Abstract
A new blind watermarking scheme for three-dimensional point-cloud models is proposed based on vertex curvature to achieve an appropriate trade-off between transparency and robustness. The root mean square curvature of local set of every vertex is first calculated for the three-dimensional point-cloud model and then the vertices with larger root mean square curvature are used to carry the watermarking information; the vertices with smaller root mean square curvature are exploited to establish the synchronization relation between the watermark embedding and extraction. The three-dimensional point-cloud model is divided into ball rings, and the watermarking information is inserted by modifying the radial radii of vertices within ball rings. Those vertices taking part in establishing the synchronization relation do not carry the watermarking information; therefore, the synchronization relation is not affected by the embedded watermark. Experimental results show the proposed method outperforms other well-known three-dimensional point-cloud model watermarking methods in terms of imperceptibility and robustness, especially for against geometric attack.
Introduction
Over the past few years, three-dimensional (3D) models are more and more important to business objectives. Greater amounts of sensitive data related to 3D models traversed both wired and wireless networks. These valuable data in business enterprises attract an increasing number of malware applications and hackers. 1 As a way of preventing network from becoming a treasure trove for cybercriminals, the authentication and copyright of the 3D models have become an increased focus. Digital watermarking is considered as one of the effective solutions to protect the authentication and copyright for the 3D models. 2
The boundary representation of a 3D model has a point-cloud model, a mesh model, and a surface model. In recent years, there are many research works on digital watermark for 3D mesh models. Many of them are watermarking algorithms involving spatial domain. In spatial watermarking algorithms,3–7 watermarking information is embedded by directly modifying topological or geometric features of mesh models. Liu et al. 3 presented a watermarking method for triangular mesh models; in this method, the multi-resolution adaptive parameterization of surface (MAPS) approach is used to partition the model, and the watermarking information is inserted into the vertices lying in the fine level. Zhan et al. 6 divided the model into bins in terms of the root mean square curvature (RMSC) value in the local neighborhood of every vertex; the mean curvature value of each bin was modified to embed watermark information. Jiang et al. 7 proposed a watermarking method that operates the least-significant bits of integer of the vertex coordinates to embed watermarking data. In frequency watermarking algorithms,8–10 some frequency toolkits are used for to capture topological or geometric features of mesh models, and the watermarking information is embedded into the frequency coefficients representing the topological or geometric features. Wang et al. 8 proposed a high-capacity watermarking method for a semi-regular mesh model that the watermarking information is embedded into wavelet coefficients in different levels. Ai et al. 9 separated 3D mesh models into Voronoi patches, each of which was projected to a reference square plane. By applying the 2D discrete cosine transform (DCT) transformation to each square plane, a bit of the watermark information was repeatedly insert into the transform coefficients of each projection image. These watermarking algorithms for 3D mesh models have demonstrated a better robustness against geometric attack and have protected the copyright of 3D mesh models to some extent.
However, compared with the attention to the mesh model, research on digital watermarking for the 3D point-cloud models is very few. Cotting et al. 11 separated a 3D point-cloud model into patches using a fast-hierarchical clustering approach; then, Laplacian operation was applied to each patch and the low-frequency components were selected from each Laplacian patch for watermark embedding. The 3D point-cloud model method proposed in Ohbuchi et al. 12 was an extension from the watermarking methods of 3D mesh models. In this method, the disjoint clusters that were derived from the disordered points of the model first produced meshes and then Zachi’s spectral analysis was applied to the meshes; the watermarking information was embedded into the coefficients of the frequency domain. Feng 13 also presented a watermarking algorithm for 3D point-cloud models. In this scheme, the point-cloud model was split into a set of patches and watermarking information was inserted into these patches by modulating angle quantization index. By modifying vector length of points in each patch obtained from the partitioned the 3D point-cloud model, a self-similarity-based watermarking method for 3D point-cloud models was proposed in Ke et al., 14 in which each bit of the watermark information was repeatedly embedded to improve its robustness. Feng 15 split the model into several bins and embedded a watermarking bit by modulating the mean distance of the bin.
Overall, research on digital watermarking for 3D point-cloud models is still at early stage. 3D point-cloud models do not have any connection information between points, 16 which enables extracting the watermark to become very difficult. Therefore, the big challenge of robust point-cloud watermarking algorithms is how to find exactly the watermarked vertices at the extraction stage.
In this article, we propose a robust watermarking method for 3D point-cloud models. In order to be still able to locate the watermarked vertices in the case of the disorder of vertices of 3D point-cloud model, the synchronization relation is first established; then, the model is separated into ball rings in terms of radial radius and the watermark bit is repeatedly inserted into vertices of each ball ring. The vertices with larger RMSC are selected to carry watermarking information; the synchronization relation is established using the vertices with smaller RMSC. The main advantages of the proposed method are as follows: (1) the vertices, which are selected to carry the watermarking information, are located in the abrupt changing regions having a good visual masking effect. This helps to carry the large capacity watermarking information and enables the method to achieve an appropriate trade-off between transparency and robustness; (2) the watermarking information is not embedded into those vertices used for establishing the synchronization relation, which ensures that watermark detection and embedding are performed in the same coordinate system, thus improving the robustness of our method against geometric attack; and (3) each bit of watermarking information is repeatedly embedded by modifying radial radii of vertices of each ball ring. The ball ring embedding and repeated embedding enable the method to successfully overcome the problem of disorder of vertices for 3D point-cloud models. The flowchart of the proposed watermarking method of 3D point-cloud models is shown in Figure 1.

