Abstract
Life history strategy (LHS) and life history contingencies (LHCs) should theoretically influence the use of exploitative and deceptive resource acquisition strategies. However, little research has been done in this area. The purpose of the present work was to create measures of exploitative strategies and test the predictions of life history theory. Pilot studies developed and validated a behavioral measure of cheating called the Dot Game. The role of individual LHS and LHCs (manipulated via validated story primes) on cheating was investigated in Study 1. Studies 2a through 2c were conducted to develop and validate a self-report measure called the Exploitative and Deceptive Resource Acquisition Strategy Scale (EDRASS). Finally, Study 3 investigated life history and EDRASS. Results indicated that while LHS influences exploitative strategies, life history contingences had little effect. Implications of these findings are discussed.
Keywords
Introduction
Acquiring resources is an essential activity for living organisms. Resources include food, shelter, mates, and (for humans in modern environments) man-made objects such as tools and currency (Gorelik, Shackelford, & Weekes-Shackelford, 2012). Buss and Duntley (2008) discuss three classes of strategies humans use to acquire reproductively relevant resources: individual resource acquisition strategies (e.g., tool making and solo hunting), cooperative strategies (e.g., social exchange and coalitional formation), and exploitative and deceptive strategies (e.g., coalitional warfare and free riding). Exploitative and deceptive strategies, the focus of this research, overlap somewhat with criminal behavior. For example, stealing money involves exploiting another’s resources, and stealing (e.g, robbery) is against the law. In contrast, coalitional warfare may be state sanctioned (and thus not a criminal behavior) but would be an example of an exploitative and deceptive strategy. The defining feature of an exploitative strategy is the gaining of a reproductively relevant resource for the perpetrator, while simultaneously depriving the victim of the resource. Although considerable research has investigated behavior like stealing from a criminal behavior perspective, Buss and Duntley (2008) argue very little attention has been applied to adaptations for exploitative and deceptive behavior. Although the present research does not test for adaptations in the form of specific cognitive mechanisms for exploitation and deception, it does test the expression of exploitative and deceptive behavior as a function of life history strategy (LHS) and life history contingencies (LHCs). Thus, this research is aimed at understanding how an exploitative strategy is influenced by an individual’s LHS and how it may further be influenced by certain environmental cues in the form of LHCs.
Life History Theory
Life history theory (LHT) is a mid-level theory partially derived from evolutionary meta-theory (McArthur & Wilson, 1967). LHT originally focused on why some species (later called r-strategists) engaged in extreme amounts of reproduction and subsequently died, whereas other species (later called K-strategists) reproduced across the life span (Cole, 1954; Dobzhansky, 1950). The terms r and K selection were then applied to understand these differing strategies (McArthur & Wilson, 1967). Pianka (1970) extended this line of thought and described how different life history traits should fall on the r-K continuum as well as the role of density-dependent selection. Thus, LHT was originally focused on between species differences and density-dependent selection. LHT has also been applied to within species differences (e.g., Gadgil & Solbrig, 1972). Rushton (1985), for example, argued that individual differences in life history could parsimoniously explain many traits in humans.
Initially, there was great interest in the r/K continuum. However, research on density-dependent habitats failed to match LHT predictions in many cases and indicated that the theory was missing some key components (Stearns, 1992). One such component was the “slow–fast” continuum (Bielby et al., 2007; Promislow & Harvey, 1990; Roff, 1992; Stearns, 1983). The slow–fast continuum focused on the adaptive covariation in life history traits and, importantly, the effects of age-specific mortality rates. The present work is based on contemporary LHT that tends to consider both population density and differential mortality rates across age-groups to be influential (Figueredo, Vásquez, Brumbach, & Schnieder, 2004).
The core of LHT concerns the allocation of bioenergetic and material resources. As these resources are finite, resource allocation involves certain trade-offs (Figueredo et al., 2004, 2006; Figueredo, Vásquez, Brumbach, & Schnieder, 2005; Kaplan & Gangestad, 2005; Stearns, 1992). Specifically, LHT proposes a continuum of resource allocation ranging from somatic effort (resources devoted to the continued survival of the organism) to reproductive effort (resources for producing new organisms). Reproductive effort can be divided further into mating effort (resources for obtaining and retaining sexual partners), parental effort (resources for enhancing offspring), and nepotistic effort (resources for enhancing kin survival). Organisms that trade-off reproductive and mating effort over somatic and parental/nepotistic effort are referred to as having a fast LHS (FLHS). Organisms that trade-off somatic and parental effort over reproductive and mating effort are referred to as slow life history strategists (SLHS). LHT proposes that organisms will adaptively assort on traits and use strategies that allow them to pursue their particular LHS. It is important to note that neither strategy is inherently superior. Each strategy can be advantageous or disadvantageous depending on the environmental context.
The individual differences in LHS in humans have been shown to be heritable. For example, Figueredo, Vásquez, Brumbach, and Schnieder (2004) found, using the National Survey of Midlife Development in the United States (MIDUS), a single higher order factor (the K-factor) that explained the genetic correlations among the scales. This factor itself was also highly heritable. Figueredo, Vásquez, Brumbach, and Schnieder (2005) also identified 20 scales measuring cognitive and behavioral dimensions (e.g., sexuality, socioeconomic status, community participation, physical health, and parenting and relationship styles) theoretically linked to LHS. These measures formed a single construct, called the K-factor, accounting for 70% of the reliable variance in these measures. Research on the individual differences in LHS has found that a fast LHS is associated with short-term mating, low parental investment, low group altruism, higher criminal behavior, and higher risk taking (Ellis, 1988; Figueredo et al., 2004, 2005, 2006). Although the evidence mentioned earlier does suggest LHS is heritable, consistent with LHT, there are also specific environmental influences that shape the development of an individual’s LHS.
LHCs
The variety of environmental contingencies that can shape an individual’s LHS are collectively referred to here as LHCs. Ellis, Figueredo, Brumbach, and Schlomer (2009) extensively detail the variety of environmental influences that play a role in the evolution and development of LHS. The two main influences are harshness (externally caused morbidity–mortality) and unpredictability (spatial–temporal variation in harshness). Additional factors include population density, intraspecific competition, and resource scarcity. These are theorized by LHT to be dependent on each other, and the combination of some factors may lead to the development and evolution of a SLHS, whereas a slightly different combination may lead to a FLHS. For example, low harshness of the environment when combined with low population density, low resource scarcity, and low intraspecific competition should result in a FLHS. A reproductive over somatic effort trade-off is more advantageous in this case because the population is not near the carrying capacity. There are an abundance of resources available to the population, and so investing in somatic maintenance is not as valuable. Apportioning more energy and resources toward mating and reproduction effort, on the other hand, has valuable fitness effects. Additionally, high harshness and unpredictability is also predicted to lead to a FLHS. Finally, low harshness combined with high population density, high resource scarcity, and high intraspecific competition should result in a SLHS.
Empirical research using multiple species, including humans, supports the hypothesized effects of LHCs (see Ellis, Figueredo, Brumbach, & Schlomer, 2009). For example, research on populations of guppies in low versus high predation areas suggests that guppies in higher predation areas display a FLHS and have traits such as faster growth, earlier age at sexual maturation, and larger litter size than do those in lower predation areas (Reznick, 1982; Reznick & Ghalambor, 2005). The researchers also moved guppies in high predation areas to low predation areas. After 11 years and several generations, the relocated guppies had shifted to a SLHS, displaying traits such as later age at maturity and fewer offspring per litter (Reznick, Rodd, & Cardenas, 1996; Reznick & Shaw, 1997).
There are many life history traits that are uniquely relevant to humans, such as criminal behavior and religiosity (Ellis, 1988; Figuerdo et al., 2005). Although studying LHCs by manipulating actual environments is more difficult to conduct in human populations, there is some evidence confirming predictions of LHT and arguing for the role of LHCs in determining these traits.
