Abstract
Quantum networks exploit the unique properties of quantum mechanics to enable communication and networking tasks unavailable to existing distributed classical systems. Recently, the research community has focused considerable effort on the simulation of large-scale quantum networks with the ultimate goal of understanding their general properties, developing technical standards, and estimating their expected performance. However, comparatively little effort has been spent considering how quantum networks may impact tactical scenarios of military relevance where both quantum and classical resources may be severely constrained. Here, we develop a custom framework, called QuanTACT, for quantum network simulation explicitly designed for future integration into existing tactical simulation tools. In particular, our framework extends the existing quantum networking tool, SQUANCH, to include channel models required to simulate deployed fiber environments. Furthermore, we implement the additional subroutines needed to simulate entanglement-based quantum key distribution (QKD) and use published results from various field-deployed QKD experiments to benchmark the performance of our framework.
1. Introduction
The coherent networking of distributed quantum systems offers the potential to execute a wide range of protocols either more efficiently than or entirely unavailable to their classical counterparts.1–4 Example applications include the remote creation of shared randomness, 5 distributed sensing,6–8 and distributed quantum computing.9–11 Generally, a quantum network consists of nodes that can generate, store, and manipulate quantum states and channels that distribute quantum states between nodes using, e.g., optical fibers12–20 or directed beams traveling through free space.21,22 The execution of quantum networking protocols requires supporting classical communication, 23 which may or may not coexist in the same communication channel as the distributed quantum states, and classical computation to perform tasks such as state characterization24–33 or parameter tuning. 34
While not true of all quantum networking protocols, the majority of military-relevant protocols rely on quantum entanglement rather than merely the point-to-point distribution of individual quantum states (see an overview of quantum networking protocols in the literature 2 and some discussions of military relevance in the literature35,36). Entanglement is a property of quantum states that allows for correlations beyond what is possible classically and is generally the key resource that protocols exploit for quantum advantage. The study of entangled states consisting of only two entangled systems is already a complex topic with a hierarchy of entanglement classes 37 and many subtle questions related to efficient verification of entanglement.38–41 The study of multipartite entangled states is also an active area of ongoing research.38,40,42–46 The long range distribution of quantum states, entangled or not, is difficult due to fundamental limitations against copying (cloning) or amplifying a quantum state, 47 necessitating the use of quantum repeaters48–50 and entanglement swapping protocols.51,52 In addition, determining the practical component requirements, such as loss profiles and non-linear coefficients,53–55 needed for efficient entanglement distribution is still an area of basic research. 3
Although quantum technology and networks can offer some advantages even when used for purely classical networking tasks, such as the communication of classical information, 56 quantum networks are unlikely to completely replace classical networks and should instead be seen as working alongside, and often relying on, existing classical networks. Understanding how combined quantum-classical networks will operate in real-world scenarios and, in turn, what physical constraints these results put on the development of constituent network elements is an area of significant recent interest. For specific network configurations and networks consisting of only a few nodes, analytical results are possible.57–62 However, in general, modeling the complex interplay between quantum and classical components of a quantum network requires simulation. As a result, multiple efforts to simulate quantum networks have been initiated63–72 (see the review 73 ). While these simulation efforts provide tremendous insight into the broader workings of quantum networks, they are generally not designed to encompass scenarios at the tactical edge where resources, both classical and quantum, are severely constrained.
Here, we detail a custom framework for quantum network simulation, which we refer to as QuanTACT (Quan↔Quantum, TACT↔Tactical) that can be integrated into existing tactical simulation tools. It uses the independently developed Simulator for Quantum Networks and Channels (SQUANCH) 67 to model quantum systems. We extend the capabilities of SQUANCH by developing novel channel models, developing methods for statistical modeling of quantum stream lengths useful for reproducing experimental results, and implementing a clear division of implicit and explicit loss that optimizes simulation performance by avoiding the computations that do not contribute to the desired performance metrics. We implement modular and reconfigurable agent behaviors to support future extension to multi-agent simulations, in addition to key sifting, information reconciliation, and privacy amplification protocols not included in SQUANCH. Finally, we explicitly apply our framework to the simulation of fiber-based quantum key distribution (QKD) networks.74,75
As one of the most mature quantum communication technologies, QKD has been deployed in real-world scenarios, and several commercial versions are available for purchase from Toshiba, ID Quantique, and Qasky. In addition, several formulations of QKD rely on entanglement distribution and hence can form a basis for generalization to other more sophisticated quantum networking protocols.76,77 Most importantly for our purpose, many published experiments demonstrating QKD over long distances 78 and in real-world scenarios are available for use as benchmarks against the basic assumptions and results of our models. In this paper, we concentrate on optical fiber-based quantum networks, motivated in part by the commonality of such systems in experimental demonstrations and by the simplicity of the channel model. Our framework is readily extensible to include free-space quantum channels where turbulence, stray light, and beam tracking become significant concerns, and in fact, such an extension is underway and will be the subject of future work. Herein, we benchmark the results of our simulation using fiber channels against published experiments that demonstrated QKD over deployed fiber in metropolitan areas.
Our choice of SQUANCH as opposed to other quantum network simulator tools is due to its use of an agent-based model which allows for fully parallelized simulations with each agent running its own process. 67 This distributed architecture is consistent with the Extendable Mobile Ad hoc Network Emulator (EMANE); hence, we have designed QuanTACT for integration with existing tactical network modeling tools.79–82 Additional design choices we have made to facilitate integration are focused on providing a drop-in replacement of SQUANCH’s native classical communications with those provided by EMANE. Once completed, the combined QuanTACT/EMANE tool will be applied to the Anglova tactical scenario,81,82 which is an experimentation scenario developed by the NATO IST-124 Research Task Group focused on battalion-sized military operations that require heterogeneous radio networks and includes mobile nodes.
This paper is organized as follows. In section 2, we present a high-level review of QKD and its supporting protocols along with a discussion of how these protocols can be extended to multi-user scenarios. In section 3, we review our quantum network simulation framework, QuanTACT, and the performance metrics we use to validate it. In section 4, we then review two published experimental fiber-based demonstrations of QKD deployed in metropolitan environments and benchmark our simulation against those measured results. Finally, in section 5, we provide a conclusion and discussion. The appendices include the technical details of the simulation, with the mathematical models in Appendix A and the code implementation in Appendix B. The body of this paper is intended to provide an accessible description, except for necessary technical detail in the benchmark comparison section, while the appendices are intended to provide a thorough technical description.
