Abstract
The Internet of Things has emerged as a wonder-solution to numerous problems in our everyday lives, such as smart homes and intelligent transportation. As an extension of the IoTs, the Internet of Vehicles (IoVs) also requires increasingly high security and timeliness. This article proposes a vehicle-assisted batch verification (VABV) system for IoV, in which some vehicles called auxiliary authentication terminal (AAT) are selected to assist the roadside unit for Basic Safety Message (BSM) verification. As a measure to enhance the timeliness performance for system dependability, comprehensive AAT selection strategies are designed. To overcome the security weaknesses of VABV system, a Sybil detection scheme based on Extreme Learning Machine is developed. For the evaluation of VABV system, the quantified Age of Information (AoI) is used as an integrated timeliness and security indicator. The proposed AoI indicator synthesizes the effects of BSM verification, re-verification for failure of some AATs, Sybil attack, and Sybil detection scheme. As illustrated by the simulation results, by employing AoI as a performance evaluation indicator, we can better and more intuitively design an AAT optimal selection strategy based on changes in AoI. Simultaneously, the performance of the proposed Sybil detection scheme can be evaluated more intuitively and effectively under different IoV scenarios based on AoI.
Introduction
The advance of IoT technology and the concept of smart cities facilitate the emergence of Internet of Vehicle (IoV). As the automobile industry and transportation network grow rapidly, vehicles provide us with increased conveniences. Nevertheless, our growing demand for a variety of vehicles leads to an increase in traffic accidents and congestion. 1 As a burgeoning paradigm, IoV is the combination of Vehicular Ad Hoc Networks (VANETs) and IoT. 2 Unlike VANETs, IoV utilizes a variety of technologies to enhance the network’s properties, including machine learning, cloud computing, and behavior detection.
In order to coordinate the traffic flow effectively, the vehicles on the roads need to exchange messages with each other with on-board units (OBUs) mounted. The OBUs also enable vehicles to communicate with the roadside unit (RSU) nearby. In the IoV, messages can be approximately categorized into two types: safety-related messages and value-added messages with the Basic Safety Message (BSM) being the most significant one. 3 Typically known as heartbeat messages, the BSMs are proposed as the primary message set used by connected vehicle safety applications to constantly exchange data within the IoV network. Using real-time exchange of BSMs, safety applications are capable of detecting and identifying any potential hazards before they occur and can then alert drivers or begin vehicle control systems to respond to the situation. In addition, the BSM becomes obsolete as soon as it is used and is disposed of. 4 It is essential to note that BSMs contain much vital information such as the real-time velocity, location, and acceleration of the vehicle and are transmitted via the wireless channel in an open environment, therefore prone to several security threats. 5 This will jeopardize the benefits of such a message-exchange based system and may cause more chaos in traffic. Consequently, in addition to verifying the entities (i.e. vehicles or RSUs) that enter the IoV, the messages (i.e. BSM) must also be verified by the potential receivers in order to prevent attacks by impersonation, tampering, and so on. 6
In light of the above consideration, numerous researchers propose a variety of security schemes for entities and messages in IoV. The schemes for entities guarantee that entities in the IoV are legitimate,7–9 while schemes for messages ensure the integrity of messages10–12 with batch verification method adopted to improve the efficiency of verification. Specifically for message verification scheme, some ordinary vehicles are selected to help the RSU with message verification13–15 to alleviate the computational pressure of RSUs. Throughout their previous works, they propose improved security mechanisms and either illustrate that their proposed mechanisms are low in overhead through comparison with other works or demonstrate that the security mechanisms are robust against cyber attacks through formal or informal security analysis. Nevertheless, formal and informal security analysis have the disadvantage of not being able to visualize the performance against cyber attacks of IoV. Furthermore, and most importantly, the aforementioned works all analyze IoVs in a qualitative manner instead of evaluating them in a unified manner. The ultimate goal of an IoV system deployment is to be able to provide satisfactory services to the users who are in it. In other words, vehicle users are not concerned with network latency, throughput, and packet loss of the current IoV system, which are the focus of much of current research.14,16,17 What they care is whether the information they need to receive will arrive on time and be of high quality. In fact, in the current research on urban transportation systems, the question of whether a system can actually provide a satisfactory service to its users is increasingly being raised by researchers. Based on the concept of satisfying user needs, and in order to evaluate the performance of each subsystem of IoVs more comprehensively, various models are proposed to define “Everything as a service (XaaS).” Using this model, an evaluation system that evaluates many systems can bring together a comprehensive concept of the service content of each subsystem, including discussions of products, processes, data & information management, and security as a service. 18 Specifically, an IoV metric is anticipated that can be used to assess its performance in all aspects, particularly its timeliness and security to ensure that the system is able to meet the maximum possible user demand for the service.
In recent years, some works introduce the concept of dependability to IoT. The original concept of dependability can be briefly described as the capability of a system to provide users with trusted, reasonable, reliable, and correct services, or, in other words, the ability to ensure continuous and uninterrupted provision of critical services. 19 In Junior and Kamienski, 20 it is attributed by the authors that the two terms Dependability and Trustworthiness refer to the same concept that explains that the trustworthiness of IoT systems is largely determined by their ability to adapt and respond to what vulnerability flaws are present during their operational cycles. Based on a brief review of the current state of research, it can be concluded that the term Dependability is often restricted to the study of security performance in dealing with malicious network attacks under IoV scenarios.21–23 It should also be noted that some studies on improving IoV trustworthiness confuse this concept with trust, by studying the trust value management of vehicles and only examining the reputation of each node in the IoV. In these works, reputation, through the acquisition, updating, and sharing of trust value, enables vehicles to evaluate each other’s behavior and determine whether the other vehicle is malicious or has decreased reputation value as a result of malicious behaviors, and therefore cannot be trusted by other vehicles.24–27
In our view, there are few description and studies of the real sense of dependability of IoV for urban transportation, and there is an absence of study of multiple quality requirements for data and information of IoV for vehicle users, not to mention the definition and quantification methods for dependability of the system as a whole. Similarly, we introduce the concept of dependability in our study of IoV networks. And in order to evaluate the IoV system from the perspective of dependability, it is therefore important for the proposed IoV system to satisfy the user’s demand for quality of service, since it is an important medium for the BSM interaction between users of vehicles, when it comes to ensuring that the data quality of the BSM after transmission is up to user’s expectations. From the perspective of the users, we then propose the concept of MIaaS (Message Interaction as a Service), based on the XaaS model, for evaluating dependable IoV systems, that is, evaluating whether the IoV system can provide the service to meet the users’ demands in terms of BSM interaction among vehicle users. Beyond that, inspired by Wang et al., 28 using the Age of Information, the IoV system is analyzed quantitatively, allowing the system dependability to be uniformly described from the perspective of vehicle users.
The biggest difference of our work with existing related work is that we perform a true dependability analysis of IoV and analyze its properties from the perspective of vehicle users. We pay more attention to the quality of BSM that vehicle users will receive instead of merely considering the possible threats that IoV may face. The proposed IoV system is evaluated with an unified indicator named Age of Information (AoI), which identifies the freshness of BSMs clearly.
Contributions
In this article, our contributions are fourfold.
We analyze the shortcomings of the existing IoV research, and the concept of dependability is creatively introduced to unify the evaluation of IoV performance. A vehicle-assisted batch verification (VABV) system based on BSM interaction is proposed, and its dependability is discussed in terms of its system framework and the security basis for message signatures.
In order to reduce the VABV system verification latency, we proposed a more comprehensive selection strategy for choosing vehicles that will serve as auxiliary authentication terminal (AAT). By taking data loss into consideration when assigning vehicles as BSM verifier, the distribution of AATs is utilized for optimal AAT selection strategy.
Considering the possible security threats that may still exist in the VABV system, the Sybil detection scheme is proposed to enhance the security of the system. The machine learning method Extreme Learning Machine (ELM) is adopted to achieve fast detection. We utilize edge servers embedded in IoV to collect information from BSMs in vehicles and extract the characteristics of vehicle mobility patterns, which will then be used to detect Sybil nodes. The Sybil detection scheme includes BSM collection, BSM data preprocessing and Sybil detection.
The quantified AoI is adopted as the integrated performance indicator, which takes into account both the timeliness and security of the VABV system. Through AoI, the evaluation of the dependability of VABV system can be made more intuitive, and the coordination of VABV system can be improved through the inspection of AoI of VABV system.
Organization
The remainder of this article is structured as follows. Section “Designed VABV system and corresponding dependability requirements” introduces the security fundamentals and VABV system model, also the corresponding dependability requirements are described. In section “Comprehensive AAT selection strategies for VABV system,” the selection strategies for timeliness of BSM verification are depicted in details. The scheme against BSM generated by Sybil nodes is described in section “Detection scheme against Sybil attacks for VABV system.” Section “Usage of AoI as the integrated indicator for VABV system” describes the novel system evaluation indicator AoI and analysis of dependability for VABV system using AoI. Section “Simulation and discussions” showcases the simulation results and discussions, followed by the conclusion of this article in section “Conclusion and future work.”
Designed VABV system and corresponding dependability requirements
The system structure under discussion is initially illustrated in this section. More crucially, the framework is used to explain the VABV system’s dependability requirements. The examination of the security basics on which the VABV system is built follows. The latency model for BSM verification is then provided within the system model. Table 1 lists the notations that are utilized.
Notations and corresponding definitions.