Demonstrating evidence of life history contingency effects in deviant social behavior, Brumbach, Figueredo, and Ellis (2009) examined data from the National Longitudinal Study of Adolescent Health. Results indicated that harshness and unpredictability experienced early in life were positively associated with social deviance. Additionally, harshness and unpredictability experienced in adolescence were related, either directly or indirectly, to the development of a FLHS in young adulthood.
Griskevicius, Delton, Robertson, and Tybur (2011) examined correlations between crime, socioeconomic status (SES), and reproductive timing. Consistent with LHT, results showed that violent crime was related to the age that people had children, even when controlling for SES. In areas with higher violent crime rates, people tended to have children sooner, consistent with a reproductive versus somatic effort trade-off. Griskevicius, Delton, et al. (2011) also manipulated harshness and unpredictability via story primes. In the mortality prime condition, participants read a supposed news article about the increasing violence in the United States and how there are many random violent deaths (e.g., shootings in residential and commercial areas). In the control prime condition, participants read a news article about losing and finding a set of keys. Participants were also asked about their perceived resources (e.g., if they felt they were wealthy compared to others) as children and at present. Results showed that the effects of the prime manipulation were moderated by perceived resource availability in childhood. The mortality cues lead participants to want to reproduce sooner but only among those who grew up relatively poor (see also Griskevicius, Tybur, Delton, & Robertson, 2011, concerning how mortality cues can influence risk and delayed rewards).
Work by Dunkel and colleagues also used manipulations of life history relevant information (Dunkel, & Mathes, 2011; Dunkel, Mathes, & Decker, 2010; Dunkel, Mathes, & Papini, 2010). In these studies, manipulations of LHCs were based on hypothetical vignettes. Specifically, participants imagined that they had 5 months, 5 years, or at least 50 years left to live. Dunkel, Mathes, and Decker (2010) found that, when participants imagined shorter life expectancies, they were more likely to show interest in short-term mating. Dunkel, Mathes, and Papini (2010) found these shorter life expectancies increased participants’ inclination to express anger and be aggressive. Finally, Dunkel and Mathes (2011) found a relationship between a FLHS and increased willingness to engage in sexual coercion. This finding is consistent with Gladden, Sisco, and Figueredo (2008) who observed that a SLHS serves as a protective factor in decreasing sexual coercion. More importantly, Dunkel and Mathes (2011) found that shorter life expectancies increased participant’s willingness to engage in sexually coercive behaviors. Thus, several studies demonstrate that manipulation of LHC information can affect a variety of relationships such as sexual coercion and aggression, both of which are related to exploitative strategies.
Life History and Exploitative Resource Acquisition Strategies
In addition to work on the effects of LHCs, there has been research on LHS and several constructs that have overlap with exploitive strategies. Although constructs such as antagonistic strategies overlap with exploitative strategies, they are conceptually different. Antagonistic strategies are those in which people see sexual interests of themselves and their partner as divergent or inconsistent, rather than mutualistic (Malamuth, 1996). Malamuth (1998) argued that FLHSs are more prone to adopt antagonistic sexual strategies that are consistent with short-term sexual strategies, rather than long-term relationships and biparental care. Figueredo and Jacobs (2010) extended this thinking from sexually to socially antagonistic strategies (see also Figueredo, Gladden, & Beck, 2012). Using structural equation modeling, Gladden, Figueredo, Andrzejczak, Jones, and Smith-Castro (2013) found evidence for a relationship between socially antagonistic strategies and LHS. Antagonistic strategy indicators in their work included psychopathy, Machiavellianism, aggression, mating strategy, and mating effort. Although exploitative resource acquisition strategies may be related to antagonistic social strategies, they are conceptually distinct. For example, antagonistic social strategies are far broader. They may include numerous behaviors that are not concerned with the acquisition of resources, nor are they necessarily exploitative. Furthermore, Gladden et al. (2013) did not investigate the role of LHCs in the use of antagonistic strategies.
Exploitative strategies are also not the same as criminal behavior or social deviance. There are many behaviors (including mate poaching, free riding, and deception to get sex) that are exploitative but not criminal. Thus, there is no published study of which we are aware specifically concerning the relationship between exploitative strategies and LHS and LHCs. Although Dunkel and colleagues (2010, 2011) have shown effects of LHCs on mating and aggression for example, their manipulations of life expectancy only concerned harshness. As discussed previously, there are many more contingencies that are theorized to have effects on LHS, such as population density and resource scarcity. Thus, research is needed that examines exploitative strategies specifically as well as the effects of multiple LHCs.
Current Study Overview
The primary goal of the current research was to examine the role of LHS and experimentally manipulated LHCs in determining the use of exploitative and deceptive strategies in an adult human population. In other words, the study aimed to answer the questions, “Are adults of varying LHS sensitive to information concerning LHC information? Does this information modify resource acquisition strategies? Do adult LHS and LHCs interact when predicting the degree one uses this acquisition strategy?” Researching these questions is important because LHT offers a potentially valuable perspective in understanding why and when someone might use exploitative strategies. Addressing these questions experimentally complements previous correlational studies of LHS and social deviance.
A second goal of the research was to develop and validate measures of exploitative and deceptive resource acquisition strategies. As discussed previously, exploitative strategies include numerous behaviors, such as mate poaching and free riding (Buss and Duntley, 2008). Measures that specifically target the behavior of interest are lacking. For example, Kruger, Reischl, and Zimmerman (2008) investigate resource exploitation but use items from the Monitoring the Future study (e.g., trespassing), which speak more toward delinquency. There are tasks that measure free riding (an example of exploitative behavior). However, many of these tasks are economic games and were not created with the goal of understanding exploitative strategies. Although this does not make the tasks unusable, it can limit the extent to which they measure an exploitative strategy. That is, they are not specific enough or do not replicate the context in which someone might exploit resources. A behavioral measure of cheating (i.e., taking a monetary resource) was chosen in order to construct an objective and practical instrument. Because the behavioral measure is narrow in scope, we also developed a self-report measure of exploitative strategies. This scale captures a wider variety of exploitative strategies. We first describe the development and validation of the cheating task.
Primes were used to communicate LHC information to participants. The FLHC prime was previously used and validated by Griskevicius, Delton, et al. (2011). We developed and validated a corresponding slow life history contingency (SLHC) prime. In Study 1, we examined the effects of LHC primes and participant’s LHS on behavior on the cheating task. In Studies 2a through 2c, we developed and validated our self-report measure called the exploitative and deceptive resource acquisition strategy scale (EDRASS). Finally, in Study 3, we examined the effects of LHC primes and LHS on the EDRASS.
Development of the Dot Game Cheating Task
In order to measure exploitative strategies behaviorally, we first developed a cheating paradigm. Existing paradigms are not ideal for several reasons. Many cheating tasks are lab based, involve stealing money from the experimenter, and do not allow for altruistic responses (see e.g., Gino, Scheitzer, Mead, & Ariely, 2011; Mazar, Amir, & Ariely, 2008; Mead, Baumeister, Gino, Schweitzer, & Ariely, 2009). An essential feature of exploitative strategies is that they involve depleting potential or actual competitor’s resources while enhancing one’s own resources. Thus, stealing money from the experimenter is likely not as ecologically valid as stealing from a peer. Finally, altruistic behavior can be defined as a behavior that benefits another person but also presents a cost to the helper (Hamilton, 1964a, 1964b). Altruism and reciprocal altruism are part of cooperative resource acquisition strategies (Buss and Duntley, 2008). Lab-based tasks also restrict the type of sample that can be obtained. An online task allows for a broader sample of participants. For example, participants drawn from Amazon’s Mechanical Turk (MTurk) tend to have more diverse characteristics including age (Buhrmester, Kwang, & Gosling, 2011). Thus, we sought to develop a task that allows for multiple resource acquisition strategies and could be conducted with an online sample.
