Abstract
As the Internet of Things (IoT) is becoming the next frontier for the digital divide, we argue that access to most of the IoT and its benefits are hindered by vendor lock-in. Yet, people with an advanced set of operational skills can find creative ways to overcome vendor lock-in. In this article, we study socio-contextual dispositions to why some people are better able to capitalize on IoT benefits creatively than others. We use interview data and a novel approach to a diary study using a mobile application among 30 households. By focusing on vendor lock-in against the interplay between operational skills and creative IoT uses, we find those with the least access to IoT benefits are users who mainly task-oriented and consider IoT tools to solve specific problems. Those with a more play orientation are better positioned to access IoT benefits and further develop their operational skills.
Introduction
The Internet of things (IoT), as a network of interconnected ubiquitous everyday objects (such as everyday household devices, wearables, and other biometric trackers) analyze data about their environment, communicate these data with other users and objects, and make autonomous data-based decisions. The IoT can provide new functions and services to households and individuals (Aliero et al., 2020; Atzori et al., 2010). For example, when the doorbell rings, lights flash in a different color but only if music is playing above a certain volume; locking the front door also switches off electronic devices and lowers the temperature on the central heating; solar panels switch on the washing machine when the sun is out and the window shades are activated; and, when a person leaves to go on vacation, lights work together to simulate natural activities in the evenings as a security measure. With operational proficiency and creativity, people can connect IoT devices to one another and tap into endless possibilities for use and function, in theory.
However, in practice, users are confronted with limitations of IoT ecosystems related to vendor lock-in, which occurs when differences in software or hardware infrastructures make interconnectivity between IoT devices from different brands difficult. Vendor lock-in is caused by competitive market relations that prevent consumers from migrating to another competitor due to either financial costs or the costs of having to relearn and re-personalize products and services (Amit and Zott, 2001; Smith et al., 1999). Vendor lock-in can be a software issue when people try to standardize their IoT to a single operational system (Pal et al., 2018). For instance, a smart lock and doorbell are tied together with Google Home, but heating and lights are installed on Apple’s home assistant (HA). In such cases, navigating through various apps and settings can take more time and effort than the actual physical button presses. Additionally, IoT hardware is plagued by interoperability issues, such as differences in network radiofrequencies (Noura et al., 2019). People, who might want to extend their smart light setups by adding new or alternative brands, also require different connection hubs and additional mobile applications. In other words, competitive market dynamics are likely to hinder access to IoT potential.
While some people experience the limitations of the IoT, while others find creative solutions to circumvent vendor lock-in. In the current contribution, we iteratively examine the interplay between creativity and operational skills as an antidote to vendor lock-in. Creativity and playfulness beyond task-oriented usage are crucial for stimulating digital skills (Robinson, 2009). Simultaneously, operational skills are needed to explore digital technologies and maximize their outcomes (Van Dijk and Van Deursen, 2014). We explore inequalities in IoT potential more specifically by asking:
Why are some people able to capitalize on the potential benefits of the IoT creatively, while others are hindered by vendor lock-in?
As people are hindered by vendor lock-in to varying degrees, we argue that vendor lock-in is an important issue to consider from a digital inequality perspective: the key component for benefiting from IoT, digital skills (Van Dijk and Van Deursen, 2014), determine the degree to which vendor lock hinders use and thus outcomes of IoT use. Moreover, the operational skills that relate to vendor lock-in often concern creative practices that emerge from everyday IoT practices. We approach creative IoT use as a concept that has relational prerequisites, namely, the metaphorical concepts of “social proximity” (distant–close) and “social warmth” (cold–warm). Experimental research shows that these metaphors are grounded by physical and perceptual experiences (IJzerman et al., 2014; Barsalou, 2008). This means that creative IoT use reflects one’s relation to their device and their socio-structural environment rather than following distinct definitions for creative use. We introduce these metaphorical prerequisites for creativity in IoT use with a novel diary study using a mobile application among 27 participants for 6 months. The diary study is embedded in a larger study where we followed and interviewed 30 households for 15 months.
In the next section, we discuss vendor lock-in, social proximity, and social warmth as they relate to our diary measures. Subsequently, we discuss methodological considerations for selecting our participants, designing our diary application, how we extracted three factors out of our diary data to guide our interview data, and our iterative process of data analysis. In the “Findings” section, we illustrate the factors that were identified through the diary study using interview data.
Theory
The vendor lock-in problem
Most IoT systems only give access to devices of specific manufacturers, such as the Philips Hue ecosystem for smart lights, which is only compatible with Philips light bulbs (Hilbolling et al., 2021). Consequently, the interoperability between IoT devices is mostly lacking. While the main advantage of open IoT systems and interoperability between IoT devices is that it can complement core functions of devices with add-on functions developed by third parties, there are several downsides for manufacturers. From a market perspective, open IoT systems increase competition because IoT data become increasingly valuable (Mosterd et al., 2021). Meanwhile, the lower quality of third parties can harm the integrity and reputation of the core device, resulting in a more costly coordination between IoT manufacturers. Especially, when it relates to security and privacy risks (Atzori et al., 2010). Moreover, for IoT manufacturers, open IoT systems can cause difficulties regarding user contracts-and-agreements (Mosterd et al., 2021).
However, from a user perspective, also resulting from discussing interoperability of the IoT with our participants, the lacking interoperability in IoT systems emerges as a vendor lock-in issue, for instance, when people try to standardize their IoT to a single operational system (Pal et al., 2018). With lacking interoperability standards in software and heterogeneous sets of IoT devices, complex IoT systems can lead to low compliment quality. Additionally, IoT hardware has interoperability issues caused by differences in network radiofrequencies (Noura et al., 2019). Therefore, IoT users can feel “locked-in” with the brands they have come to use. Vendor lock-in describes the market relations where migrating to different manufacturers becomes too costly or strenuous to relearn or re-personalize (Amit and Zott, 2001). Likewise, expanding IoT systems is more strenuous with lacking interoperability standards and more costly when core functions of IoT devices have poor complement qualities for add-on functions. Consequently, as people are hindered by vendor lock-in to varying degrees, we argue that vendor lock-in is an important issue to consider from a digital inequality perspective.
