Abstract
Nowadays, many kinds of flexible manufacturing systems are used to process many complex manufacturing works due to their machine flexibility and routing flexibility. However, such competition (i.e. robots and machines) for shared resources by concurrent job processes can lead to the problem of a system deadlock. In existing researches, almost experts adopted place-based as controllers to solve the deadlock problems of flexible manufacturing systems whatever the concept of siphons or the reachability graph method are used. Among them, only the reachability graph ones can obtain maximally permissive live states. In this article, the authors try to propose one novel transition-based deadlock prevention concept to solve flexible manufacturing system’s deadlock problem. In addition, two algorithms are developed to support above concept. The experimental results indicate that the proposed policy not only can obtain maximally permissive controllers but also recover all original deadlock markings.
Keywords
Introduction
Flexible manufacturing systems (FMSs) 1 are a variable working system using all kinds of machines, robots, and conveyors that are shared resources. The FMSs may consider varied resource allocation systems (RASs). 2 The deadlock occurs if two or more competing actions in shared resources. Thus, engineers must consider and solve the deadlock problems when they want to design and control the deadlock-prone FMS. Petri net3–8 is good to model and analyze FMSs because of the wonderful dynamic and graphic representation. Therefore, almost researchers use Petri nets as their tool to obtain all kinds of controllers. Furthermore, there are three kinds of controllers used to solve FMS’ deadlock problems. They are control places based on siphon concept,1,9–14 control places in reachability graph analysis,15–17 control arcs, 2 and control transitions.18–20
Liu et al. 9 presented a concept of controllable siphon basis that adding a control place and related arcs to each strict minimum siphon forming a controllable siphon basis. A new deadlock prevention policy was proposed by an algorithm for constructing a controllable siphon basis. This novel deadlock prevention policy by controllable siphon basis is better than the elementary siphon algorithm. 11 But how to find a controllable siphon basis to get a best performance is a heavy cost to finish in the large Petri net (PN).
Wang et al. 10 proposed an algorithm using an emptied siphon based on loop resource subnets to extract a desired emptied strict minimum siphon (DESMS). Then, they applied the mixed-integer programming (MIP) to obtain a maximally permissive liveness-enforcing supervisor. When one extracts a desire emptied strict minimum siphon, it must be going through three steps of processing. The complexity increases. Although the MIP obtains a maximally permissive liveness-enforcing supervisor, the marking states of PN will be sacrificed some.
Uzam and colleagues15,16 develop a deadlock prevention policy based on theory of regions to obtain maximal liveness performance. However, the policy fails to determine all sets of event-state-separation-problems (ESSPs), and its application seems limited to some special nets only. Therefore, some works21–24 aim to develop a computationally more efficient optimal deadlock control policy based on the theory of regions.
Another new method named interval inhibitor arcs 2 is proposed. Two main stages are present as follows: the first stage is to analyze the reachability graph of PN. The next step is searching the good markings, dangerous markings, bad markings, and dead markings. And, it prevents good markings into the bad markings. Finally, the deadlock system will be live. Note that this approach needs the reachability graph to distinguish the various markings. When the PN system is large, there are too many constraints and variables to consider. Thus, the method is hard likelihood to obtain a live PN. Furthermore, these too many constraints and variables cause not to be an achieved live PN.
Recently, Chen et al.25,26 propose one novel technology called maximal number of forbidding first bad marking (FBM) problem (MFFP) to obtain optimal states with a small number of control places. It solves the time-consuming problem successfully. According to our survey, the MFFP method seems the best one in existing literature based on place-based controller concept. However, this policy merely can be used in some special nets. For general cases, deadlocks could still exist.
Above means adopt place-based or arcs-based to prevent deadlocks from occurring. The last mean is transition-based controller concept. Huang et al. 18 first used the concept of control transitions to solve the deadlock problem. Advantage of control transition is that it can obtain more permissive markings using state equations. 3 However, it is pity that it cannot identify the correct optimal number of reachability graph of one FMS. In following, Zhang and Uzam 19 apply the reachability graph to obtain the control transitions using formulations of the set covering technique. 27 However, the efficiency seems too low of the proposed method since it depends on the reachability graph completely. In addition, it also cannot identify the correct optimal number of reachability graph of one FMS in advance.
Based on above disadvantages of two transition-based control policies, this article proposes two improved deadlock prevention policies. The two transition-based deadlock prevention policies not only can identify correct maximally permissive number of reachable markings of one FMS in advance but also recover all original illegal markings.
The rest of this article is organized as follows. Section “Preliminaries” briefly reviews the basic concept of PNs used in this article. Section “The proposed algorithm of transition-based controllers” presents our proposed two transition-based deadlock prevention policies. Section “Examples” gives two examples to test the efficiency of the proposed policy. Section “Conclusion” makes the conclusion.
