Abstract
Cognitive radio is a promising technology for frequency allocation to improve the spectrum utilization efficiency of licensed bands. However, in recent years, the attention of the researchers is focused on security issues that have to be faced by cognitive radio technology. One of the most important issues consists of radio frequency jamming attacks, where adversaries can use on-the-fly reconfigurability and learning capabilities of cognitive radios in order to devise and deploy advanced jamming tactics. Jamming attacks can noticeably affect the performance of wireless communication systems and can lead to significant overhead in terms of data re-transmission and increased power consumption. In this article, a novel compressed sensing-based jammer detection algorithm is proposed using cyclic spectral analysis and artificial neural networks for wideband cognitive radios. A wideband spectrum is considered that is composed of multiple narrowband signals. Narrowband signals can be legitimate or jamming signals. Compressed sensing is used to reduce the overhead of the analog-to-digital conversion and it allows one to estimate a wideband spectrum with sub-Nyquist rate sampling. After the signal has been estimated, the second-order statistics, namely, spectral correlation function, is computed to extract cyclic features of the wideband signal. Finally, a pre-trained artificial neural network is proposed to classify each narrowband signal as a legitimate or jamming signal. Performances of proposed algorithm are shown with Monte-Carlo simulations under different empirical setups.
Keywords
Introduction
Over the years, spectrum resources are becoming more and more expensive; for example, industrial, scientific, and medical (ISM) bands are clutched and busier than ever. However, the licensed spectral bands are reported as under-utilized (spectrum holes) by the Primary Users (PUs). Cognitive radio has been proposed to allow opportunistical usage of the licensed bands by Secondary Users (SUs) without causing interference to PUs. This is one of the reasons why cognitive radio has obtained great attention from wireless communication community in recent years. A cognitive radio dynamically interacts with the environment, and it adapts the operating parameters according to the purpose of dynamic spectrum access/opportunistic spectrum access (DSA/OSA).1,2 In order to discover spectrum holes, spectrum sensing is the primary task needed to be performed. 3
In the literature, various spectrum detectors have been proposed for cognitive radios, such as matched filter detector (MFD), energy detector (ED), and cyclostationary feature detector (CFD).
4
The MFD can detect the primary signals with good performances, but the overall prior knowledge is needed for the PU’s signal. Furthermore, MFD performances degrade in non-stationary environments. The ED is easy to implement, and usually, it shows good performances in low-noise environments. ED is included in the IEEE 802.22 standard for spectrum sensing. However, it fails at low signal-to-noise ratios (SNRs). In most cases, spectrum sensing is needed to detect the weak primary signals accurately. Therefore, another typical spectrum detector called CFD has been proposed to significantly improve the detection rate of the PU signals. CFD is able to accurately detect and even classify the primary signals’ different modulations under low SNR conditions, thanks to its cyclic frequency features. Such performances are achieved at the cost of increased implementation complexity. CFD uses the cyclostationarity of the modulated primary signals by detecting spectral peaks by means of the spectral correlation function (SCF) or spectral coherence function (SOF),5–7 which are sparse in both angular
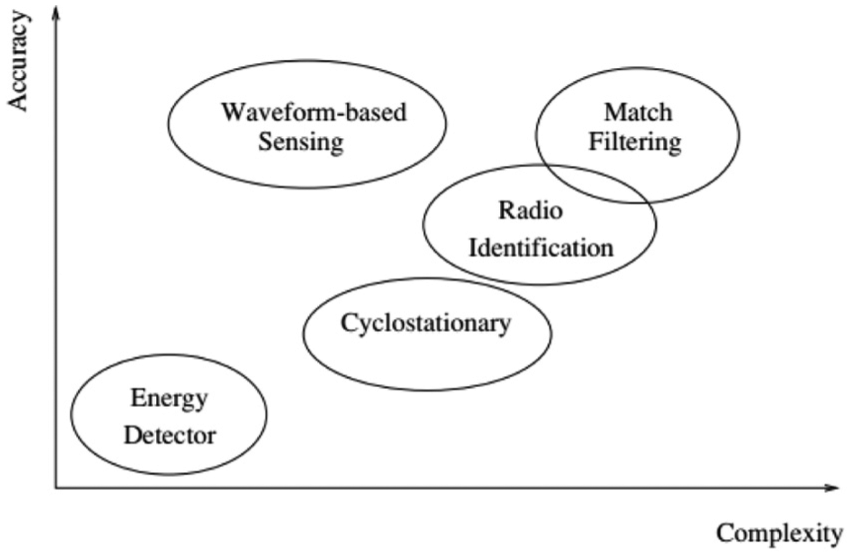
Accuracy versus computational complexity of spectrum sensing detectors.
When cognitive radios are operating on a wideband (from few hundred MHz to several GHz), the sensing task becomes more complex. A large overhead is imposed to the spectrum sensing system due to the high-rate sampling. Analog-to-digital (A/D) converter and heavy memory usage are particularly affected. Compressive sensing (CS) 12 is an interesting solution to alleviate requirements of high sampling rates provided that the signal is sparse in an appropriate transform domain. Signal sparsity is the main requirement for CS to work, and in the case of cognitive radio networks, it can be a practical assumption because not all frequency bands are occupied all the time in all geographical locations. 1 Therefore, spectrum of the cognitive radio network can be considered sparse in the frequency domain due to low occupancy by the PUs. CS requires non-linear optimization to find an optimal solution through signal estimation, and this could be achieved by means of greedy algorithms such as Matching Pursuit (MP) 13 or Orthogonal Matching Pursuit (OMP). 14 The other solutions in literature are based on the use of Convex Programming as in Basis Pursuit (BP). 15 Then, CFD needs to estimate the SCF of the received wideband (WB) spectrum from sub-Nyquist samples. A possible approach 16 is to first recover Nyquist samples from sub-Nyquist samples; and then, it is necessary to estimate the SCF and perform feature extraction. To perform Nyquist sample recovery, Mishali and Eldar 17 used modulated wideband converter (MWC). However, a different method is adopted in Tian and Colleagues,18,19 where they perform SCF estimation directly from sub-Nyquist samples by exploiting the sparsity in two-dimensional SCF domain.
Radio frequency (RF) jamming is the process of transmitting illegitimate signals on one or more occupied channels with the objective of disrupting the communication of the targeted system. Jamming and anti-jamming concepts are as old as radio communications itself, but recent development in cognitive radio technology has permitted devising and deploying of more advanced, self-configurable jamming 20 and anti-jamming 21 solutions. Spectrum sensing plays a key role in designing anti-jamming systems. This spectrum sensing information can be used to detect potential jammers 22 and to take proactive measures to ensure communication continuity and security. Furthermore, an observation set can be maintained over the time and used to employ more effective anti-jamming tactics. For example, when a frequency hopping spread spectrum (FHSS)-based system is used, cognitive radio can modify its hopping sequence to avoid the channels which are occupied by jamming entities. 23 In order to design an appropriate anti-jamming system, there is a need for a reliable jammer detection algorithm.
In this work, we propose a new jammer detection algorithm for WB cognitive radios. The first step is to recover the Nyquist rate WB spectrum, which consists of various narrowband (NB) signals, from sub-Nyquist samples using CS. To this end, conventional BP technique
15
is used. The reconstructed signal is then fed to the CFD to estimate the SCF of the WB signal. The cyclic frequency profile
The rest of this article is organized as follows. Section “System model and problem formulation” presents the system model and problem formulation. Section “Proposed algorithm” outlines cyclostationary spectral analysis, neural network classifier, and proposed algorithm. Experimental results are described in section “Experimental results and discussion,” whereas conclusions and future road map are presented in section “Conclusion.”
System model and problem formulation
A received WB spectrum of
where

