Abstract
Femtocell is a promising technology for wireless communication in the near future, due to its benefits in improving indoor coverage and enhancing system throughput. Access control is a critical issue for both operator and mobile users, and there lie three choices including open, closed and hybrid access. Hybrid access seems to be a promising choice since the femtocell opens part of the resources for macrocell users while reserving the residual part for its own femtocell users. In this way, the femtocell helps improve the network performance without much sacrifice of its own utility. Meanwhile, the macrocell should offer adequate incentive to motivate the femtocells, otherwise the femtocells are unwilling to open their resources. As another challenging obstacle, the macrocell could hardly ask femtocells to truthfully reveal their private information which is important for hybrid access, thus the situation with asymmetric information happens. Contract theory is hereby introduced to deal with such a problem. In this article, we propose a mechanism for hybrid access control, wherein the macrocell remunerates certain amount of spectrum to femtocells according to their contribution of data rate to macrocell users. This design ultimately improves the service quality for macrocell users. After figuring out the sufficient and necessary conditions for feasible contract using contract theory, we further derive the optimal contract. We also discuss several issues due to the distinctive characteristics of our problem.
Introduction
Motivation
In the area of wireless communication, demand for data transmission is soaring at an incredible speed. It is estimated that by 2017 there would be over 10 billion mobile-connected devices requesting data traffic at the level of 11.2 exabytes per month. 1 As a significant technology to cope with this increasing demand, femtocell has revealed powerful potential. 2
As a practical application of short-range transmission, the femtocell could provide wireless terminals with better service quality due to the proximity between transmitters and receivers. However, the deployment of femtocells reduces operating expenditure for macrocell provider, such as construction of new macrocell base stations (MBSs) and electricity expenses of transmission power. In addition, femtocells enhance spectrum efficiency by great spectrum reuse.
Femtocell access schemes can be classified into three categories: 3 open access that all resource is open to public use, closed access that only authorized femtocell users (FUs) could get access, and hybrid access that some of the resource remains reserved while the residual part is open.
All three configurations have their own pros and cons. Open access could improve the overall capacity of network because considerable macrocell users (MUs) locating at poor-coverage area could get access to femtocells. 4 However, open access substantially increases the handovers between cells and thus the call drop probability rises. On the contrary, closed access guarantees service quality and confidentiality of FUs, whereas it causes strong cross-tier interference between macrocells and femtocells. Hybrid access reaches a compromise between open access and closed access.
From this perspective, it is a reasonable option that macrocell providers turn to femtocell owners and ask for some of femtocells’ resources to be assigned to MUs. Nevertheless, since femtocell owners are obviously uninterested in sharing their own resources without any reward, macrocell providers have to offer adequate incentive to ensure femtocell owners’ contribution is not fruitless.
In order to set up the hybrid access, lots of private information of each femtocell should be shared with the macrocell provider. The private information may include channel conditions, resource constraints, and transmission costs. Although such information could be obtained,5,6 those femtocell owners might be reluctant to share, or even intentionally conceal such information for the sake of their privacy. Thereby, as a common scene, dealing with problems under asymmetric information is of great significance.
Contract theory 7 is a useful tool in dealing with circumstances under asymmetric information. Usually a principal–agent model8,9 is set up, in which the principal gives various contracts, and every agent picks out a suitable contract truthfully according to its private information. A vivid analogy is a labor market where an employer provides the contract and employees work for the reward.
In this article, we concentrate on a problem about interactions between a macrocell provider and several femtocell owners. As mentioned before, the macrocell provider looks forward to some help from femtocell owners such that MUs could enjoy better service quality, while the macrocell provider also offers some refund to make up the performance loss of femtocell owners. Specifically, the amount of such help represents the extent of openness of femtocells. Femtocell owners could choose hybrid access, or even open access, if the reward is inviting. We assume the macrocell provider would pay some spectrum as the refund for femtocell owners. Each femtocell owner would use self-paid spectrum and the refunded spectrum to serve its own users and relevant MUs. The macrocell provider would design different contracts. Then each femtocell owner would pick one out according to its own type that represents its private status and information. Our major goal is to design an optimal contract that makes the macrocell provider maximize its utility.
Related works
Femtocell has attracted growing research interests recently. In Claussen et al. 10 and Knisely et al., 11 the concept of femtocell is introduced. Extended problems consisting of spectrum sharing, 12 interference management, 13 as well as energy efficiency14,15 have also been investigated. Moreover, cognitive radio16,17 is applied to enhance the performance of femtocells.18,19
For femtocells, how to manage access control is a challenging task. 2 There are three access mechanisms as listed above: open access, closed access, and hybrid access. De La Roche et al. 20 and Feng et al. 21 discuss the access mechanisms, yet without further specifications on hybrid access. Chandrasekhar and Andrews 22 focus on uplink capacity analysis and interference avoidance when closed access is selected. Xia et al. 23 claim that the open and closed access should be matched with non-orthogonal and orthogonal multiple access schemes, respectively. A few recent studies switch view to hybrid access, including Valcarce et al. 24 in which hybrid access aims to reduce interference and Chen et al. 25 in which utility-aware femtocells are refunded for their open part of resources.