The creativity antidote
While vendor lock-in has been identified as a hindering factor for IoT use (Aliero et al., 2020; Noura et al., 2019; Pal et al., 2018), its effect in shaping digital inequalities is understudied. We aim to fill this gap by focusing specifically on the interplay between creativity and operational skills to overcome vendor lock-in. Ignatow and Robinson (2017) emphasize the importance of creativity and playfulness with digital technologies with a framework inspired by Bourdieu. This framework explains differences in the internalized digital habitus when using the Internet as a necessity versus a luxury (Ignatow and Robinson, 2017; Robinson, 2009). Bourdieu (1984) argued that due to limited access to economic resources and temporal urgency “necessity imposes a taste for necessity which implies a form of adaption to and consequently acceptance of the necessary” (p. 372). A taste for necessity becomes deeply ingrained in one’s lifestyle, people who internalize such a taste also develop stronger feelings against squandering. Consequently, rather than seeing implicit benefits, such as investing in social capital with engagement parties, a taste for necessity prefers the practical or technical. The antithesis to a taste for necessity is formulated by Bourdieu (1998, 2000); as an ideal academic habitus. The academic habitus is a contrasting disposition that allows someone to divulge in activities that people constrained by urgency and necessity perceive as wasteful. Rather, it describes a playful interest, after Plato’s skholé, distanced from necessity and urgency but allowing oneself to be interested in problems that “serious and truly busy people” ignore (Bourdieu, 1998: 128).
Research on the digital divide has been prolific in studying gaps between access, skills, use, and outcomes (for a review, see Scheerder et al., 2017). Likewise, Robinson (2009) showed how inequalities in Internet-related skills originate in inequalities of access but ultimately emerge from cultural values related to total life contexts. She found two versions of an information habitus: a task-oriented information habitus common among the disadvantaged—enacting a taste for necessity—and a contrasting playful information habitus common among upper-middle-income families. Just as squandering engagement parties are indirect investments of social capital, playfulness and creativity with digital technologies indirectly promote skill development (Ignatow and Robinson, 2017). More importantly, those with a taste for necessity do not acquire the same skills and benefits as those engaged with a playful interest in digital technologies.
To overcome the hindrance of vendor lock-in with IoT devices, we consider playfulness and creativity investments that stimulate operational skills and help actualize a greater potential for IoT use. As the IoT is designed to work less visibly and more autonomously after the initial setup, operational skills may not be considered to have an effect in the long run (Van Deursen and Mossberger, 2018). However, van der Zeeuw et al. (2020) showed that with minimal operational skills, people still find proficient uses with the core functions of their IoT devices, whereas with more operational skills people use more advanced settings and add-on functions through third-party apps. The most operationally advanced users exploit IoT devices by modifying software scripts or hardware to redesign the original use of open IoT systems or they open closed systems themselves.
Prerequisites of play
For creative use of the IoT, we consider two prerequisites based on Lakoff and Johnson’s (2008) notion that metaphorical concepts correspond to everyday basic activities and experiences. First, experiencing the IoT as distant devices that work autonomously presumably does not stimulate exploration or playfulness that leads to creative uses. Therefore, IoT users need some degree of closeness to their devices to operate them, be creative with them, and in turn, develop their operational skills to lessen the hindrance of vendor lock-in. Feelings of social proximity indicate attachments to persons, objects, or experiences that are not necessarily at present (Liberman et al., 2007; Williams and Bargh, 2008). To depict social proximity, we use Elias’ (1978) idea of figurations. Figurations are networks of people but emphasize changing patterns of social and physical relations rather than their topology; they are the “flexible latticework of tensions” between those who are interdependent on each other (Elias, 1978). Figurations are generally used to study longer periods of time (e.g. Elias, 1994 [1939]) and focus on macro-processes spanning centuries or decennia (Mennell, 2014; Wouters, 2007). In our diary study, we aimed to encapsulate the flexible latticework of interdependencies by focusing on human-IoT figurations rather than human-to-human figurations with a micro-approach. By measuring the distance of a connection over time, we add the changing quality of a connection in figurations. Hence, we take figurations to indicate changing notions of proximity (e.g. feeling more dependent on IoT devices for comfort), according to the spatial orientations we give to properties in our environment (Lakoff and Johnson, 2008). The main difference between human figurations and human-IoT figurations is that with the latter feelings of attachment are in one direction, as most devices do not (yet) feel. Still, users need to operate their IoT devices to experience their benefits and are interdependently attached to their IoT devices by operational necessity; through practices or the cognitive strains that the IoT puts on its users.
Second, users should consider their IoT devices to be more than “just a machine” that fulfills its core functions. Experiments in embodied realism showed that purely functional and instrumental competences are often considered cold whereas people, experiences, and objects are described as warm when they signify competences of creativity (IJzerman et al., 2014; Fiske et al., 2007). Likewise, warmth is a quality shown to be associated with playfulness in people, experiences, and with objects (Goodwin et al., 2014; Kouchaki et al., 2019). Therefore, we add social warmth as second quality to the connections in human-IoT figurations. We consider warmth as a metaphorical prerequisite to indicate the added emotional value that fosters playfulness and creative use over its core functions. Our diary study, in effect, is a pragmatic yet simplified approach to both figurations and human–object relations.
Methods
Interview data
The interview data were collected during a 15-month study among 30 Dutch households with IoT devices. Via flyers and mailing lists, we recruited participants with at least one IoT device in their household (e.g. smart lights, thermostats, doorbells, locks) and preferably at least one device that measures biometric data (e.g. activity trackers). Although these selection criteria proved rather constrained in 2019, we still aimed to maximize the variation in our participants by household size, number of IoT devices, rarity of IoT devices, educational level, field of work, or social influences by neighboring participants, family, and colleagues. We used no other predefined socio-demographic categories to limit our assumptions (Latour, 2005). Participants were rewarded 400 euros for their contribution. During the 15-month study, we interviewed participants five times on different themes. One theme was dedicated to feelings of creativity and playfulness with IoT devices. We asked participants if they could be creative with their IoT devices, if they could think of any uses other than those intended, and if their IoT contributes to an emotional atmosphere or ambiance. Most of the interview data were related to this theme, but answers overlapped with other interview themes. The other four themes concerned IoT adoption, economic incentives, and rationalizations, shifting power balances and responsibilities, and data and privacy. The first author conducted all interviews, made extensive memos of the interviews, and transcribed and analyzed the data during the research process. We used abductive analysis with increased attention to surprising findings or gaps in established theories (Tavory and Timmermans, 2014), and focused our attention to vendor lock-in. As an inductive element for data analysis, we used the method of constant comparison from grounded theory, by circulating incidents and cases in comparison to concepts (Glaser and Holton, 2004). To saturate our findings, we used a factor analysis described below. Then, in an iterative process, we used our preliminary findings and relevant theory to substantiate subsequent interviews.
