Abstract
Wireless sensor networks play an important role in daily life and have been applied in diverse fields. In practice, malware tries to infect sensor nodes, while wireless sensor network prevents from attacking. This article establishes a new attack–defense game based on Stackelberg game. In this game, malware selects its strategy of attacking first, and then wireless sensor network makes decision after observing the action of malware. This game considers the situation in which malware is more dominant than wireless sensor network. Then this game is solved and an equilibrium solution is calculated, which is the best strategy for malware and wireless sensor network to maximize their payoffs. With infection probability and defense probability, mean time to failure of a sensor node is computed and is used to analyze the reliability of wireless sensor network. The experiments show the influence of true-positive rate and false-positive rate on the equilibrium solution of game and the reliability of wireless sensor network. Finally, the proposed method is compared with the existing method based on a simultaneous game.
Introduction
Wireless sensor networks (WSNs) are widely applied in different systems,1–3 for example, smart grid, 4 cooperative localization, 5 environmental monitoring, 6 and power system. 7 In the WSNs, sensor nodes gather,8,9 transmit,10,11 and fuse data.12–15 But limited energy and other factors limit the normal operation of WSNs. 16 A challenge in WSNs is to reduce communication and computational costs and ensure a high level of coverage 17 and connectivity. 18 In order to solve this problem and make the network work longer,19,20 many different methods have been studied. Some of these methods propose more reasonable energy management schemes,21–23 some study clustering schemes 24 , some research new topologies,25,26 and some study communication protocols.27,28 In addition, the uncertain factors such as uncertain environment also affect WSNs.29,30 These uncertainties are difficult to assess31–33 and cause the data collected by different sensor nodes to conflict with each other.34,35 In practice, WSNs are vulnerable to a variety of attacks. 36 Some methods are used to detect attacks 37 and reduce the impact of network failures. 38 Therefore, it is necessary to analyze the state of WSNs, and reliability is an important indicator for measuring the state of WSNs. 39 Many methods have been applied to analyze reliability, such as dependency assessment,33,40,41 Markov models,42,43 fuzzy evaluation, and game theoretic methods.44,45
When analyzing the reliability of WSNs, security is an important factor to consider. The attackers deliberately attack the vulnerable nodes in WSNs, while WSNs use intrusion detection systems (IDSs) to defend against the intrusion. Malware is an attacker that destroys the WSN through infection. Many extension models based on classical epidemiological models46–48 have been proposed to simulate the propagation of malware. These models describe the transition relationships between different states of sensor nodes and are used to evaluate the reliability of WSNs. In order to analyze reliability, it is necessary to calculate the probability that a node is infected. The successful infection probability is affected by the infection probability of malware and the defense probability of WSN. So it is determined by the strategies of malware and WSN. In adversarial decision making, game theory is used to find the optimal strategies for decision makers.49,50 It has been used in different fields51–54 to solve some decision-making problems. For WSNs, there are some studies based on game theory to solve some problems such as topology control, 55 resource allocation, 56 intrusion detection, 57 and data quality. 58 In addition, in order to maximize the lifetime, 59 games are used to control power60,61 and save energy.62,63 And some articles focus on the reliability of WSN, for example, a network game between router and attacker is formulated to analyze the reliability, 44 and evolutionary game theory is to used to establish the model. 64 In the attack–defense of malware and wireless networks, the game is established to predict the possible actions of malware and WSN. By solving the game, the best attack probability and defense probability are obtained.
In the existing attack–defense game, there are a simultaneous game and Stackelberg game.65,66 In the simultaneous game, both of the players are fair and make decision simultaneously. Stackelberg game is used to consider the situation, where someone in this game dominates and has the priority to decide its strategy. In the attack and defense of WSN and malware, there will be situations in which one of them dominates, and Stackelberg model can take it into account. In the existing Stackelberg game, WSN is the leader and attacker is the follower. The attacker makes its decision after knowing the strategy of WSN, so WSN dominates the game. However, in some cases, malware will have more initiative than WSN, and its decision will affect WSN. Unlike those methods, this article establishes a new attack–defense game based on Stackelberg game. In this game, malware is seen as the leader and WSN is the follower. When making decision, WSN has some information and knowledge about the known malware. According to the knowledge and perception about malware, WSN will predict the possible action of the opponent and then make its decision. For malware, the pessimistic situation is that the infection probability predicted by WSN is equal to its true strategy. To find the best infection probability of malware, a new game is established. In this game, malware moves first and WSN makes decision later after knowing the strategy of the leader. Comparing to WSN, malware is more dominant in this game. Through solving this game, the successful infection probability is calculated. Using the method proposed in Börcsök et al., 67 the mean time to failure (MTTF) of a sensor node is calculated. Then, according to the approach introduced in Shen et al., 45 the reliability of WSN is analyzed. The main work of this article is as follows:
Based on Stackelberg model, this article establishes a new attack–defense game. This game considers a situation in which malware is more influential than WSN. In this game, malware is the leader and WSN is regarded as the follower, and the strategy of malware affects the decision of WSN.
The proposed game model is compared with the simultaneous game. The results illustrate that the new game better reflects the real situations when making decisions, because the proposed game considers the influence of more relevant factors on their strategies. Through analyzing the expected payoff matrix, it can be found that the equilibrium strategy of the proposed game is better for WSN than the strategy of the simultaneous game.
Sufficient experimental results and analysis are given. And these results illustrate the effect of different factors on the infection probability, defense probability, and reliability of WSN. The conclusions and analysis also show that the experimental results of this method are consistent with the actual situation.
The rest of this article is organized as follows. In section “Stackelberg game,” the Stackelberg game is introduced. In section “A new attack–defense game,” a new attack–defense game based on Stackelberg game is established. In section “Stackelberg equilibrium of the proposed attack–defense game,” the proposed game is solved to find the equilibrium solution. Then in section “Analysis of reliability of a clustered WSN,” the method of computing MTTF and the method of analyzing the reliability of WSN are introduced briefly. In section “Experimental results,” some experimental results and conclusions are given. In section “Comparison with a simultaneous game–based reliability analysis approach,” the proposed method is compared with a simultaneous game–based reliability analysis approach. Finally, this article is concluded in section “Conclusion.”
Stackelberg game
The Stackelberg game is a strategic game in economics. The players of this game are two firms whose aim is to maximize their profit. Unlike the simultaneous game, in Stackelberg game the leader firm moves first and then the follower firm moves sequentially. The leader firm can be seen as a market leader whose decision influences the price and the output of the follower. In general, the price function for the duopoly industry, denoted as