A couple of works have discussed several kinds of refunding patterns. For instance, Chen et al. 25 propose that the refund is proportional to open time of each femtocell, which provides a fresh angle to view hybrid access. Besides open time, however, it is more valid to take other pertinent factors into consideration since channel state information also largely influences the achievable data rate. In other words, when resulting in an equal date rate, a femtocell which dedicates more open time because of poorer channel state should obtain no more refund than another femtocell which dedicates less open time with better channel state. In this sense, to be more objective and justifiable, we figure out the refund on the basis of achievable data rate.
Moreover, to cope with circumstances under asymmetric information, auction mechanism is an applicable approach. In auction, bidders could truthfully compete while the seller does not need every aspect of information.26,27 As another practical method, contract theory has also been utilized widely in the domain of management, marketing, and economics.28,29 Reaping benefits from its effectiveness to tackle problems under asymmetric information, 30 an increasing number of works have brought contract theory into wireless communication problems. Spectrum trading 31 and spectrum sharing32,33 are cogent examples.
Contribution
In this article, we uniquely make use of contract theory to design a mechanism about hybrid access for femtocells under asymmetric information, aiming to improve the utility of MUs.
The main contributions of the article are as follows:
We study the access problem of femtocell, using contract theory to cope with the problem of femtocell’s hybrid access with asymmetric information. Without too much information exchange, which also protects the privacy of femtocells, the macrocell provider could pinpoint the type of femtocells. According to different types of femtocells, the macrocell provider is able to give reasonable contracts to them and easily obtain their help to satisfy the demands of MUs. With some spectrum paid by the macrocell in return, femtocells save the cost on self-paid spectrum.
We use the achievable data rate to calculate the refund, which convincingly reflects the contribution of each femtocell. Using data rate as the criterion, we depict how much help a given femtocell exactly offers, thereafter avoiding the ambiguity when other indicators such as service time are taken into consideration. On this line, it leads to a tangible interaction between the macrocell provider and femtocells.
We provide the sufficient and necessary conditions, that is, individual rationality (IR) and incentive compatibility (IC), for a feasible contract. We then prove the optimality of our designed contract. Our final results show that only one type of femtocells would make contribution to the MUs and correspondingly acquire the refunded spectrum. In this way, the interaction protocol could work efficiently by letting the macrocell provider pick out the femtocells which have the suitable type.
We discover that hybrid access is a convincing mechanism for femtocells. The simulation results demonstrate that the femtocells do not have to open too much resource. Instead, a moderate open proportion—no more than 0.3—is viable enough. Hence, the femtocells are able to reserve adequate resource for their own FUs rather than sacrificing a lot. Our work goes forward with a practical application of hybrid access from the previous dual-option circumstance (open access and closed access).
The rest of this article is organized as follows. In section “System model,” we elaborate our system model. We then formulate the problem with contract theory in section “Problem formulation with contract theory.” Feasible contract along with relative sufficient and necessary conditions is analyzed in section “Feasible contract,” followed by the optimal contract design in section “Optimal contract design.” We make several further discussions in section “Further discussions.” Simulation results are presented in section “Simulation results,” and the conclusion is drawn out at last.
System model
In this section, we elaborate the basic system model. Figure 1 illustrates a two-tier network consisting of a single MBS and multiple femtocell base stations (FBSs). In total, there are N FBSs denoted as
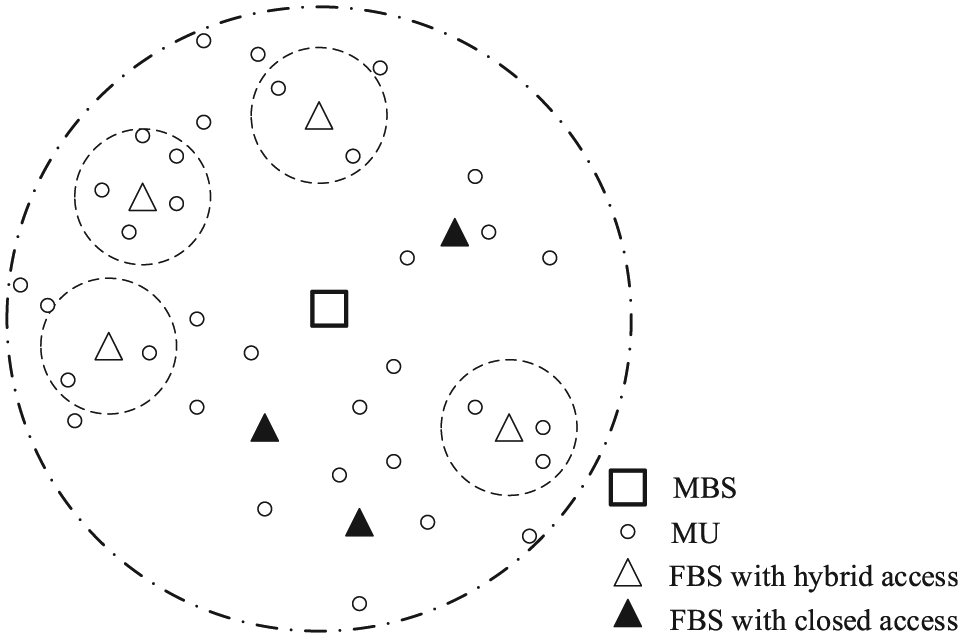
System model.
