Abstract
How to use as few sensor nodes as possible to detect composite event in large area is a difficult problem because multiple heterogeneous sensor nodes are required for detecting the composite event which consists of several atomic events, and the detection accuracy would be worse if there are no enough sensor nodes. Most of the traditional methods are focusing on atomic event detection which only needs one type of homogeneous node. Considering costs, weights, and sensing capability of different types of heterogeneous sensor nodes, a deployment cost minimization problem for composite event is put forward, and its corresponding mathematical model is given in this article, with the purpose of minimizing deployment costs subject to the constraint of achieving a required coverage quality. Different from traditional methods, according to the temporal and spatial association of heterogeneous nodes, two novel models for atomic event and composite event are proposed, respectively, and the coverage quality which is very important to the detection accuracy is analyzed based on these two models. Then, based on the composite event model and the coverage quality model, an exact algorithm and a greedy strategy approximation algorithm are proposed to solve the optimization problem. Also, the time complexity and approximability of these two algorithms are analyzed. The experimental results show that the proposed approximation algorithm has low deployment cost and low time complexity under the same coverage quality.
Introduction
Public security events, natural disasters, and accidents occur frequently all over the world, which bring a great threat to people’s personal and property security. Wireless sensor networks (WSNs) have been widely used in the detection of these events.1–5 For example, there has been a forest fire as shown in Figure 1. But if sensor networks are deployed in the forest in advance as shown in Figure 2, the fire may be found in time to avoid the occurrence of forest fire.

Forest fire disaster.

Monitor forest fires using wireless sensor networks.
In most detection cases of security events or natural disasters, monitoring scopes are usually large and events are complex. Large-scale monitoring requires a large number of sensor nodes which lead to a high deployment cost. For example, suppose that the sensing radius of every node is 20 m, and nodes are uniformly distributed in deployment area. There are totally 1250 nodes required for the deployment area of 1000 m × 1000 m, which require a big budget. Furthermore, complex events usually have multiple attributes so that a variety of heterogeneous sensor nodes are required for joint detection. This would further increase the deployment cost. For example, when the fire occurs, the temperature and brightness of the surrounding environment increase and accompanied by smoke. Temperature, brightness, smoke, and other types of heterogeneous sensor nodes are usually used to jointly detect the fire to improve the detection rate. Overall, for the composite event detection in large area, how to use as few sensor nodes as possible to detect the composite event effectively is a challenge.
Most of the traditional methods are mostly concerned with atomic event, which only has a specific property that only needs one type of homogeneous sensor node for detection. And they aim to guarantee that the monitoring area is covered by at least one sensor node or

