Abstract
The original minimal exposure path problem in wireless sensor networks did not consider path constraint conditions. To consider the actual demand, this article proposes a minimal exposure path problem that requires the passage of the path through the boundary of a certain region. In this situation, because a corresponding weighted graph model cannot be developed, the methods that are used to solve the original minimal exposure path problem (the grid method and the Voronoi diagram method) are ineffective. Thus, this article first converts the problem into an optimization problem with constraint conditions. Because of the difficulty in finding a solution due to the model’s high nonlinearity and high dimensional complexity, as well as the special characteristics of the problem, a hybrid genetic algorithm is proposed to find the solutions. This article also provides a proof for the convergence of the designed algorithm. A series of simulation experiments demonstrates that the designed optimization model with constraints and the hybrid genetic algorithm can effectively solve the proposed minimal exposure path problem.
Introduction
Wireless sensor networks (WSNs) are composed of large numbers of sensor nodes that have sensing, data processing, and wireless communication functionalities. Because of their advantages of low cost and expendability, WSNs have been widely used in commercial and military fields (e.g. environmental monitoring, earthquake and weather forecasts, underground and deep-water probes). Research and applications of WSNs have attracted the attention of many researchers and manufacturers.
Coverage is one of the key fundamental technologies of WSNs; it reflects the WSN’s perceptibility of the monitored region. The coverage quality directly influences the performance of the monitoring system, and the measurement of coverage quality helps to describe the coverage of the entire network for the monitored targets (stationary or moving targets); it is also helpful in guiding the adjustment and optimization of sensor node deployments.
There have been many discussions about measuring coverage for target detection,1–7 and most have concentrated on fence coverage problems. From the perspective of the characteristics of the monitored objects, 1 the coverage problem in WSNs can be categorized into regional coverage, scanning coverage, and fence coverage. The goal of research on fence coverage is to find one or multiple paths that connect the starting point to the end point, so these paths can describe the quality of detection and monitoring of moving targets under different definitions of coverage quality. “Exposure crossing”2,8 simultaneously considers the temporal factor of “target exposure” and the special factor of the “sensing strength” of the sensor node on the target. Mathematically, it can be described as the integration of the sensing strength curve along the crossing path over time and space, and it is used to judge the quality of the coverage of a deployed sensor node on the exposure path. This measuring method was first discussed for the fence coverage problem and is currently the most widely used method.2,8 The path that corresponds to the minimal exposure crossing is called the minimal exposure path; the problem of searching for this path is called the minimal exposure path problem.
It is pretty remarkable that in the practical WSN coverage problems, the importance of each location in the covered region might not be the same; for example, some regions in the area might be more sensitive. In addition, due to particular conditions (such as high temperatures, harsh environments, or sensitive and dangerous regions), some regions are not accessible; sensor nodes cannot be deployed within these regions, and the only option to protect these regions is to deploy sensors in the surrounding area. The moving target starts at a fixed point. When it reaches a sensitive region, it can only move along the boundary of the region (a small portion of the path in Figure 1 belongs to the boundary of this sensitive region) and then reaches the fixed end point. Thus, the ability of the WSN to monitor the moving target from the starting point to the end point along a certain path needs to be quantified, and the path with minimal exposure must be obtained. For convenience, this type of sensitive region is called a special protection region and corresponds to the problem discussed in previous studies.2,8 The path that is sought is called the minimum exposure path problem with constraint conditions (MEP-CC problem). The proposed MEP-CC problem in this article considered that the mobile target only can move along some part border of a special region as it cannot get through this special region. There is no restriction that the region is whether in the middle of the monitoring area.

A minimal exposure problem that contains special protection region boundary condition constraints.
The main contributions of this article are as follows:
To consider realistic scenarios, this article proposes a minimal exposure path problem with constraint conditions. The problem considers the special requirement that the moving target can only move along the boundary of an inaccessible area of the covered area because sensors cannot be deployed in that region.
