Abstract
In vehicular ad hoc network, wireless jamming attacks are easy to be launched in the control channel and can cause serious influence on the network performance which may cause further safety accidents. In order to address the issue of wireless jamming attacks, a new technique which localizes the jamming attackers and prevents vehicles from jamming through human intervention is proposed. In this article, we propose a range-free approach to localize the source of the attacker and determine the number of jamming attackers. The data set is the locating information and the jamming detection information associated with each vehicle. Then, we formulate the problem of determining the number of attackers as a multiclass detection problem. We define the incorrectly classified area and use it to measure the distance between samples and centroids in fuzzy c-means algorithm. We further determine the number of jamming attackers through the coverage rate of beaconing circles and utilize weight-based fuzzy c-means to classify the data set. When the data set is classified as acceptable, we further explore the means of using particle swarm optimization algorithm to calculate the positional coordinates of each attacker. We simulate our techniques in MATLAB, and both urban traffic area and open area are considered in our simulation. The experimental results suggest that the proposed algorithm can achieve high precision when determining the number of attackers while the result of the classified performance is always satisfying. Our localization results lead to higher accuracy than other existing solutions. Also, when the data set is limited, the chances of taking accurate localization are higher than other measures.
Keywords
Introduction
Vehicular ad hoc network (VANET) is a type of self-organized peer-to-peer (P2P) wireless network formed by on-board units (OBU; e.g. vehicles) and roadside units (RSU). As shown in Figure 1(a), OBU is used to communicate with other vehicles or RSUs, and RSUs are used to connect with application servers and trust authorities. The communication between vehicles is called vehicle-to-vehicle (V2V), and the communication between OBUs and RSUs is called vehicle-to-roadside (V2R). VANET is developed to perform the public safety applications; such applications can save lives and improve traffic flow by transmitting safety-related messages. Moreover, the VANET can also provide some commercial and entertainment service to meet the demand of the drivers for both convenience and comfort purposes. In 1999, US Federal Communication Commission (FCC) allocated a bandwidth of 75 MHz spectrum at 5.9 GHz, usually referred to as the dedicated short-range communications (DSRC). The DSRC radio technology has been standardized on the definition of the media access control (MAC) and physical layer protocols as IEEE 802.11p by the IEEE 1609 working group. Figure 1(b) shows that the DSRC spectrum has been divided into seven 10-MHz wide channels. Channel 178 is the control channel where all common safety messages are exchanged in it. It is important to point out that Channel 178 is generally restricted to safety communications only. Other non-safety usage in control channel is limited to occasional advertisements of private applications from the service channels which are insignificant to overall channel load.