Framework of the proposed method: (a) flowchart for watermark embedding and (b) flowchart for watermark extraction.
The article is organized as follows. Section “The proposed watermarking algorithm” describes the proposed method in detail. Section “Experiments and results” gives the simulation results and analyses about the performances of the proposed method. Finally, we state the conclusion and discuss future work in section “Conclusion.”
The proposed watermarking algorithm
Selection of the embedding positions
Whether the watermarking information can be embedded into the appropriate vertices plays an important role in achieving a good trade-off between imperceptibility and robustness. Theoretically, the embedding of the watermark into the 3D point-cloud models should not produce any visual changes. That the vertices of the flat regions of the 3D model are disturbed would result in perceptible distortions of the model, whereas the vertices of the regions with abrupt changes disturbed would not lead to marked visual distortions. Therefore, the vertices lying in the bumpy regions should be appropriate to carry the watermark information. We use the RMSC value of local set to find these vertices from the model, requiring the following two steps: (1) defining the local sets of vertices and (2) calculating the RMSC values of vertices.
Defining the local set
3D point-cloud model is a representation of a set of vertices lying in the exterior surfaces of an object and these vertices have no implicit order like pixels of 2D images (Figure 2(a)). To describe geometric feature of the neighborhood of each vertex, there is a need to define a geometric structure, the local set we called. Whether the vertex is suitable for carrying the watermark information depends on the feature parameter that indicates the geometry property of its local set. Delaunay triangulation scheme is exploited to define the local set of each vertex.