In contrast to the traditionally used grid-based method and Voronoi-diagram-based method, this article first abstracts the proposed MEP-CC problem into an optimization model with constraints, which allows the use of mathematical optimization methods to solve the MEP problem.
Due to the difficulty in solving the designed complex high dimensionality and highly nonlinear optimization model with constraint conditions, this article considers the characteristics of the actual problem and designs a reasonable form of the fitness function and a local searching method that can eliminate paths with sawtooth patterns. A hybrid genetic algorithm is designed to solve the proposed MEP-CC problem, and the proof of the overall convergence of the algorithm is provided.
The MEP-CC problem proposed in this article is an expansion of the original MEP problem; the designed solution method is suitable for large-scale sensor node deployments.
The remaining content and structure of this article are as follows: In section “Related works,” we present some related works in MEP problem. Section “Problem description” introduces the basic concepts and limitations of the traditional MEP problem and proposes a MEP-CC problem that contains a special protection region. Section “Multivariate optimization model for the minimal exposure path problem with special protection region boundary condition constraints” analyses the reason that traditional MEP problem-solving methods are ineffective for the proposed problem and then develops a multi-variant optimization model. Section “A hybrid genetic algorithm” analyses the highly nonlinear characteristics of the new model, combines the characteristics of the practical problem, and designs a hybrid genetic algorithm. Section “Global convergence analysis of the hybrid genetic algorithm” provides a proof for the convergence of the designed algorithm. Section “Experiments and discussions” develops and analyses six experimental scenarios (including deterministic, random, and large-scale deployments of sensor nodes), and section “Conclusion” presents the conclusions.
Related works
The essence of the minimal exposure path (MEP) problem is the curve extreme problem in mathematics, 9 which is also called the functional extreme variational problem. 10 A common mathematical method of solving the variational problem is to solve the corresponding Euler–Lagrange differential equation; 5 an analytical solution of this differential equation can provide a precise expression of this path. However, in the multiple sensor nodes scenario, the Euler–Lagrange differential equation is difficult to express and is even more difficult to solve due to its high nonlinearity. Thus, an accurate analytical solution cannot be obtained even when the mathematical essence of this problem had been determined.11–13 Currently, the only available accurate analytical solution is for a single sensor node scenario; 11 only approximation solutions are available for the minimal exposure path problem in the multiple sensor nodes scenario. Approximation solution methods mainly include grid-based searching methods and the Voronoi-diagram-based computational geometric method. Meguerdichian et al. 14 first designed an exposure crossing problem-solving method based on the idea of grids. This method first divides the sensing region into square grids, calculates the degree of exposure of each side of the grid based on the node distribution, and uses a shortest path algorithm, such as the Dijkstra algorithm, to find the path that crosses the sensing region and has the minimum exposure. The Voronoi-diagram-based computational geometric method was proposed by Veltri et al. 15 The set of next candidate positions of the moving target is analyzed through a Voronoi diagram; at the same time, the degree of exposure of the moving object that follows the path during a certain time period is defined as the sensing strength of the sensor nodes along the path. Improvements to these two methods and applications to various scenarios have been proposed: several studies11,12 have combined the Voronoi diagram method with the Euler–Lagrange differential equation for a single sensor node and have proposed an improved method, while another study 13 applied the grid method to solve for the minimal exposure path of anisotropic sensor nodes. These studies address variants and applications of the grid method and the Voronoi diagram method for specific situations.