Participants were recruited through MTurk and paid US$0.10, with a chance to earn a bonus of up to US$1.00. Twenty (12 male) participants (M age = 30.70 years, SD = 8.61) read a description of the study and clicked a link taking them to the online experiment. This study and all others in this article were designed and given through Qualtrics. Participants answered several health and demographics questions and then completed the cheating task called the “Dot Game.” Participants were presented with a series of pictures with a white background and large black dots (a total of 20 pictures created using Adobe Elements 11). The task was to, as quickly as possible, count the dots, click the arrow in the bottom right of the screen, and choose (from a list of four multiple choice answers) the correct number of dots. The participants were told their reaction time would be measured and that they were competing against another participant for a US$1 bonus. They were also told that there were two roles in the game, the “feedback player” and the “no feedback player.” They would be randomly assigned to one of these roles. Specifically, they were told that “If you are the feedback player, at the end of the game you will receive feedback on how many trials total each player has won. It is also up to you to distribute the money. The other player never receives feedback. If you are the no feedback player, you will never receive feedback on how many trials total you have won or lost.”
Participants then received further instruction reiterating the roles and how to actually play the game. The computer then “randomly” assigned them to one of the two roles. In reality, all participants were assigned to be the feedback player, and they were not actually playing with another person. After completing the game, participants were given feedback on how many trials in total each player won. All participants were told they won 10 trials, and the other player won 10 trials. Thus, if participants were fair, they should have allocated US$0.50 to themselves (half of US$1.00). Ten participants allocated more money to themselves than they should have based on the feedback. Nine participants allocated the money fairly (i.e., US$0.50) and one participant allocated US$0.10. Overall, participants tended to behave in a manner consistent with an exploitive or deceptive strategy (M = .66, SD = .25).
After allocating the money, participants were asked several questions to determine whether the task was understandable and whether the deception was effective. All participants indicated that the instructions were clear, and all but one indicated that the feedback made sense. Difficulty ratings were low (measured using a 5-point Likert-type scale, 1 = not at all difficult to 5 = very difficult, M = 1.40, SD = .503). Only two participants indicated suspicion concerning whether they were really paired up with another person or of anything else in the Dot Game. Thus, the Dot Game appears easy to understand and believable to participants. Moreover, a fair number of participants engaged in exploitative and deceptive behavior on the task. That is, they exploited a limited resource by taking more for themselves, leaving less for the other person, than they should have.
Validation of the LHC Primes
The FLHC (i.e. mortality prime) and neutral primes for Study 1 were the “news stories” developed by Griskevicius, Delton, et al., (2011; see Appendix for all primes). A SLHC prime was constructed with three components in mind: food scarcity, increasing population, and competition in the dating market. The conclusion of the article was that people needed to invest in themselves in order to compete with other people. The SLHC prime was formatted to look like a New York Times article, consistent with the FLHC and neutral primes. We intended the FLHC prime to make people feel that the world is more dangerous, unsafe, uncertain, and unpredictable (i.e., communicating high harshness and unpredictability). The SLHC prime should make people feel that the population is increasing, they need to be more competitive, there is high intraspecific competition, and they must invest in themselves. However, they should not feel that the environment is harsh. In other words, the prime should communicate environmental contingences that result in a SLHS.
A pilot study was conducted to validate the primes to be used in the main study. Participants were 148 (41.9% male, 58.1% female, M age = 33.62, SD = 12.60) people recruited through MTurk. Participants answered several health and demographics questions and then proceeded to the instructions for the primes. Participants were told they were about to read a news article recently published in the online Sunday section of the New York Times and that the story was chosen because the length makes it ideal for memory tasks. They were told to read the article carefully because they would be asked several questions about the story afterward. Participants were randomly assigned to read one of the three articles. They then answered a series of theory relevant questions rated on a 7-point Likert-type scale (1 = not at all to 7 = very much).
Planned contrasts compared the FLHC prime to the neutral prime. Participants indicated that the FLHC prime made them feel that the world is more dangerous, t(145) = 6.006, p < .001, d = 1.216, unsafe, t(145) = 4.964, p < .001, d = 1.004, unpredictable, t(145) = 3.814, p < .001, d = .772, and more uncertain, t(145) = 4.464, p < .001, d = .903, compared to the neutral prime. Planned orthogonal contrasts compared the SLHC prime to the neutral prime. Participants rated the SLHC prime as making them feel more competitive, t(145) = 3.535, p = .001, d = .700, that they wanted to invest in themselves more, t(145) = 2.646, p = .009, d = .524, and that the population is increasing, t(145) = 7.215, p < .001, d = 1.429. Importantly, the prime conditions did not significantly differ in emotional arousal, F(2,145) = .055, p = .946. It was therefore concluded the primes had their intended effects.
Study 1
Study 1 examined the role of LHS and experimentally manipulated LHCs in the use of exploitative strategies in an adult human population. The strategy of interest was cheating as measured by the Dot Game. Theoretically, actual environmental changes should have the greatest effect on behavior, and past work suggests that LHCs are more likely to influence younger individuals (Brumbach, Figueredo, & Ellis, 2009; Ellis et al., 2009). If it could be shown that a relatively minimal manipulation of environmental contingency information could alter the use of exploitative strategies even in adults, this would be strong evidence for the importance of LHCs. The following predictions were made based on the theorizing mentioned earlier.
Additionally, LHCs were tested for a possible moderating relationship between LHS and cheating, but no specific direction or magnitude was hypothesized.
Material and Method
Participants and Design
Participants consisted of 182 (44% male and 56% female, M age = 34.5, SD = 12.54) people recruited through MTurk. All participants had to be located in the United States, have at least a 95% approval rating, and be at least 18 years of age in order to participate. Participants were paid US$0.50 for participating in the study and up to US$1.00 as a bonus on the Dot Game task. All studies in this work were approved by the institutional review board at the University of Wyoming. The experiment employed a between-participants design (LHC primes with LHS and self-report antisocial behavior/delinquency as additional predictors). Further descriptive participant characteristics included yearly income before taxes and current relationship status. Income: <10,000 (15.9%); 10,001 −25,000 (19.2%); 25,001–40,000 (28%); 40,001–50,000 (9.9%); 50,000–75,000 (14.8%); 75,001–100,000 (6.6%); and >100,000 (5.5%). Relationship status: single (25.8%), dating (19.8%), cohabitating (10.4%), engaged (3.8%), married (34.6%), divorced/separated (4.9%), and widowed (0.5%).
Measures
Arizona Life History Battery
LHS was measured using the Arizona Life History Battery (ALHB; Figueredo, 2007). The ALHB was developed to measure the multifaceted nature of this construct, and as such, it is comprised of several subscales. The scale contains 199 items on eight separate inventories assessing behavioral and attitudinal manifestations of LHS, with higher scores indicating a SLHS. Inventories include Mini-K short form measure of LHS (20 items), Insight, Planning and Control (20 items), Mother/Father relationship quality (26 items), Family Social Contact and Support (15 items), Friends Social Contact and Support (15 items), Experiences in Close Relationships (36 items), General Altruism (50 items), and Religiosity (17 items), α = .88.
Delinquency
The Delinquency Short Form (D-20; adapted from Charles & Egan, 2005; see also Figueredo et al., 2006) was used to measure trait delinquency/socially deviant behaviors (α = .84). The scale asks participants to indicate the frequency with which they have engaged in a variety of behavior such as “Using a weapon” and “Fighting in the street.”
LHC primes
There were three primes, FLHC, SLHC, and a neutral prime. All primes were formatted to look like a New York Times article.
