Abstract
In the
Keywords
Introduction
A wireless sensor network is a new type of network architecture that is connected by a self-organizing multi-hop, which is formed by thousands of sensor nodes. The physical world and information world are organically integrated and involve data acquisition, data calculation, data communication, and data storage.1,2 As a result of the rapid development of information technology, a wireless sensor network can be applied in all types of engineering fields, such as military affairs, environmental monitoring, disaster relief, smart homes, health care, agricultural production, and transportation.3,4
Energy consumption and coverage quality are the two key issues in wireless sensor network research,5,6 the behavioral characteristic of which is the deployment of sensor nodes. The problem of energy consumption includes how to effectively suppress rapid energy consumption of sensor nodes to extend the network lifetime and improve Internet service. The coverage quality and network energy consumption are dependent on the deployment probability of sensor nodes.4,7 In general, as a result of the limitations of the topographic and geomorphic conditions and environmental factors, we typically use the methods of stochastic deployment to handle the deployment of sensor nodes. Moreover, because of randomness, it is not possible to predict the specific location of sensor nodes during deployment, which indicates that there are several or enough sensor nodes in a specific monitoring area or at a monitoring point. It may ultimately form
Regarding the deficiencies and shortcomings of the previously described research, the main contributions of this article will be presented as follows:
Following an assessment and analysis of the relevant domestic and international literature, we propose the Optimization Coverage Conserving Protocol with Authenticated (OCPA) algorithm in this article, which was facilitated by theoretical ideas from the literature.
In the monitoring area, this article selects
When the target nodes are covered by joint nodes or single nodes, this article provides comparative methods of the awareness intensity. Moreover, by limiting the value range of the adjustable parameter
Through a simulation experiment and by comparison to other algorithms, we verify the effectiveness and feasibility of the OCPA algorithm.
Relative literature
The technique of coverage control represents essential research regarding the wireless sensor network and is also currently one of the hotspot problems in the wireless sensor network. The coverage quality will affect the lifetime of the network. In recent years, many experts and scholars at home and abroad have thoroughly and carefully conducted many studies. Zhao et al.
11
propose an optimization strategy for the coverage algorithm based on Voronoi. Satisfying the condition of a specific coverage quality, the algorithm may add work nodes to the coverage hole to improve the current coverage probability; furthermore, it will search for reasonable information regarding the repairing site to guarantee the connection of the whole network. Meng et al.
12
provide a constructive method of the connected coverage protocol. The protocol provides the proportional relation between the network coverage quality as well as the network and performance indexes of all of the parameters of the network system; moreover, it creates the scheduling control algorithm (SCA), which uses the fewest nodes needed to guarantee the connection of the whole network system. Mini et al.
13
introduces artificial intelligence algorithms, that is, the swarm intelligence algorithm and granule algorithm, to complete node deployment of the whole network monitoring area; in the stage of coverage optimization, the whole coverage is optimized by the two artificial intelligence algorithms and ultimately attains complete coverage of the monitoring area; with respect to energy consumption, it completes scheduling conversion of the node energy via heuristic node scheduling, which extends the lifetime of the network. Hanid et al.
14
also include the Voronoi as the research objective; it solves the information of the wire rod site formed by the geometric variation in the Voronoi and sensor nodes and ultimately completes coverage of the monitoring area. Tseng et al.
2
include a partial coverage optimization and constitute the partial
To improve the effective coverage of the monitoring area, and on the basis of Li et al. 15 and Zhibo et al., 16 this article proposes an OCPA. The protocol described in this article calculates the coverage expected value of the moving target nodes to the sensor nodes with the relative knowledge of the probability. Moreover, it provides a solving process of the coverage expected value of the target nodes to the sensor nodes for the first time. In terms of energy, on the basis of the analysis of all sensor node energies in the whole network, the algorithm performs an energy comparison under the multilateral and unilateral connections, that is, the energy consumption of the data in the multicast nodes is less than that in the unilateral nodes. In terms of energy conversion, the algorithm completes energy conversion among nodes using the self-scheduling mechanism, which extends the lifetime of the network. Finally, through simulation experiments and comparison with other algorithms, the effectiveness and stability of the OCPA algorithm are verified.
Prerequisite knowledge
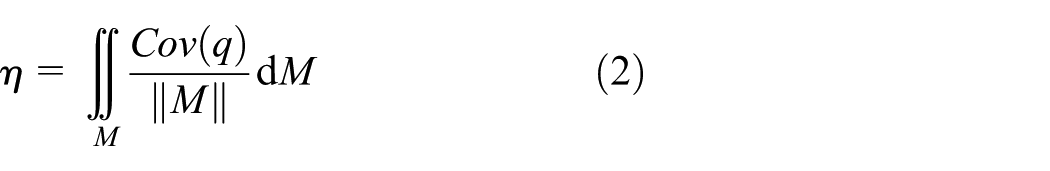
To simplify the description, the following symbol will be used ||
Definition 1
As for any one point

