Abstract
Wireless sensor networks (WSNs) are very prone to ongoing security threats due to its resource constraints and unprotected transmission medium. WSN contains hundreds and thousands of resource-constrained and self-organized sensor nodes. These sensor nodes are usually organized in a distributed manner; thus, it permits the creation of an ad hoc network without predefined infrastructure or centralized management. As WSNs are going to get control of real-time applications, where a malicious activity can cause serious damage, the inherent challenge is to fortify the security enforcement in these networks. As a solution, software-defined network (SDN) has come out and has been merged with WSN to form what is known as software-defined wireless sensor network (SDWSN). SDWSN has come into existence, and it legitimizes network operators with more flexibility and control over the network. SDWSN has more tightened the security enforcement based on the global view and centralized control of the network topology. Moreover, machine learning (ML)–based and deep learning (DL)–based network intrusion detection systems (NIDS) have been introduced to the SDN environment to protect the networks against anomaly threats. In this review article, we illustrated the SDN–based security approaches to WSN followed by its architectures, advantages, and possible security threats. Finally, ML/DL–based NIDS integrated with the SDN controller is proposed as a complete solution for the WSN environment to confront the ongoing anomaly threats and to sufficiently protect the network against both known and unknown attacks.
Keywords
Introduction
Wireless sensor network (WSN) is the accumulation of several wireless devices (nodes) used to deploy in different applications for information monitoring or control applications. The WSN was primarily proposed for the areas where wired network was not possible due to nodes’ mobility or for infrastructure-lacking environment. It comprises hundreds and thousands of resource-constrained and self-organized sensor nodes. The dispersed nature of these sensor nodes allows the institution of an ad hoc network, 1 which does not adapt to any fixed infrastructure or centralized management. Numerous applications of WSN have been emerged, particularly for monitoring 2 and tracking 3 purpose. Several challenges arise while managing these highly distributed and dynamic networks. Especially, due to the dynamic nature of topology, the networks are more vulnerable to different types of threats. Moreover, the nature of communication is unprotected and unsafe inside WSN due to its limited processing capacities.4,5 There may be higher chances of security attacks to such networks. As WSNs are very prone to security attacks, security is one of the top concerns in this domain.
Several methods have been researched and built up to solve these challenges in WSN; some of these methods revolve around the concept of software-defined network (SDN). SDN is a new paradigm shift in networking architecture.6–8 The concept is simply based on separating the control and data plane. The network routes are determined by the control plane, and the data plane is simply given to forward the network packets. 9
Some efforts have been made to apply the concept of SDN to WSN called software-defined wireless sensor network (SDWSN). SDWSN brings the management flexibility and programmability to the network. 10 Integration of SDN provides module-based functionalities to the controller where the functionality can be added or removed according to application requirements. Due to its tremendous advantages for the sensor-based networks, SDWSN is being constantly researched and developed.10,11 Several management approaches for WSN have been proposed in the last few years.12,13 However, it is still not freed from security challenges and faced a multitude of security challenges inherited from both SDN and WSN, 14 which has become a bottleneck in its operations and applicability. However, there has been a little emphasis on how SDN may improve the security issues in WSN environment. 15
SDN features are facilitating innovative applications, dictating a new networking paradigm capable of implementing network intrusion detection systems (NIDSs). 16 Furthermore, machine learning (ML) and deep learning (DL) approaches can be used in NIDS integrated with SDN controllers to enhance network monitoring and security. 17 The attackers always try to generate new form of attacks that cannot be detected by signature-based intrusion detection schemes. To tackle with these anomaly threats, ML- and DL-based trained model is the sole manner to identify these unknown threats based on the previous data knowledge.18–20 It has also been argued that ML/DL-based NIDS provides more satisfactory results to protect the SDNs against anomaly threats.16,21,22
In this follow-up article, first, we briefly presented the concept of WSN, SDN, and its combined approach called SDWSN. Different types of SDN-based approaches are given by following its architectures and benefits to the WSN environment, from a security perspective. The possible security challenges in both SDN and WSN, which are transferable to SDWSN, have also been identified. In addition, the possibility of security threats to SDWSN is highlighted in detail. As a solution, ML/DL-based NIDS has been proposed to completely secure the SDWSN against different anomaly-based attacks. Finally, the current research gap is introduced along with future research directions to catch the attention of researcher in this highly demanded area.
The remainder of this article has been organized as follows: the concept of SDN and WSN followed by a discussion of network softwarization for wireless network environment has been introduced in “Wireless network softwarization” section. The current possible security threats and challenges to the SDWSN have been presented in “Security threats and challenges to SDWSN” section. In “Network intrusion detection system” section, the ML/DL concept is given along with its integration to NIDS for SDN platform. “Research issues and future work” section proposes ML/DL-based NIDS to completely secure the SDWSN and also highlights the current security loopholes in the proposed system along with future research directions, and the article is concluded in “Conclusion” section.
Wireless network softwarization
The concept of wireless network sofwarization has been planned with an architecture featuring a clean-cut separation between a data and a control plane. The architecture was realized by considering several limitations in WSN—the limtations, including resource underutilization, that are rigid to policy changes, hard to manage, and so on. In this section, we first discussed the concept of SDN, WSN, and SDWSN in details, and then briefly presented the SDN-based solutions that are presently being used for WSNs.