Preliminaries
One PN original structure is defined as follows.
Definition 1
N = (P, T, F, W), where P = {p1, p2, p3, …, pm} is a finite, non-empty, and disjoint set of places. T = {t1, t2, t3, …, tm} is a finite, non-empty, and disjoint set of transitions.1,3F ⊆ (P×T) ∪ (T × P) is a set of arcs called flow relation. The element F is a set of directed arcs with the arrows from places to transitions or from transitions to places. W(·) is assigned the weight to an arc. Furthermore, the set of arcs in PN are nonnegative integer. A PN n is called ordinary when its weight of arcs is equal to one. Furthermore, for one real FMS net (N) modeled by PN, we called it PN model (PNM). It can be defined as follows.
Definition 2
Definition 3
Enabling and firing rule: 18 in one PNM, if a node x ∈ P ∪ T, then the preset of node x is defined •x = {y ∈ P ∪ T | (y, x) ∈ F}. The post set of node x is defined as x• = {y ∈ P ∪ T | (x, y) ∈ F}.
A transition t ∈ T is enabled at marking M by iff ∀p ∈ •t and M(p) ≥ W(p, t) that will be denoted as M[t
Definition 4
State equation:3,18 ones write matrix equations, Mk denotes a m × 1 column vector. The entry jth of Mk denotes the token’s number in place j immediately after the firing sequence (kth firing). The kth firing vector uk is a n × 1 column vector which are n − 1 zeroes and one nonzero entry. The “1” in the ith position indicates that transition i fires at the kth firing. Since the ith row of the incidence matrix A deduces the change in the marking as a result of the firing transition i, we can write the state equation as follows
Definition 5
Necessary reachability condition:3,18 the assumption that a destination marked Md is reachable from M0 by a firing sequence {u1, u2, …, ud}. According to the state equation for i = 1, 2, …, d and summing them, which can be rewritten as follows
where ΔM = Md − M0. Here, x is a n × 1 column vector of nonnegative integers that is called the firing-count vector. The ith entry of x deduces the number of times that transition i must fire to change M0 to Md.
Definition 6
Livelock: 18 x ∈ Z m , x ≠ 0, is a T-invariant if A T x = 0, where x is called the firing-count vector and matrix A denotes the change of the marking. Z m is the firing set of x. 11 One can deduce that a livelock is formed if a reachability graph is not a T-invariant. The characteristic of a livelock marking is not a deadlock and cannot reach the home state.
Definition 7
Reversibility: 29
1.A PN N has a home state Mh for an initial state M0 if for every reachable state Mi ∈ R(N, M0), a firing sequence σi exists such that Mi[σ
i
2.A PN N is reversible for an initial state M0 if M0 is a home state.
Definition 8
Simple sequential processes with resources (S3PR):
1
An S3PR is defined as the union of a set of nets sharing common places PRi, such that
Places in Pi are called operation places. PRi are called resource ones.
Pi ≠ ∅, pi0 ∉ Pi; PRi ≠ ∅,
∀p ∈ Pi,∀t ∈ •p, ∀t′ ∈ p•, •t ∩ PR = t′• ∩ PR = {rp}.
∀p ∈ Pi, (••p ∩ PR = p ∩ PR) ∧ (|p•• ∩ PR| ≦ 1).
Ni′ is a strongly connected state machine where
Every circuit of Ni′ contains the place
Ti is a finite set of transitions and the function of Ti is defined by W(·).
W(·) is a function defined on the set of transitions.
Fi is the same as the functions I and O describe the input and output arcs of the transitions, respectively.
Definition 9
Saturated number of tokens in idle places: for one real PNM, the size of its reachability graph will become larger when the number of tokens in idle places is adding from small to large. Finally, the number of reachable states will reach to one maximal number whatever the number of tokens increased in idle places. Under the situation, we call the number of tokens saturated number. Please note that the situation also can be called the optimal number of tokens.
For example, in Figure 1, Table 1 shows the different number of tokens in two the idle places (i.e. p1 and p6). From Table 1, we can see that the PNM reaches the maximal reachable states when the (p1, p6) is (3, 3). The experimental groups 21–24 are just used to present that the maximal reachable states of the PNM are equal to 15. Furthermore, the maximal reachable states are 15 whatever how large number of tokens is added into or increased into the idle place. Therefore, the set of (3, 3) is what we want, it is the saturated number of tokens in idle places of this PNM.