In the binary sensing model, the sensing area of node
Definition 2
The proportion of the monitoring area
A sensor network may be abstracted as an undirected graph
Definition 3
The specific value of the effective coverage of the sensor nodes with the coverage area of the sensor nodes

Definition 4
In the target set, any one of the target nodes is covered by at least one sensor node

Theorem 1
The sensor nodes randomly deployed in the monitoring area comply with the probability density,
Proof
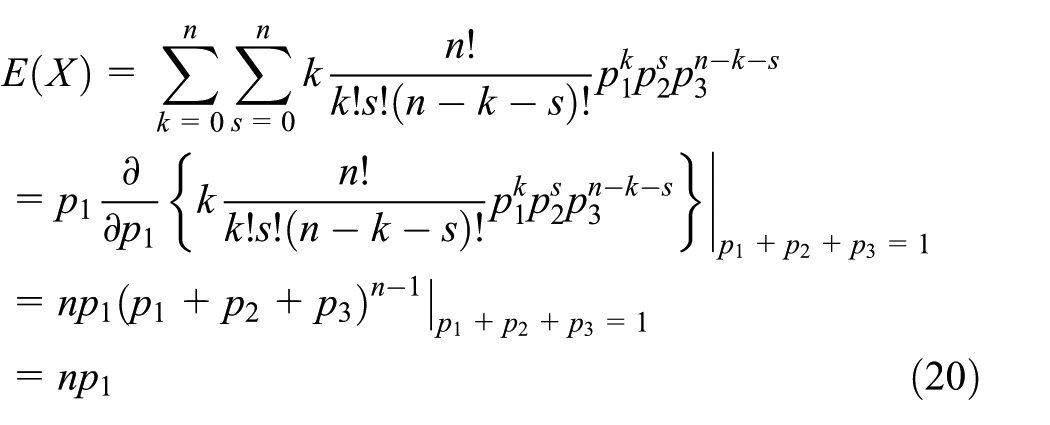
Suppose that
Regarding the whole monitoring area, the density of the sensor nodes is

Solve it, thus
When the number of sensor nodes in the monitoring area approaches infinity, that is, when