The mathematical problem that corresponds to the MEP-CC problem is the curve extreme fitting problem, 9 and the essence is a variational problem (unilateral variational problem with functional extremes).9,10 Similar to the original MEP problem, under the multiple sensor nodes scenario, the MEP-CC problem cannot be solved by solving Euler–Lagrange partial differential equations. Due to the constraints of the protected region boundary conditions, a corresponding weighted diagram model cannot be developed; the two basic types of approximation solution methods, the grid-based method and the Voronoi-diagram-based method, are also no longer appropriate. To solve this type of problem, this article first abstracts the MEP-CC problem with a special protection region into an optimization problem with constraints. This optimization problem is a complex problem of high dimensionality and high nonlinearity; it is difficult for traditional mathematical optimization methods to find an overall optimized solution. Under the framework of a genetic algorithm, this article combines the characteristics of the problem and designs a hybrid genetic algorithm solution method. A series of experiments demonstrates that the designed model and solution method can solve this new minimal exposure path problem. Compared with the grid-based and Voronoi-diagram-based methods, the designed method can not only be applied to the MEP-CC problem but also to the original MEP problem and is more general than the existing method.
Problem description
Degree of exposure and the minimal exposure path problem
The degree of exposure was first defined by Meguerdichian and colleagues.2,8 Assume that m sensors, s1, s2, …, sm, are distributed within the range of sensing region A to monitor a moving target crossing A. These sensor nodes can capture their own position information through some defined mechanism16–18 and can ensure the reliability of coverage of the areas surrounding them.19–21 A moving target travels from a fixed starting point s along a path P across region A to a fixed end point. The mathematical definition of the degree of exposure is2,8
where I(P) represents the sensing strength of m sensors, s1, s2, …, sm, when detecting the moving target at a certain point p on path P. Common expressions of I(P) include the full sensing mode
The MEP problem (for convenience, this is called the original MEP problem in the remainder of this article) is to find the path that connects the starting point s to the end point d that has the minimum degree of exposure. Assuming that path P can be expressed in the form y = y(x), equation (1) is a function of the function y(x), and it can be described mathematically as a functional11–13
The MEP problem can thus be expressed as
A minimal exposure path problem with constraint conditions
In practical field applications, certain regions within the sensing region A need to be protected. However, limitations that are caused by some conditions, such as geospatial restrictions; harsh environments; or unreachable, dangerous, and sensitive regions, prevent sensor nodes from being deployed in some locations, and the only option is to pre-deploy sensor nodes around these regions. The moving target cannot enter this region; when it approaches the region from the starting point, it can only move along the boundary of the region. It will then leave the boundary at a certain point and eventually reach the end point. In the example shown in Figure 1, the region within the curve f(x, y) = 0 is a sensitive region that needs to be protected. Due to the local conditions, sensor nodes cannot be deployed within the region f(x, y) < 0 and can only be deployed in the region f(x, y) > 0. The moving target departs from the starting point s, follows a path, reaches point c on the boundary of the protected region, moves along the boundary to point k, and then follows a path from k to point d. The goal is to find the path with the minimal degree of exposure. This is the MEP problem with a special protected region boundary constraint condition, which corresponds to the curve extreme fitting problem in mathematics 9 (unilateral variational problems with functional extremes).9,10
The path in Figure 1 can be expressed as being composed of three path segments,
The MEP problem that contains a must-pass region boundary can then be expressed as
The constraint condition represents that the integration path
Multivariate optimization model for the minimal exposure path problem with special protection region boundary condition constraints
The common solution methods for the original MEP problem2,8 include the grid-based method 14 and the Voronoi-diagram-based method; 15 both methods abstract the problem into a diagram model to obtain the solution. However, the grid method is ineffective for the minimal exposure path problem with a must-pass region boundary constraint proposed in this article because the constraint condition makes it impossible to calculate the weight of the grid node that corresponds to the boundary position of the constraint region; thus, the corresponding weighted diagram model cannot be developed. The Voronoi diagram method is also ineffective for the proposed problem because the constraint condition destroys the connection between the boundary of the protected region and the Voronoi vertex, so the corresponding weighted diagram model cannot be developed. As discussed in section “Introduction,” the core of the MEP-CC problem with a special protection region boundary (3) is a functional extreme with constraints problem, and the variational method cannot be used to obtain accurate analytical solutions of functional extreme problems.11–13
Based on these considerations and analysis, this article employs an indirect functional extreme solving method: the finite difference method.