Figuration diaries
During the 15-month research project, participants used a mobile application as a 6-month diary study. The diary study aims to group participants by their views on metaphorical prerequisites of social proximity (close–distant) and warmth (cold–warm) rather than using preconceived notions of creativity. Complementary to our goals for abductive analysis (Tavory and Timmermans, 2014), this statistical method acts as a guiding tool to highlight otherwise overlooked and surprising findings. We developed a mobile phone application because it had two main advantages. First, it made our diary study less demanding. Diaries require a long-term commitment of participants, who often experience fatigue and drop out (Jones and Woolley, 2015). Participants were asked to fill in a figuration diary once every 2 weeks because we anticipated small changes in IoT use over time (e.g. thermostat changes when weather changes). We send notifications and nudges to help participants remember to fill in their diary. Participants could immediately fill in the diary without using other material (e.g. pen and paper). The application also logged when they accessed their diaries. Second, participants can find it challenging to repeatedly add entries with value and—especially when typing is slow—they have trouble with the written form (Fitt, 2018). Like scales that use faces to reflect pain intensity (Tomlinson et al., 2010), metaphors are indeterminately used by our participants without writing, yet grounded in intersubjective experiences. Metaphorical concepts are intuitive to use, but they are not necessarily intuitive to define in a numerical or linguistic format. By utilizing the “drag & drop” mechanism of touchscreens, we aimed to bridge this gap, while also reducing the hindrance of scrolling and lengthy questions in mobile diaries (García et al., 2016). Social proximity was indicated by orbits on which participants could drop items. Social warmth is indicated by color—blue indicates cold and red indicates warm. As a starting exercise, we asked participants to first define metaphors of social proximity and warmth for themselves by applying them to other household members when they filled in their diaries, and then try to extend their definitions to their IoT devices. To guarantee their privacy, we removed household members from the analysis. Additionally, we asked respondent to place devices together if they felt they were connected, interoperable, or otherwise used together. Participants first used the app in the first author’s presence to ensure the instructions were clear. After 3 months, we conducted a mid-term evaluation of the diary followed with the interviews on creativity and playfulness.
Figure 1 shows the steps for filling the diary. At the top of the application, participants saw the title of the study “Internet of Things in a social context,” and the middle bar shows the last part of an explanation emphasizing their own experiences. After receiving a notification to fill in figuration diary, they saw screen (a) in Figure 1, with their devices on the outermost orbit. They could place their items with a “drag & drop” mechanism onto orbits to represent social proximity. With the plus (+) button at the bottom, screen (b) would pop up to add an item. Participants were asked if the item would be another person or device, name the item, and indicate how warm this item felt to them on the gradient from blue (cold) to red (warm). Warmth is indicated by the connected line shown in screen (c) along with the device’s location.
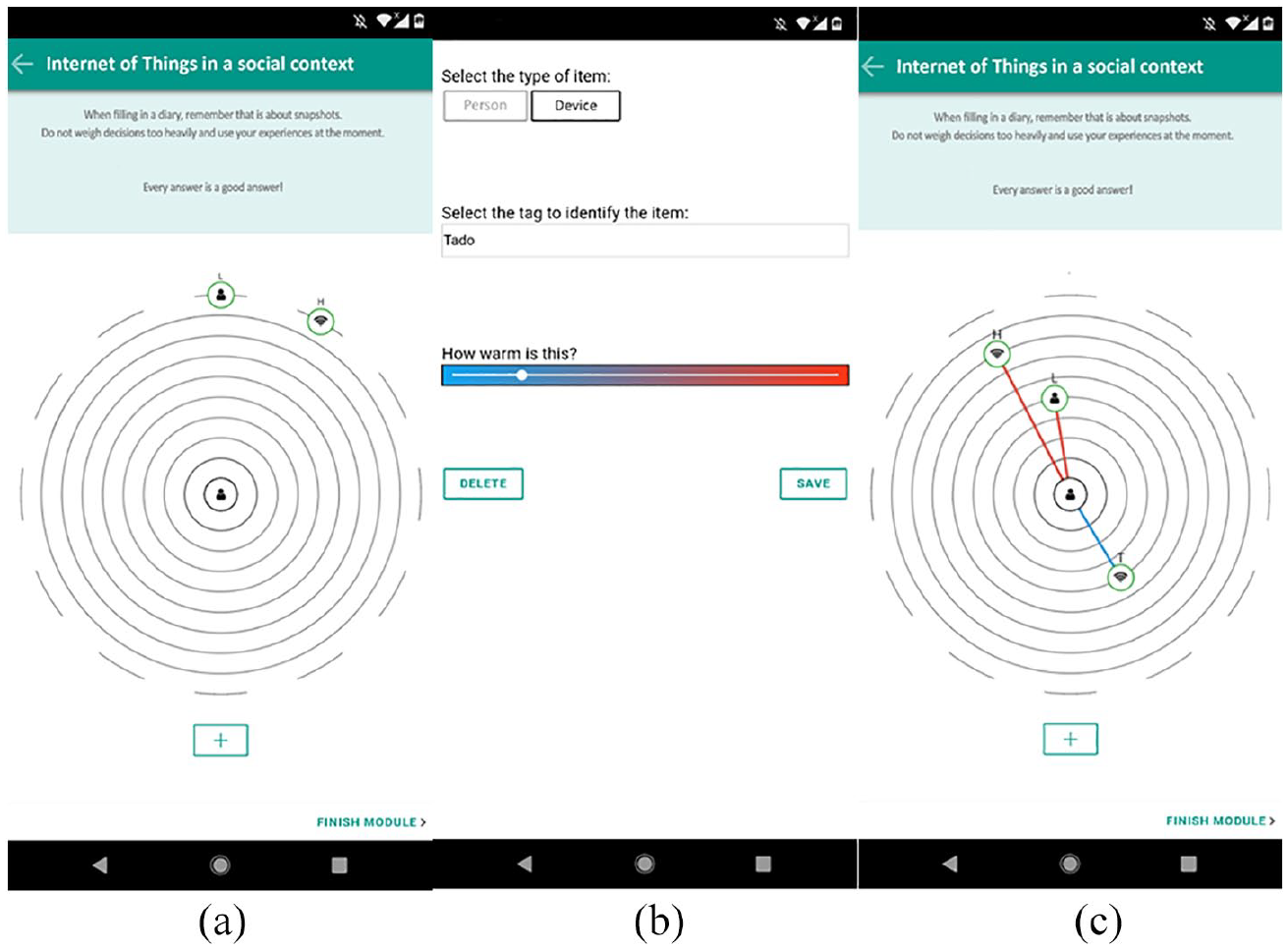
Setting up a figuration diary: (a) Start up with previous items. (b) Adding an item. (c) Placing the items on orbits.