(a) Wideband spectrum divided into multiple sub-bands (SB), and each SB is occupied by a narrowband signal. (b) Narrowband jammer (Tone) jumps to the neighboring SB to jam licit (BPSK or QPSK) signal.
For our proposed system, the jamming signal is considered as being centered at one of the NB signal frequencies with an equal bandwidth. The jammer is considered to be a cognitive jammer, which can detect and analyze carrier frequencies of legitimate signals to have perfect knowledge of current spectrum occupacy and used modulations. This jammer can jam any of the SBs, if it has higher power than the legitimate signal as depicted in Figure 2(b). The tone jammer is very successful against NB signals, due to the fact that it allows to concentrate all power on a single-data channel. The tone jamming is often considered as the best strategy for jammers with limited transmission power.
24
Let us assume that the targeted signal is QPSK-modulated and uncoded, and that targeted system uses the coherent detection. Then, the error probability
here,
Proposed algorithm
In this section, we first introduce SCF, CS, and ANN, and finally, the new proposed algorithm is presented.
Cyclostationary spectral analysis
A process
The autocorrelation function of a wide-sense cyclostationary process can be expressed in terms of its Fourier series components
where
The Fourier transform of the CAF is known as SCF and is given by
where
The major benefit of spectral correlation is its insensitivity to background noise. Since noise occupies the same spectral band as the signal, there is no way to separate the noise from the signal’s PSD. However, as spectral correlation measures the temporal correlation of different frequency components, the noise does not play a significant role in the computation of SCF. The reason behind this is that noise is a wide-sense stationary process, and therefore, the spectral components of noise are uncorrelated in time. This fact allows the spectral correlation of a signal to be accurately computed even at low SNRs. Furthermore, different types of modulated signals (BPSK, AM, FSK, minimum-shift keying (MSK), QAM, and pulse-amplitude modulation (PAM)) with overlapping power spectral densities have highly distinct SCFs. Our simulations are restricted to the BPSK and QPSK modulation schemes due to the fact that higher order QAM and PSK do not exhibit second-order periodicity but the same features as QPSK. Therefore, these signals can be distinguished by higher order spectral analysis. 25 An example of SCF of a WB signal is depicted in Figure 3.
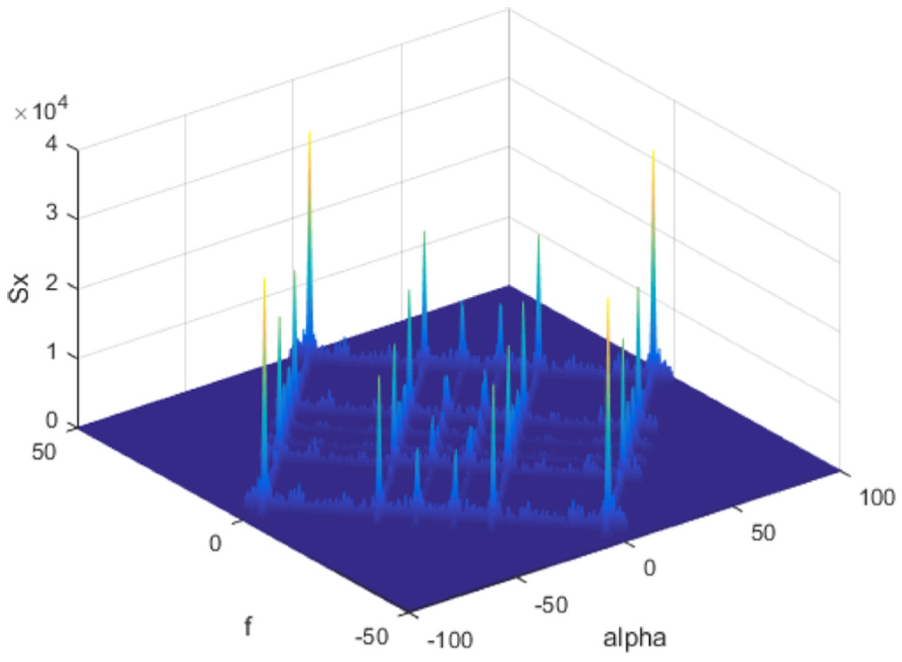
SCF of a wideband spectrum hosting BPSK- and QPSK-modulated signals and a non-modulated tone signal.
SCF computation requires large amount of data, which makes it unreasonable for a classifier to operate on it in real time. We used here

