Abstract
At present, wearable devices are in the ascendant in the field of personal smart communication terminals across the globe, but their information security issues deserve attention. We hereby propose a secure transmission solution that addresses the special requirements of wearable devices in information security. It is based on the principle of quantum secure communication and works well to protect sensitive information on wearable devices. The solution utilizes the coherence properties of quantum entanglement and uses quantum information security techniques such as quantum key distribution and non-orthogonal base measurement to realize secure transmission of sensitive information on wearable devices. Unlike traditional encryption methods based on the complexity of the mathematical algorithm, the solution has unconditional security.
Introduction
The wearable device refers to a category of small-scale portable electronic devices that can be directly worn on the user’s body or integrated into the user’s clothes, such as smart glasses, smart watches, smart wristbands, and smart shoes. In addition to these wearable devices for daily life and sports and health care, medical wearable devices such as insulin pumps and cardiac pacemakers are very common in daily life. The latter has higher requirements for information security. In 2012, the launch of “Google Glasses” marked the actual entry of wearable devices into people’s daily lives from the laboratory. Subsequently, wearable devices have flourished in the field of global communications electronics and personal smart terminals. Academia has reached a consensus that wearable devices will certainly be the future of electronic products1,2 and gradually replace existing mainstream information terminal devices like smartphones and tablets. In addition, wearable devices are further associated with the rising Internet of Things, and people can use their own devices to implement real-world manipulations such as smart offices, smart homes, and smart cars. Our working life will become more convenient and comfortable.
However, the information security issues of wearable devices should be taken into consideration seriously. If information security of wearable devices is not equipped with reliable protection, it can cause the leakage of life habits, health information, and personal privacy. It has become a security risk that induces various criminal activities such as telecommunications fraud. In particular, it is used by hackers to hijack medical devices such as pacemakers. Wearable devices directly endanger the lives of patients. With the rapid development of smart wearable devices, their information security problems will gradually become prominent, and in the future it may become a fatal short board that restricts further development and wide application of wearable devices.3,4 Therefore, the information security of wearable devices cannot be ignored.
Given the importance of information security for wearable devices, we need to consider appropriate information security technologies to protect information security of the wearable device. However, the mature classical security technology adopted by the Internet 5 belongs to the classical cryptosystem based on the intractability of the complexity problem of mathematical calculations. It has two inherent defects: from a mathematical point of view, it is based on mathematical computational complexity theory, with the continuous improvement of network computing capabilities, which will be compromised or gradually become insecure; from a physical point of view, the classical cryptosystems use electronic or photon classical attribute load information. Even simple eavesdropping attacks cannot be detected, and this is the inherent major flaw. Fortunately, quantum cryptography is now developing and improving in practice. The quantum cryptosystem can just make up for the above deficiencies of classic passwords. The security of quantum cryptography is guaranteed by the physics of the quantum state, rather than the computational complexity of mathematics. Therefore, it is independent of the computational conditions (computational power or computational resource size) possessed by the attacker. This is the “Unconditional security of quantum cryptography.” In addition, the attacker’s behavior will be discovered by perturbing the quantum state of the information carrier, which is the detectability of quantum cryptography for eavesdropping attacks. 6 The author believes that the use of quantum information security technology to protect the wearable device information security is a good idea.
Recently, combined with the special requirements of wearable devices for information security technology, Wen et al. 7 used quantum information technology such as quantum key distribution (QKD) and quantum teleportation, and proposed a secure transmission scheme for protecting sensitive messages in wearable devices. This scheme adopts the quantum teleportation technology and requires a classical channel communication. The receiver needs to carry out the corresponding quantum transformation operation on the photons of his or her own hand according to the information of the classical communication. In this article, based on the quantum entanglement coherence property, a quantum non-orthogonal basis measurement method is used, and another quantum scheme for protecting the secure transmission of sensitive messages in wearable devices is proposed. Our solution eliminates the classical channels and receiver’s quantum unitary transform operations, which are used for quantum teleportation in the Wen’s program. This makes our scheme simpler and more reliable.
Fundamental principle
Quantum measurement base
This article will use two measurement bases: base
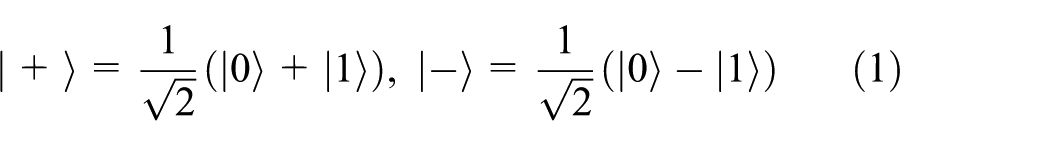
or