(a) 3D point-cloud model for Pig; (b) the local set of vertex
For every vertex of the 3D model, if there is a Delaunay edge connecting vertices
where
Calculating RMSC
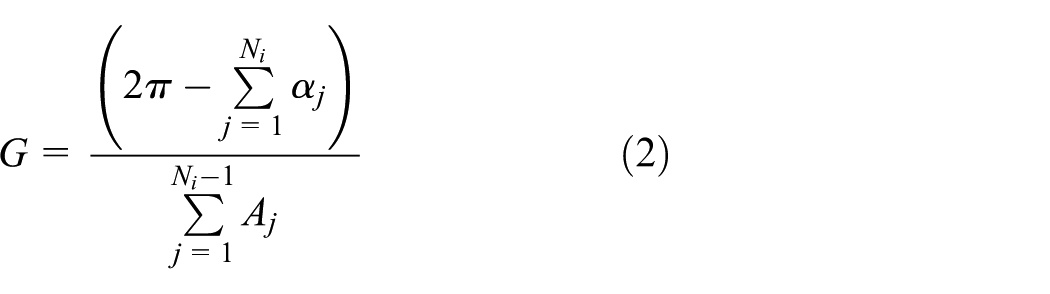
The vertices that are most appropriate to carry the watermarking information should be located in abrupt-change regions. In order to find these vertices, the Gaussian curvature and the mean curvature of each vertex should be first obtained. The Gaussian curvature G and the mean curvature H of vertex Vi can be approximately calculated from all the vertices within its local set; the calculation is shown in equations (2) and (3)
where Ni is the total number of local set of vertex Vi, αj (j = 1, 2, …, Ni) denotes the interior angle adjacent to vertex Vi, βj (j = 1, 2, …, Ni − 1) represents the angles between the normals of the two adjacent triangles, and Aj (j = 1, 2, …, Ni − 1) is the triangle area belonging to the local set of vertex Vi.
When the Gaussian curvature G and the mean curvature H of each vertex are obtained, the bumpy region of the 3D model can be measured according to the following equation
The RMSC value is represented with
All the vertices of a 3D point-cloud model are ordered according to
The candidate vertices (vertices marked with red) carry the watermarking information and the rest are used to establish the synchronization relation.
Establishing the synchronization information
Unlike pixels of an image, vertex data of 3D models do not have an implicit order. In order to find those watermarked vertices during the watermark extraction to improve the performance against geometric attacks, a synchronization relation needs to be established between the processes of watermark embedding and watermark extraction. In the method, we used the vertices of the reference set Sr to build a new coordinate system and embedded the watermarking information into the candidate vertices in the built coordinate system. During the watermark extraction, although the coordinate values of vertices have changed when the model is subjected to geometric attack, the relative positions between the watermarked vertices and the origin of the built coordinate system remain unchanged. This is because the embedded watermarking information has no any impacts on the vertices that are used to build the coordinate system. The steps of establishing the synchronization information are depicted as following:
1. The coordinate origin.
The origin of the established coordinate system is defined as equation (5)
where
2. The coordinate axes.
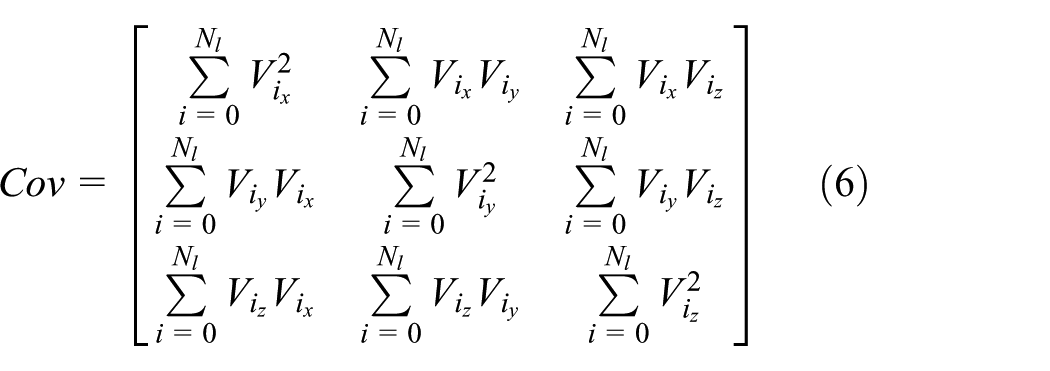
Suppose that the coordinate axes of the established synchronization relation are u, v, and n axes, a covariance matrix Cov is first constructed using vertices of the reference set Sr to determine the directions of u, v, and n axes
The square matrix Cov is decomposed via eigen decomposition and can be represented as
where matrix
3. Translation transformation.
Translation matrix Tf
The corresponding coordinates of the transformed vertex are represented as
4. Rotation transformation.
Rotation matrix Rf
where
5. Conversion to spherical coordinates.
The vertices of the model need to be represented with spherical coordinates, and vertex Vi with Cartesian coordinates
6. Scaling the model.

