Abstract
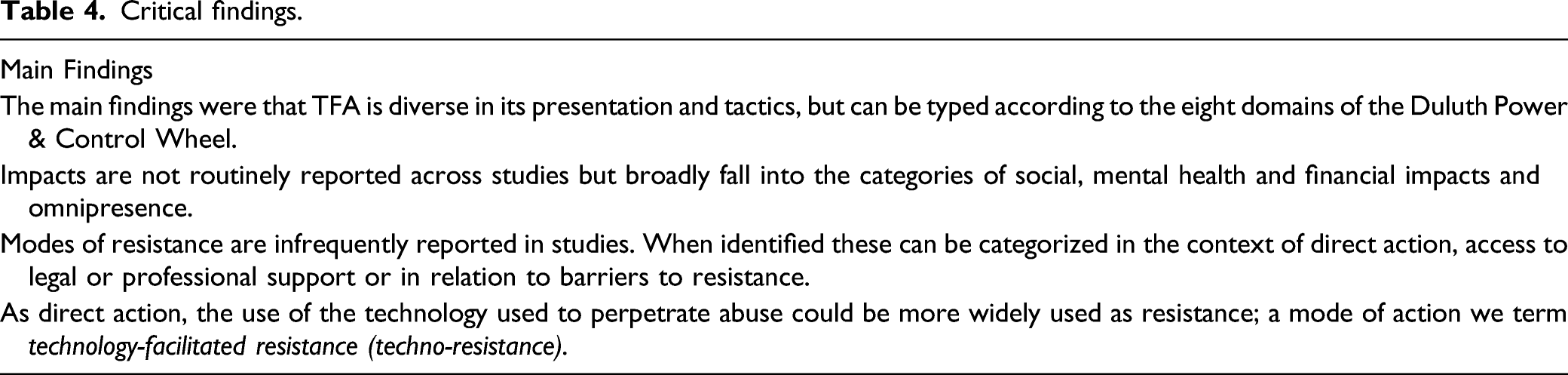
Technology-facilitated abuse (TFA) is a significant, harmful phenomenon and emerging trend in intimate partner violence. TFA encompasses a range of behaviours and is facilitated in online spaces (on social media and networking platforms) and through the misuse of everyday technology (e.g. mobile phone misuse, surveillance apps, spyware, surveillance via video cameras and so on). The body of work on TFA in intimate relationships is emerging, and so this scoping review set out to establish what types of abuse, impacts and forms of resistance are reported in current studies. The scoping review examined studies between 2000 and 2020 that focused on TFA within intimate partnerships (adults aged 18+) within the setting of any of these countries: the UK and Ireland, USA, Canada, New Zealand and Australia. The databases MEDLINE, CINAHL and Scopus were searched in December 2020. A total of 22 studies were included in the review. The main findings were that TFA is diverse in its presentation and tactics, but can be typed according to the eight domains of the Duluth Power & Control Wheel. Impacts are not routinely reported across studies but broadly fall into the categories of social, mental health and financial impacts and omnipresence. Similarly, modes of resistance are infrequently reported in studies. In the few studies that described victim/survivor resistance, this was in the context of direct action, access to legal or professional support or in the identification of barriers to resistance.
Introduction
Intimate partner violence (IPV) is recognized globally as a serious public health problem which occurs in all settings and among all socioeconomic, religious and cultural groups (World Health Organization (WHO), 2021). IPV includes a wide range of behaviours that can be enacted within an intimate relationship with partners of opposite, same or other gender across the lifecourse (Rogers, 2020). These behaviours include the following: physical abuse (e.g. slapping, punching, strangling, choking, burning, pinching and scratching); psychological abuse (e.g. belittling, criticisms, verbal assaults, shouting and name calling); sexual abuse (e.g. unwanted touching, sexual assault, rape, forced pornography use, forced sex work or sexual activity with others); and financial abuse (e.g. taking and controlling money, not allowing a victim to work or building up debts in their name) (WHO, 2021). IPV also includes coercive control which is a pattern of actions including humiliation, intimidation, isolation, stalking, punishments and restricting access to health care or education (Stark, 2007). Global estimates suggest that one in three women experience IPV in their lifetime (WHO, 2021). IPV can lead to significant harm with extensive consequences ranging from impacts to a person’s physical and mental health to economic, employment, social and behavioural effects and, in some cases, IPV can have a fatal outcome (WHO, 2021).
Briggs (2018) notes a growing trend in the use of digital and communications technology to control and abuse intimate partners. Examples include incessant texting or calling, use of surveillance apps, spyware or other tracking devices as well as the perpetration of abuse over social media and networking platforms. The so-called Internet of Things which includes smart home technology (such as home assistants and home thermostats) can also be used to harass and abuse (Tanczer, 2020). These practices are commonly referred to as technology-facilitated abuse (TFA). However, a diverse range of terminology and definitions are in operation across the literature, and Messing et al. (2020) argue that we need a clearer framework (including agreed definitions and measurements) to better understand TFA.
Notwithstanding this lack of an agreed framework, TFA has become more visible as the expansion of digital and communication technology has created an arena in which established forms of abuse, such as surveillance or harassment, are being more frequently reported in research. When enacted within the context of an intimate relationship, TFA is a subset of IPV. While TFA can be perpetrated by family members, strangers and acquaintances, this scoping review focuses on TFA perpetrated within the context of an intimate partnership when perpetrated by current or former partners.
The expansion of digital technology has created new possibilities, such as disrupting someone’s life through hacking into their home networks or covertly installing spyware in personal devices and domestic spaces. TFA transcends the boundaries of proximity and temporality which can impede abuse perpetrated in the physical world (in-person IPV) as abuse is carried out with greater ease in digital spaces (Woodlock, 2017). Importantly, victims/survivors can use technology to resist abuse. The purpose of this scoping review is, broadly, to establish what is known about TFA as well as the methods used by victims/survivors to resist it (Munn et al., 2018). Our focus on resistance differs from existing literature which mostly seeks to describe forms of TFA and its consequences (Afrouz, 2021).
Whilst there is a large body of evidence detailing IPV when enacted in-person, there is much less evidence that examines abuse that is facilitated virtually through technology. Scholarly concern about TFA has been building since 2002 in Australia, the USA and the UK (Laxton, 2014; Woodlock et al., 2020). Subsequently, studies on in-person abuse and TFA are drawing attention to ongoing changes in relationship practices as the co-occurrence of TFA and other behaviours are increasing (Duerksen & Woodin, 2019). For example, a study in Spain reported that 35.8% of female and 26.5% of male university students reported being a victim and a perpetrator of TFA at the same time (Villora et al., 2019). Briggs (2018) describes the use of technology as an emerging trend in IPV.