The game is solved by backward induction. The leader firm considers the best response of the follower and then decides its output to maximize its profit. To calculate the equilibrium solution, the best response of the follower is considered first. When the output of the leader,

Set this equation to zero for maximization, and

The profit of the leader is modified as follows

The first partial derivative of
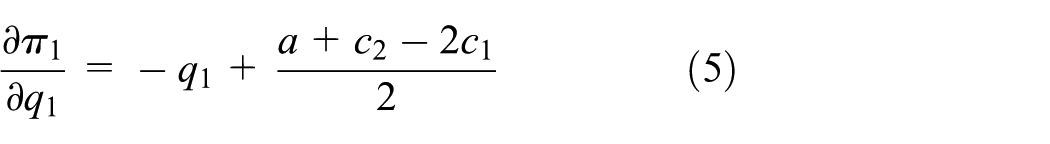
Setting this to zero for maximization, compute the best output of the leader

With the function

where
A new attack–defense game
The previous section introduces the Stackelberg game briefly, and this section establishes a new attack–defense game based on Stackelberg game. As for known malware, WSN gains knowledge based on its experiences and perceptions about malware. According to the knowledge, WSN is able to predict the possible strategy of malware. From the perspective of malware, the worst case is that its strategy is successfully predicted by WSN and then WSN maximizes its payoff. So malware can use a Stackelberg game to model this situation where WSN makes decisions based on the predicted infection probability of malware. For malware, when selecting the optimal strategy, it assumes that the WSN successfully predicts its strategy and moves later, that is, the predicted infection probability is equal to the real infection probability. Then a new game is established to compute the optimal strategy for malware, and in this game the malware is seen as a leader and WSN as a follower. After analyzing this game, the best infection probability is calculated and the optimal strategy for WSN is also obtained.
Table 1 lists the parameters used in the proposed game.
Parameters used in the proposed game.
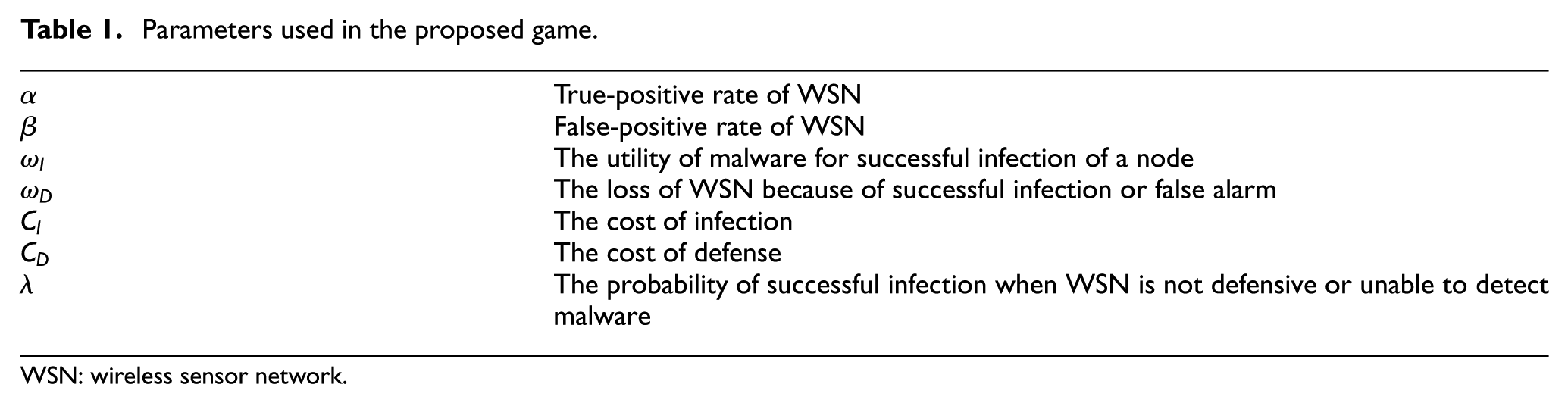
WSN: wireless sensor network.
This game has two players: malware (
The payoff matrix of the proposed game.