Cyclic frequency profile of a wideband spectrum hosting BPSK and QPSK and a tone signal at different cyclic frequencies.
Compressed sensing
This section presents an overview of CS process. The frequency response of the observed WB signal shown in equation (1) can be obtained through
where
where
where
where
This optimization problem can be solved, for example, by means of convex programming as in BP.
15
After the reconstructed Nyquist rate WB signal has been obtained from sub-Nyquist samples, CFD can be used to estimate the SCF of the reconstructed signal. The estimated SCF in this case is definitely dependent on how well the WB signal was estimated from CS, which in turn depends on the sparsity of the signal and the compression rate. The procedure of SCF computation is given in previous section. Then, the features are extracted from obtained SCF of the WB signal and used to train ANN. The
Neural network classifier
The proposed system uses an ANN as classifier due to the simple implementation and the ability to generalize any parameter, such as carrier frequency, symbol rate, phase offset, and compression ratio. The system is designed to classify signals as BPSK, QPSK, Jammer (single tone), QPSK plus Jammer, and BPSK plus Jammer. This is done with one ANN, which is trained to identify the above five classes of signals. The SCF of WB produces a large amount of data, which makes impossible for a classifier to work on it in near real time. In order to reduce the amount of data for the classification stage, we used
The selection of a single hidden layer is proposed due to the classification process simplicity of this particular problem. It was found that with a single hidden layer ANN, an overall accuracy of
A total of
From Figure 5, it is possible to observe that the architecture of