2. Overview of QKD and supporting protocols
2.1. Background
Secure communication is a subfield of cryptography that enables the private transmission of information between users such that unauthorized access to a message’s contents is impossible or very unlikely. Many approaches to encrypting information for secure communication exist and can be categorized as either symmetric or asymmetric. Symmetric encryption utilizes the same key for both encryption and decryption. In principle, symmetric encryption achieves perfect information security given stringent restrictions on key length, key reuse, and the privacy of the key. Still, symmetric key encryption requires the often impractical step of sharing keys between users. Alternatively, asymmetric key encryption relies on two keys, one termed private and the other public, where one is used for encryption and the other for decryption. The public key is available to everyone, with the private key remaining secret. Thus, key distribution is relatively easy for asymmetric key encryption, while a mechanism for securely distributing a key between users is necessary (and non-trivial) for symmetric key encryption.
Unlike symmetric encryption, where perfect security is possible in principle, the security of asymmetric key encryption is based on the computational difficulty of inverting the so-called “one-way functions.” That is, figuring out a private key from its associated public key would require solving an intractable mathematical problem, such as integer factorization or the discrete logarithm problem. However, the discovery of Shor’s algorithm for efficiently factoring integers using a quantum computer has put the long-term security of many asymmetric encryption schemes in doubt.83,84 The rapid rise of quantum computing technology has hastened the search for alternative, quantum-safe encryption methods. Some classical approaches to quantum-secure encryption are under active investigation.85,86 These so-called “post-quantum cryptography” methods aim to identify alternative one-way functions on which to base the security of classical cryptography algorithms. Specifically, post-quantum cryptography endeavors to find the cryptosystems that are secure against attacks from both quantum and classical computers.
Another quantum-secure method of encryption is QKD, a generic term used to describe several related methods for exploiting distributed quantum systems to generate shared secret random bits between users.87–90 Once shared, these random bits can be used as a shared secret key for symmetric encryption. Security proofs of QKD depend on a restricted set of assumptions with highly capable potential adversaries that are allowed unlimited computing power. In addition, adversaries are assumed to have access to all communicated classical information and as much quantum information as is permitted by the laws of physics. In other words, in an ideal scenario, QKD is resistant even to a quantum-capable adversary.
In practice, QKD implementations may include various imperfections that expose loopholes that are exploitable, at least in principle, by an eavesdropper. 91 Significant research has been devoted to identifying and closing these loopholes with the most stringent versions of QKD, which are referred to as Device Independent QKD (DI-QKD) 92 and Measurement Device Independent QKD (MDI-QKD). 93 While DI-QKD and MDI-QKD protocols guarantee security with very few assumptions, they are technically difficult to implement. Deciding which currently available implementation of QKD to use entails considering a trade-off between security and increased technical difficulty. For example, deciding if intermediate or end nodes are trustworthy and if loss can be attributed to physical processes or eavesdroppers may result in fewer or no security assumptions but leads to lower practical key generation rates.87,88 Furthermore, it should be noted that QKD in general assumes authentication is provided a priori and has no method for establishing authentication if lost.
Due to the practical challenges of implementation,94,91 relatively low key generation rate, authentication problems, and the potential of post-quantum cryptography, QKD is not currently considered a viable strategy for quantum-proof communications by the National Security Agency. 95 We therefore emphasize that our use of QKD in this paper is not an endorsement of QKD as a field-ready technology, and that we use it because it is a relatively mature technology with a wealth of experimental results publicly available for simulation benchmarking. Furthermore, we explicitly implement an entanglement-based QKD protocol, as the distribution of entanglement is the basis of the most interesting defense-relevant quantum networking use cases. In contrast, many QKD systems use weak coherent states to achieve high secret key generation rates with decoy states added for security, 96 but these systems are not suitable as a basis for entanglement-based networks. Finally, we note that when writing this in 2022, most quantum networks in existence are utilized to perform QKD. Thus, our aim in this project is to develop a useful simulation tool for modern quantum networks as a foundation to extend to more complex quantum networking operations.
2.2. Generic QKD protocol
Many different QKD implementations exist (see Pirandola et al. 87 for a thorough review). They all require both classical and quantum communication and can generally be divided into an initial quantum communication stage followed by a classical post-processing stage. 97 We note that the quantum communication can be performed in different ways, such as using single photons, one photon of an entangled pair, or even weak coherent states.76,93,96,98,99 Each method for implementing the quantum systems required for QKD has their own implications on the security of the protocol. In Figure 1, we outline the stages of a generic QKD protocol. In the quantum communication stage, the sender, traditionally referred to as Alice, prepares a quantum state and sends it to a receiver, referred to as Bob, who measures the state and records the results. How the state is prepared, and whether it is entangled or merely describes an individual quantum system, depends on the particular implementation. In any case, the security of this stage against an eavesdropper (Eve) is derived from the so-called “no-cloning” theorem 47 of quantum mechanics that essentially states that any attempt by Eve to copy or extract information from the system during its transit from Alice to Bob necessarily disturbs the quantum system, resulting in a measurable indication of eavesdropping. Eve can make imperfect copies of quantum states and gain information about the shared key, but Alice and Bob are able to assess how much information could have leaked and compensate using privacy amplification protocols. Ultimately, this allows Alice and Bob to establish a secret key with a strong statistical guarantee that it is impractical for a potential eavesdropper to use the information obtained in quantum communication to guess the key. We refer to Alice and Bob as the “users” of QKD, while Eve is not a user.