Software-defined network
Traffic control and packet forwarding remained the principle focal point of every networking device. Traditionally, each networking device first takes routing decision by consulting stored information of the topology and then performs packet forwarding according to a configured protocol mechanism. All the traditional devices running on the same concept build the information first on its routing table. The routing table acts as a feedback provider and packet routing decisions are made based on this structured data. The finalized rules are inserted by the controller to the network switch using OpenFlow protocol. 23 With the increasing data traffic, sensor nodes faced a lot of challenges in terms of energy consumption, limited power source, delay tolerance, and topology management.24–26 Several methods are proposed for energy efficiency, delay and fault tolerance, and scalability issues.24,27,28 But the notable point is that the traditional network equipment performs dual jobs: controlling and forwarding. The node consumes most of the resources in decision-making process. It is an effort-demanding task to manage dense networks and become extremely difficult in case of any fault occurrence to track the desired one. The dramatic increase in Internet traffic demands for efficient resource utilization. However, network design is also proposed for efficient management. 29 But the main hurdle is the combination of the control plane and data plane residing at the same device as shown in Figure 1(a).

SDN controlled switch versus traditional network switch.
SDN 30 concept proposed to provide the solution by splitting the control plane from the data plane is shown in Figure 1(b). Networking devices are used to control virtually from a centralized software which is called control layer, while the data traveling process is performed by the device itself. SDN is a paradigm shift 31 to shape the limitation of current network infrastructure. Separation of control logic and data logic of underlying network devices is performed first, and then the device is dedicated for forwarding plane in the second phase. It simplifies the device to obtain the instruction from the virtual controller rather to take intelligent decision by itself. The controller work as a central policy management system to manage a range of control function for the whole network. In first generation, the SDN was based on OpenFlow; 23 currently, it is being kept up by the Open Network Foundation (ONF). 32 A high-level architecture overview for SDN is shown in Figure 2.
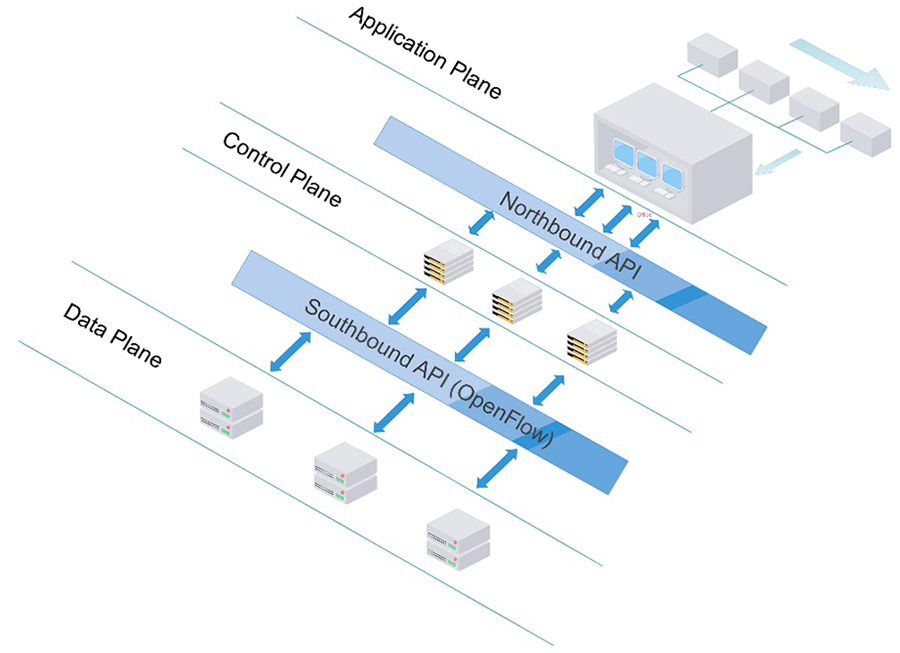
SDN architecture.
The SDN architecture mainly consists of three layers: application, control, and data forwarding. The application layer is dedicated for operators to monitor and configure the network in an abstract way. It consists of application services, interacting with controller switch through the northbound interface. The control switch consists of one or a combination of controllers (e.g. Open Network Operating System (ONOS) 33 and OpenDayLight), which keeps the network in a virtual dynamic form. Controller switch exists in the middle and listens to the user request to convey with the physical network via southbound interfaces (e.g. ForSA, 34 OpenFlow, and ForCES). 35 SDN controller is simply like a software entity that receives abstract knowledge about data plane resources. SDN controller can be deployed same as a software element on any number of physical device, and distributed elements are necessary to synchronize at peak and keep a flexible aspect of data.
The significant result of SDN principles is the break-up of data commands and data flow in the middle of network procedure in switch. This leads to better monitoring and flexible management, divides the network fault into traceable pieces, makes the network more dynamic, and simplifies the evolution of network. SDN got interest from both academia and industry for its notable compatibility to provide a common platform for heterogeneous networks. 36
Wireless sensor network
WSN are the sensor node networks deployed in various areas like atmosphere monitoring, 37 working environment monitoring, 38 industrial process monitoring, 39 and health care monitoring. 40 Each node has three main physical components: radio (for signaling), power source (battery), and micro-controller (for processing). These networks consist of small individual sensors cooperatively pass data through hopes to its sink or controller for further processing and acting. A sensor node can be stable or moving, aware of its location or not. The sink node is considered as a controller for its local network to perform desired operations. There are two types of sink node in WSN, single sink and multiple sink as shown in Figure 3.