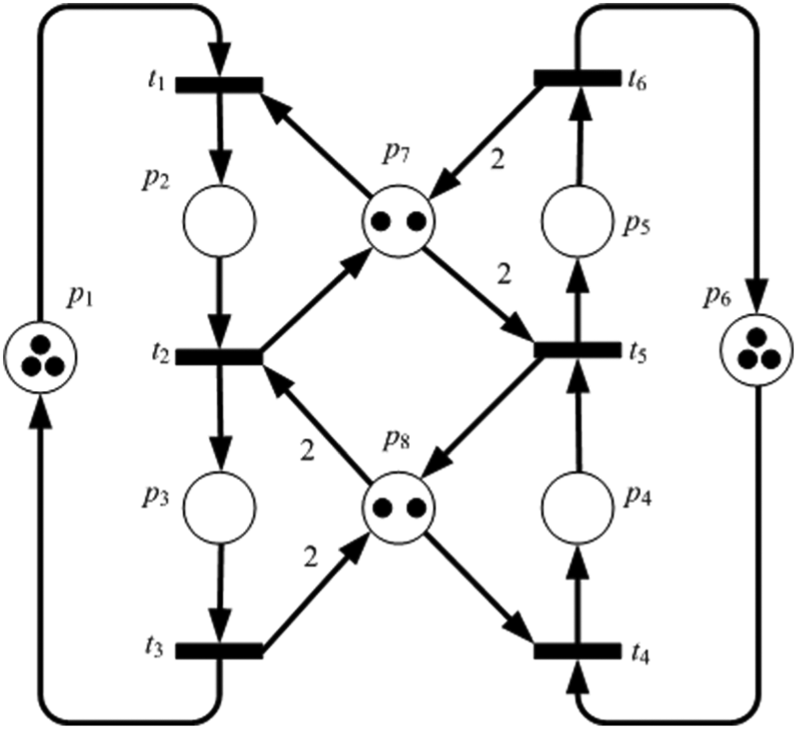
One small Petri net. 6
The variety of the number of RG when given different number tokens of (p1, p6).
RG: reachability graph.
Definition 10
The first deadlock marking (FDM): based on Definition 9, for one real PNM, one deadlock marking appear first in this system while the number of tokens for idle places is adding from small to large. The deadlock marking is defined as the FDM.
The proposed algorithm of transition-based controllers
In this section, two novel algorithms based on control transitions will be developed. Please note that the proposed algorithms can not only solve the deadlock problem but also recover all original markings of one PNM whatever they are live or deadlock initially. In other words, in this article, the so-called “maximally permissive states” means that all original deadlock markings can be further recovered under the proposed algorithms. Please also note that under the two algorithms, the saturated number of tokens in one PNM’s idle places can be identified. Therefore, the maximal reachable markings of one PNM’s reachability graph can then calculated correctly. Huang et al.’s 18 deadlock prevention policy just uses the dead marking and the initial marking to calculate the control transition. In other words, it does not know what the saturated number of tokens is. In this article, we can identify the correct and maximal number of one PNM’s reachable markings once the framework is established.
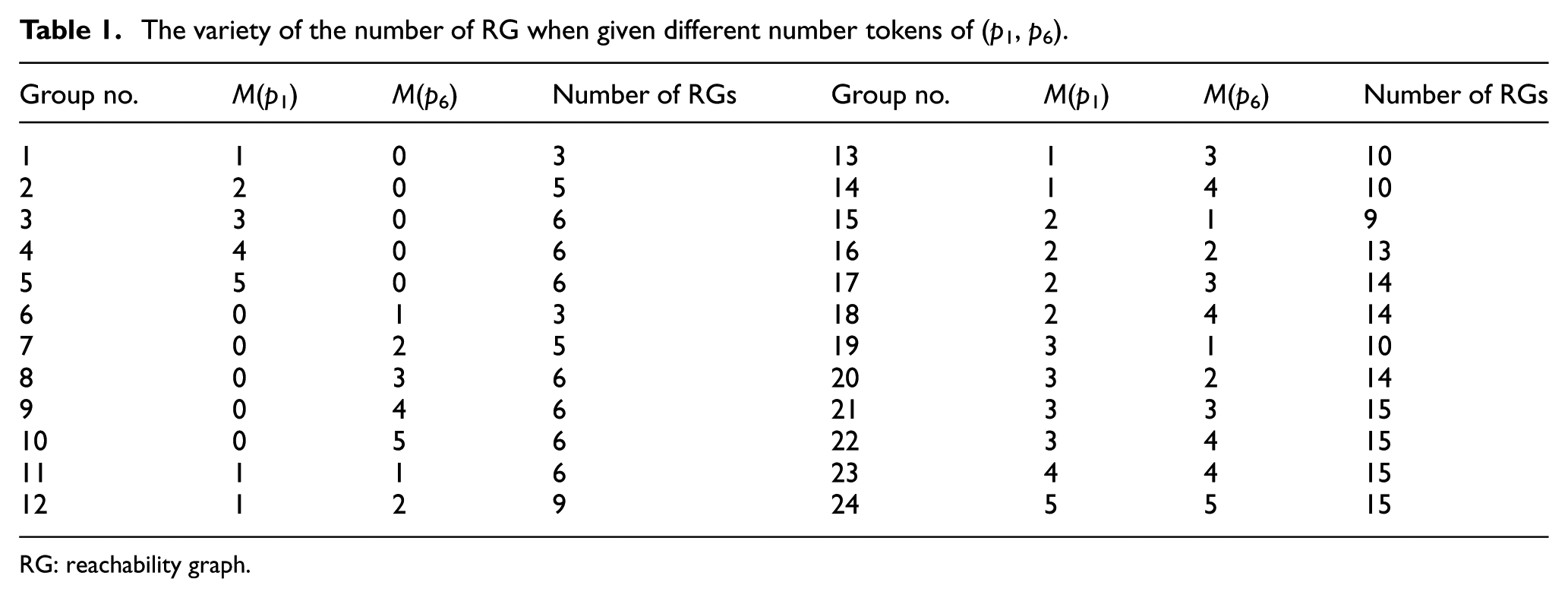
One small typical example 6 shown in Figure 1 is used to illustrate the proposed algorithms. In Figure 1, one can see that there are two idle places (i.e. p1 and p3) in this PNM, and their saturated or called optimal value is equal to 3. Under this situation, the number of its reachable markings shown in Figure 2 is equal to 15. Please note that there are four illegal markings (i.e. three quasi-dead markings and one deadlock marking) in the reachability graph. The detailed information is shown in Tables 1 and 2, respectively.
