Abstract
This article proposes an iterative deadlock resolution method for flexible manufacturing systems modeled with G-systems. To design a non-blocking controlled system with maximally permissive behavior in a G-system (GS), a reachability graph-based analysis technology is utilized. Since the reachability graph of a large-scale GS easily becomes unmanageable, an optimal non-blocking supervisor becomes a challenging problem in a GS. To facilitate this problem, the Divide-and-Conquer approach is a good choice for complex G-systems. First, an uncontrolled GS resolves into a number of associated subnets. Then, every subnet suffering from deadlocks is utilized to design the liveness-enforcing supervisor for the original GS. Thus, additional monitors can be obtained if the liveness of all subnets is achieved. Subsequently, a partially controlled GS is derived by including all monitors within the GS, and its liveness can be ensured by designing a new set of monitors. Consequently, a non-blocking GS is derived. The major advantage of the proposed method is that a non-blocking supervisor with near-optimal behavioral permissiveness can be obtained in general. Finally, a typical GS example popularly studied in the literature is applied to demonstrate the validity and the availability of the method in this article.
Introduction
The survivability of a manufacturing system to a large extent depends on its capability to swiftly respond to the variable market requirements, leading to the emergence and development of flexible manufacturing systems (FMSs) that can produce multiple product types with a small batch. An FMS is a conglomeration of computer numerically controlled machine tools, buffers, fixtures, robots, automated guided vehicles (AGV), and other material-handling devices. It usually exhibits a high degree of resource sharing in order to increase flexibility such that market changes can be responded quickly. Deadlocks are a constant threat to the continuous run of an FMS. They always block a system which even leads to catastrophic results in highly automated manufacturing systems. In order to optimize dynamic performance of a system, it is thereof necessary to explore an effective and computationally efficient mechanism such that deadlocks can never occur. Over the last two decades, a great deal of researches has focused on solving deadlock problems in FMS, leading to significant results in theory and successful industrial applications.1–7
Above all, Petri nets have been proven to be very useful in dealing with deadlock problems due to their natural ability on describing and analyzing the behavioral properties of an FMS. Generally, Petri net-based deadlock resolution methods can be classified into three strategies. They are deadlock detection and recovery,8,9 deadlock avoidance,10,11 and deadlock prevention.12–18 Deadlock detection and recovery is an optimistic strategy that grants a resource to a request as long as the resource is available. A deadlock detection algorithm is used to detect the occurrence of deadlocks. Once a deadlock is detected, a recovery mechanism is initialized by aborting one or more processes involved in the deadlock and the resources held by the aborted processes are relinquished. In the deadlock avoidance approach, at each system state, an online control policy is used to determine the correct system evolution among the feasible ones. Some aggressive deadlock avoidance policies do not eliminate all deadlock states. As for the deadlock prevention method, an off-line computational mechanism is usually established before the control implementation of a net system. Specially, the deadlock prevention approach always prevents a system from reaching deadlocks by adding external monitors. Deadlock prevention is considered to be one of the most effective methods in deadlock control.19–25
The analysis techniques of Petri nets used to deal with deadlocks in FMSs can be usually classified into two categories: structural objects and reachability graph (RG). Falling into the former category, a number of deadlock control policies can be developed based on the special structural objects of a Petri net model (PNM), that is, siphons, which are well recognized to be tied with deadlocks in either ordinary or generalized Petri nets.26–34 The deadlock control policies can be achieved by adding monitors to the original PNM. Generally, there are three very important criteria in evaluating the performance of a liveness-enforcing supervisor (LES) for a system to be controlled: behavioral permissiveness, structural complexity, and computational complexity. Many researchers have developed a great number of siphon-based deadlock control policies in order to achieve LESs with maximal permissiveness, simple supervisory structure, and low computational complexity. Especially, behavioral permissiveness plays the most important role in evaluating the performance of an LES. A maximally permissive, that is, optimal, supervisor always means all legal markings are kept in the controlled system. In this case, the utilization of system resources has the minimal limitation. However, supervisors obtained using siphon-based control methods in generalized Petri nets are not optimal, or even overly restrictive and conservative, from the behavioral permissiveness standpoint.35–37
As for the latter, the utilization of this technique can always lead to an optimal or a near-optimal supervisor with high behavioral permissiveness.38–41 A representative work on the design of optimal Petri net supervisors is the theory of regions. 42 The work by Uzam 43 proposes an approach to design optimal Petri net supervisors using the theory of regions. It establishes a connection between transition systems and Petri nets through net synthesis. The idea behind the theory of regions is that a state-based model, a model describing which states a process can be in and which transitions are possible between these states, can be transformed into a Petri net, a compact representation of the state space, explicitly showing causality, concurrency, and conflicts between transitions. Its appearance is followed by a large amount of research aiming to develop optimal deadlock prevention policies.44–46 Shortly after the work in Uzam, 43 using popular and plain linear algebra, Ghaffari et al. 44 explore the condition on the existence of an optimal monitor-based liveness-enforcing Petri net supervisor and develop a methodology to synthesize such a supervisor. However, it bears much computational cost. In such an approach, one first needs to generate the RG given a plant PNM. Then, the set of marking/transition separation instances (MTSI) is calculated. Finally, for each instance, a monitor is computed by solving a linear programming problem in which the number of constraints is approximately equal to that of nodes in the RG. Another RG-based deadlock prevention method was proposed by Uzam and Zhou, 46 which does not require complex computations for obtaining the monitors. The method proposed in Uzam and Zhou 46 is an iterative deadlock prevention approach. Deadlocks can be eliminated effectively by preventing the firing of transitions enabled at a first-met bad marking (FBM)’s father marking such that the FBM is unreachable. In general, the work in Uzam and Zhou 46 presents a simple and effective method. However, the size of the RG was the only problem for applying such an approach to very large-scale Petri nets since it suffers from the problem that the computation of RG is necessary at each iteration step. Due to the notorious state explosion, the scalability issue always impedes the acceptance of current methods despite their theoretical appeal.