PID: pseudo-identity.
System model and dependability requirements
System model
The framework of VABV system is depicted in Figure 1. It can be seen that the VABV system consists of three parts: Trusted Authority (TA), Roadside Unit (RSU), and vehicles. Vehicles can be divided into auxiliary authentication terminals (AATs) and ordinary terminals (OTs).

VABV system model.
Vehicles interact with each other in a VABV system via a BSM to implement applications such as collision avoidance and path planning. Before a vehicle sends a BSM, a cryptography-based signature of the BSM needs to be generated for ensuring the authenticity of the BSM. TA is regulated by government departments and is absolutely credible. It is responsible for the issue of system parameters in the Initialization phase before the whole system runs. At the start of the system, all vehicles in the network are ordinary terminals. After the AAT selection, some of OTs are selected as AATs and such vehicles are used to help the RSU in completing the BSM verification. RSU is established alongside the road or the intersection of roads. It is responsible for the selection of AATs, BSM verification, and validation of confirmation messages sent by the AATs. In the VABV system, the BSM of vehicles not verified by AATs will still be verified by RSU. Simultaneously, via a wired secure communication channel with the TA, the RSU receives system parameters from the TA and distributes them to all vehicles within its coverage area for generation of BSM signatures by the vehicles. The edge server connected to it is responsible for the Sybil detection. It first generates the corresponding steering state transition matrix (SSTM) of each vehicle through BSMs collected by RSU from the vehicles within the coverage of RSU. The driving characteristics of each vehicle are captured by the eigenvalues of SSTM. And based on the dissimilarity of driving features of benign vehicles and Sybil nodes, machine learning algorithms are used to identify Sybil nodes.
Dependability requirements
Based on the proposed VABV system, as the quality of BSMs has a great deal of influence on the functionality of this system, it is of critical importance to evaluate it in terms of BSM. In light of the characteristics necessary to initiate and function a VABV system smoothly and effectively, the dependability requirements for a VABV system can be summarized as follows:
ECC-based batch verification
Based on the system’s requirements for timeliness and information security, a cryptography algorithm needs to be chosen that are suitable to our system. The selection of the encryption algorithm must take into account not only the security strength of the algorithm but also the calculation time overhead which has to be minimized for message encryption and verification. Rivest-Shamir-Adleman (RSA), ECC, bilinear mapping, and so on are the most commonly used encryption algorithms on the IoVs. With respect to the RSA algorithm, 160-bit ECC and 1024-bit RSA have the same level of security; however, 160-bit ECC signatures and decryptions are considerably faster than RSA. 29 The cost of bilinear pairing operations and scalar multiplication operations is much higher than the cost of the scalar multiplicative calculations performed by ECC. 30 In addition, in some previous works, the Map to Point Hash function is used, which also evidently increases computation delay. 31 The upper part of Figure 2 illustrates how a high computational overhead encryption algorithm can result in multiple BSMs not being verified until after the expiration date has passed, resulting in their discard. Overall, the use of ECC as a secure foundation for our work can be more effective in meeting the system’s needs for timeliness. All the messages must be encrypted with ECC and the RSU and AATs should verify these message signatures. In order to confirm the validity of multiple BSM signatures at the same time, we adopt the batch verification method based on ECC. The security process is briefly described as follows.

Batch verification and re-verification process for BSMs with specific valid time.
Elliptic curve cryptography
An elliptic curve
Definition 1
(ECDLP, Elliptic Curve Discrete Logarithm Problem). For a random number
Initialization
The TA sets up the system and generates the system parameters based on ECC encryption as
The generation of vehicles’ pseudo-identity and message signature
When the vehicle constructs a message, it must sign it before sending it to ensure the authenticity. The TPD of the vehicle randomly chooses
The batch verification performed by RSU and AAT
After receiving

The establishment of the Eq. (1) indicates that no message is tampered with in the batch. The correctness of the above batch verification is given as follows

Regarding the characteristics of batch verification as shown in the lower part of Figure 2, when there is at least one invalid signature in the batch (either tampered with or sent by a malicious vehicle itself), the verification of this batch will not pass and the invalid signature needs to be found with re-batch verification applied and then discarded. In this work, since the main type of attack we consider is the more threatening attack, in order to simplify the model, the case where the batch is re-verified because it contains invalid signatures inside is not considered for now.
Latency model
On the basis of aforementioned system model, the corresponding latency model is shown in Figure 3.