(a) The spherical coordinates of vertex Vi, (b) dividing the model into ball rings, and (c) embedding a watermark bit into each ball ring.
In order to resist against scaling attacks, component
Scaling factor Sf
The final coordinates of the transformed vertex are represented as
Watermark embedding
In addition to establishing the synchronization relation, the 3D point-cloud model has to be segmented into several units to locate the embedding positions of the watermark. We assume that the 3D point-cloud model is encircled by a sphere whose center is the coordinate origin of the established coordinate system, and radius is equal to the largest value of spherical coordinate of the 3D model. Then, the model is split into M (M represents the watermarking capacity) ball rings between the minimum radius ρmin and maximum radius ρmax using equation (14)
where Rm expresses all vertices belonging to the mth ball ring, and
The watermarking information is embedded by modulating the radial radius
where
Figure 4(c) helps to explain the meaning of equation (16). Supposing that regions R1 and R2 on the largest cross section are the projections of the two ball rings and all the vertices of these two ball rings fall within region R1 and region R2. The black points express the vertices of the reference set S r while the red points represent the vertices of the candidate set Sc. If the embedded bit of the watermark information is “1,” only the candidate vertices (points marked with red) within the inner half of region R1 are modulated and moved to the outer half of region R1 to become the watermarked vertices (points marked with green), whereas the candidate vertices (points marked with red) within the outer half of region R1 keep unchanged because they do not meet the requirement of equation (16). If the embedded bit of the watermark information is “–1,” only the candidate vertices (points marked with red) within the outer half of region R2 are modified and moved to the inner half of region R2 to become the watermarked vertices (points marked with blue). Similarly, the candidate vertices (points marked with red) within the inner half of region R2 should not be modified. We summarize the main steps for embedding a watermark as below.
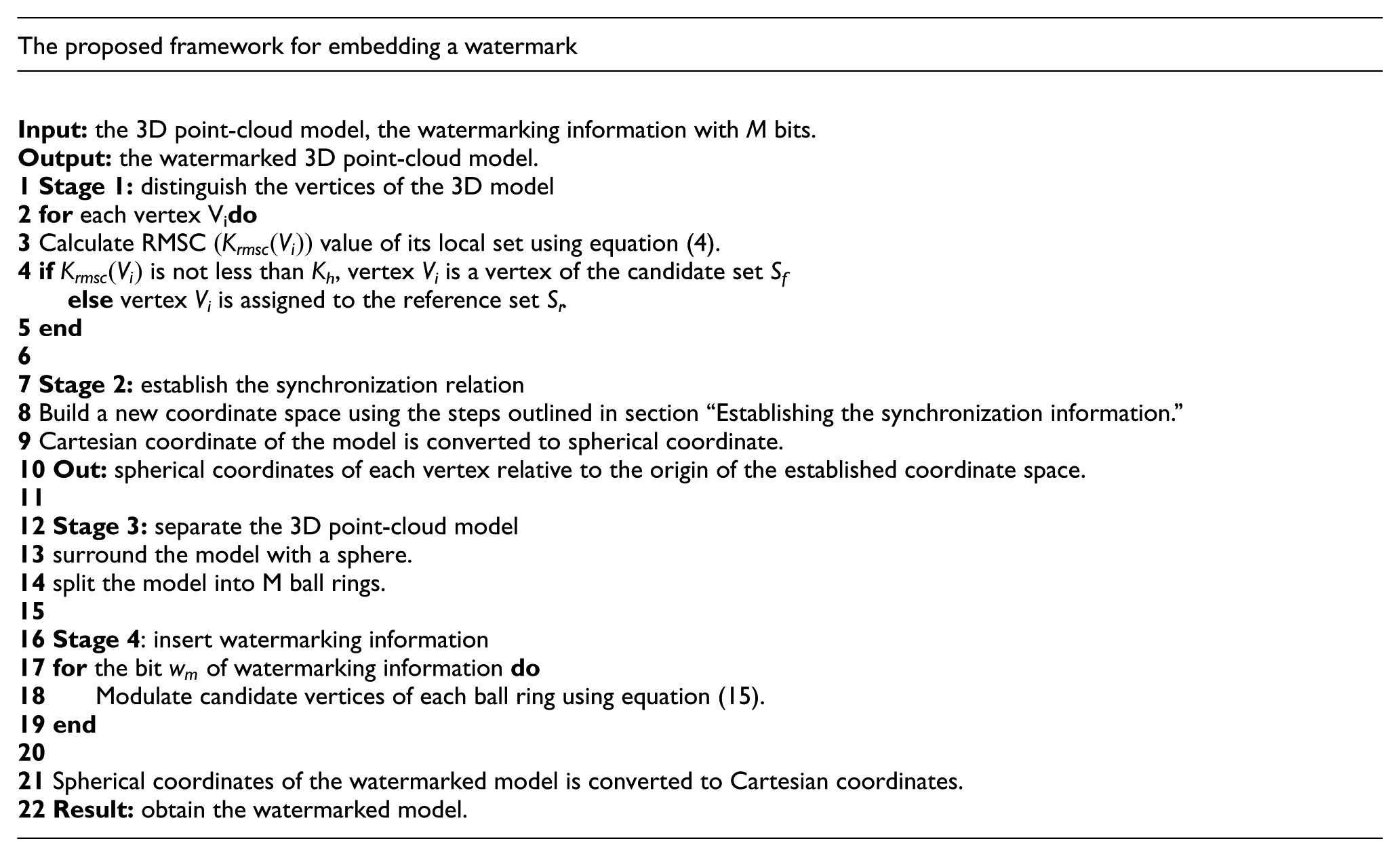
Watermark extraction
In the proposed method, the watermark extracting does not need the original 3D point-cloud model, that is, it is a blind extraction. Like the process of the watermark embedding, the RMSCs