The MBS is the major wireless service provider of MUs. However, the MBS is not able to constantly meet MUs’ requirement on data rate. To be more explicit, as scores of MUs are asking for service, the MBS would have difficulty dealing with overwhelming requests beyond its capability. Considering the advantages mentioned before, a feasible solution is to turn to the FBSs. Notice that in the rest of the article we no longer intentionally distinguish the MBS and MUs and consider them interchangeable unless specified otherwise since they want to achieve the same goal.
The FBSs, however, play a positive role. In each frame, as long as the incentive from the MBS is sufficiently attractive, each FBS dedicates a portion of spectrum to its own FUs and offers service to MUs using the residual spectrum. Hence, FUs and MUs are distinguished in frequency. Each FBS transmits data to its own FUs via pre-assigned orthogonal channels by time division multiple address (TDMA), such that no intra-cell interference among FUs exists. Similarly, when a MU is admitted by a femtocell, it is also separated from FUs by orthogonal transmissions. As a consequence, the FBSs are able to provide better service quality to MUs and relieve the pressure on the MBS. Note that FUs are not explicitly depicted in Figure 1 as they are integrated with corresponding FBSs.
The incentive, as mentioned above, is the spectrum that the MBS pays to the FBSs. For the routine operation of the network, we assume that the MBS owns a fixed amount of spectrum to serve MUs. Yet, the FBSs are more flexible, and they are privileged to purchase certain amount of spectrum according to their instantaneous demands at the beginning of each frame. Rather than sharing part of its own spectrum with the FBSs, the MBS would pay a part of spectrum to the FBSs as a kind of spontaneous incentive and remuneration because the MBS always exhausts all of its own spectrum to cope with the overwhelming data requests from MUs. However, the idea that the MBS refunds the involved FBSs with spectrum instead of gratuity lies in the lower price of MBS’ preemption on spectrum. In practice, the spectrum deal could be implemented with the notion of cognitive mobile virtual network operator (C-MVNO),34,35 but we would not discuss it any more as it is out of our main scope.
Problem formulation with contract theory
In this section, we propose the utility functions of the MBS and FBSs and some principles in contract theory.
As specified in section “System model,” the MBS asks FBSs to help serve MUs and pays FBSs some spectrum in return. Meanwhile, the FBSs benefit from the free spectrum obtained by serving MUs.
Since the MBS and FBSs are rational and selfish, all of them care for their own utilities. In other words, the MBS wants to acquire more help from FBSs paying less spectrum, while the FBSs hope to get a larger amount of free spectrum without sacrificing their FUs a lot. In this way, the problem could be proposed. We would next discuss their utility functions.
Utility of the MBS
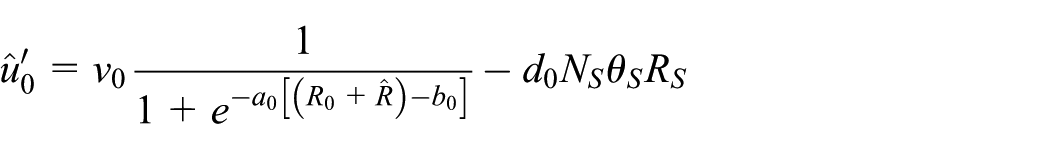
In this part, we concentrate on MBS’ utility. Having a fixed amount of spectrum, the MBS would fully utilize the spectrum to serve MUs. We denote the achievable data rate solely provided by the MBS as R0. At the same time, the MBS asks for FBSs’ help, and the FBSs would cooperate to increase available data rate to MUs if possible. Suppose that FBSn contributes data rate Rn, thereby the total achievable data rate of MUs is calculated as
However, in order to remunerate the FBSs, the MBS would pay some spectrum to them. For FBSn, the amount of spectrum that the MBS would pay is Bn with the unit price d0. As a result, the MBS has to expend
So the utility of MBS could be expressed as
where v0 is the unit revenue gain, a0 describes the sensitivity toward the increase in data rate, and b0 represents the reserved data rate requirement of MUs. Both a0 and b0 are positive. Note that Sigmoid function
36
is introduced here, which has been widely used to evaluate the satisfactory of users regarding resource allocation or service quality.37–39 It is obvious that MUs would be hardly satisfied below the threshold b0, whereas the satisfaction would increase swiftly once b0 is reached until reaching an asymptotic value. a0 determines the speed of increment, that is, a larger a0 means faster growth and vice versa. Notice that equation (1) means that a larger data rate, that is,
Apparently the MBS would like to maximize its utility u0 with the largest
Utility of the FBS
Driven by the spectrum paid by the MBS, the FBSs offer service to MUs. In this way, the FBSs could save some expenditure. We would next depict the problem from the perspective of FBSs.