Joint detection of composite event using heterogeneous sensor nodes.
The contributions of this article are as follows:
Based on the study of the temporal and spatial association among atomic events, a novel atomic event model and composite event model are proposed in this article.
The deployment cost minimization problem (DCMP) is formulated based on the event model, and its corresponding mathematical model is given. As we know, this is the first work to study the composite event DCMP problem.
An exact algorithm and a greedy strategy approximation algorithm are proposed to solve the DCMP, and the time complexity and approximability of the algorithms are analyzed in this article.
The rest of this article is organized as follows. The related works are analyzed in section “Related works.” The event models and definitions of the coverage quality are described in section “The event model and coverage quality evaluation method.” In section “DCMP and algorithm description,” the deployment cost optimization problem and its mathematical model are presented, and an exact algorithm and an approximate algorithm are proposed. The experimental results and analysis are provided in section “Experimental results.” Finally, a conclusion is drawn in section “Conclusion.”
Related works
The detection of composite event is mainly based on the temporal and spatial association among atomic events to improve detection accuracy. At present, there are some representative works about the detection of composite event.
S Lai et al. 10 studied the energy cost of composite event detection in WSNs and proposed a distributed composite event detection algorithm TED (type-based composite event detection) to solve the minimum energy cost problem. Its essential idea is type-based event fusion, where some sensor nodes are selected as fusion points. X Liu et al. 11 took structural health monitoring as an example to illustrate how to support EECPS (Energy-Efficient Coverage-Preserving Scheduling) to extend the system lifetime in some special applications of WSNs. The authors re-defined the coverage model and proposed two methods, based on multi-dimensional knapsack problem and genetic algorithm, respectively, to partition the deployed sensor nodes into qualified cover sets so that the system lifetime could be maximized by letting these sets work by turns. In the energy-efficient k-watching composite event detection problem, M Marta et al. 12 proposed a localized connected dominating set–based approach and a sensor scheduling mechanism to increase network lifetime. The above articles mainly prolong the lifetime of the sensor network from the aspect of algorithm.
In addition, Y Li and colleagues13,14 studied the timely energy-efficient k-watching event detection problem and proposed a real-time mechanism to improve the system response performance for some urgent composite event detection, at the same time prolong the network lifetime.
In the above literatures, the life cycle and real-time performance of sensor networks are studied, but coverage problem is less concerned. Y Yang and M Cardei 15 divided the monitored area into grids, gave the initial deployment, and studied how to deploy the movement-assisted sensor nodes for minimum-breach composite event detection. But it is a deterministic deployment-based problem which is not suitable for the large area deployment. J Gao et al. 16 first put forward a coverage quality maximum problem of composite event detection and studied how to deploy sensor nodes to maximize the coverage quality in a wide range of composite event monitoring and then proposed an approximate algorithm to solve this optimization problem.
In summary, most of the above papers are able to effectively use the temporal and spatial association among atomic events to detect composite event, but they mostly focus on the lifetime and real-time performance of the networks. And the literature 16 is mainly concerned with the problem of maximizing the coverage quality. In the work by Dong, 17 a DCMP and its optimization method are presented briefly, and in this article, this method is extended as follows:
An analysis of the complexity of the DCMP problem is added to prove that the problem is a nondeterministic polynomial complete (NP-complete) problem, which is the premise of the proposed approximate optimization method.
The approximate optimization method proposed by Dong 17 is modified in this article, and the upper bound of the number of sensor nodes in the initial deployment scheme is given as equation (19).
The time complexity and approximability of the exact algorithm and approximation algorithm are analyzed in this article, and, finally, show that the theoretical analysis is consistent with the experimental results.
Conducted more experiments using different sample data, including experiments on the relationship between deployment cost and monitoring area, deployment cost and number of node types, coverage quality and running time, and coverage quality and deployment cost. And the experimental results are analyzed in detail.
To the best of our knowledge, in composite event detection, there is no relevant research result about how to minimize deployment costs, meanwhile achieving a required detection accuracy. And this is very important to large-area composite event detection and has a good research value.
The event model and coverage quality evaluation method
Event model
In WSNs, events are usually classified into atomic event and composite event and denoted as an occurrence of a phenomenon or an object. As shown in Figure 1, forest fire disaster happens occasionally in all regions in this world, and using sensor nodes to monitor forest fires is an important application of WSNs. When forest fire occurs, environmental parameters around will be changed, such as the temperature, smoke, and light. So, different types of heterogeneous nodes can be used to monitor these environmental parameters. Here, temperature, smoke, and light are properties of different aspects of fire, so they denote atomic events of the fire while fire is the composite event. When temperature, smoke, or light exceed the given thresholds, the fire will probably happen.
In this article, based on event models,16,18,19 a novel atomic event model and a composite model are proposed, which are important to the WSN deployment problem.
Atomic event
Occurrence of atomic event denotes that one aspect of the state, which can be detected by one type of sensor node, of a target or a phenomenon exceeds a given threshold. In this article, an atomic event model is proposed, which can be denoted as follows