Of the 30 participants, 27 made at least 10 entries into the diary app, and these were used for the analysis. Three participants had difficulties with their phones which were unresolvable.
Measurements and analysis of the diary study
The scales for the metaphorical prerequisites of social proximity and warmth were maximized to the size of common mobile screens. Social proximity was measured on an orbital scale from 1 to 8 (ninth orbit was reserved for inactive devices, like a “never” option). Social warmth was measured on a larger scale from 1 (blue) to 11 (red) to maximize the effect of the gradient. After using Shapiro–Wilk’s criterion to reject normality if p-values are less than .05 (Shapiro and Wilk, 1965), social proximity (p = .53), and social warmth (p = .10) were transformed to z-scores for comparability. As a third and fourth measurement, we were interested in how much scores for social proximity and warmth change. Therefore, we took the standard deviation of each device and then calculated the average standard deviations over the devices in both measurements to achieve commensurability between people with fewer or more devices.
Finally, we used an inverse principal component analysis as a guide to group participants with similar viewpoints toward their IoT devices. Stephenson (1935) proposed clustering participants rather than variables by transposing the data table, which has been a staple in Q methodology (Watts and Stenner, 2012). While Q methods usually conform to a pyramid-shaped distribution of statements, Watts and Stenner do suggest differently shaped distributions and let participants freely assign (multiple) items to ranking positions; without violating linear assumption of correlation (Kline, 2014). For factor reliability, we extracted factors with at least four factor loadings greater than .60 (Guadagnoli and Velicer, 1988) and an eigenvalue higher than 1.00 as per the Kaiser Guttman criterion (Guttman, 1954; Kaiser, 1960). A varimax rotation extracted three factors that met these criteria, which are shown in Table 1. The first factor had an eigenvalue of 13.67 and explained 50.61% of the variance. This factor grouped participants with common IoT uses by average proximity and warmth. The second factor had an eigenvalue of 9.07 and explained 33.59% of the variance; it grouped participants with a higher score for proximity and a lower score for warmth. The third factor had an eigenvalue of 4.30 and it explained 15.80% of the variance; it positioned participants with a lower average standard deviation for social proximity and warmth against participants with a higher standard deviation.
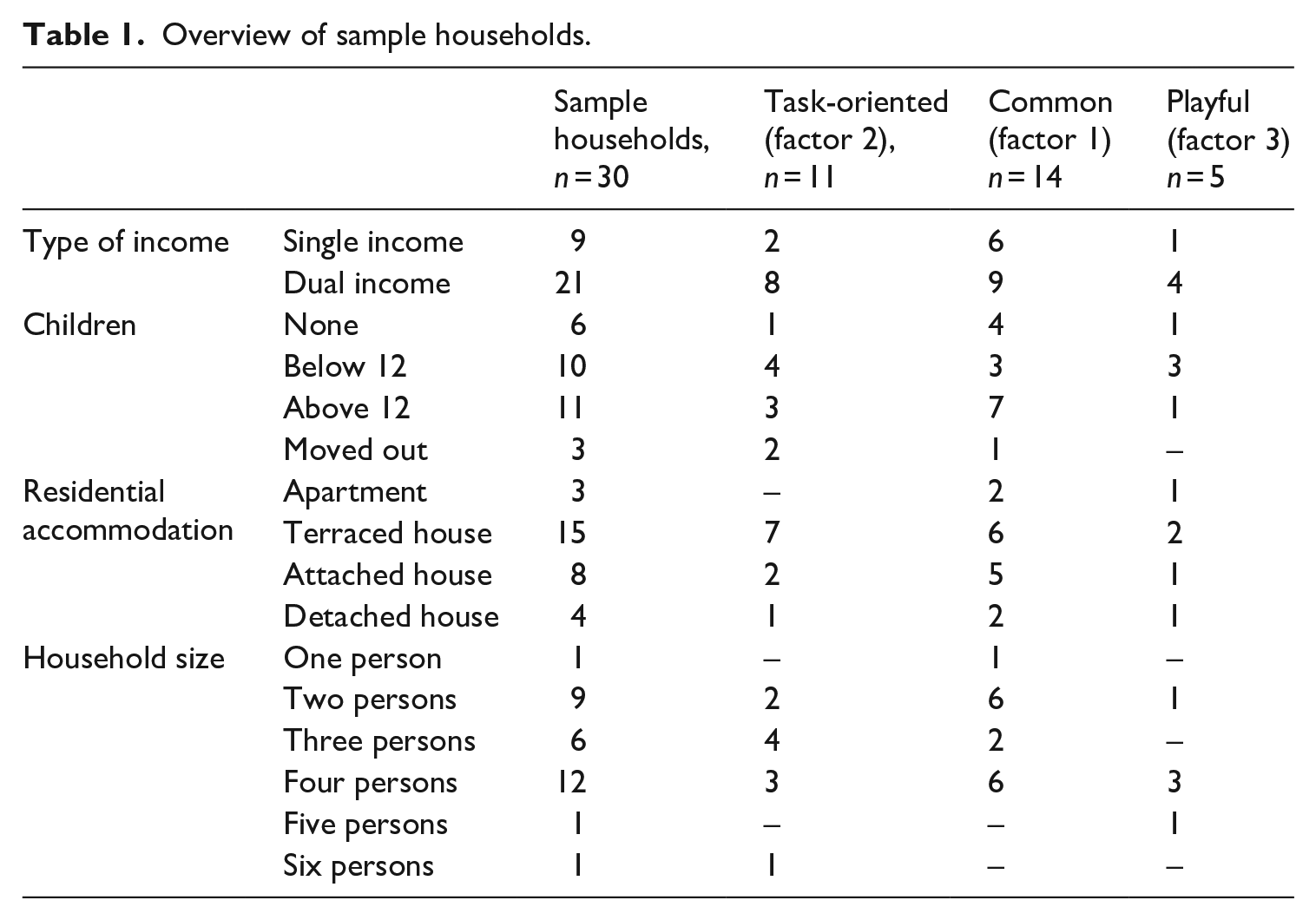
Overview of sample households.