Due to the increased availability and development of both digital devices and technological capabilities, measuring prevalence is particularly challenging (Stonard, 2021). However, research on TFA prevalence describes it as widespread. For instance, a recent study conducted by the Economist Intelligence Unit (2021) of women (n = 4500), in 45 countries with the largest online populations, has shown that: 38% of women have personally experienced online violence; and 85% of women have witnessed online violence being perpetrated against another woman. A UK-based survey of victims/survivors (n = 307) found that 45% reported TFA during their relationship and 48% had experienced some form of TFA post-separation (Laxton et al., 2014). In the USA, Marganski and Melander (2018) found that 75% of 540 college students in their sample had experienced TFA perpetrated by a partner or former partner. Australian national research, undertaken by the eSafety Commissioner
Aim and Research Questions
The primary aim of the review is to identify and synthesize a broad, but not exhaustive, range of studies exploring TFA in intimate partner relationships and the methods used to resist such abuse. The scoping review questions are: 1. what is known about TFA in intimate relationships? and, 2. what methods are used to resist TFA by victims/survivors?
Method
Scoping reviews are a growing methodology (Pham et al., 2014) which are useful in addressing broad research questions and when mapping key concepts that are reported in or underpin a varied range of studies (Arksey & O’Malley, 2007). For this review, we adopted the PRISMA framework which is an established format for undertaking and reporting scoping reviews (Tricco et al., 2018). The protocol was developed by the research team and registered at the Open Science Framework on 20/11/2020 [ https://osf.io/t56my/].
Study Eligibility
The Inclusion Criteria were the following:
• Population: Victims/survivors of technology-facilitated abuse; adults aged 18+; • Concept: technology-facilitated abuse when perpetrated within the context of an intimate relationship; • Context: UK or countries with some shared cultural background – the UK and Ireland, USA, Canada, New Zealand and Australia; • Type of sources: primary research and case studies published in peer-reviewed journals; • English language only; translation resources were not available for this project; • Date: From 2000 to the search dates in December 2020.
Studies were excluded if it was not clear that the perpetration of TFA was in the context of a current or former intimate relationship. They were also excluded if samples included a majority of victims/survivors under 18 years.
Study Selection and Data Extraction
Search terms.
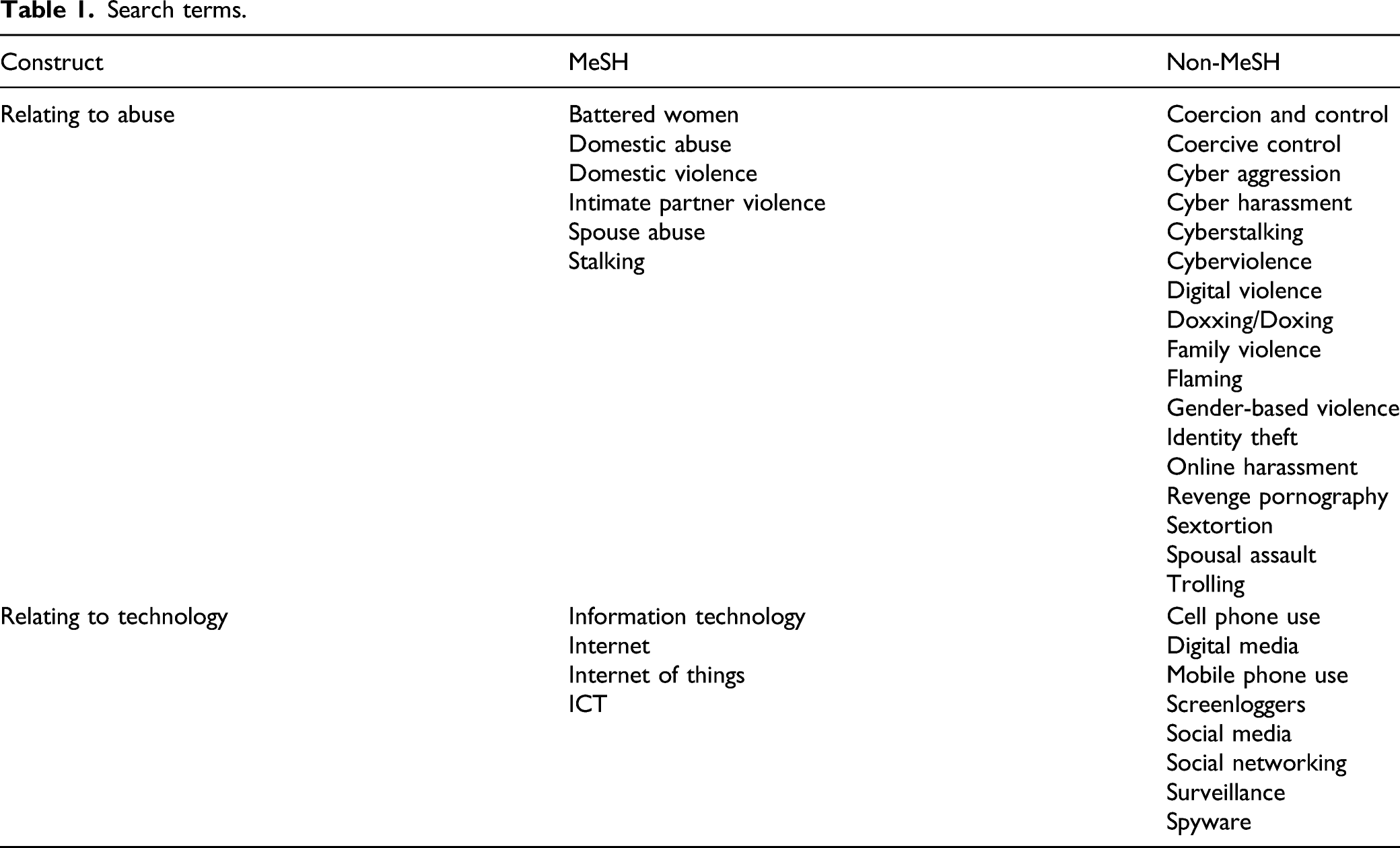
Two additional searches were performed as a check following the search of bibliographic databases. First, Google Scholar was searched using the terms ‘Information technology’ OR ‘Internet’ OR ‘Internet of things’ OR ‘ICT’ AND ‘Intimate partner violence’. The first 1000 items returned were checked for additional relevant articles not found by the main search. Second, the findings of any relevant literature reviews uncovered during the search were checked for potential additional material meeting our search criteria.