Latency model for BSM verification of VABV system.
According to Figure 3, the system verification latency consists of two parts: one is the latency on the verification by RSU and AAT and we record them as

The two parts of the latency model are described as follows:
Latency from the RSU
The latency induced by the RSU consists of two parts: one latency

where

In order to validate confirmation messages from AATs, batch verification is conducted. Let the total number of AAT to be M, then

Latency from the AAT
For the AAT, the latency consists of three parts. The first one is
For the verification latency of BSMs on AAT, the batch verification is also used. Let the batch size that the

where
For the transmission latency induced by the sending of confirmation messages from the AAT to the RSU, the data transmission rate is set as
To sum up, the latency on the AAT is

In the subsequent analysis and calculation, the transmission latency
Comprehensive AAT selection strategies for VABV system
In this section, the proposed AAT selection strategies are described. BSM interaction is improved by selecting a certain number of vehicles as AATs before the BSM verification process begins. The whole process of AAT selection is depicted in Figure 4.

AAT selection process.
Initial determination of the number of AATs
When the RSU needs auxiliary vehicles for message verification, the first step is to determine how many vehicles are required. To achieving this, enlightened by Wu et al.,
14
where in an ideal IoV, all the ordinary vehicles have the same computing power for verification, the computing power of the ordinary nodes can be calculated by



In an ideal IoV, the number of ordinary terminals verified by each AAT is the same. Eq. (9) indicates that the sum of the number of ordinary terminals verified by all AATs and the number of ordinary terminals verified by RSU is equal to the sum of all ordinary terminals in the system. Eq. (10) represents the condition that minimizes the total system verification latency. The goal of minimizing the total verification latency of the ideal IoV is described in Eq. (11). From the above, we can calculate out the estimated initial number of AAT
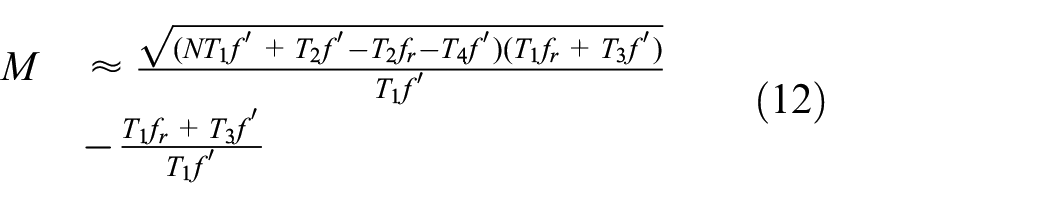
The batch size of each ordinary terminal in this ideal IoV is

Each AAT verifies the same number of signatures according to this value and the batch size remains unchanged once the number of ordinary vehicles is determined.
Ordinary terminal evaluation
It is expected that the verification latency of the system will be as low as possible, as well as that the communication between AATs and RSUs will become stable in order to reduce the likelihood of re-verification. 15 Therefore, distance and computing power of each vehicle should be assessed. However, these two factors may not be satisfied simultaneously. For instance, there may exist some vehicles with a short distance to RSU but has a poor computing power for verification, which may be not suitable to be AATs. Therefore, we need to evaluate all the vehicles in the IoV in an integrated way.
To evaluate each ordinary vehicles more precisely, we fuzz these two factors. The RSU can calculate the distance between itself and the vehicles with the aid of GPS. Let
Next the computing power of each vehicle is described by calculating
By the time RSU calculates these two evaluation indicators for all vehicles in its vicinity, it will record and score them as shown in Table 2. On the basis of the vehicle’s current condition, we can assign each vehicle within the system a score indicating its priority to be selected as an AAT.
The evaluation of vehicles.
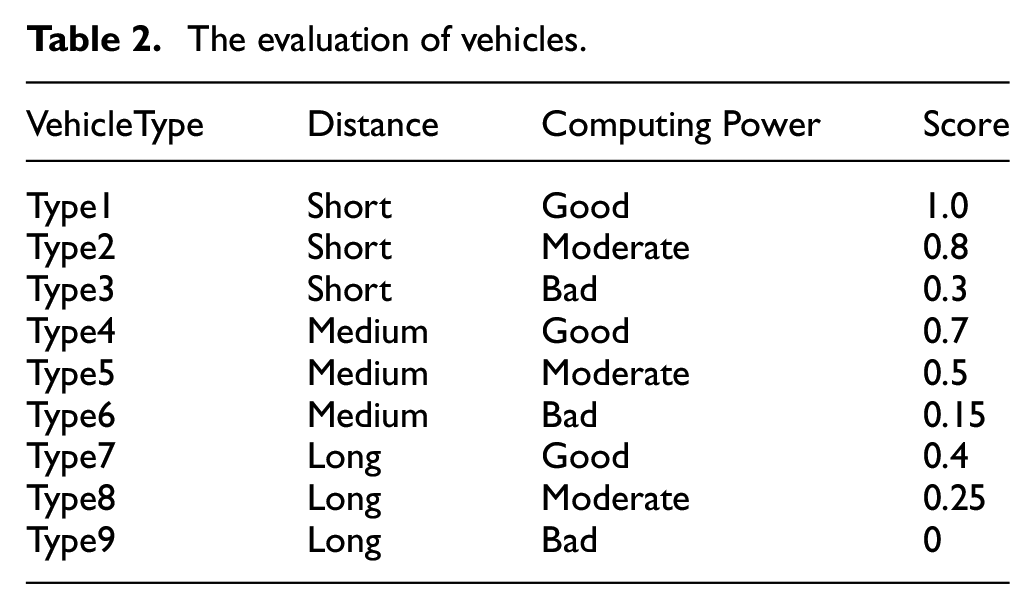
We use a scoring criterion for the determination of the priority. The distance judgment (Short, Medium, Long) is scored (1,0.5,0) correspondingly, while the property judgment (Good, Moderate,Bad) is scored (1,0.5,0). Then the score for each vehicle

where
Distribution of AATs
During the verification cycle, if the communication overlap area between the assigned AATs is too large, a large number of redundant verification will be introduced (i.e. an OT verified by one AAT will also be verified by another AAT). The number of OTs verified by the RSU in this case rises, which in turn affects the total verification latency of the system. If the communication overlap area between assigned AATs is small, some assigned AATs may be located far from the RSU, resulting in poor communication quality with the RSU and introducing re-verification problems, which also introduces additional latency. Therefore, when selecting AATs, besides considering the performance of the vehicle itself, the distribution of AATs also needs to be considered.
Regarding this, we consider the model where a RSU is at the intersection and its communication range is
Network coverage indice
A probability associated with the grid point