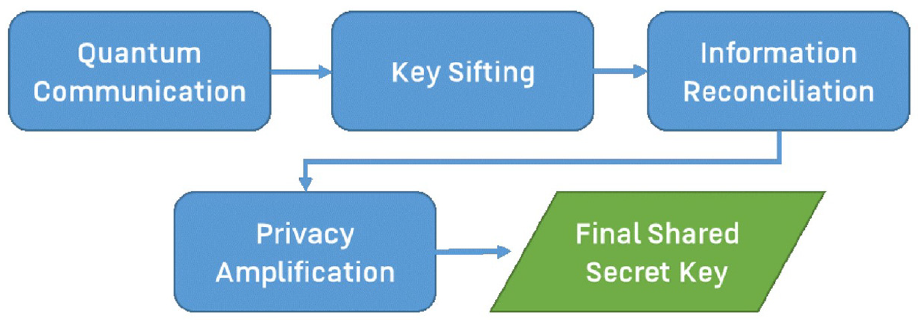
Flowchart of the stages comprising quantum key distribution, which produces an output shared secret key. QuanTACT uses SQUANCH 67 to simulate qubits in the quantum communication stage, and custom implementations of the protocols executed in all other stages.
Next, in the classical post-processing stage, Alice and Bob perform three entirely classical procedures: sifting, information reconciliation, and privacy amplification. Sifting is a method for identifying and discarding experimental outcomes that cannot generate shared random bits. After sifting, information reconciliation is used to detect and correct bit-flip errors induced by channel imperfections or, potentially, by Eve’s actions. Alice and Bob cannot distinguish between errors induced by Eve’s actions and those due to channel imperfections. Thus, for security, all errors are attributed to Eve. Finding errors necessitates revealing information about the key, which ultimately means Alice and Bob must discard some bits to ensure privacy. The number of discarded bits increases as the number of bit-flip errors increases, and the presence of too many errors can prevent generation of a shared secret key. Finally, in privacy amplification, Alice and Bob assess the amount of information Eve could have extracted from their key based on measured error rates in their system during both the quantum communication and information reconciliation steps, and they perform a distributed algorithm that results in a shared key of shorter length but of higher secrecy.
We now focus on a specific QKD protocol and describe each stage in greater detail. In particular, we choose the QKD protocol from the 1992 paper by Bennett, Brassard, and Mermin, denoted BBM92. 77 If interested, we refer the reader to Nielsen and Chuang 90 for the details of the quantum physics underlying QKD.
Fundamentally, QKD relies on Alice and Bob’s ability to each perform their measurements in one of two incompatible “bases.” Intuitively, this can be thought of as Alice and Bob each having two settings that they can choose between when measuring their individual systems, with the further caveat that whichever of the two choices is made, they learn nothing about what the outcome would have been if they had made the other choice. Practically, this “choice” can be made at random using an element that “selects” each basis option half the time without any input from Alice or Bob (see Figure 1), 75 as long as Eve does not know which basis will be used ahead of the measurement and Alice and Bob can ascertain which basis was used for each measurement.
To consider a specific example, the polarization of a single photon can be described as the superposition of two orthogonal directions, such as horizontal (H) and vertical (V). A measurement of this form can be implemented using a polarizing beam splitter (PBS) that sends input light in the H polarization to one of two output ports, and input light in the V polarization to the other output port. A single photon detector is then placed at each output to record the incident light. A photon with a polarization state which is an equal combination of H and V is equally likely to exit each of the two outputs of the PBS and generate a measurement at the corresponding detector, but a single photon can only generate detection at a single detector, so only one of those two detectors will register a detection, ultimately reporting that the photon was observed with H polarization or with V polarization. This constitutes measurement in the H/V basis. Alice and Bob can each individually choose to use a waveplate to rotate the polarization of their photon by 45° before the PBS to instead measure the polarization along the diagonal (D = H + V) and anti-diagonal (A = H − V) directions, which constitutes a measurement in the D/A basis. In the D/A basis, the detection system can report observing a photon with D polarization or with A polarization. Alice and Bob separately decide, for each measurement, whether to measure their photon in the H/V basis, or in the D/A basis. Alice and Bob both use the same binary encoding to record their measurement outcomes, e.g., when their measurement outcome is H or D, they record a 0, and when the outcome is V or A, they record a 1.
When Alice and Bob make the same basis measurement choice and the channel is ideal, entanglement ensures that the outcomes they measure are correlated (or anti-correlated). For example, if Alice measures a 1, then Bob will also measure a 1 (or 0 if anti-correlated). The correlation or anti-correlation of the measurement results is controlled by which entangled state Alice generates. A logical not operation on one user’s key transforms anti-correlated bits to correlated bits, so Alice and Bob can always generate a shared key as long as they know which entangled state is generated. QKD security proofs ensure that Eve does not know what these outcomes are and cannot obtain enough information to feasibly guess the final shared secret key that is generated from these correlated bits.
The stages of the BBM92 protocol are as follows:
Quantum Communication: Alice generates a pair of entangled qubits, such as polarization-entangled photons. She directs one of them to her measurement device and distributes the other to Bob via a quantum channel. We assume users measure quantum signals upon reception and use no quantum memory (though Eve is allowed to perform sophisticated attacks that store quantum states). Both users record their measurement results and the basis choice used for each measurement, which are both classical bits (either 0 or 1). This step is repeated many times, and Alice and Bob label their measurement records as their raw key. As we discuss in section 3.1, the raw key can contain “None” entries, which are not bits, but indications that no photons were detected.
Key Sifting: key sifting is the process in which Alice and Bob both identify which bits in their raw key can be used to distill a shared secret key. When Alice and Bob both happen to measure in the same basis, their measurement results are highly correlated and a shared key can be distilled from those bits. When they measure in different bases, their results are not correlated, and those bits must be discarded. Photons can be lost during quantum communication, where loss means that photons are directed somewhere other than the intended user, who then does not detect a photon. Alice and Bob publicly communicate after the quantum communication phase is complete to determine when they measured in the same basis and both saw outcomes, and both select those measurement outcome bits for inclusion in their sifted key.
Information Reconciliation: errors must be found and corrected to produce usable shared secret keys. Multiple approaches exist to do this (see Johnson et al., 100 for a comparison of them). We use a tree-based Cascade algorithm101,102 (see Appendix B for discussion of the tree structure), the essence of which is communicating the parity of specified subsets of the sifted key to locate and correct errors. Alice and Bob use their sifted keys as inputs to this step, and both of them get a reconciled key as the output. If information reconciliation is successful, these reconciled keys are identical. Note that some versions of this use a sampling approach where a fraction of the sifted key bits (typically 25%–50%) are used to assess the error rate and the remaining bits are kept in what we refer to as the reduced sifted key.