(a) Architecture of VANET and (b) 5.9-GHz DSRC band plan.
Due to the openness of the wireless transmission medium, wireless communications are vulnerable to malicious injection of jamming. Certain low-cost jamming devices can be easily purchased by the adversaries, which can be used on the commonly available platforms in order to launch attacks with little efforts. Such attacks are known as the Denial-of-Service (DoS) attacks. The DoS attack can eliminate the network capacity to execute its normal function 1 by affecting its throughput, network load, end-to-end delay. 2 In VANET, the control channel is generally restricted to exchange specific messages only. The messages like traffic information messages, general safety-related messages, and liability-related messages are transmitted in the channel. Traffic information messages are used to disseminate traffic conditions in a given region, and they affect public safety by preventing potential accidents from traffic congestion; general safety-related messages are used by public safety applications such as cooperative driving and collision avoidance; liability-related messages are exchanged in liability-related situations such as accidents. The control channel is a shared wireless medium, and its communication technologies are publicly accessible. The adversaries can easily observe the V2R or V2V communications; then they launch simple DoS attacks against wireless networks by injecting false messages. Also, the adversaries are able to use the well-known communication rules as basis to launch DoS attacks in this channel. The effects of this DoS attack are twofold: on the side of the transmitters, it renders the medium busy resulting in large back-off times; while on the side of the receivers, it dramatically decreases the signal-to-noise ratio (SNR) resulting in a large number of packet collisions. Under this attack, the common safety messages are disabled because they will not be sent to the receivers in time. The consequences of such attacks will cause some city-wide chaotic traffic problems like traffic congestions, traffic disturbances, and traffic accidents. According to the study of Xu et al., 3 jammer can be categorized as follows:
The methods to detect the jamming problems have been widely researched by scholars and professions.4–10 In addition to these solutions toward the jamming problems, different strategies and techniques which counter the attacks from adversaries, including frequency-hopping spread spectrum (FHSS) and direct-sequence spread spectrum (DSSS), ultra-wide band (UWB) technology, antenna polarization, and directional transmission methods, have been developed through time. 11 But, these solutions overwhelmingly rely on cryptography, which means the mechanism of key establishment must be decided by consensus in advance. As a result, when the shared key is revealed to the adversaries, the solutions may become useless. Another weakness is that when the additional infrastructural overhead is too big, it is impossible to be used as OBU.
Recently, new approaches which utilize localizing algorithm associated with range-based properties to combat attackers in wireless networks have been proposed.12–18 But in VANET, errors can often be masked through fault tolerance, redundancy, aggregation, or by other means. In certain situation, the additional cost of hardware required by the range-based solutions may be inappropriate in relation to the required location precision. Because of the high mobility and large scale of vehicles in VANET, an alternate range-free solution toward the problem of jammer localization is needed. We focus on using the range-free algorithms to find the location of the jamming attacker in VANET. Such solutions can be effective by eliminating the attackers from the network and guiding the routing protocol to avoid the jammed region. The vehicles record their locating information and combine the information with if-jammed signal in every fixed time interval. The collected information of each vehicle is transmitted to the RSU when the vehicle moves into the communication range of this RSU. Then, RSUs forward their collected information to the application server. At last, the application sever localizes jammers using corresponding algorithms.
The main contributions of our work are as follows: we use the incorrectly classified negative area to measure the distance between samples and centroids in fuzzy c-means (FCM) algorithm, then use the weight-based FCM to classify the data set. We provide two new definitions named
In weight-based FCM, the calculation formula of the distances between points and centers was redefined with incorrectly classified negative area. At the same time, the possibility of the point being classified into incorrect cluster went down. We then applied the
Moreover, we utilized the clusters returned by weight-based FCM to further localize multiple adversaries. We also used minimum cover circle to define the evaluation function in PSO. Then, the PSO-based localization algorithms were developed to calculate more accurate coordinates of jamming attacker in each cluster. As we demonstrated through our experiments in MATLAB, our approach is highly effective in finding and localizing multiple attackers in VANET.
Furthermore, we proposed a general-purpose localization framework to perform multiple jamming source positioning. This framework could combine varieties of technologies like jamming detection, jamming source location, and jamming countermeasure. It is designed with fully distributed functionality while easy to be deployed in practical applications.
The rest of the article is organized as follows: we place our work in the context of related research in section “Related work.” Our network assumption is presented in section “Network assumptions.” We provide our theoretical analysis and describe how to determine the number of attackers in section “Determining the number of attackers and classifying the data set.” We formulate the problem of localizing the jamming attacker as an optimization problem of using PSO algorithm in section “Locating the jammer source.” In section “General-purpose localization framework of positioning multiple jammer,” we present the general-purpose localization framework to perform multiple jamming source positioning. Finally, we conclude our work in section “Conclusion.”
Related work
The jamming attacks were first studied and concluded by Xu et al.; 3 they have divided the elementary jammers into four types according to their different jamming characteristics, that is, constant jammer, deceptive jammer, random jammer, and reactive jammer. And the elementary jammers always interfere transmission signal at physical layer. Then, a lot of intelligent jammers were proposed in the following researches.19–21 Unlike the elementary jammers, the intelligent jammers focus on the MAC layer; they sense the channel at first and inject some jamming signal until the related packets have been transmitted in the channel, that is, request to send/clear to send (RTS/CTS) frame jammer, DATA frame jammer, ACK frame jammer.