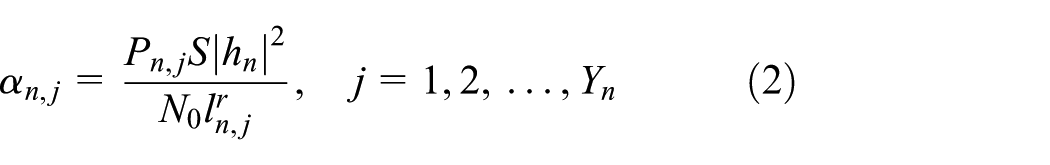
Every FBS utilizes pre-assigned orthogonal channels resulted from TDMA to transmit to MUs on corresponding spectrum. We assume log-normal distributed shadowing channel 40 to model the wireless channels. Suppose Yn MUs are served by FBSn, thereafter the received signal-to-noise ratio (SNR) between FBSn and MUs is given as
where Pn,j is the transmission power of FBSn, S is the log-normal shadowing component which has 0 dB as the mean of 10logS and σ
s
dB as the standard deviation, hn is the Rayleigh-distributed fading magnitude wherein
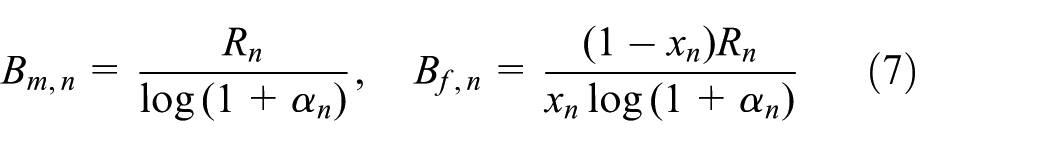
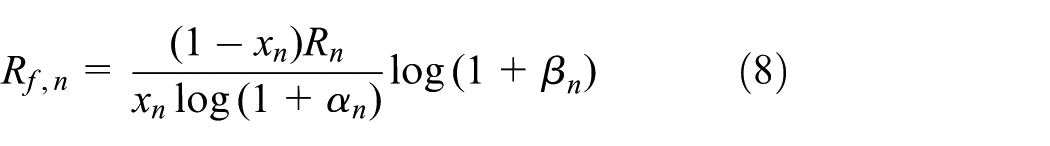
where Bm,n is the bandwidth that FBSn allocates to MUs.
In the meantime, the achievable data rate that FBSn serves its own FUs via pre-assigned orthogonal channels is
where Bf,n is the bandwidth FBSn allocated to FUs, βn is the received SNR between FBSn and its own FUs. Similar to equation (2), βn is derived as an identical value since FBSn could adjust its transmission power to control βn,k, which is the SNR between FBSn and all of the corresponding FUs
where Pn,k is the transmission power, ln,k is the distance between the FBSn and the kth FU, and Zn is the total amount of FUs served by the FBSn.
Then define the open proportion as
Obviously xn denotes the proportion of bandwidth contributed to MUs, while 1 − xn is the residual part of bandwidth reserved for FUs. Closed access, open access, and hybrid access are, respectively, established when xn = 0, xn = 1, and
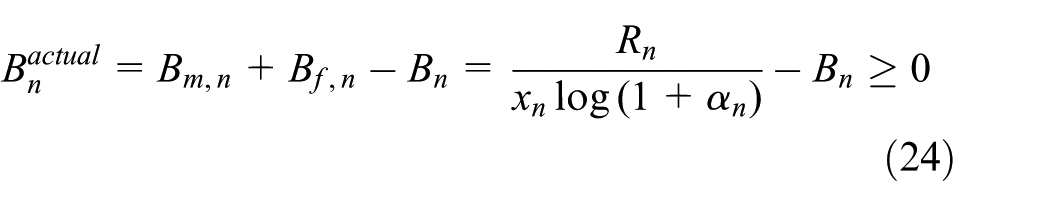
Combining equations (3), (4), and (6) would lead to
and further
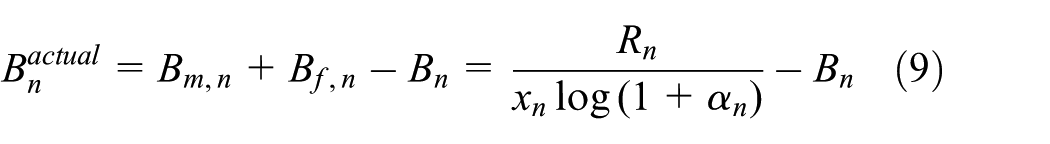
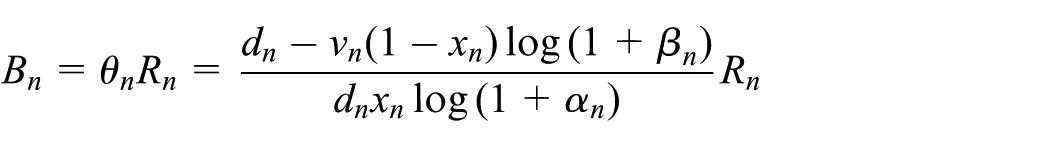
To give service to MUs and FUs, the FBSs have to purchase adequate spectrum at the beginning of each frame because the FBSs own no spectrum. FBSn should have paid for the total amount of spectrum it would occupy, namely,
At this moment, the utility of
where vn is the unit revenue gain of FBSn, and dn is the unit price per bandwidth for FBSn. Notice here that
It is straightforward that the utility of FBSn in equation (10) stands for the difference between the service gain to its own FUs using Bf,n bandwidth and the cost of purchased spectrum
Dividing both sides of equation (10) by dn would lead to the normalized utility
where
We assume that the unit price dn is always high enough to ensure that FBSn prefers the amount of bandwidth paid by the MBS as much as possible. It also guarantees
Notice here that
Obviously each FBS wants to maximize its own utility
Contract formulation
Both the MBS and the FBSs are eager to maximize their own utilities due to their rationality and selfishness, thus they have conflicting objectives. The conflict could be observed from u0 and un as well. The MBS wants to get larger Rn while spending less Bn, whereas the FBS would like to obtain more Bn with less contribution Rn.