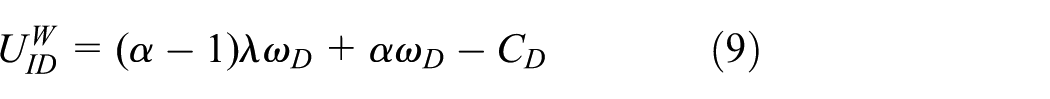
Analyze the strategy combination {Infect, Defend}. When using IDS to defend, WSN cannot detect the infection of malware accurately. The probability that WSN detects malware is

For the strategy combination {Infect, Non-defend}, malware gains

On the other hand, WSN loses

Then, for the strategy combination {Non-infect, Defend}, malware has neither gain nor loss so the payoff of malware,

But for WSN, in addition to defense costs

Finally, for the strategy combination {Non-infect, Non-defend}, the payoff of malware,

and the payoff of WSN,

Let

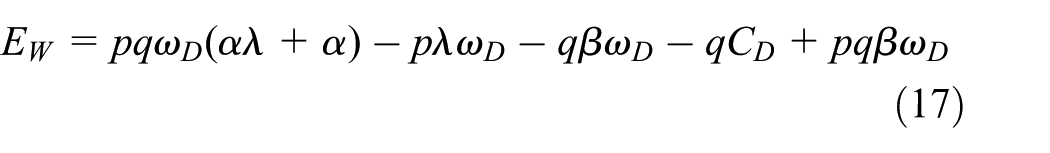
Before solving this game, modify the costs
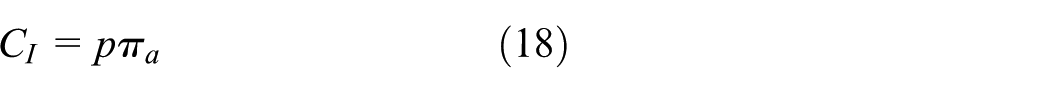

where

Use equation (19) to replace

Stackelberg equilibrium of the proposed attack–defense game
In the last section, a new attack–defense game based on Stackelberg game is established. In this game, the malware makes the decision first and then WSN chooses its strategy. This game is solved by backward induction. To calculate the equilibrium solution, the best response of WSN is considered first. When the strategy of malware is known, the best response of WSN is changing its defense probability to maximize the expected payoff.
The first partial derivative of
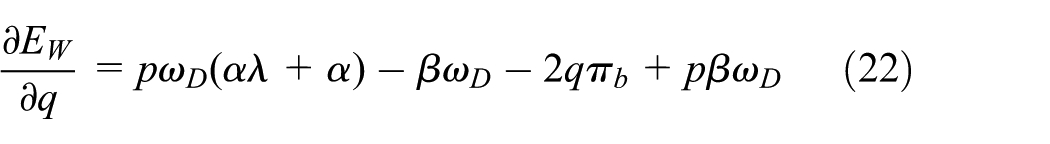
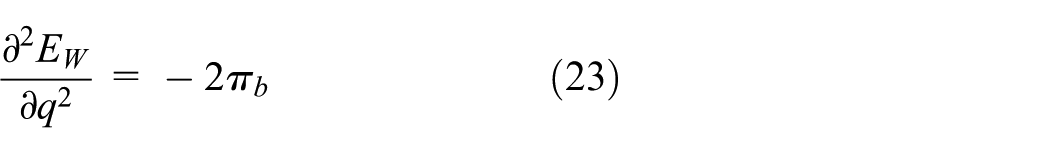
Because the second partial derivative of