where num1 and num2 denote the number of candidate vertices within the inner part and the outer part in the mth ball ring, respectively. If the candidate vertex is located in the outer part, add to num1 with a value of 1; if the candidate vertex lies in the inner part, add value 1 to num2. The main steps of watermark extraction were summarized as below.

Experiments and results
We conducted the experiments to validate imperceptibility and robustness of the proposed method in this section, compared with the watermarking algorithms for 3D point-cloud models in Ke et al.
14
and Feng.
15
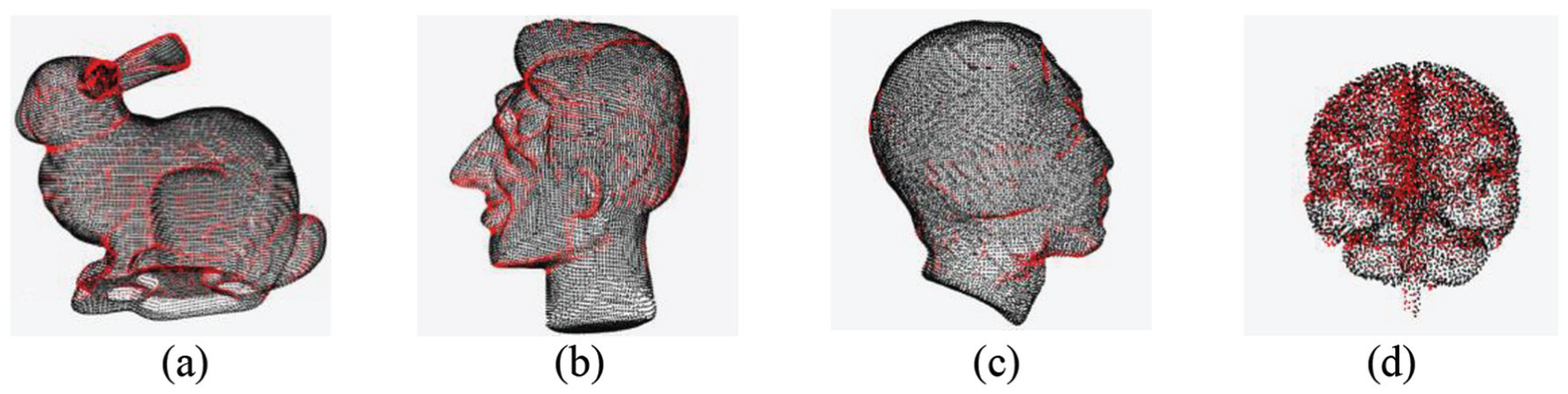
The experiments were carried out on some 3D models chosen from Stanford model library and the Princeton Shape Benchmark library, four models of which are shown in Figure 5: Bunny, M365, M355, and M285. The watermarking information with the size of


Original cloud-point models: (a) Bunny, (b) M365, (b) M355, and (d) M285.
In addition, the signal-to-noise ratio (SNR) was also used to evaluate the model degradation caused by the embedded watermark. The SNR is given by equation (19)