The method does have its limitations. Foremost, the statistical power certainly does not warrant conclusive remarks from our sample to a larger population. Second, we selected these variables beforehand which make the resulting factors predictable. However, the strength of this method is that it guides us to group participants together without relying on interviews alone. As a result, participants are clustered in closer alignment according to their viewpoints on IoT use with extracted factors. The reverse also occurred, where two participants strongly described their IoT devices as cold and distant during the interviews, while their diaries showed otherwise. In these two cases, we followed the interview results. Two of the remaining participants shared viewpoints with factor 1 and the third with factor 3. Moreover, diary data have strength in illustrating polarizing differences in user profiles. In the findings, we show participants with higher factor loadings to illustrate variations in uses. In addition to social proximity and social warmth, we also found the location of IoT devices on the orbits to be important to depict interoperability. This has been visualized by replicating their most occurring figurations.
Findings
The issue of vendor lock-in: the task-oriented IoT
The figuration diary in Figure 2 shows the boxplots of the IoT devices as viewed by Ash, a married and middle-aged father of two girls. In interviews, Ash initially seems to approach the IoT as a hobby-like activity. His figuration diaries, however, prompted a revision of the interview data to acknowledge what sets him apart from other hobbyists—namely, the absence of playful or frivolous tinkering with IoT hardware or software. N denotes Ash’s Nefit thermostat. The minimum distance, indicated by the rectangle, is only 6.00, and the maximum distance is 8.00. Moreover, to Ash, his Nefit thermostat is a cold device, indicated by the blue color. Ash’s KlikAanKlikUit system, denoted by K in Figure 2, is blue and cold as well. KlikAanKlikUit is an open Dutch home automation platform consisting of multiple devices connecting electrical outputs and appliances (e.g. lights) to the Internet. While cold, the KlikAanKlikUiT system is slightly less distant, with a min of 5.00, and as indicated by the dot in Figure 2, the third quartile is more variable in proximity. In contrast, a smart Internet protocol (IP) camera for security denoted by C has the smallest standard deviation. Overall, all IoT devices are continuously placed distant from the user and described as cold. Figure 2 also shows that the IoT devices are placed distant from one another.
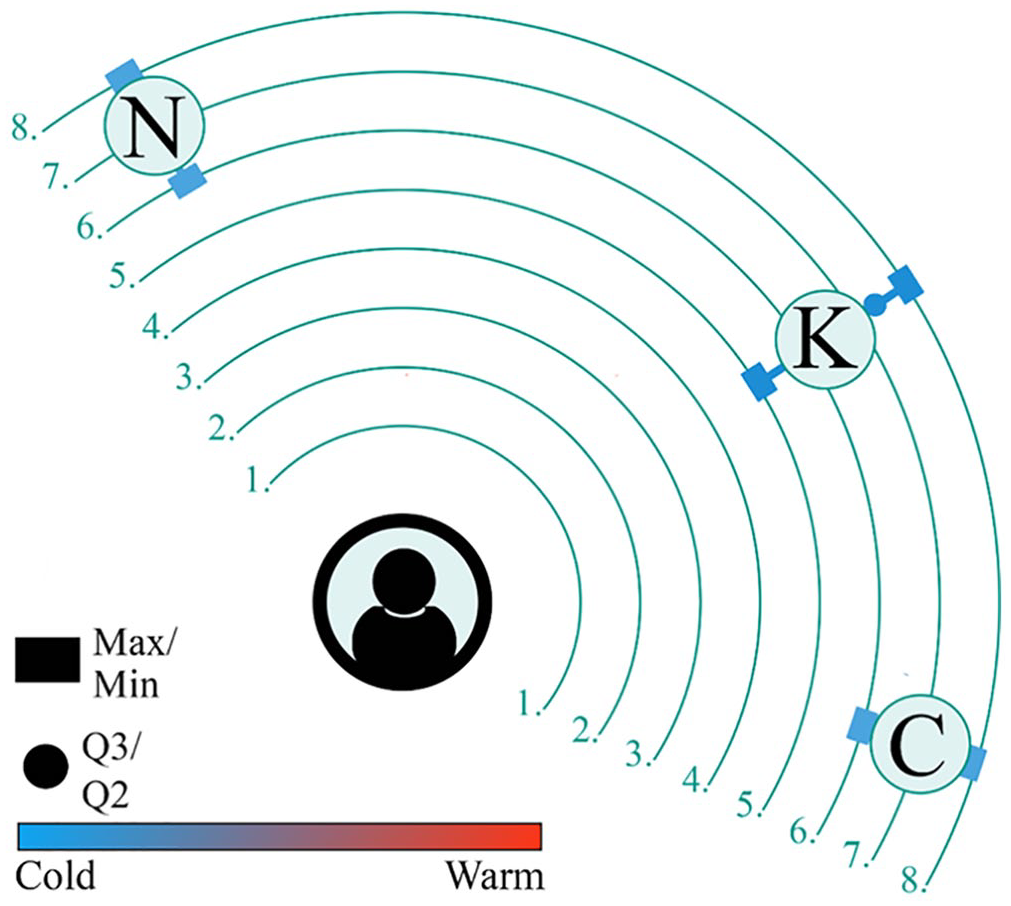
IoT as tools.
During the interviews, IoT users with figuration diaries like that of Ash in Figure 2 were specific in pointing out how the IoT should be functional. They prefer their IoT to be unnoticeable. However, as much as IoT devices should be functional, users, such as Ash do enjoy functional devices. A similar viewpoint can be found with Thomas, who has a smart thermostat and a Polar activity tracker. Thomas explains,
To me they are just devices, they are tools. But I am someone who loves tools. Things must be functional. Well, if they are beautiful also, I mean, I have a coffee machine which I think looks nice, but that is in sight. It is nice if it is also beautiful, but otherwise tools just have to fulfill their function well. It doesn’t have to feel nice or warm to me.
To users like Thomas, aesthetics come second to the primary concern that his IoT has a core function to fulfill, that is, there is a necessity to its use. However, a wider spectrum of core functions with an IoT device can still be preferable. Thomas continues,
I do always check which things are possible, though. And I would rather choose a device that offers a wide spectrum of possibilities of which I only pick a piece. Because then maybe I can pick up other pieces later if I want to. Well look, with my sport watch you can go very far in the interface and create all kinds of sports programs and add training programs. So you can use that creatively. But that is not the way I use it, because it is outside my field of interest.
What troubles Thomas is whether his IoT devices can fulfill functions in the future or if being locked-in now could ultimately cost more later when switching devices. Moreover, such a task-oriented perspective places the potential of use with the core functions of the device—as a whole and separate tool—rather than accessing its networked potential as part of an IoT system.