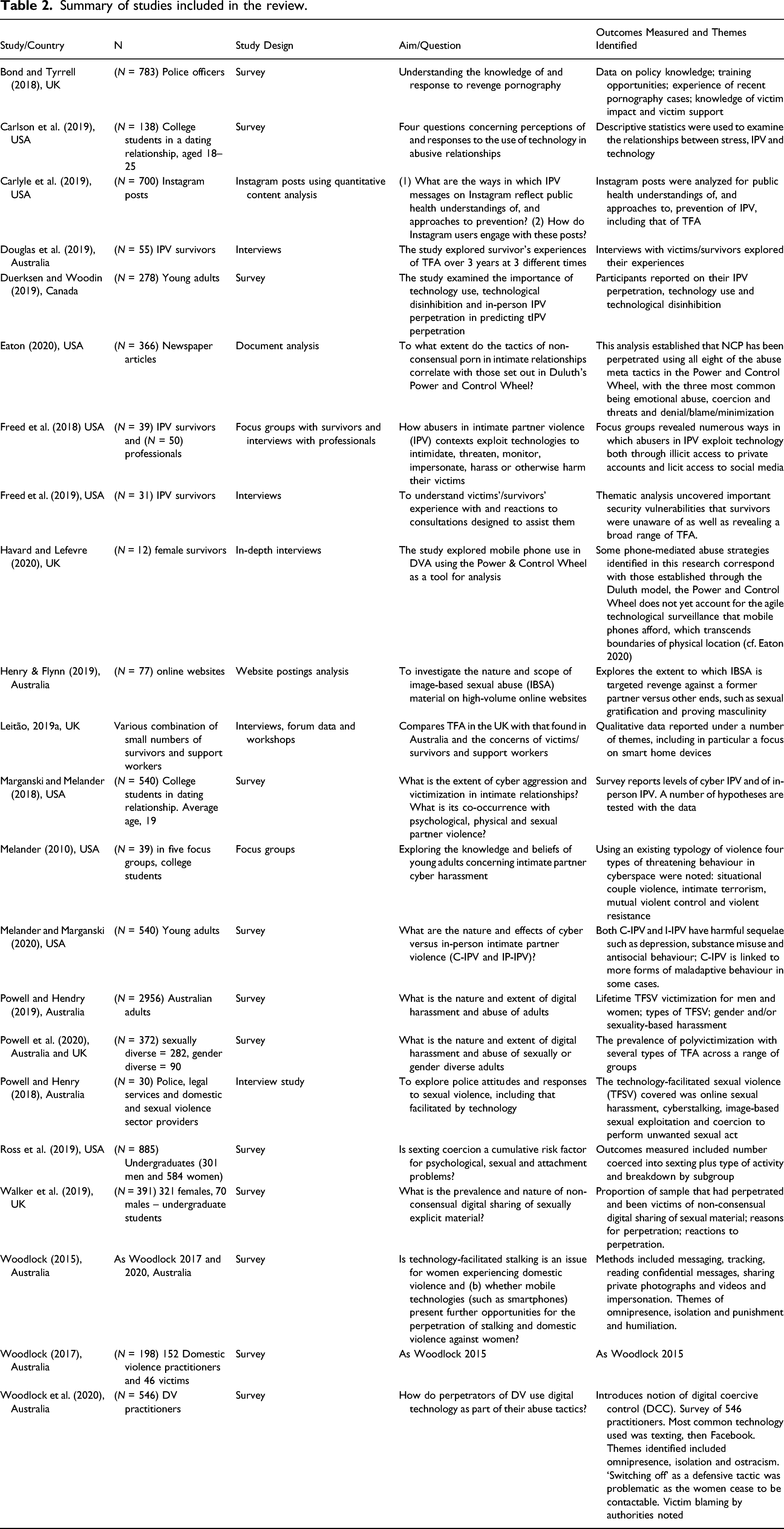
Summary of studies included in the review.
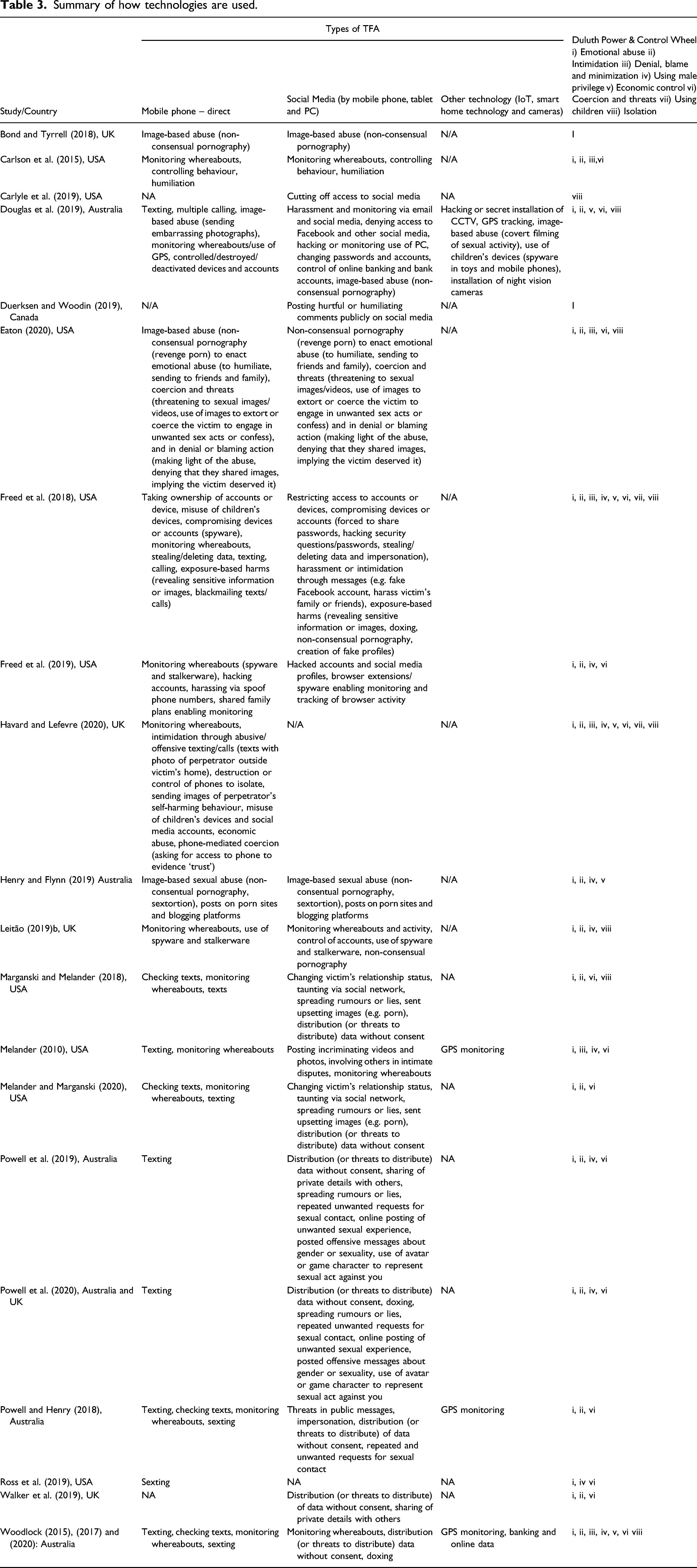
Summary of how technologies are used.