To develop a computationally efficient method of the LES for a large-scale FMS, the RG-based deadlock control methods must be further improved. One of the most interesting directions is to segment a global system into some subsystems, and the additional monitors can be first computed for the subsystems and then merged into the set of monitors included in the global system. To achieve this, the work in Uzam et al. 47 presents a Divide-and-Conquer (D-C) strategy in designing the LES from subsystems for a large-scale system. Motivated by the seminal work in Uzam et al., 47 this article intends to extend the D-C strategy to the synthesis of an optimal non-blocking supervisor for a more general Petri nets, called G-systems (GS). To obtain the non-blocking supervisor for a complex GS, the G-system GS is divided into some smaller subnets. The set of monitors is computed only for those connected subnets with deadlocks such that the liveness of all related subnets can be ensured. By computing the RG of each subnet suffering from deadlocks, a dead-zone (DZ) and a live-zone (LZ) can be derived by splitting its RG. All reachable states in DZ are removed with respect to the simplified place invariant (PI)-based control method. 45 Note that the set of additional monitors is computed in an iterative way, that is, the earlier calculations of monitors may be contained within the latter subnets. Therefore, the DZ of the latter subnet is more smaller than its original subnet. The iterative process will terminate till all subnets are live. After that, we get a partially controlled G-system (PCGS) and sequentially compute monitors for the PCGS. In the end, a non-blocking G-system is obtained. The proposed method makes it possible to design non-blocking supervisor for a complex G-system when the RG of the PNM is big.
The remainder of the article is organized as follows. Section “Motivation of deadlock prevention policy for G-systems” outlines the motivation of the proposed deadlock prevention method for G-systems. Section “An iterative D-C synthesis approach for deadlock prevention in G-systems” develops an iterative deadlock prevention policy for G-systems and also provides a G-system example with two job processes to illustrate the applicability of the proposed policy. In section “A case study,” a typical case study from the literature is provided to show the validity and universality of the proposed method, and comparison study among different control methods and some discussion are made accordingly. The final section “Conclusion” concludes the article.
Motivation of deadlock prevention policy for G-systems
Some preliminaries related to Petri nets definitions used throughout this article can be referred to Li and Zhou. 48 Without loss of generality, we consider the most general classes of Petri nets as an example in this work, called G-systems, which are the most general processing-oriented class of generalized Petri net in the literature. A G-system can well model an FMS with process flexibility, assembly and disassembly operations, assignment flexibility, and permutation flexibility, whose corresponding definitions are depicted as Zhao and Hou. 49
As is well known, for most general classes of Petri nets, G-systems, a variety of deadlock prevention policies are developed based on structural analysis, that is, siphon control. However, the siphon-based control policies for G-systems are of exponential complexity due to a complete or partial siphon enumeration.50,51 Furthermore, the behavioral permissiveness problem is referred to as the fact that permissive behavior is overly restricted by the siphon-based control policies, that is to say, the supervisor excludes some safe (admissible) states. This is so since the output arcs of a monitor are led to the source transitions of the net model, which limits the number of workpieces being released into and processed by the system. Consequently, the approaches derived from siphon control are in general not optimal, or even overly restrictive and conservative, from the behavioral permissiveness standpoint.
In order to design maximally permissive supervisors for generalized Petri nets, RG analysis is a reliable, accurate, and effective (surely not efficient) method of a Petri net, although it is computationally expensive. Based on the theory of regions, Uzam and Zhou develop an iterative deadlock prevention approach. 46 It is assumed that there is a monitor solution to the deadlock prevention for a plant net model. The RG is divided into two parts: LZ and deadlock zone. A LZ is in fact the maximal strongly connected component that contains the initial marking. A deadlock zone contains markings from which the initial marking is unreachable. An FBM is defined in the deadlock zone. It does not satisfy live control requirements and its father node is in the LZ. Then, deadlocks can be eliminated by preventing the firing of the transitions enabled at an FBM’s father marking such that the FBM is unreachable. It is shown that the transition firing control can be converted into a generalized mutual exclusion constraint (GMEC) problem that can be implemented by a monitor whose computation is highly efficient. However, the approach in Uzam and Zhou 46 suffers from the state explosion problem when enumerating all reachable states in a sizable net model. Moreover, at each iteration step, one needs to compute the RG once. In order to circumvent this problem, it is necessary to seek a strategy that optimizes computational complexity, structural complexity, and behavioral permissiveness.
The D-C approach is a significant design paradigm in computer science to develop computationally efficient algorithms. When considering the RG-based deadlock resolution methods for a complex FMS, it is a really good option for improving the computational efficiency. Based on this mind, the work in Uzam and Zhou 46 first introduces the D-C approach, which divides a PNM into smaller subsystems and then carries out the monitors computation for the subsystems. Finally, the set of all monitors is added to the complex system. Then, Li et al. 52 propose a D-C method to prevent deadlocks for a class of ordinary Petri nets, called S 3 PR. Using the structural object of Petri nets, that is, resource circuits, a PNM is split into three strategies, which are idle subnet, autonomous subnet, and connected subnets. An LES, called a toparch, is designed for each connected subnet. If a particular separation condition holds in a PNM, the computational overhead of toparches is significantly reduced. This research shows that the resulting net by composing the toparches derived for the connected subnets can serve as an LES for the whole plant model. It has been claimed in Li et al. 52 that D-C-based deadlock control method is computationally superior compared with some global-conquer deadlock control policies such as Uzam and Zhou 46 and Ezpeleta et al. 53
To inherit and reserve the advantages of RG analysis in a complex FMS, this work proposes a deadlock prevention method for G-system by utilizing the D-C strategy. To obtain the non-blocking supervisor for a structurally complicated G-system GS, the global system model is first split into a few of smaller connected subnets. Based on the place-invariant (PI) control methods, monitors (control places) are added for every deadlocked subnet. In order to obtain as many as reachable states, the RG analysis is used to generate the state space of all subnets, which can be divided into good markings, dangerous markings, bad markings (BMs), and deadlock markings. The two former belongs to the LZ, and the two latter are included in the DZ. All states in the DZ must be excluded from the state space in terms of the simplified PI-based control method proposed by Uzam and Zhou. 45 Starting with the simplest subnet, monitors are computed to make the subnet live. Note that the computation of additional monitors and related arcs is a gradual process started with smaller subnets. The further calculation of the bigger subnets contains all monitors in previous iterations. Obviously, the DZ of the bigger subsystem by running the iterative process is smaller than that of in the original subsystem. When the computational iterations of all subsystems are completed, a set of monitors and a PCGS are obtained. After that, we add a number of new monitors for the PCGS to enforce its liveness. Consequently, a non-blocking controlled G-system, called CGS, is derived. The following section presents an iterative algorithm of deadlock control method for G-systems in detail.