Privacy Amplification: the number of errors found and parity bits communicated in Step 3 are used to determine how many bits need to be discarded to ensure secrecy. There are multiple approaches available,23,103–105 and we use the Toeplitz matrices, which are essentially the hash functions that utilize efficient matrix multiplication. Alice and Bob use their reconciled keys as the inputs, and they receive their final shared secret key as the output. If the reconciled keys are not identical and even a single bit error remains, the output bit arrays will be very different. Each iteration of the QKD protocol produces one block of shared secret key. The protocol can be run multiple times to generate a larger key by combining blocks.
When the QKD protocol succeeds, it generates a shared secret key containing some number of bits. The protocol can be repeated to build up a reserve of secret key bits to enable large communications. In the presence of too many errors, it may be impossible to discard enough bits to ensure secrecy, and the protocol fails to produce a secret key. This failure marks an inability to enable secure communication, but in a broader sense, secrecy is not compromised and QKD has succeeded in denying information to eavesdroppers. Alice and Bob can try again in this instance, but just as Eve could disrupt communication lines, her persistent presence could render a QKD connection unable to generate shared secret keys—a denial of service attack. Another practical challenge to consider is that information reconciliation is not guaranteed to find every error, and even one residual error can lead to users having different “keys.” Encryption will not work properly in this case, and Alice and Bob will not know that the problem has occurred. The protocol should be configured to protect against this outcome, but there is a trade-off that more thorough checks for errors cost more bits and ultimately reduce the key generation rate. We check that keys are identical in simulation for diagnostic purposes.
Finally, we want to note a few basic assumptions inherent to QKD:
User facility security: Eve is assumed to not have access to user locations.
Authenticated communication: Eve is assumed not to be able to impersonate other users on the public channel.
Basis alignment: Alice and Bob have established a shared reference frame, meaning that if Alice prepares and sends light of a certain polarization, Bob’s laboratory receives that same polarization (or, in practice, knows what rotation he needs to apply to “undo” rotations caused during transmission). This amounts to ensuring that Alice and Bob actually measure in the same basis when their apparatuses are set to do so.
Although QKD is generally a “point-to-point” protocol involving only two nodes, there are several avenues for extension to larger multi-user networks. The nearest term version of this is the creation of “trusted node” networks where this protocol is performed independently across multiple point-to-point connections, and keys are combined with bitwise XOR operations and public communication. 106 In the context of trusted node QKD networks, there are many options available for the ordering and location of post-processing tasks. These have been explored in the DARPA quantum network testbed, 107 e.g., where all-to-all classical connectivity was assumed between nodes and certain aspects of post-processing were delayed and only performed at the end nodes rather than at each intermediate node. Other theoretical work related to how the delay of post-processing steps impacts security is explored in the literature.108,109
3. Overview of simulation framework
This section provides a brief overview of the QuanTACT framework for the simulation of tactical quantum networks. In particular, we describe extensions we made to SQUANCH67,110,111 explicitly aimed at simulating entanglement-based QKD experiments. We refer interested readers to Appendix A for more details of the modeling that is implemented in SQUANCH and to Appendix B for details about the simulation code environment. Specifically, we make custom modules to perform all steps discussed in Figure 1, including implementations of the Cascade protocol for information reconciliation, the Toeplitz-based privacy amplification, and accurate fiber-optic channel models.
As shown in Figure 1, QKD consists of an initial quantum communication step where measurement records, consisting of classical bits, are generated. After that, all communication and information processing is classical. The relative simplicity of SQUANCH, its parallelized agent-based design, and its open-source nature makes it ideal for integration into other systems. SQUANCH can, in principle, simulate general quantum computations. We utilize the SQUANCH agent framework and simulate quantum communication using its modules for handling the stream of quantum states (QStream), quantum gates, errors, and channels. Using this foundation, we implement SQUANCH agent behaviors, and we develop custom models for timing and classical protocols for information reconciliation and privacy amplification.
This paper focuses on QKD between two agents (Figure 2), which forms a primitive protocol that can be extended to multi-agent networks. Eve is implemented as an intermediate agent that passes through classical and quantum information, but does not modify quantum states. The classical channels considered herein are idealized and transmit messages without errors and without detailed consideration of the classical networking infrastructure used to convey them. However, we have designed our framework such that the classical channels considered here can be easily replaced by detailed EMANE classical communication models to simulate tactical scenarios.
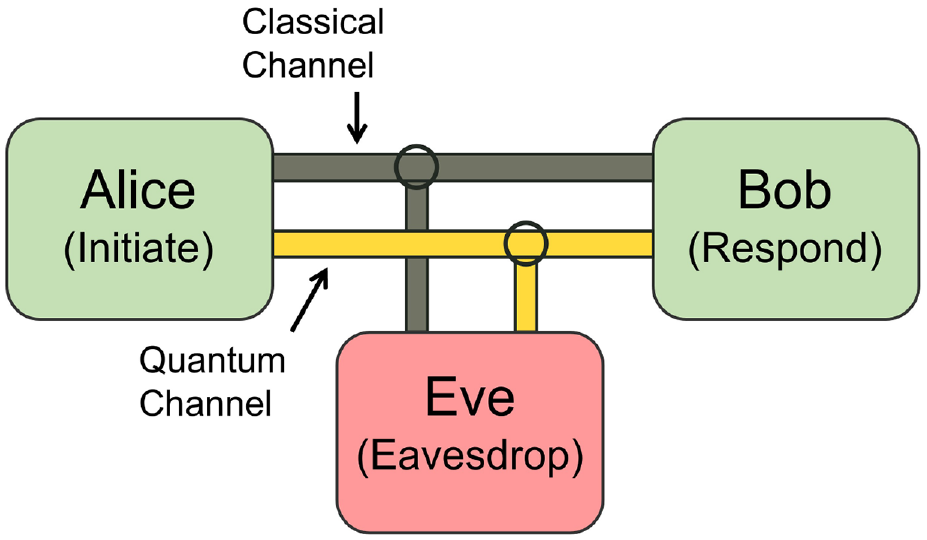
Illustration of agents Alice and Bob connected by quantum and classical channels. Example agent behaviors are labeled in parentheses. QKD security proofs guarantee that the secret key is known to Alice and Bob even if an eavesdropper (Eve) is assumed to have full knowledge and control over the channels and can extract the maximum amount of information allowed by physics.