Sink node–based topology of WSN.
Single sink mode has scalability issue. With the increase in network size, the single sink node might become overloaded to handle the heavy data traffic. It also has delay-tolerant issue, and in case of any fault occurrence, the whole network might be unavailable. The multiple sink mode ensures better performance for a network. It overcomes the single mode limitations by increasing the probability of delivery if one path unavailable the other may active.
WSN got interest for its simplicity of deployment and cost-effectiveness. However, it has a little measure of resource particular of memory and processing capacities. A better management is a difficult task due to its resource constraints. Nevertheless, the usage of WSN increases and is adopted on a large scale with thousands of sensors working cooperatively for different tasks. From the future perspective, it will be in millions. Table 1 provides some WSN technology implementation in different applications.
WSN technologies in various applications.

PIR: passive infrared; IR: infrared.
The above table shows that WSN is not limited to specific applications, but take place in almost all major areas of our life. The Internet has billions of interconnected devices over the world. These devices share the information among each other in the form of digital packets. Different networking protocols are designed for communication among them. 43 Sometimes, in a same network, the devices may exist in sparse mode. Network protocol and policy for on-the-fly network is a major challenge. Network management is also complicated when it comes to large quantities of devices. As sensor node has constraints of memory size and processing capability, such flexible managing system is required to relieve the individual device from overhead of complex routing. The concept of SDN has been introduced to sensor networks with the realization that all these low-powered devices should be managed from a central entity in a bidirectional way to use the resource allocation in well manner. 44 SDN is going to emerge as the future of networking by offering simplicity, security, flexibility, scalability, and innovation over the traditional network model. SDN separates the control plane from data plane and keeps the control plane centrally from where the network nodes control remotely. The routing decisions are made by controller and insert the rules to the SDN switch to route the nodes’ packet. SDN reserves the resources of individual node for forwarding purpose. The whole network can be overlooked from controller in an abstract way. The best route is determined by the controller by considering the whole topology.
Software-defined wireless sensor network
The SDN paradigm has been merged with the WSN to form what is known as SDWSN, 10 shown in Figure 4. SDN provides the control part of the network to the application end; thus, a complex network can be centrally managed. Also, it provides an energy-efficient solution to WSN. 46 The sensor nodes may have deployed in areas where physical access might not be easy and where the device runs at low-powered battery which may not have any renewable energy source. Traditionally, running complex protocols and high computational task is not possible for these low-powered node. SDN provides a broad model to overcome these issues, and above all, it is also very reliable from a security perspective. It is obvious that these tremendous features are highly desirable for WSN nodes. There are many approaches designed47,48 to implement the SDN concept for WSN. The WSN devices usually seem application specific which creates the need to design a common framework for SDN. It is also necessary to integrate different vendors with different devices for better deployment. For example, when a node is hijacked, the controller may notify to direct the traffic to the NIDS 49 for further analysis.

SDWSN architecture. 45
SDN benefits appropriate for WSN include, but are not limited to, the following:
SDN for energy efficiency of WSN: energy consumption is an increasing trend, mainly for IoT (Internet of Things) appliance. Several methods have been proposed for better energy efficiency of low-powered devices. The energy constraints affect the performance of the whole network. SDN relieves the individual nodes to save its energy considerably. 46 In traditional network, the node consumes most of its energy in the decision-making process. In the SDN environment, the controller takes the path determination responsibility while the node just consumes the energy for forwarding process. As a result, traffic management, quality of service, and resource allocation can be achieved with lower energy overhead.
SDN for dynamic topology network: in an MANET (mobile ad hoc networks), a VANET (vehicular ad hoc networks), or an FANET (flying ad-hoc networks) scenario, the node appears and disappears simultaneously in the network. At the same time, the multiple node may appear or disappear, which results in dynamic nature of topology. With SDN, the controller can modify or append policy on the fly, but it may generate a lot of control packets exchange between the ordinary nodes and the control plane. This may lead to additional energy consumption. a fuzzy logic–based solution, called Fuzzy Topology Discovery Protocol (FTDP) is proposed 50 to make the SDN-based WSN more efficient by increasing lifetime of network and decreasing the packet loss.
SDN for network management: network management is more challenging in case of IoT scenario. Normally, different vendor’s devices are implemented with different applications to realize the heterogeneous network. Furthermore, this complex network sub-splits up into software heterogeneous, which focuses on the use of different wireless hardware, and hardware heterogeneous, which focuses on the use of multi-protocols and standards. SDN-based cross layer architecture provides the support to communicate between different devices and protocols. 51 The usage of different vendor components makes the management process more complicated. The cost of managing WSN is relatively high, and tracing the specific fault by physically locating individual component is an additional effort. Therefore, SDN offers the most appropriate approach to reduce the administration effort and cost.