The traditional approaches to prevent the DoS are to use the sophisticated physical layer technologies such as FHSS and DSSS, UWB technology, antenna polarization, and directional transmission methods. 11 A similarity is that all the traditional approaches use the cryptographic-based authentications and key management schemes as basis for further decoding.22–24 A secure and efficient key management (SEKM) framework is studied by Wu et al. 22 SEKM builds a public key infrastructure (PKI) by applying a secret sharing scheme and an underlying multicast server group. A key management mechanism with periodic key refresh and host revocation is implemented to prevent the compromise of authentication keys in the study of Wool. 23 An authentication framework for hierarchical ad hoc sensor networks is proposed in the study of Bohge and Trappe. 24 However, the cryptographic authentication may not be always applicable in VANET because of the additional infrastructural overhead and computational power. Since the communication rules in VANET are open while the key is easily exposed to attackers, it makes even harder at certain situation to apply the solutions.
The localization techniques have been researched widely by scholars and professions. The signal processing–based localization techniques have been studied in the earlier literatures. Various approaches which use the advanced signal processing techniques have been proposed in order to locate the jamming attackers. 25 These techniques are all operated at the physical layer. In addition, they require special and additional infrastructures to achieve their goals. The VANET may be used everywhere in the city, yet the jamming attack also may be launched anywhere. A large number of additional hardware is needed to widely deploy such techniques, and the high cost which brings a heavy burden to the governments is unacceptable. Dealing with the ranging methodology, range-based algorithms involve distance estimation using the measurements of various physical properties such as received signal strength (RSS),12,13 time of arrival (TOA), 14 time difference of arrival (TDOA), and direction of arrival (DOA). 15 RSS-based techniques require the measurements of RSS at various positions (landmarks) to form a signal map. Some well-known approaches belonging to this category are the (weighted) centroid 16 and trilateration 17 approaches. In the study of Bahl and Padmanabhan, 12 a radio direction and ranging (RADAR)-gridded algorithm is proposed; it uses an interpolated signal map which is built from a set of averaged RSS readings with known locations. The nearest neighbor will be returned as the estimated location when an observed RSS reading with an unknown location is given. In the study of Elnahrawy et al., 13 an area-based probability estimated method is studied. Such method utilizes an interpolated signal map while the experimental area is divided into a regular grid of equal-sized tiles. RSS readings are used to compute the probability of the existence of the attackers at each tile through Bayes’ rule. The tile which has the maximal probability will be returned as the estimated result. In the study of Madigan et al., 18 Bayesian networks localization is proposed, and it is a multilateration algorithm that encodes the signal-to-distance propagation model into the Bayesian graphical model for localization. Through Markov chain Monte Carlo (MCMC) simulation, belief network (BN) returns the sampling distribution of the possible location coordinates as the localization result. All of these RSS-based schemes require landmarks to measure the RSS values at different positions. And a set of previously collected measurements, including coordinates and the corresponding RSS values, are required in order to apply the algorithms to identify the positions of attackers. In a slightly different context, Pelechrinis et al. 26 use gradient descent minimization to get the position which has minimal packet delivery ratio (PDR), and this position is taken as the estimated result.
In the study of Bulusu et al., 27 a heterogeneous network which contains powerful nodes with established location information is considered as being useful. In this work, anchors beacon their positions to neighbors that keep an account of all received beacons. Using this proximity information, a simple centroid localization (CL) model is applied to estimate the location of the listening nodes. An enhanced version of CL is known as the weighed CL, 28 which adds weight values into the procedure of estimating the targeted node position. Liu et al. 29 proposed the virtual force iterative localization (VFIL) algorithm which performs better than CL and weighted centroid localization (WCL) in terms of the localization accuracy. VFIL first estimates the jammer’s location using traditional coarse localization scheme such as CL, and then iteratively localizes the jammer by defining a virtual force. Cheng et al. 30 further uses basic geometric concepts to improve the performance of VFIL. Also, a rudimentary system based on SNR measurements and bifurcation points is provided by the same researcher. 31 All of the methods can be used to locate the jammer. However, the localization accuracy of above range-free solutions is unsatisfactory. When the testbed is partly distributed, all the approaches will generate the wrong results.
The works in the previous studies32–34 are most closely related to ours. Yang et al.
32
propose the cluster-based mechanisms to determine the number of spoofing attackers. In addition, some range-based localization algorithms are also used for localizing the adversaries like RADAR-gridded, area-based probability, and Bayesian networks. In his work, the cluster-based mechanism uses the merge energy and partition energy
35
to determine the number of the attackers. The relationship between these two energies indicates the divisible state when the system is composed of
All techniques mentioned above focus on WSN. Compared to WSN, VANET has a larger number of nodes which are the mobile vehicles and jamming attackers which locate at anywhere on the whole urban traffic map of a city are needed to be concerned. Some effective range-based solutions of jammer localization in WSN have two requirements in common: the sensor nodes are static while the RSS values at various positions can be measured. However, the city-wide applied region of VANET is too big to deploy these techniques. In such case, it is feasible and significant for some methods to utilize their own characteristics to localize the jamming attackers. Our work differs from the previous studies in that we use the locating information and if-jammed information gathered by vehicles without any additional infrastructure. Furthermore, our work is novel because it uses big data–based range-free solutions to determine the number of jamming attackers and localize their positions. An iteration-based mechanism is invited to determine the number of attackers with higher accuracy. The PSO-based localization algorithm works well with non-uniformly distributed data set, and the weight-based PSO can make an effective estimation even when the data set is partly distributed.
Network assumptions
Network model
We consider a VANET within an open map as well as an urban traffic map. The open area means that any pairwise coordinate
Jamming model
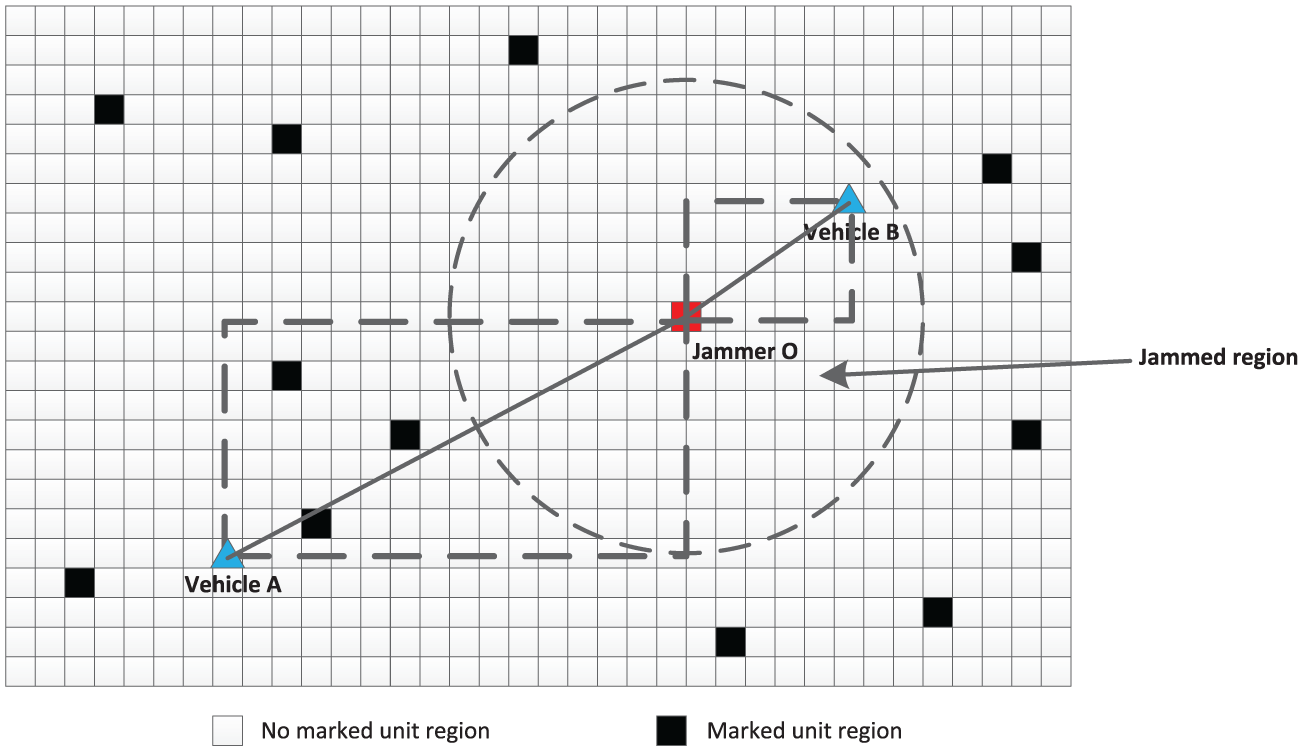
As shown in Figure 2, vehicles can perceive two different categories under jamming condition: jammed and unaffected-jammed. That is because vehicles under unaffected-jammed can use control channel to broadcast and receive messages as usual. This fact is important for our future research of anti-jamming techniques once the jamming regions and sources are confirmed. The unaffected-jammed regions are also necessary for the algorithms like WCL,
28
MCCL.
34
Both of the algorithms are used to compare with our proposed algorithm. Thus, the vehicles record a triple