Procedure
Participants completed a health demographic questionnaire, ALHB, and the D-20. After completing these questionnaires, participants read one of three primes (FLHC, SLHC, or neutral). Participants then read instructions for the Dot Game, played the game, and allocated the bonus money. Finally, participants were debriefed.
Results
Data Screening
No missing values were identified, and variables were adequately normally distributed (skew < 2.0, kurtosis < 3.0). LHC manipulation showed even splits (FLHC prime = 58, SLHC prime = 61, and neutral prime = 63). There were no univariate outliers (i.e., Zs > 3.29). One multivariate outlier was detected based on Mahalanobis distance >20.515 for a chi-square distribution with five predictors and p ≤ .001 (Case # 176). This case was removed from the data set, reducing the sample size to N = 181. No problematic collinearity was detected. There was sufficient linearity and homogeneity of variance (F max = 1.67). The residual plot indicated that residuals were normal and independently distributed.
Cheating
Cheating on the Dot Game was present (M = 0.68, SD = 0.25). Scores ranged from US$0.00 to US$1.00. Thus, some people acted altruistically and took less, whereas others took the maximum amount, leaving nothing for the (nonexistent) other player. Approximately 47.5% of people allocated more to themselves than was fair, demonstrating exploitative and deceptive behavior. Additionally, a bivariate correlation between cheating scores and the D-20 showed a positive association, r(179) = .178, p = .016. Participants who scored higher on the measure of delinquency/deviant behavior tended to cheat more on the Dot Game. The means and SDs for cheating in each experimental condition are presented in Table 1.
Means for Cheating.
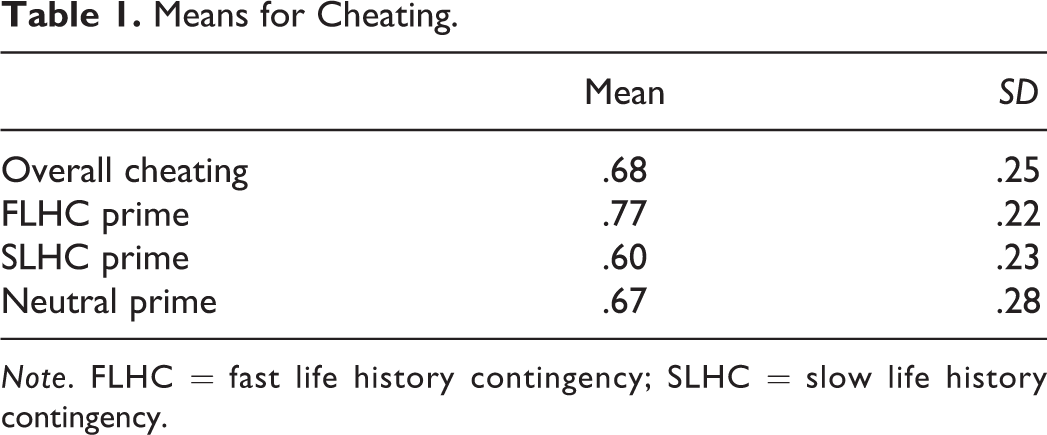
Note. FLHC = fast life history contingency; SLHC = slow life history contingency.
Multiple regression was used to test the effect of LHS, LHCs, and their interaction. The LHC primes were dummy coded with the neutral prime as the reference group. The standardized solution is presented. The overall model was significant, F(5, 175) = 7.079, p < .001; R 2 = .168, CI95 [0.061, 0.247]. Thus, this combination of predictors is expected to account for between 6.1% and 24.7% of the variability of cheating in the population. LHS significantly predicted cheating, β = −.297, t(175) = −4.243, p < .001. Specifically, as LHS increased (indicating a SLHS) by 1 SD, there was a −.297 SD decrease in cheating, and LHS uniquely accounted for 8.6% of the variance with a CI95 of [0.026, 0.172]. The FLHC prime also predicted cheating, β = .163, t(175) = 2.053, p = .042. This uniquely accounted for 2% of the variance in cheating, CI95 [0, 0.079]. The SLHC prime was not significant, β = −.141, t(175) = −1.79, p = .075, nor was the interaction between LHS and the SLHC prime, β = .009, t(175) = .121, p = .903, nor the interaction between LHS and the FLHC prime, β = .049, t(175) = .587, p = .558.
Discussion
The results of this study provide preliminary evidence for LHS and LHCs in predicting exploitative and deceptive behavior (specifically, nonviolent theft of monetary resources). Consistent with LHT, SLHSs cheated less than FLHSs. The relationship between LHS and exploitative behavior has until now only been tested through related constructs, such as criminal behavior, psychopathy, and social deviance indicators including Machiavellism (Ellis, 1988; Ellis et al., 2009; Gladden, Figueredo, & Jacobs, 2009). These findings are consistent with the evidence that FLHSs, compared to slow, tend to engage in more criminal behavior (Ellis, 1988). Thus, the current research extends past findings to exploitative behavior which is not criminal or socially deviant, providing converging evidence for LHT. Moreover, the present study extends past work by directly observing exploitive behavior. Most of the research in the area of LHS and criminal behavior has involved reports of past behavior (e.g., Brumbach et al., 2009). Our research showed LHS to be associated with an observed instance of exploitation.
This study also provided support for the role of LHCs in exploitative behavior. Specifically, the FLHC prime resulted in more cheating compared to the neutral prime. Thus, the results of this experiment converge with the findings of Brumbach et al. (2009). However, although a FLHC was associated with more exploitative behavior, a SLHC was not associated with a significant decrease. Furthermore, the effect size for the FLHC prime was very small, and the confidence interval on the effect size included zero. Thus, it is unclear whether the effect of LHCs on cheating is a reliable effect. Replicating the current study should help determine this. There was also no interaction between LHS and either the FLHC or the SLHC prime. Therefore, the relationship of LHS to exploitative and deceptive behavior did not depend on LHCs. Nonetheless, these results tentatively suggest that even adult humans may be sensitive to LHC information and that this information influences resource acquisition strategies. This study also further validates the Dot Game as a measure of exploitative behavior that can be easily administered in lab settings and over the Internet. This feature gives researchers greater flexibility in recruiting diverse samples.
Although this study provides some support for the relationship of LHS, LHCs, and exploitative behavior, one limitation of this study is the scope of the measure of exploitative and deceptive resource acquisition strategies. Specifically, the cheating task captures only one of the tactics that theoretically makeup an exploitative strategy. For example, Buss and Duntley (2008) also discuss free riding and mate poaching as examples of an exploitative strategy. In addition, there are other tactics (e.g., using violence) or other resources (e.g., mates) that were not measured with the Dot game. Therefore, the Dot Game is limited in breadth. To address this, in Studies 2a through 2c, we develop and validate a self-report measure that captures multiple behaviors that are part of an exploitative strategy.
Study 2a
To develop the items for the self-report measure, a total of 22 scenario-based questions were written to capture behaviors that would be theorized to have evolutionary implications. For example, infidelity is hypothesized to be an important cue to when a male kills his intimate partner (Daly & Wilson, 1988). Other items that have evolutionary implications included mate poaching and free riding. Pilot data indicated that phrasing items in terms of how tempted individuals would be to engage in the behaviors (rather than how likely) resulted in higher item endorsement and so this phrasing was used. The items were written to capture many different tactics (e.g., violence, threat of violence, deception) and many different resources (e.g., money, mates, a job). Group-level tactics such as coalitional warfare were not included. The items were written with just enough detail to allow participants to imagine or simulate the situation (see Table 2).
EDRASS Questions.

Note. Corresponding factors are in parentheses. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Material and Method
Participants
Data from 241 (42% male, 58% female, M age = 36.69) MTurk participants were collected. All participants had to be located in the United States, have at least a 95% approval rating, and be at least 18 years of age in order to participate. Participants were paid US$0.20.