10
Figure 2 illustrates the path
where

A path that has been discretized by the finite difference method.
The constraint condition
A hybrid genetic algorithm
Many mathematical deterministic optimization methods can be used to find solutions to optimization problems, such as the steepest descent method,
22
the quasi-Newton method,
23
and the filled function method.
24
However, these methods require information such as the derivative of the function and can only be used in global optimization problems with well-behaved functions; they are difficult to use for complex engineering optimization problems. The form of the derivative of the optimization object function
Compared to the deterministic optimization methods described above, stochastic optimization methods have fewer requirements for the functions; only the values of the functions are needed, and there are few requirements for the properties of the objective functions (e.g. differentiability, continuity). They can be used to solve most optimization problems and are well suited for complex engineering optimization problems. This article uses the genetic algorithm, 25 which is a relatively mature stochastic optimization method, to design a method to solve the MEP-CC problem. However, the direct application of the standard genetic algorithm would result in a sawtooth-shaped path (Figure 3) because of the difficulty in controlling the amount of computation of the genetic algorithm when solving high-dimensional nonlinear optimization problems; thus, the rate of convergence toward the global optimized solution is slow. Many researchers26–32 have studied the fundamental theory and techniques of the genetic algorithm in detail and have designed operators to speed up the convergence and improve the quality of the optimized solutions as well as the corresponding hybrid genetic algorithms. This article designed a key fitness function and a highly efficient local search method by considering the actual problem, which can effectively eliminate the occurrence of the sawtooth path solution and increase the convergence speed. The specific analysis and design process is as follows.

Part of a path that corresponds to the continuous component
Fitness function
Only a well-designed fitness function can guide the algorithm in a desired searching direction. The genetic algorithm is an iterative searching algorithm; thus, designing a fitness function with a good form is critical. In the optimization problem equation (5), the continuous variable to be optimized is
Coding and constraint condition treatment
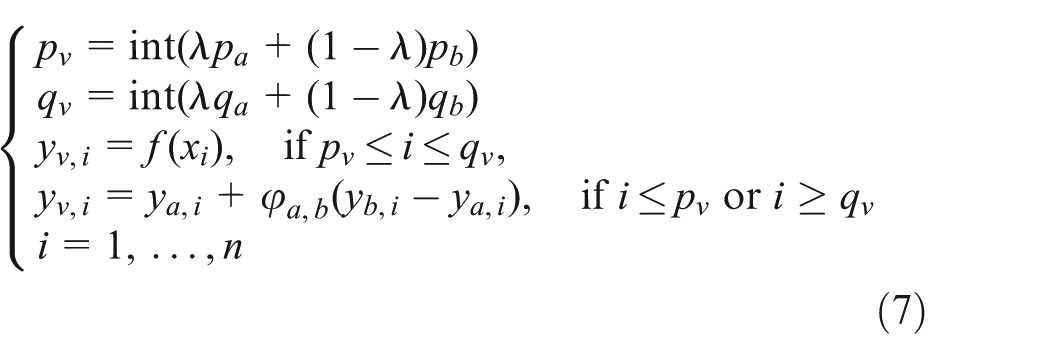
The variables to be optimized in the optimization problem (5) include the n − 1dimensional continuous variables
Population initialization
Following the normal method, the individual population members
where
Crossover operator
For two different individual members
where int represents a rounding function,
To ensure that the individual is legitimate, for the
Mutation
Multiple Gaussian mutations are used; every component of the continuous variable
where
Local search operator
For the integral component and continuous component contained in the individual
Local search for the continuous component
Because equation (5) is a highly nonlinear and high-dimensional optimization problem, the convergence rate is not sufficiently fast when the standard genetic algorithm is used, and a solution with a sawtooth-shaped curve is often obtained (Figure 3). For a high dimensionality and highly nonlinear complex fitness value function
A gene segment
where
The gene segment value
Local search for the integral component
For the integral component
Selection method and production of the child population
In all of the individuals in the current population (parent generation) and all of the child populations (which are produced by crossovers and mutations), we select the first pop individuals to form the seed population for the next generation.
