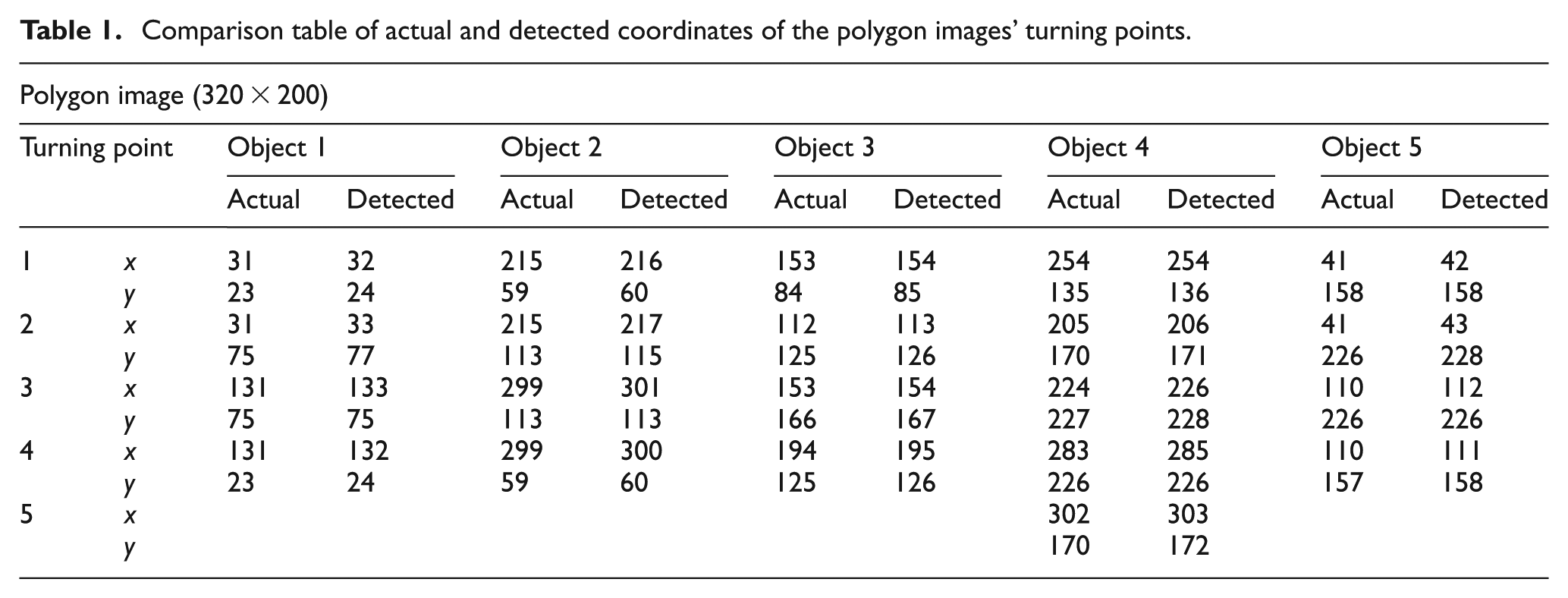
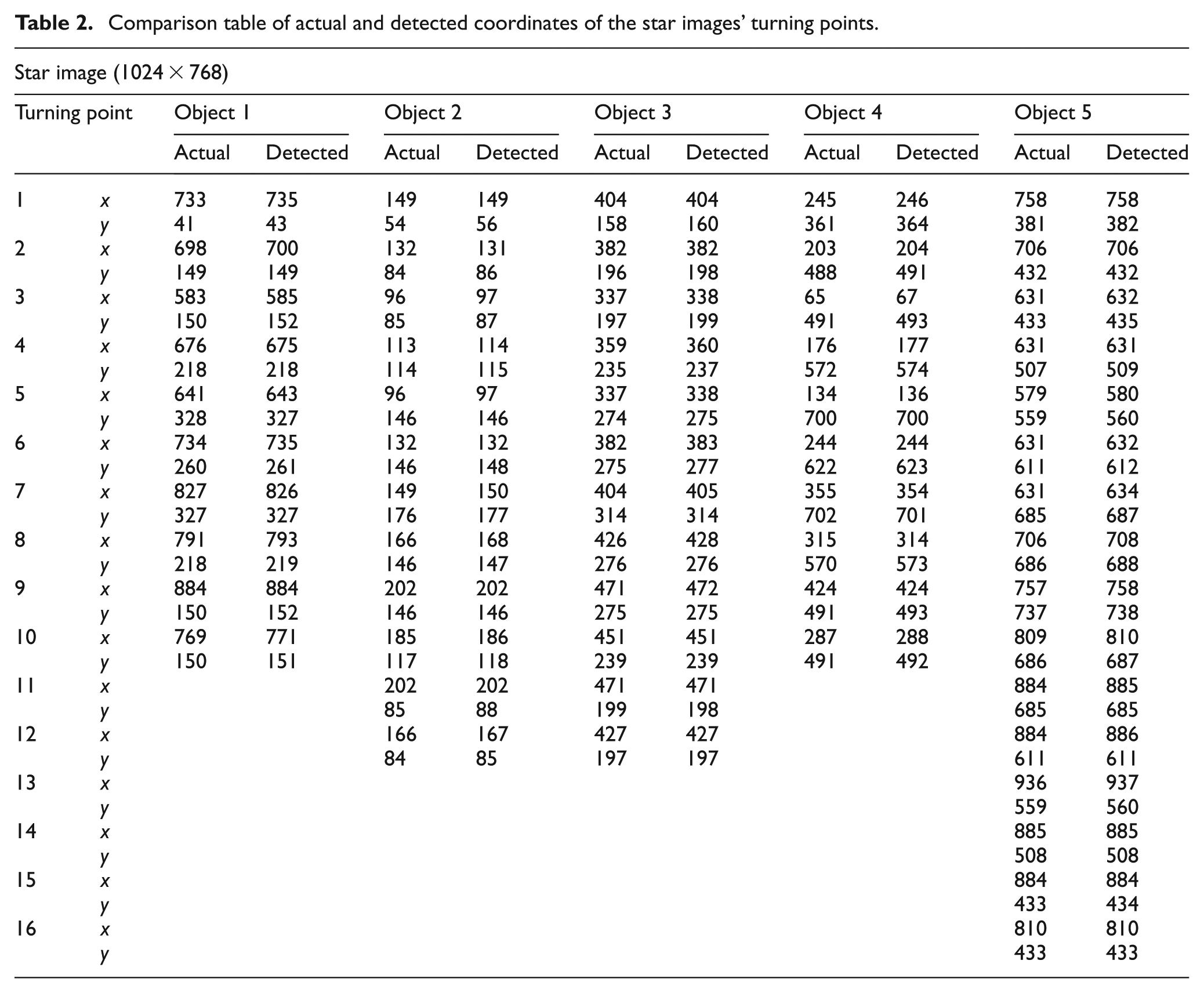
Using the programming language MATLAB 7.0, the proposed boundary sequence permutation of this study and the turning point detection algorithm were used to conduct simulation validation; Figures 10 and 11 illustrate the processing results of the turning point detection method, and Tables 1 and 2 record the comparison of the turning point actual coordinates and the actual detection results of the algorithms. First, the boundary sequence permutation of objects was used to complete the recording of the number of objects in the image and the edge point permutation coordinates of each object. Then, the turning point detection algorithm was used to identify the point of curvature value greater than threshold value,

Polygon images.

Star images.
Comparison table of actual and detected coordinates of the polygon images’ turning points.
Comparison table of actual and detected coordinates of the star images’ turning points.