Measures and Procedure
Participants completed a health and demographic form, the D-20 (adapted from Charles & Egan, 2005; see also Figueredo et al., 2006), and answered the 22 items of the EDRASS (items were presented 1 per page). Interspersed within the EDRASS were four questions adapted from the unethical decision-making scale (Detert, Treviño, & Sweitzer, 2008). In order to show discriminant validity, these items did not contain ethical dilemmas or exploitative behavior. An example of a nonethical dilemma question is, “Your professor/boss asks you to complete a voluntary survey. How tempted would you be to NOT do it because you’re just too busy?” We also included these items to show that similarly worded items would nonetheless differ from the EDRASS. Participants responded to the EDRASS items and the adapted items from the unethical decision-making scale using a 7-point scale (1 = extremely untempted to 7 = extremely tempted).
Results
Data Screening
Data were screened prior to analysis, all values were in range and plausible, and no missing values were identified. For outliers (based on Z score ≥ 3.29, p ≥ .001), one participant’s data were excluded based on Z = 5.4288 for the EDRASS Item 9. Two subjects were excluded based on Z = 5.2147 for the EDRASS Item 21. This reduced the sample size from N = 241 to 238. Most items demonstrated acceptable skew and kurtosis. However, because EDRASS Item 1 was negatively skewed and demonstrated a significantly larger mean (M = 4.62) than did the other items, it was removed from analysis. Because of problematic univariate distribution (skew = 3.65 and kurtosis = 14.25), EDRASS Item 2 was also removed. This left 20 items for factor analysis, and a case to variable ratio of greater than 11 to 1.
Factor Analysis
An initial exploratory factor analysis (EFA) was conducted on the remaining 20 items. Principal axis factoring was utilized, as the goal was to identify the underlying latent construct (Gorsuch, 1983). A promax rotation was chosen to allow underlying factors to correlate, as the underlying latent construct is assumed to encompass a correlated set of exploitative and deceptive tactics. The Kaiser–Meyer–Olkin measure of sampling adequacy was .868, and Bartlett’s test of sphericity was significant, χ2(190) = 2,091.960, p < .001, suggesting the data were factor analyzable. Examination of the scree plot highly suggested a four-factor solution. Examination of the pattern matrix yielded several problematic items. Item EDRASS 7 was removed due to its highest loading (on the fourth factor) of .286. Item EDRASS 22 was removed due to it not loading greater than .5 on any one factor and having consistent cross loadings greater than .2. Item EDRASS 10 was removed due to the low communality estimate (.251) and no factor loading greater than .4. The final iteration of the EFA contained 17 items.
Principal axis factoring with a promax rotation was used, and the scree plot once again highly suggested a four-factor solution (see Figure 1). Kaiser–Meyer–Olkin measure of sampling adequacy was .848, and Bartlett’s test of sphericity was significant, χ2(136) = 1731.651, p < .001. The pattern matrix with factor loadings and communality estimates for the final solution are presented in Table 3. As shown in the table, primary loadings were greater than .40, and there were no substantial cross loadings.

Scree plot from the final solution for Study 1.
Factor Loadings and Communality Estimates for 17 Items From the EDRASS, Study 1.

Note. Factor loadings less than .3 are suppressed. N = 238. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Construct Validity
To provide construct validity for the relationships of the total EDRASS (with all 17 items in order to conserve tests) with the D-20, sex and the single item, “have you ever been arrested?” were tested. EDRASS and the D-20 were positively correlated, r(236) = .387, p < .00; EDRASS and the item “have you ever been arrested” were positively correlated, r(236) = .197, p = .002; and EDRASS and sex (0 = Female, 1 = Male) were positively correlated, r(236) = .171, p = .008. Therefore, having higher scores on the EDRASS was associated with greater delinquency/criminality, having been arrested, and being male. There was a small correlation between scores on the EDRASS and the nonethical items, r(236) = .193, p = .003.
Discussion
Through principal axis factoring, the initial 22 items were reduced to 17 items. The remaining items showed a clear four-factor solution. However, several factors had less than 5 items, which according to Gorsuch (1983) is the minimum recommended number of items per factor. Therefore, new items were generated that could relate to these factors, and a new sample was collected.
Study 2b
In Study 2b, 5 new items were generated, making a total of 22 items. A new sample was collected and the analyses from Study 2a repeated.
Material and Method
Using MTurk, 236 (60% female) participants were recruited, M age = 34.72. All participants had to be located in the United States, have at least a 95% approval rating, and be at least 18 years of age in order to participate. Participants were paid US$0.20 for participating. Measures and procedure were the same as Study 2a.
Results
Data Screening
Data were screened prior to analysis, and all values were in range and plausible, no missing values were identified, and items approximated normality (skew ≤ 3.0; kurtosis ≤ 8.0; Kline, 2005). Several outliers on items were identified based on Z > 3.29. Seven scores were identified as outliers (6 scores of Z = 3.82 and 1 score of Z = 4.87) for EDRASS Item 13. Case #186 (Z = 4.87) was removed from the data set, reducing the sample size to N = 235, however, the other six cases were retained as these scores were part of a continuous distribution. That is, there was no clear break between these scores and the rest of the distribution. Although outliers were detected for other items, all represented a continuous distribution and Zs were < 4.2. As no items required removal, this left 22 items for factor analysis and a case to variable ratio of greater than 10.6:1.
Factor Analysis
An EFA was conducted on the 22 items, and, as in Study 2a, principal axis factoring was used with a promax rotation. The Kaiser–Meyer–Olkin measure of sampling adequacy was .903, and Bartlett’s test of sphericity was significant, χ2(231) = 2,721.385, p < .001. The scree plot once again suggested a four-factor solution.
The pattern matrix with factor loadings and communality estimates are presented in Table 4. Primary loadings were greater than .35, and there were no substantial cross loadings. Although several items had factor loadings below .40, these items were in the previous EFA in Study 2a and had loadings greater than this threshold, added to conceptual interpretation, and did not show substantial cross loadings. Additional solutions were explored, but none led to a more interpretable solution.
Factor Loadings and Communality Estimates for 22 Items From the EDRASS.

Note. Factor loadings less than .3 are suppressed. N = 235. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
It should also be noted that separate factor analyses were conducted for male and female participants. The results were very consistent across sex. Specifically, each analysis showed a four-factor pattern, with similar initial eigenvalues, and the same items loading on the same factors. Because separating the analyses would substantially reduce the case to variable ratio, and there was no strong evidence to suggest a different factor solution for men and women, subsequent analyses were conducted for the whole sample.
The four extracted factors were examined and the following labels were generated: First factor—coercion for sexual resources, second factor—retaliatory violence, third factor—deception and manipulation for monetary resources, and fourth factor—deception and manipulation for sexual resources. On all factors and the total score, higher scores indicated greater item endorsement. Moderate correlations between each factor are presented in Table 5. Composite scores were created for each factor and the total scale. Descriptive statistics including reliability estimates are presented in Table 6. The total EDRASS was normally distributed and highly internally consistent.
Correlation Matrix for the Four Factors of the EDRASS, Study 2b.

Note. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Descriptive Statistics for the Four Factors and Total EDRASS, Study 2b.

Note. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Construct Validity
Construct validity was assessed by testing for a relationship with the D-20, sex (0 = Female and 1 = Male), and the single item, “Have you ever been arrested.” EDRASS and the D-20 were positively correlated, r(235) = .335, p < .001. The EDRASS and sex were positively correlated, r(235) = .229, p < .001. EDRASS scores and the item, “have you ever been arrested” were not significantly correlated, r(235) = .053, p = .418. Therefore, having higher scores on the EDRASS was associated with greater delinquency and being male but not a criminal record. This provides some convergent validity to the ERASS.