Hybrid genetic algorithm

Global convergence analysis of the hybrid genetic algorithm
This section presents the mathematical analysis and proof of convergence for the designed algorithm. It is a kind of stochastic search iterative algorithm, during each iteration, the population is modified by a number of successive probabilistic transformations such as crossover operator, mutation operator, and designed local search operator. The resulting new population depends only on the state of the current population in a probabilistic manner. This property reveals that Algorithm 1 is of a stochastic nature. Notice that the deterministic concept of “convergence to the optimum” is not appropriate to define exact stochastic convergence as follows.
Let
Definition 1
Let

then the proposed algorithm is called to converge to the global optimal solution with probability 1, where Prob{ } represents the probability of random event { }.
To discuss the globally convergent properties of the proposed Algorithm 1 , we need to introduce the following concepts.
Definition 2
For the given two chromosomes a and b, if

then b is called to be reachable from a by crossover and mutation, where MC(a) represents the offspring that were generated from chromosome a by crossover operator and mutation operator.
Lemma 1
If a genetic algorithm with a finite search space S satisfies the following conditions, it will converge to the global optimal solution with probability 1 regardless of the initial population distribution.
Hypothesis 1. For any two chromosomes a, b ∈ S, b is reachable from a by crossover and mutation.
Hypothesis 2. The population sequence

For the proposed Algorithm 1 , the following conclusion applies.
Theorem 1
The proposed Hybrid Genetic Algorithm for the MEP-CC model (5) of the MEP problem converges to the global optimal solution with probability 1 regardless of the initial population distribution.
Proof of Theorem 1
According to the initial population generation method as described in section “Population initialization,” a solution
First, it is proved that
Algorithm 1
satisfies the Hypothesis 1,that is, for any two chromosomes
After applied local search operation in Step 4, if
Consider the probability of
The proof is similar for
So, Algorithm 1 holds Hypothesis 1. Now, Algorithm 1 is proved to satisfy Hypothesis 2. In fact, it can be seen from the selection scheme at Step 6 of the proposed algorithm that P(k + 1) consists of the best pop chromosomes chosen from P(t)∪O1∪O2∪O3 for t = 0, 1, … Thus, the population sequence P(0), P(1), …, P(t), … is proved to be monotone.
From Lemma 1, we have the conclusion Algorithm 1 that converges to the global optimal solution with probability 1 regardless of the initial population distribution.▪
Experiments and discussions
To test the effectiveness of the designed algorithm in solving the MEP-CC problem that contains protected regions, we designed a series of simulation experiments that include scenarios with deterministic and random distributions of sensor nodes outside the protected region.
The computer used as the test platform was configured with a 2.8 GHz Pentium(R) Dual-Core CPU E5500, 2 GB of RAM internal memory, and the Win XP (SP3) operating system. MATLAB 7.6.0 was used as the simulation software. Deterministic and random distributions (including the large-scale random node distribution) of the sensor nodes were established. The experimental parameters for the nodes were
Scenario of the deterministic deployment of sensor nodes and experimental results
Experimental scenarios for the deterministic deployment of equilateral triangular and square sensor node distributions outside the protected region were designed; the specifics are as follows.