Jamming model.
Determining the number of attackers and classifying the data set
The inaccurate estimation of the attacker number and unsatisfactory segmentation of data set will eventually result in failure in localizing the multiple adversaries. To address this issue, we use a weight-based FCM model. We first define the beaconing circle and the coverage rate. Then, we further use them to design a evolutional procedure to determine the attacker number and classify the data set.
The data set gathered from vehicles can be seen as

Confusion matrix and common performance metrics of clustering
Weight-based FCM
FCM clustering is a typical unsupervised pattern recognition method which has been successfully applied to feature analysis, clustering, and classifier designs in the fields such as astronomy, geology, medical imaging, target recognition, and image segmentation. This method was initially developed and improved by Dunn
36
and Bezdek,
37
respectively. As a “fuzzy” version of
FCM algorithm generates fuzzy partitions and prototypes for any set of numerical data. In our work, the jammed region consists of many jammed points, and every point has the positional characteristic that it locates closer to its own jamming source than the other sources. Hence, FCM algorithm is useful in this situation, and we use the FCM algorithm to perform a series of clustering processes to

where

Mostly, the Euclidean distance in equation (2) is used as the similarity metric of the distance between sample and centroid. However, such method is not suitable in our work, since the classification rules in our work are not only defined by spatial distance but also the spatial distribution of
We must redefine the distance using distribution of
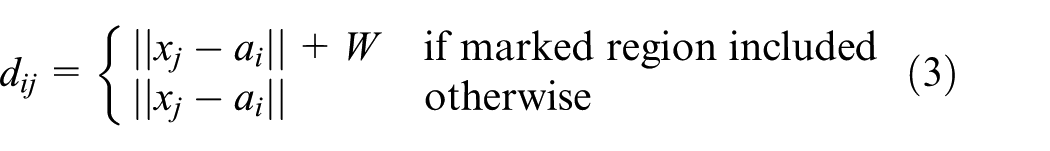
Use marked unit regions to weight the distance between sample and cluster centroid.
The membership functions and cluster centroids update as shown, respectively, in equations (4) and (5)