An iterative D-C synthesis approach for deadlock prevention in G-systems
As the results stated previously, when an uncontrolled G-system is considered, the RG analysis technique is very useful in designing an optimal non-blocking supervisor. Obviously, the set of legal markings of the RG represents the optimal permissive behavior of the controlled system. Therefore, to obtain an optimal supervisor, an effective deadlock control policy should be established by excluding the DZ from the RG, while reserving all legal markings within LZ. To achieve this purpose, the theory of regions has been used for a PNM with respect to its RG. However, the computation of RG in a very complex net system cannot be carried out using the global-conquer methods as in Zhao and colleagues.51,54 In order to improve the computational efficiency of the supervisor, this section develops a D-C-based deadlock control algorithm for G-systems. At first, the definition of non-blockingness in a G-system is depicted as follows:
Definition 1
A G-system GS is well-formed if there exists an initial marking
Definition 2
A G-system
Remark 1
Note that the concepts of liveness and non-blockingness are totally different. Given a Petri net
As is well known, three kinds of places are defined in a G-system, which are resource places, operation places, and source/sink places. The first one represents all system resources of a G-system. Generally, a number of tokens are placed in resource places initially, which describes the number of available capacity. Operation places represent an action to produce a part in a processing sequence by a resource such as machines, robots, and so on. Note that there are no tokens initially in those places. The tokens in each source place describe the maximal number of concurrent job parts that can possibly take place in a processing route. In a cyclic model, the function of a sink place is the same as the source place and vice versa. Therefore, to simplify the structural analysis of the G-system net model, a sink place and a source place in a cyclic process are usually merged into an idle place.
Example 1
The net shown in Figure 1(a) is a G-system, where source places and sink places are
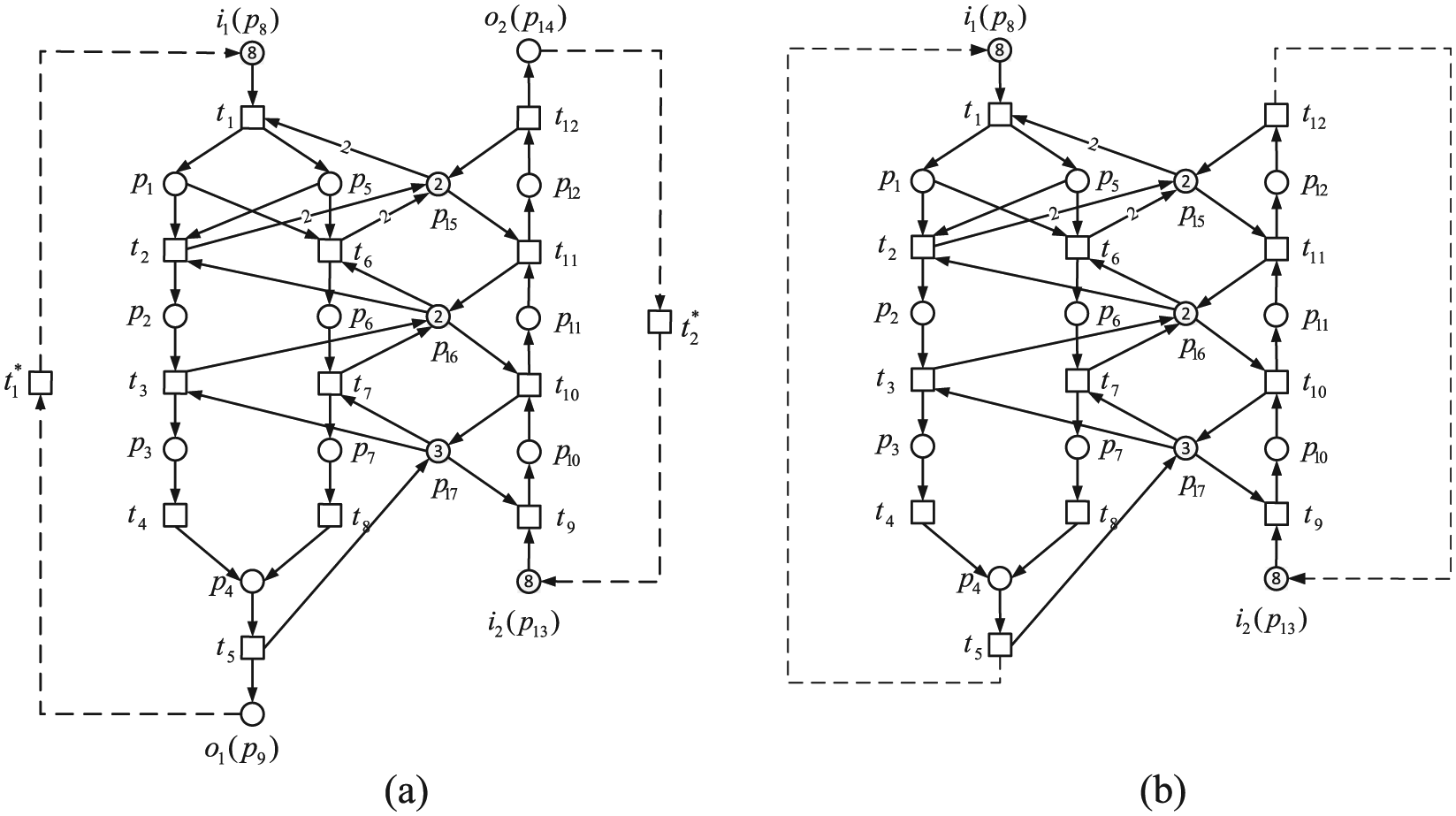
(a) A G-system net
When considering a large-scale G-system net model, the G-system is first divided into some smaller connected subnets such that the following RG computation can be simplified. Specially, each connected subnet consists of SR places with their corresponding input and output transitions and related connected arcs. In addition, operation places with their input and output arcs presented among those transitions of SR places should be included in the connected subnet. Subsequently, the formal definition of connected subnet
Definition 3
Let