In this part, we introduce contract theory to solve the whole problem. Here, we first introduce the principal–agent model. As the principal, the MBS offers contracts to the FBSs who act as the agents in the model.
The principal’s task is to design a set of rate Rn and bandwidth Bn. Without loss of generality, we assume that the set of types of FBSs is
After knowing the possible contracts offered by the MBS, each FBS chooses among these contracts according to its type. Obviously, a FBS would never take a contract which makes its utility negative.
Definition 1: IR
A contract that type
Also, as the MBS offers scores of contracts, each FBS would prefer a given contract to any other contracts.
Definition 2: IC
Type
for
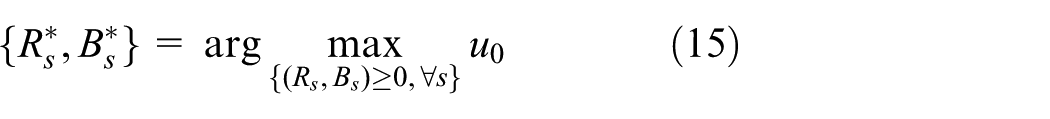
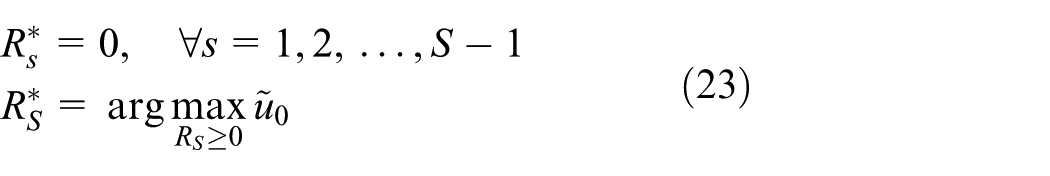
The optimal contract design for the MBS is the one maximizing its own utility as follows
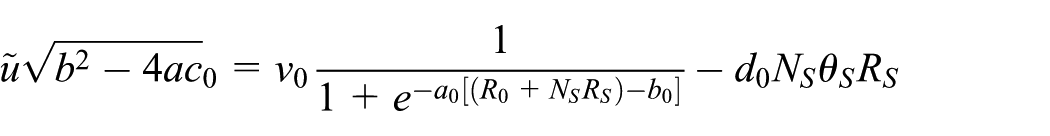
subject to the IR and IC constraints in equations (13) and (14), where u0 is deducted from equation (1) and rewritten as
In this article, the vector operations are considered component-wise. Specifically,
We here explain why xn = 0 is eliminated. It is obvious that, if a FBS determines xn = 0 which means that it contributes nothing to MUs, the MBS would definitely not pay any spectrum to this FBS in return. From this perspective, it is actually equivalent to the circumstance that this FBS quits as it is unwilling to help. Hence, the contract would be effective only when
However, the goal of FBSn is
subject to the IR and IC constraints in equations (13) and (14).
Till now, we have proposed the whole problem. We will next derive the optimal contract defined in equation (15).
Feasible contract
In this section, we provide the necessary and sufficient conditions to guarantee a contract to be feasible. It would be useful when we subsequently derive the optimal contract.
Necessary condition 1
For any feasible contract
Necessary Condition 1 demonstrates that a FBS which contributes more to MUs would have more spectrum paid by the MBS, and vice versa. In this sense, FBSs with identical amount of contribution would be refunded equally, and vice versa.
Corollary 1
For any feasible contract
Besides the above necessary condition and corollary, there is another necessary condition required for a contract to be feasible.
Necessary condition 2
For any feasible contract
Necessary Condition 2 demonstrates that the FBSs with a smaller type should have more spectrum paid by the MBS. Combining it with Necessary Condition 1 shows that the FBS having a smaller type would make more contribution as well as get more remuneration. It rightly corresponds to the discussion after equation (12) that a smaller type is advantageous.
The aforementioned necessary conditions and corollary are typical in contract theory. Referring to Gao et al., 31 we omit their proofs here for brevity.
From Necessary Conditions 1 and 2, we could reach the conclusion that for a feasible contract, the following structure should be satisfied
with
Also, we could obtain the following Theorem.
Theorem 1
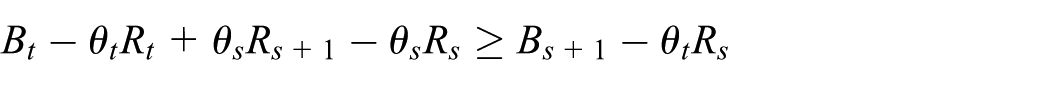
For a contract
Condition A.
Condition B.
Condition C. For any
Proof
Similar to Appendix A in Duan et al., 33 mathematical induction method is utilized here to prove the theorem.