The general procedure of weight-based FCM algorithm is shown as following:
Determine value of
Compute every distance
Compute cluster centroids
Compute an updated membership matrix
Compare
Beaconing circle and coverage rate
The movement of vehicles can be considered as a continuous Markov process. It means when a vehicle moves from inside the circle
Definition 1 (Beaconing circle)
When a system arrives at state
Definition 2 (Coverage rate)
At state
In our work, if every point in
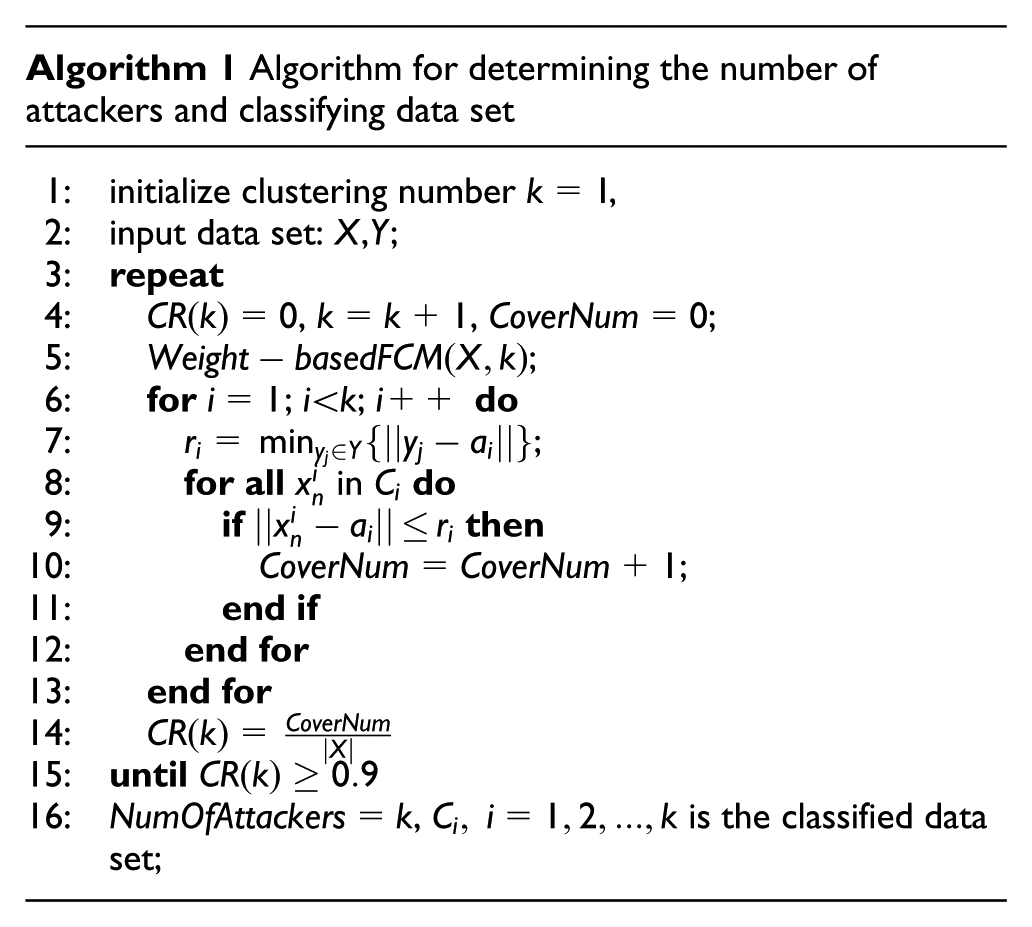
System evolution
As mentioned above, when the coverage rate reaches closer to 100% at state
Experimental evaluation
The following experiments are to evaluate whether the proposed method can find out the correct number
Experimental environment
We implemented our approach in MATLAB. Both the open map and the urban traffic map were used. As being in the

Urban traffic map used in our work.
Validity and comparative experiments of attackers estimated method
In this article, when the coverage rate is greater than 90% at state