where
For example, atomic event
Composite event
Composite event is composed of several atomic events and it needs various types of heterogeneous nodes for joint monitoring. As shown in Figure 4, three types of heterogeneous nodes such as temperature sensor node, smoke density sensor node, and light intensity sensor node are used to detect the fire.
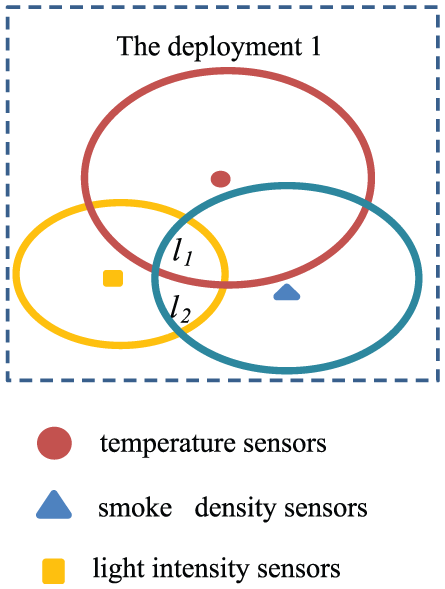
Detection of composite event.
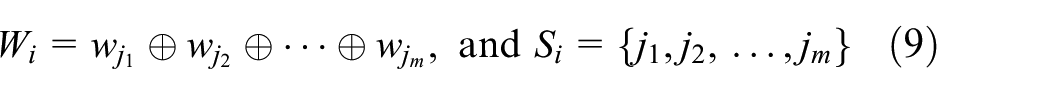
Suppose that the composite event consists of

where
Then, a composite event can be denoted as

where

For example,
Coverage quality evaluation method
Different deployment schemes have different coverage qualities. As the deployment schemes 1, 2, and 3 shown in Figure 5, locations

Covered by different deployment schemes.
In this article, the deployment of WSNs is stochastic deployment, and the coverage quality estimation model is based on Gao and Li.
18
Suppose that
Let



where
As shown in Figure 5, the coverage quality of
Thus, from the probability

where |
DCMP problem and algorithm description
Problem description
Definition 1
DCMP
Suppose that the number and cost of each type of heterogeneous nodes are

s.t.

When the arithmetic “+” is used to fuse the detection results of the related heterogeneous nodes, the DCMP optimal model has a simpler form as

s.t.

where
Complexity analysis for DCMP problem
Theorem 1
If the fusion operator
Proof
The purpose of DCMP problem is to find a best solution to decrease the deployment cost rapidly under the constraint of achieving a certain coverage quality. The following equation can be used to find the destination node which should be subtracted
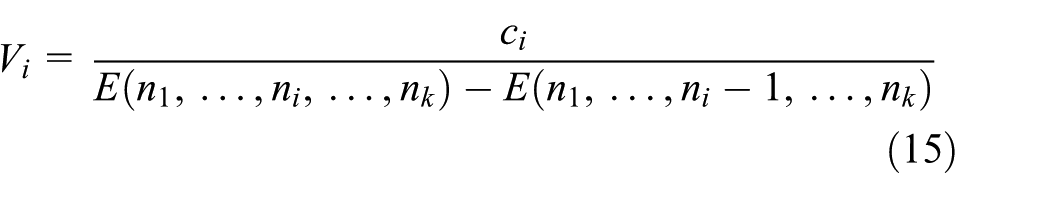
where

So, DCMP problem can be transformed to coverage quality maximization problem (CQMP) under the cost constraint which can be denoted as follows

s.t.

where
Algorithm implementation
Approximate algorithm
Based on the same composite event model of equation (3) and coverage quality evaluation model of equation (10), deployment cost minimization subject to coverage quality constraint can be transformed into coverage quality maximization subject to deployment cost constraint. Just as described in section “Complexity analysis for DCMP problem,” the DCMP problem, shown as equations (13) and (14), can be transformed to the CQMP problem, shown as equations (17) and (18), and the objective function of equation (17) is proved to be nondecreasing and submodular. 16 For the submodular function, greedy algorithm is considered as the best method.20,21 Thus, greedy strategy is used to solve the DCMP problem in this article.
Table 1 shows the approximate algorithm with greedy strategy for solving the DCMP problem, including the inputs, outputs, and the key steps of the algorithm. As shown in Table 1, the main steps of the algorithm are as follows:
Details of the approximate algorithm for DCMP problem.