where

In this case, the network coverage index
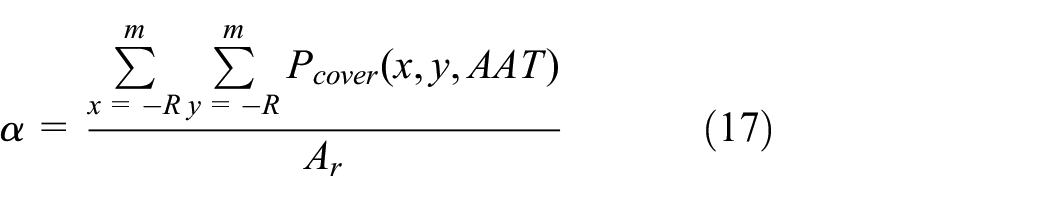
where
Network redundant indice
We calculate the probability of a grid point

where the

For simplicity of calculation, we convert the highest coverage rate to the lowest uncovered rate, so that when the RSU chooses the AAT among ordinary vehicles, the following value is used which we call the distribution index

where
Detection scheme against Sybil attacks for VABV system
To enhance the security of the VABV system, in this section we analyze the security risks that may be present and propose a detection scheme that uses information contained within the BSM to detect abnormal nodes.
Vulnerability analysis
Sybil security threat in vehicular networks has attracted much attention in recent times. 33 The proposed system is equally vulnerable to such attacks. In Figure 5, the Sybil attack that may exist in VABV system is shown.
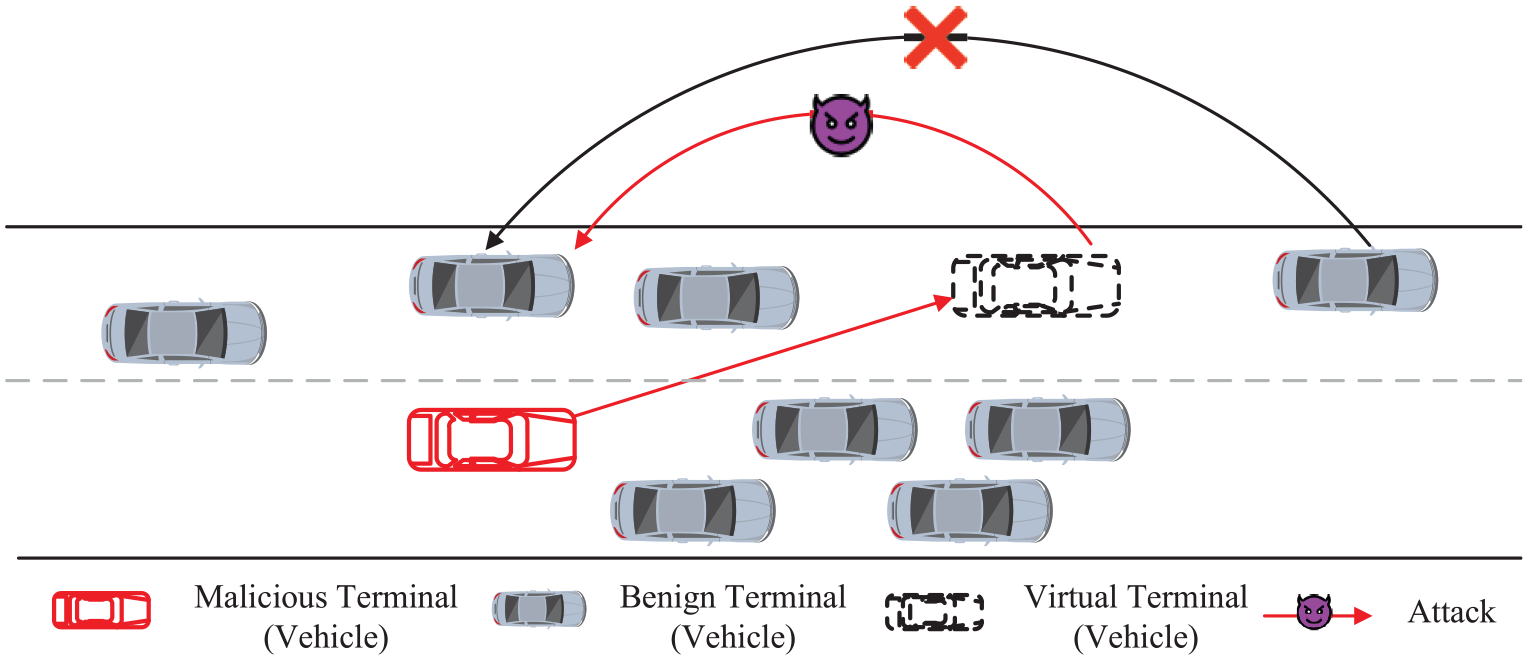
Influence of Sybil attack.
In VABV system, each vehicle is equipped with a TPD storing system parameters. Vehicles periodically broadcast signed BSMs. In order to guarantee the users’ privacy, each vehicle has two pseudonyms
To achieve the purpose of launching Sybil attacks successfully, malicious vehicles must calculate the ideal idle space on the road for virtual nodes generation. Due to the virtual nature of Sybil nodes, if they claim a geographic position occupied by an existing physical vehicle, they will be easily detected by other benign vehicles and the attack will not succeed. In addition, malicious vehicles must modify the BSMs that virtual nodes broadcast in order to make them more reasonable.
According to the above analysis, the attacking tricks used by malicious vehicles will be upon the BSMs from benign vehicles. Malicious vehicles will fabricate some unreal BSMs according to the BSMs from its neighbors.
Attack detection
In Gu et al., 34 a support vector machine (SVM)-based Sybil detection scheme is proposed, where the detection rate is relatively high; however, it suffers from high complexity. In addition, the accuracy of such a shallow learner is heavily dependent on feature extraction. 35 If the extracted features cannot effectively show the differences between vehicles well, the detection accuracy will likely be greatly reduced. In vehicular networks, due to the large amount of BSMs, detection scheme with relatively low complexity is needed. 36 To explore the potential of machine learning in this study and overcome the problems such as high complexity that will happen in traditional BP networks, the ELM is adopted. 37 The whole process of proposed Sybil detection scheme is shown in Figure 6. Since the purpose of virtual vehicles is to eliminate the safety of other benign vehicles, the steering states of benign and virtual vehicles should differ, which may not be judged intuitively. Hence, the detection of Sybil nodes can be equivalent to the measurement of difference of steering state.