We denote
To start with, we show that
Next we show that, when
Point 1. The IR and IC constraints for the new item
Point 2. For the existing types
Proof of point 1
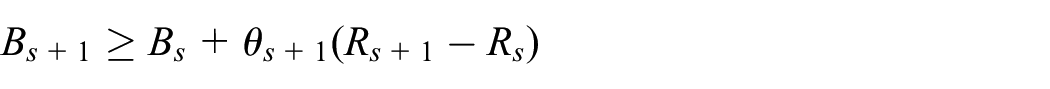
Now we prove the IR and IC constraints, that is, equation (18). As
Substituting s by
Combining the above two inequalities, we could obtain
Since
Again combining the above two inequalities, we would derive
and thus complete the proof of the IC constraint.
As for the IR constraint, due to
Combining the above two inequalities with
and thus complete the proof of the IR constraint.
Proof of point 2
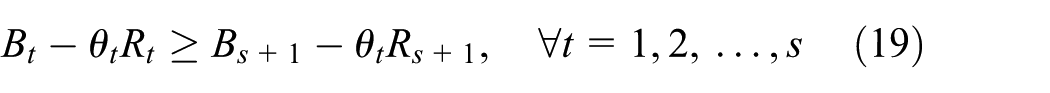
Now we prove the IC constraint in equation (19). As
Substituting s by s + 1 in the right side in Condition C induces
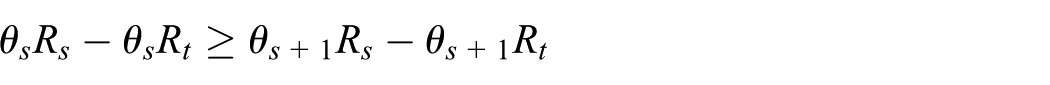
Combining the above two inequalities, we could obtain
Since
Again combining the above two inequalities, we would derive
and thus complete the proof of the IC constraint.
With all of the above-mentioned details, the theorem is proved to be true. ■
It is also necessary to point out the following theorem.
Theorem 2
The sufficient conditions in Theorem 1 are also the necessary conditions for a feasible contract.
Proof
Note that the sufficient conditions in Necessary Condition 2 are also necessary for a feasible contract. To be more explicit, Condition A is the same as the structure mentioned in equation (17), while Condition B pinpoints the IR constraint for the highest type
prove Condition C ■
Optimal contract design
After obtaining the conditions for feasible contract, we look for the optimal contract in this section. The optimal contract has to enable the MBS to maximize its utility. In common scenes, the MBS merely knows the exact number of each type, that is,
An ordinary way to deal with the problem is to find out the solution to equation (15), yet it appears to be difficult to a large extent because of complication. So we take the advantage of contract theory, especially the IR and IC constraints. Also notice that contract theory works well in such an asymmetric situation where
Specifically, we introduce a sequential optimization approach with three steps in the following:
Given a fixed feasible rate
We then obtain the best rate
We ultimately prove the optimality of
Following the line of section V in Duan et al., 33 we derive the optimal contract below.
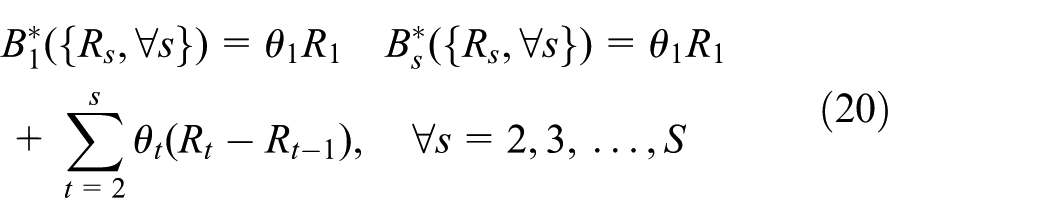
Proposition 1
Let
Proof
To begin with, it is easy to find out that the bandwidths in equation (20) could form a feasible contract using Theorem 1. Thereby, we would concentrate on the optimality and uniqueness in what follows.
We first prove that, with fixed rates, the bandwidths defined in equation (20) would lead to the maximization of MBS’ utility in equation (16). Contradiction method is used here.
For the MBS, suppose another feasible bandwidths
For s = 1, there would have
Also, for
Continuing the above process, we could finally reach
Consequently
We then demonstrate its uniqueness. Using contradiction method again and supposing another feasible bandwidths
With Proposition 1, equation (15) could be transformed to
where
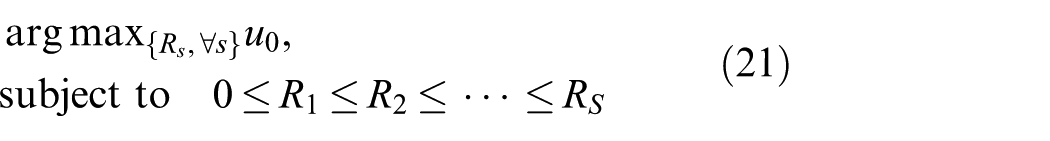
Theorem 3
As an optimal contract, the contract items for FBSs with the lowest type are positive, while contract items for others are zero, that is
Proof
Contradiction method is used here. Suppose there is an optimal contract in which
If such a constant overall rate
It is obvious that
so
Theorem 3
It facilitates us to simplify the optimization problem (21) as
where
Because Sigmoid function contains both concave and convex segment, it is difficult to give a closed-form solution
Based on the above-mentioned theorems and proposition, we could derive the theorem below.