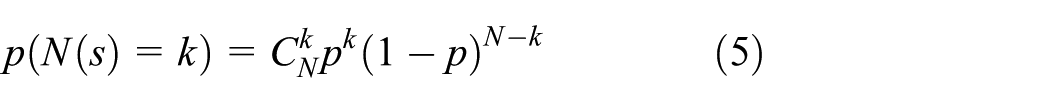
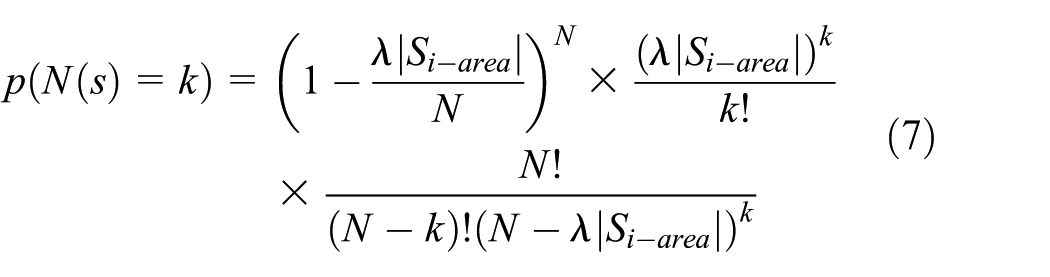
According to theorem 1, the sensor nodes randomly deployed in the monitoring area exhibit mutual independence and a uniform distribution relationship. The deployment of the number of sensor nodes obeys the probability density
The random deployment model of the sensor nodes mainly addresses the problem of the distribution density of the sensor nodes.19–21 How to use the fewest sensor nodes to complete effective coverage of the monitoring area depends on the number of sensor nodes deployed in the monitoring area at random. When there are sufficient sensor nodes deployed in a specific monitoring area, complete coverage cannot be reached; however, it is impractical from the point of node energy consumption and node redundancy. When there are many sensor nodes in the monitoring area, one node will consume substantial sensor node energy, which has no benefit for extending network life; even when the energy of a specific sink node is consumed, the whole network system will rapidly collapse. Moreover, because of the existence of many sensor nodes, a substantial number of redundant nodes will be produced during connection of the sensor nodes, and the existence of these redundant nodes will cause interference to the wireless channel, as well as consume the energy of the redundant nodes and reduce the lifetime of the network.
To overcome these two shortages, network service should be improved to a better level, and the lifetime of the network should be extended as long as possible to complete effective coverage of the monitoring area, which will improve the coverage rate of the whole monitoring area. Thus, this article introduces corollary 1.
Corollary 1
In the monitoring area, the coverage rate of the joint coverage of the sensor nodes is
Proof
The coverage rate of any target node that is not covered by the sensor nodes is

After the calculation
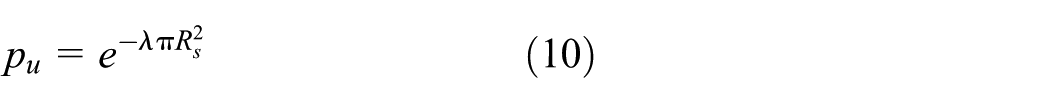
Thus, in the monitoring area, the coverage rate of joint coverage is
The coverage quality and protocol
Redundancy coverage
In the process of covering the monitoring area and meeting a specific coverage rate, to improve the coverage quality to a better level, reduce network energy consumption, and extend the life of the network to the maximum limit, as well as to effectively schedule the work of the sensor nodes in the monitoring area, as long as the focused nodes enter the coverage hole, coverage will be degraded. To avoid hole production and complete the maximum coverage area with the fewest sensor nodes, that is, in the monitoring area, real-time monitoring of the whole monitoring area is not required; rather, coverage of the focused target nodes is required. When there are several nodes that work together and all of the Euler distances between any two nodes are smaller than or equal to the perceived radius, there will be many redundant nodes; thus, only through the dispatching schema of a node are some redundant nodes closed; when they are awoken again, the coverage rate of the redundant nodes complete coverage of the target nodes only after specific conditions are met.6,22,23 Thus, when redundant nodes are transformed to working nodes, if the coverage rate of the redundant node did not reach the minimal value, the redundant node will go to sleep. As for the target nodes in the monitoring area, the random movements of the target nodes will make a specific sensor node cover a specific target node several times, and the value of the expected coverage value of the target node depends on the proportional relationship of the coverage rate with the movement of the target.
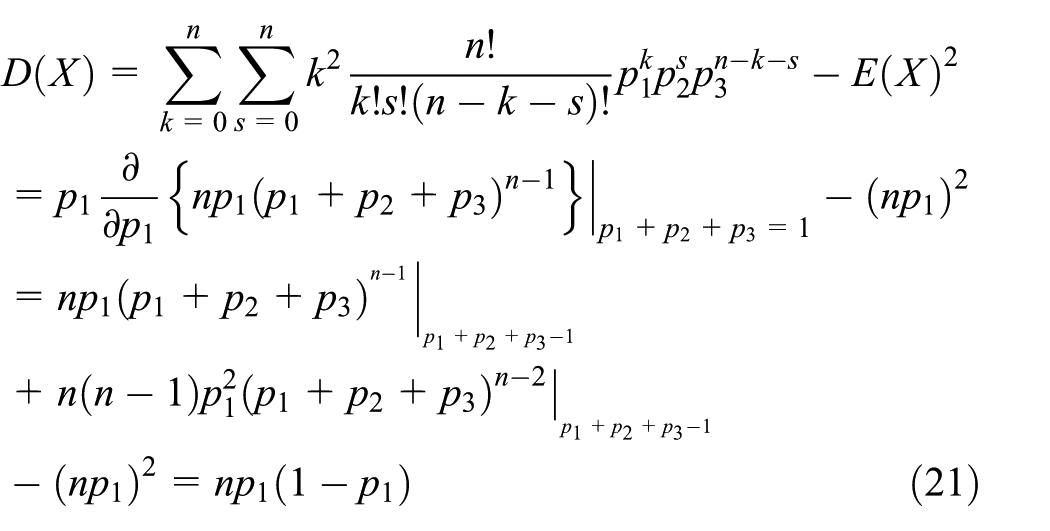
According to definition 1, the proportion that point