When
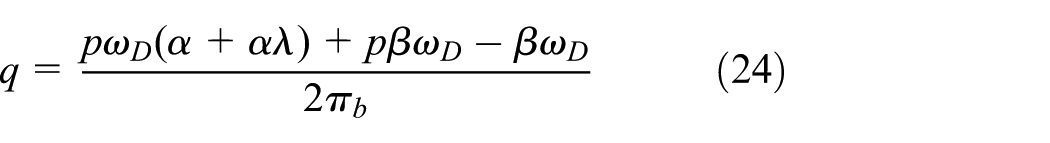
After obtaining the response function of the follower, the infection probability that maximizes the expected payoff of malware can be calculated. The first partial derivative of

Because the second partial derivative is smaller than zero,

Through solving the game, malware obtains the optimal infection probability that maximizes its expected payoff. With equation (24), WSN can calculate the optimal defense probability when
Analysis of reliability of a clustered WSN
Computing the MTTF of a sensor node
The reliability of the WSN indicates the probability that the WSN will work normally. MTTF denotes the expected time to failure for a sensor node, and it is a typical way to analyze the reliability of WSN. Based on the Markov chain model, the MTTF of the sensor node can be calculated. The Markov chain model describes the transition relationship between different states. In order to build the Markov chain model, the probability that a normal node is infected successfully is calculated first. In the last section, a new attack–defense game based on Stackelberg game is established. By solving this game, the infection probability and the defense probability are calculated. But not all attacks will succeed because of the defense of WSN or other reasons. So the successful infection probability, denoted as

where

Figure 1 illustrates the Markov chain model mentioned in Wang et al. 46 From this model, the state transition probability matrix is obtained. As shown in this figure, there are seven states.
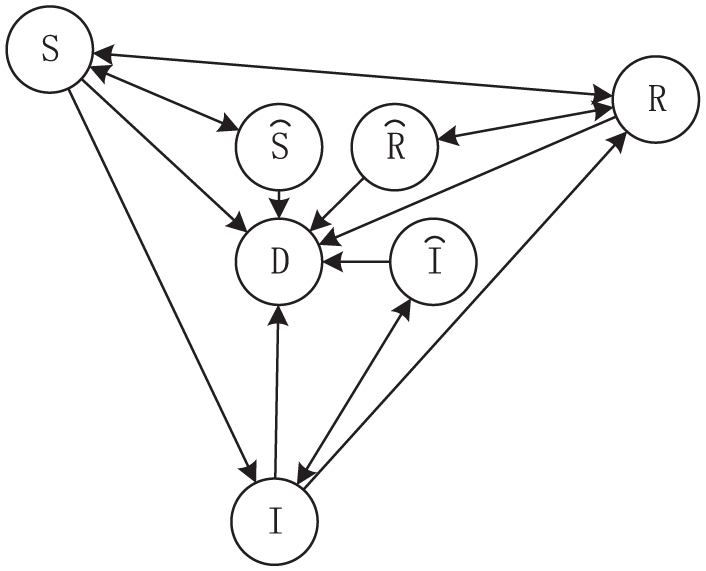
The Markov chain model of state transition.
A susceptible node works normally, but is vulnerable to malware. A infected node tries to infect other nodes, while a repaired node is immune to known malware. When the node is dormant, it cannot be infected or propagate malware to the adjacent nodes. A node becomes unusable because of exhaustion or destruction. And
The state transition probability matrix denoted as
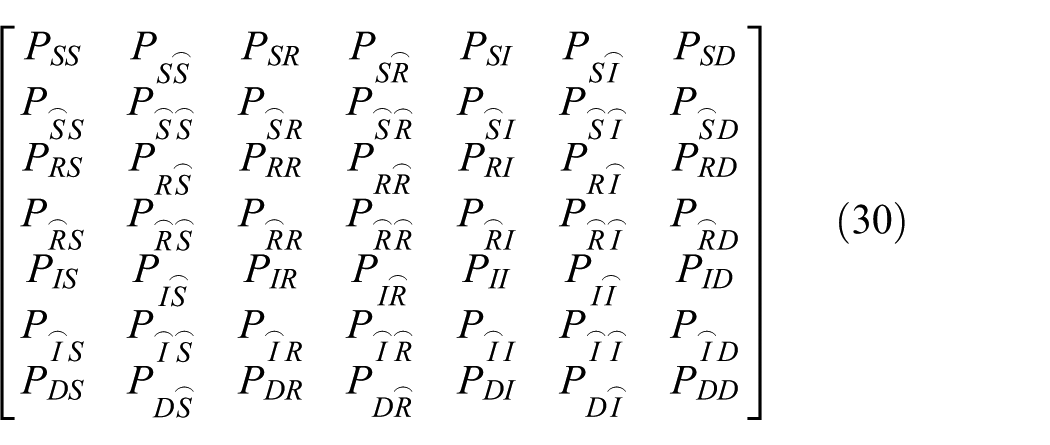
Then the approach proposed in Börcsök et al.
67
is used to compute the MTTF of a sensor node. Separate out the normal working states of the node