Simulation of realistic quantum networks can require large amounts of memory and computation time, so it’s beneficial (and sometimes necessary) to determine what properties of the network require explicit modeling and what can be computed or implicitly modeled without degrading simulation accuracy (see Appendix A). Our simulation does not fully emulate the state of every network element and relevant phenomenon, but rather focuses on events that can lead to measurement outcomes and affect the performance of QKD. For example, explicitly including all loss sources can become very resource-intensive in high-loss networks, so an alternative is to account for the loss by decreasing the effective probability of successful photon-pair generation. This reduces the number of quantum communication events considered instead of spending compute time performing calculations for events that will not impact QKD performance. We refer to loss modeled in this way as implicit loss, while we refer to loss which is directly included in a channel model as explicit loss.
The entangled photon source (EPS) in our simulation is assumed to produce ideal polarization-entangled photon-pair states with no consideration of multi-photon effects or imperfect state visibility (further detail in Appendix A). Thus, the simulation considers a series of ideal entangled qubit pairs in an SQUANCH
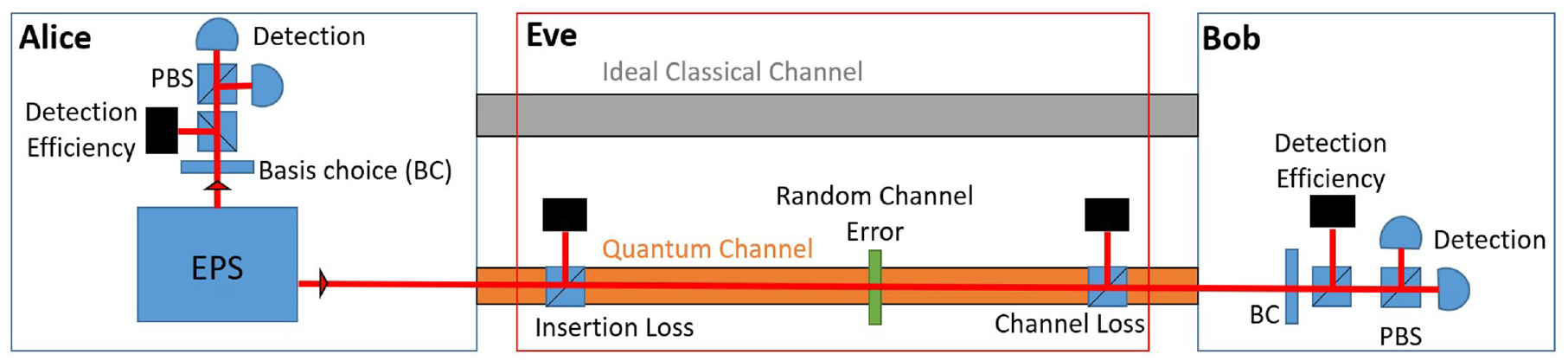
Illustration of an effective optical hardware setup. One photon from each pair is directed to Alice’s detectors and the other is sent through the quantum channel to Bob. BC is the basis choice, e.g., an ideal fast variable waveplate with two settings that chooses the measurement basis for each measurement. All non-polarizing beamsplitters have reflectivity according to the loss they model. Channel loss accounts for the loss per unit length light experiences while propagating in the fiber. All loss at fiber inputs, outputs, and interfaces is combined into a single insertion loss coefficient Λ. Eve is assumed to have maximal information allowed by physics, and thus all errors are attributed to Eve and all information sent through a channel can be measured by Eve.
3.1. Performance metrics, errors, and the fiber channel model
The primary figure of merit we use for quantifying QKD performance is the
Our fiber channel model uses two error types. Optical fibers are excellent at directing light with low loss, but they are imperfect and some fraction of input light will not reach Bob’s detection system, resulting in
In addition, polarization-encoded qubits experience a polarization rotation due to the birefringence of the fiber. This is the second type of error included in our fiber channel model and is shown as the
These bit-flip errors are deleterious in more than one way. Since errors are attributed to Eve, Alice and Bob must perform privacy amplification and effectively discard bits to compensate for information Eve may have obtained. In addition, the secret keys shared by Alice and Bob must be identical in order to be useful, so bit-flip errors must be located and corrected. This search necessitates further revealing bits to perform information reconciliation.
An important quantity for characterizing the likelihood of bit-flip errors is the
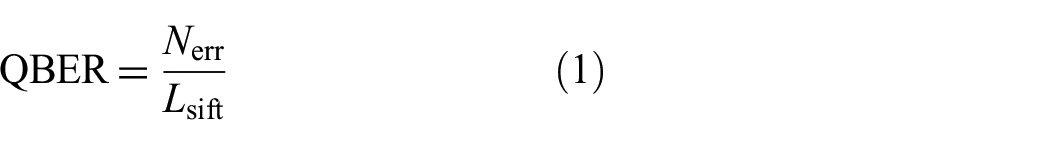
where

For
4. Benchmarks
We validate our simulations against published experimental data to demonstrate that our simulation replicates reported results. We refer to these two experiments as the Zeilinger (Z) benchmark 74 and Ling (L) benchmark. 75 Both experiments use polarization-entangled photon pairs which are generated by spontaneous parametric down conversion sources, distributed through optical fiber between two agents (Alice and Bob), and measured using a BBM92 QKD scheme. 77 The primary quantities we aim to replicate are the QBER and secret key generation rate.
4.1. Z benchmark
The Z benchmark performs QKD over a 1.45-km long fiber deployed underground in the Vienna sewer system, where it is subject to realistic environmental conditions including the strain induced in installation and temperature fluctuations. 74 We summarize the parameters used to simulate this benchmark in Table 3. We started by including all loss explicitly specified in the paper, including the fiber propagation loss and additional loss from coupling into and out of the fiber. However, the key lengths indicate additional loss must have been present, as we now explain.