SDN for routing protocol: routing mechanism can be highly improved in OpenFlow-based SDWSN. A new OpenFlow-based hybrid routing protocol is proposed for wireless environment, which runs faster and is able to run independently in case of controller failure. 16 The routing protocol integrated with SDN has outperformed the traditional protocols in terms of death node number, network lifetime, and, more specifically, the better transmission rate.
SDN-based architectures for WSN
Some of the notable, proposed architectures for using SDN in WSN are as follows:
SDWSN:
SDN was essentially proposed for wired network and the OpenFlow protocol did not possess the capacity to fulfill WSN requirement. Therefore, with some modifications, a new protocol called Sensor OpenFlow was proposed, which is the core component of SDWSN. 52 Sensor OpenFlow was the first approach to consider the technical challenges of WSN. It enabled the communication between control plane and data plane in the context of WSN. It also made the resource-constrained device configurable via high-level programming language. The architecture considered the possible challenges and offered fruitful features. SDN was designed with the assumption that underlying network is composed of high-speed switches such as Ethernet/MPLS (multiprotocol label switching) switches and IP (Internet protocol) routers. Therefore, it represents significant challenges while designing for WSN:
Creating flow which should be data centric in WSN. Whereas in actual (wired), OpenFlow is address centric. Therefore, attribute-based scheme should be implemented.
Sensor OpenFlow controls the channel which is based on end-to-end connection in OpenFlow. However, it should provide TCP/IP (transmission control protocol/Internet protocol) connectivity.
Traffic overhead tends to be large in sensor network due to the dynamic nature of WSN.
Sensor always generates continuous data traffic.
Data aggregation should be performed on sensor node to reduce the data redundancy.
The above-identified challenges have been resolved with a suite of preliminary solutions, which are as follows:
Two optional cases are presented: the first case is to redefine a flow table (non-IP scheme) using predefined addressing scheme. For this purpose, OpenFlow extendible Match (OXM) field is used to match the flow. Furthermore, two new features are added, OXM-SOF-SRC and OXM-SOF-DST, for source and destination matching purpose, respectively. The second case is to augment WSN with IP address for which IPv4 and IPv6 stack are recommended.
Two solutions for control plane: if non-IP solution is chosen by operator, then channel can offer at the top of transport protocols. Otherwise, channel would be self-supplied in case of IP base solution. The addresses scheme was generally unavailable in WSN, which is addressed by SDWSN to ensure orderly message delivery by deploying TCP-IP stack.
The control traffic mainly comprises packet-in and packet-out. When an unknown packet received by sensor node, it generates packet-in (lookup request) toward controller. The controller sends back a packet-out (response) toward sensor node for its query. Hence, in case of multi sensors, multiple request would generate from different sensors simultaneously, which may result in traffic overhead. To tackle with this issue, SDWSN presents a mechanism, that is, once a packet-in is generated by a node, all any other packets will be withdrawn by nodes having same destination address until the corresponding packet-out is received.
To reduce traffic overhead, the packet-in (a flow request to controller) is only sent until the corresponding packet-out (response from controller) is received.
SDWSN presents a mechanism to control the continuous data generation by maintaining the sensor node in different states. For instance, in blocking state, the node would have to synchronously wait until the sensory data become available, and round-ribbon has to periodically check if the sensory data are available.
Data aggregation module is implemented by SDWSN to perform in-network processing if needed when the new data are received and then to send it to flow table. Data aggregation can be obtained via standard operators such as mean, mode, min, and max. The aggregated flows can be managed in flow table but they remained an open issue for researchers.
2. Tiny SDN:
SDWSN does not support the characteristics of interruption, smaller link frame, and communication delay in WSN. Furthermore, in a traditional sensor device, just one radio module exists, which performs transmission and receiving at certain frequency in a specific time. Therefore, the control packet and data packet travel on same path (a feature known as in-band control).
TinySDN 53 was proposed to deploy SDN paradigm in WSN by running multiple small controllers within the network. It makes the sensor node to be able to support SDN paradigm, and the sensor node now can work as a node and an SDN switch as well. The communication standard IEEE 802.15.4 54 (which is being currently used) had very limited bandwidth, which often results in network overhead. The solution is achieved by placing multiple controllers in the network, one of them work as sink per area to further simplify the network. Thus, the network overhead has been significantly reduced. SDN sensor node and SDN sensor controller are the core components of proposed architecture.
SDN node consists of the followings:
Application layer (generate data and place on API) for which it uses TinyOS, 53
Controller within sensor node to check whether the incoming packet matches the flow table,
ActiveMessageC which ensures the sensor node communication with radio module.
SDN controller node consists of the followings:
Sensor mote module which works as a communication enabler between sensor network and the central controller,
Control server which holds the control logic of the network and injects rules via mote to the physical network.
For network topology discovery, the TinySDN uses Collection Tree Protocol, 55 a well-known route discovery protocol for WSN. TCP collects data from one or more nodes and sends to one or more root nodes. The support of multiple root controllers and hardware independence are the prominent features of this scheme.