In theory, the number of possible connected subnets equals to
Property 1
Let
Example 2
First of all, let us check the necessity of the idle places
When all connected subnets are derived from Definition 3 for an uncontrolled G-system, the RG analysis is used to compute the set of subnets suffering with deadlocks. Meanwhile, the LZ and DZ of those subnets are obtained. In order to implement the liveness of those connected subnets, all states in DZ should be removed according to the PI-based control method. 45 Specially, the purpose of the control policy is to prevent all BMs of the subset from being reached. Each BM related to operation places can be described as a PI in the G-system, the sum of tokens in PI has to be at most one less than their current value within the BM such that the BM is unreachable. Generally, each PI can be achieved by adding a control place and its connected arcs. Based on the RG of those connected subnets, monitors are computed to make all connected subnets live.
Subsequently, the controller computation method is presented based on PI control method, where the control specification on an uncontrolled G-system can be formulated by the following form
where M means a marking vector while l and b are integer constants. To achieve it, a monitor V should be imposed on the net system according to the following equations
where
Notation 1
Let
Consequently, in order not to reach a BM
Remark 2
The first step of Algorithm 1 is to divide a whole net model into a number of connected subnets due to Definition 3. Note that the number of connected subnets is closely related to the sets of SRs and resource circuits. For those connected subnets including more than one resource, there must exist the resource circuit simultaneously. That is to say, those unconnected resources cannot derive connected subnets. Therefore, the numbers of SR places and resource circuits in a PNM are the decisive factor of connected subnets in the actual computation. Although there are
Non-blocking Supervisor Design for a G-system Using D-C Synthesis Method.

Example 3
Now let us utilize Algorithm 1 to design a non-blocking supervisor for the uncontrolled net shown in Figure 1(b).
Step 1: The G-system shown in Figure 1(b) is divided into connected subnets based on its SRs. Since there are three (
Step 2: By analyzing the liveness of each connected subnets
Step 3: Next, additional monitors are designed for each connected subnet in
For For The PCGS with monitors
Step 4: Finally, the controlled G-system with additional monitors

Three connected subnets with one shared resource of the system in Figure 1(b): (a) SN11. (b) SN12, and (c) SN13.
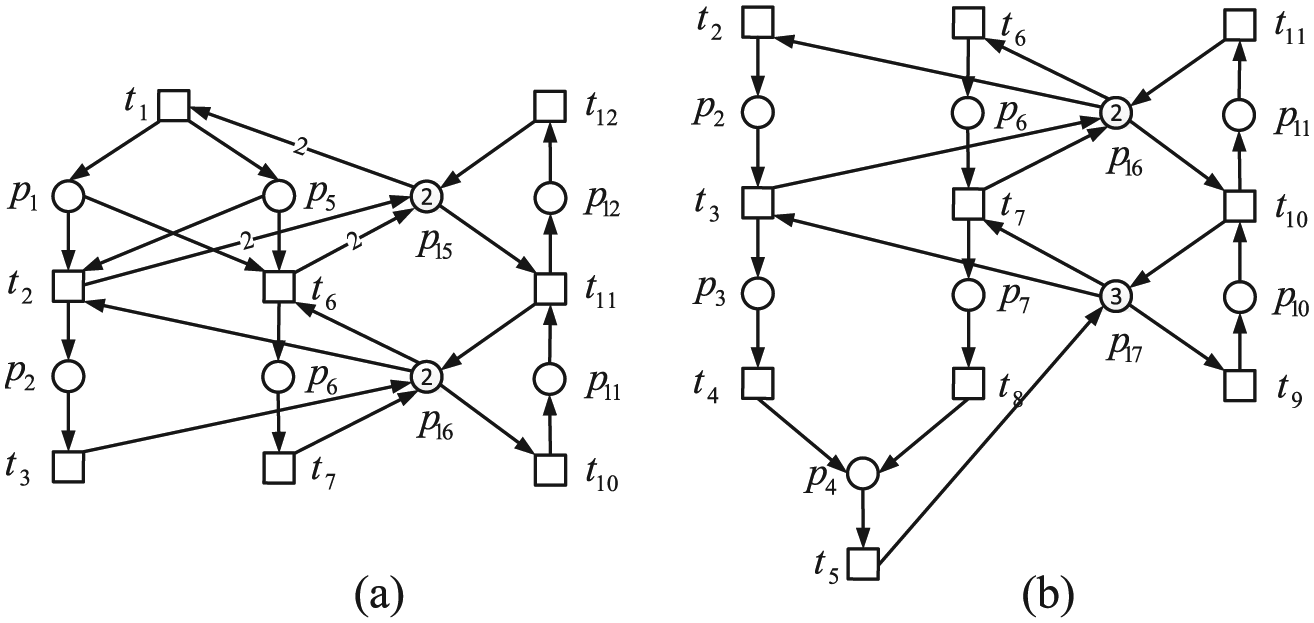
Two connected subnets with two shared resources of the system in Figure 1(b): (a) SN21(SN1) and (b) SN22(SN2).