DCMP: deployment cost minimization problem.
It is known that if the weight value of the node is small, more nodes are needed to keep the coverage quality. Therefore, let the weight value of all types of sensor nodes be equal to the minimum weight value, that is,

Let

From the above, it can be seen that the upper bound of the number of any type of nodes is

Exact algorithm
From section “Problem description,” it is known that the DCMP problem is at least NP-complete, and it is difficult to use an exact algorithm to solve the problem. However, in some applications, sensor nodes could be very expensive. So, it is preferable to obtain the best deployment scheme with minimum cost using the exact algorithm.
In this article, as shown in Table 2, the enumerate method is used to list all the possible deployment schemes which satisfy the required coverage quality (line 1). Then, calculate all the costs of the enumerated deployment schemes (line 2) and find the optimal deployment scheme which has minimum cost (lines 3 and 4). Finally, return the minimum cost
Key steps of the exact algorithm.

Performance analysis
1. The time complexity of the DCMP-greedy strategy
Conclusion 1
The time complexity of the DCMP-greedy algorithm is
Proof
In the DCMP-greedy algorithm, as shown in Table 1, the computational complexity of inner iterations, that is, lines 3–4, is
2. The approximability of the DCMP-greedy strategy
Conclusion 2
The approximate result of DCMP-greedy algorithm is (1
Proof
From last section, it is known that the DCMP problem can be transformed to the optimal problem which is described as equations (17) and (18). In the work by Lai et al.,
10
it has been proved that the objective function of equation (17) is nondecreasing and submodular, and Gao et al.
16
and Sviridenko
21
proved that the greedy strategy which is used for maximization of submodularity objective function subject to knapsack constraint has (1
3. The time complexity of the DCMP-enumerate strategy
Conclusion 3
The time complexity of the DCMP-enumerate algorithm is
Proof
Suppose that
Experimental results
In the experiments, the related performance of the two proposed methods is compared.
Stochastic deployment scheme is used for all types of sensor nodes, and the coverage quality estimation model is based on equation (10). Suppose that four types of heterogeneous sensor nodes are deployed in monitoring area
In the first experiment, the relationship between the deployment cost and the coverage quality is evaluated for the two proposed algorithms under the condition that the monitoring area is fixed. The related parameters are as follows: costs and weights of each type are {0.15, 0.25, 0.28, 0.32} and {0.2, 0.26, 0.24, 0.3}, respectively. Sensing radius of each node and deployment area are 20 m and 200 × 200 m2, respectively. Table 3 shows the corresponding deployment costs, deployment schemes, and node numbers of each requirement coverage quality. It can be observed from Table 3 that deployment costs of the two algorithms increase with the increase in requirement of coverage quality since the increasing coverage quality means that more sensor nodes should be deployed or replace the sensor nodes with the other with more weight which may have more costs in most cases. And the costs of the greedy strategy algorithm are just slightly more than costs of the enumerate strategy algorithm. This could also be seen from the number of sensor nodes. It can also be observed from the listed deployment schemes that the two algorithms tend to select the first type of sensor node since the first type of node has the largest greedy value which could be simply denoted as
Deployment schemes of different coverage quality.