Selection of Sources of Evidence
As noted, we adopted the PRISMA framework in conducting and reporting this scoping review: see Figure 1 which shows the selection of evidence (Tricco et al., 2018). Our searches identified 2404 papers following removal of duplicates. These were initially screened and 2273 were removed on the basis of title or abstract. Amongst these were 26 review articles of some relevance whose citations were checked against our results. PRISMA Flow chart.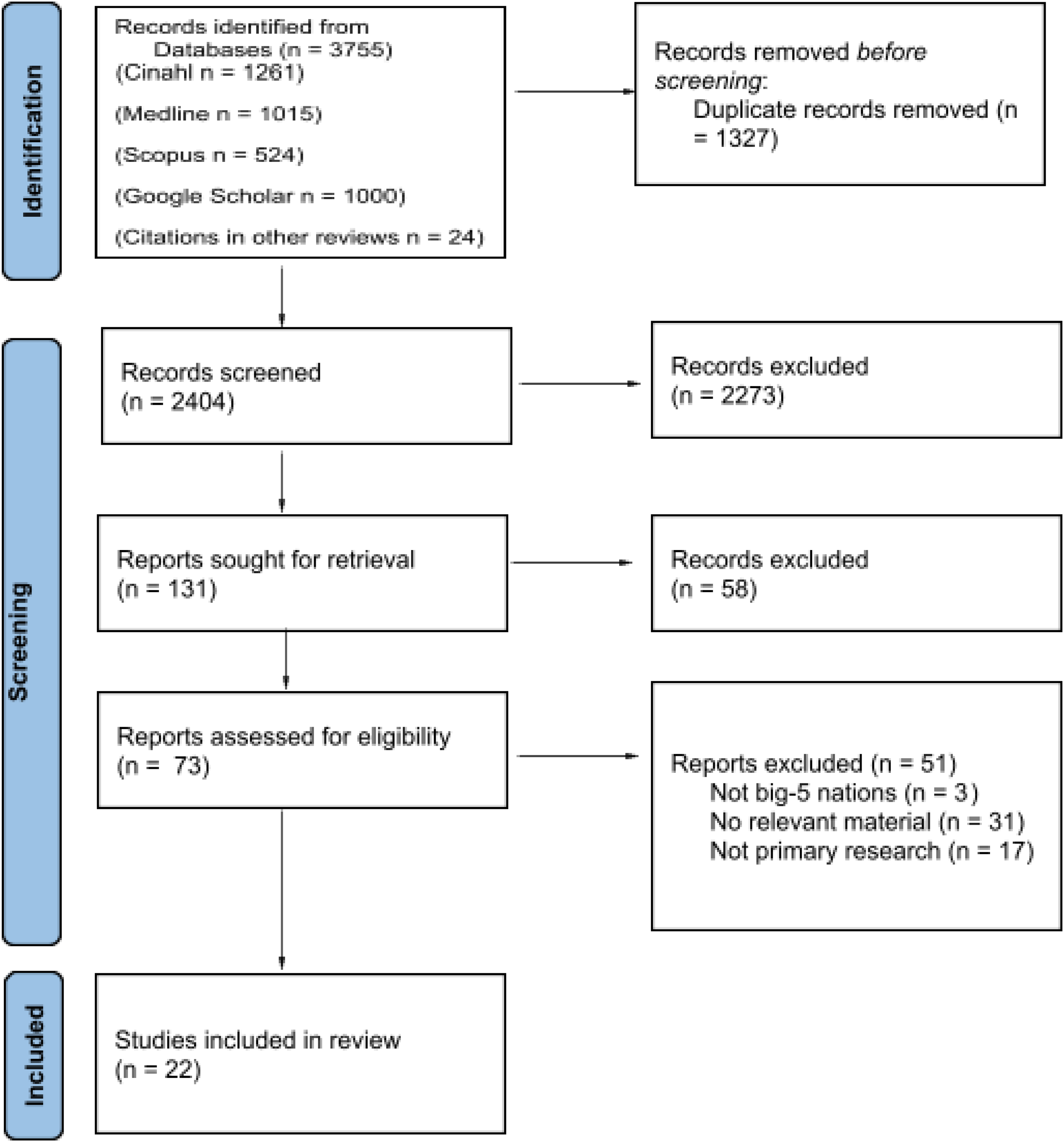
One hundred thirty one articles were retrieved as full text plus 24 additional citations identified from the review articles (155 in total). Of these, 82 were excluded; some abstracts contained sufficient material for exclusion but were only available with the full text. Seventy three articles were assessed for eligibility. Fifty one were excluded: 17 were not primary research; 31 did not contain relevant material; and 3 did not contain material from the included nations. This left 22 articles included in the review: Table 2 provides a summary of included studies.
Results
Synthesis of Findings
This scoping review focused on TFA in intimate relationships and results are presented under the following main headings: types of TFA in intimate relationships; the impact of TFA; resistance to TFA in intimate relationships; and implications for policy and research.
Types of TFA in Intimate Relationships
Several authors categorized abuse using pre-existing frameworks, including: a social ecological model (Carlyle et al., 2019); Johnson (2010) typology (Melander, 2010); the Women’s Experience of Battering framework (Melander & Marganski, 2020); and the Duluth Power and Control Wheel (Pence & Paymar, 1993). The latter is adopted in several included studies (Marganski & Melander, 2018; Eaton, 2020; Melander & Marganski, 2020). It lists eight categories of power and control (or ‘spokes of the wheel’) used within relationships including: i) emotional abuse; ii) intimidation; iii) denial, blame and minimization; iv) using male privilege; v) economic control; vi) coercion and threats; vii) using children; and viii) isolation. In a document analysis of 366 newspapers articles published between 2012 and 2017, Eaton (2020) used this framework to categorize TFA finding that seven of the eight categories appear frequently in combination. Table 3 illustrates the way the technologies reported in the included studies mapped to the eight categories of the Duluth Power & Control Wheel (Pence & Paymar, 1993).
Table 3 shows the reported technology used for IPV in the studies examined and abuse perpetrated via mobile telephone and social media usage were the most widely cited, with GPS and hacking technology also frequently used. For example, in Woodlock’s (2015) study the most common was the smartphone, followed by social media (which can, of course, be accessed via smartphone). More sophisticated use of technology, such as GPS tracking and hacking into bank accounts, was also reported.
Abuse was often described broadly in accordance within a pattern of coercive and controlling behaviour including: restricting access to or ownership of devices (Freed et al., 2018; Woodlock et al., 2020); limiting social media use and restricting links to social networks (Douglas et al., 2019); destruction of devices (Freed et al., 2018); hacking accounts, changing passwords or removing friends (Melander, 2010; Freed et al., 2018; Woodlock et al., 2020); deleting messages or context (Woodlock, 2015; Freed et al., 2018; Woodlock et al., 2020); and use of children’s accounts and devices (Freed et al., 2019).