Then compute matrix

The matrix

Finally, sum up the first row of matrix
Method of reliability analysis
Then the reliability of WSN is analyzed with the MTTF of a sensor node. This section applies the method developed in Shen et al. 45 to analyze the reliability of WSN. Using the MTTF of a sensor node, the reliability of a sensor node is computed

Figure 2 illustrates the topology of a clustered WSN. There is a cluster head in a cluster of sensor nodes for coordinating sensor nodes. This structure is a two-layer model, in which the upper part comprises cluster heads and the lower part contains sensor nodes. Sensor nodes transmit sensed data to the responsible cluster head. A cluster is a parallel system consisting of a number of sensor nodes, so, as long as a node can work normally, the cluster can work normally. Then the cluster head collects and transmits data to the base station via other cluster heads in this route. Each route that contains a set of clusters is a serial system because the route does not work even if one of the clusters fails. In a clustered WSN, the sensed data can be transmitted to the base station through different routes. As long as a route in WSN works normally, the WSN works normally, so a clustered WSN is a parallel system. According to the topology, the reliability of WSN can be analyzed.

The topology of a WSN.
The reliability of a cluster denoted by

Then the reliability of the route is computed
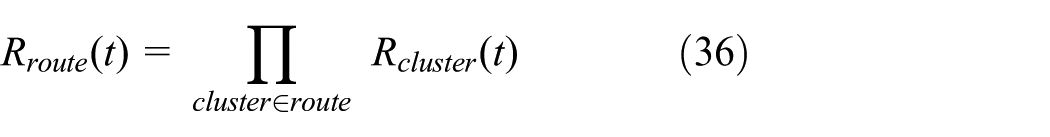
At last, the reliability of WSN is

Experimental results
Infection probability
In this section, some experimental results are presented to illustrate the influence of true-positive rate
Figure 3 shows the influence of

The influence of
If
Defense probability
Figure 4 shows the effect of

The influence of
As analyzed in the last subsection, WSNs with higher
Successful infection probability and MTTF
As introduced in the last section, when malware chooses to attack, there is a probability that malware attacks failed. And the successful infection probability

The influence of
In order to compute MTTF of a sensor node, the parameters of state transition probabilities are set as follows