To provide discriminant validity, the mean of the EDRASS (M = 2.33, SD = .93) and the mean of the nonethical items (M = 4.89, SD = 1.18) were compared and found to be significantly different, t(235) = 26.58, p < .001. This suggests participants responded to the items from the EDRASS and the nonethical items differently. Additionally, there was no correlation between the EDRASS and the nonethical items, r(235) = .037, p = .574.
Discussion
Through principal axis factoring, all 22 items showed a clear and interpretable four-factor solution of moderate to high reliability. Although men score higher on the EDRASS than do women, there was no evidence of sex differences in the factor structure. This does not imply that there are not meaningful sex differences in exploitative strategies. For example, there are probably resources that only men or only women try to acquire. However, as an empirical matter, our data did not show a significantly different factor pattern for male versus female participants. The factor pattern discovered as a result of Studies 2a and 2b was tested in a confirmatory analysis in Study 2c.
Study 2c
The purpose of Study 2c was to test the hypothesized four-factor structure of the EDRASS identified in the two previous studies as well as to further validate the measure. In particular, we were interested in examining the relationship between the EDRASS and the mating effort. Mating effort scale (MES) and the EDRASS both measure the attainment of sexual partners, thus it is of interest to see to what extent they overlap.
Material and Method
Participants and Design
The sample consisted of 237 MTurk participants (51.6% male and 48.4% female, M age = 32) who were paid US$0.20 each. All participants had to be located in the United States, have at least a 95% approval rating, and be at least 18 years of age in order to participate.
Measures
Participants completed a health and demographic form, the MES, and the EDRASS. The MES is measure of how much mating effort one allocates, with higher scores indicating greater mating effort (Rowe, Vazsonyi, & Figueredo, 1997). There is a male (α = .76) and female version (α = .69) both with 10 items. An example item from the male version is, “I would rather date several girls at once than just one girl.”
Procedure
Participants answered the health and demographic form and then based on their answer to the question concerning their sex, they were automatically presented with either the male or the female version of the MES. Finally, participants completed the EDRASS (1 item per page).
Results
Data Screening
Values were in range and plausible, and no missing values were identified. Although items approximated normality, there was some positive kurtosis greater than 2.00 on several items (skew ≤ 3.0, kurtosis ≤ 8.0; Kline, 2005). One outlier was identified based on Z > 3.29 for EDRASS Item 21 (Z = 4.49). This participant was removed, reducing the sample size to N = 236. No additional participants were removed, and other potential cases represented a continuous distribution (Z < 4.2). The case to variable ratio was 10.72:1.
Analytic Strategy
A four-factor model was specified, with 6 items for coercion for sexual resources, 5 items for retaliatory violence, 6 items for deception and manipulation for sexual resources, and 5 items for deception and manipulation for monetary resources. Latent factors were allowed to covary, and no items were selected as marker indicators. As several items showed some kurtosis, a robust estimator (Satorra-Bentler, MLM) was used. Indices of model fit were root mean square error of approximation (RMSEA), standardized root mean square residual (SRMR), comparative fit index (CFI), and Tucker–Lewis index (TLI). Based on Bentler (1990) and Kline (2005), the following values were considered as criterion for adequate model fit: RMSEA (values less than .08), SRMR (values less than .10), and CFI and TLI (values greater than .90). Additionally, based on Hu and Bentler (1999), the following values were considered close fit: RMSEA (values less than .06), SRMR (values less than .08), and CFI and TLI (values greater than .95). Analyses were conducted using MPlus version 6.
Confirmatory Factor Analysis
The initial model of the hypothesized four-factor structure was significant, χ2(203) = 378.06; p < .001, and provided the following fit indices: RMSEA = .060 (CI90 = [.051, .070]), SRMR = .061, CFI = .910, and TLI = .897. Thus, RMSEA and SRMR values suggested close fit, whereas CFI and TLI values suggested adequate or near adequate fit. All indicators showed substantial association with their respective latent factors (λ = .55 to .80), and no complex loadings were observed. Modification indices suggested improvement in the model through allowing error variances for 2 items to covary (EDRASS Item 11 and EDRASS Item 14). Only one error covariance was indicated, and both items were indicators for the same factor. Output indicated that by respecifying the model and allowing covariance between these errors, there would be a significant improvement in the model fit, Δχ2 = 24.56. Thus, the model was respecified. This model demonstrated improved fit, χ2 (202) = 356.11; p < .001, RMSEA = .057 (CI90 = .047, .066), SRMR = .063, CFI = .920, and TLI = .909. These results suggest adequate to close fit on all indices. Factor loadings and standard errors are presented in Table 7, and latent factor correlations are presented in Table 8. Means, standard deviations, skewness, kurtosis, and reliability estimates are provided in Table 9.
Factor Loadings for the Final CFA Model, Study 2c.

Note. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Latent Factor Correlations for the Four Factors of the EDRASS, Study 2c.

Note. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Descriptive Statistics for the four factors and EDRASS total, Study 2c.

Note. EDRASS = Exploitative and Deceptive Resource Acquisition Strategy Scale.
Construct Validity
To further demonstrate construct validity, the overlap of mating effort with the total EDRASS score was assessed. We also examined the relationship with the deception and manipulation for sexual resources factor, as this factor is theoretically most similar to mating effort. Using bivariate correlation, EDRASS and sex (0 = Female, 1 = Male) were positively correlated, r(235) = .239, p < .001. A regression model with the MES and sex as predictors was used in order to determine the unique relation of each predictor with the EDRASS. MES significantly predicted total EDRASS score, β = .741, t(233) = 8.16, p < .001. Thus, higher mating effort was related to greater reported use of exploitative strategies. Further, MES uniquely accounted for 20.9% of the variance in total EDRASS scores. Sex did not significantly predict scores on the EDRASS, β = .172, t(233) = 1.524, p = .129.
MES significantly predicted scores on the deception for sexual resources factor, β = .867, t(233) = 6.846, p < .001, uniquely accounting for 15.5% of the variance in this factor. Sex also significantly predicted scores on the deception for sexual resources factor, β = .378, t(233) = 2.046, p < .017, uniquely accounting for 1.9% of the variance. Thus, men and those reporting higher mating effort scored higher on the deception for sexual resources factor.
Discussion
Study 2c confirmed the hypothesized four-factor structure of the previous studies. Specifically, this study supports the hypothesis that these factors are an interrelated set of goals and tactics, constituting aspects of an exploitative resource acquisition strategy. The coercion for sexual resources factor has the goal of either directly or indirectly acquiring mates. The tactics are violence or the threat of violence. The retaliatory violence factor has the goal of retaliation due to the use of an exploitive and deceptive strategy by a conspecific. The means involve violence. The deception and manipulation for sexual resources factor has the goal of sex or sexual resources. The tactic is nonviolent deception and manipulation. The deception and manipulation for monetary resources factor has the goal of attaining monetary resources. The tactic, like the previous factor, is deception and manipulation. As there is a moderate relationship between the factors, individuals are likely use multiple strategies to exploit others.
Although men are more likely to score higher on the EDRASS, sex did not uniquely predict scores on the EDRASS with mating effort in the model. This suggests that mating effort may be driving the relationship between EDRASS and sex. Although there is a male and female version of the MES, we did not control for sexual orientation. We expect the effect of mating effort and the EDRASS to hold for both heterosexual and homosexual relationships. More importantly, it does not appear that the EDRASS and MES are measuring the same construct. Rather, there is likely a close relationship between the use of exploitative strategies and mating effort, which would be predicted by LHT. Further analysis, preferably using structural equation modeling, will be necessary to determine the nature of the relationship of these constructs and other life history traits.