There were, however, some more distinct themes presented across the studies including: economic abuse; emotional abuse; harassment; intimidation; tracking and monitoring; image-based sexual abuse; abuse via social media and web-based platforms. Many of these behaviours overlapped and were experienced simultaneously (phenomenon known as polyvictimization). For example, in Eaton (2020) the tactic of emotional abuse appeared in 90.7% of cases (total n = 366 cases) of non-consensual pornography (a form of image-based sexual abuse). Havard and Lefevre (2020) claimed that most of the data in their study was classified under various headings but, ultimately, it amounted to emotional abuse as the behaviour was intended to undermine, intimidate, frighten or cause distress. Similarly, this study noted that image-based sexual abuse was prevalent. Their claims, however, were based on a small sample of interviewees (n = 12).
A common finding reported in the studies was the use of technology and digital means to enable stalking and monitoring. Many of the victims/survivors in a qualitative study by Douglas et al. (2019) (n = 55), the only longitudinal study in the sample, described how mobile phones were commonly used to monitor and track their movements and whereabouts. One victim/survivor observed that her car’s battery drained quickly and it was found to have a GPS tracking device installed. Another reported that her ex-partner had set up night vision cameras in her bedroom, with another describing how her partner installed video cameras in every room in their home on the pretense of being able to see their baby in each space. In a study of college students (n = 540), survey participants were aware that they were being monitored, but in others, they were not aware until the spyware, stalkerware or other covert monitoring had been uncovered (Marganski & Melander, 2018).
Another common theme across the studies was the use of text- and image-based abuse of both a sexual and non-sexual (but often intimidating) nature (Douglas et al., 2019; Henry & Flynn, 2019; Melander & Marganski, 2020; Powell & Henry, 2019; Woodlock, 2015). Douglas et al. (2019) found that participants in their study reported mobile phones often used with perpetrators making multiple calls and texts with threatening or harassing messages or through sending intimidating or embarrassing photographs. One woman in their study described how her ex-partner forced her to have sex and covertly filmed it. He then threatened to post the pictures onto the internet if the victim did not change her evidence in a forthcoming court hearing. This case provides an explicit example of sextortion.
Indeed, non-consensual sharing of images (aka revenge pornography) was commonly used as emotional abuse and/or to blackmail, humiliate and cause distress (Eaton 2020; Freed et al., 2018; Powell & Henry, 2018, 2019; Powell et al., 2020; Walker et al., 2019). It was shared with the public via the internet and directly with the families and children of victims/survivors. One study combined qualitative content analysis with a digital ethnographic approach to investigate the different types of pornography websites (n = 77), sites which facilitated image-based sexual abuse, and classified these as: revenge, ex-girlfriend and rape sites (Henry & Flynn, 2019).
Cyber harassment was commonly reported and enacted via a range of devices and technologies (Marganski & Melander, 2018; Melander & Marganski, 2020; Powell & Henry, 2019; Powell et al., 2020; Ross et al., 2019; Woodlock, 2015). Broadly, these behaviours can be divided into types of TFA that align with in-person IPV. For example, the threat of TFA was used to coerce victims/survivors into, for example, staying in the relationship and/or having unwanted sexual contact with the threatening partner or former partner. Additionally, new types of abuse are made possible through technology; for example, doxing (or doxxing) which is the act of publicly revealing private and personal information about an individual through the internet (Melander & Marganski, 2020). The division is not clear-cut because technology can transform in-person abuse; for example, the ability to monitor a partner’s activity is hugely enhanced by technology such that its effects on the victim may be overwhelming, as seen by the impact of omnipresence, described below.
The Impact of TFA
A small number of studies reported the consequences of TFA. Where data on impact was presented, it often depicted extreme and concerning effects on the victim. No studies reported how the perpetrators were affected having committed abuse. More importantly perhaps, although TFA often works by being socially visible, there was nothing directly reported on how it affects intimate relationships more widely. We return to this point in the discussion. There were four main themes on impact including: financial impacts; mental health outcomes; social impacts; and a sense of a perpetrator’s omnipresence. We also note that consequences are rarely experienced in isolation but as overlapping and interacting.
Financial Impacts
A number of studies described how victims/survivors had experienced financial consequences of TFA (Douglas et al., 2019; Eaton, 2020; Leitão, 2019b; Melander, 2010; Woodlock, 2015; Woodlock et al., 2020). Impacts varied and included: lack of or limited access to finances and online banking; loss of employment; restrictions and prevention in securing employment; the accrual of debt; payment of hefty fees for the removal of sexual images from social media and web-based platforms; financial implications of purchasing new or replacement devices. Douglas et al. (2019) found that the intersecting control of finances and technology resulted in a lack of access to banking (and therefore money) when a perpetrator changed passwords for the internet banking of a victim/survivor and then destroyed her laptop (thereby incurring social impacts too in that the victim was isolated from her social network and had no resources to pay for a replacement). Alongside the financial impacts of this, victims/survivors’ limited participation in the digital world can have a negative impact in terms of job prospects and other aspects of daily living (Douglas et al., 2019). Eaton (2020) described how the removal of sexual images that have been uploaded to ‘slut-shaming’ websites by a perpetrator in an act of non-consensual pornography was potentially unachievable for many victims/survivors noting that some of these sites charge hundreds of dollars in fees to remove sexual images.
Mental health outcomes
The reported harms to the mental health of victims/survivors ranged from the diagnosis of mental health conditions (e.g. depression and general anxiety disorder) to the doubting of one’s sanity (through gaslighting) and suicidal ideation (Bond & Tyrrell, 2018; Eaton, 2020; Melander & Marganski, 2020; Powell et al., 2020; Ross et al., 2019; 2019a; Woodlock, 2015, 2017). In Bond and Tyrell’s (2018) UK-based survey of police officers (n = 783), they found that a large proportion (n = 607) thought that non-consensual pornography could lead a victim to experience mental health impacts such as depression and anxiety. Widespread feelings of fear and humiliation were reported across studies and, in some instances, embarrassment and fear meant some were unwilling to report the abuse.
From their content analysis of U.S. news stories, Eaton (2020) concluded that the negative impact of non-consensual image-sharing was especially traumatic and long-lasting, and often coupled with social and economic consequences. They reported how one victim, named ‘Jane’, whose ex-husband had posted pictures and videos online after surreptitiously recording their sexual encounters, likened the experience to that of being raped. Another victim described how the experience drove her to the brink of suicide. These findings were supported by a survey of students (n=391) who had sent private sexually explicit messages to their intimate partners that were subsequently widely shared (Walker et al., 2019). In a qualitative study, 2019a identified a different tactic used in cases of gaslighting as the misuse of smart home devices, such as locking and unlocking doors, remotely triggering alarms and changing heating settings. The use of gaslighting led to victims/survivors feeling that they were ‘losing their mind’.