3. SDN-WISE:
SDN-WISE was the first attempt to create node environment that can support SDN functionalities. The node would take forwarding decision without querying controller when the information is locally available. This tremendous feature is enabled by network function virtualization (NFV) in sensor node and thus it can considerably reduce the network overhead. The node executes a trusted firmware that has full control on node peripheral. This firmware is responsible to restrict node execution behavior according to instruction directed by trusted platform module (TPM). TPM ensures the node current context and instructs accordingly. For instance, Apple proposed 56 a solution to disable all the recording functionalities of smart phone in prohibited area.
SDN-WISE architecture 56 was presented with the following objectives:
To enhance the existing solution functionalities,
To control the network traffic flow in more flexible way,
To control duty cycle of nodes via SDN controller,
To increase energy efficiency of sensor node,
To provide API on node side for information access,
To enable virtualization on node side for geographic routing, and
To support on-the-spot operation on node side to behave according to the context.
The topology discovery protocol also runs on node side to gather neighbor nodes information and build a path toward controller. The packet contains the identity of node/sink, current battery level, and distance from the node to sink or sink to controller. The generated information is use to deliver to the controller for topology making and best path determination. The network overhead problem has been solved by introducing geographic routing feature, 57 which reduces the signaling overhead and flow entries the table has to sustain. A new type of packet format has been introduced for this geographic routing feature. In geographic routing, the node relays the incoming packet to its connected neighbor which is near to destination.
ONOS 33 is the core component of the framework for all these functionalities. It is an open source network operating system for SDN. ONOS is extended for SDN architecture which consists of Northbound, Distributed Core, and Southbound. Northbound API has concern with end user and provides access to SDN-WISE’s services, which is independent of hardware characteristic. The Distributed Core relies between Northbound and Southbound APIs which host computational services, for example, context discovery, topology discovery, best path planning, and rule identification. Southbound lies between physical network and Core Distributing. Southbound provides higher layer of resource-supported services, for example, layer 2 packet format and sensor-generated data format.
SDN-WISE is a comprehensive architecture for resource-constrained networks. It enabled visualization functionalities by leveraging operating system, which can further have used to implement any function in the network like geographic routing. The second accomplishment is that the node can be regulated via TPM mechanism to behave in the network context accordingly. Thus, SDN-WISE is the most appropriate solution for future wireless sensor networking whose behavior can be limited to comply with current setting. The overview and detailed comparison for different SDN based WSN architectures have been presented in Table 2.
Overview and comparison of SDN-based WSN architectures.

SDN: software-defined network; WSN: wireless sensor network; SDWSN: software-defined wireless sensor network; TCP/IP: transmission control protocol/Internet protocol; CTP: collection tree protocol; ONOS: open network operating system; NFV: network function virtualization; TPM: trusted platform module.
Security threats and challenges to SDWSN
Security is one of the top concerns in WSN. A new network paradigm of trust, security, and privacy is required to address the possible threats to the wireless networks. Consequently, SDN provides an efficient, reliable, and flexible network management solution. OpenFlow is the most commonly used protocol for communication between controller and switches, which defines control messages to enable secure communication path. Moreover, OpenFlow enables fast response to security threats and the flow rules (forwarding decisions). Using OpenFlow, the network switches can be dynamically modified in order to adapt to different network changes.
SDN has been merged with WSN to control and manage highly densified sensor networks. Although it has achieved greater efficiency and sustainable heterogeneity in the WSN, 58 the security challenges inherited from both SDN and WSN are combined in SDWSN. In this section, we first presented the possible threats to SDN and WSN separately and then reviewed security advantages and challenges brought by SDN to WSN environment.
Security in SDN
Although SDN offers numerous advantages for securing networks, it also raises questions about new vulnerabilities. 6 SDN itself is intended to introduce new security mechanisms that were not previously possible. It might detect the attacks in an easier and reliable way, but also increase the attack surface. 59 There are opposite opinions that security problems in SDN are manageable or even more complex to properly secure. 60 For example, inconsistencies of network policies can be ensured with centralization, but the central controller is single point of failure and the attacker may able to gain entire view of the network from a single location. Attacks against SDN controllers and the introduction of malicious controller apps are probably the most severe threats to SDN. 61 The possible security threats to the SDN environment are as highlighted below:
Attack by host and switch: when a malicious data packet does not match by flow regulation at the switch, the switch immediately transmits it to the controller. The processing of malicious packet creates opportunity for the malicious hosts to take over the network access. Second, in case DoS/DDoS (denial of service/distributed denial of service) attack, 62 the controller might be resulted in failure of the whole network. Finally, the flow rules information can be captured from the switch via side channel attacking techniques. 63
Network topology: the controller builds up its topology record by looking at the topology protocol’s packet, for example, LLDP (Link Layer Discovery Protocol), IGMP (Internet Group Management Protocol), and ARP (Address Resolution Protocol) generated by the switches. There are possibilities of spoofing these packets by malicious hosts, which can result in network topology corruption and illegitimate flow rules to the switch.
Data plane forwarding: malicious hosts try to consume the resources of controller and switches by generating DoS/DDoS attacks in the network.
The FS-OpenSecurity 64 model is a protocol-independent defense framework, which addresses the above challenges and prevents attacks on all three planes in the SDN platform. Moreover, SDN network can be protected against different types of known vulnerabilities using rosemary 64 and the security can be more strengthened with range of frameworks,15,65–68 but the common drawback is that all these cannot work against unknown threats.