Setting the other transition probabilities to zero, the

Figure 6 shows the trend of
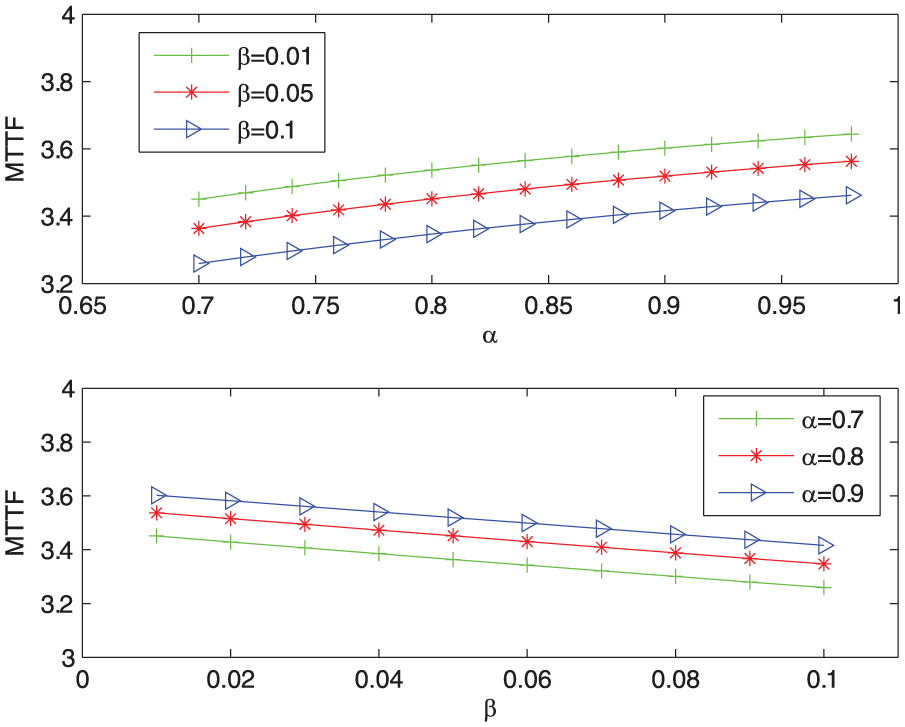
The influence of
According to the former experimental results, when the detection rate is higher, the successful infection probability is lower which means that it is more difficult to infect. So the sensor node works normally for a longer time, and
Reliability of WSNs
The reliability of WSN can be calculated and analyzed using the methods mentioned in the previous section. This subsection assumes that the WSN has four routes, one route has four clusters, and one cluster has four nodes. Then it analyzes the influence of
The first subgraph in Figure 7 shows that the reliability of WSN varies with
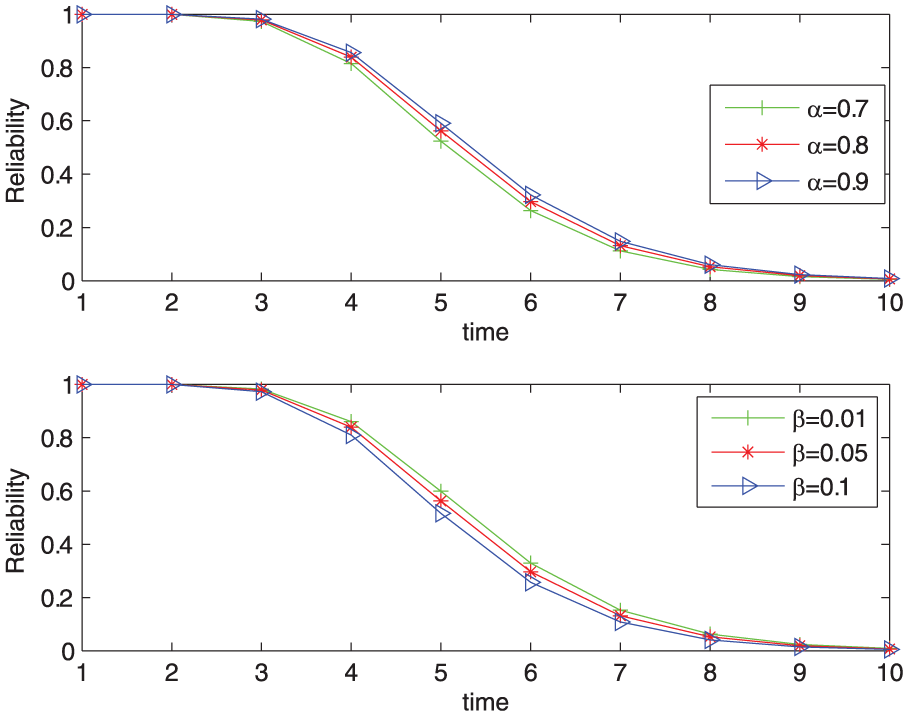
The influence of
Figure 8 illustrates the impact of infection cost
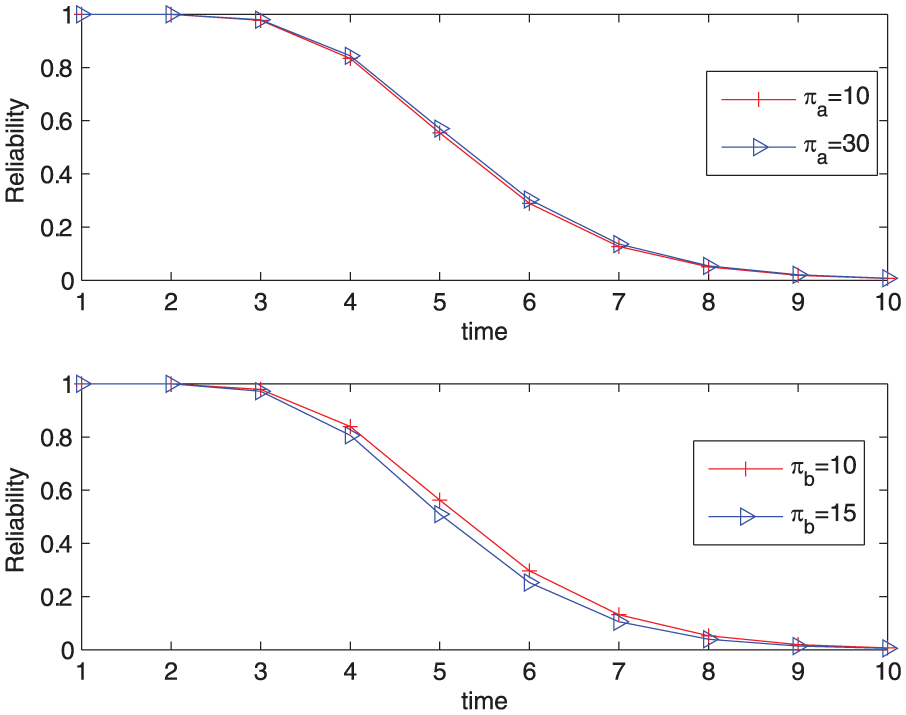
The influence of
Comparison with a simultaneous game–based reliability analysis approach
This section compares the proposed method with the existing method based on a simultaneous game and analyzes the differences between them. The simultaneous game discussed in Shen et al.
45
is one in which attacker and defender make decisions simultaneously. Table 3 illustrates the payoff matrix of the simultaneous game; let