Set of operation places existing in the connected subnets
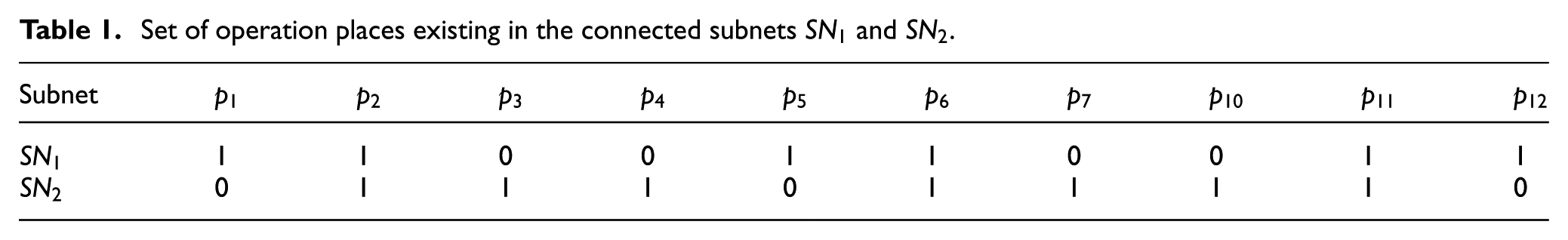
Monitors added for the G-system in Figure 1(b) by the proposed method.
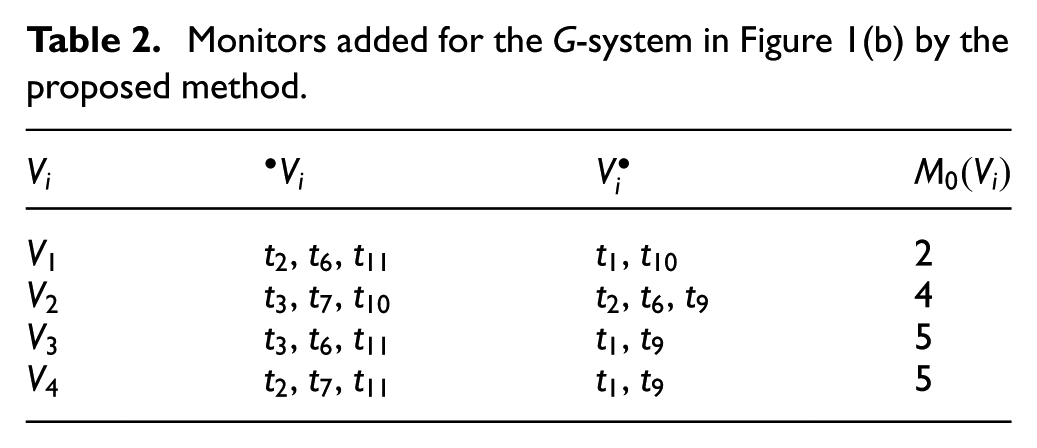
Non-blocking design procedure for the G-system in Figure 1(b).

The non-blocking supervisor obtained by the proposed method is near-optimal. In this article, “optimal supervisor” is used as a synonym for “maximally permissive supervisor.” A maximally permissive supervisor always implies high coefficient utilization of SRs. In general, the reachable states in LZ of a PNM can be viewed as a “quality metric.” Therefore, the highest quality can be provided in terms of the optimal control policies. In this sense, the proposed method is a good choice for designing an optimal supervisor. Since G-systems are the most general net models in the literature, a G-system is referred to as a PNM of an FMS in this article. For a bound G-system, the RG analysis of G-systems can be carried out by INA 55 that can provide both LZ and DZ. The DZ is regarded as the collection of all BMs for each connected subnet. According to Algorithm 1, if all BMs in RG are forbidden, implying that the controlled system is live since it cannot enter DZ anymore.
Theorem 1
Algorithm 1 can always terminate in a finite number of steps for a bounded G-system, and its termination gives a non-blocking supervisor and a controlled system
Proof
As is well known, a BM was main incentive of deadlock in an uncontrolled net system. If all BMs are eliminated and no new bad states are generated in the resulting controlled system
Remark 3
The RG analysis is an effective approach that can derive a maximally permissive supervisor for a PNM by adding monitors if such a supervisor exists. When there exists an optimal solution in a Petri net, a BM is optimally controlled if none of the good markings in the RG is removed. Unfortunately, since the coefficient of each PI equals 1, some legal markings may be forbidden when the related monitor is added to forbid the selected BM. 38 In this case, the maximally permissive supervisor cannot be obtained. Therefore, the proposed method cannot lead to the controlled system with maximally permissive behavior in a G-system. That is to say, the computed monitors may not allow some GSs to be reached when disabling the bad ones in an uncontrolled G-system. However, it is appealing to design a “near-optimal” supervisor, implying that the most number of legal markings are kept after adding monitors. In the practical applications, a lot of examples have been verified, overwhelming majority of which can obtain a high performance by the proposed method. Due to the limited space, we could not present all examples here. In this article, two experimental G-systems show that the supervisors are a near-optimal with high behavioral permissive. Meanwhile, the computational cost is reduced greatly by comparing with some RG-based global-conquer methods.