Case 2
The MATLAB graphical user interface (GUI) toolbox was used to write the simulation software for obstacle avoidance paths, performed under a 2.8-GHz Pentium 4 processor. This study proposed the combination of boundary sequence permutation method, turning point detection method, forbidden path detection method, and modified Dijkstra’s shortest path search in a multi-functional integrated window. The image captured by the CCD or the users’ own selection set the obstacle distribution in the environment model. For example, the working interval in Figure 12(a) shows the coordinates of the starting point to be (0, 0) and the end point coordinates (25, 25). The user selected a triangular obstacle with a central point at (10, 5) and a radius of 3, a pentagonal obstacle with a central point at (15, 15) and a radius of 3, and a hexagonal obstacle with a central point at (20, 20) and a radius of 2. The goal was to design the shortest path curve from the start point to the end point coordinates. The turning point detection algorithm of image processing obtained a total of
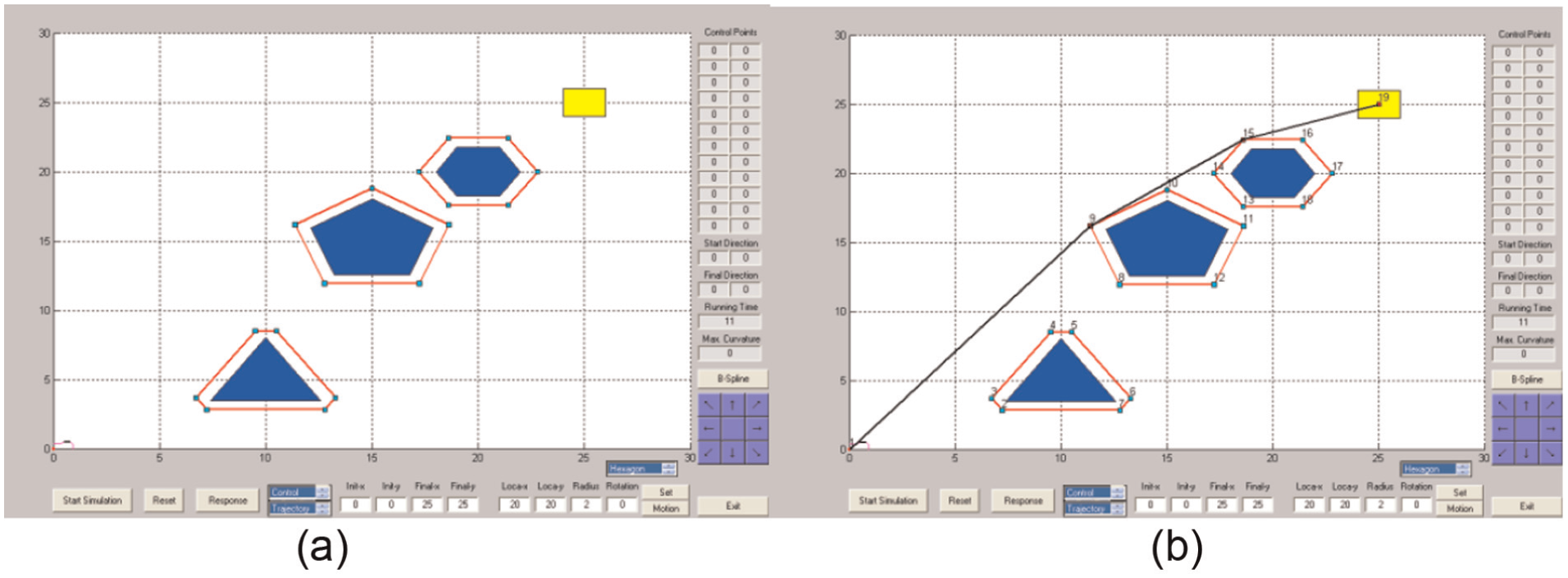
(a) Obstacle distribution and (b) path planning results.

(a) Obstacle distribution and (b) path planning results.
Conclusion
The main purpose of this study is to identify and avoid obstacles using images to plan out the shortest and smoothest obstacle-avoiding path. Through the boundary sequence permutation method and Rosenfeld–Johnston’s turning point detection algorithm, all the turning point coordinates of the object were measured. The modified Dijkstra’s algorithm was used to find an obstacle-avoiding path connecting the start point, turning point of the obstacle, and end point. Compared with the traditional method, the method proposed achieved the goals of global search by forward and reverse modes. To direct future improvements, the discovery of digitizing errors through the simulation process is an important factor affecting detection results.
Footnotes
Academic Editor: Stephen D Prior
Authors note
Pu-Sheng Tsai is now affiliated to Department of Electronic Engineering, China University of Science and Technology, Taipei, Taiwan.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The authors would like to thank the Ministry of Science and Technology of the Republic of China, Taiwan, for financially supporting this research under Contract No. MOST 105-2221-E-197-021.