Theorem 4
Further discussions
Interaction protocol
In this part, we elaborate the interaction between the MBS and the FBSs. The algorithm consists of four steps:
The MBS broadcasts the possible contract
Each FBS chooses one contract and feeds its choice back to the MBS. To be competitive, every FBS would make efforts to make its type as small as possible.
According to the contract, the MBS pays some spectrum to each involved FBS, and the FBS purchases the residual part of the bandwidth.
After everything is set down, the MBS and the FBSs begin to give service.
Spectrum paid by the MBS
Compared with the idea that the MBS could reimburse some gratuity directly, it appears confusing to some extent that the MBS refunds the FBSs with spectrum. We will explain it in terms of social surplus.
In our model, social surplus is defined as the aggregate utility of MBS and all involved FBSs
In contrast, if the MBS directly pays refund
Due to the low price of spectrum resulted from MBS’ preemption, that is,
Bandwidth constraint
In section “Utility of the FBS,” we assumed that
which means that the bandwidth the MBS paid for
In terms of Proposition 1 and Theorem 3, we have known that
Contradiction method is then used and suppose that
Substituting
into equation (25), we would derive
and further
Apparently, equation (26) fails to be satisfied, thereafter equation (24) is guaranteed, implying that the refunded bandwidth could always be employed.
Limited bandwidth in practice
In our previous parts, we assume that the MBS could purchase as much bandwidth as possible without any upper bound. However, in practice, there is always limited bandwidth available. Let
To cope with the problem, we randomly pick out
where
On this line, in case
Incomplete information on contract design
In this section, we focus on the special scene where the MBS does not even know the number of each type of FBSs and it only knows the total number of FBSs N, the probability
To address the optimization in this scenario, we adopt the low computation complexity approximate algorithm, decompose-and-compare algorithm, to compute a close-to-optimal solution efficiently. Specifically, in this algorithm, we will compare S simple candidate contracts and pick the one that yields the largest utility for the MBS. The key ideas behind this heuristic algorithm are as follows:
One positive contract item per contract. In each of the S individually optimized candidate contracts, there is only one positive contract item (for one or more types). For the contract item in the sth candidate contract, this positive contract item is offered to FBSs with types equal to or smaller than type
A tradeoff between efficiency and uncertainty. Among S optimized candidate contracts, the best one that achieves the best tradeoff between efficiency and uncertainty will be picked. Under the incomplete information, it is not clear which type is the lowest among all FBSs existing in the current system. If a candidate contract offers the same positive contract item for types equal to or smaller than type
The decompose-and-compare algorithm works as follows:
Decomposition. Construct S candidate contracts, where for the sth contract Offers the same contract item Computes the optimal
Comparison. Choose the best contract out of S candidates to maximize the MBS’ expected utility.
Unlike the algorithm in common scene, here the computational complexity increases with the number of FBS types. This is because that the MBS may want to involve more than one type of FBSs in the contract to mitigate the uncertainty and avoid risk of having no relay in a particular network realization. However, the complexity of this approach will increase with the number of types. In addition, in section “Simulation results,” we show by numerical results that the proposed decompose-and-compare algorithm achieves a performance very close to the optimal solution in most cases.
Simulation results
In this section, we present some numerical results in order to evaluate how contract theory performs in our scenario. We consider an area of
In our simulation setting, there are overall
As our focus, the open proportion affects the type of each FBS and consequently the data rate of MUs served by the FBSs. It has been discussed before that a larger open proportion would make the type smaller and make the data rate of MUs higher. Figure 2 demonstrates such phenomena. When the open proportion rises from 0 to 1, in other words from closed access to hybrid access and ultimately to open access, the service data rate increases as well. The service rate from FBSs to MUs is another crucial factor since poor SNR counteracts the advantage of more bandwidth. We depict different situations where

Date rate
Thanks to the service data rate, the utility of MBS would be correspondingly enhanced. Figure 3 shows the contribution of FBSs’ open proportion to the MBSs utility. Notice here that the increase in utility is particularly remarkable when the FBSs step off closed access. Hence, merely a small part of spectrum is able to improve the utility of MBS to a large extent, meaning that each FBS could reserve abundant spectrum for its own FUs instead of sacrificing a lot.