Neural network performance for different number of neurons.
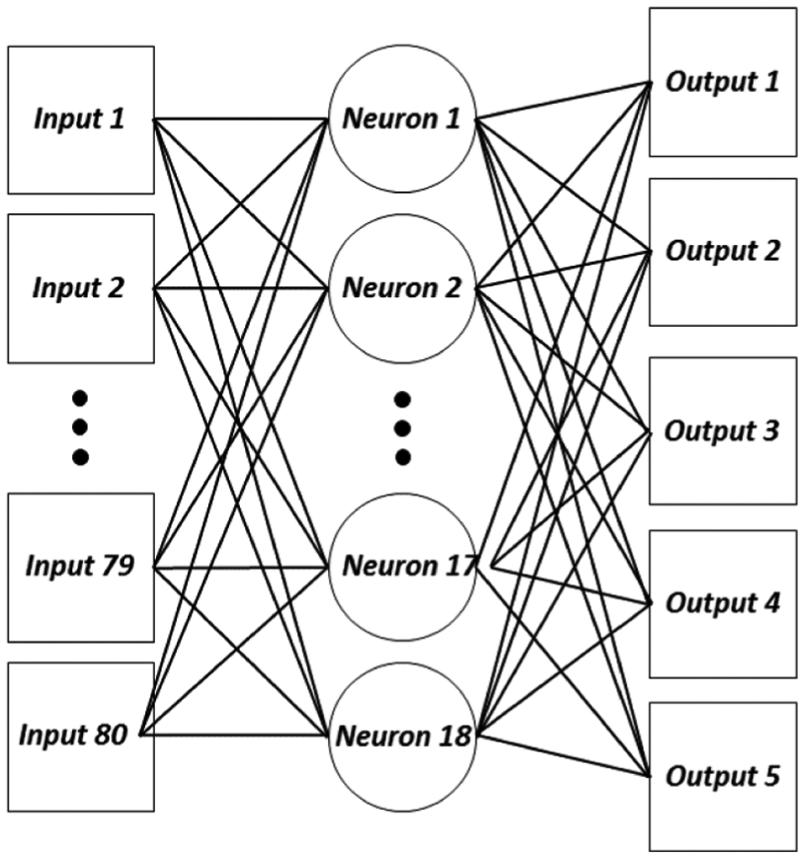
Proposed neural network.
The proposed algorithm can be summarized as follows: the receiver observes a WB spectrum, which consists of multiple NB signals. The compression ratio is set to a particular value and WB is randomly sampled. Then, the measurement matrix,

A generic block diagram of the implementation of proposed algorithm.