The experiment generates 100 blocks of sifted keys with an average length of
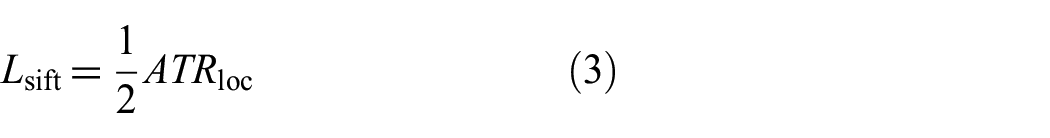
where the factor of 1/2 is the average fraction of the time that Alice and Bob’s randomly selected bases match, the transmission factor
The Z benchmark specifies a total channel loss of 6 dB, including endpoint losses. This value is not consistent with the sifted key length calculation above. Thus, instead of using the endpoint loss derived from their implied value, we use the value calculated in equation (4) to account for the additional unspecified loss. This adjustment produces simulated block lengths that agree with the reported experimental values. The detector quantum efficiency is unspecified in the Z benchmark. While this quantity is a useful parameter for understanding and bounding channel performance, it does not need to be explicitly specified to reproduce these results (see Appendix A).
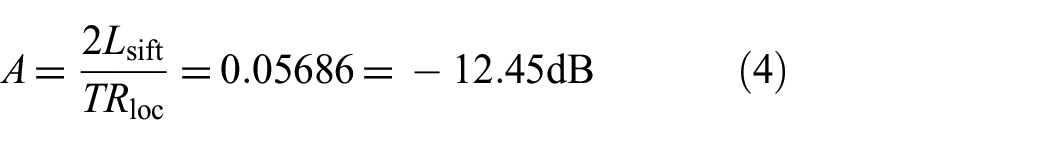
We simulate 100 blocks and compare them to the published results (Figure 3 in Poppe et al. 74 ) in Figure 4. The Z benchmark uses a sample of the sifted key to calculate an estimated error rate (which we call the estimated QBER) and sorts their data into ascending order according to this value. In addition, they report the real (sifted key) error rate. We do the same. The mean values and standard deviations for the relevant quantities are summarized in Table 1.
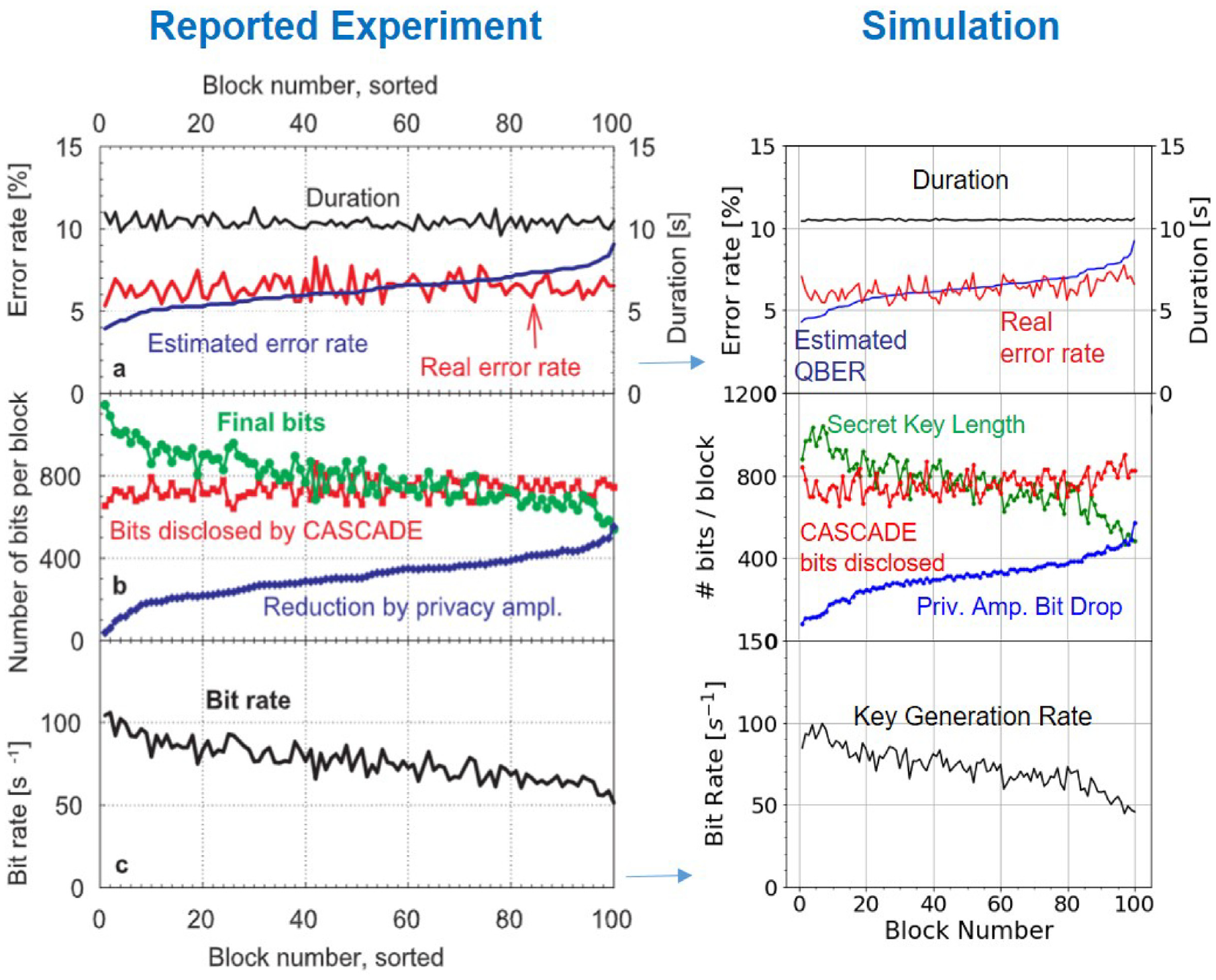
Comparison of our simulation results for a 100 block run to published benchmark results. The experimental data on the left are reprinted with permission from Poppe et al., 74 © The Optical Society. The range of the simulation plots matches those of the benchmark figure.