where N is the number of vertices of the 3D model,

where
Imperceptibility evaluation
Figure 6 shows the four models that the watermarking information is embedded into using our proposed method. Some vertices with a larger RMSC value were chose from ball rings to carry the watermarking information. Radial radius ρ of the candidate vertex is modulated to embed the watermarking information while the other two components θ and φ are kept unchanged. These mechanisms are helpful for achieving a better imperceptibility for the watermark. It can also be seen from Figures 6 and 7 that the watermarked models have no significant difference from the original 3D models in visual perception. The two-objective metrics of RMSE and SNR also confirm the observation. In Table 1, the RMSE values are lower while the SNR values are higher obtained from our proposed method, when compared with the corresponding results obtained with the methods in Ke et al. 14 and Feng. 15 Beyond that, we observe that the imperceptibility of the watermark is associated with the proportion of the watermarked vertices that occupied in the 3D models. When each model carried the watermark with the same bits, the smaller the percentage of the watermarked vertices that occupied the 3D models is, that is, the model might contain plenty of vertices, the better the invisibility of the watermark is. Among the four models exhibited in Figure 5, the number of vertices of the 3D model Bunny is maximum while the 3D model M285 contains the minimum number of vertices. The objective values (RMSE and SNR) in Table 1 shows that, whether for our proposed method or the two methods in Ke et al. 14 and Feng, 15 the 3D model Bunny achieved the best results while the 3D model M285 got the worst results. However, whether for model M285 containing sparse vertices or model Bunny with dense vertices, our proposed method achieves the RMSE results less than 70 × 10−4 and the SNR results greater than 40 dB. This demonstrates that our proposed method can ensure the visual quality of the watermarked models under meeting the requirement of the capacity of the embedded watermark.

Original illumination models: (a) Bunny, (b) M365, (b) M355, and (d) M285.

Watermarked models: (a) Bunny, (b) M365, (b) M355, and (d) M285.
Invisibility comparison of the watermarking methods in terms of RMSE × 10−4 and SNR.

RMSE: root mean square error; SNR: signal-to-noise ratio.
Robustness evaluation
Robustness is an indispensable evaluation metric of 3D watermarking methods. The comparison of the robustness of the three methods was conducted on each model that the same watermarking information with the size of
The values Corr of four 3D point-cloud models when subjected to different attacks.


Comparison of average values of the correlation coefficients: robustness against (a) noise (σ × 10−3) and (b) simplification (%).

Simplification attack on models (50% reduction): (a) Bunny, (b) M365, (c) M355, and (d) M285.
Additive noise attack
The Corr values of the second line in Table 2 were obtained in the case that the watermarked models were subjected to the attacks of Gaussian noise. Figure 8(a) shows the robustness of the three methods against noise when the strength
Simplification attack
The goal of vertex simplification is to generate a point-cloud model with as few vertices as possible on the premise of minimizing distortion from the original model. For a 3D model carrying the watermarking information, simplification operation is regarded as an attack that will remove some watermarked vertices from the model. The strength of simplification attack should not cause the perceived deformation of the model. If the attack intensity makes the tested 3D models severely degraded, the copyright of the tested models need not be protected because they have already lost their application value. Therefore, it is not important whether the watermark information can be extracted from the tested models. It can be observed from the third line in Table 2 and Figure 8(b) that, when simplification intensity of vertices does not cause any visual distortions, the values Corr obtained from our proposed method are all greater than 0.5. This illustrates that our watermarking method can detect the watermarking information successfully; comparatively speaking, the results of Corr obtained using the methods in Ke et al. 14 and Feng 15 are inferior to the results of our method when the number of the simplified vertices changes from 3%, 12%, to 21%. However, when the simplified vertices is greater than 30%, which results in significant visual distortions of the models (Figure 9), the performances of the three methods are not very well (Corr < 0.5). Our method is that more than one candidate vertex is selected from each ball ring to carry the same watermark bit, that is, redundant embedding. When a certain number of vertices within the ball ring are removed, we can still detect the watermark bit from the remained candidate vertices within the ball ring. Therefore, the performance of the proposed method to resist the simplification attack is relatively better than those of the methods in Ke et al. 14 and Feng. 15
Rotation attack
The performance to resist geometric attack is investigated, for example, rotation attack. In our method, the vertices with smaller RMSC value, that is, the reference vertices we called, are used to establish the synchronization relation between the watermark embedding and extraction; whereas, the vertices with larger RMSC value, that is, the candidate vertices we called, are exploited to carry the watermarking information. The reference vertices are not affected by the embedded watermarking information; as a result of which, the established synchronization relation is not going to change. If the synchronization relation between watermark detection and watermark embedding remains unchanged, the relative positions of the watermarked vertices with the origin of the established coordinate system are also unchanged; therefore, geometric attack such as a translation, scaling, and rotation attack does not weaken the robustness of the proposed method. The fourth line in Table 2 and Figure 10(a) illustrate that our proposed method is effective in resisting the rotation attacks.