The property of all reachable markings of Figure 2.

The reachability graph of Figure 1.
Transition-based controllers
Based on Definition 4, one formalized equation for seeking transition-based controllers is developed. First, recall the Definition 4, the state equation is Mk = Mk − 1+A T ·uk. Besides, it is assumed that a deadlock-prone PNM should contain at least one deadlock marking Md in its reachability graph at which no transition is enabled. Therefore, Definition 4 can be replaced to Md = M0+A T ·ud for a deadlock-prone PNM. Please note that M0 is initial marking, A is the incidence matrix of a deadlock-prone PNM, and ud is the firing sequence from M0 to Md. As a result, one must find another relatively firing sequence from Md to M0 as follows: Md − A T ·ud = M0. The equation can be rearranged to M0 = Md − A T ·ud. Then M0 = Md+A T ·(−ud). Let yd = −ud. Then, one can obtain the new state equation for calculating transition-based controllers of a deadlock-prone PNM as follows

From above equation, undoubtedly, one can identify one set of firing sequence such that Md can be recovered.
Two algorithms based on different viewpoints
Two algorithms based on different viewpoints are present as follows:
Algorithm 1: based on the all reachability graph viewpoint.
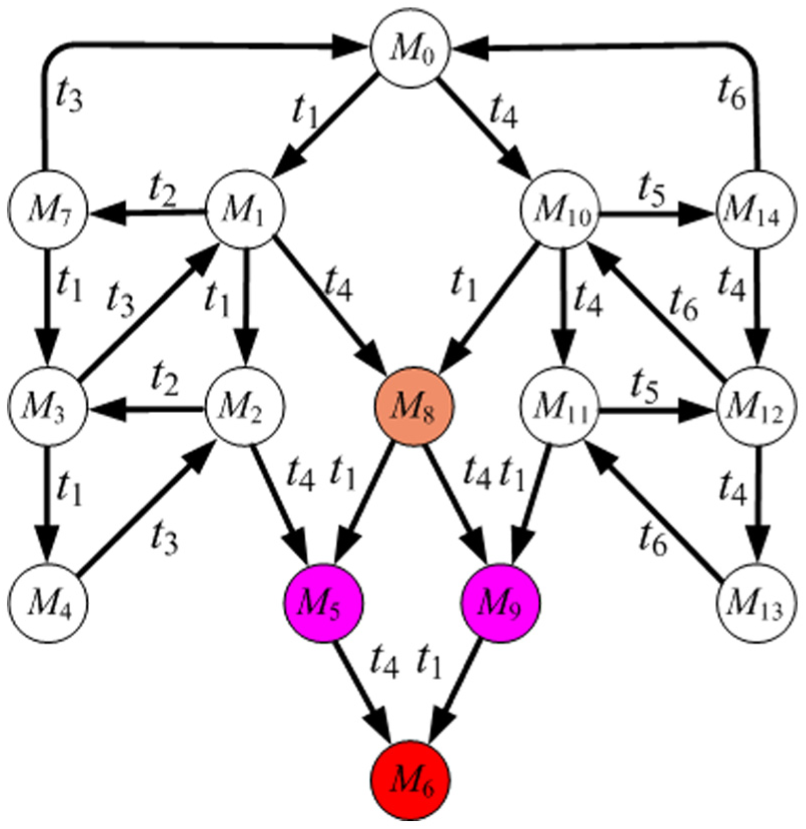
First, from Figure 2 and Table 2, one can identify that the property of the initial marking and the deadlock marking are M0 = 3p1+3p6+2p7+2p8 and M6 = p1+2p2+2p4+p6, respectively. Therefore, according to definitions 4 and 5, the control transition equation (CTE) can be listed as follows: Mh = Md+(O(Tcx) − I(Tcx)). Thus, the output control transition is O(t7) = 2p1+2p6+2p7+2p8 and the input control transition is I(t7) = 2p2+2p4. When the set of control transition is put into the original PNM shown in Figure 3, all 15 reachable markings including the 4 illegal markings are live shown in Figure 4.