To make the coverage qualities of the monitoring area

If ln(1 −
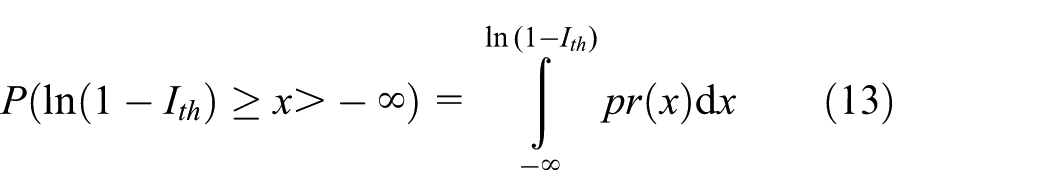
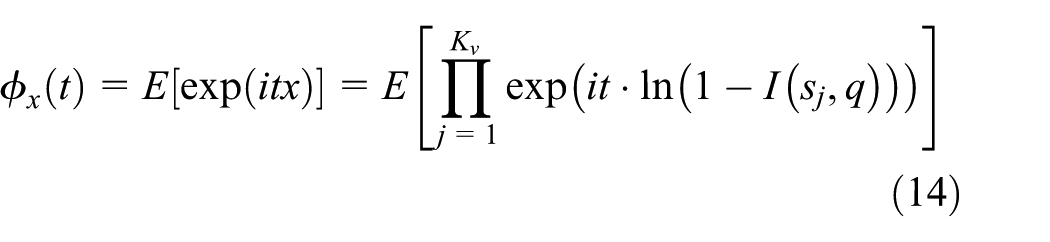

When ln(1 − exp(−
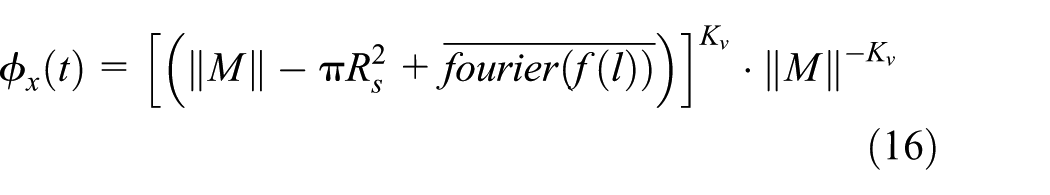
and
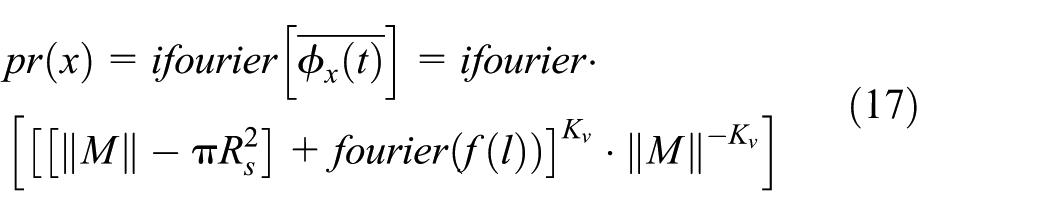
According to formulas (13), (14), and (17)