Process of Sybil detection.
Vehicle steering state description
In order to describe in great detail the transition of steering state of vehicles, a matrix should be used. A matrix is defined as a set of data indicative of the movement of the vehicle in a given period of time. According to the contents in BSM, the steering state transition matrix (SSTM) of vehicles from the time
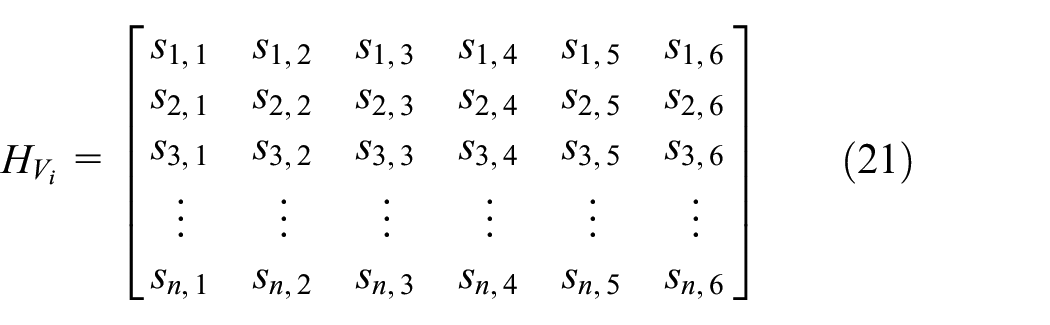
The above specific matrix
Vehicle steering state transition matrix preprocessing
From the formulation of SSTM, we can see that it is not suitable for direct analysis since the SSTM of each vehicle varies and the characteristic of them are not obvious at this dimension. Hence, the SSTM should be processed under dimension reduction by the calculation of each SSTM

For each SSTM
Next, the eigenvalues of
Also, it is of necessity to select out some eigenvalues that well depict the mobility characteristic of a vehicle, the suitability of which can be represented by the Energy (E) of the eigenvalues. A total Energy higher than 90% is considered suitable. 38 Hence, for each SSTM, once its eigenvalues are calculated out, Algorithm 1 traverses all its eigenvalues to fine the best eigenvalues, which are prepared for the subsequent Sybil detection.
Sybil node detection
The core of Sybil detection is ELM. An ELM network is characterized by a combination of random parameters set for hidden nodes of the Generalized Single-Hidden Layer Feedforward Networks (SLFNs). Using Moore-Penrose generalized inverse matrix, the output weights can then be determined analytically. It can be seen that the iteration is not needed in ELM, thus greatly reducing the time needed for model training.
The contents contained in the RSU from all the vehicles are collected, and the SSTM
Assuming that there are

where

The vector
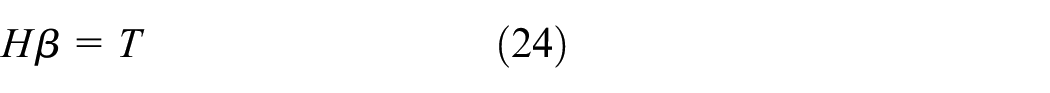
where
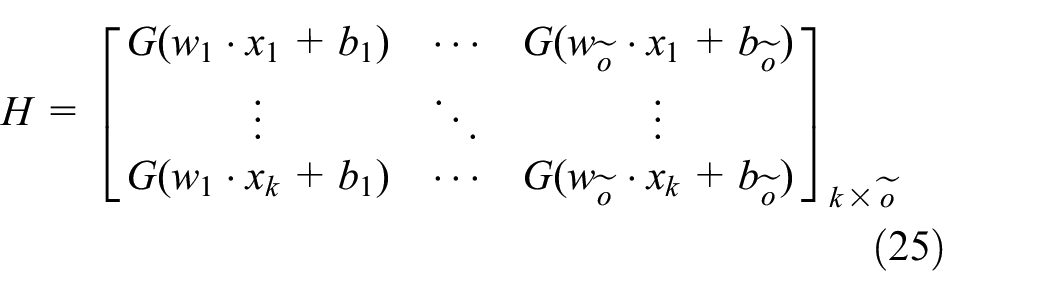
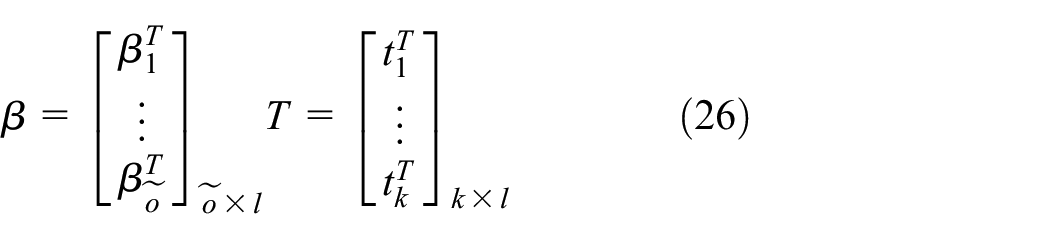
Hence, the ELM training process is described as follows:
Choose activation function
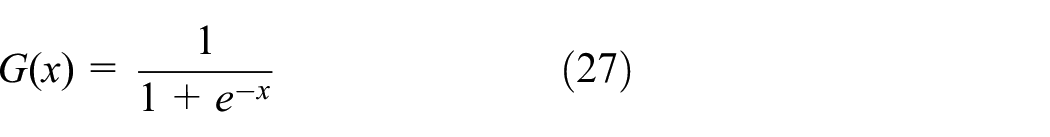
Given training data
Calculate the output matrix
Determine the output weight vector

where
Usage of AoI as the integrated indicator for VABV system
In VABV systems, the periodic transmissions of BSMs from vehicles are closely related to the system’s dependability. The large BSM verification latency and hazardous attacks can cause havoc in the VABV system. Indicators of IoV traditionally used to evaluate IoV are not appropriate for evaluating timeliness and security performance synthetically. Therefore, the concept of the AoI is proposed to be used as a key indicator for VABV systems in order to quantify the dependability.
The analysis of AoI as indicator for evaluation of timeliness and security
According to the aforementioned analysis of dependability requirements of VABV system, the AoI is adopted to quantify the dependability of VABV system.
First introduced into the area of research for vehicular networks in Kaul et al.,
39
AoI is used to quantify the freshness of information at a destination node (i.e. a receiver vehicle) generated by the source node (i.e. a sender vehicle). To describe it in a more formal way, AoI in IoV networks can be defined as the time elapsed since the last successfully received BSM at the side of receiver vehicle which is generated at the sender vehicle.
40
Even if a fabricated BSM is received, the safety-related application cannot generate correct driving decision according to the contents in it. Hence, it cannot be considered a successfully reception of BSM. Any disturbance happens in VABV system will be reflected by the AoI. Hence, through AoI, we can better analyze the VABV system from the perspective of IoV users. For better understanding the AoI, Figure 7 illustrates a formation of AoI, denoted by

Evolution of AoI at the side of receiver vehicle r according to the BSMs received from sender vehicle s. The sending time and receiving time of BSMs in i-th verification period are denoted as
As depicted in Figure 7, the curve of

Note that from the definition of AoI, the lower the value of AoI, the fresher the information. Also, the sending time of BSM makes no sense to the AoI. It is also noteworthy that
For the convenience of quantification, the area under the envelope of AoI is calculated. And in order to calculate in an easier way, the area of envelope curved by the AoI is divided into three parts: a polygon area