Coverage rate at different estimated number of attackers according to the number of actual attackers: (a) two actual attackers, (b) three actual attackers, (c) four actual attackers, and (d) five actual attackers.
In order to evaluate the performance of our method, we introduce another common multiclass detection method which can be obtained by classifying a data set.
35
This method studies two closest clusters after a clustering process, and it provides a pair of evaluation criteria at different estimated number
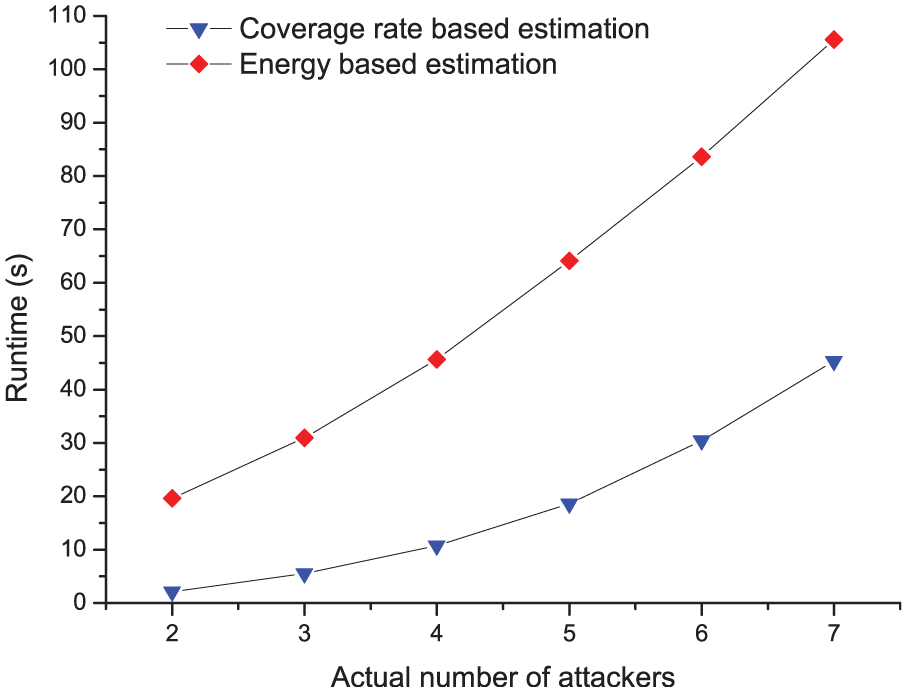
Comparison graph of runtime between energy-based estimation and coverage rate–based estimation.
Comparison of weight-based FCM and other clustering algorithms
The most important technique of determining multiple jamming attackers is how to correctly classify the data set which has been collected. Some widely used algorithms can be divided into five different types: the partition-based, the hierarchy-based, the density-based, the grid-based, and the neural network–based clustering algorithms. In our research, the data set we chose is 2D which contains a large number of positions. Our goal is to get the correct partition on the data set (jammed points which are interfered by the same jammer must be classified into one cluster) as fast as possible using these clustering algorithms. Although the hierarchy-based and density-based algorithms do not need to assign the cluster number in advance, their qualities of clustering results are always poor. Using these two types of algorithms, some critical points are always misclassified into an individual cluster, and it makes our estimation method failure. The grid-based algorithms are always used in data search because of its high efficiency. Yet, the gird structures are built with many attributes, and it is inoperative in our work. The reason is that we only consider the positional attribute in our work. Finally, the efficiency of neural network–based algorithm is too low to be accepted. Based on these facts, we choose the partition-based clustering algorithms in our work; some popular partition-based algorithms such as
Due to the city-wide applied range of VANET, the data set used in our work is very big. This feature requires the clustering algorithms must perform efficiently. Hence, our first experiment was implemented to evaluate the runtime of each clustering algorithm. We considered six cases with different number of actual jamming attackers which changes from 2 to 7. And in every case, the data set is generated by vehicles with the fixed vehicle number, simulation time, and jamming range. Then, we used

The runtime of
When two jammed regions are located very close to each other, the
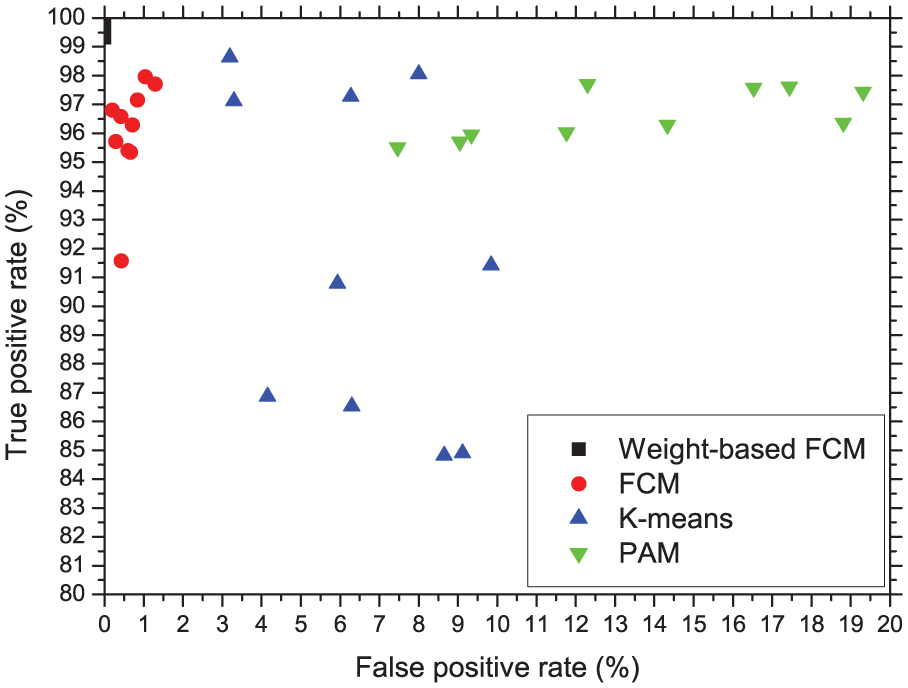
ROC graphs obtained by
It can be seen from above experiments that our proposed weight-based FCM is the best choice for dealing with the clustering problem in VANET. It can achieve the most accurate classification with an acceptable runtime.
Performance experiments of weight-based FCM
As mentioned above, if one
The multiclass ROC matrixes and the true-/false-positive rates obtained by weight-based FCM with three actual attackers.