Other IoT users show a similar interest in the core functions of IoT devices but prefer the directness of using the IoT. While this notion contrasts with selecting devices for having broader potential, it is similar in task orientation of IoT devices. This is the case with Arthur, who has a wide variety of IoT devices, including a smart doorbell, a smart lock, two hardware setups for his lamps (the open KNX and the closed Philips Hue), and various connection hubs. However, Arthur still prefers the IoT for its functionality and, as he explains, preferably only that:
It just has to work, and it has to do what I bought it for. But it is not like I spend six hours going through the menu. That is not the case. Let’s say I want something, I look for a functionality, and then I look for a device that can be used for that. And then it is not the case that I will also use all those additional functionalities. It’s more like, it has to do what I want, and that’s that.
Here, the potential of the IoT device is solely related to the solutions it can offer. While both Thomas and Arthur consider a task-oriented necessity for their IoT devices, users, such as Thomas, look for more potential in its core software functions. Users, such as Arthur, on the other hand, find this cumbersome and prefer a direct interface. That is, IoT devices are considered solely to provide solutions to current or future problems.
The trouble with choosing devices solely based on task orientation is that, as Ash puts it, “devices do not talk to each other.” Especially when using devices from different manufacturers, vendor lock-in hinders interoperability. As a result, and as shown in Figure 2, Ash’s devices are relatively separated from each other. This problem is described in more detail by Arthur:
Well, how do you make sure . . .? Imagine standardizing it on Apple home kit, and then you pick up a doorbell, but it works with Google and not with the home kit, and vice versa. There are also products that do not work together. How do you integrate KNX . . .? Well, you can go on like this. There is no overarching standard. I think that’s the problem, not the device itself. Usually, that is very simple. But to have everything talk to each other and just get one system where you don’t actually have to do anything. That is difficult!
Choosing the core functions for specific everyday task orientation of IoT devices rather than IoT systems, as described by Thomas, Arthur, and Ash, uncovers the main issues of vendor lock-in. Vendor lock-in gives users, such as Thomas, a reason to seek the greatest potential within the device. This is usually a costlier option, and in effect, the costs of switching become higher. Another option is to select devices that are chosen solely for specific functions. However, vendor lock-in prevents the use of interoperability standards like meta-software to operate the IoT (Mosterd et al., 2021). This option would require more operational skills to use and integrate IoT devices within the household context.
Locked-in creativity: finding different uses than intended
A more common use is shown in Ellen’s figuration diary in Figure 3. Ellen uses the same Nefit thermostat as Ash but gives it a warmer evaluation and positions it closer to her with the minimum at 4.00 and second quartile at 6.00. She occasionally forgets to lower the thermostat, so that, an Internet-connected thermostat can be a great help. Even warmer, indicated by the red color, is Ellen’s Fitbit activity tracker like Thomas’ Polar, used to track her sleep, monitor her heart rate, and count her steps. Used daily, Ellen placed her Fitbit close to her and relatively warm. Moreover, both devices are standardized to Apple’s software environment.
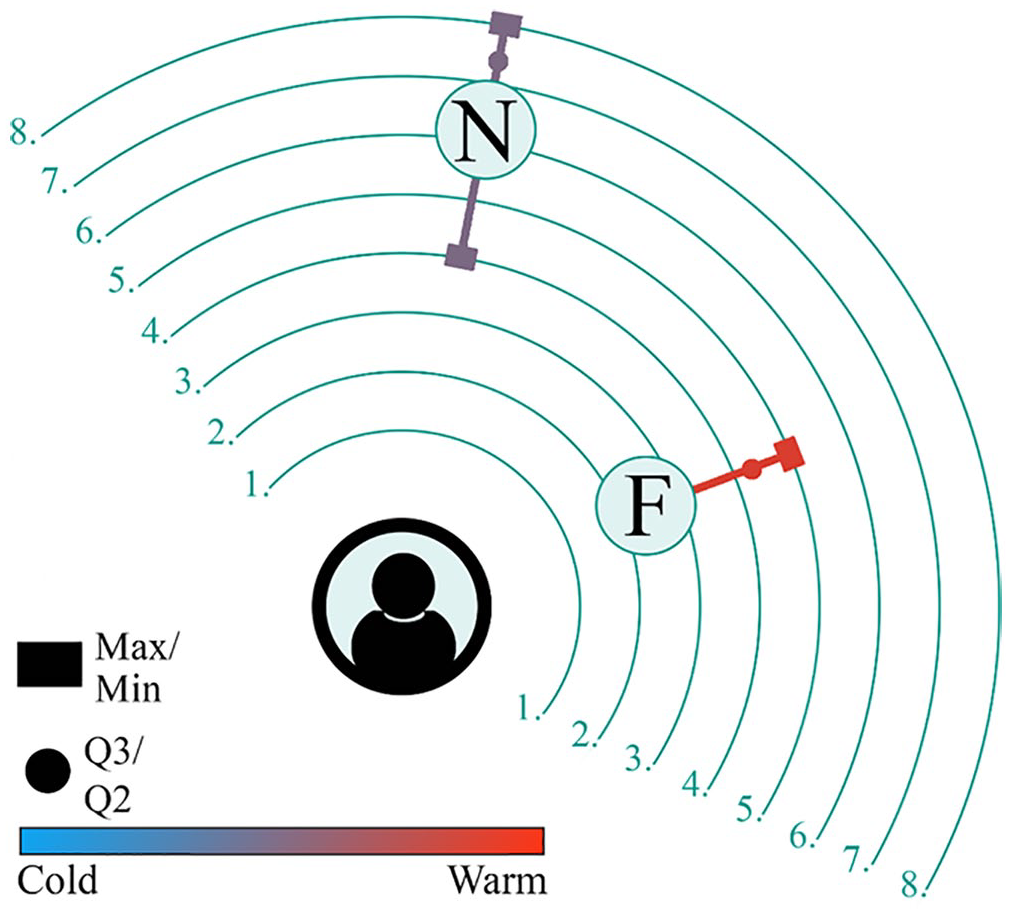
Common IoT use.