The broadcast interval of BSM is given by

Using Eq. (31) and Eq. (32), the average AoI between the sender vehicle s and receiver vehicle r can be calculated by

Considering that for a specific receiver vehicle r, it has

Eventually, the VABV system average AoI with N vehicles can be calculated as

In VABV system,

In a verification period, the peak AoI represents the time when the dependability of the VABV system is at its worse. The analysis of peak AoI can provide timely information about the effect some disturbances have on the VABV system.
The performance of AoI indicator on timeliness
The first issue that influences AoI is necessary BSM verification latency. In the above analysis of AoI, it is easily concluded that the value

It is easy to find that the number and computing power of AATs influence the performance of AoI in each BSM verification cycle, which is closely related to the AAT selecting strategies.
Another issue that influence AoI is data loss. To make the verification system function better, the success of confirmation messages delivered to the RSU should be guaranteed. To achieve this, the distance of AATs to the RSU is considered, which can be reflected by the distribution of AATs. In Cui et al.,
15
the authors think that the relatively short distance from the AAT to the RSU will provide a more reliable communication. Since the longer the distance between the AAT and the RSU is, the more path loss (PL) will be generated, which will affect the communication quality between them as well as the possibility of data loss. Hence, by the time some vehicles have been assigned to be AATs, the transmitting power

where
The estimation value of receiving power for each
If a confirmation message failure is reported on an AAT during each BSM verification cycle, the vehicles near that AAT that fails to deliver the confirmation message will be evaluated by the RSU and selected to complete the BSM verification for that BSM cycle in its place and to resend the confirmation message. Then the value

where
From the above analysis, we can infer that both verification for BSM and data loss ratio influence the performance of AoI by the variation of
To sum up, the AoI performance with respect to the BSM verification in VABV system is
where then token
The performance of AoI indicator on information security
In the first part of this section, we can infer that the quantitative factors that affect the VABV system AoI include
AoI performance of VABV systems considering Sybil attacks
From the above analysis on Sybil attack that may happen in VABV system, we can infer that if a vehicle suffers a Sybil attack, the malicious node intercepts the BSM of the benign vehicle with which it would otherwise interact with a normal BSM, pretends to be real by forging a PID and furthermore fabricating a virtual node, and sends a fake BSM to it.
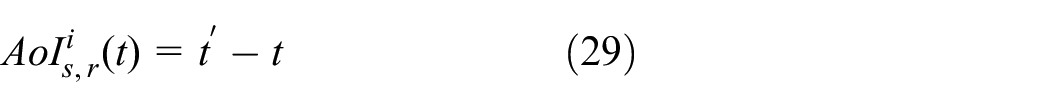
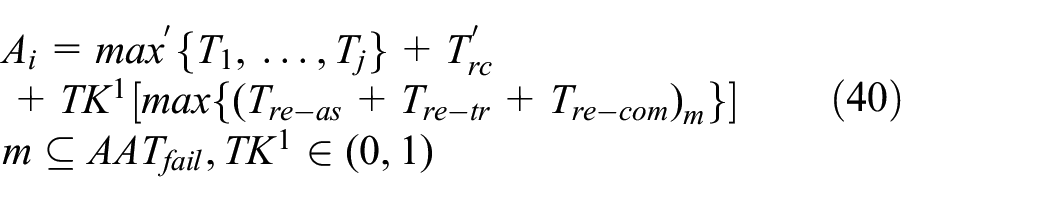
Unless the attacked vehicle is able to take security detection measures in time, it may not receive the correct BSM for several consecutive BSM verification cycles, which will result in an incorrect driving decision, which will pose a significant risk to road safety. In this case, the

where
Since the BSMs received when they are attacked by Sybil are spurious, it is meaningless to analyze

From the above analysis, it can be seen that if appropriate and efficient Sybil detection method is not adopted, the
AoI performance of VABV systems considering detection scheme against Sybil attacks
By using Sybil BSM detection based on machine learning, Sybil attacks can be effectively countered and thus the dependability of the VABV system can be improved. However, there is a certain error in identifying Sybil BSM, and the unnecessary processing latency brought by it will likewise have an impact on the system AoI. Therefore, we also need to make a dependability analysis of the VABV system that utilizes Sybil detection. A Sybil detection parameter
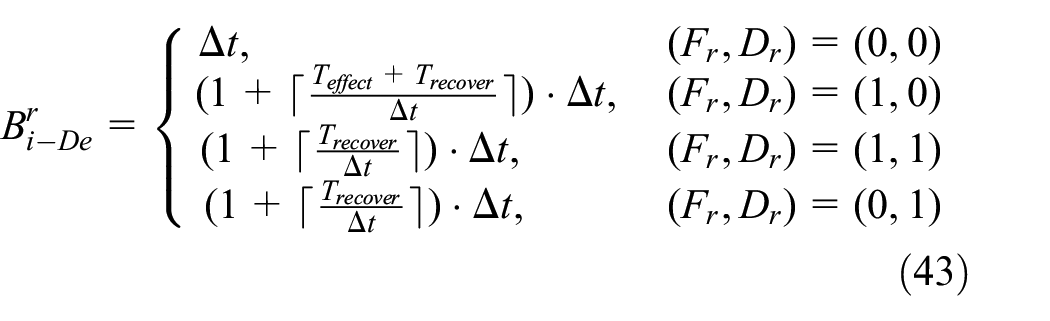
As described by the Eq. (43), based on the actual condition of the vehicle and the detection results, it can be divided into four scenarios, which correspond to the corresponding
After recovering from the attacks, for a receiver vehicle