Comparison of average values of the correlation coefficients: robustness against (a) rotation angle around X-axis and (b) cropping percentage (%).
Cropping attack
Cropping is an operation that removes all the vertices from a certain part of 3D model, which is regarded as an attack difficult to improve robustness. The fifth line in Table 2 and Figure 10(b) display the evaluation results for robustness against cropping. The evaluation results indicate that the performance of our proposed method outperforms the methods in Ke et al 14 and Feng 15 when the tested models encounter the attacks of weak cropping; as the strength of the attack increases, the robustness of our method is close to those of the two methods. In our method, each bit of the watermark is embedded into multiply vertices which are irrelevant to each other in the same ball ring. This mechanism is helpful for successfully extracting the watermark information from the models attacked by a cropping operation. However, if the sheared part is large and the sheared part is close to 30% of the model, many vertices that carry watermark bits are lost, thus resulting in failing to detect the correct watermarking information. Therefore, the performance of the proposed method is not satisfied when encounter strong cropping attacks.
ROC evaluation
ROC curve is regarded as an important assessment indicator of the robustness performance of a watermarking method. 18 ROC curves describe the relationship between the probability of false negatives Pfn and the probability of false positives Pfp when correlation coefficient (Corr) value varies. The probability of false positives expresses the probability of extracting a watermark from a non-watermarked model or from a model that was embedded another watermark. The probability of false negative represents the probability of failing to extract the correct watermark from a watermarked model.
In this section, we verify the robustness of our proposed method by analyzing the ROC curves. The probabilities Pfn and Pfp that are evaluated with 200 correct watermarks and 200 wrong watermarks are plotted by varying the correlation coefficient (Corr) values and the correlation results are approximated by Gaussian functions. Equal error rate (EER) is the value of the point on the ROC curve when the probability of false negatives Pfn is equal to the probability of false positives Pfp and is considered as a quantitative evaluation index of robustness performance of the watermarking method. The smaller the EER value is, the better the robustness of the method can be.
Figure 11(a) and (b) shows the ROC curves of the three methods when the model Bunny is, respectively, subjected to attacks of the strength σ = 0.0001 of the additive noise and 10% vertices reduction. Figure 12(a) and (b) shows the ROC curves of the three methods when the model Bunny is, respectively, subjected to cropping attack (cutting off 5% of the model) and rotation attack (10° around X-axis). It can be seen from Figures 11 and 12 that the robustness of the proposed method to resist common attack and geometric attack is fairly well, especially for geometric attack. For example, when the model Bunny is subjected to the attack of a rotation 10° around X-axis, the EER value obtained using the proposed method is close to

ROC curves: (a) Gaussian noise (σ = 0.0001) attack and (b) simplification (10% reduction) attack.

ROC curves: (a) rotation (10° around the X-axis) attack and (b) cropping (5% of the model) attack.
Conclusion
In this study, we present a blind and robust watermarking method for 3D point-cloud models. The RMSC of the local set of each vertex is first calculated; the vertices with smaller RMSC values are used to establish the synchronization relation between the watermark embedding and extraction; the vertices with RMSC values are considered to lie in the abrupt regions of the 3D point-cloud models and have a good visual masking effect for the embedded watermark. The model is divided into ball rings and a bit of the watermark is embedded by altering radial radii of candidate vertices of each ball ring. The embedding of the watermark does not have any impacts on the established synchronization relation. The highlights of our study are as follows: (1) the occlusion effect of the embedding positions improves the transparency of the embedded watermark; (2) the establishment of the synchronization relation between the watermark embedding and extraction, as well as its invariance to the embedding of the watermark, helps to enhance the robustness of the proposed method against geometric attack; and (3) the strategy that a watermark bit is repeatedly embedded into a ball ring of the model makes the watermark extraction irrelevant to connectivity of 3D point-cloud models. Experiments show that the proposed method has a good robustness against common attack and geometric attack while ensuring a minimal distortion. In future work, we will combine the proposed framework with the geometric properties of the 3D model19,20 to further improve robustness against common attack and geometric attack, especially for a combination of common attack and geometric attack.
Footnotes
Handling Editor: Shancang Li
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported, in part, by the National Natural Science Foundation of China (No. 61472319), by the Natural Foundation of Shaanxi Province Key Project (No. 2017JZ015), by the Xi’an Science and Technology Project (No. 2017080CG), by the Shaanxi Science and Technology Co-ordination and Innovation Project (No. 2016KTZDGY05-09), and by the Innovation Project of Shaanxi Provincial Department of Education (No. 17JF023).