While everyday IoT devices are generally limited in their creative uses, IoT users, such as Ellen, have found additional core functions on their devices which are different than they initially expected. However, ease of use appears to be an important factor to stimulate creativity. Ellen, who praises Apple products for their stability in the interviews, explains how interoperability standards in software are inviting and allows for the exploration of additional functions:
When I look at the app, it is all pretty self-explanatory. In the past, you could still break something if you pressed something, but on an iPad, you can just push and if you don’t want something, you just go back. Nothing can go wrong. You can just turn on something to see what happens. For example, recently, my daughter was in the shower for very a long time. So, we thought about the app and if you could just turn off the hot water. Well, I looked with the iPad, my husband with the iPhone. “How are we going to do that?.” “Oh I can set this up.” “Oh here is the button for the hot water.” ((Screams: mimicking daughter)). “Hey it works.” So yeah, you can just discover how things work in a playful way.
Ellen’s perceived stability of Apple products gives her more confidence in applying basic operational skills and adds a degree of play-oriented IoT use. The downside is that she uses a relatively closed software environment that is generally more expensive and, in effect, more susceptible to vendor lock-in. Moreover, Ellen’s operational proficiency is mediated by her familiarity with the limited environment of Apple products. However, for people, such as Ellen, this vendor lock-in inspires confidence, which stimulates exploration and finding creative solutions.
Similarly, the ease of use and system integration that comes with vendor lock-in can inspire reusing devices for applications that differ from their intended core functions. Such is the case with Joan, who used an IoT device as a smart solution for an older product. Like Ellen, Joan, and her partner are common IoT users, as they have a Fitbit and a series of Philips smart products. One of these products is a Philips power plug, advertised to connect normal lights to Phillips Hue software. However, Joan uses the plug for an old-fashioned radio instead. As Joan explains,
We have not had this smart power plug for very long, and we had that radio there for a long time, but we never actually used it. Well, because you have to get up each time to use it. Now we really use it a lot. We actually had the plug connected to the robot vacuum cleaner at first but that just was not practical. So, we opted for the radio and I must say we really use the radio a lot more now.
Being familiar with one software standard generally improves the operational ease for IoT devices. Consequently, as Joan demonstrates, the ability to shift IoT devices around to different applications is based on one’s play-oriented ability to explore unexpected practical matters. The ease of exploring functions and applications appears to depend on one’s familiarity with the software standards, especially when operational skills are limited. As such, the locked-in creativity experienced by users, such as Ellen and Joan, are expressed in their confidence in exploring the potential of IoT devices.
Creativity versus lock-in: do-it-yourself work-arounds and personal solutions
Samuel’s figuration diary, shown in Figure 4, is distinct by its larger standard deviations for IoT devices. This is typical for IoT users who constantly update and tweak their IoT systems. Samuel is a young adult who lives with his girlfriend and considers his interest in IoT devices a hobby. What stands in out Samuel’s figuration diary in Figure 4 is the distance, location, and color of Samuel’s Google Home device (G) compared to his other devices. This Google Home device is often used as a central connection hub. Instead, Samuel found an alternative in HA, an open-source hub like Ash’s KlikAanKlikUiT, to connect with his harmony (H), a programmable remote control, and smart lights (L) from Philips and Ikea. Consequently, Google Home is considered as cold and distant, whereas HA is warm and close.
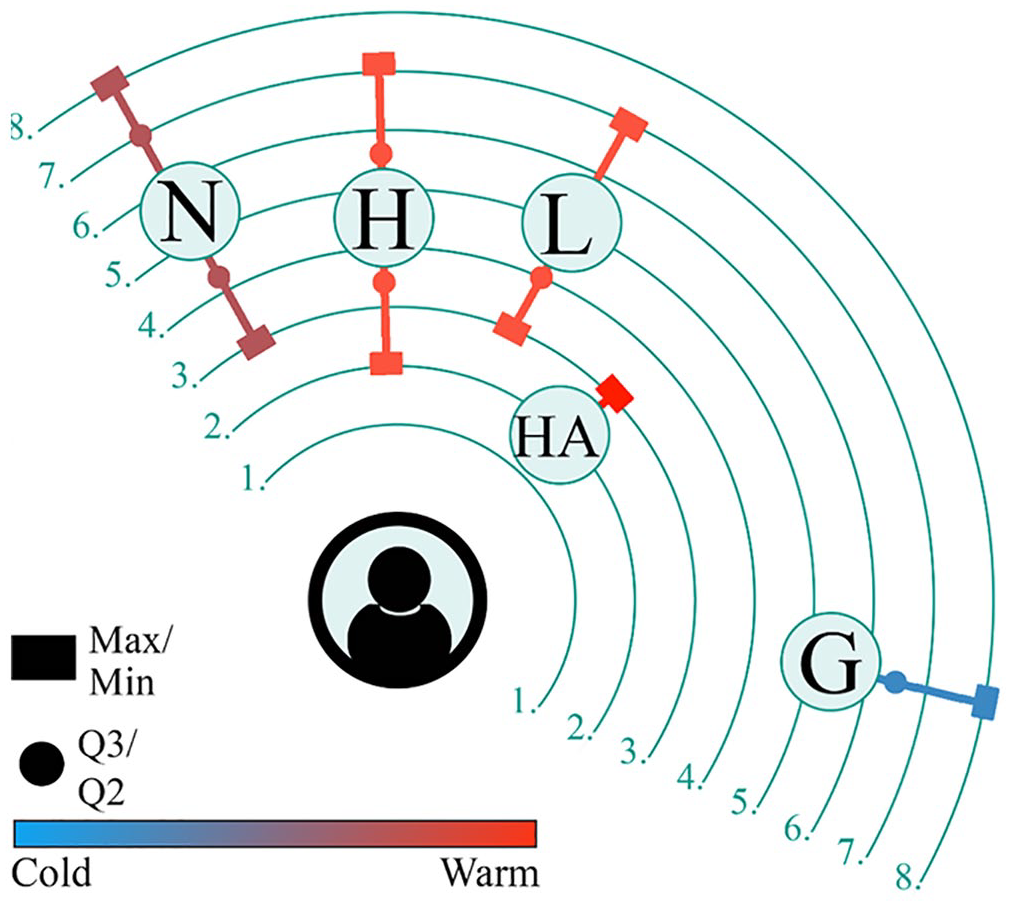
Changing IoT uses.
Vendor lock-in can create a bounded playing field that inspires confidence for users, such as Ellen and Joan. For users, such as Samuel, however, vendor lock-in is a barrier to overcome. Working with the complexity of IoT infrastructures, tech savvy users, such as Samuel, find ways to limit the number of different connection hubs and create a more streamlined infrastructure. Additionally, financial expenses motivate do-it-yourself (DIY) methods. This appears to be a viable combination, as Samuel explains,
Officially, you need a hub for this, but I didn’t feel like buying an extra hub, so I bought a USB stick online for ten euros. And that can just read the protocol, regardless of what brand it is.