It is easy to know that the two sets of measurement bases

where




Quantum entanglement coherence: non-orthogonal basis measurement
Quantum entanglement is a phenomenon unique to quantum mechanics and is the strangest and most inconceivable feature of quantum mechanics, setting it apart from classical mechanics. Entanglement makes quantum information possess many new features that classical information does not have, and the entangled state also provides new physical resources for information transmission and information processing. Assume that two photons A and B are in the Einstein–Podolsky–Rosen (EPR) entangled state
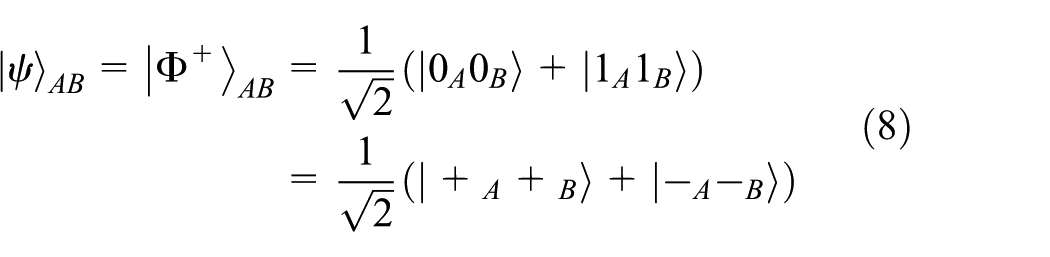
We agree that Alice owns photon A and Bob owns photon B. Due to the entanglement of EPR pairs, Alice’s measurement of photon A momentarily determines the state of photon B entangled with it, regardless of how far apart the two photons are. From equation (8), we can see that when Alice measures photon A, photon B will inevitably collapse to the same state as photon A.
Let us now consider the correlation of quantum measurement results of the base
Scheme description
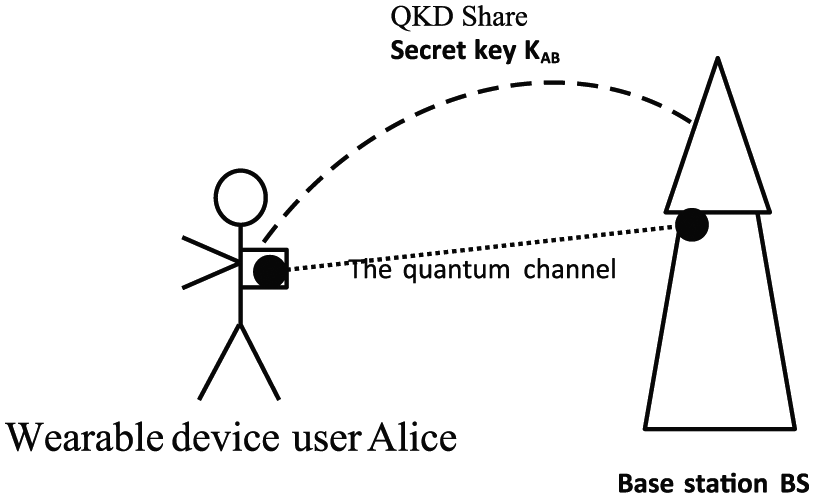
The quantum security communication model of wearable device and base station.
The idea behind the solution is as follows: sensitive information is loaded on the quantum state, the coherence of the entangled quantum state is used, and sensitive information is obtained using the correct non-orthogonal measurement basis for quantum measurement. The selection of the correct measurement base is determined by the value of the shared key
System initialization
Sensitive message transmission
For simplicity, let us assume that the wearable device user Alice has a sensitive message


Every time Alice abandons or saves a measuring result, she tells BS through public channels.
Sensitive message reception
Since the base station BS and Alice share the same key
Analysis of scheme characteristics
Correctness and unconditional security of the scheme
Comparison between this scheme and the work by Wen et al.
The design idea of Wen et al. 7 is to load sensitive information on the quantum state, transmit the quantum state in a teleportation state, and then obtain sensitive information using the quantum measurement of the correct basis. Some quantum principles and features, such as the quantum state unclonable theorem and the stochastic collapse feature of quantum measurement, are used to protect the security of sensitive information. Teleportation requires the transmission of classical information, which can instruct the recipient to perform appropriate corrective transformations to restore the waited quantum state. The classical information has nothing to do with sensitive information, and it is not afraid of eavesdropping and disclosure.
The biggest difference between this scheme and that of Wen et al.
7
is that the quantum information is directly transmitted through the quantum channel shown in equation (3), and quantum teleportation is not adopted. It thereby eliminates the need for the classical channel and the receiver’s quantum unitary transformation operation in the scheme described by Wen et al.
7
The sender expresses the sensitive message by making a proper measurement base of the photon in his own hand in equation (3). It uses the coherence of the entangled quantum state, and the receiver performs quantum measurement using the correct non-orthogonal measurement basis. The sensitive message is obtained. The selection of the correct measurement base is determined by the value of the shared key
Resistance attack performance of the scheme
Conclusion
Wearable devices have become an inseparable part of our everyday life. They are used to transmit an ever-increasing amount of sensitive health, financial, and personal information. This exposes us to the growing scale and sophistication of cyber-attacks. QKD can provide unconditional and future-proof data security but implementing it for handheld mobile devices comes with specific challenges. To establish security, secret keys of sufficient length need to be transmitted during the time of a handheld transaction (~1 s) despite device misalignment, ambient light, and user’s inevitable hand movements. Transmitters and receivers should ideally be compact and of low cost, while avoiding security loopholes.
The good news is that recently Chun et al. 14 demonstrated the first QKD transmission from a handheld transmitter with a key rate large enough to overcome finite key effects. Using dynamic beam steering, reference-frame-independent encoding, and fast indistinguishable pulse generation, they obtained a secret key rate above 30 kb/s over a distance of 0.5 m. Therefore, using their handheld QKD technology, combined with our quantum information coding and transmission scheme, it will not be long before we achieve the high-security transmission of sensitive information on wearable devices.
Footnotes
Handling Editor: Gary Leavens
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was partially supported by the National Natural Science Foundation of China (No. 61771222), Science and technology projects of Guangdong Province (Nos 2016A010101017 and 2016A030313023), Science and Technology Project of Guangzhou (No. 201707010253), 2018 Shenzhen Discipline Layout Project (No. JCYJ201708151 45900474), and Shenzhen Basic Research Project (No. JCY J20170818115704188).