Security in WSN
WSNs are more vulnerable to a range of security threats due to resource limitations and physical exposure of sensor devices. The networks are often deployed in a publicly accessible environment and lack the computational resource availability. In general, the attacks can be broadly categorized into goal oriented, performance oriented, and layer oriented.69,70 Active and passive attack are the types of goal oriented. In passive attacks, the malicious host monitors network activity without any privileged access; in active attacks, the attacker uses passively generated information against the network to obtain admission. Outside and inside attacks are the types of performance oriented. The outside attacks are where the attacker monitors transmission medium and tries to inject false data to cause failure in the network. In the inside attack, the intruder tries to get privileges as a legitimate user and then tries to launch their desired attacks. The outside or inside attacks boundaries are not so clear and easy, as they often cause similar behavior. Therefore, we discussed the attack types for individual layer. Finally, the layer-oriented attacks target various layers of the network stack. 71
Physical layer: the lowest layer where the packets are transmitted in the form of signals. The signals are wirelessly broadcasted, which makes it more susceptible to range of attacks such as eavesdropping, jamming, and hardware hacking.
Data link layer: it offers a shared access to the medium for nodes, also check for transmission errors. Jamming and collision attacks can be launched against this layer.
Network layer: it creates a routing path for node communication where a malicious node access in the network can cause a broad range of internal attacks. Spoofing, replaying, and selective forwarding are the common attacks for this layer.
Transport layer: if offers the end-to-end reliability to the data transmission. The data can be compromised during transmission by altering the content or injecting false data.
Application layer: it deals with the end user and is susceptible to application bugs or range of malware attacks.
Multilayer attacks: it can be the combination of previously defined attacks residing on different layers to target the WSN protocol. DoS and man in the middle attacks are the well-known example.
A considerable consideration has been given to WSN protocols to satisfy the communication needs of diverse applications.72,73 Although the sensor node resources can be used with kind of lightweight protocols, it cannot fulfill the diverse range of security requirements for each layer. 71 For example, physical and media access control (MAC) layer security is based on cryptographic algorithms, network layer security is based on identity authentication, and the transport layer required two-way authentication scheme. Neither WSN protocols have been designed with the security goal in mind, nor it can fulfill the security demand of individual layer. Therefore, it is highly desirable to take the security requirements into account as a whole and design an appropriate solution.
Security in SDWSN
SDN approaches toward WSN resulted to form a new paradigm called SDWSN. 14 In SDWSN, the control logic is used to handle a central controller, and the sensor node is dedicated for packet forwarding purpose. Many problems have been resolved using this approach in terms of sustainability and interoperability in WSNs. Especially, this new paradigm presents many advantages while considering security in WSN.
The centralized programmable control plane resulted in centralized security management. The security policy configuration of two to seven layers can be centrally controlled. The required changes can be made effectively based on the abstract view of the entire network. Also, it frees up the sensor node resources significantly. As a result, it allows the implementation of effective security algorithms in the WSNs. Moreover, the abstract view of network speeds up the process of malicious activity identification. The most significant characteristic is that sensor node is only committed to taking control commands from the controller and hence it cannot be used for malicious purpose. Nevertheless, it is possible to use it as a gateway for other nodes.
The use of SDN is gaining high momentum and has been widely adopted by security research communities. The Flowvisor 74 framework offers security feature on top of the controller to verify each incoming/outgoing connection according to predefined security policies. By doing so, the malicious traffic generated by cybercriminals can be blocked using access list. Moreover, several strategies have been used to timely detect DDoS attacks in a centralized manner.75,76 The network programmability feature of SDN controller increased the deployment of security applications and also provided several advantages to extend the network functionalities. 77
The dynamic updates of flow rules are the key feature of SDN, which raise the challenges of appropriate security mechanism in network applications. Therefore, various SDN-based security functions such as firewall and IDS/IPS (intrusion detection system/intrusion prevention system) have been designed and implemented. 78 Moreover, the SDN-based flow management feature is extremely important where the objects communicate more frequently, for example, industrial control system (ICS). An IDS has been positioned to analyze traffic flow of the sensitive or unknown traffic stream in the network. 79
The WSN devices are susceptible to range of attacks, especially due to open radio access and the plain text of metadata. The SDN can bring the advantages of protection and reconfiguration to these devices. Founded on these motivations, a computational framework is suggested to offer a program to control and secure information exchanges for devices in an ad hoc network. 80 The cluster-based mechanism is used in the proposed system, where each cluster has a cluster head to control the devices in its own cluster. The cluster heads are also able to communicate with each other and with the controller via an inter-domain link. In addition, a dynamic firewall is attached with each cluster head to monitor the network traffic for malicious activities.
A hierarchical framework is offered for the WSN environment, which improves the security in the network by taking low complexity and high security requirements into account. 81 The framework of the proposed system consists of low level and high level of attack detection. The sensor node has simple rules installed to perform low-level detection. Sensor node reports the sink node in case of unknown event occurrence. High-level detection is performed on sink node, programmed with complex rules. Grounded along the high-level rules, the sink node determines whether the event is suspected to malicious user or normal. The role of the SDN controller in the framework is to generate the current probabilities for the attacks. It performs the attack mitigation based on the topology and vulnerability information from the network. The scheme resulted in better feasibility and efficiency.