A live Petri net system based on Algorithm 1.
The reachability graph of Figure 3.
Algorithm 2: based on the FDM viewpoint.
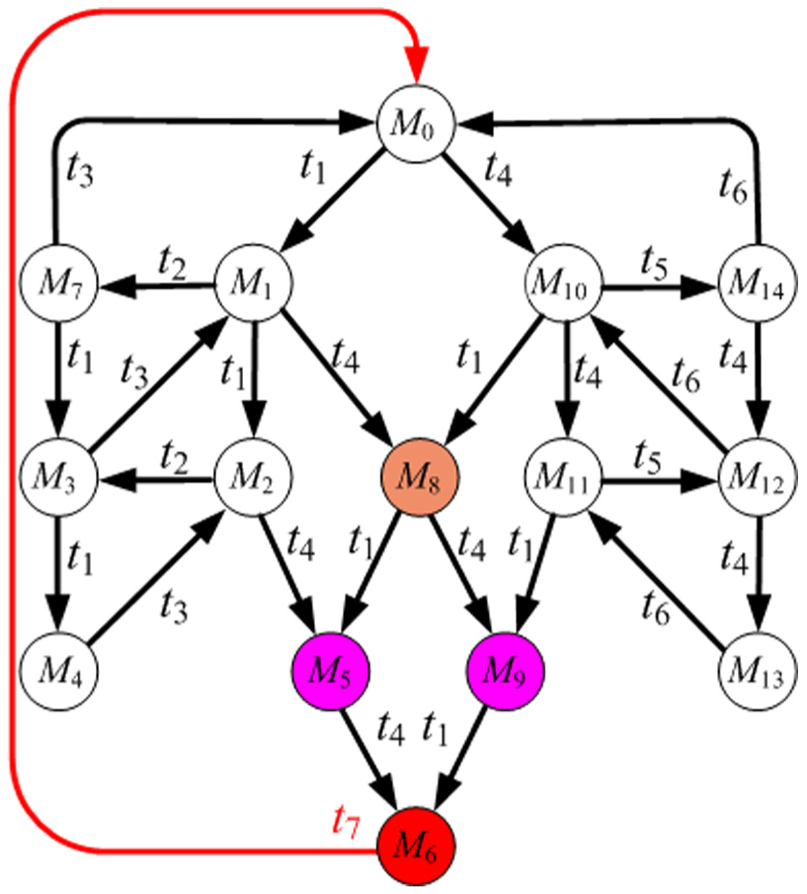
In the following, according to Definition 10 one can identify that the system meets the FDM while the two idle places (p1, p6) are given (1, 1). The detailed information is shown in Tables 1 and 3.
The property of all reachable markings of Figure 5.

Based on Table 2, one can realize that the saturated number of the two idle places (p1, p6) is (3, 3). It means that the maximal number of the reachability graph of the PNM is equal to 15 whatever how many tokens are added into (p1, p6). This is also called the full reachability graph viewpoint. On the contrary, in Algorithm 2, we just check when the first one deadlock marking will be produced by the PNM. Since the 12th group starts to produce the FDM, we use its data to calculate the controller. From Table 3, one can identify the deadlock marking is M3, and its property is p2+p4+p7+p8. Besides, the property of the initial marking M0 is p1+p6+2p7+2p8. From CTE, one can obtain the output control transition O(t8) = p1+p6+p7+p8 and the input control transition I(t8) = p2+p4. The PNM is deadlock-free when we put the controller into it. Figures 5 and 6 show the results.

A live Petri net system based on Algorithm 2.

The reachability graph of Figure 5.
Algorithms 1 and 2 present the very different viewpoints. Furthermore, Algorithm 1 adopts the viewpoint of global framework. However, Algorithm 2 adopts the viewpoint of local framework. Whatever what viewpoint is adopted, the PNM will be live and can also hold the maximally permissive states. More important, both of the proposed algorithms recover the all deadlock markings.
Theorem 1
Proposed algorithms can recover the deadlock PNM and is maximally permissive.
Proof
According to equation (1), one set firing sequence must exist, such that, Md can be led back to M0 once controllers exist. And, the controllers will not make the dead markings vanished. Therefore, the proposed algorithms can recover the deadlock PNM and is maximally permissive.