ROC: receiver operating characteristics; FCM: fuzzy c-means.
The multiclass ROC matrixes and the true-/false-positive rates obtained by weight-based FCM with four actual attackers.

ROC: receiver operating characteristics; FCM: fuzzy c-means.
Locating the jammer source
In the last section, the point set
PSO algorithm
There are two insights of a process of optimization using swarm particles: 39 First, being assumed as particles in space, the points will tend to move toward and influence one another, with the objective of seeking agreement with their neighbors; second, the space in which the particles move is heterogeneous with respect to evaluation: some regions are better than others. Some points in the parameter space result in greater fitness than others. With this architecture, the process of finding better regions can be viewed as solving the problems of optimization. As a typical method for the implementation of swarm intelligence (SI), the PSO algorithm39,40 is inspired by social behavior of bird flocking or fish schooling. PSO is a population-based stochastic optimization technique and also a popular and robust strategy for some optimization problems. 41 PSO algorithm suggests that individuals moving through a socio-cognitive space should be influenced by their own previous behaviors and by the successes of their neighbors. As the system is dynamic, each individual is presumed to be moving at all times. The direction of movement is a function of the current position and velocity, the location of the previous best success of individual, and the best position found by any member of the neighborhoods. It has been shown in equation (6)

In equation (6),
System evolution
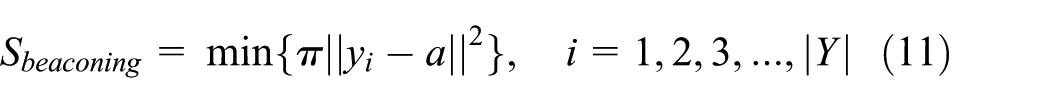
When the point set

Then, the problem of using

In order to use PSO algorithm to obtain the minimum value of
PSO algorithm can be consequently taken into consideration as a mean for looking for the most appropriate circle center by the following equation

When using PSO algorithm to find the extremum of a function, it will fall in a stable state after several iterations. Moreover, almost all particles are equal to the global optimal centroid


In addition, as shown in Figure 10, sometimes the distribution of the points in

Situation of the point set
Experimental evaluation
The following experiments are to evaluate the effectiveness of locating jammer with PSO algorithm and make comparisons with some existing range-free and range-based location algorithms.
Experimental environment
We implemented our approach in MATLAB as well. The maps, motion model of vehicles we used in this section are the identical ones that we used in the last section. The particle size
Validity experiments of PSO algorithm
When the particle size is determined, the only input data is
First, we consider the impact of jammer’s transmission range. We kept vehicle number the same (

CDF curves with different jammer’s transmission range when vehicle number is fixed on open map: (a) transmission range

CDF curves with different jammer’s transmission range when vehicle number is fixed on urban traffic map: (a) transmission range
Figure 11 shows the performances of four different localization algorithms in the scenario of an open map. Figure 12 shows the same performance in the scenario of an urban traffic map. In general, we observe that PSO algorithm always has the highest precision, while the errors generated by PSO are stable and almost less than 1 in all cases. Furthermore, as the jammer’s transmission range increases, the localization error becomes smaller. It indicates that the PSO algorithm is sensitive to the transmission range. The reason is when the jammer’s transmission range becomes larger, the jammed area grows larger as well. And more jammed points will be detected and added in
Second, we consider the impact of vehicle number. The transmission range of the jammer was fixed at 50 ft. The vehicle number was varied from 20, 30, 50 on open map and 40, 60, 100 on urban traffic map. The reason we chose these numbers is because the urban traffic map is bigger than the open map in our simulation. Each localization algorithm was run 30 times to obtain the estimated positions of different jammers. The experimental results are shown in Figures 13 and 14, where the

CDF curves with different vehicle number when the transmission range is fixed on open map: (a) vehicle number

CDF curves with different vehicle number when the transmission range is fixed on urban traffic map: (a) vehicle number
As shown in Figures 13 and 14, we observe that PSO algorithm still achieves the best localization accuracy, and it is sensitive to the number of vehicles. The larger the number is, the better the localization accuracy is. The reason is that more vehicles are used in the experiment, so more jammed points are recorded by them. As mentioned above, larger vehicle number also leads to a big chance to get more different areas in the jammed circle so that it can improve the localization accuracy.
Validity experiments of weight-based PSO algorithm
We have introduced the applied scene of weight-based PSO above. In this experiment, we created a corresponding jammed region which allows vehicles to access partial areas. We implemented our experiment only on open map. The transmission range of the jammer was fixed at 100 ft, while the vehicle number was fixed at 50. Each localization algorithm was ran 30 times to obtain the estimated positions of different jammers. Figure 15 shows the experimental results, where the