However, SDN offered considerable security features and architectures to WSN environment, but it is not free from security challenges. SDWSN is more vulnerable to security attacks due to lack of major security components like middleware and transport layer security (TLS). 82 The centralized controller also poses a single point of failure and is also prone to DoS and intrusion attacks. However, efforts have been to mitigate the possible attacks in SDWSN but not completely mitigated. 82 Some threats can be adopted from SDN and WSN. The threats which are inherited from SDN are forged traffic flow, forwarding device attacks, DoS attack against control plane, and lack of trust between controller and management applications. 83
In after mentioning work, the security issues have been carefully considered and resolved considerably. But all of the existing approaches are designed for well-known attacks and are still unable to respond to unknown threats. So it can be argued that all these methods are even prone to anomaly threats and thus are not the perfect security solutions.
Network intrusion detection system
In the response to increasing cyber-attacks, NIDS has been one of the top concerns among research communities. Detection and protection against cyber-attacks at early stage is on the focused issue. NIDS is used to detect intending activities trying to get unauthorized access or creating network failure by generating malicious traffic. Abnormality detection speed, accuracy, and reliability are the common factors on which the performance and success rate of an NIDS can be quantified. Effort has been made to improve the detection accuracy based on ML techniques. 84 And DL has likewise been adopted 18 as an advanced stream of ML. The recent approaches focus on the deployment of ML-based NIDS to the SDN environment. 16 Hence, the network monitoring and security can be advanced by implementing ML approaches into the SDN environment.
Research work has been done for the integration of DL approaches with NIDS. A deep neural network is made to classify the characteristics of normal and abnormal traffic, and integrated this anomaly detection algorithm into OpenFlow switch using a controller. 16 In addition, a DDoS detection system is proposed, which comprises three different modules implemented on the top of the controller. 85 The DL model is further used to extract the features from the traffic and perform real-time classification task.
The performance of algorithms in NIDS can be compared based on performance metrics. The metrics includes accuracy, false negative rate (FNR), false positive rate (FPR), time used, and memory consumption. The detection is always performed based on two common techniques called signature and anomalies based. The signature-based techniques are based on predefined set of rules. The signatures are used to store into the database where it checks for the packets known to be malicious. The disadvantage is that it requires detailed knowledge of each attack pattern and is not capable of discovering new types of attacks on its own. Unlike the signature-based techniques, the anomaly-based IDS is event driven. First, it defines the normal network and then continuously monitors the activities inside the network. If it finds any activity differs from normal behavior, then it marks the event susceptible. A comparison of these two methods is presented in Table 3, based on different performance metrics.
Comparison of detection method.
ML/DL in NIDS
ML is used to create a trained model by implicitly identifying hidden pattern from the data. 86 The trained model is used for further data analysis. ML-based techniques resulted in improved performance of autonomous systems in terms of better detection rate and decreased computation cost as well. 87 There are three types of ML techniques called supervised, unsupervised, and semi-supervised learning. 88
In supervised learning, the algorithm predicts unknown data based on defined input labels. In intrusion detection systems, support vector machine (SVM) and random forest are being widely applied for classification and regression problems, respectively. These both algorithms are preferred due to its better classification power and practicality in computation. 86
In unsupervised learning technique, the algorithms model the underlying structure or distribution in the data in order to find out more about the data. The example of unsupervised learning includes clustering (self-organizing map (SOM)) and feature reduction (principal component analysis). These are used to speed up the unlabeled feature learning process. 89 Also, these have been used for feature selection before classification. 90 Moreover, SOM has been used for payload size reduction in NIDS. 91
Semi-supervised learning is the combination of both supervised and unsupervised learning that uses both labeled and unlabeled data, usually mostly unlabeled. Two semi-supervised-based approaches called Spectral Graph Transducer and Gaussian Fields are used for anomaly detection. One semi-supervised clustering method called metric pairwise constrained K-means (MPCK-means) is used to improve the performance of the detection system. 92 In addition, the accuracy of NIDS has been improved via semi-supervised SVM. 93
ML/DL-based NIDS in SDN
ML-based intrusion detection systems in SDN environment provide better security enforcement. The abstract view of network provides a better chance to strengthen the network security. A block diagram of intrusion detection system in the SDN architecture is shown in Figure 5. DL algorithms are the advanced approach that permits the systems to learn the data with various levels of generalization. It has been applied to intrusion detection and many other domains. 94 Table 4 presents an overview of methods and usage of different DL approaches used for NIDS in SDN.

NIDS in SDN environment.
DL-based approaches for NIDS in SDN environment.