The effect of Samuel’s operational savviness is shown in Figure 4, where the USB stick with HA creates a more interoperable IoT system, while simultaneously pushing Google Home outwards. Consequently, the open system of Samuel holds the potential for playful DIY projects and add-on functions. One such project is described by Samuel as follows:
I have that remote for the smart speaker from IKEA. I don’t use it for the speaker but for the lamps. I bought it last week, and it is a dial that is actually for the speaker. It has a wireless protocol, and with that, you can also operate the lamps. Well, that is what we want, of course. That is not officially intended, but you can use it however you want with the Home Assistant. I had the predecessor of this from Ikea that was made for the lamps. Only, that thing does not work so well. That was just a poorly designed product.
Somewhat like Joan, Samuel finds different applications for his IoT devices. However, Samuel’s devices require reprogramming to fit his IoT system with add-on functions. The IoT is generally a closed system, and users need confidence to open it and adjust its software. Moreover, Samuel’s emphasis on the device’s functionality echoes remarks made by Thomas, Arthur, and Ash. The difference is that Samuel lets his IoT devices “talk to each other,” improving its add-on functions and compliment quality rather than letting vendor lock-in be a hindrance.
The DIY approach to the IoT is cost effective as issues of interoperability, like the lamps of Philips and Ikea, are solved by creatively by playfully repurposing products. Samuel’s remarks show that his play-oriented DIY approaches are partly motivated by a financial incentive. This is also the case for Dennis, another IoT enthusiast, who enjoys tinkering with open-source single-board microcontrollers, such as Arduino, to modify IoT devices and tie them together. According to Dennis, finding a cheaper solution is part of the goal itself:
It is a bit of a sport to me. So, I also want to be challenged a bit creatively in that. It is a sport for me to get the most out of it and not go for convenience and spend three hundred euros more.
Remarkably, Dennis’ play-oriented approach places the potential of IoT devices in its complement quality rather than convenience and expense, unlike most IoT users. However, such a play-oriented disposition requires a technical level of operational skills. Consequently, IoT systems change often for users, such as Samuel and Dennis, as functions are constantly added and made redundant. While users, such as Arthur, emphasize that their IoT “just has to work,” it is striking that Samuel and Dennis approach IoT devices as not fully actualized to begin with. In fact, this is where they find much of their enjoyment.
Conclusion
Main findings
In this current contribution, we argue that vendor lock-in will be an important component of the continuing digital divide. As the IoT is projected to expand to general households (Aliero et al., 2020; van der Zeeuw et al., 2019), it is important to recognize that different aspects of vendor lock-in are common for IoT infrastructures (Noura et al., 2019; Pal et al., 2018). We explored vendor lock-in as a market-orchestrated component of digital inequalities by asking why some people are limited by vendor lock-in while others can creatively capitalize on the potential benefits of the IoT. In our methods, we used interviews and a diary study for statistical guidance. We would note again that our statistical results are not conclusive in terms of generalizing the findings from our sample to a larger population. Instead, evaluating relative positions to IoT creativity using metaphorical prerequisites gives us a conceptual understanding of IoT use that is transferable to future studies on digital inequalities related to the IoT.
In exploring our research question, we find three distinct perspectives. First, the limitations caused by vendor lock-in become apparent when people use their IoT as a task-oriented tools for specific problems rather than considering the interoperability of IoT systems. Therefore, one solution is to choose devices with more core functions because it can be difficult to switch devices in the future. Second, we find that vendor lock-in can promote confidence that stimulates play orientation and, in effect, operational skills. Thus, vendor lock-in can provide an environment like a protected playground, albeit with a relatively higher entrance fee. This implies that vendor lock-in is stimulating rather than hindering, but only if people have sufficient financial resources to integrate their IoT systems; a “rich-get-richer” effect that was emphasized by Ignatow and Robinson (2017) and is common in digital inequalities (Lutz, 2019). Third, vendor lock-in can be considered a boundary and also a play-oriented challenge. Creative and operationally skilled people can reduce financial costs by reprogramming hardware and software to improve compliment quality and by investing time and effort.
When we relate these findings to one another, we find a pattern of exclusion. Namely, the broader potential of IoT devices is mostly accessible for people with more financial resources or people who excel in operational skills and creative problem-solving. Thus, the people who are most excluded from the potential of the IoT are those who perceive IoT devices as tools tied specific problems. In the experience of such users, IoT systems tend to become more expensive due to the additional costs of restructuring interoperability standards. Moreover, IoT use does not seem to stimulate operational skills or creativity in these users. This means that this type of users would not only experience additional costs but are also more likely experience impoverished digital skills in the future.
Future research and limitations
We hope to inspire future digital inequality research to consider dynamics of vendor lock-in as a contributing component. In our approach we have emphasized commonalities in using the IoT as a platform more than the sum of its parts. We argue that using the IoT is something different than using individual IoT devices separately. Research indicates that future digital inequalities will continue to involve access to multiple hardware devices (Van Dijk, 2020), which will also require a focus on interoperability. However, future research should focus also on limitations posed by specific devices. The IoT might be more than the sum of its parts, yet its parts still need individual examination. An alternative approach to our contribution would be to examine the limitations of individual devices in terms of technology affordance (Bayer et al., 2021). Moreover, technology affordance can be a viable counterpoint to our study as it focuses on goal-directed actions of goal-oriented actors, whereas we emphasized play-oriented action and IoT use beyond goal orientation in relation to vendor lock to stimulate operational skills. As such, a goal-oriented technology affordance models may add limitations not only to people but also in relation to individual devices.
Our contribution is not without limitations, and some of our considerations may raise some concerns. First, one might ask if our figuration diaries test how willing people are to use metaphors rather than test metaphorical prerequisites themselves. At the very least, we would argue that an unwillingness to use metaphors, rather than viewing their IoT as devices cold and distant, coincides with perceiving the IoT as “nothing but” a functional tool. This concern also relates to a second limitation: that we have forced answers in the figuration diaries using only two prerequisites. Here, we emphasize that our diary study was embedded in interviews. However, we hope to inspire future research to use abstract concepts to reveal social phenomena.
Footnotes
Authors’ note
Giedo Jansen is now affiliated to University of Amsterdam, Amsterdam, Netherlands.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work is part of the research programme ‘Any Thing for Anyone? An individual and Socio-contextual approach to the Internet-of-Things skill inequalities’ with project number 452-17-001, which is (partly) financed by the Netherlands Organisation for Scientific Research (NWO).