Scenario 1
The sensing region is a 10 m × 10 m square, and the bound of protected region is a parabola, which is marked by the solid blue line in Figure 4. In total, 31 sensor nodes are deployed deterministically outside the protected region, and no sensor nodes are deployed within the protected region. The adjacent sensor nodes outside the protected region form squares. The path starts at (0, 3.5) and ends at (10, 4.5); this scenario is shown in Figure 4(a) (the descriptions of these items in Figure 4 that shows the subsequent scenarios will not be repeated). The black stars mark the locations of the sensor nodes. The red plus signs and the red dashed line mark the minimal exposure path obtained; the number of every fifth point on the path is marked. The black dashed line marks the sides of the Voronoi diagram (usually called the Voronoi sides) that correspond to the sensor nodes; because the sensor nodes are distributed in squares, the corresponding Voronoi sides form a square grid. The values of the relevant parameters in the algorithm are as follows: the individual code size is 56, the population size is 50, and the local search parameters are Δ = 2 and k = 10. With the exception of the portion along the protected region boundary, the minimal exposure path outside the protected region almost always lies along Voronoi sides; this is consistent with the conclusions of traditional MEP problems.1,14,15 The final fitness value is 57.2942. The curves in Figure 4(b) show the evolution of the optimum path during the 1st, 10th, 20th, 40th, 75th, and 150th generations of the seed populations.

Scenario 1: starting point (0, 3.5); end point (10, 4.5); the special protection region is a parabola; and 31 sensors form a square distribution: (a) node deployment and final path result and (b) optimum path evolution process.
Scenario 2
In total, 30 sensor nodes are deployed deterministically in a 10 m × 10 m region; the adjacent sensor nodes outside the protected region are arranged in equilateral triangles. The path starts at (0, 3) and ends at (10, 5). The boundary of the protected region is a parabola, which is marked by the solid blue line in Figure 5, and no sensors were deployed within the protected region; this scenario is shown in Figure 5(a). Because the sensor nodes outside the protected region are deployed in equilateral triangles, the