Social Impacts
Several studies included references to social impacts including; safety concerns; reduced contact with significant others; and social isolation (Douglas et al., 2019; Havard & Lefevre, 2020; Powell & Henry, 2018; 2019a; Woodlock, 2015). Overwhelmingly, the most frequently reported outcome was social isolation resulting from the direct actions of perpetrators. Studies also reported the consequences of advice given by professionals to TFA victims/survivors as leading to social isolation as such advice included changing email accounts, limiting or ceasing use of the internet and social media, blocking texts, messages, calls and emails or replacing devices (Powell and Henry, 2018). Inevitably, this can limit victims/survivors’ participation in the digital sphere, restricting or losing their social connections and contact with others.
Omnipresence
One of the most striking consequences of TFA, marking its distinctiveness from other abuse, is its pervasiveness and reach. Almost all people carry a mobile phone, regularly access the internet and social media. As such, mobile phones can be used to abuse both for coercive control and maleficence on an almost continual basis. This pervasiveness was repeatedly cited in the empirical data reported and termed ‘omnipresence’ in many studies.
Omnipresence refers to the state of being widespread or constantly encountered. In the case of TFA, it describes how perpetrators achieved the property of being present everywhere at all times. To convey omnipresence, Melander (2010) described a message received by a victim/survivor which simply read: ‘I’m always in your inbox’. The sense of a perpetrator’s omnipresence could be described as a tactic of TFA but it was also depicted in studies as a consequence (Douglas et al., 2019; Havard & Lefevre, 2020; Woodlock, 2017; Woodlock et al., 2020). Technology was used covertly and overtly to enable surveillance of victims/survivors to create the sense of omnipresence. Some victims/survivors described this relative to their experiences of IPV during and after their relationship had ended. Perpetrators used different technologies and methods (incessant texting or calling, social media postings). Havard and Lefevre (2020) found that in addition to omnipresence, TFA also resulted in some victims/survivors viewing perpetrators as omniscient (all knowing) and omnipotent (all powerful).
Some forms of TFA were omnipresent not just in their continual nature but also in their spread across time and social space. Time-wise, for example, images could not be erased from the internet and, disconcertingly, could reappear at any time. In addition, something posted on social media could be accessed widely both by personal, social and work associates. Some victims/survivors were concerned about how it might affect their future job prospects.
Resistance to TFA in Intimate Relationships
Most reviewed material focused on the perpetration of TFA, rather than resistance. Despite this, there were some empirical data on resistance reported. In particular, the dual nature of some technology was noted in terms of how it was used to both perpetrate and resist abuse. There were three main themes in relation to resistance including: direct action to stop TFA; legal and specialist support routes; barriers to resistance.
Direct Action to Stop TFA
Various types of action were identified. First, victims/survivors actively disengaged with technology and digital platforms by blocking contacts on social media, mobile phones or email (Douglas et al., 2019; Freed et al., 2019; Havard & Lefevre, 2020; Melander, 2010) or disconnecting from social media altogether (Douglas et al., 2019). They also took action by making changes to devices, cloud storage providers, phone numbers, email addresses or security settings (Douglas et al., 2019; Freed et al., 2019; Havard & Lefevre, 2020). As it was reported that children’s devices or accounts were sometimes used as a means to enact abuse (mostly through covert recording or use of spyware), some victims/survivors reported how they had learned how to check their children’s phones for new apps or devices after contact visits (Douglas et al., 2019; Eaton 2020).
Powell & Henry (2018) found that technology has a dual nature such that it can be used to resist as well as perpetrate abuse. Similarly, a study by Douglas et al. (2019) reported the different ways that victims/survivors used technology for: protection (using, for instance, closed-circuit television (CCTV) and GPS); safety in relation to child contact (e.g. handing over a child in public where there was CCTV); recording evidence of abuse experiences (for instance, one victim recorded evidence of violence and threats resulting in a support service installing surveillance cameras in her home); and to justify separation from the perpetrator (one victim saved pictures on their phone to justify their separation to their partner’s relatives). Victims/survivors could thus use technology to record perpetrators in ways that were effective in enabling separation or providing evidence for legal redress (Powell & Henry, 2018, 2019). Unfortunately, of course, some perpetrators could respond by ensuring their abuse could not be tracked or that messages were erased once received.
Legal and Professional Support Routes
A number of studies explored the utility of professional support in cases of TFA resistance (Bond & Tyrrell, 2018; Douglas et al., 2019; Freed et al., 2018, 2019). Bond and Tyrrell (2018) investigated police officers’ understanding of non-consensual pornography concluding that police in the UK have a limited understanding of the legislative framework pertaining to non-consensual pornography and lack confidence both in investigating cases and responding to victims/survivors. This finding was echoed in a study of Australian police responses to TFA which suggested that online sexual harassment, cyberstalking and image-based sexual exploitation were not viewed as part of a continuum of violence with other forms of abuse; the researchers suggest this is a failure to recognize its serious consequences (Powell and Henry, 2018).
In an Australian study by Douglas et al. (2019), a number of women (n = 17) reported successful use of legal responses including: reporting TFA to police; adding specific conditions about TFA to their civil protection orders; and organizing for lawyers to send letters to abusers asking them to cease using technology to enact harm. There is a much richer body of empirical evidence on TFA that has emerged from Australia which possibly accounts for a more informed evidence-based response for victims/survivors.
A qualitative study in the US (Freed et al., 2019) reported findings from a study that explored the value of technical help as consultants tested a tool, named a technograph. The technograph enabled a clear picture of victim’s digital footprint and entanglements to draw connections between people, devices and accounts to inform safety planning. Researchers in this study noted the limited ability of legal professionals to advise on what digital forensic evidence would be needed for use in a client’s legal case as both clients and legal professionals looked to the research team for advice about what should be documented and how; for example, they were asked: ‘so how do I prove that he’s doing all these things? What are the next steps?’
Other studies detailed non-legal professional support or made conclusions on the basis of study findings. For example, after surveying a sample of college students (n = 138), Carlson et al. (2015) argued that because technology features heavily in young people’s lives and in their personal relationships, relationship counselling should be more freely available to enable young people to incorporate technology in healthy ways within their relational practices.
Barriers to Resistance
There were a number of impediments to resistance. Some studies reported that perpetrators took physical action in destroying mobile telephones and devices belonging to victims/survivors effectively preventing them from reaching out to the police or other supports (Douglas et al., 2019; Freed et al., 2018). In addition, victims/survivors had their access to services withheld or cut (Douglas et al., 2019). While professionals frequently advise victims/survivors to disconnect or undertake a ‘digital detox’ (Levy, 2014), this approach isolates victims/survivors, from their supports and potentially interferes with their ability to engage in work and education. Douglas et al. (2019) also highlight that it is unfair to ask victims/survivors, to forsake their social links and connectedness when it is the perpetrator who has mis-used the technology. In addition, it can be highly impractical for victims/survivors to disconnect from technology and the digital world as increasingly routine services and daily activities require such a connection (Woodlock, 2015).