In order to be more intuitive to see the growth trend of the deployment costs as the coverage quality increases, Figure 6 shows the coverage quality changing from 30% to 80%. It can be observed from the figure that the two trend lines almost overlap together, and the deployment costs increase faster and faster with an increase in the coverage quality, since the approximate result of greedy algorithm is (1
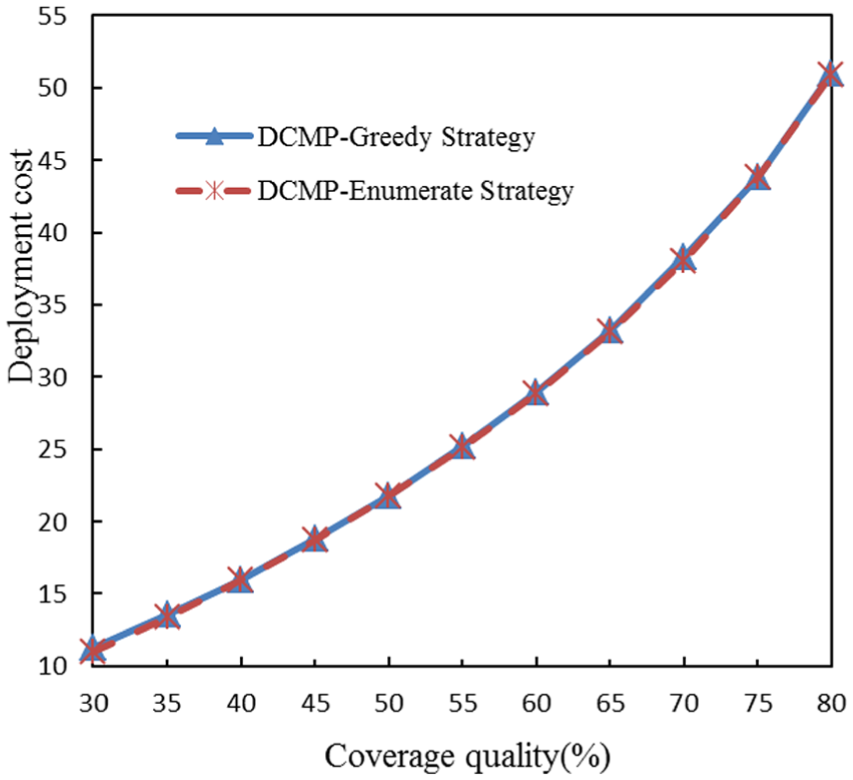
Deployment costs with varying coverage quality.
In the second experiment, the running time for the two proposed methods is evaluated while the coverage quality changes from 20% to 90%. The related parameters are the same as experiment 1. It can be observed from Figure 7 that the running time of the enumerate strategy algorithm increases rapidly as the coverage quality increases, and the running time of the greedy strategy algorithm grows very slowly, so that it is barely visible. From last section, it is known that the time complexity of enumerate strategy algorithm is

Running time with varying coverage quality.
Table 4 shows the results of the third experiment, in which the relationship between deployment cost and deployment area is evaluated, while the coverage quality remains unchanged. The related parameters are as follows: costs and weights of each type are {0.15, 0.25, 0.28, 0.32} and {0.2, 0.26, 0.24, 0.3}, respectively. Sensing radius of each node and coverage quality are 20 m and 60%, respectively. The deployment areas change from 50 × 50 to 400 × 400 m2. It can be observed from Table 4 that with an increase in the area, the deployment costs also increase since more sensor nodes are needed to be deployed in the monitoring region in order to maintain sufficient coverage quality. On the whole, the deployment costs of the enumerate strategy algorithm are slightly less than that of the greedy strategy.
Deployment costs of different deployment areas.

Furthermore, in order to be more intuitive to see the growth trend of the deployment costs as the coverage area increases, Figure 8 is given. It can be observed from the figure that the two trend lines almost overlap together because the deployment costs of the two algorithms are almost the same.