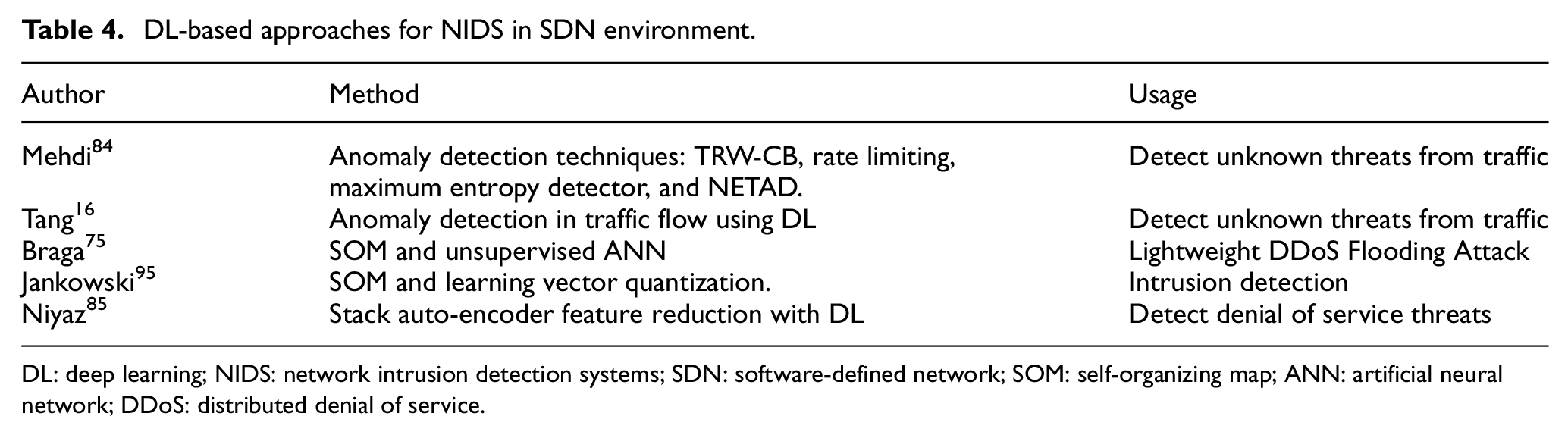
DL: deep learning; NIDS: network intrusion detection systems; SDN: software-defined network; SOM: self-organizing map; ANN: artificial neural network; DDoS: distributed denial of service.
It can be seen that DL techniques are gaining more interest by research community compared to ML. It performed better than ML techniques when applied to classification problems in SDN. 85 It takes more inputs to form an output that results in better finding correlation in the data. So it is more adaptable method for advance intrusion detection techniques. 86 As most of the attacks are unknown to systems, unsupervised learning algorithms are the only feasible solution to undertake. Therefore, recurrent neural network (RNN)-based 96 and hybrid-based algorithms 97 would be the finest solutions for NIDS implementation in SDN platform.
Research issues and future work
An intelligent threat detection system is highly desirable but is less explored in WSN domain. Developing an exhaustive detection solution is highly demanded, which can endure the continuing anomaly threats in the WSN. According to the research work on ML/DL-based intrusion detection system in the SDN environment, it can be arguing that detection accuracy has significantly improved. Hence, it would be the finest solution to implement this ML/DL-based NIDS approach to the SDWSN. By doing so, each controller would have an NIDS attached to continuously monitor the traffic behavior at bottom level. In large distributed environment, the network can be divided into clusters where each cluster head 80 would have an NIDS attached. Moreover, the detection capability should also be provided to the sensor node to some extent. In the development of targeted system, there are some challenges in developing flexible and efficient protection system for the WSN environment:
The ML/DL-based system is the only quick fix to confront the unknown threats in the network. However, the potent challenge is to use a proper feature selection method that can match the significance of features to intrusion detection and the excess between features. 81 Hence, it is a research challenge in ML/DL to determine the perfect number of model parameters and improve the computation practicality.
The efficient packet processing is the bottom-line challenge in the NIDS integrated with SDN controller.
The implementation of ML/DL-based NIDS with high volume of data is also a big challenge that needs to be addressed. 98
The SDN controller performance degradation is due to the control packets overhead in large networks. The integration of NIDS with SDN controller might increase the control packets for monitoring purpose, which will put more packets overhead on the controller. Therefore, to cut back the controller bottleneck and implement NIDS is another research challenge. 76
The sensor node has limited resources in terms of power and computational capabilities, which can be easily compromised and can be encountered to its own network for malicious actions. Therefore, effective and lightweight security algorithm is required to perform low-level detection in the network. In Wu et al., 81 a simple rule-based mechanism is used at the node level to detect some common attacks, but it cannot respond to anomaly threats. To completely address this issue, the controller needs to generate probabilities from the whole network behavior and distribute the dynamic rules to the end nodes in distributed manner.
Conclusion
In this review article, we briefly provided the concept of network softwarization, followed by its importance and security approaches toward sensor-based networks. It is stated that SDN has an integral role in overseeing and protecting the complex network particular to WSN. The role of SDN in the wireless network environment is shown along with its existing architectures, advantages, and research challenges. It has been argued that ML/DL-based NIDS is more appropriate solution to the SDN environment to keep the network protected against anomaly threats. Also, we introduced the research challenges associated with the ML/DL systems to NIDS. Ultimately, the ML/DL learning–based NIDS is proposed as a complete protection solution to the SDWSN platform to cope with growing anomaly threats.
Footnotes
Handling Editor: Mohsin Iftikhar
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work has supported by the Xiamen University Malaysia Research Fund (XMUMRF) (Grant No. XMUMRF/2019-C3/IECE/0007).