The payoff matrix of the simultaneous game.
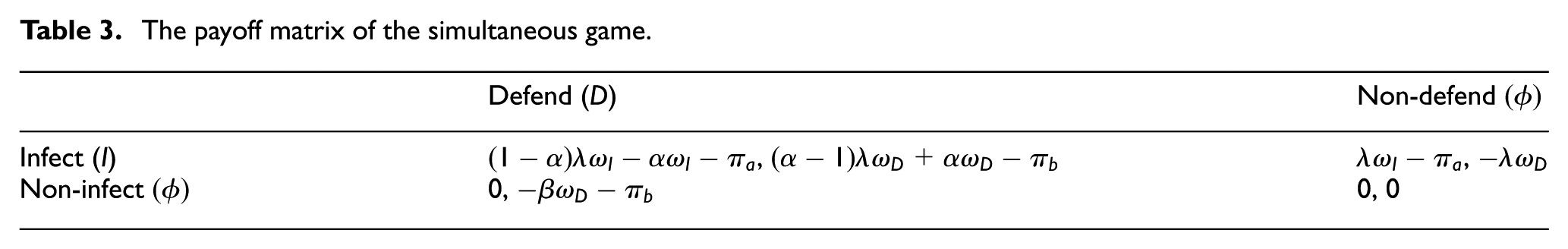
Let

In the same way, compute the infection probability

Set
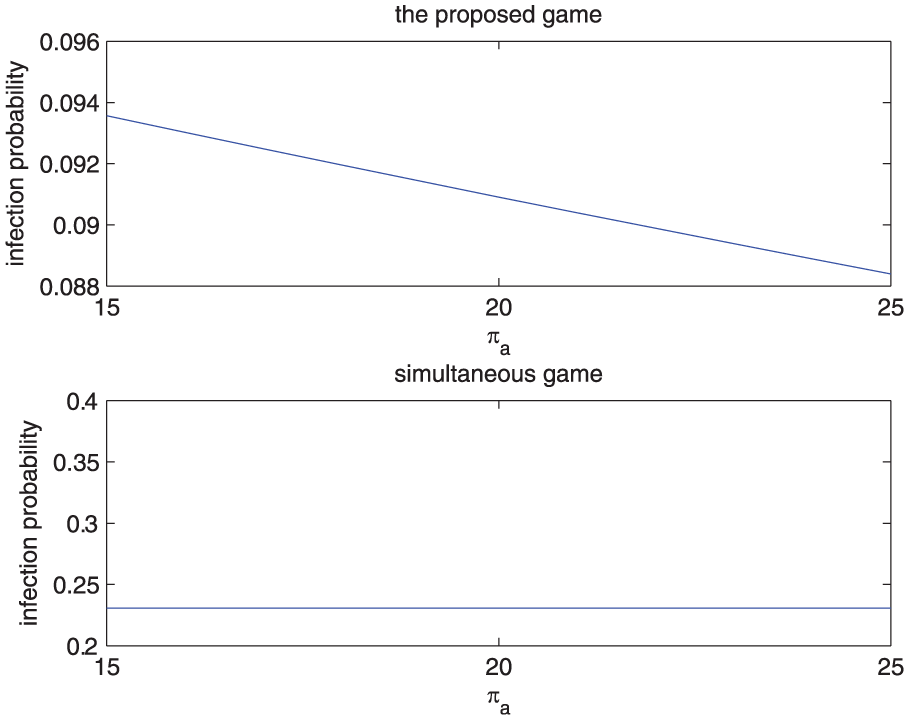
The influence of
Figure 10 illustrates that the defense probability varies with defense cost
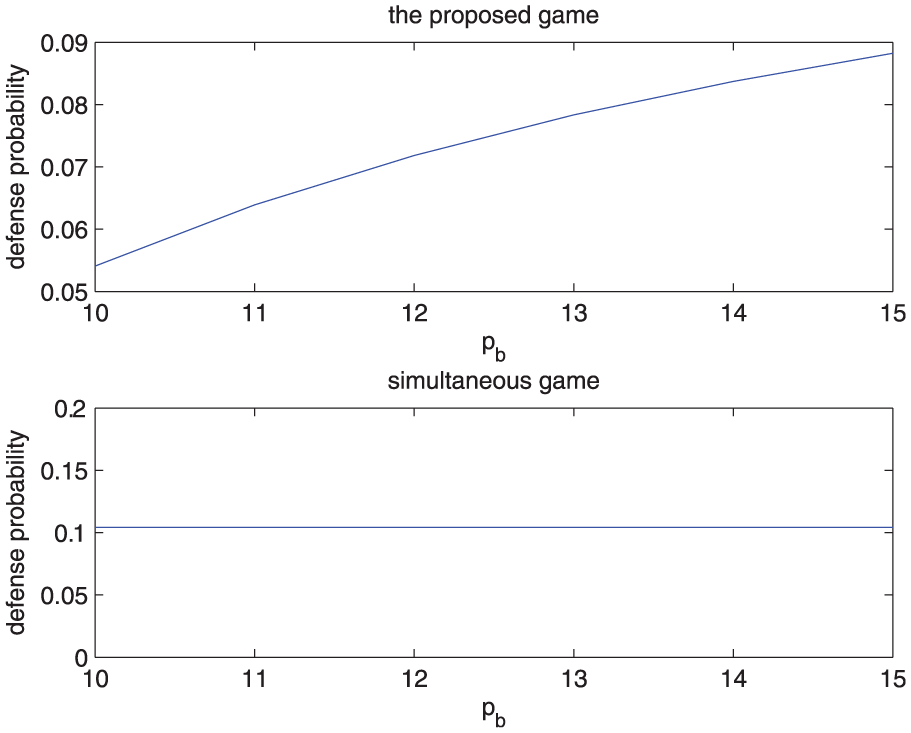
The influence of
After analyzing the influence of infection cost and defense cost on the strategies of WSN and malware, the influence of
Figure 11 shows the influence of