Similarly, Freed et al. (2018) found that professionals tended to, as the first port of call, advise that victims/survivors replace their devices but, in many cases, victims/survivors are unable to afford the cost of a new device or mobile plan particularly if perpetrators have been the main or sole financial provider in the family. More concerningly, on making reports that they were worried that there were apps or tracking software on their devices, some studies reported victims/survivors being told by professionals that their devices were malfunctioning or that they did not know how to use them properly, further disempowering victims/survivors by questioning their judgements and demonstrating concern about the ‘believability’ of such cases (2019a). Even when believed, victims/survivors subsequently realized that professionals frequently had gaps in knowledge regarding TFA.
Discussion
This review of 22 studies exploring TFA in intimate relationships has revealed that TFA is positioned on a continuum of intimate partner violence that integrates abuse that is facilitated by technology as well as that which is perpetrated as types of in-person IPV. This illustrates a continuity and relationship between the two (TFA and in-person abuse), particularly when experienced as polyvictimization. However, it is salient to highlight the distinctiveness of TFA. We are living in a digital world in which we can be connected to others at all times of the day, from all corners of the world. This means that perpetrators of IPV can transcend temporal and physical world boundaries to covertly and/or overtly enact a wider range of abuse from anywhere, at any time. Thus, the scope and opportunities for TFA perpetration are considerable. Coupling this wide-ranging potential with the victim/survivor’s experience of abuse as omnipresent, it is reasonable to argue that a victim/survivor’s ‘space for action’ to resist TFA and seek support is significant reduced (Kelly, 2003).
Melander and Marganski (2020) compared the effects of TFA and in-person IPV in a survey of undergraduate students (n = 540). They found inter alia that IPV was related to anger and depression and, independently, problematic substance use, with males at a higher risk of the latter. Importantly, TFA was linked more strongly than in-person IPV with certain maladaptive behaviours, such as substance use. They argue that TFA as IPV should no longer be considered by authorities as a less serious form of abuse than in-person IPV. A similar conclusion is drawn from a survey of undergraduate students (n=885, constituted by 584 women and 301 men) of sexting and in-person sexual coercion, which showed that sexting independently contributed to psychological, emotional and sexual problems in women (Ross et al., 2019).
Overall, the evidence on types of TFA illustrated that it maps consistently to the domains of the Duluth Power and Control Wheel (Pence & Paymar, 1993) in terms of representing: i) emotional abuse; ii) intimidation; iii) denial, blame and minimization; iv) using male privilege; v) economic control; vi) coercion and threats; vii) using children; and, viii) isolation (Eaton, 2020; Freed et al., 2018, 2019; Havard & Lefevre, 2020; Marganski & Melander, 2018; Melander & Marganski, 2020; Woodlock, 2015; Woodlock et al., 2020). Many of the behaviours described are also examples of what Stark (2007) calls micro-regulation and contributed to the victim/survivor’s lack of privacy, social isolation, reduced autonomy, financial dependence and, for many, poor mental health.
Determining the range of impacts, however, was less reported in the studies than the tactics and types of TFA found. It may be that some of the impacts are broadly similar to in-person abuse (in terms of their social, health, mental health and economic consequences), but there are some distinctive impacts resulting from TFA such as those that result from image-based abuse (non-consensual pornography in particular) and the ever-present threat of future appearances of humiliating and embarrassing images on the internet. The availability and presence of personal, sexual images or media, as noted above, can have catastrophic and distressing effects for victims/survivors (Henry & Flynn, 2019). In addition, the very existence of photos or videos of a sexual nature was used by perpetrators and highlighted Woodlock (2015: 13) who noted how some women felt absolutely ‘stuck’, ‘trapped’, powerless and totally controlled when perpetrators threatened to release photos or videos to family, friends and work colleges. This also served to prevent women from seeking police interventions and intervention orders.
The findings relating to gender were mixed in the papers reviewed. The qualitative papers were primarily focused on women who were victims/survivors; some papers only had women as the focus of abuse (e.g. Douglas et al., 2019; Woodlock, 2015). Where a quantitative comparison was drawn, the gender balance of abuse was less clear. For example, in relation to non-consensual sharing of sexually explicit media, and to sexting and sexual coercion, men also featured as victims/survivors at a level approaching that of women (Ross et al., 2019; Walker et al., 2019). Powell & Henry (2019) found, in a survey of Australian adults, that women and men report similar prevalence of technology-facilitated sexual violence against them; however, they note that it was likely that men were also probably the perpetrators of most of this violence, including that against other men.
Critical findings.
Implications for policy, practice and research
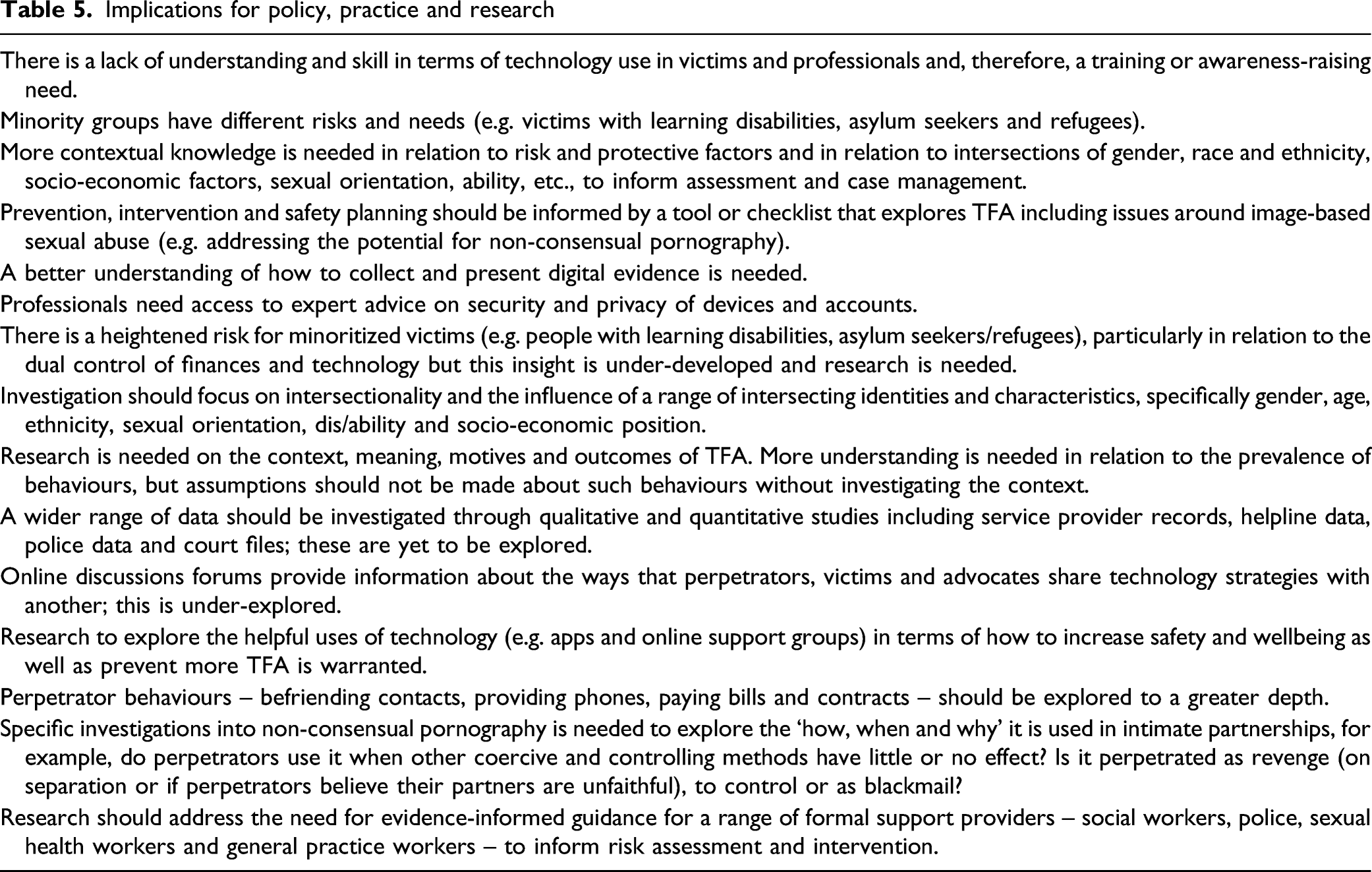
A small number of studies paid attention to diversity; for example, Douglas et al. (2019) provided a number of case studies of women from diverse ethnic and cultural backgrounds noting the heterogeneity of TFA types, impacts and modes of resistance in these instances. However, mostly studies did not illuminate or draw attention to such differences highlighting a future research priority in relation to TFA in terms of enabling a more informed understanding of TFA when experienced by minoritized people. Another implication for future research pertains to the lack of studies that focus on the role of children and how they are drawn into TFA either covertly or overtly. The use of TFA by proxy (i.e. abuse perpetrated through a third party such as a child, family member or friend of the victim/survivor) is under-researched more generally. This is particularly the case in the context of post-separation parenting in which technology provides perpetrators new ways of abusing, controlling, stalking and harassing their former partners and there is a clear need for qualitative and longitudinal research that examines the use of technology where there are children of the relationship (Markwick et al., 2019).