To ensure the establishment of formula (18),
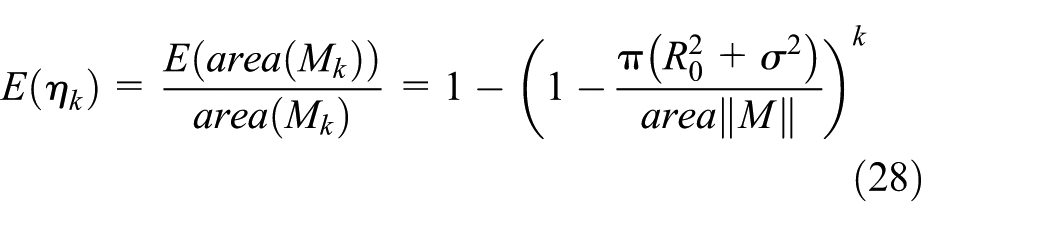
Parameters of the simulation table.

Definition 5
For a specified sensor node
Theorem 2
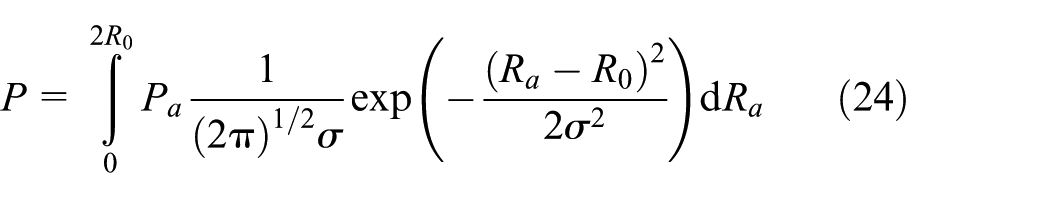
Considering the triple square monitoring area as the research object, the mathematical expectation of the area that must be focused on is
Proof
As indicated in Figure 1, for the whole target coverage area, suppose that there are


Multiple coverage.
For
Moreover, the tolerance of
In the same way, formula
Theorem 3

Proof
The nodes in area

Because the perceived radius of point
and

Because the positions of all of the nodes in area

Suppose that the area covered by one of the

Thus
According to theorem 1, the expected minimal number of sensor nodes that meet the coverage quality,

Theorem 4
After closing the redundant nodes, if the remaining working nodes accurately meet the coverage quality, then the expected number of redundant nodes,

Proof
Supposing that the left number of working nodes is


Because the perceived radius of all of the nodes comply with the normal distribution,

According to the calculation of formula (33)

and because

Thus

Hence


Thus, the number of working neighboring coverages of redundant nodes meets

Definition 6
The sending intensity of any sensor node

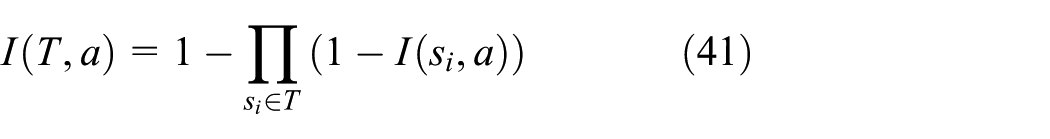
The expression of formula (41) is similar to that of any target node covered by at least one of
Theorem 5
In the sensing range, the sensing intensity of the federated nodes is higher than that of the neighboring nodes.
Proof
Suppose that when the federated nodes cover moving target nodes, the sensing intensity is