where
From the perspective of information security, the Sybil attack detection latency and the accuracy of detection are the two most significant factors that impact the dependability of VABV systems.
Simulation and discussions
In this part, we analyze the AoI performance with respect to Timeliness and Information Security based on simulations.
Simulation scenario and parameters setting
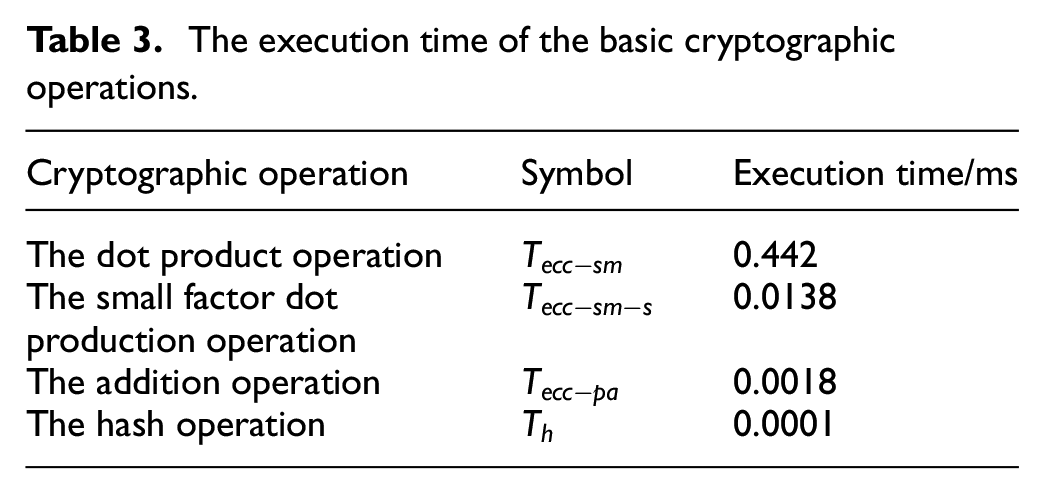
In order to evaluate the timeliness of the VABV system, the simulation is built on a scenario where the RSU is located at the junction. The coverage range of the RSU is set to a circular area with a radius of 1000 meters. We refer to Wu et al. 14 and get the execution time of the basic cryptographic operations shown in Table 3. As we describe in the section “Comprehensive AAT selection strategies for VABV system,” compared with RSUs, all ordinary vehicles will be classified into three categories with respect to their CPU frequency, that is, computing power. Assuming that the CPU frequency of RSU is 3 GHz, vehicles with CPU frequencies equal to, two-thirds of, and one-third of the computing power of RSU will be classified as Good, Moderate, and Bad, respectively. Therefore, in the simulated IoV, there are three kinds of ordinary vehicles with the computing power evaluated as Good, Moderate, Bad, and the computing power of them are set to 3 GHz, 2 GHz, and 1 GHz, respectively. In the IoV, 30% ordinary vehicles are with a computing power of 3 GHz, 40% of the ordinary vehicles are with a computing power of 2 GHz, and 30% of the ordinary vehicles are with a computing power of 1 GHz. The computing power of the RSU is set to 3 GHz and 2 GHz. Simulation of Urban MObility (SUMO) simulator is used to simulate traffic flows in an urban environment for the purpose of evaluating the information security of VABV system. In the simulation scenario, each Sybil attacker generates three Sybil nodes and sends BSMs in an attempt to launch attacks based on the traffic information it knows. The remaining simulation parameters used are listed in Table 4.
The execution time of the basic cryptographic operations.
Simulation parameters.

BSM: Basic Safety Message; RSU: roadside unit.
AoI performance of VABV system on timeliness
First, we analyze the relationship between the number of AATs and the system average AoI. As we analyze in section “Usage of AoI as the integrated indicator for VABV system,” the verification latency affects

System average AoI varies with the number of AATs when N = 50, 100, 200, respectively.
Then the improvement of VABV system average AoI compared to the RSU-only BSM verification system is depicted in Figure 9. The higher the percentage improvement, the better the optimization performance of VABV system. We can see from Figure 9 that comparing to the RSU-only BSM verification system, the average AoI performance of the VABV system has been improved for a certain number of terminals. However, the improvement percentage of system average AoI varies for different number of terminals. When the number of terminals is relatively small, the RSU is capable for BSM verification, thus being not put under stress for BSM verification. Consequently, the average system AoI improvement is not apparent compared to the RSU-only verification system. However, when the number of terminals is high, the average system AoI improvement becomes increasingly evident. When the total number of vehicles is 200, the maximum system average AoI improvement percentage is 47.4 % in comparison with the RSU-only verification system, showing that the VABV system has a more significant performance improvement than the RSU-only system when the number of terminals is large.

Average AoI improvement varies with the number of terminals in VABV system compared to the RSU-only BSM verification system.
Next, the system verification latency and the data loss, both of which effect the
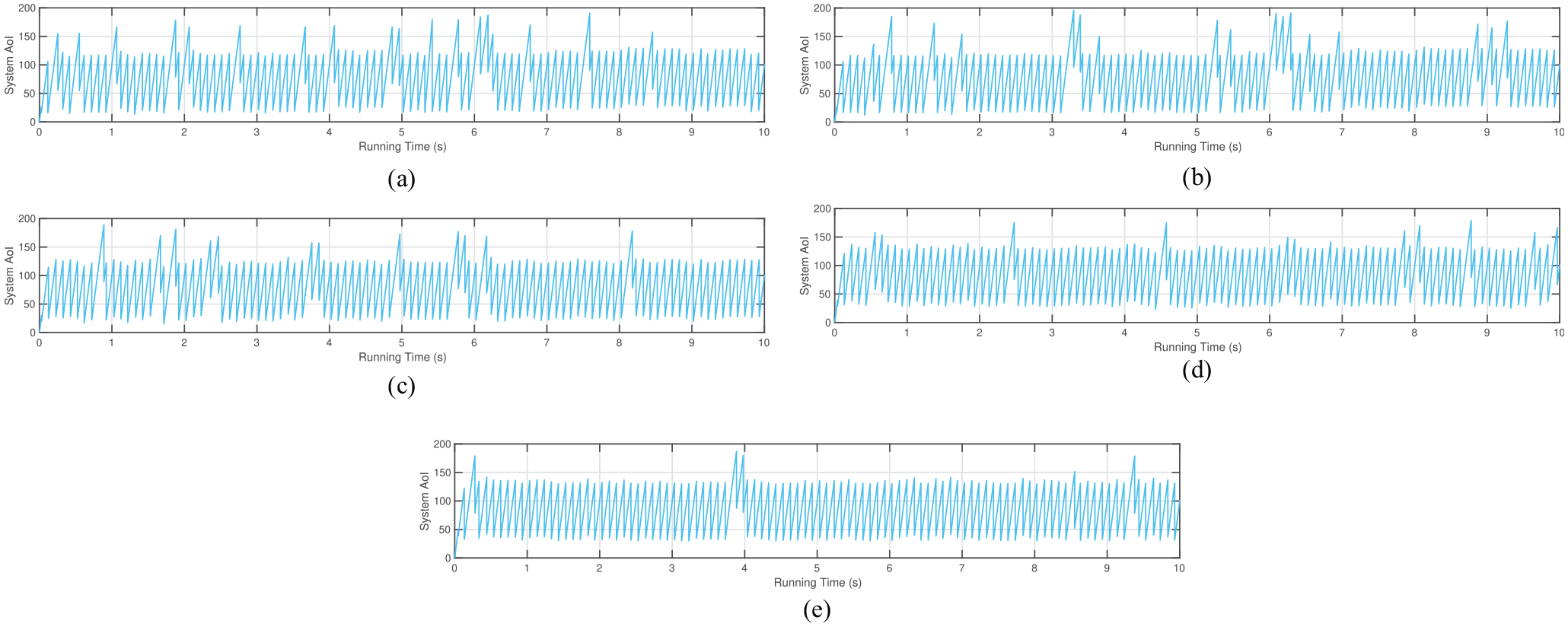
AoI of VABV system under different distribution index. (a) N = 50, M = 8, Distribution Index ξ = 0; (b) N = 50, M = 8, Distribution Index ξ = 0.2; (c) N = 50, M = 8, Distribution Index ξ = 0.4; (d) N = 50, M = 8, Distribution Index ξ = 0.6;(e) N = 50, M = 8, Distribution Index ξ = 0.6.
AoI performance of VABV system on information security
In this subsection, the BSM security reflecting on AoI variation is analyzed. The attackers randomly launches a total of 100 attacks in the simulation scenario. The performance of aforementioned Sybil detection scheme is analyzed. Figure 11 is the chosen simulation results of system AoI under different Sybil percentage under the simulated scenario from 0 s to 10 s and 40 s to 50 s. In light of the analyses in section “Usage of AoI as the integrated indicator for VABV system,” the