CDF curves with different localization algorithms when
Comparison and analysis
In VANET, compared to the signal processing–based localization techniques, RSS-based localization techniques and some existing range-free-based techniques, the PSO-based range-free localization algorithm we proposed has several advantages. The advantages can be described as follows:
Compared to the signal processing–based localization techniques, our method is software based which operates at application layer instead of physical layer. Our method does not rely on the additional infrastructure like ultrasound, infrared, or laser. This feature can significantly reduce the cost of jammer localization when there are many jamming attackers on the bigger concerned map.
Compared to the RSS-based techniques mentioned in section “Related work,” our method does not rely on the RSS measurements at various positions. Instead, our method is a self-diagnosed method because it uses the normal nodes in VANET to collect information, and the collected information is processed by the server. When RSS-based techniques are used to localize jamming attackers, at least three landmarks are required to monitor RSS values in jammed region. On one hand, the trilateration algorithm is the only method which can be used in the situation of three landmarks, yet the accuracy of this algorithm is lower than the other methods. On the other hand, the concerned map in VANET is always at a big scale (a city-wide traffic map), and the landmarks are required to be uniformly located with a high density on the map. The project of deploying such a large number of landmarks is unpractical, despite the fact that in some cases, certain RSUs can be reused as landmarks. Furthermore, all the existing RSS-based methods focus on the wireless networks whose nodes are static, which means the RSS readings of empty load are easy to measure through an overall management. However, in VANET, vehicles are mobile nodes, and they have complete autonomy. Also, their movement is unpredictable. Thus, the RSS measurements can be seriously interfered by vehicles. As a result, the localization accuracy is unsatisfactory.
Compared to the existing range-free techniques, our proposed method is based on geometric covering. And PSO-based solution is an evolutive model, and it indicates that if the diversity of reference positions is greater, the obtained results are more precise. Moreover, our proposed weight-based PSO algorithm also performs well in jammer localization when the data set is partly distributed. The reason is that the mobile nodes are considered in our research; due to the continuity of motion, we use the beaconing circle to lead the particles to move toward the best solution. In addition, the computational complexity of our method is
The comparative experiments between the existing range-free solutions and our proposed solution have been implemented and discussed in previous sections. To further illustrate our viewpoints, a RSS-based method which uses trilateration localization algorithm is simulated in this section. We use three landmarks to measure RSS values. The transmission range of jammer is 50 ft, and the shadowing model is used to evaluate the distance between jammer and landmarks as shown in equation (12), where


Comparison graph of RSS-based trilateration algorithm and PSO algorithm.
General-purpose localization framework of positioning multiple jammer
VANET is different from other wireless networks. It is a self-organized P2P wireless network. It has several features compared to WSN: first, the node size and applied regions of VANET are much bigger, the hardware-based methods are hard to be deployed; second, nodes in VANET are more powerful on energy and computational ability, and most of them have an on-board GPS receiver. But, nodes in WSN are always energy constrained and computational ability constrained, and the positional information only can be computed with sensor data without any calibration; Third, every node in VANET has complete autonomy, and they are uncontrolled and unpredictable. All nodes can be used as information collectors instead of processors, and the RSUs can be easily reused as repeater stations; Fourth, the control channel of VANET is completely accessible for any user; some interference avoidance algorithms are not useful. Based on these facts, we have proposed a general-purpose localization framework to perform real-time jammer positioning. This framework is designed with fully distributed functionality, and it is easy to be deployed in real world. It is built around all components in VANET: OBUs, RSUs, and server. The framework architecture is identical as it has been shown in Figure 1. During the localization process, the following steps will take place:
The vehicles record their own GPS information and combine them with the if-jammed signal in every fixed time interval.
Vehicles transmit their recorded information to the RSU when vehicles enter the coverage communication range of this RSU.
RSU forwards its collected information to the application server.
Application sever use weight-based FCM and PSO algorithms to localize multiple jamming attackers.
If there is a need to use certain anti-jamming methods, the server can transmit the jammer location and the jamming range to vehicles through RSUs. These results can help vehicles to take corresponding measures in jammed region and further reduce the energy use.
Conclusion
In this article, we proposed to use a range-free solution to localize multiple jamming attackers in VANET. Vehicles only need to record their positions and if-jammed signal in every fixed time interval. This method does not rely on cryptography and additional hardware infrastructures as the basis. We formulate the problem of localizing multiple jamming attackers as a process of determining cluster number, classifying data, and searching circle center on the data set which consists of the information collected by vehicles. First, we provide two new definitions of
To validate our approach, we conducted many simulation experiments in MATLAB associated with the data set generated by the SUMO simulator. The experimental results provide strong evidence of the effectiveness of our proposed approach. We discover that the
Footnotes
Acknowledgements
The authors would like to thank the anonymous reviewers for helpful comments. L.P. and X.C. contributed equally to this work and share first authorship.
Academic Editor: Zhipeng Cai
Declaration of cconflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the National Natural Science Foundation of China under grant nos 61171173, 60932003, 61271220, and 61864068. This work was also supported in part by “Security in Internet of things” which is a subproject of Project Xuguangqi.