Theorem 2
Given a G-system
Proof
In theory, the number of reachable states in RG is exponential with the size of PNM. Since the RG generation of a given G-system GS is necessary at each iteration step in Algorithm 1, the computational complexity of Algorithm 1 is exponential.
Remark 4
Although the computational complexity of the proposed method is exponential, it is faster than the traditional global-conquer approaches to compute a RG and has been used widely in deadlock prevention policies.
A case study
In this section, a typical case study is presented to demonstrate the effectiveness and availability of the proposed method in an FMS. First, a G-system example is considered to illustrate the design steps in detail. Then, the performance comparison of non-blocking supervisors is made among different deadlock control polices in Li and Zhao 37 and Zhao and Hou, 49 and some discussion is also given subsequently.
A G-system example
Now a benchmark example is used to illustrate deadlock control polices presented in this article. An FMS as shown in Figure 4 consists of two robots R1 and R2, each of which can hold three parts every time, and four machines M1–M4, each of which can process two or three parts at the same time. Parts enter the system through three loading buffers I1–I3, and leave the system through three unloading buffers O1–O3. Three part types J1–J3 are produced.
R1 handles part movements from I1 to M1, M1 to M2, M2 to M1, and M1 to O1.
R2 handles part movements from M2 to M3, M3 to O1, I2 to M3, M3 to M2, I3 to M4, and M4 to O3.
M1 performs operations on J1 and J2.
M2 performs operations on J1 and J2.
M3 performs operations on J1 and J2.
M4 performs operations on J2 and J3.

An FMS layout.
Figure 5(a) shows the net model of the FMS that may use a multi-set of resources at a work processing step. The net system is a G-system that contains three processes

(a) A G-system net
Now let us utilize Algorithm 1 to design an optimal or a near-optimal non-blocking supervisor for the G-system shown in Figure 5(b). The RG of the uncontrolled G-system model has 68,531 states, whose DZ contains 2131 bad states, and LZ includes 66,400 GSs.
First, there are six (
Connected subnets with one shared resource for the net system in Figure 5(b).

Connected subnets with two shared resources for the net system in Figure 5(b).

Connected subnets with three shared resources for the net system in Figure 5(b).

Connected subnets with four shared resources for the net system in Figure 5(b).
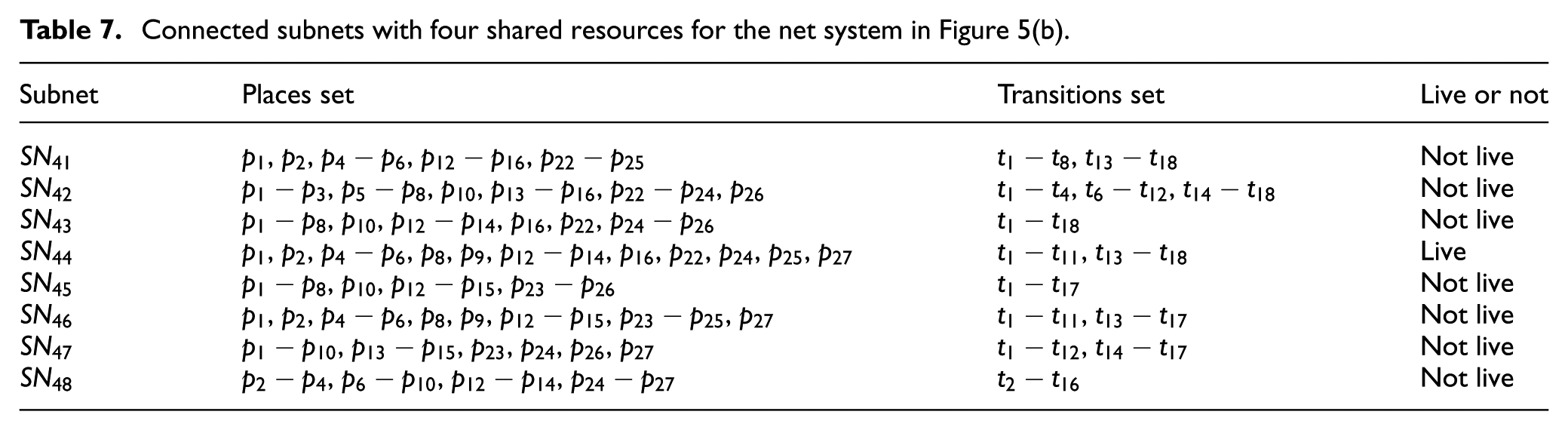
Connected subnets with five shared resources for the net system in Figure 5(b).
From above results, we obtain 35 connected subnets from this net model. After computing RG
ij
of above 35 connected subnets
Reachability graph analysis of the subnets in

Set of shared resources constituting the subnets prone to deadlocks.

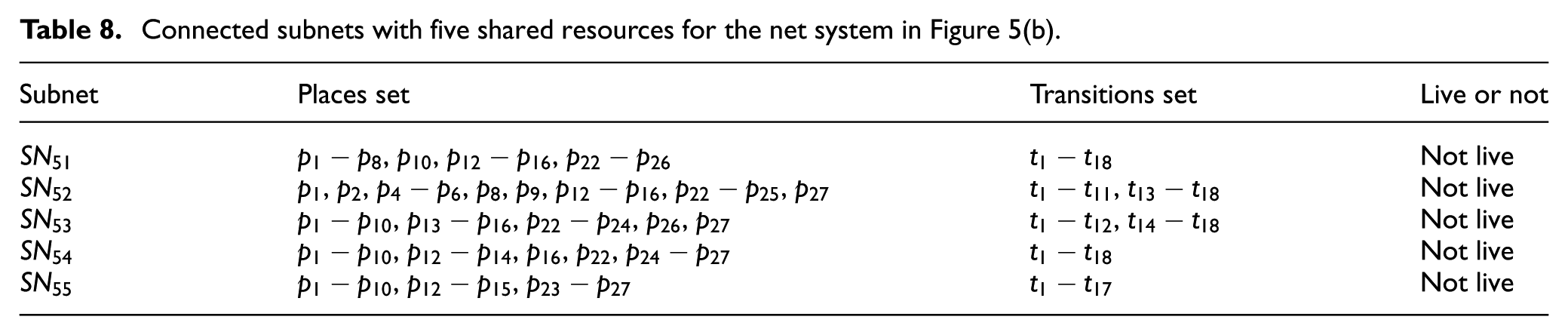
For clarity, all BMs in DZ and PIs are derived for all connected subnets
Place invariants computed for all bad markings of the G-system in Figure 5(b).