In this work, two different approaches are adopted to train ANN. In first case, the ANN is trained at Nyquist rate, while in second case, it is trained for different compression ratios. In both approaches, the ANN is then tested against different compression ratios.
Experimental results and discussion
A WB spectrum of
Proposed classifier
Both ANNs, selected based on the process described in neural network classifier section, are trained with
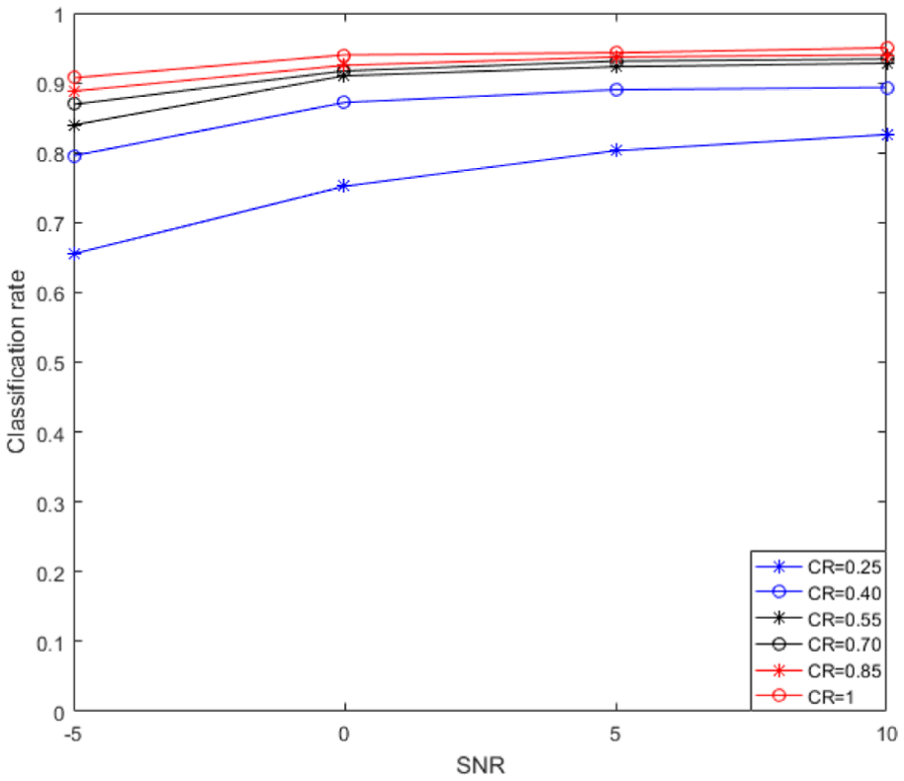
The performance of both systems is further evaluated for independent test signals, with different compression ratios and SNRs (

Performance comparison of the two proposed ANN-based classifiers. One is trained at Nyquist rate samples and the other is trained with samples obtained with different compression ratios.
Jammer detection rate
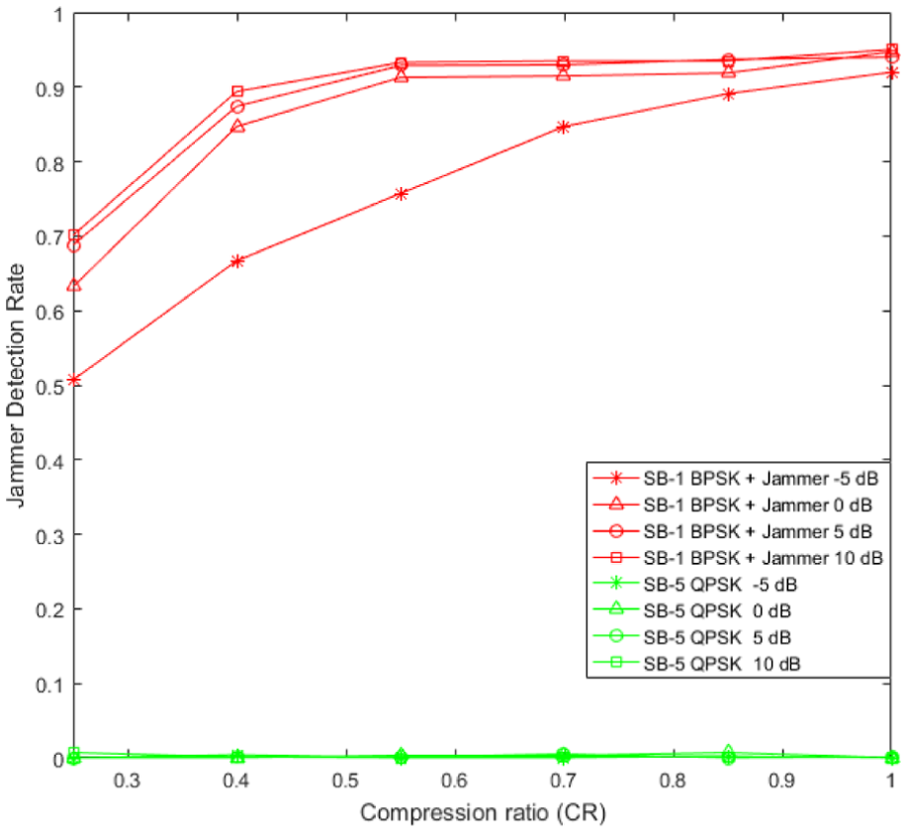
Figure 9 shows the jammer detection rate versus the compression ratio for occupied SBs. It can be noticed from Figure 9 that at