corresponding Voronoi diagram is a regular hexagonal grid. The values of the relevant parameters in the algorithm are as follows: the individual code size is 64, the population size is 50, and the local search parameters are Δ = 1.8516 and k = 10. As in the previous scenario, the minimal exposure path almost always follows Voronoi sides; this is consistent with the conclusions of traditional MEP problems.1,14,15 The final fitness value is 95.3662. The curves in Figure 5(b) show the evolution of the optimum path during the 1st, 10th, 20th, 40th, 75th, and 150th generations of the seed populations.
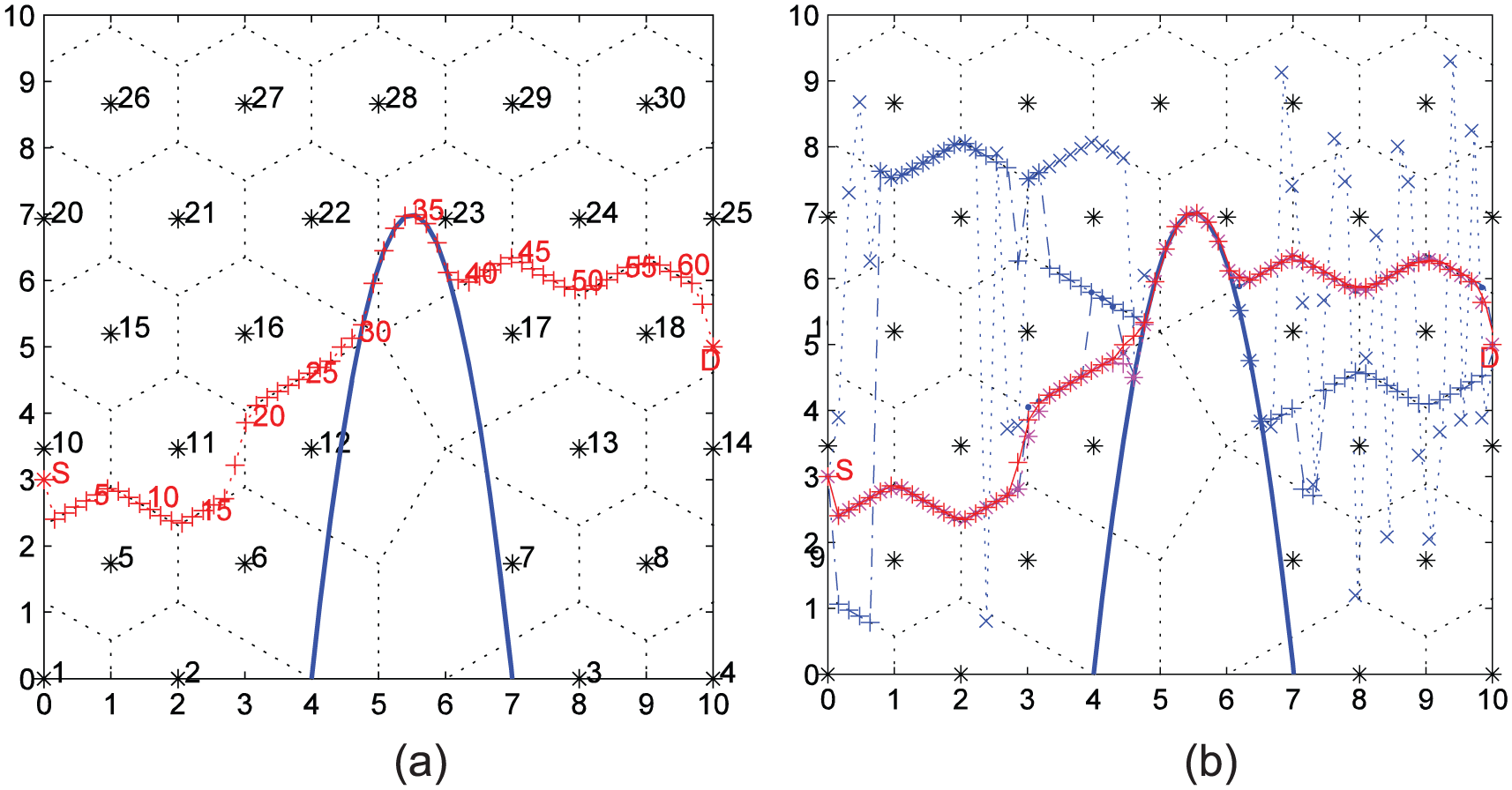
Scenario 2: starting point (0, 3); end point (10, 5); the special protection region is a parabola; and 30 sensors form a triangular distribution: (a) node deployment and final path result and (b) optimum path evolution process.
The minimal exposure paths outside the protected region follow Voronoi sides in both scenarios, which is consistent with the conclusions from previous studies.1,14,15 This demonstrates the accuracy and reliability of this method of determining the minimal exposure path in scenarios with deterministic sensor node deployments.
Uniform random deployment of sensor nodes
To generate a uniform random deployment of sensor nodes, we produced coordinate locations for each sensor node
Scenario 3 is in a 10 m × 10 m region, and the special protected region is a parabola marked by a solid blue line. A total of 46 sensor nodes are randomly deployed outside the protected region, and no sensors are located inside the protected region. This scenario is shown in Figure 6. Scenarios 4–6 use 160, 250, and 350 sensor nodes in a 100 m × 100 m region; these scenarios are shown in Figures 7–9, respectively.

Scenario 3: starting point (0, 40); end point (100, 50); 46 randomly distributed sensors; population size 50; codeSize = 72; total evolution generation 150; search range Δ = 16.9706, k = 8; and final fitness value 861.47: (a) node deployment and final path result and (b) optimum path evolution process.

Scenario 4: starting point (0, 40); end point (100, 50); 160 randomly distributed sensors; population size 50; codeSize = 128; total evolution generation 150; search range Δ = 4.2, k = 10; and final fitness value 520.1987: (a) node deployment and final path result and (b) optimum path evolution process.