Monitors for the net system in Figure 5(b) by the proposed method.

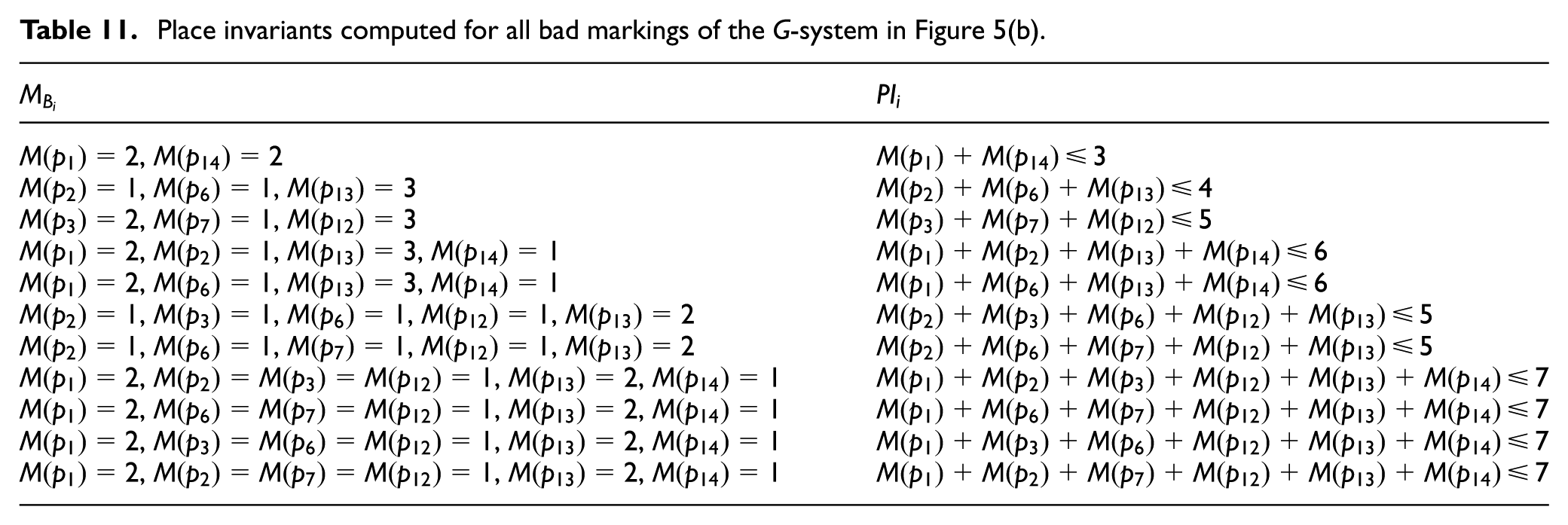
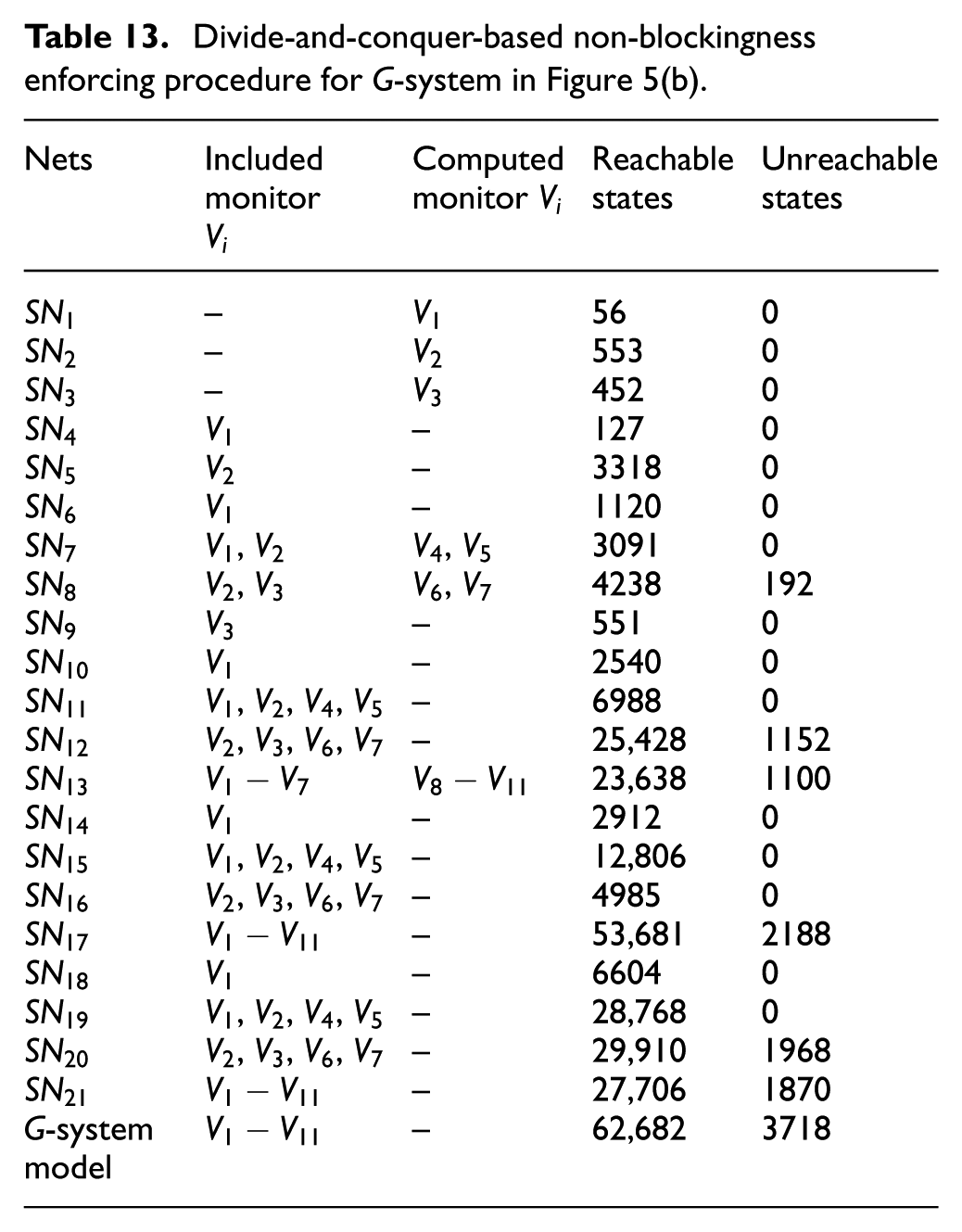
Divide-and-conquer-based non-blockingness enforcing procedure for G-system in Figure 5(b).