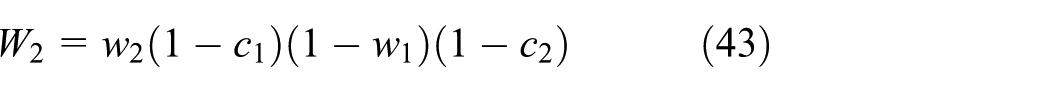
When

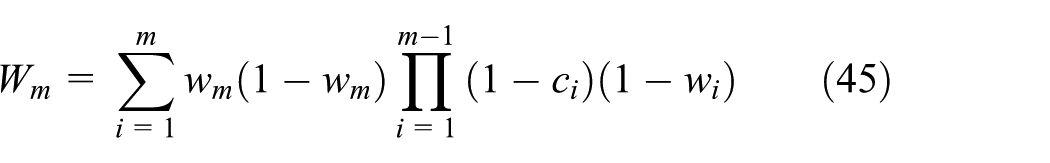
Because the positions of any sensor nodes are the same and their probabilities are events of equal probability, the sensing intensities are the same, that is,

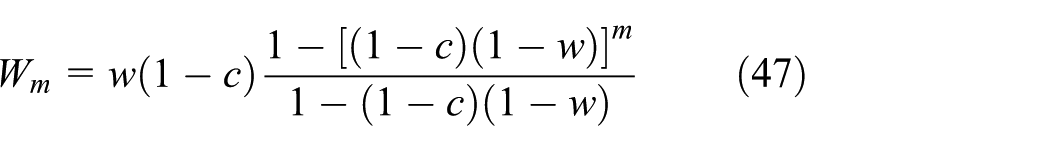
When


Because the coverage area of the federated nodes is larger than that of the single nodes,

According to the probability theory,
The OCPA protocol and description
In terms of the redundancy of the sensor nodes, the redundant connected graph of the sensor nodes is established, that is, all of the nodes in the set are used to calculate the redundant information of the nodes themselves as well as their neighboring nodes according to localization, such as the received signal strength indicator (RSSI), and subsequently fuse them; the information is then sent to the sink nodes through the communication link. When the sink nodes receive redundant information, and after calculation and analysis, the redundant connected graph,

Energy conversion
The OCPA algorithm uses one round of the runtime of the network as the fundamental unit, and each round includes information regarding the coverage control and information of the steady state. During the working stage, the working nodes constantly work, and all of the redundant nodes are closed to save network energy. At the steady-state stage, every node has five running states, which include the judgment, competition, standby, start-up, and sleeping states. The judgment state: at the beginning of each round, the nodes are in the judgment state.25,26 When the nodes meet the redundant judgment requirement, they enter the sleeping state, and when the requirement is not met, the nodes will enter the competition state. The competition state: when the nodes are in the competition state, they can enter the state of the working state; otherwise, they will enter the standby state. The standby state: the nodes that fail the competition will enter the standby state; when they receive the information “

Complexity analysis of the algorithm
When the protocol in this article sends or receives information, it utilizes single-looping measurements to complete receipt and delivery. Thus, the complexity of the algorithm in this article is O(
System evaluation
To verify the effectiveness and stability of the algorithm in this article, the MATLAB7.0 platform is selected as the simulation platform to analyze and perform experiments on the algorithm. The computer configuration adopted in this article includes the operating system WINXP and a dual-core 1.7-GHz CPU, and the memory is 2 GB. The simulation experiment deploys all of the sensor nodes at random in the monitoring area, which has radius