Because each factor represents a different goal and tactic, it could be argued that the factors should be analyzed separately, rather than using a total score for the EDRASS. However, researchers may not be interested in differences in individual’s exploitative and deceptive behavior on one specific factor or may wish to conserve tests. In this case, it could be argued that the total score on the EDRASS should be used. An advantage of using the total score on the EDRASS is that the full scale is more internally consistent and normally distributed than any one factor. Considering these arguments and that the factors are only moderately correlated does not suggest a strong position either way.
Three separate samples suggested a four-factor structure, provided consistently strong reliability estimates, and produced evidence for construct validity for the EDRASS. Therefore, the evidence suggests the EDRASS to be a valuable measure, meeting one of the primary goals of this research. The final study returned to the question of whether LHS and LHCs influence the use of exploitative strategies as measured by the EDRASS.
Study 3
The purpose of Study 3 was to further examine whether LHS, LHCs, or their interaction predict how tempted adults would be to engage in a variety of exploitative and deceptive behaviors. As in Study 1, primes were used to manipulate LHCs. The sample included only adults. The following predictions were made.
SLHSs will have lower scores on the EDRASS factors, relative to FLHSs.
The FLHC prime will result in higher scores on the EDRASS factors, compared to the neutral prime.
The SLHC prime will result in lower scores on the EDRASS factors, compared to the neutral prime.
As in Study 1, we tested whether LHCs moderated the relationship between LHS and exploitative strategies, though no specific direction or magnitude was hypothesized.
Material and Method
Participants
Participants were 187 (42.8% male and 57.2% female, M age = 34.1, SD = 11.93) people recruited through MTurk and paid US$0.20 for participation. Additional descriptive participant characteristics include family income growing up and current relationship status. Family income growing up: <10,000 (8.0%); 10,001–25,000 (18.2%); 25,001–40,000 (23.5%); 40,001–50,000 (12.8%); 50,0001–75,000 (16.0%); 75,001–100,000 (13.4%); and >100,000 (8.0%). Relationship status: single (37.4%), dating (13.4%), cohabitating (7.5%), engaged (5.9%), married (27.3%), divorced/separated (7.5%), and widowed (1.1%).
Design and Procedure
This study employed an experimental design with one between-participant factor (LHC primes). Participants completed a health and demographic questionnaire and the Mini-K measure of LHS. After completing the questionnaires, participants read one of three primes (FLHC, SLHC, or neutral) and then completed the EDRASS.
Measures
The Mini-K (a part of the ALHB) is a measure of LHS and was chosen for its brevity (Figueredo, 2007). The Mini-K correlates well with the full ALHB (r = .77) and is reliable (α = .80). The EDRASS was also administered as a measure of the different tactics and goals used in an exploitative and deceptive strategy (α = .90).
LHC primes
The same primes as in Study 1 were used here.
Results
Data Screening
No missing values were identified, and variables were adequately normally distributed (skew < 2.0 and kurtosis < 4.0). LHC manipulation showed even splits (FLHC prime = 66, SLHC prime = 59, and neutral prime = 62). There was one univariate outlier (Z = 4.22), on the coercion for sexual resources factor of the EDRASS based on Z > 3.29. However, this represented a continuous distribution. No multivariate outliers were detected based on Mahalanobis distance > 18.467 for a chi-square distribution with four predictors and P ≤ .001. No problematic collinearity was detected. There was sufficient linearity and homogeneity of variance (F max = 1.16). Residual plots were examined and indicated the residuals were normal and independently distributed.
Main Analyses
Multiple regression with dummy coding was used. Dummy codes were used to contrast the prime conditions, with the neutral prime as the reference group. A regression model was run for each of the factors of the EDRASS, with the following predictors in the model: LHS, two LHC dummy codes, the interaction between LHS and the FLHC prime, and the interaction between LHS and the SLHC prime. 1 Each variable in the model was standardized.
Coercion for sexual resources
The overall model was significant, F(5, 181) = 2.413, p < .001; R2 = .062, CI95 [0, .117]. Thus, this combination of predictors is expected to account for between 0% and 11.7% of the variability of this factor in the population. The LHS significantly predicted coercion factor scores, β = −.182, t(180) = −2.49, p = .013. Specifically, as LHS increased (indicating a SLHS) by 1 SD, there was a −.182 SD decrease in the coercion factor. LHS uniquely accounted for 3.24% of the variance with a CI95 of [.001, .094].
The FLHC prime was not significant, β = .059, t(180) = .702, p < .483. The SLHC prime was not significant, β = −.053, t(180) = −.641, p = .523, nor was the interaction between LHS and the SLHC prime, β = −.127, t(180) = −1.449, p = .149,nor the interaction between LHS and the FLHC prime, β = −.074, t(180) = −.892, p = .373.
Retaliatory violence
The overall model was not significant, F(5, 181) = 1.574, p = .169; R 2 = .042. LHS did not significantly predict retaliatory violence scores, β = −.073, t(180) = −.985, p = .326. The FLHC prime was not significant, β = −.118, t(180) = −1.379, p = .170. The SLHC prime was not significant, β = .046, t(180) = .537, p = .592, nor was the interaction between LHS and the SLHC prime, β = −.132, t(180) = −1.479, p = .141, nor the interaction between LHS and the FLHC prime, β = .024, t(180) = .284, p = .777.
Deception and manipulation for sexual resources
The overall model was significant, F(5, 181) = 2.757, p = .020; R 2 = .071, CI95 [.001, .129]. Thus, this combination of predictors is expected to account for between 0.1% and 12.9% of the variability of this factor in the population. LHS significantly predicted deception for sexual resources scores, β = −.256, t(180) = −3.493, p = .001. Specifically, as LHS increased by 1 SD, there was a −.256 SD decrease in deception for sexual resources and LHS uniquely accounted for 6.3% of the variance with a CI95 of [.012, .135].
The FLHC prime was not significant, β = −.036, t(180) = −.428, p = .669. The SLHC prime was not significant, β = −.035, t(180) = −.415, p = .679, nor was the interaction between LHS and the SLHC prime, β = −.089, t(180) = −1.012, p = .313,nor the interaction between LHS and the FLHC prime, β = −.037, t(180) = −.447, p = .655.
Deception and manipulation for monetary resources
The overall model was significant, F(5, 181) = 3.325, p = .007; R 2 = .084, CI95 [.007, .146]. Thus, this combination of predictors is expected to account for between 0.7% and 14.6% of the variability of this factor in the population. LHS significantly predicted deception for monetary resources scores, β = −.288, t(180) = −3.961, p < .001. Specifically, as LHS increased by 1 SD, there was a −.288 SD decrease in deception for monetary resources, and LHS uniquely accounted for 8.0% of the variance with a CI95 of [.019, .155].
The FLHC prime was not significant, β = −.031, t(180) = −.377, p = .707. The SLHC prime was not significant, β = −.030, t(180) = −.357, p = .722, nor was the interaction between LHS and the SLHC prime, β = −.058, t(180) = −.668, p = .505, nor the interaction between LHS and the FLHC prime, β = −.009, t(180) = −.114, p = .909.
Discussion
Results indicated that SLHSs scored lower on average than did FLHSs on most, but not all, factors of the EDRASS. Specifically, FLHSs scored higher on coercion for sexual resources, deception and manipulation for sexual resources, and deception and manipulation for monetary resources but not retaliatory violence. In all cases, the effect sizes were small but consistent with LHT. Fast LHSs are more tempted to engage in exploitative behavior to acquire sexual or monetary resources, and they are more likely to use deception and coercion. However, LHS did not significantly predict retaliatory violence scores. The retaliatory violence factor of the EDRASS is different than the other three factors in that the use of this tactic is in response to someone else’s exploitative behavior. Thus, at least in this sample, FLHSs did not report being more tempted than were SLHSs to use violence in response to exploitation, only choosing a violence-based tactic to gain sexual resources. This does not imply that fast and slow LHSs engage in similar levels of retaliatory violence in all contexts or that there are no meaningful differences in the expression of retaliatory violence. This finding does imply that acquiring resources versus protecting resources is a meaningful distinction.