Examples
In this section, we want to present the high efficiency of the two proposed algorithms by testing two classical examples.15,18 The first example is used to present the proposed algorithms and the second example is used to make comparison with previous literature. First of all, two deadlock prevention policies are listed based on the two algorithms as follows.
Deadlock Prevention Policy I.

Deadlock Prevention Policy II.

In the following, we use example 1 to test the proposed Deadlock Prevention Policies I and II. Figure 7 shows its PNM. According to the Deadlock Prevention Policy I. The full reachability graph is surely needed to run. Figure 8 presents the full reachability graph of Figure 7.

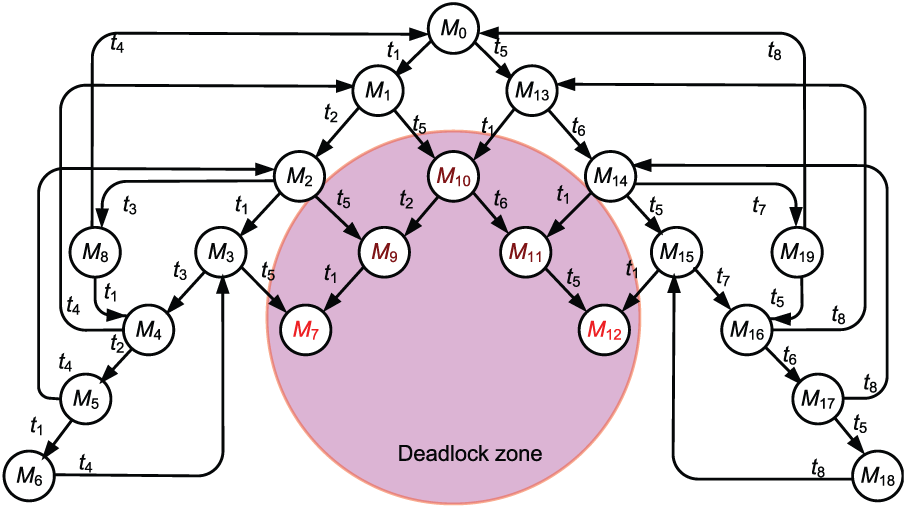
The full reachability graph of Figure 7.
Due to the limitation of paper space, we just show the properties of initial markings and two deadlock markings in Table 4.
The properties of initial and two deadlock markings based on Algorithm 1.

Then, we can obtain two controllers t9 and t10 based on Table 4 and the CTE. The detailed information of t9 and t10 are I(t9) = p2+p5+p10, O(t9) = 2p1+p3+p6+p9+p11, and I(t10) = p2+p7+p10, O(t10) =p1+p3+p6+p9+2p11, respectively. When the set of control transition is put into the original PNM of Figure 7, all 20 reachable markings including the 5 illegal markings (i.e. M7, M9, M10, M11, and M12) are live (please refer to Figures 9 and 10).

The two controllers are added into the PNM of Figure 7 based on Algorithm 1.
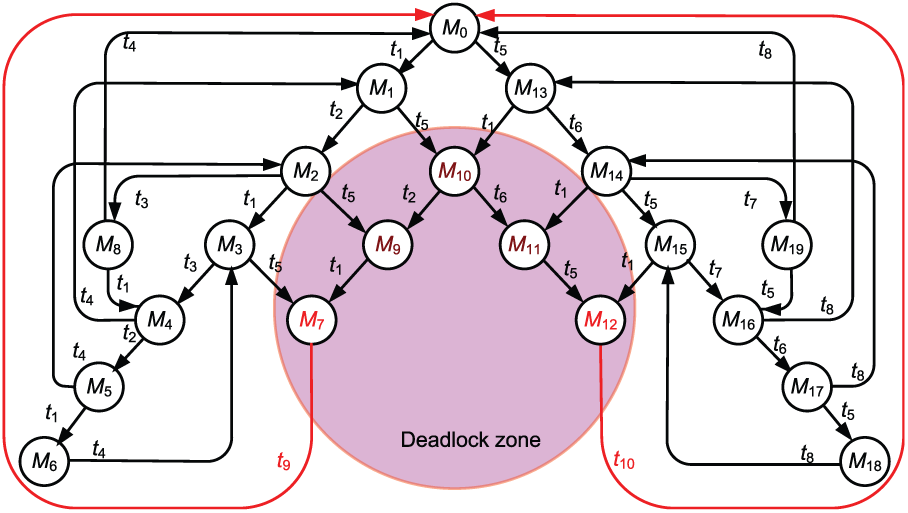
The full live reachability graph of Figure 8 based on Algorithm 1.
In the following, we adopt Deadlock Prevention Policy II to test the example 1. The system meets two FDM while the two idle places (p1, p11) are given (1, 1). The detailed information is shown in Tables 5.