Scenario 5: starting point (0, 40); end point (100, 50); 250 randomly distributed sensors; population size 50; codeSize = 152; total evolution generation 300; search range Δ = 6, k = 9; and final fitness value 1290.6453: (a) node deployment and final path result and (b) optimum path evolution process.

Scenario 6: starting point (0, 40); end point (100, 50); 350 randomly distributed sensors; population size 50; codeSize = 176; total evolution generation 300; search range Δ = 5, k = 9; and final fitness value 758.4164: (a) node deployment and final path result and (b) optimum path evolution process.
The four scenarios with randomly deployed sensor nodes use increasing numbers of nodes and include situations with small- and large-scale random sensor node deployments; the corresponding dimensionality of the model (5) gradually increases as well. In Scenarios 4–6, the dimensionality of the continuous component exceeded 100; the dimensionality of the problem (individual code size) was very high. The algorithm can solve these problems very well. Outside the protected region, the obtained minimal exposure paths still follow Voronoi sides, which is consistent with the conclusions from previous studies.1,14,15
Algorithm convergence speed
Due to space limitations, only the convergence performance of Scenario 4 is presented. The curves in Figure 10 represent the changing relationship between the optimal fitness value and the generation number that corresponds to Scenario 4. The curves decrease rapidly and converge to a stable state, which demonstrates that the designed algorithm rapidly converges to the global optimal solution and is highly efficient.

Relationship between the optimal fitness value and evolution generation number. The horizontal axis is the generation number, and the vertical axis is the fitness value.
Conclusion
The original minimal exposure path problem considers a path from a fixed starting point to a fixed end point with no intermediate constraints. This article discusses the minimal exposure path problem with constraint conditions that arise from restrictions from the conditions (such as high temperatures, harsh environments, or sensitive or dangerous regions) that prevent the deployment of sensors in some inaccessible regions; thus, the sensor nodes can only be deployed in the areas surrounding these regions. The moving target departs from a fixed starting point, and when it encounters a sensitive region, it can only move along the boundary of the region. The target then reaches the fixed end point. The problem proposed and discussed in this article is a variant and extension of the original minimal exposure path problem. By considering the ineffectiveness of the original methods, this article abstracts the proposed problem into an optimization model. Despite the difficulty in solving the problem, which has a high model dimensionality and is highly nonlinear, the designed hybrid genetic algorithm can effectively obtain solutions. The minimal exposure path problem with constraint conditions uses isomorphic nodes. The MEP-CC problem proposed in this article is only related to one special restricted region in the monitor area. When there are multiple special regions in the monitor area, it indeed become more complex as the visited order of these regions must be considered. But it can be researched from the problem introduced in our article. When the number of these special regions is less (for example, there are two special regions), we can modify equation (7) twice again to solve the proposed problem. It will be our further work in the future when the number of the special regions is more. Future studies will also investigate methods of solving problems with anisotropic node arrangements with different sensor types and distances between sensors as well as problems that involve the redeployment of nodes to improve the coverage quality based on the obtained minimal exposure path while considering the cost of the nodes and their isotropic or anisotropic characteristics.
Footnotes
Acknowledgements
The authors would like to thank the (associate) editors and reviewers for their valuable and constructive comments and suggestions for improving this article. L.L. and M.Y. contributed equally to this work.
Academic Editor: Tiziana Calamoneri
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research work obtained the subsidization of National Natural Science Foundation of China (Nos. 61363070, 61163058, and 61662018), Guangxi Key Laboratory of Automatic Detecting Technology and Instruments (No. YQ16205), the General Programs of the Scientific Research Project of Guangxi Educational Committee (No. YB2014148), Guangxi Colleges and Universities Key Laboratory of Cloud Computing and Complex Systems (No. 2015209), and Guangxi University Key Laboratory Fund of Embedded Technology and Intelligent Information Processing (Guilin University of Technology) under grant no. 2016-01-06.