The influence of
Figure 12 illustrates the influence of

The influence of
The previous sections discuss the influence of

The influence of
Then this section calculates and compares the expected payoffs of the two players under different strategies. Assume that both of the players have two models to choose, that is, the simultaneous model and the proposed model. Set
The expected payoff of malware.

The expected payoff of WSN.
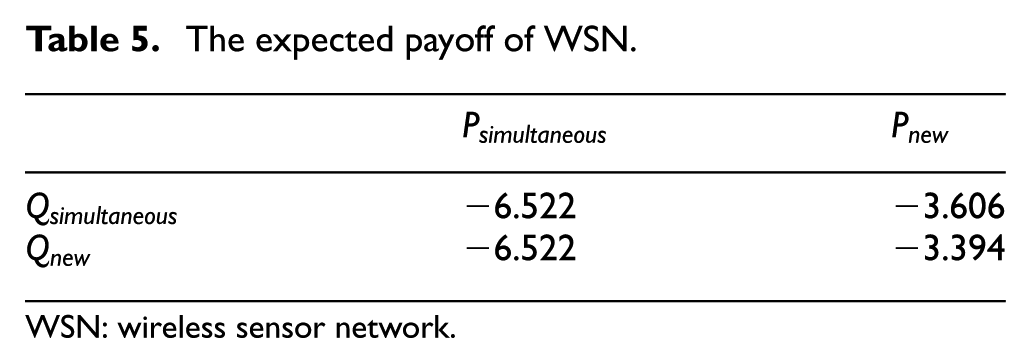
WSN: wireless sensor network.
Therefore, the proposed method based on Stackelberg game considers more relevant factors when analyzing infection probability and defense probability, but the existing method based on the simultaneous game ignores the influences of these parameters. However, these factors affect the decisions of malware and WSN in practice. Through analyzing the expected payoffs of WSN and malware under different strategies, it can be observed that the equilibrium strategy of the new game is better for WSN.
Conclusion
This article proposes a new attack–defense game between malware and WSN based on Stackelberg game. With the equilibrium solution, the reliability of WSN is analyzed. This game considers a situation that malware is more initiative than WSN in adversarial decision making. Malware is regarded as a leader and WSN as the follower. The malware decides its strategy first and then WSN makes its decision according to the action of the former. Compared with the method based on a simultaneous game, this method considers the influence of more relevant parameters. And the equilibrium strategy is better for WSN than the strategy of the simultaneous game. In addition, sufficient experimental results and analysis illustrate the influence of different parameters on the equilibrium solution and reliability of WSN. In future research, when researching the optimal strategy for WSN in adversarial decision making, the more complex situation can be considered where WSN and malware both have some methods to select, and the relationship of topology and strategy selection can be taken in account.
Footnotes
Handling Editor: Daming Zhou
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was partially supported by the National Natural Science Foundation of China (Program Nos 61671384 and 61703338) and the Natural Science Basic Research Plan in Shaanxi Province of China (Program No. 2018JQ6085).