The properties of initial and two deadlock markings based on Algorithm 2.

Similarly, we can obtain two controllers t11 and t12 based on Table 5 and the CTE. The detailed information of t11 and t12 are I(t11) = p5+p10, O(t11) = p1+p6+p9+p11, and I(t12) = p2+p7, O(t12) = p1+p3+p6+p11, respectively. Please notice that, when the two sets of control transition are put into the original PNM of Figure 7, all 20 reachable markings (also including the 5 illegal markings) are live (please refer to Figures 11 and 12).
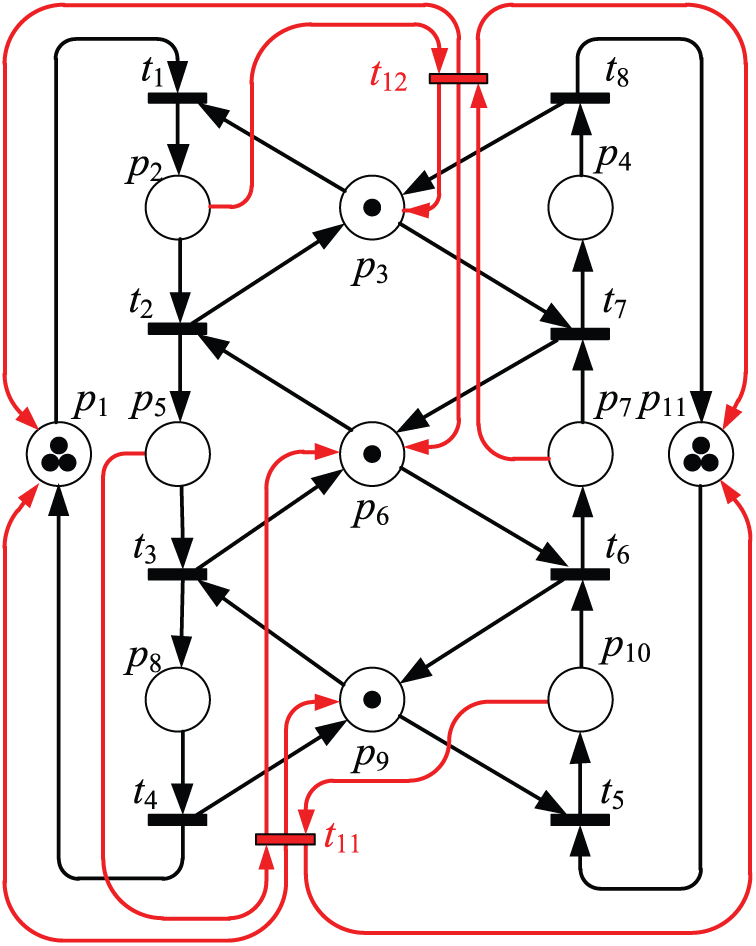
The two controllers are added into the PNM of Figure 7 based on Algorithm 2.

The full live reachability graph of Figure 8 based on Algorithm 2.
The second example shown in Figure 13 is from Huang et al. 18 and Zhang and Uzam. 19 Huang et al. 18 identify 32 reachable markings including 4 deadlock markings (e.g. 2p0+p5+p6+p8+p9, p0+p2+p6+p8+p9, p2+p3+p8+p9, and p0+p3+p5+p8+p9). Finally, they recover all reachable markings by their two control transitions (I(ti) = 2p7+p11+p12 and O(ti) = p8+p9; I(tj) = p7+p10+p11 and O(tj) = p8+p9).