Z benchmark: comparison of the mean average values plus or minus the standard deviations for simulated QKD performance metrics and the reported average experimental values.
QBER: quantum bit error rate; NS: not specified in the Z benchmark.
The Cascade bits disclosed quantity is calculated from the reported bit reduction attributed to the error correction process
Overall, the agreement between simulated and reported results is excellent. Every quantity besides the duration looks to span approximately the same range with roughly the same characteristic shape. The results are stochastic, so exact agreement is not expected. As discussed in Appendix A, this benchmark subtracts an offset from their estimated QBER when calculating how many bits to remove in privacy amplification, and we replicate that here to reproduce their results [see equation (24)]. This benchmark paper does not use a security parameter to set a floor on how many bits are dropped, but our setting of
The Z benchmark does not specify exactly how the block duration is set and exhibits a range of durations for each block. We use a model set with a duration parameter aimed at the average of the published duration data, so our more uniform duration results are expected.
4.2. L benchmark
The L benchmark also tests QKD performed over a fiber deployed in a metropolitan environment. The experiment differs from the Z benchmark experiment in the following noteworthy ways:
They use a longer fiber (10.4 km vs 1.45 km) at a wavelength with lower loss per unit length (1320 nm vs 810 nm).
Total channel loss of −8 dB, of which −4 dB is propagation loss, and −4 dB is from patching and splicing.
Detector quantum efficiency is specified.
Correlated source (L) versus anti-correlated source (Z).
Modified cascade protocol.
We consider loss from the polarization control system implicitly as a local transmission probability (see Appendix A). We also account for light lost due to detector quantum efficiency implicitly by modifying the success probability according to the specified
The L benchmark paper indicates that their Cascade information reconciliation algorithm is based on Sugimoto and Yamazaki, 102 but they do not specify the modifications from the original Cascade algorithm. We use a version of Cascade that uses 3 core Cascade passes and 10 Sugimoto biconf runs (see Appendix B). Note that we do not perform QBER error sampling in this version of Cascade, but instead use the number of errors found during Cascade to calculate the QBER [equation (1)]. Our initial Cascade block size is set using an assumed QBER of 7%. We also check if there are uncaught errors in Alice’s and Bob’s secret keys and find none. That is, the secret keys shared by Alice and Bob are confirmed to be identical. Figure 5 shows our simulation results plotted next to the reported results from the L benchmark paper. 75 The average values for relevant QKD performance quantities are summarized in Table 2.
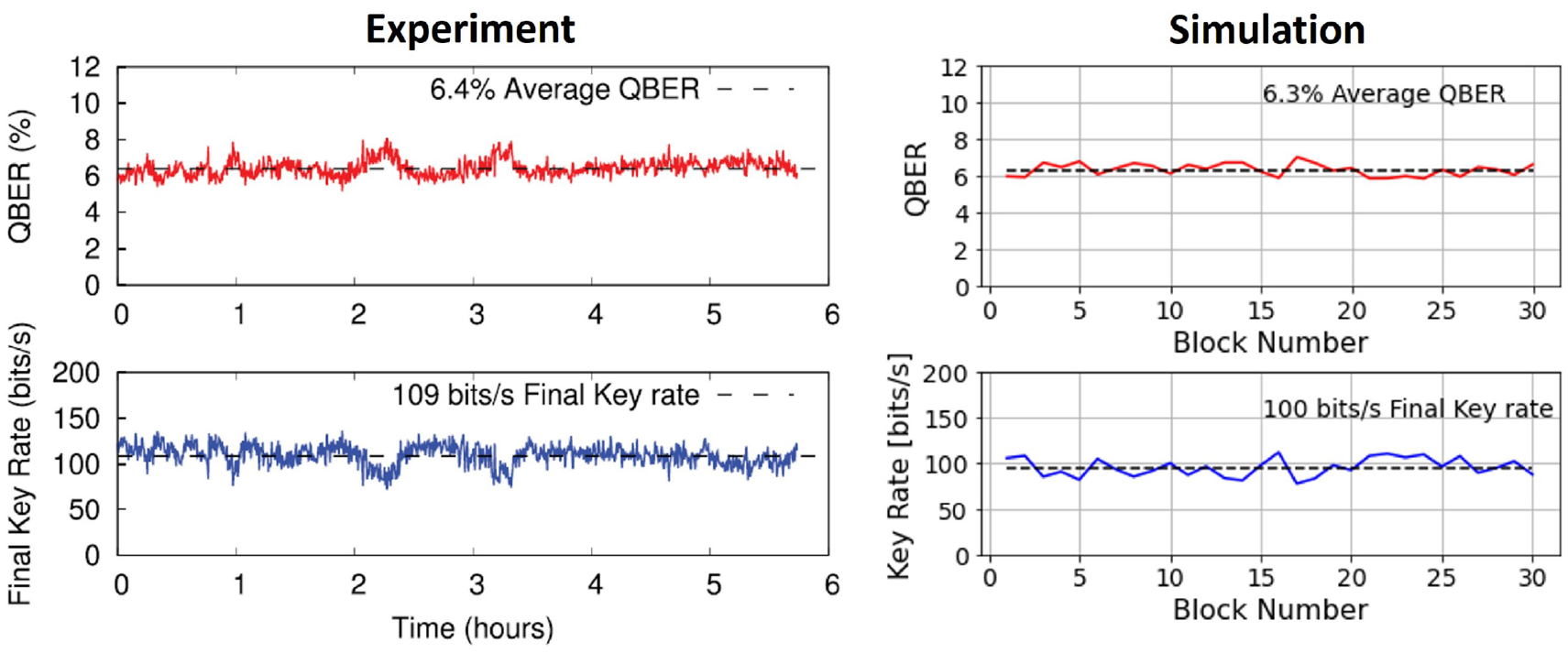
Comparison of experimental and simulated QBER and secret key generation rates for the L benchmark. Left: experimental data reprinted from Shi et al., 75 with the permission of AIP Publishing. Right: simulation results. The vertical scales are matched between experimental and simulation results, while the horizontal scales differ.
L benchmark: comparison of the mean average values plus or minus the standard deviations for simulated QKD performance metrics with the reported average values.