Performance of jammer detection algorithm over various compression ratios and SNRs. SB-1 is used by BPSK signal, SB-5 is occupied by QPSK signal, and SB-3 is occupied by jammer.
Jammer detection rate versus the compression rate is plotted in Figure 10 for second test configuration where the jammer jumped into SB-5 to jam the licit QPSK signals. It can be seen that the jammer detection rate falls to

Performance of jammer detection algorithm over various compression ratios and SNRs. SB-1 is occupied by BPSK signal, while jammer has jumped from SB-3 to SB-5 to jam QPSK signal.
In third test configuration, the jammer jumped to SB-1 in order to jam the BPSK signals. The jammer detection rate in this case is shown in Figure 11. The jammer detection rate is
Performance of jammer detection algorithm over various compression ratios and SNRs. SB-5 is occupied by QPSK signal, while jammer has jumped from SB-3 to SB-1 to jam BPSK signal.
The proposed algorithm performance is compared with the study by Mughal et al.,
22
and it can be seen from Figure 12 that the usage of ANN not only increases the classification rate but also greatly improves the jammer detection rate. In Mughal et al.,
22
classification was made based on simple comparison of parameters from database. The robustness of the algorithm is shown in Figure 13. It can be seen, even for low compression ratio of

Performance comparison with database matching method.
Robustness of proposed algorithm.
The purpose of the proposed algorithm is also to determine an optimum value for compression ratio and SNR, which reduces the overall cost of the system under consideration. The signals can be further categorized into two broad classes: licit signals (BPSK, QPSK) and illicit signals (Jammer, BPSK plus Jammer, and QPSK plus Jammer). The illicit case is more harmful for any communication system, and the SBs occupied by these signals must be avoided. Table 1 presents the classification rate for
Signal classification for CR = 0.40 at −5 dB.

BPSK: binary-phase shift keying; QPSK: quadrature-phase shift keying; CR: cognitive radio.
Table 2 shows signal classification rate at SNR
Signal classification for CR = 0.40 at 0 dB.

BPSK: binary-phase shift keying; QPSK: quadrature-phase shift keying.
Therefore, by analyzing Figure 8 and Tables 1 and 2, it can be concluded that a
This work considered a constant jammer that sends out random bits without following any medium access control (MAC)-layer protocols. It will be interesting to use this algorithm to detect other types of jammers, for example, deceptive and reactive jammers. 24
Conclusion
In this article, a cyclic features–based jammer detection algorithm is proposed for WB cognitive radio using ANN. The WB signal is considered to be composed of several NB signals. To reduce the A/D complexity, CS was used for recovering the Nyquist rate samples of the WB signal from sub-Nyquist sampling. The recovered WB signal was then fed to the CFD to compute the SCF of the signal. The
In the end, algorithm determines the optimum value for compression ratio and SNR in order to reduce the sensing energy and to work in an environment where noise level exceeds the signal level. The algorithm classifies the signals with a high accuracy in noisy channels and can save more than half of the sensing energy. Additionally, such a jammer detection algorithm could be helpful in formulating intelligent anti-jamming strategies for WB cognitive radio systems.
In future work, more sophisticated jamming attacks, such as deceptive and reactive jamming attacks, will be considered. The deceptive jammer is one that transmits regular packets into the channel, following the physical and MAC layer protocol. However, reactive jammer is equipped with sensing ability and only transmits when there is an activity on channel. Furthermore, these jammers may have the learning ability. These types of jamming attacks are hard to detect and hence present potential future research topic.
Footnotes
Acknowledgements
Carlo S Regazzoni has contributed to produce this work partially under the program UC3M-Santander Chairs of Excellence.
Handling Editor: Al-Sakib Khan Pathan
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.