Utility of MBS u0 with different open proportion
The type of FBS is another important element. We have shown that smaller type is more competitive. Therefore, we investigate the relationship between
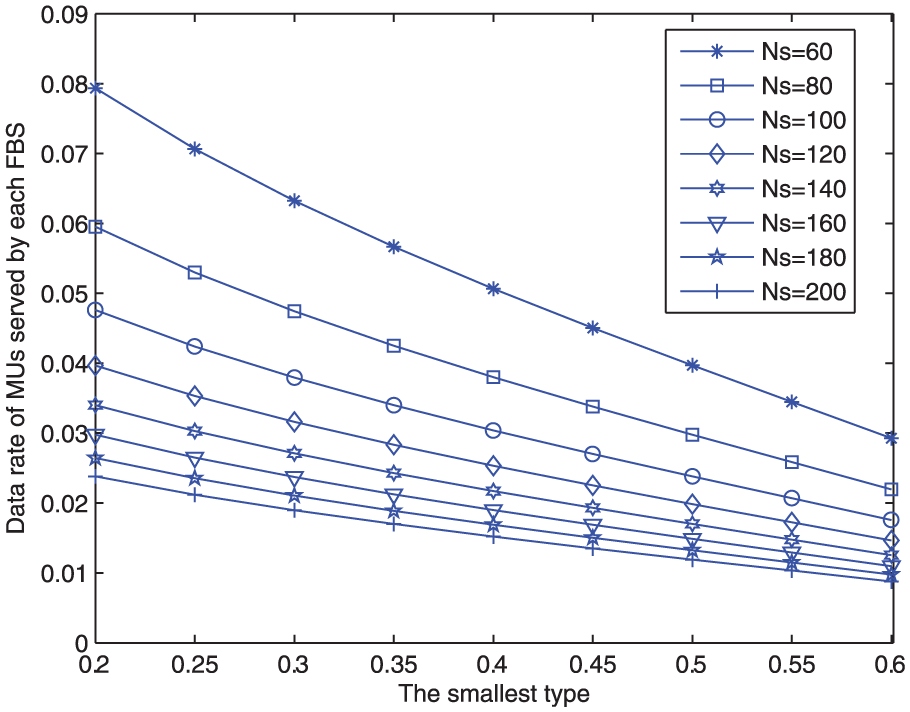
Date rate
The analysis of remuneration to type

Total bandwidth refund
Intuitively, the price for the MBS to purchase bandwidth affects MBS’ utility as well as FBSs’ willingness to help. We thus manage to observe the utility of MBS by gradually increasing the unit price. Figure 6 checks the standpoint that higher price appears to be less attractive and leads to the decrease in utility. Hence, the difference between the price for the MBS and for the FBSs should be great enough as the motivation.

Utility of MBS u0 with different unit price of bandwidth for MBS d0.
Moreover, we add a random algorithm for the comparison with the proposed contract theory–based algorithm. Specifically, the random algorithm picks out

Utility of MBS with different
Finally, to illustrate the performance of decompose-and-compare algorithm for incomplete information in section “Simulation results,” we consider only two types of FBSs:
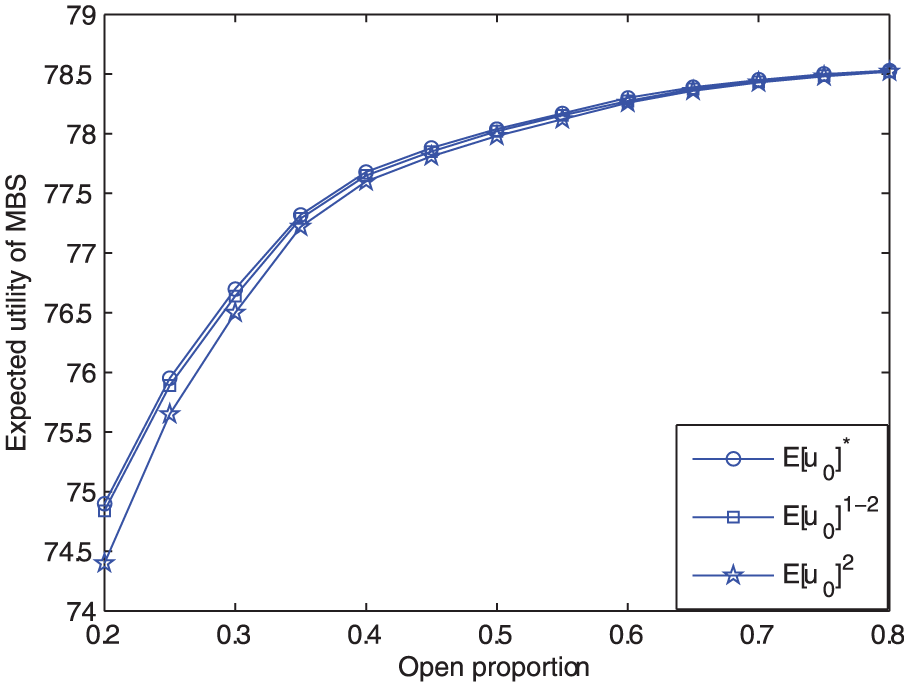
Comparison between MBS’ optimal expected utility using optimal exhaustive search method and the two candidate contracts of the decompose-and-compare algorithm, as a function of the open proportion

Comparison between MBS’ optimal expected utility using optimal exhaustive search method and the two candidate contracts of the decompose-and-compare algorithm, as a function of the open proportion
Conclusion
In this article, we investigate hybrid access for the femtocells with asymmetric information. To maximize the utility of MBS, the FBSs would open a portion of their spectrum to help serve MUs, while the MBS pays part of the spectrum to the FBSs as refund. Considering asymmetric information, we build a principal–agent model and use the rate–bandwidth combinations to describe the interaction between the MBS and the FBSs. We introduce contract theory to model the problem, incorporating the IR and IC constraints. We define the type of FBS at first and then derive the optimal contract after studying the necessary and sufficient conditions for feasible contract. In this way, the service quality of MUs could be improved thanks to the open spectrum of the FBSs. Also, several issues are discussed to corroborate our design.
Footnotes
Academic Editor: Sangheon Pack
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by National Natural Science Foundation of China (61174127, 61573245).