AoI of VABV system with Sybil detection scheme under different Sybil percentage. (a) N = 50, M = 8, Sybil Percentage = 2%; (b) N = 50, M = 8, Sybil Percentage = 6%; (c) N = 50, M = 8, Sybil Percentage = 10%.
As a way to analyze the Sybil detection scheme reflected by AoI curve, the number of peak AoI violation times under different proportions of Sybil nodes are quantitatively compared. The number of peak AoI violation times is calculated without taking into account the effects of BSM verification latency or re-verification by setting a peak AoI threshold of 400 and exceeding token of 1. When peak AoI in some verification cycles exceeds the preset threshold, the exceeding token will be set as 2. We can clearly figure out in Figure 12 the total number of peak AoI violation times under different proportions of Sybil nodes. During the operation time, with Sybil detection scheme, the number of peak AoI violation times are 32, 23, and 14 when the proportion of Sybil nodes are 2%, 6%, and 10%, respectively. The times at which the peak AoI violation occurs decrease as the proportion of Sybil nodes increases. This implies that the proposed Sybil detection scheme performs better in scenarios with a high proportion of Sybil nodes, and that further optimization is needed to enhance the scheme’s security performance in low-Sybil proportion scenarios.
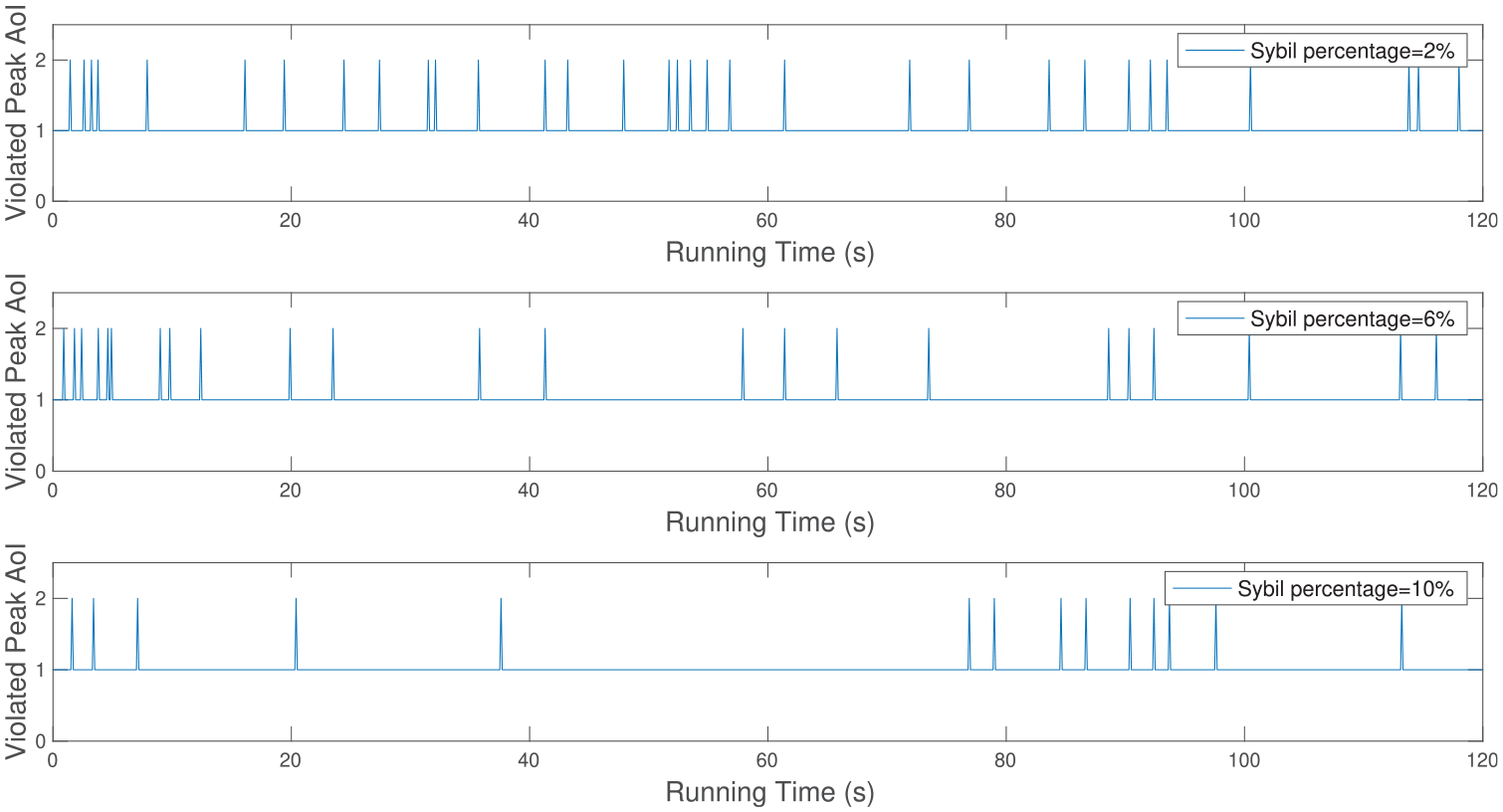
Times of violated peak AoI of VABV system under different Sybil percentage.
Conclusion and future work
In this article, we proposed a novel vehicle-assisted IoV in which some vehicles are assigned for BSM verification. By more comprehensive AAT selection strategy, the efficiency and VABV system can be enhanced. By using machine learning–based Sybil detection scheme, the security performance of VABV system can be further enhanced. The AoI was proposed as an indicator to evaluate the VABV system from the prospect of timeliness and information security in a unified and intuitive way. The system average AoI and peak AoI were used to synthetically evaluate the dependability of VABV system, through which optimal AAT selection strategy can be made and performance of proposed Sybil detection scheme can be intuitively tested. For future work, we will apply the proposed dependability analysis method to more complex scenarios in IoV and make modification and optimization to the Sybil detection scheme to fit proposed VABV system better.
Footnotes
Handling Editor: Peio Lopez Iturri
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported in part by the Fundamental Research Funds for the Central Universities under Grant 2021RC225, in part by the National Natural Science Foundation of China under Grants 62102019 and 61931001.