The model of the energy consumption of the receiver is

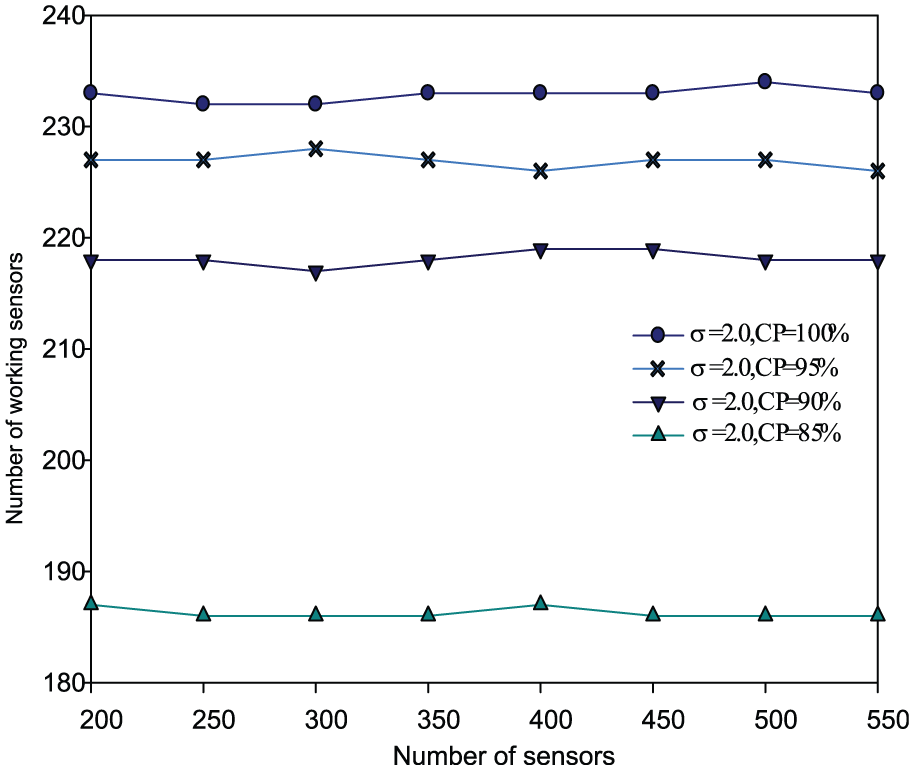
Figures 2–7 indicate the changing curves of four working nodes that occupy the total number of sensor nodes under different coverage probabilities when the values of




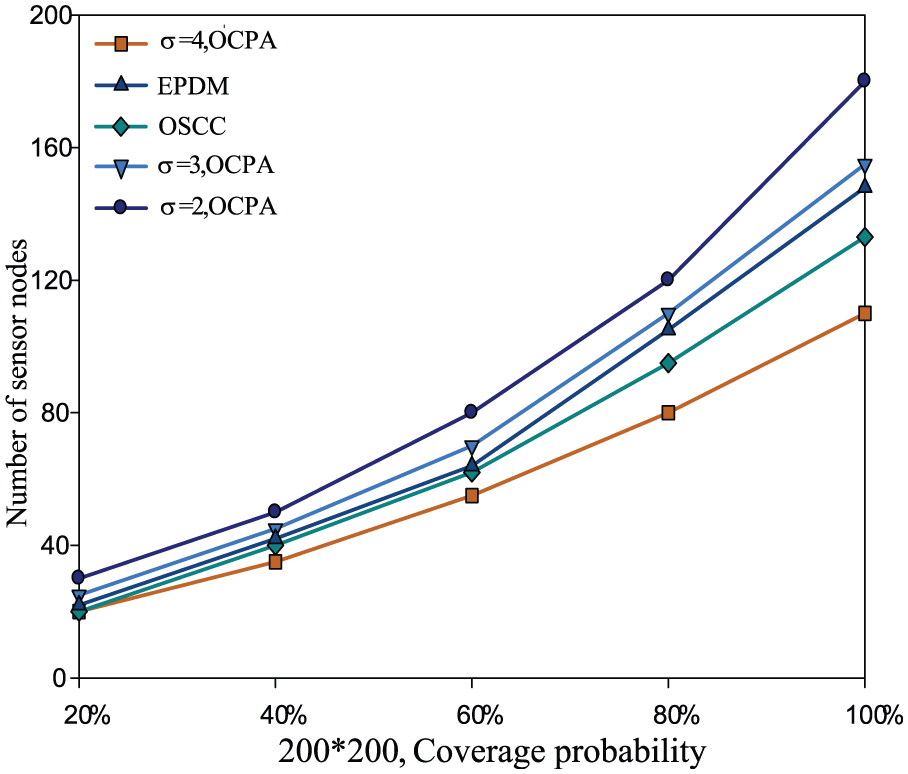
200 × 200 m2, comparison of the coverage probabilities of different algorithms.

300 × 300 m2, comparison of the coverage probabilities of different algorithms.
Figures 8–11 show the contract experiments of the OCPA protocol with the energy-efficient target coverage algorithm (ETCA)
29
and LP_MLCEH protocol
30
in terms of the network lifetime in different monitoring areas. In the experiments, the values of

100 × 100 m2, curves of network life.