While studies illustrate how technology enables abuse, only a small number of studies show technology as facilitating resistance when digital and communications technology could be used more in this regard (Rempel et al., 2019; Grimani et al., 2020). In other words, the technology used to perpetrate violence and abuse (social media, video cameras, mobile phone and so on) could be used as technology-facilitated resistance (or techno-resistance). For example, social media could be used to generate formal networks of support to victims/survivors both to identify perpetrators and their deeds and to break through the isolation which victims/survivors of IPV frequently report. Indeed, a study that did not meet our inclusion criteria nonetheless made use of one such wider network (McCauley et al., 2018). Social media could also be better used as awareness-raising to increase people’s knowledge of how to detect and disarm covert surveillance techniques (e.g. spyware).
Finally, several studies reported findings from samples of young people, often college students (Carlson et al., 2015; Duerksen & Woodin, 2019; Marganski & Melander, 2018; Melander, 2010; Ross et al., 2019; Walker et al., 2019). Due to the nature of such samples, recruitment methods were often not random, but based on biased means such as recruiting students from a particular course of study. Additionally, there are limits of applying these findings to a population of all victims/survivors of IPA without an age boundary. Further, while a considerable number of studies can be found on youth and young adults in relation to cyberbullying and dating violence, TFA in long-term intimate partnerships has not been adequately explored (Freed et al., 2018; Powell & Henry, 2019). For this review, most research was conducted using quantitative surveys, highlighting the need for more qualitative research. Hence, there are clear implications for future research including the need to pursue consensus on defining and delimiting TFA within intimate relationships and when designing research taking recruitment, sampling and methods into account.
Limitations
The limitations of any study lie on a spectrum from the unavoidable to the avoidable. At the unavoidable end, for this study, are those shared with all scoping reviews. First, is the lack of full quality appraisal of the studies. Whilst we used a quality assessment tool as a simple method to exclude papers of poor quality, we did not go further in, for example, weighting the findings. This was appropriate for a scoping review, which does not seek definitive answers to a clear, quantitative question. However, it means that lying behind the findings reported are the limitations of included studies. There are some clear examples. The first is that of diverse methodologies, recruitment methods and sampling which are identified across the literature making comparison more challenging. Second, definitions of abuse are not always clear or consistent; thus, what is reported as impersonation in one paper might be recorded as doxing in another and gaslighting in a third. Third, the reporting of gender identities of abuser and victim/survivor is often inconsistent and/or unclear.
At the avoidable end of the spectrum, our protocol specified adults aged 18+; however, many papers had proportions of younger victims and we ended up using a post-hoc rule of using these where the majority were 18+. This probably had little effect on our findings but we would be more precise in future. Also avoidable was our decision to limit findings to the big five anglosphere countries. This choice was made in order to keep the data within manageable limits and was, to this extent, justified. Additionally, a recently published scoping review, describing technology-facilitated domestic abuse, did not adopt exclusion criteria by country yet only found relevant papers from regions in the big 5 (Afrouz, 2021). This provides further justification for our decision.
In the middle of the spectrum, probably nearer the unavoidable end, was the difficulty in parsing the findings with regard to any groups other than women who were the victims/survivors of TFA perpetrated by men. There were findings relating to other groups and to groups by other characteristics, such as ethnicity. Our study, however, focused almost exclusively on women as a whole. Since this work was done, however, there has been at least one scoping review focused exclusively on IPV in gay and bisexual men, although this has little to say concerning TFA (Callan et al., 2021).
The final limitation, which is at the unavoidable end of the spectrum, relates to the release of new relevant material outside the search time parameters. As well as the scoping reviews mentioned (Afrouz, 2021; Callan et al., 2021), we note, in particular, the publication of a new book that includes research of relevance including, for example, TFA amongst gay and bisexual men. The book is the Emerald International Handbook of Technology Facilitated Violence and Abuse. At present (August 2021), it is available freely online (Bailey et al., 2021). The new empirical material would probably leave unchanged our main findings, particularly concerning future research. However, the book also contains relevant discussion and should be a reference for anyone researching TFA in the near future.
Concluding Statement
This review has uncovered some critical messages for future directions. First, there are policy and practice implications to this evolving but nascent scholarship in that an evidence-informed framework for professional responses to TFA is needed. Second, enhanced understanding about the ways in which victim/survivors can adopt varied forms of digital and technology-facilitated resistance is needed to couple with evidenced-informed professional action. Third, better insights are needed of the ways in which TFA by proxy, particularly when involving children, is needed especially in post-separation cases when legal proceedings are ongoing. Fourth, we chose to focus on the big five countries, and we end with a call to all researchers, including colleagues in the Global South, to engage in research to advance understanding about TFA.
Footnotes
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: The authors received financial support from the World Universities Network for this project.