There was no evidence to conclude the FLHC prime or the SLHC prime influenced scores on any factor of the EDRASS. Thus, whether participants were shown environmental information for the development of fast or slow life histories did not have an effect on people’s temptation to engage in exploitative behavior. In addition, there was no evidence that LHS and exploitative strategies depended on LHCs.
General Discussion
The present studies extend past research by developing new measures of exploitative strategies and testing the predictions of LHT. The Dot Game is a behavioral measure of exploitative strategies that can be used online or in a lab setting. The EDRASS demonstrates the variety of tactics and goals that can be pursued in an exploitative strategy. Moreover, the EDRASS has been shown to be a reliable, flexible, and valid measure of these behaviors. Thus, one of the primary goals of this research was accomplished.
The second purpose of this research was to test whether LHS and LHCs influence exploitative strategy use. There were consistent results with LHS. First, FLHSs were found to deceptively take more money in a competitive limited resource game. This finding extends past work by directly observing exploitive behavior, rather than relying on retrospective reports of past behavior as most previous studies have done (e.g., Brumbach et al., 2009). Second, we found that FLHSs are more tempted to engage in coercion for sexual resources and deception for sexual and monetary resources. These findings confirm that life history strategists assort on traits, allowing them to pursue their particular reproductive strategy.
Effects of LHCs
In contrast to associations with LHS, there were inconsistent effects of LHCs on the use of exploitative strategies. There was a reliable but very small increase in cheating on the Dot Game in the FLHC prime condition, compared to the neutral prime condition, in Study 1. However, this effect was not replicated in Study 3 for any factor of the EDRASS. Moreover, there was no effect of the SLHC prime in either study. There may be several explanations for the small or nonsignificant effects of the primes.
The first possibility is that the primes were too minimal of a manipulation. That is, there may be a true effect of LHCs on exploitative strategy use, but the manipulation was not strong enough to reliably produce such an effect. The primes were designed to communicate relevant LHC information to participants in a news report that participants could simply read. This was a useful approach for an online study. However, these stories could have seemed too abstract to be very effective. The primes did not involve actual environmental changes. In their predictions concerning the effects of environmental harshness and unpredictability, Ellis et al. (2009) assume actual environmental changes (e.g., real changes in the population density and mortality rates). Although the primes were designed to communicate that same information, this is a rather indirect manipulation. Minimal manipulations can be very useful by demonstrating that even a small manipulation can produce an effect (Prentice & Miller, 2003). Because a very small effect was found for only one of the primes in Study 1, one could conclude that the primes were indeed too minimal. An additional consideration is that an effect was observed in Study 1 because a more spontaneously generated exploitative behavior was utilized, rather than asking participants to consciously reflect on scenarios describing exploitative behavior.
A second possibility is that the effect of LHCs could be limited to juveniles. Certain environmental information may be relevant to exploitative strategies but only during certain ages. Because the current studies were conducted with adult participants, we may not have observed reliable effects of the primes. In studying reproductive timing and life history, Griskevicius, Delton, et al. (2011) suggested that childhood may be a sensitive period in which environmental contingencies alter life history parameters. Evidence showing that stress and health vary according to childhood SES, but not current SES, is consistent with the view that there may be periods in development in which individuals are sensitive to LHCs (see Cohen, Doyle, Turner, Alper, & Skoner, 2004). In investigating the effects of harshness and unpredictability and LHS, Brumbach et al. (2009) hypothesized and found evidence that individuals who experience these conditions in adolescence were more likely to develop a FLHS in adolescence and early adulthood. Therefore, exploitative and deceptive behavior may by modified by LHCs but not in adulthood. This question is worthy of investigation. Similar experiments as used in this research but with a sample of juveniles would shed light on the importance of age when LHCs are experienced.
Research by Dunkel and colleagues found that LHC manipulations can affect willingness to be aggressive and sexually coercive. Importantly, they found these relationships in a college population (Mage being around 21). This may indicate that LHC effects on exploitative strategies are reduced among older individuals.
Implications and Future Directions
As the primes may have been too subtle, future studies should use stronger manipulations of LHC information. For example, researchers could develop a more realistic, impactful video that contains the relevant LHC information. Another direction could be to develop a measure of exploitative strategies in which the LHC information is embedded into the task. For example, participants could play a game in which they have the option of cooperating with or exploiting other players. The degree of harshness and unpredictability in the game could be manipulated to measure which strategies are exhibited. This approach has the advantage of directly connecting LHCs to resource acquisition strategies.
Future research should also develop measures of other exploitative strategies. For example, measures of coalitional warfare and other group-related tactics would expand upon the present work. Modifying the EDRASS or developing new measures to capture behaviors specific to males and females may be useful. On the other hand, we observed the same factor pattern for males and females in our studies.
Future research should also continue the validation of the EDRASS. For example, although the relationship of the EDRASS with mating effort and criminal behavior was assessed, there are many more constructs that could be associated with scores on the EDRASS. The dark triad (Machiavellianism, narcissism, and psychopathy) would be one such example. Jonason, Li, Webster, and Schmitt (2009) found that measures of Machiavellianism, narcissism, and psychopathy formed a single latent factor that they labeled “exploitative social style.” They further found this factor to be related to a short-term mating strategy. Recall that in Gladden et al. (2013) the indicators of antagonistic social strategies included two traits from the dark triad (Machiavellianism and psychopathy) as well as mating strategy. This raises the question of whether an exploitative social style and/or an exploitative resource acquisition strategy are part of an antagonistic social strategy. It would not be surprising if the EDRASS, the dark triad, mating effort, and mating strategy formed a single latent construct. However, there is a loss of specificity when focusing on these larger factors. If the goal is to specifically understand exploitative strategies or adaptations for exploitative strategies, we argue a more useful approach would be to use measures such as EDRASS that were designed to measure them directly. Additionally, unlike measures of psychopathy, the EDRASS can be used in experimental designs because it is not based on past behavior. Rather, it asks participants to consider how they feel at the moment and how tempted they would be to engage in hypothetical behavior.
A final future direction could be determining the mechanisms that mediate changes in resource strategy use. Then these mechanisms could be modeled with other life history traits to see how they function together. Dunkel, Mathes, and Beaver (2013) have examined self-control with relation to LHS, LHCs, and criminal behavior. Indeed, self-control is a prime candidate for mediating the role between LHCs and a variety of behavior including exploitative strategies. That is, LHCs may affect self-control, which, in turn, may regulate exploitative strategies.
Conclusion
Although there were limitations to the present studies, significant contributions include the development and validation the Dot Game and the EDRASS. The present research is also notable for using controlled experimental manipulation of multiple LHCs, adding to the LHT literature. Finally, the present work expands the literature on LHS and adaptations for the exploitation of resources. Most work in this area has focused on criminal or socially deviant behavior and LHS. However, an exploitative resource acquisition strategy need not be criminal. Acquiring different kinds of resources (e.g., mates and food) and deciding which tactics to use (e.g., solo hunting and coercive exploitation) is an important problem to solve and one faced by many species. How resource procurement and related tactics are affected by trade-offs in somatic versus reproductive effort is an important question. The conclusions drawn from the present studies are that life history trade-offs of reproductive over somatic effort and mating over parental effort result in greater use of coercion and deception for sexual and monetary resources. On the other hand, there is not enough evidence to conclude that LHCs affect exploitative resource procurement among adults.
Footnotes
Appendix
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