200 × 200 m2, curves of network life.

300 × 300, curves of network life.
200 × 200, curves of network coverage.
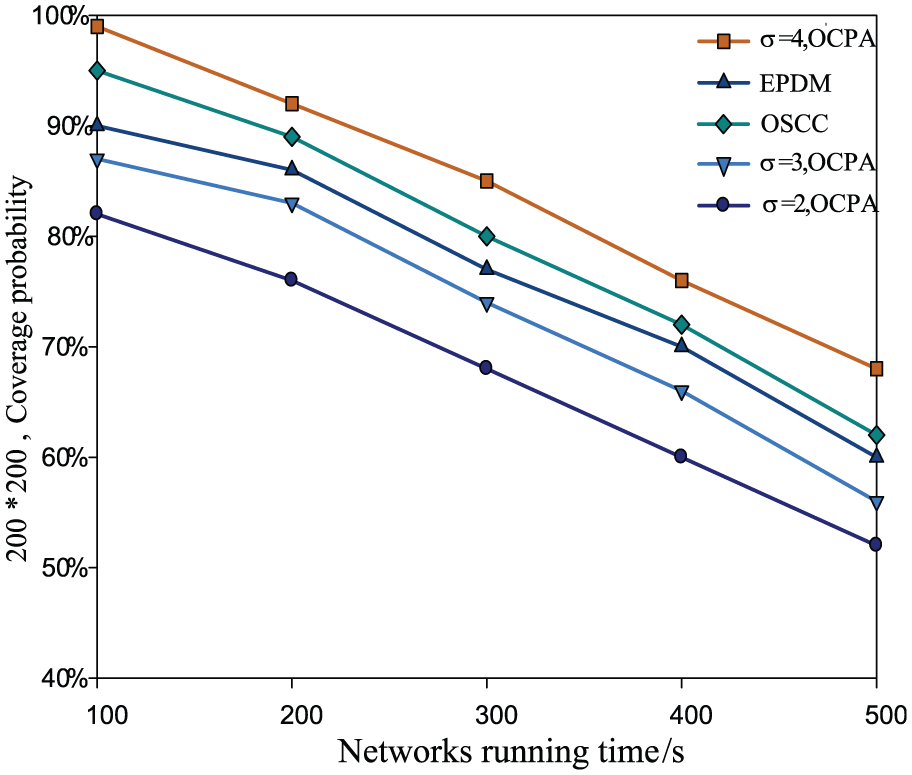
200 × 200, curves of network runtime.

Curves of the sensor working nodes and sensor nodes.
Conclusion
To determine the coverage of a wireless sensor network, this article proposes an OCPA. The protocol in this article seamlessly provides a method to solve the largest coverage area of the three-circle first; moreover, taking advantage of the probability theory, this article provides the expected value of the coverage quality of the monitoring area. On this basis, this article also provides a solving method for the smallest number of sensor nodes. On the basis of analyzing the coverage probability of the nodes, this article provides the contract relationship of the sensing intensity of federated nodes and single nodes. In terms of the coverage of redundant nodes, this article proves the conditions of the redundant coverage of sensor nodes. Finally, the protocol in this article simulates the optimized deployment, coverage probability, redundancy, network lifetime, and running time, as well as analyzes the simulation results, which verified the effectiveness and feasibility of the OCPA protocol.
Footnotes
Academic Editor: Fei Yu
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This study was supported by projects 61628210 and 61503174 supported by the National Natural Science Foundation of China; projects (no. 2016GGJS-158) supported by Cultivation Young Key Teachers in Colleges and Universities of Henan; projects 17A520044 and 15A413016 supported by the Henan Province Education Department Natural Science Foundation; projects 162102210113 and 162102410051 supported by the Henan Province Department Science Natural Science and Technology Research; projects 1201430560 supported by the Guangzhou Education Bureau Science Foundation; projects 2016A030313540 supported by the Guangdong Natural Science Foundation of China; and projects 2016SF-428 supported by the Shanxi Education Bureau Science Foundation.