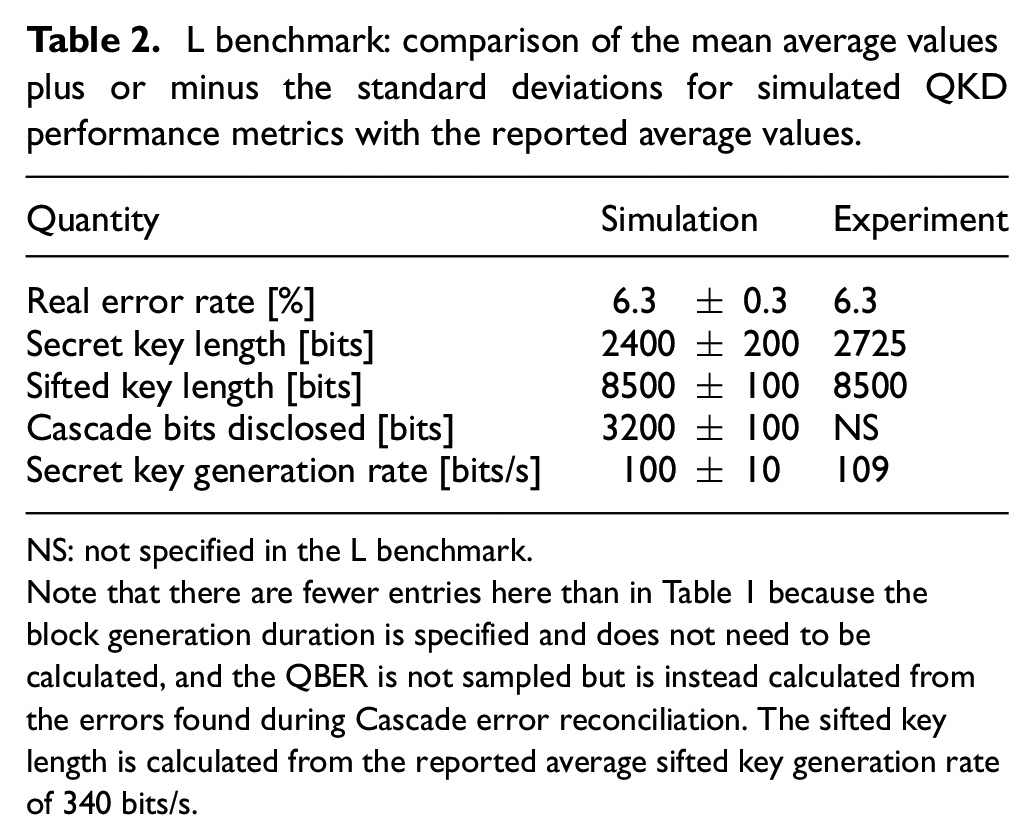
NS: not specified in the L benchmark.
Note that there are fewer entries here than in Table 1 because the block generation duration is specified and does not need to be calculated, and the QBER is not sampled but is instead calculated from the errors found during Cascade error reconciliation. The sifted key length is calculated from the reported average sifted key generation rate of 340 bits/s.
Each block corresponds to 25 s of time in the experimental plot, so our simulation spans 12.5 min of QKD, which is sufficient for comparison. There is time-dependent variation in the experiment that we do not include in our model. The simulated QBER is statistically consistent with the reported average result. Note that the L benchmark text specifies an average QBER of 6.3% while their figure is labeled with 6.4%. The key generation rate is slightly lower than the average experimental reported value while the sifted key lengths are consistent. This indicates a slight difference in classical post-processing after key sifting (Figure 1) and likely stems from differences between our Cascade implementations. Even so, the simulated secret key generation rate is within one standard deviation of the average reported value, and the agreement of the sifted key lengths validates the accuracy of the channel model. We consider these results a compelling approximation of the actual measured QKD performance.
5. Conclusion and discussion
In this paper, we have presented a framework for simulating entanglement-based quantum networks in Python and with SQUANCH. Our QuanTACT simulation framework is specifically designed for compatibility with existing emulation frameworks for classical tactical networks, thus enabling detailed simulation of quantum networks and their applications. To benchmark the performance of our simulation and its associated channel models and subroutines, we have modeled two different published experiments that performed QKD in metropolitan environments using entangled quantum states. In each case, we were able to produce compelling approximations of the experimental results.
Although this paper focuses on the simulation of entangled quantum systems, several design choices have been made to ease the integration of our newly developed tools into existing emulation frameworks for classical tactical networks. In particular, we chose to use the SQUANCH quantum networking tool as the basis for our framework as it uses an agent-based model and enables fully parallelized simulations with each agent running on its own process.67,111 Such a distributed architecture is consistent with the EMANE.79–82 Furthermore, EMANE classical communications techniques can be used as a “drop-in” replacement for those available in SQUANCH. Integration of our new tool with EMANE is underway, and a future paper will discuss details of the integration process and tactical simulation results.
In summary, we use QKD in this paper to benchmark our simulations because of the relative maturity of QKD as a commercial technology with a wealth of available experimental results that illuminate the performance of modern quantum networks. Since we have specifically implemented an entanglement-based QKD protocol, our underlying framework is readily extensible to more complex quantum networking applications. Furthermore, the novel channel models developed here can be directly applied to simulations of other quantum networking applications in the future. The QuanTACT framework developed in this manuscript offers a direct route toward integrating quantum networking and quantum communication protocols into existing tactical network simulation and emulation environments, making a valuable tool for generating a more nuanced understanding of how the rise of quantum technology will impact the warfighter.
Footnotes
Appendix A: Implementation of QKDsimulation framework
This section details the physical modeling that underlies our simulation framework.
Appendix B: QuanTACT Simulationenvironment
Our implementation of the QKD protocol presented in this paper is built in the Python programming language. The simulations use the SQUANCH library for the core functionality of creating quantum networks. We have added several features that help enable the development of quantum network protocols and declare configurations of quantum networks. This section outlines those features and how they are used to build the QKD protocol.
Acknowledgements
The authors acknowledge Jake B. Perazzone and Eric Graves for helpful conversations. This class file was developed by Sunrise Setting Ltd, Brixham, Devon, UK.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