Comparison and discussion
Many researchers develop deadlock prevention algorithms that can obtain LESs with maximally permissive behavior, simple supervisory structure, and low computational complexity. Especially, a maximally permissive supervisor can always lead to high utilization of system resources. In general, most existing deadlock prevention polices for G-systems in the literature are not maximally permissive.37,49,54 However, the proposed method provides an optimal or a near-optimal deadlock prevent policy for designing a non-blocking supervisor for a G-system. Next, we review and compare the proposed method with that in Zhao and Li 54 and Zhao and Hou 49 through a typical case study proposed in this section.
To reduce the structural complexity of the controlled system, elementary siphons theory is a good choice for designing LESs with simple structure. The approach in Zhao and Li
54
can lead to structurally simple liveness-enforcing monitor-based supervisors using elementary siphons. Take the plant net model shown in Figure 5(b) as an example. The net has 68,531 reachable states, 66,400 of which are legal. Based on the method in Zhao and Li,
54
the net has 13 minimal siphons, 5 of those are elementary siphons, and the others are dependent. As a result, the elementary siphon-based supervisor of the example has five monitors only for elementary siphons, namely
Monitors added for the net system in Figure 5(b) due to the policy in Zhao and Li. 54

Due to the inherent complexity of Petri nets, any deadlock prevention policy that depends on the complete siphon enumeration is definitely exponential with respect to the size of its plant net model. In order to tackle the computational complexity problem, a mixed integer programming (MIP)-based deadlock detection method finds its further applications. The study in Zhao and Hou
49
proposes a two-stage iterative deadlock prevention policy for G-systems using MIP-based deadlock detection technique. Similarly, for the model shown in Figure 5(b), five monitors are computed due to the method in Zhao and Hou,
49
namely
Monitors added for the net system in Figure 5(b) due to the policy in Zhao and Hou. 49

As stated previously, behavioral permissiveness is one of the most important criteria in evaluating a supervisor. Determining how to design a maximally permissive Petri net supervisor has been an interesting yet significant problem. Note that RG is a reliable, accurate, and effective analysis method. However, the method usually suffers from expensive overhead since the complete state enumeration of a Petri net is exponential with its size and initial marking. Aiming at solving the deadlock problems for complex FMS, by further improving the RG-based control policies, the D-C strategy is a significant application on designing a non-blocking supervisor for G-system. Likewise, taking the net model shown in Figure 5(b) as an example. There are 11 monitors designed by the proposed method, namely
Conclusion
The deadlock prevention approaches in the literature are usually developed by either structural analysis or RG analysis. The former utilizes structural objects such as siphons, P-invariants, and resource circuits. Generally, the major weakness of existing deadlock prevention polices based on structural analysis is the behavioral permissiveness. Specially, an optimal or a near-optimal supervisor cannot be obtained in a generalized net since siphon control is conservative in general. By contrast, the theory of regions is a technique that can find an optimal LES in general cases when it exists. However, its computation is notoriously expensive since the complete state enumeration is necessary. Therefore, the bottleneck of the RG-based method limits its broad application for structural complex systems.
The proposed deadlock prevention policy aims to felicitously trade off behavioral optimality for computational tractability. To achieve this, a D-C iterative algorithm is explored for the most general classes of Petri nets, called G-systems. First, a given G-system is parted into some connected subnets, and then partial controllers for those subnets prone to deadlocks are designed based on the RG analysis. Obviously, the RG computation of the subnet becomes much easier compared with the global G-system. Finally, a non-blocking supervisor is designed after all subnet and its partially controlled system are live. The applicability and the effectiveness of the proposed method to realistic systems have been shown by considering two blocked G-systems from the literature. Experiment results indicate that the method proposed in this article can always lead to a near-optimal non-blocking supervisor. Moreover, the computational cost of the proposed method is lower, which is applicable to big FMS prone to deadlocks.
Footnotes
Academic Editor: ZhiWu Li
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the Natural Science Foundation of China under Grant Nos 61563045, 61403296, and 61104110, in part by the research grant of the Scientific and Technological Research Council of Turkey under the project number TüBiTAK-112M229, and in part by the Fundamental Research Funds for Central Universities under Grant Nos XJS1404, JB140407.