Deployment cost with different deployment areas.
In experiment 4, the relationship between the number of types of heterogeneous nodes and the deployment costs is evaluated. Suppose that the coverage quality and the deployment area remain unchanged. The number of types of heterogeneous node
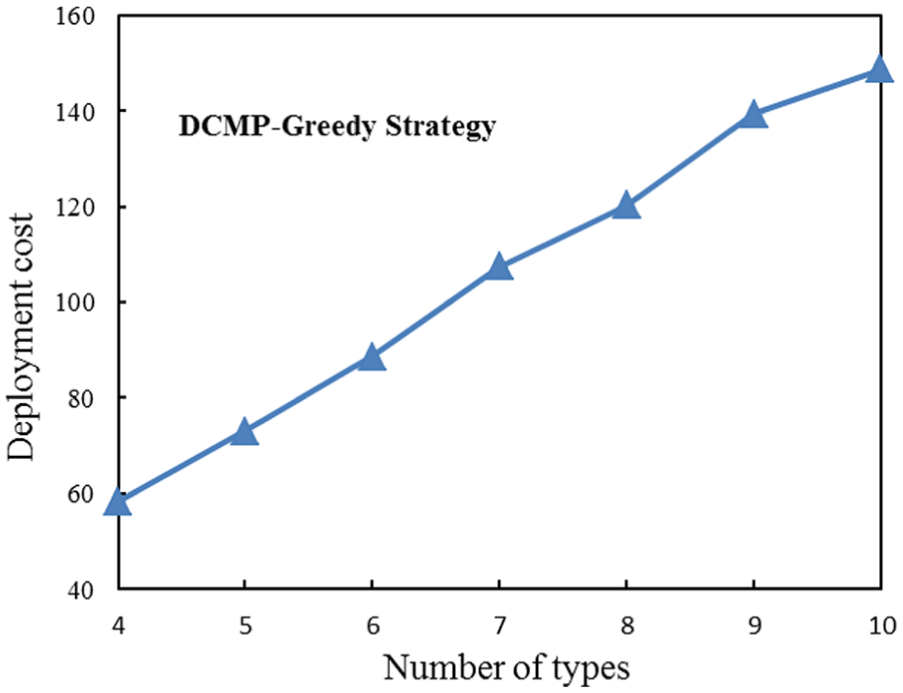
Deployment cost with varying
From the above four experiments, it can be seen that the performance of the exact algorithm in experiments 1 and 3 is slightly better than that of the approximate algorithm because it can find the optimal solution using the enumeration strategy. From experiment 2, it is known that the efficiency of enumeration strategy is poor because it needs to list all the possible deployment schemes, while the greedy strategy has a very high efficiency that its running time grows very slowly as the coverage quality increases. Generally speaking, the approximate algorithm with greedy strategy has better comprehensive performance and better adaptability. The exact algorithm of enumeration strategy is suitable for the applications in which the monitoring areas are relatively small or nodes are very expensive, and there is no need to consider the limitation of running time.
Conclusion
In this article, a novel composite event deployment problem was studied with the purpose of minimizing deployment costs subject to the constraint of achieving a required coverage quality, and the mathematical model for this optimal problem is given. Considering the temporal and spatial association of the heterogeneous nodes, a novel atomic event model and composite event model are proposed, and the coverage quality of the monitoring region based on these two event models is analyzed. Then, an exact algorithm using enumeration strategy and a greedy strategy approximation algorithm for finding the optimal solution are proposed. Furthermore, the time complexity and approximability of these two algorithms are analyzed.
Experimental results show that in the wide range of composite events monitoring, a feasible deployment scheme which has relatively less deployment cost and good coverage quality could be obtained rapidly using the greedy strategy approximation algorithm.
Footnotes
Acknowledgements
The authors thank the ICISCE conference for providing an opportunity to preliminarily present the DCMP problem and its preliminary solution. The authors also thank the anonymous reviewers for their constructive advice.
Academic Editor: Daniel Gutierrez-Reina
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is supported by the Science and technology project of Guangdong Province (2016A020209012 and 2015A010103015), the major projects in Guangdong Province (2015B010104005), Chinese National Natural Science Foundation (61502110), and the natural science foundation of Guangdong Province (2014A030307014).