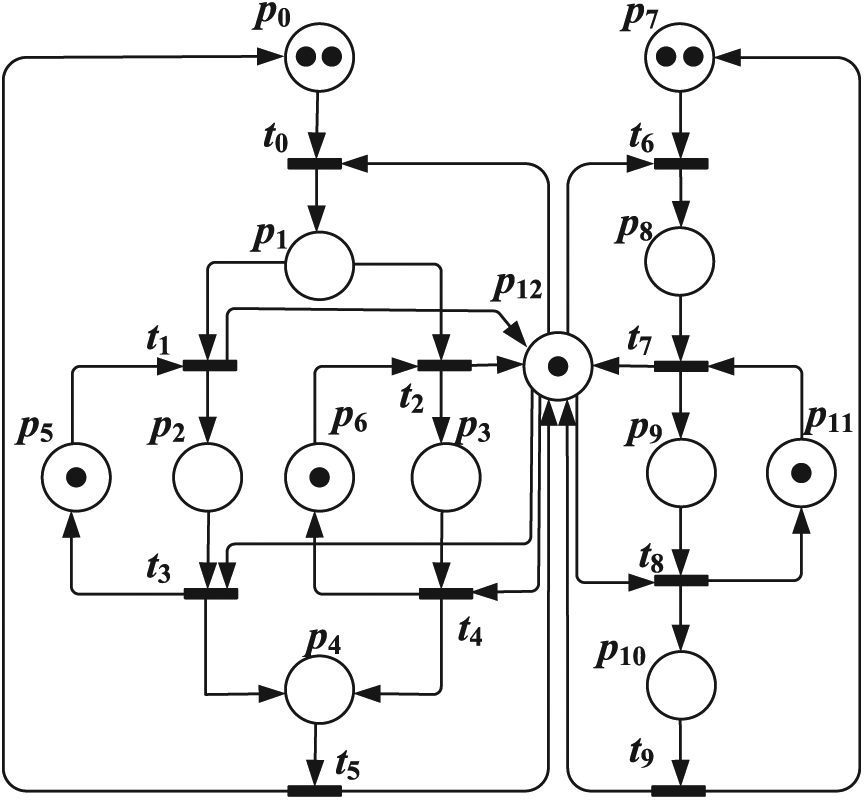
Zhang and Uzam 19 discover a set covering problem and obtain two control transitions to solve the deadlock problem of this example. They also use two same transition-based controllers to make the system deadlock-free. However, in example 2, in fact, according to our study in this article, there should be 34 reachable markings including 6 deadlock markings (shown in Table 6) when the idle places (p0, p7) are equal to (3, 2). Furthermore, saturated number of tokens in idle places for example 2 should be (3, 2). Please note that the six deadlock markings are checked by famous software TINA. 30 Due to the limitation of paper space, we just show the property of the 6 deadlock markings.
The properties of six deadlock markings checked by TINA in example 2.
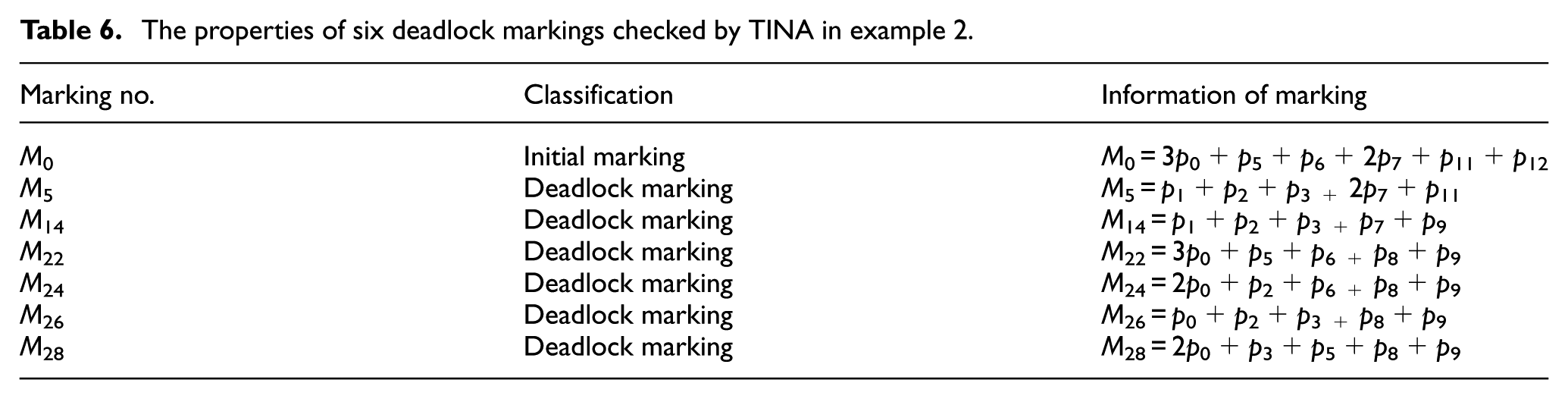
Finally, two controllers (I(t13) = p8+p9, O(t13) = 2p7+p11+p12, and I(t14) = p1+p2+p3, O(t14) = 3p0+p5+p6+p12) are hence obtained under the proposed Deadlock Prevention Policy II, and all 34 reachable markings are recovered when the two controllers are added into example 2.
Conclusion
In the existing literature, almost all researches adopt place-based deadlock prevention method to solve the FMS deadlock problem. However, they cannot obtain real maximally permissive controllers since some bad and deadlock markings could not be recovered in the process of controlling FMS. Based on above reason, this research presents one novel deadlock recovery policy using transition-based technology. The proposed policy is obvious better than all existing literatures even all publishing transition-based deadlock prevention policies. Moreover, the proposed policy not only obtains maximally permissive controllers but also recovers all original deadlock markings. Preciously, we can make all markings alive whatever they initially belong to deadlock or illegal ones. In other words, this work is the innovation in deadlock prevention domain. In future works, we will use the proposed policy to test all kinds of FMS or a larger PNM.
Footnotes
Handling Editor: Artde Lin
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.


